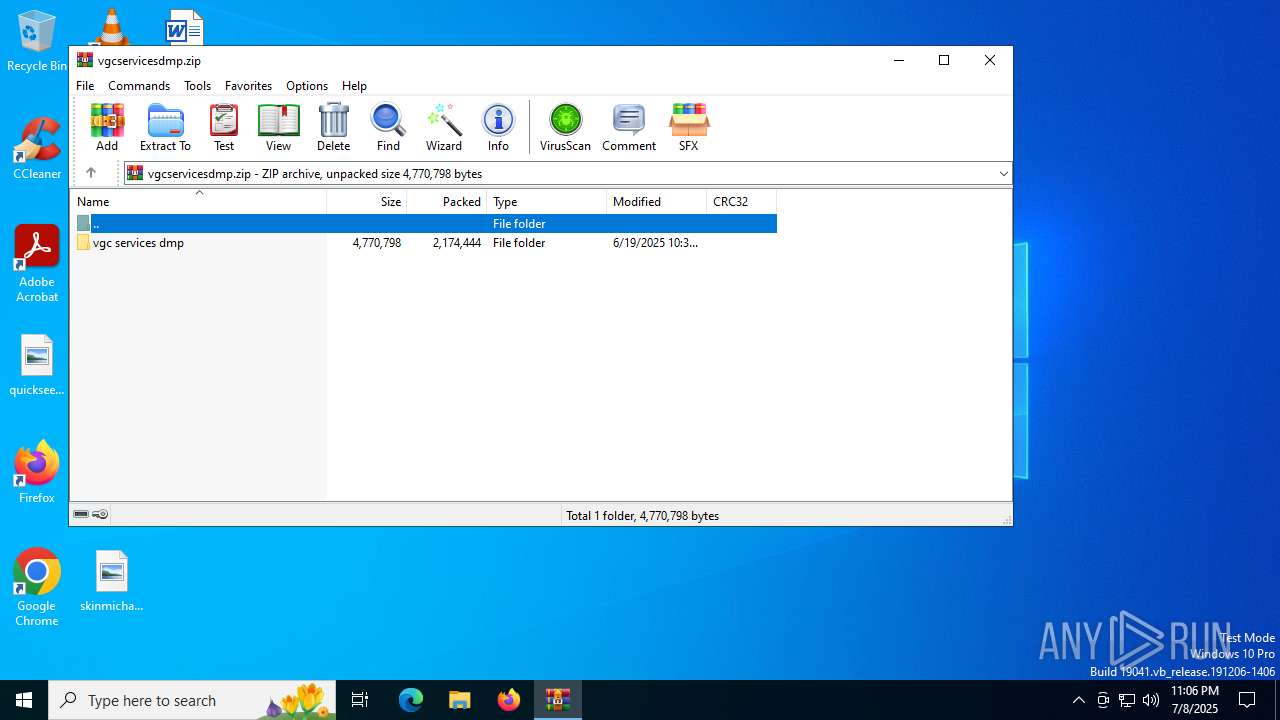
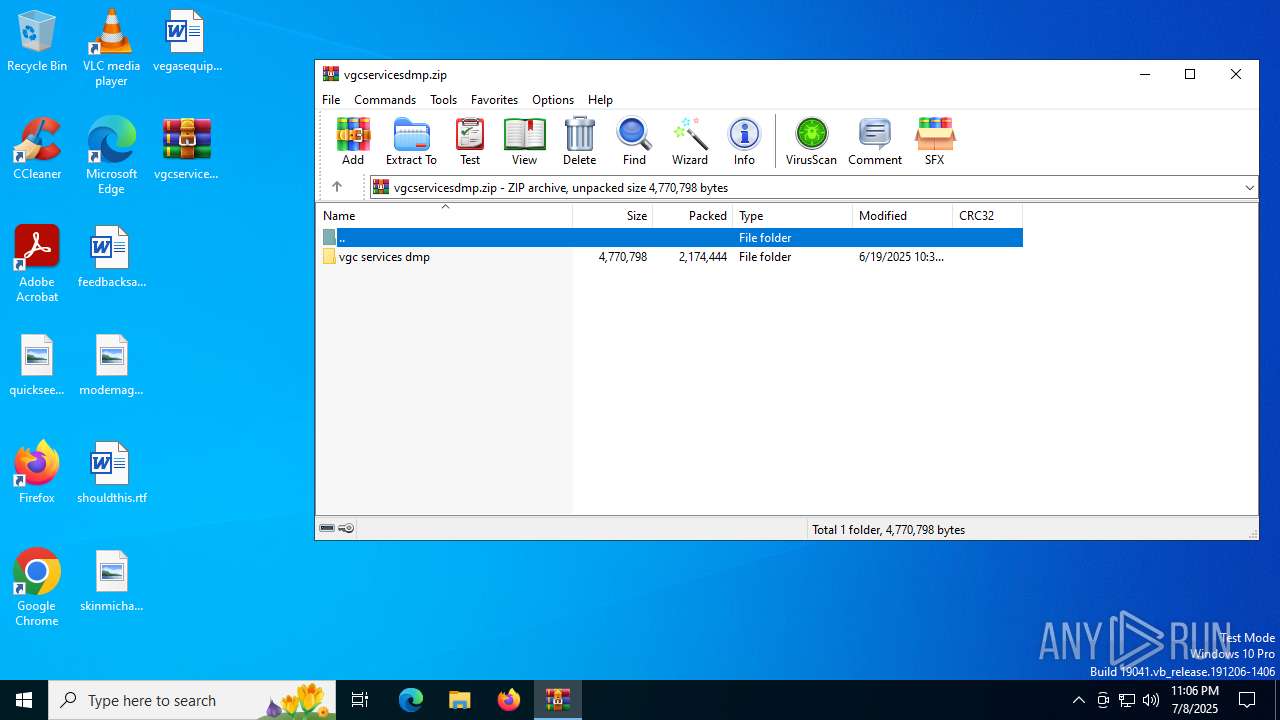
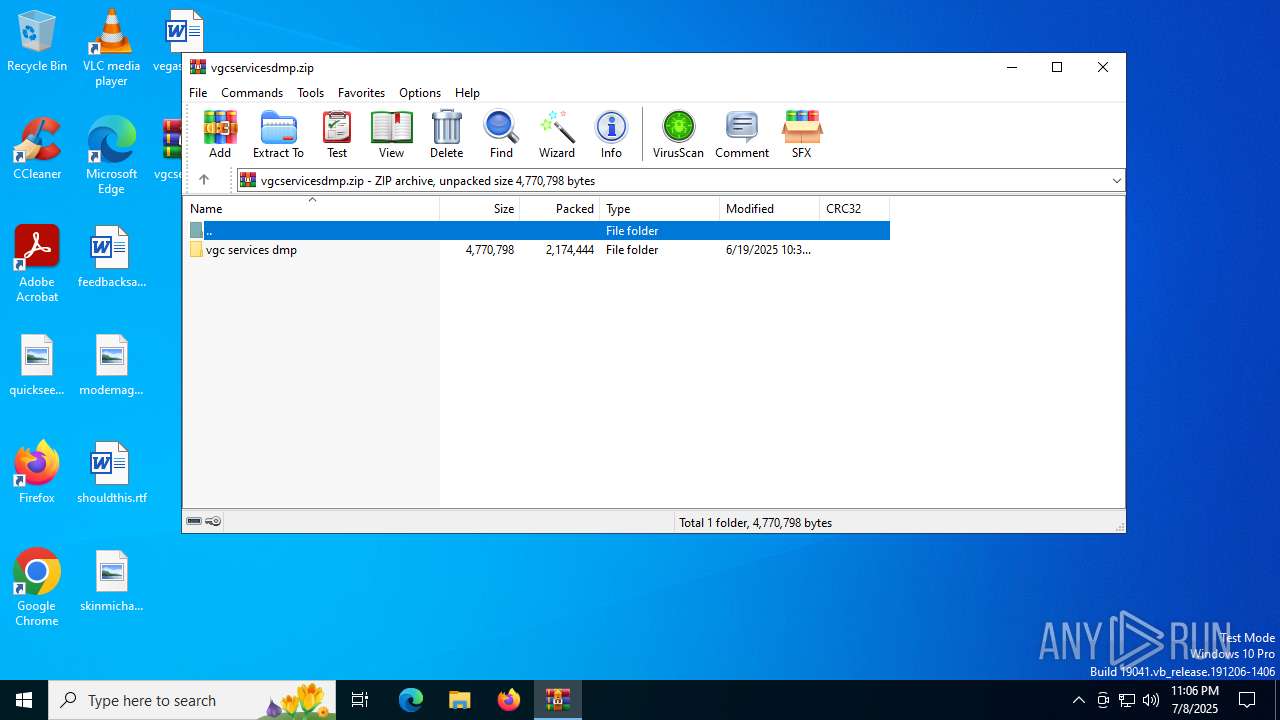
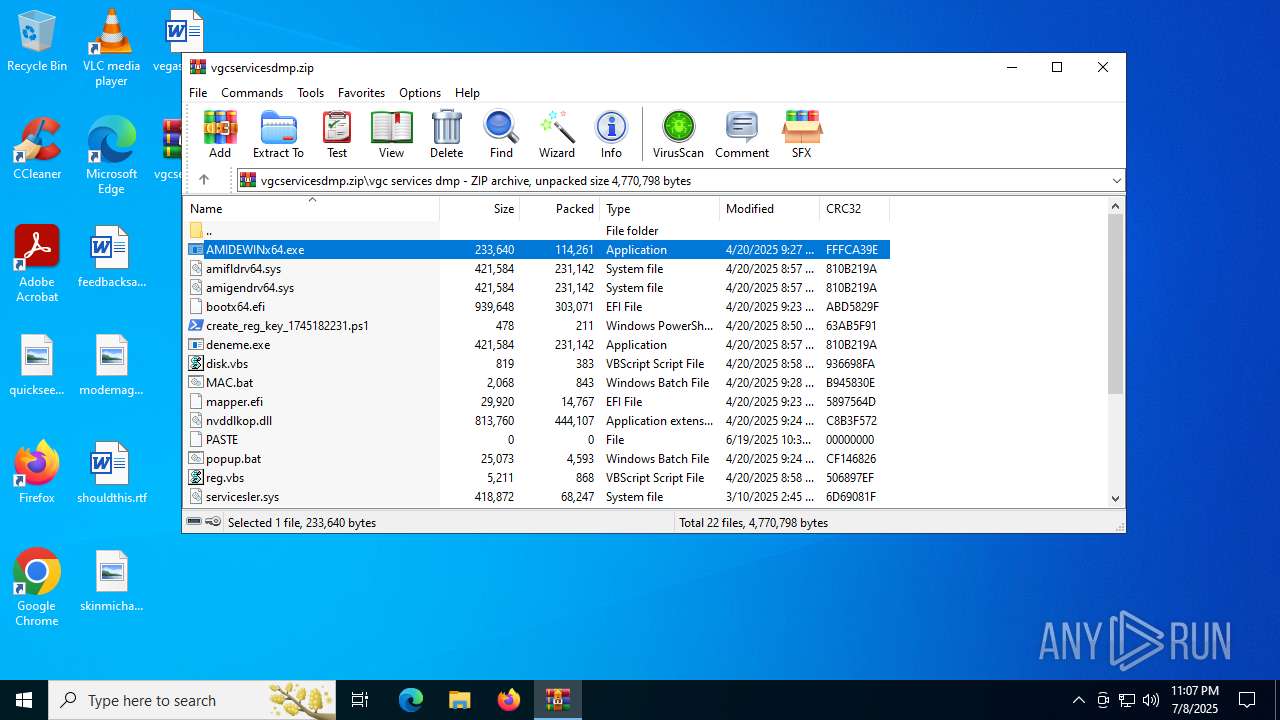
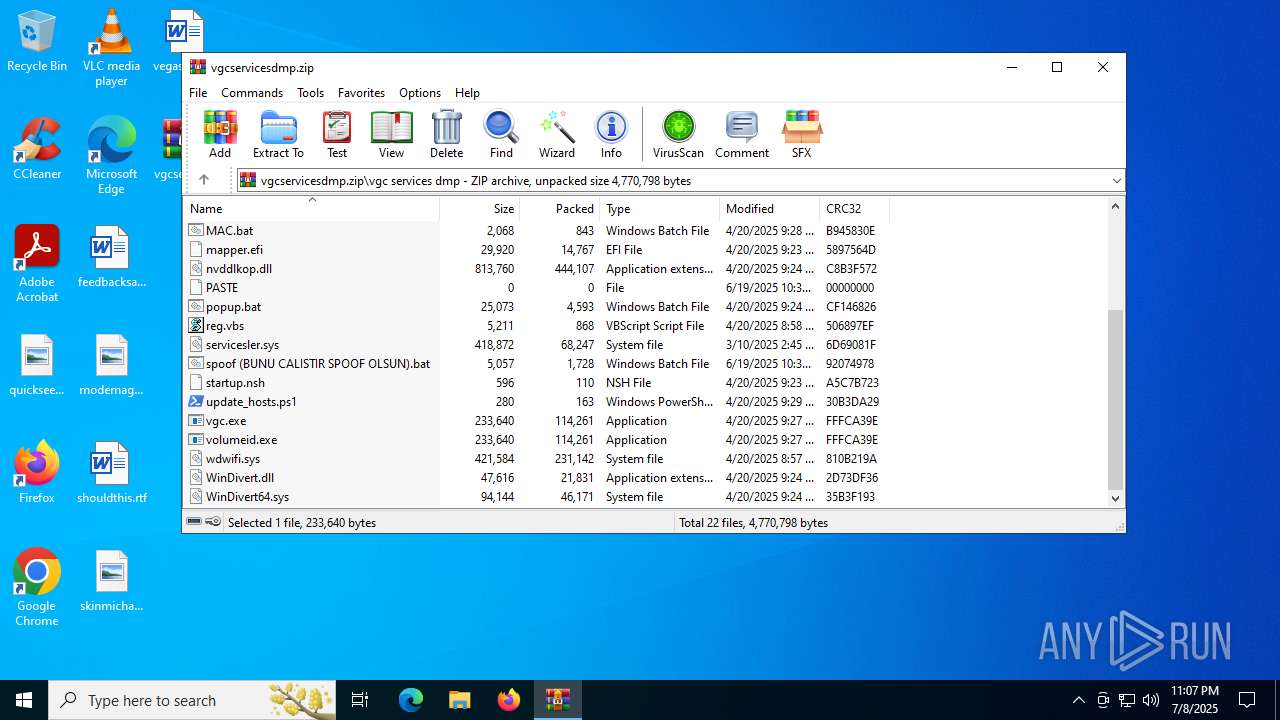
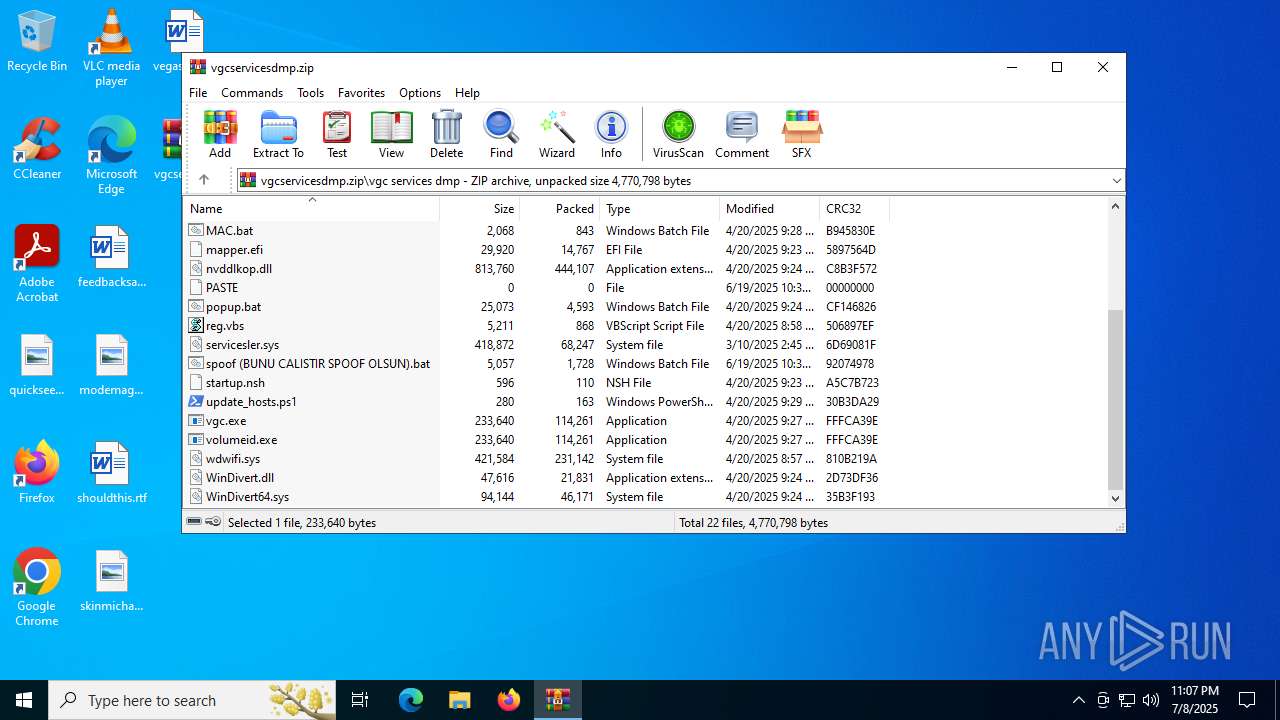
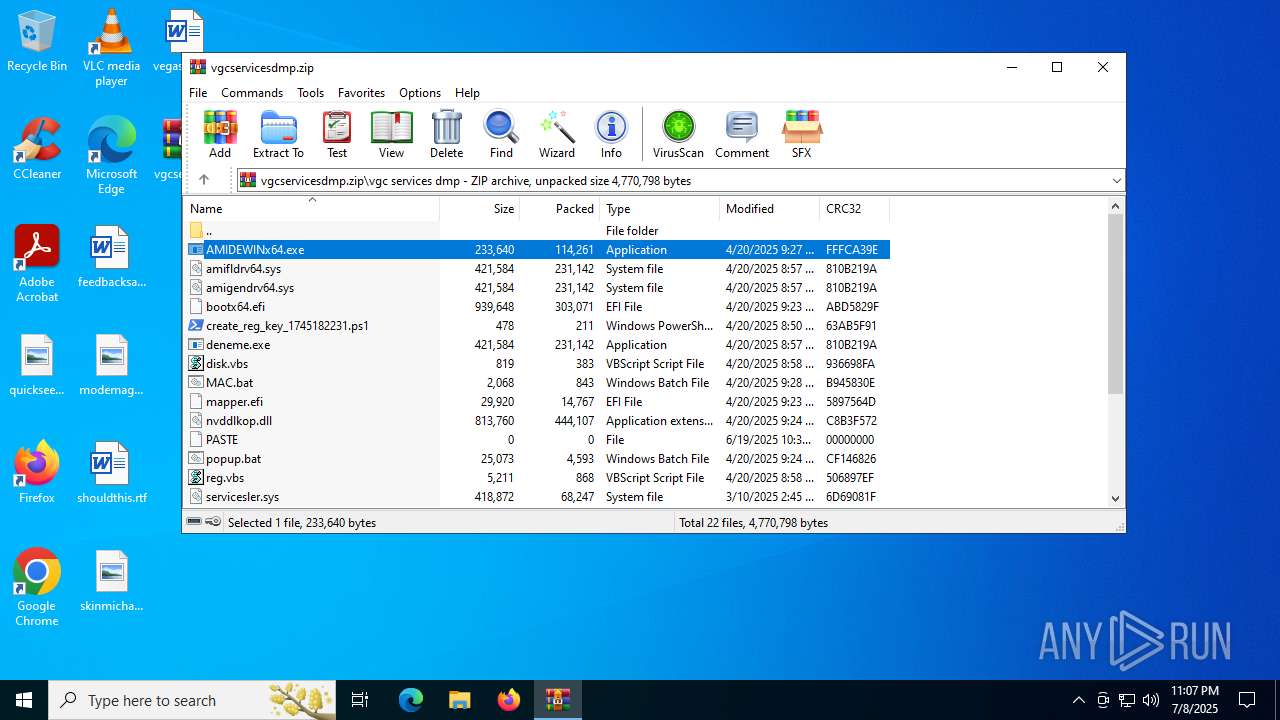
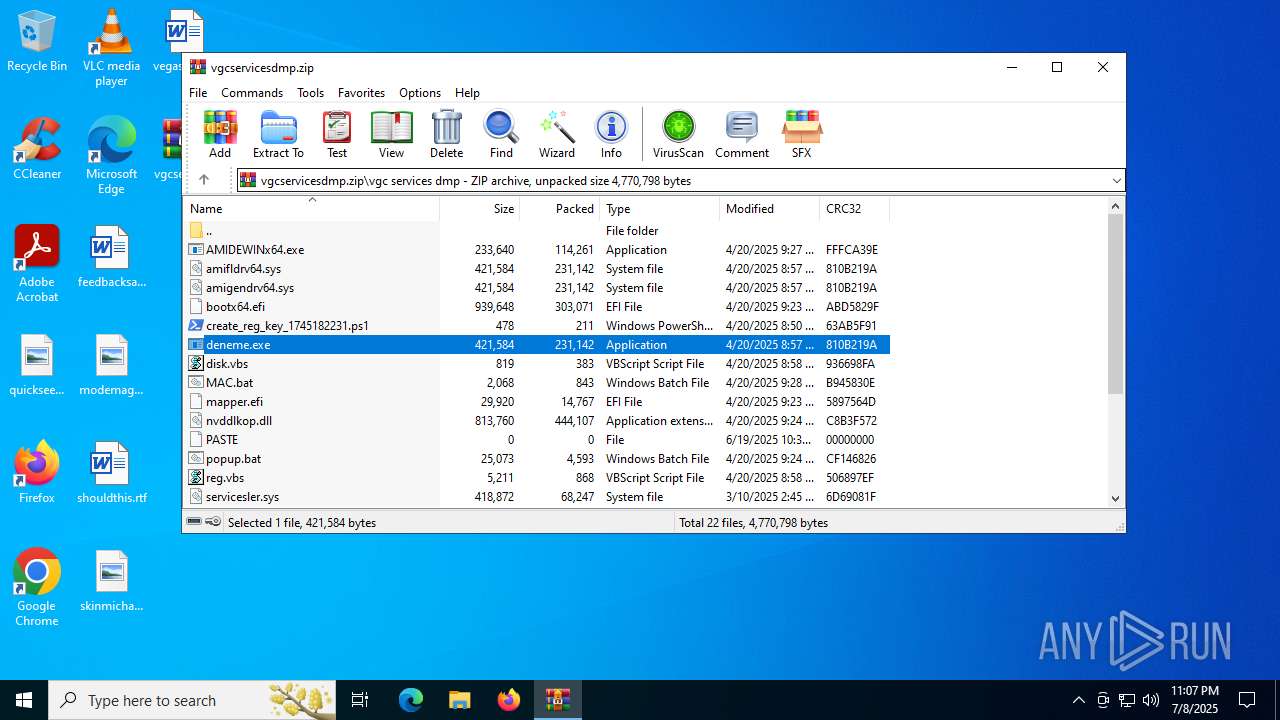
| File name: | vgcservicesdmp.zip |
| Full analysis: | https://app.any.run/tasks/10eb9ec3-7217-4f51-a7e9-2b02a125cc6d |
| Verdict: | Malicious activity |
| Analysis date: | July 08, 2025, 23:06:05 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v1.0 to extract, compression method=store |
| MD5: | F278F2C26E5EAD67D12700CD07D2C35B |
| SHA1: | 377EB8C15D95D1C6C19A60429EE9A33ADF34AD9C |
| SHA256: | 5E197BA11AA89423AFAFA3C77E6D911F8CE40F009E58C08DE76FD6BBB41684BF |
| SSDEEP: | 98304:1Ix/T+W47VpFo0zy6kPFo0zy6kd9KJIrXkKDEF8fJ2Fo0zy6ktlTYFmNA1XW5bUq:p3 |
MALICIOUS
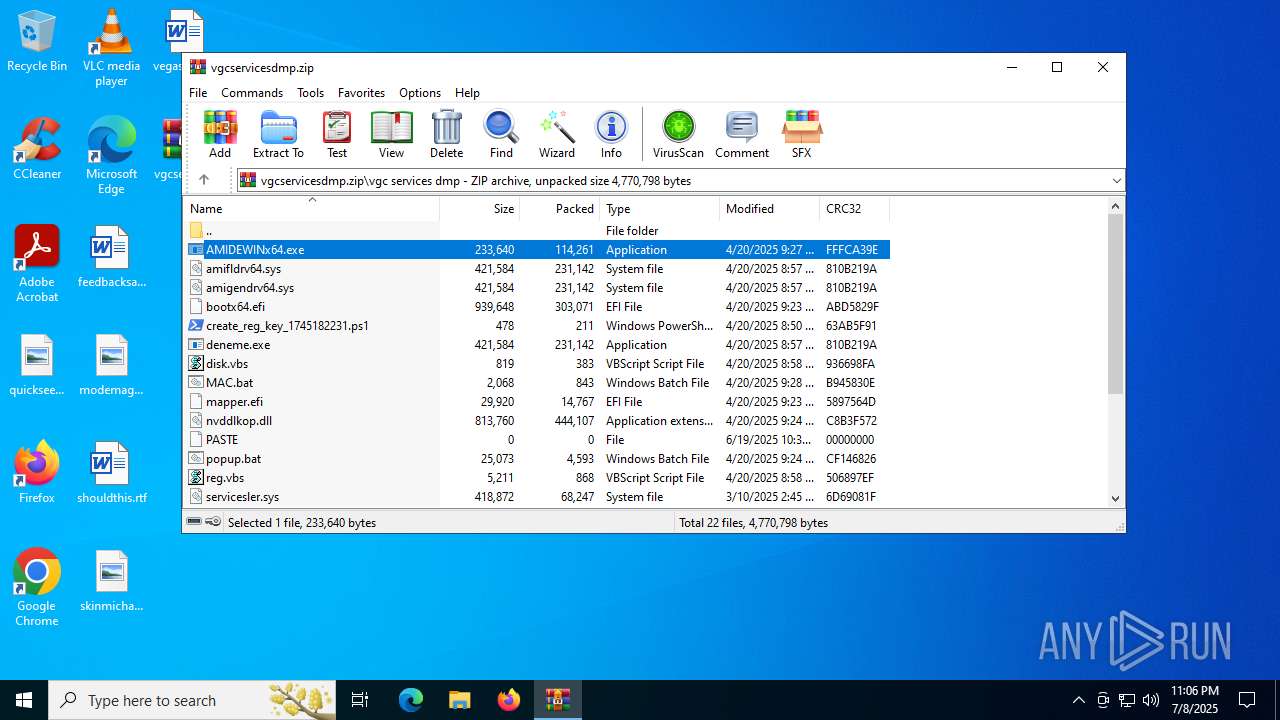
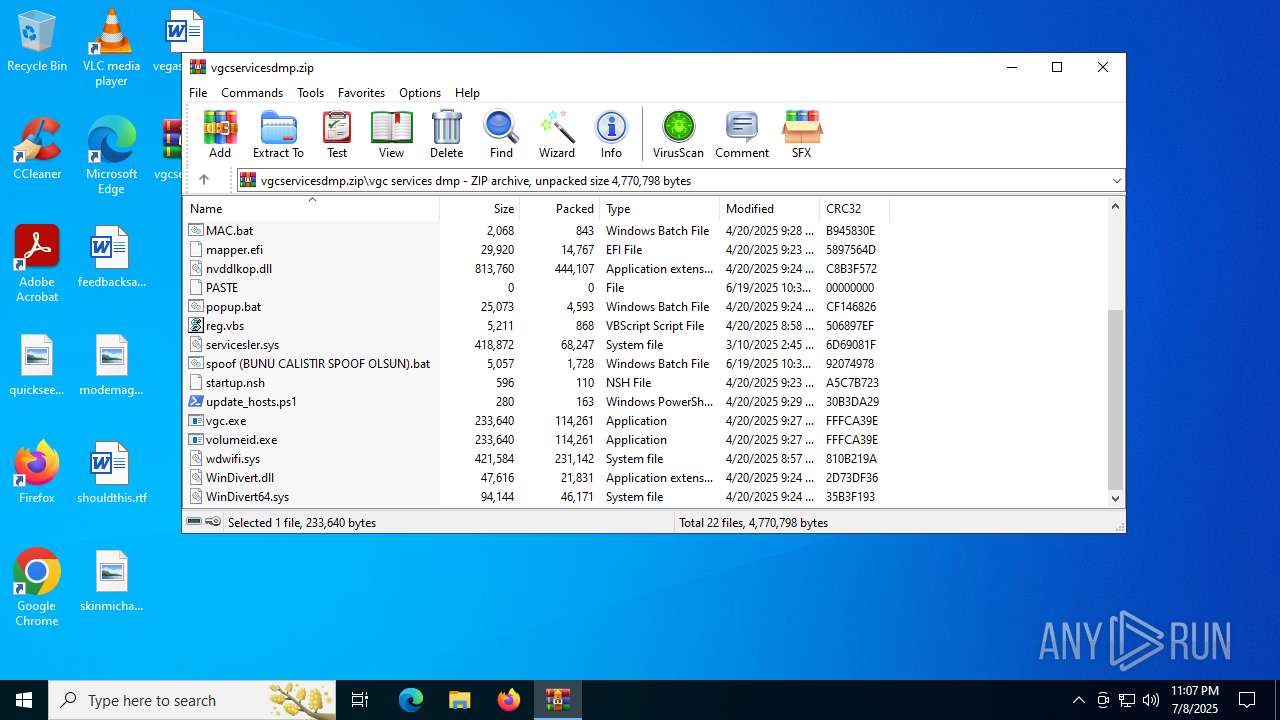
Malicious driver has been detected
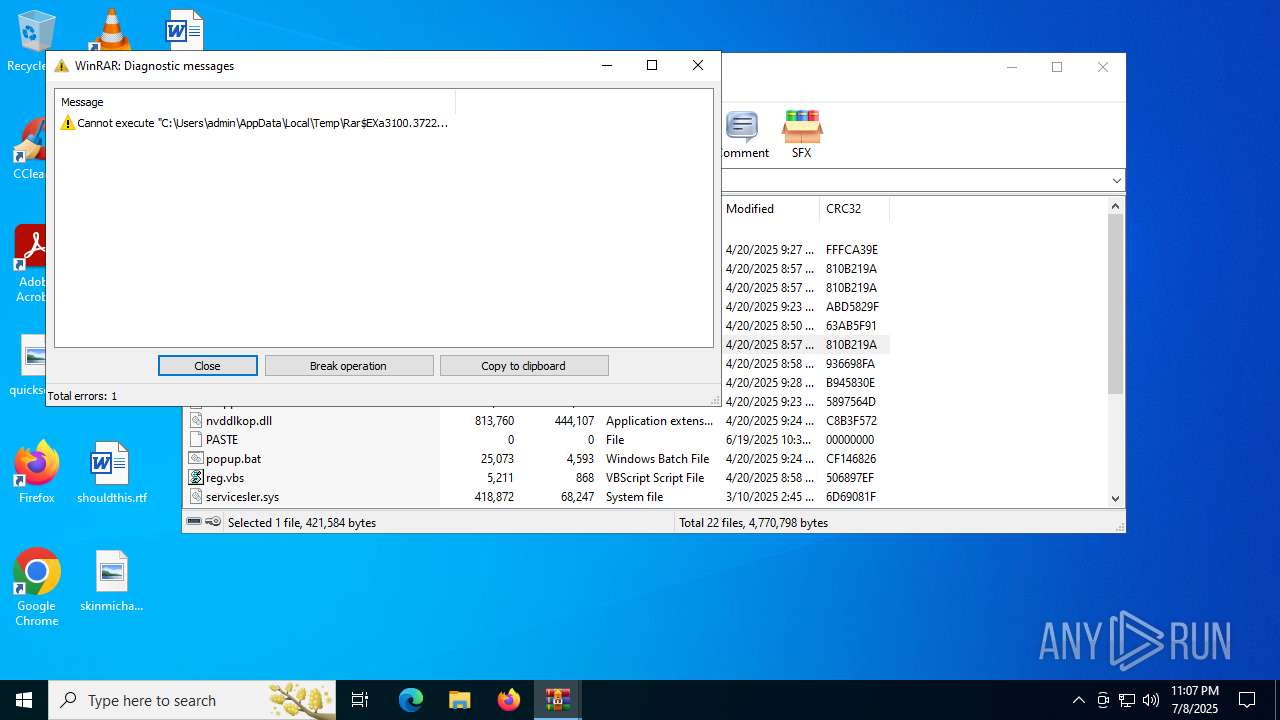
- WinRAR.exe (PID: 3100)
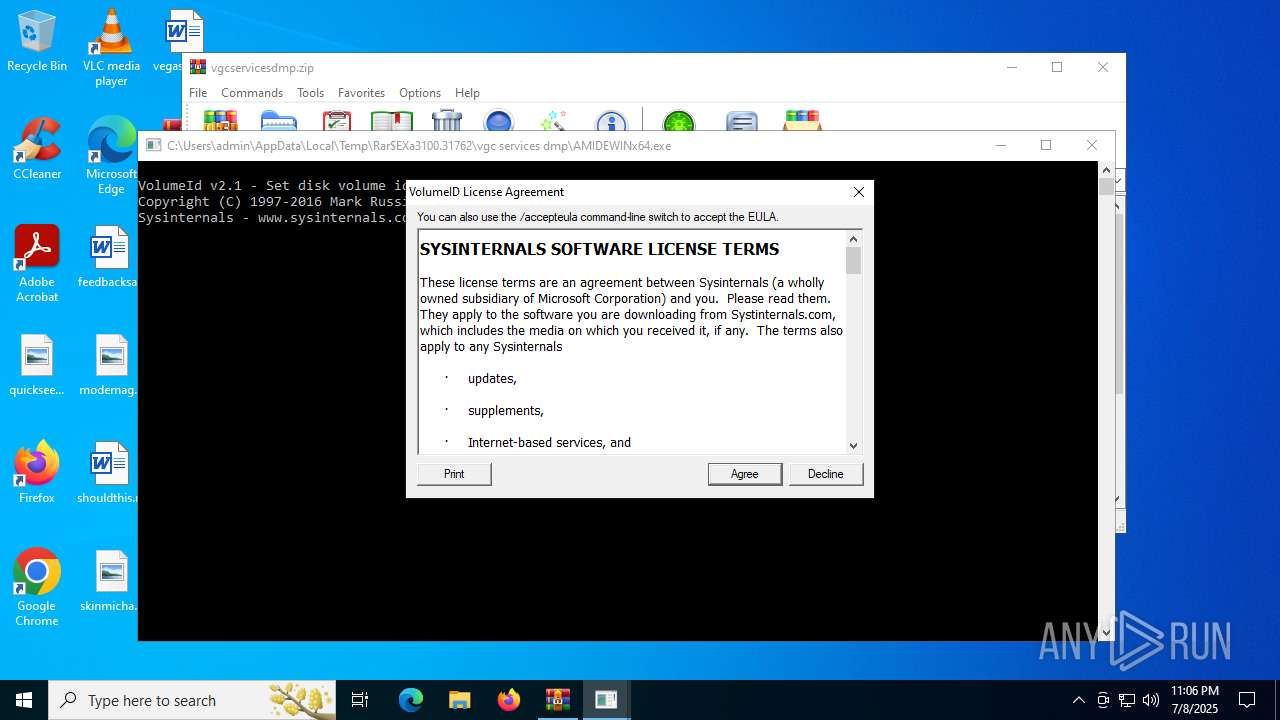
Executing a file with an untrusted certificate
- AMIDEWINx64.exe (PID: 6380)
- AMIDEWINx64.exe (PID: 6348)
SUSPICIOUS
Drops a system driver (possible attempt to evade defenses)
- WinRAR.exe (PID: 3100)
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 3100)
INFO
The sample compiled with english language support
- WinRAR.exe (PID: 3100)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 3100)
Checks supported languages
- AMIDEWINx64.exe (PID: 6380)
- AMIDEWINx64.exe (PID: 6348)
Reads the computer name
- AMIDEWINx64.exe (PID: 6380)
Checks proxy server information
- slui.exe (PID: 1564)
Reads the software policy settings
- slui.exe (PID: 1564)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 10 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | None |
| ZipModifyDate: | 2025:06:20 01:32:32 |
| ZipCRC: | 0x00000000 |
| ZipCompressedSize: | - |
| ZipUncompressedSize: | - |
| ZipFileName: | vgc services dmp/ |
Total processes
144
Monitored processes
7
Malicious processes
1
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1564 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
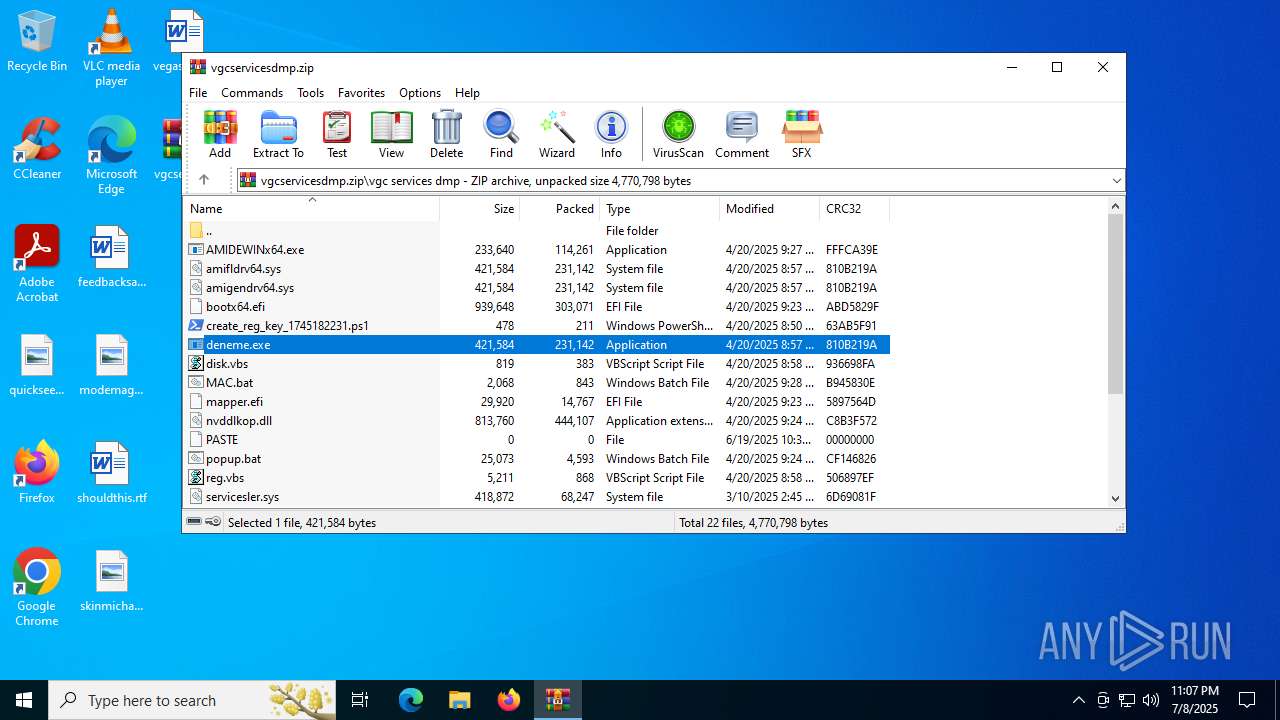
| 2692 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa3100.37222\vgc services dmp\deneme.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa3100.37222\vgc services dmp\deneme.exe | — | WinRAR.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3100 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\Desktop\vgcservicesdmp.zip | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Version: 5.91.0 Modules
| |||||||||||||||
| 5436 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | AMIDEWINx64.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6348 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa3100.36168\vgc services dmp\AMIDEWINx64.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa3100.36168\vgc services dmp\AMIDEWINx64.exe | — | WinRAR.exe | |||||||||||
User: admin Company: Sysinternals - www.sysinternals.com Integrity Level: MEDIUM Description: Set disk volume id Exit code: 1 Version: 2.1 Modules
| |||||||||||||||
| 6380 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa3100.31762\vgc services dmp\AMIDEWINx64.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa3100.31762\vgc services dmp\AMIDEWINx64.exe | — | WinRAR.exe | |||||||||||
User: admin Company: Sysinternals - www.sysinternals.com Integrity Level: MEDIUM Description: Set disk volume id Exit code: 1 Version: 2.1 Modules
| |||||||||||||||
| 7060 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | AMIDEWINx64.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
2 560
Read events
2 550
Write events
10
Delete events
0
Modification events
| (PID) Process: | (3100) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (3100) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (3100) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (3100) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\vgcservicesdmp.zip | |||
| (PID) Process: | (3100) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3100) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3100) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (3100) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (6380) AMIDEWINx64.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Sysinternals\VolumeID |
| Operation: | write | Name: | EulaAccepted |
Value: 1 | |||
| (PID) Process: | (6348) AMIDEWINx64.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Sysinternals\VolumeID |
| Operation: | write | Name: | EulaAccepted |
Value: 1 | |||
Executable files
39
Suspicious files
0
Text files
24
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3100 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa3100.31762\vgc services dmp\update_hosts.ps1 | text | |
MD5:0199FA53B7CDB95D27179FFEDD4A7B8C | SHA256:D9C9CCAFBC52AED5BB60C6823157A85E99D6B769D7AD15EF087887B9B8F0C1AB | |||
| 3100 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa3100.31762\vgc services dmp\popup.bat | text | |
MD5:F50A5AA54B7F167653495BD9DAB137B4 | SHA256:6D9EC7C495A6A396A6A10A910688C4D9596731002B112730120A003CDC36B2CE | |||
| 3100 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa3100.31762\vgc services dmp\disk.vbs | text | |
MD5:E2E55CE217658A13775610D5982347DC | SHA256:045AC02F8832A8ADFB14A0DA0F75CD9445CBC362743CA8F65258977FE5393138 | |||
| 3100 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa3100.31762\vgc services dmp\MAC.bat | text | |
MD5:86630F471A1C7F40E8494347F9AB8249 | SHA256:C15FAADE0E71ACD4ABCB60A7E9F3F002A46D3D47BD294F7B12D811C871D1292C | |||
| 3100 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa3100.31762\vgc services dmp\wdwifi.sys | executable | |
MD5:8D2692C5A0915C19FE65F298D7100DA3 | SHA256:A4D3D3C794C6FD0C238B8E99D7480BD7255DF7F7C8F159E1A588E7A1A1D582AE | |||
| 3100 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa3100.31762\vgc services dmp\vgc.exe | executable | |
MD5:4D867033B27C8A603DE4885B449C4923 | SHA256:22A2484D7FA799E6E71E310141614884F3BC8DAD8AC749B6F1C475B5398A72F3 | |||
| 3100 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa3100.31762\vgc services dmp\startup.nsh | text | |
MD5:E24B799708329072FB55564EAB613023 | SHA256:0342793216AE3211E8F5414618B9DB8EDE63C5C646BC0F6368FE96E79D34FFE0 | |||
| 3100 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa3100.31762\vgc services dmp\mapper.efi | executable | |
MD5:7D8F71AF64A5CEEEAC726C1477943F4F | SHA256:2B75094D8D2E4A909DB292DF1EC7209CA7EC4AFC120FDAB1854774B43E49D16D | |||
| 3100 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa3100.31762\vgc services dmp\create_reg_key_1745182231.ps1 | text | |
MD5:B162C4443D31A8075F94E0D3BCEC936E | SHA256:45E7101967D7D1D77F1FC8411CA7C46167B08636DFCDB528FA53D0772682539C | |||
| 3100 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa3100.31762\vgc services dmp\amigendrv64.sys | executable | |
MD5:8D2692C5A0915C19FE65F298D7100DA3 | SHA256:A4D3D3C794C6FD0C238B8E99D7480BD7255DF7F7C8F159E1A588E7A1A1D582AE | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
8
TCP/UDP connections
37
DNS requests
20
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1268 | svchost.exe | GET | 200 | 23.216.77.28:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
2764 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
5328 | SearchApp.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
5328 | SearchApp.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
3740 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
3740 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
2940 | svchost.exe | GET | 200 | 2.23.197.184:80 | http://x1.c.lencr.org/ | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1268 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5944 | MoUsoCoreWorker.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6004 | RUXIMICS.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1268 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1268 | svchost.exe | 23.216.77.28:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
1268 | svchost.exe | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
2764 | svchost.exe | 40.126.31.0:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2764 | svchost.exe | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
www.bing.com |
| whitelisted |
fp.msedge.net |
| whitelisted |
nexusrules.officeapps.live.com |
| whitelisted |
th.bing.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Unknown Traffic | ET USER_AGENTS Microsoft Dr Watson User-Agent (MSDW) |