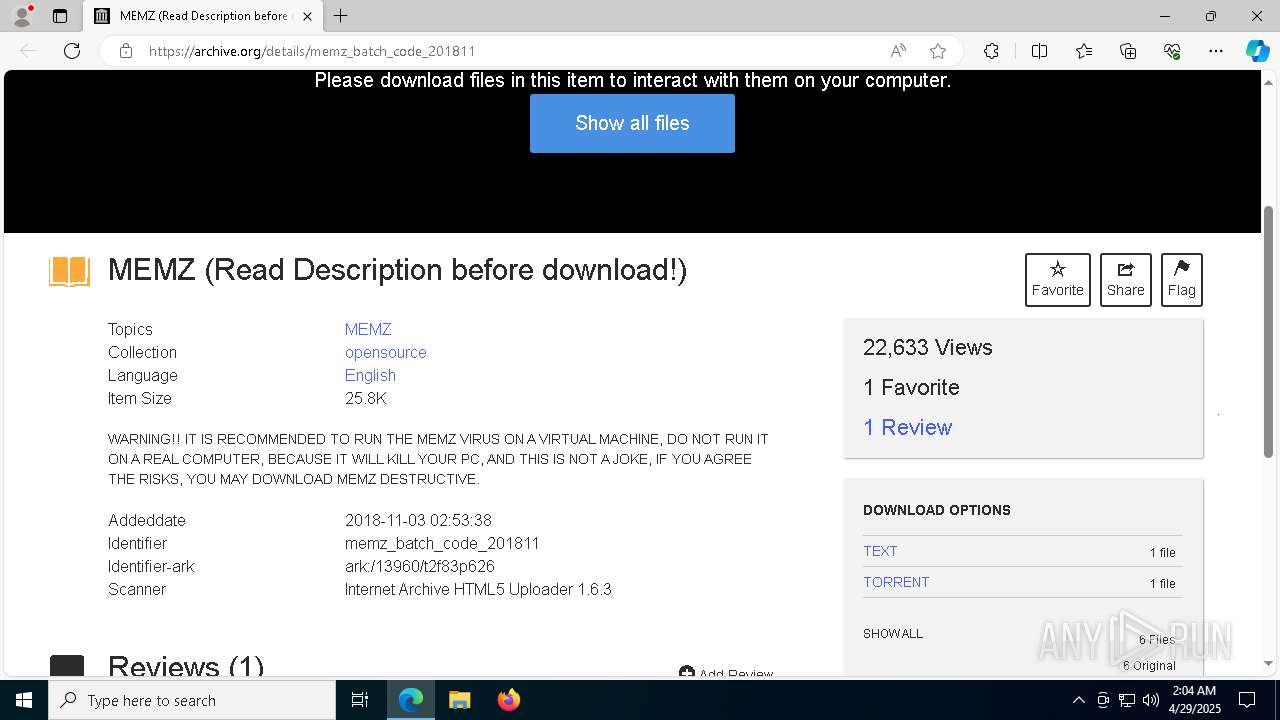
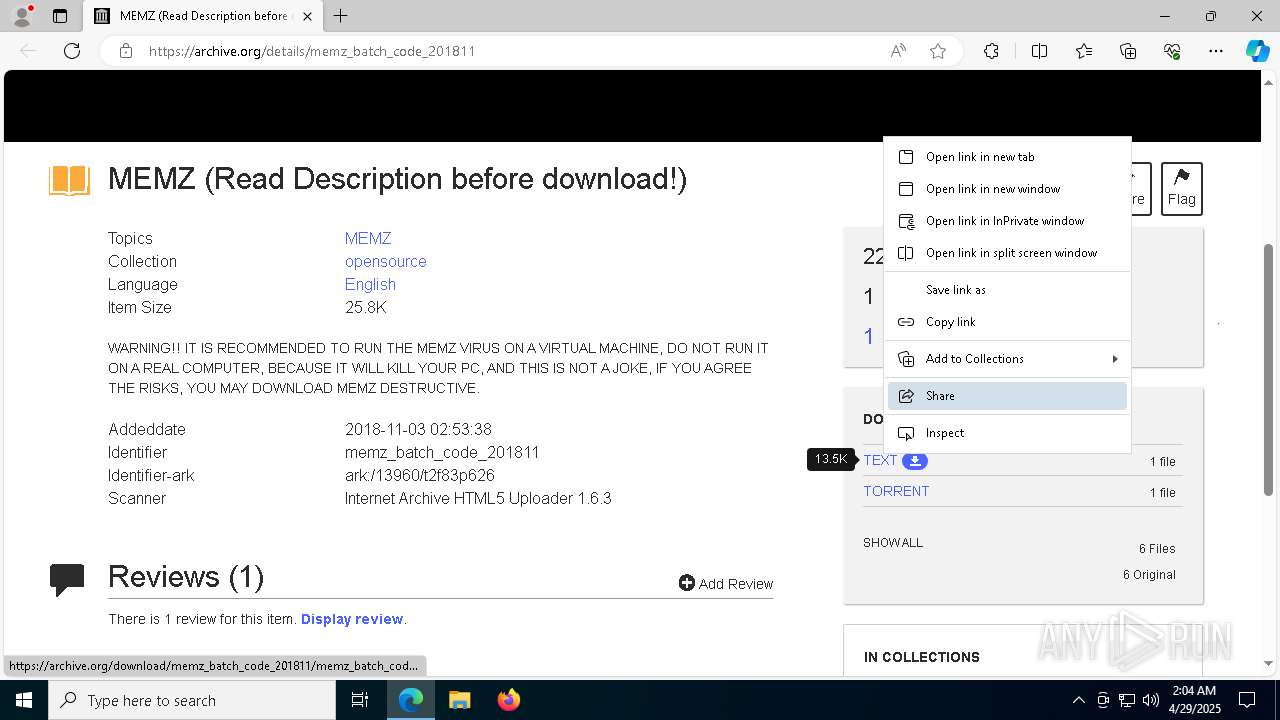
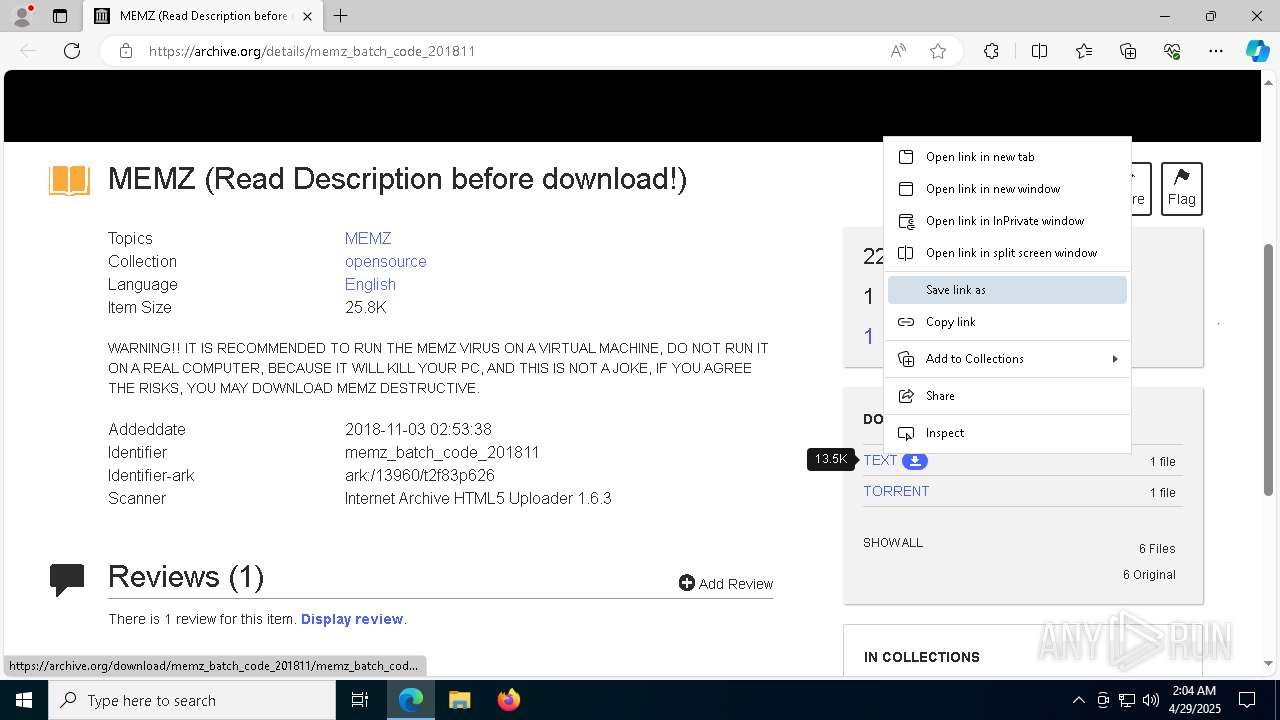
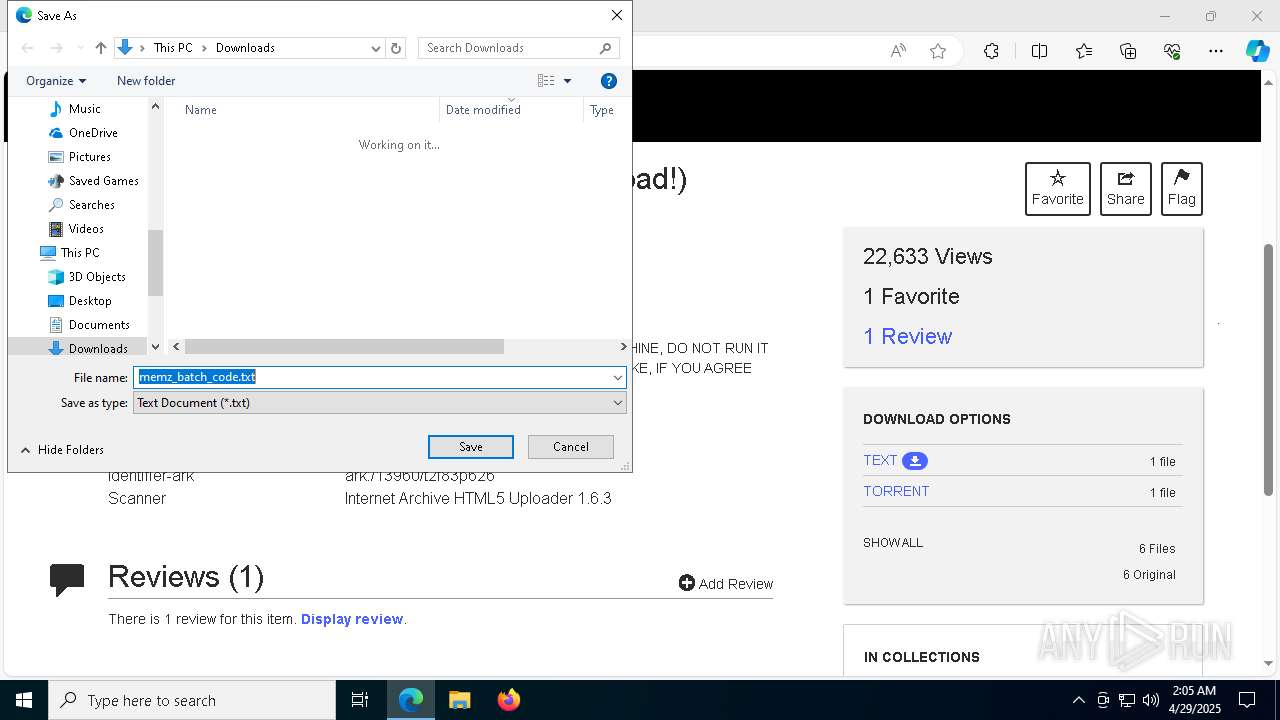
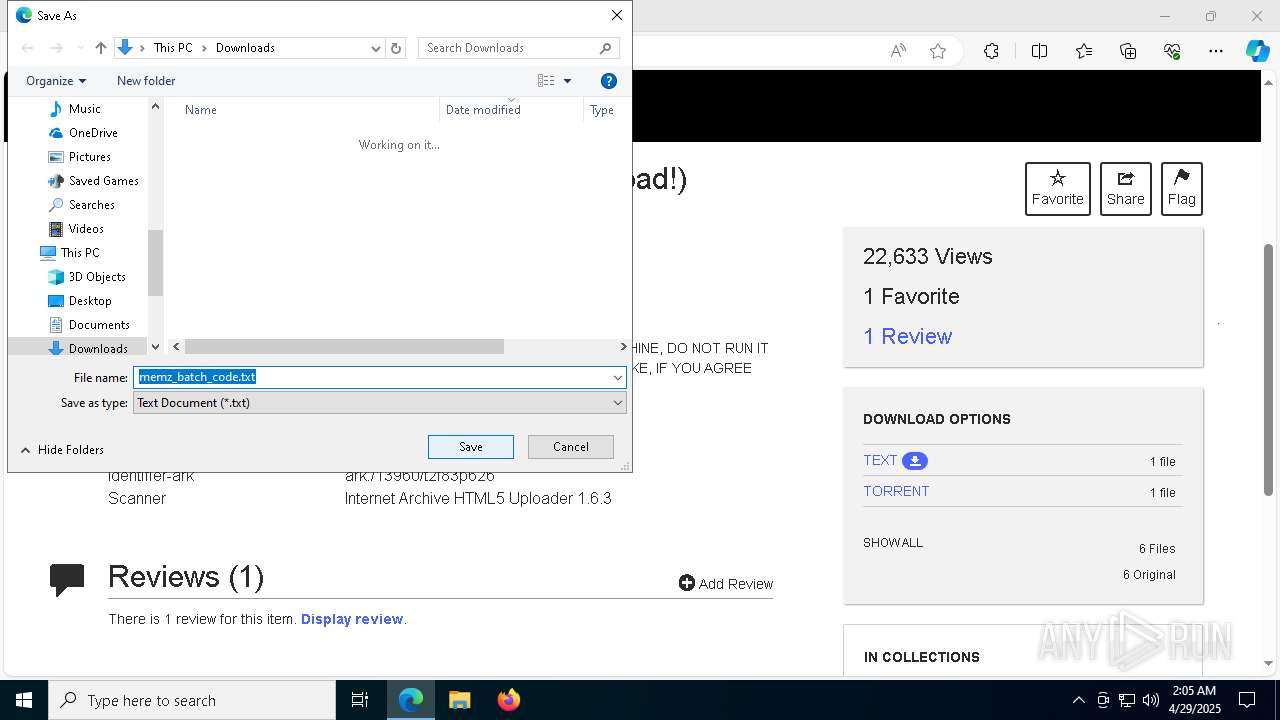
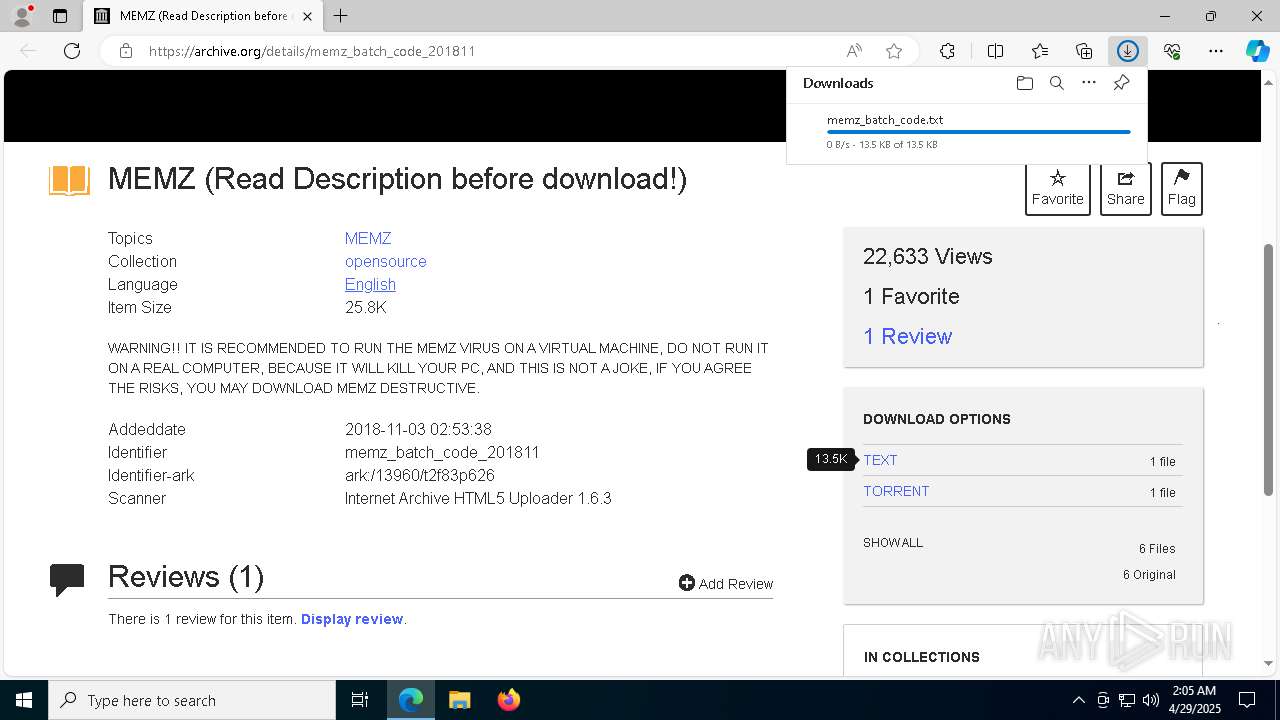
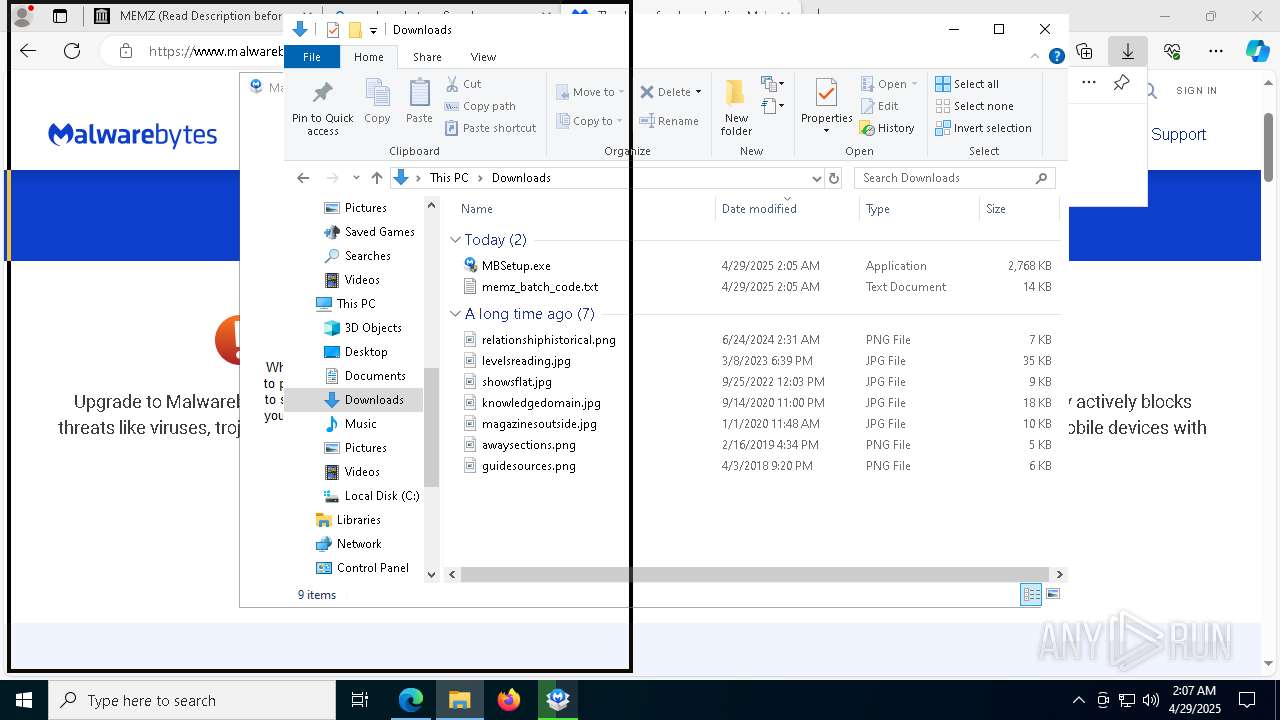
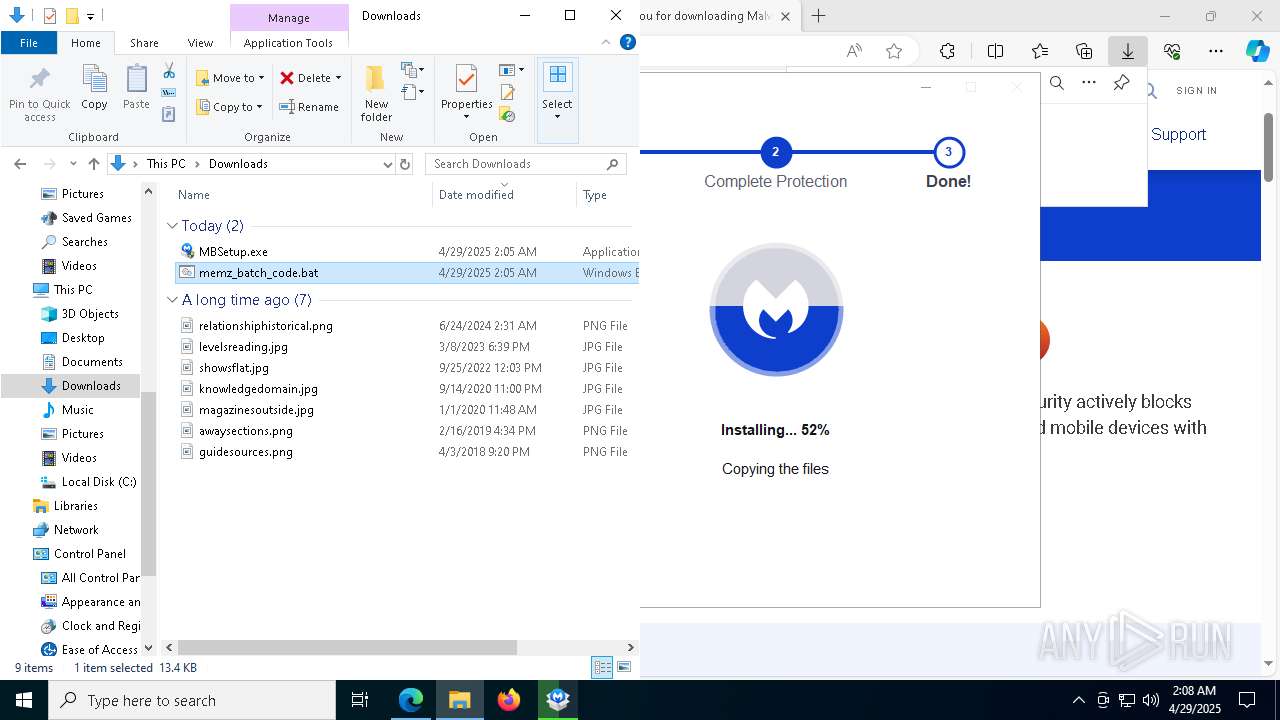
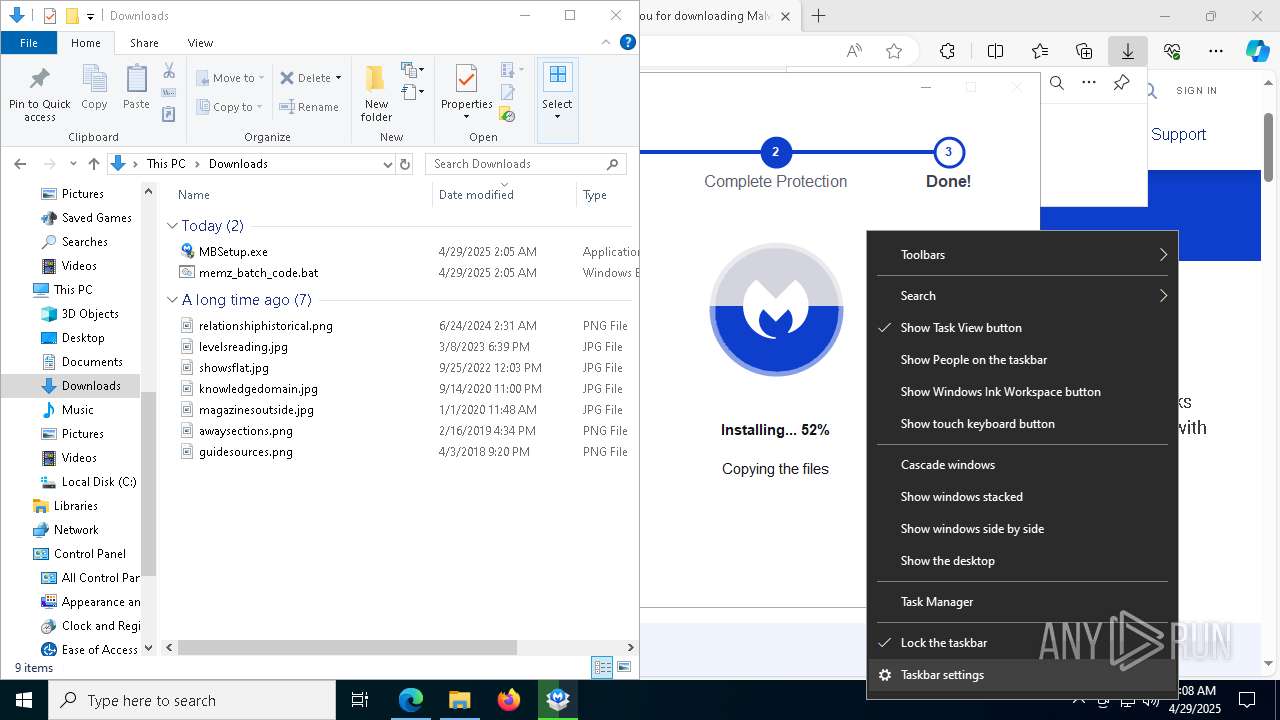
| URL: | https://archive.org/details/memz_batch_code_201811 |
| Full analysis: | https://app.any.run/tasks/b107347a-9565-46bf-8f35-84f3ff62846f |
| Verdict: | Malicious activity |
| Analysis date: | April 29, 2025, 02:04:42 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 8C7D264007E0663115ACC63829B9D288 |
| SHA1: | 6DB4A0843D093421796CD80C6B6F886B8CE23424 |
| SHA256: | 5DFEAD1A0F4B742DD6A1CECAEF4FCA9F440847D66FB8A61A739F46AC592E19A2 |
| SSDEEP: | 3:N8MFXJwJNItSH56ccU:2MFXeNItSH564 |
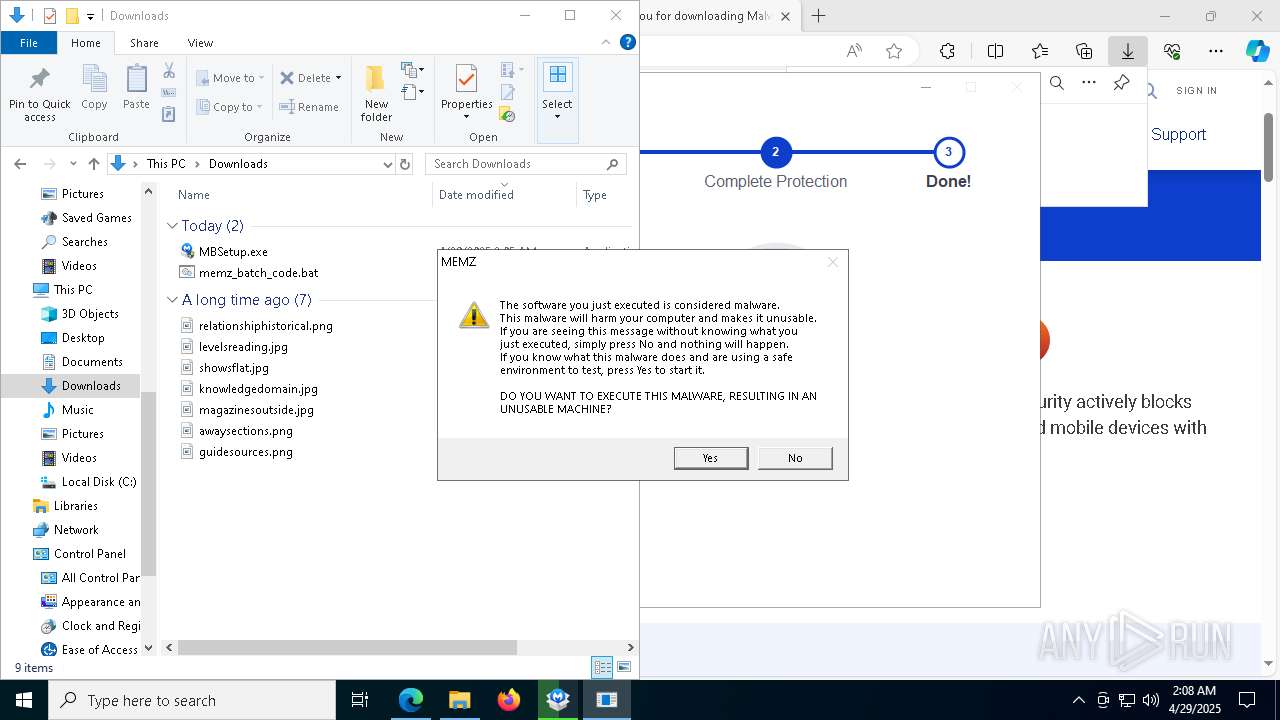
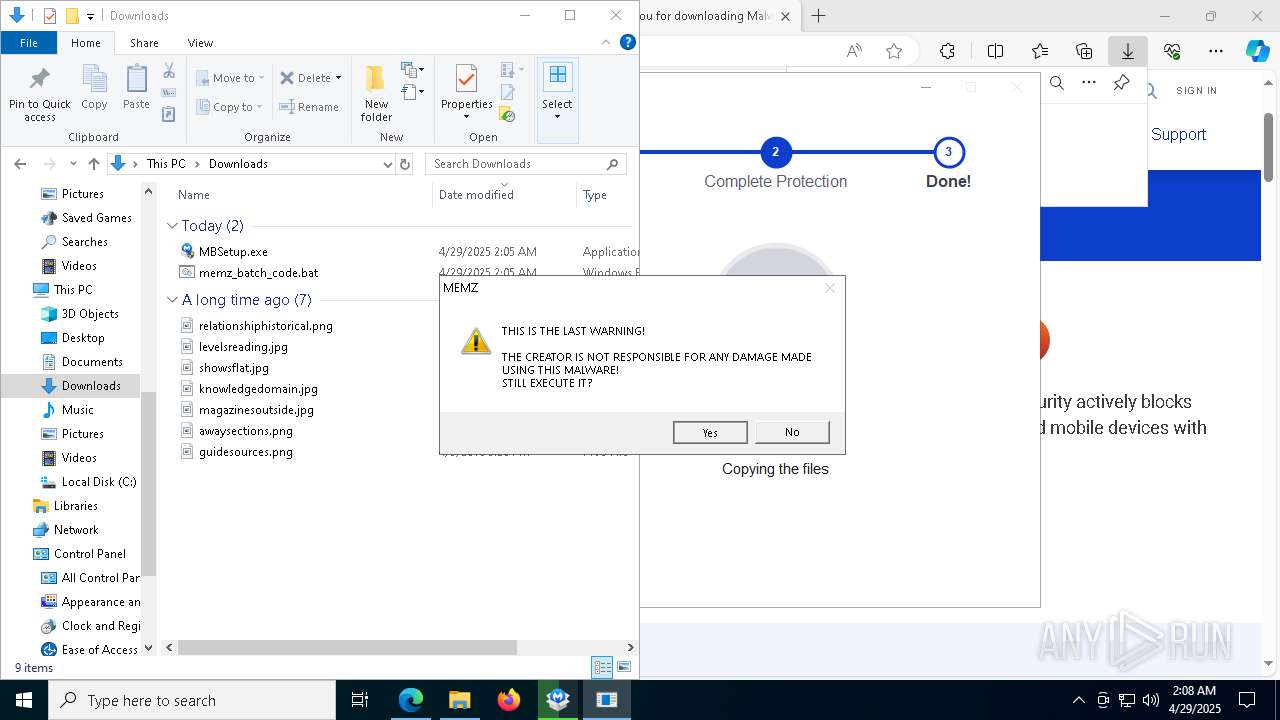
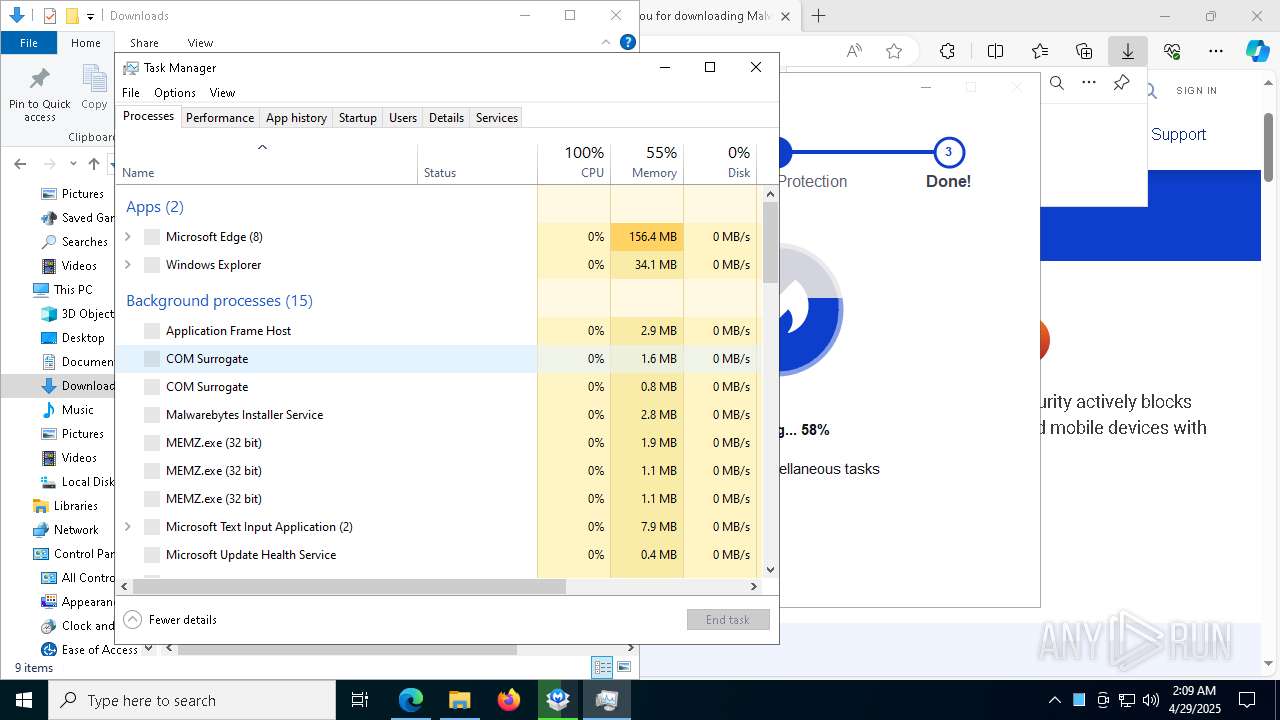
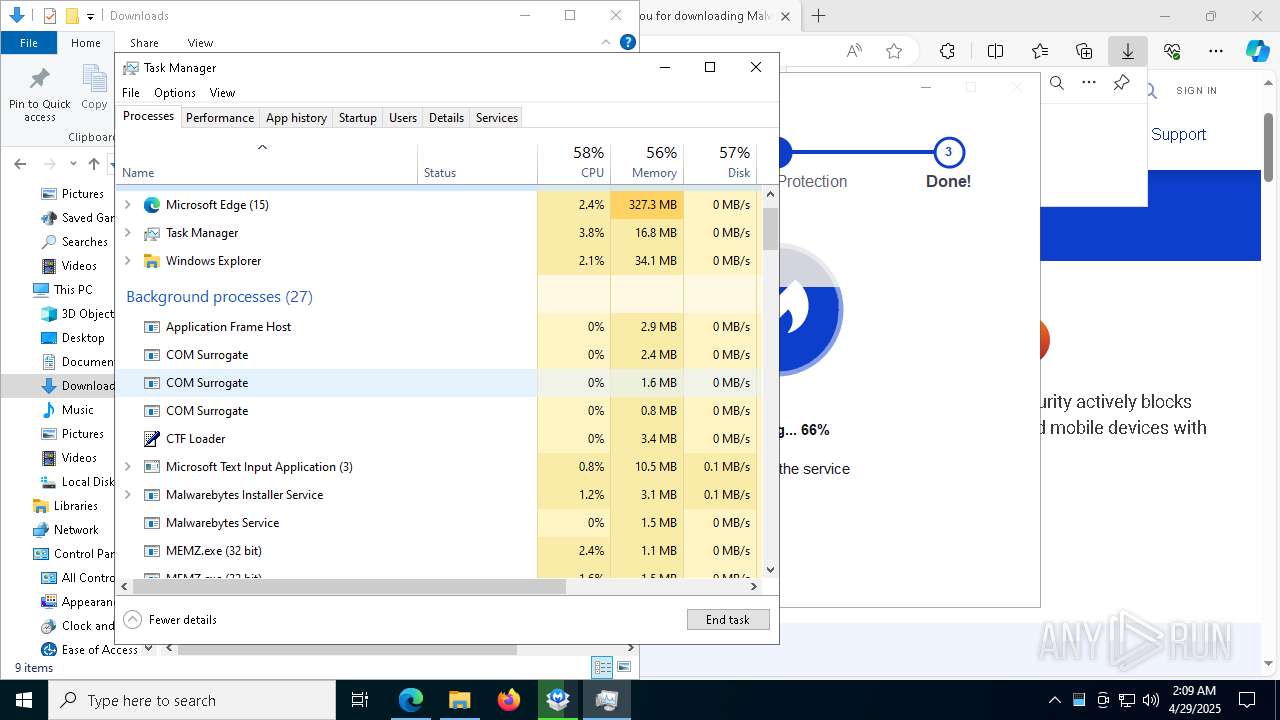
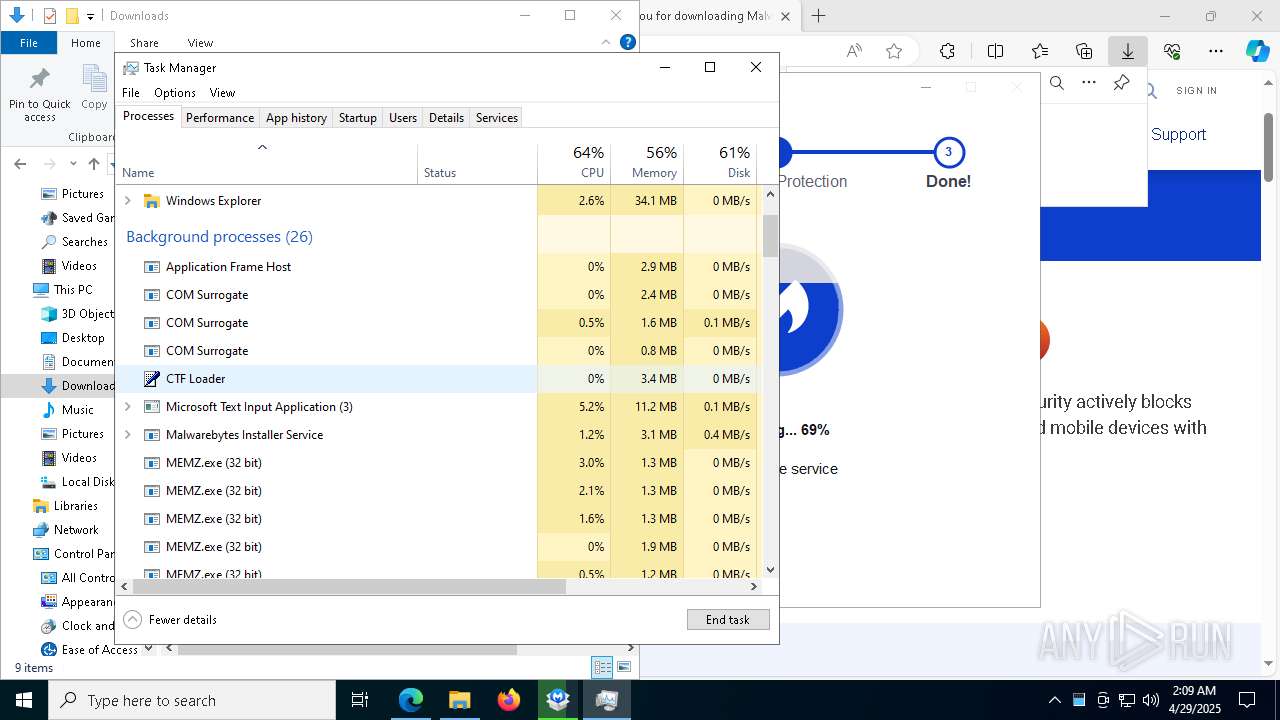
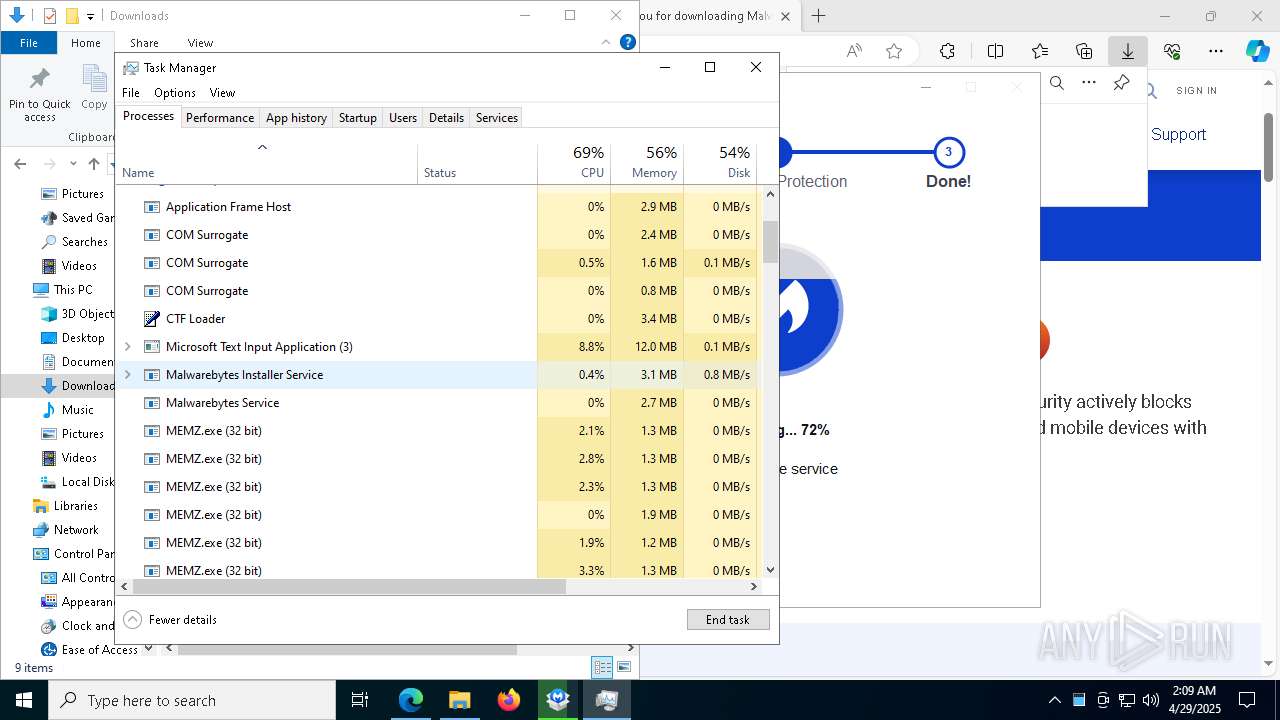
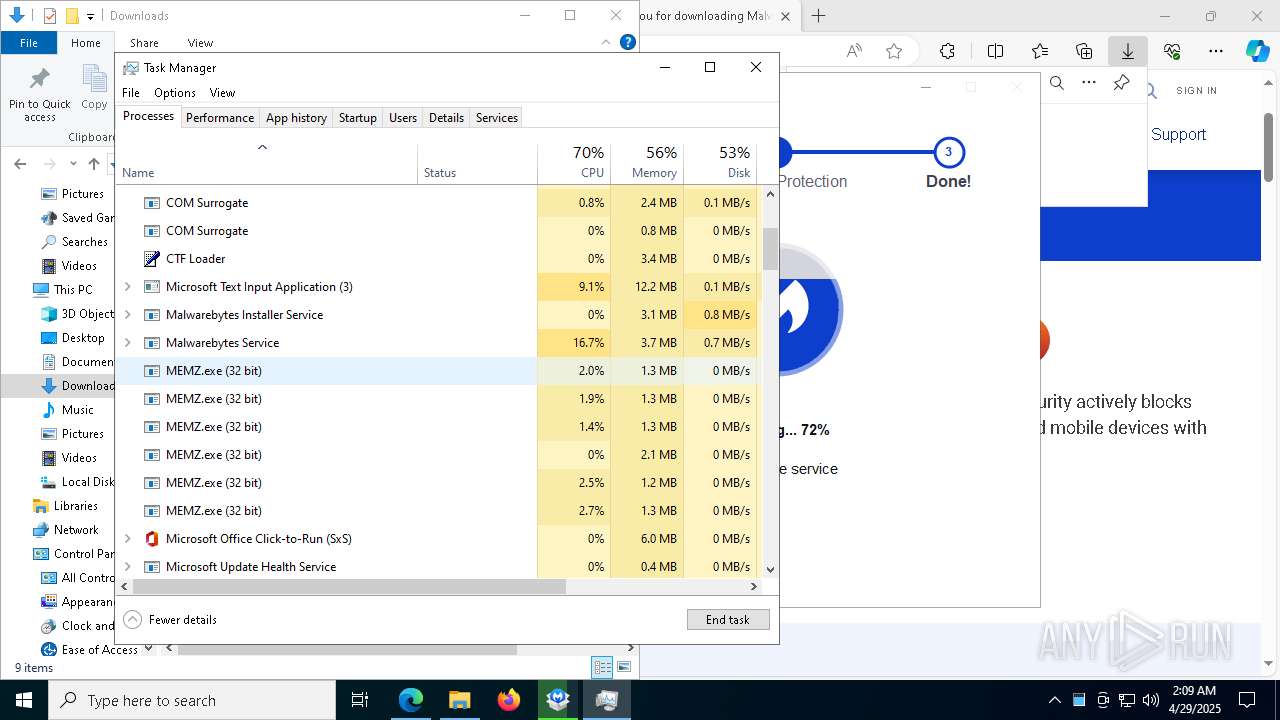
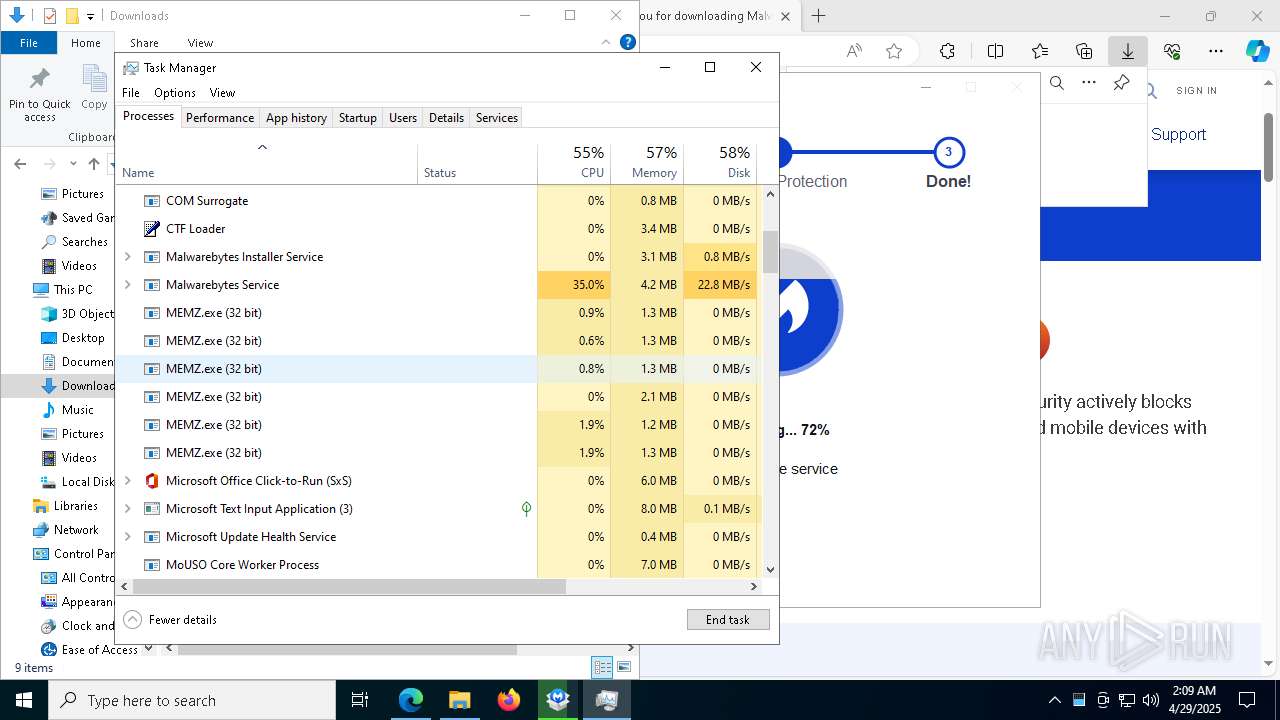
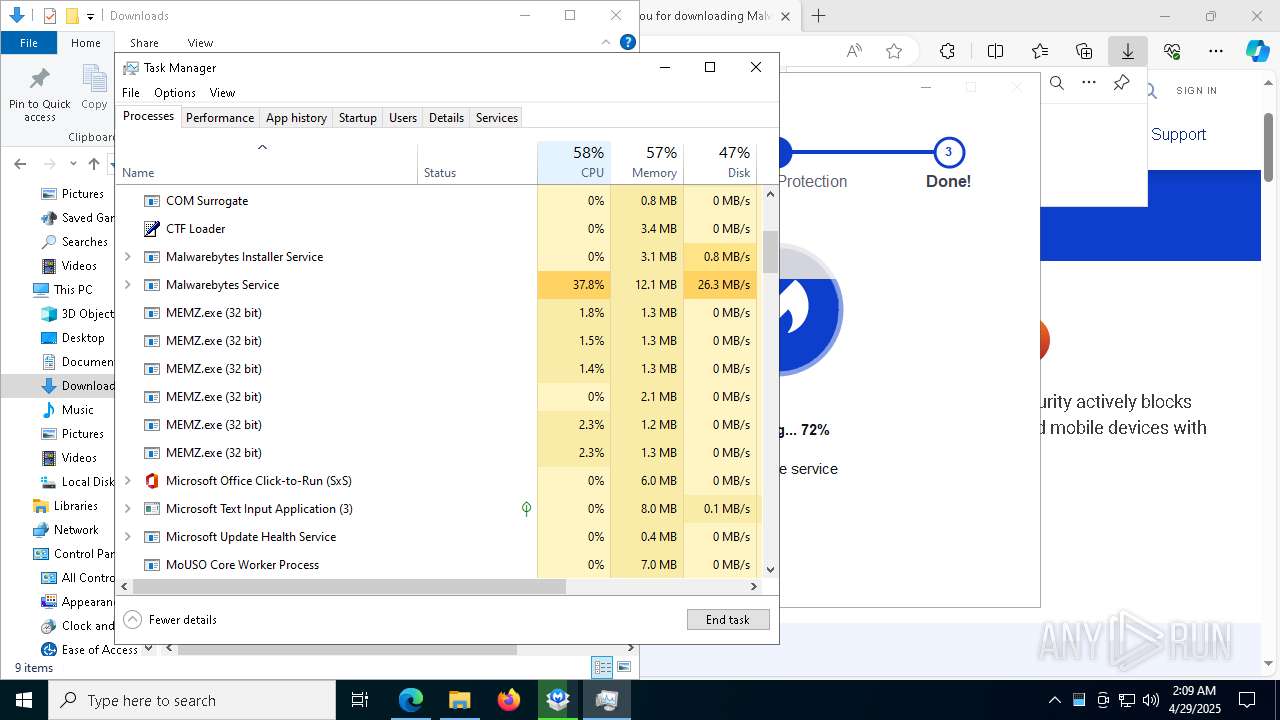
MALICIOUS
MEMZ has been detected (YARA)
- MEMZ.exe (PID: 7000)
- MEMZ.exe (PID: 1004)
- MEMZ.exe (PID: 472)
- MEMZ.exe (PID: 8136)
- MEMZ.exe (PID: 5384)
- MEMZ.exe (PID: 5776)
SUSPICIOUS
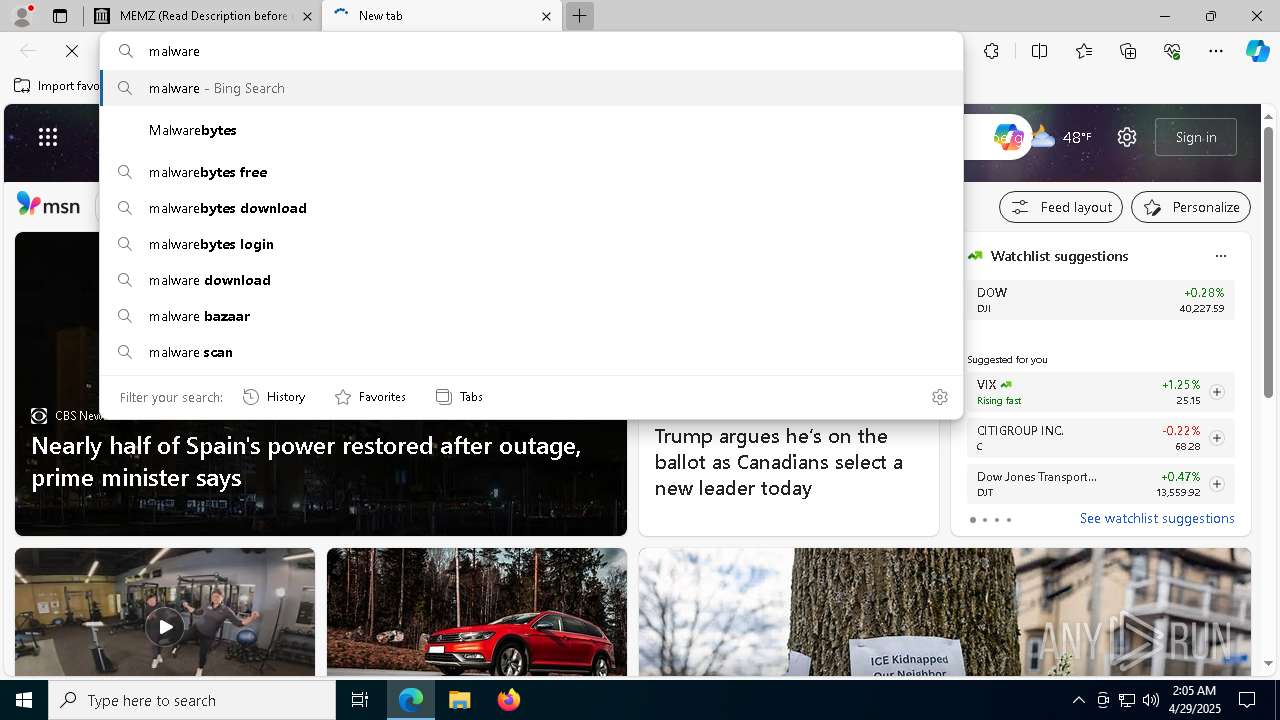
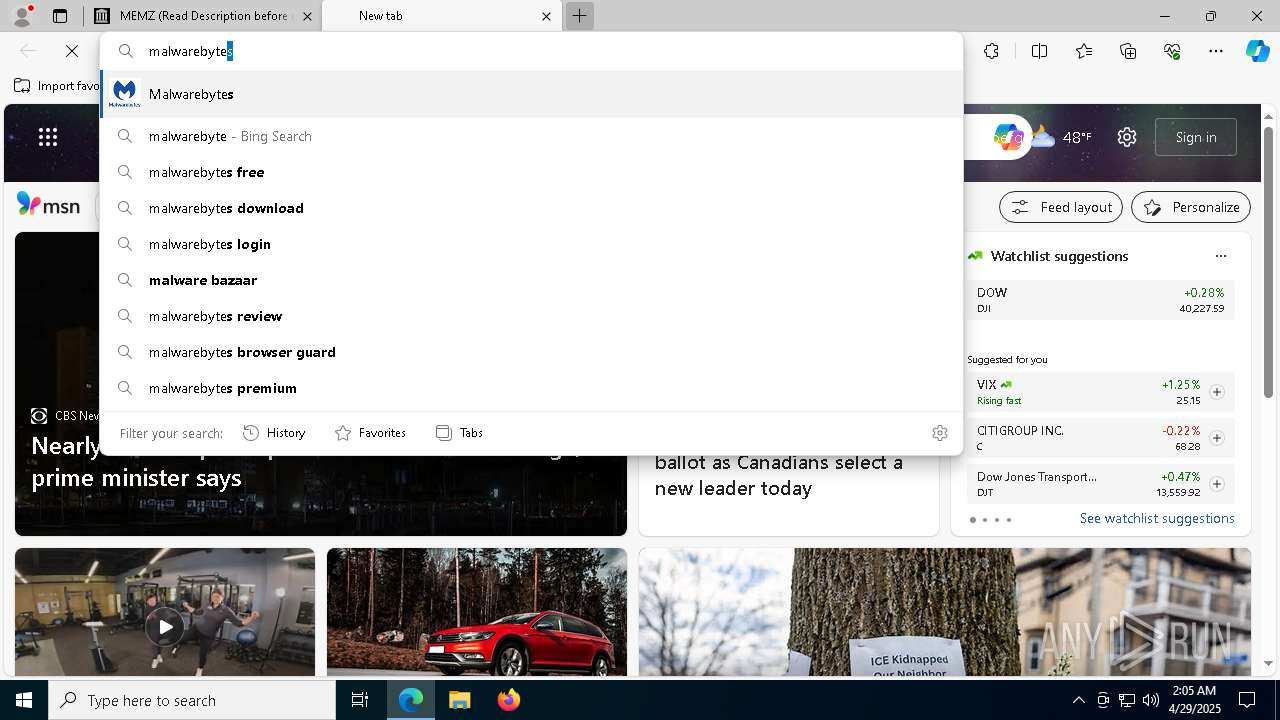
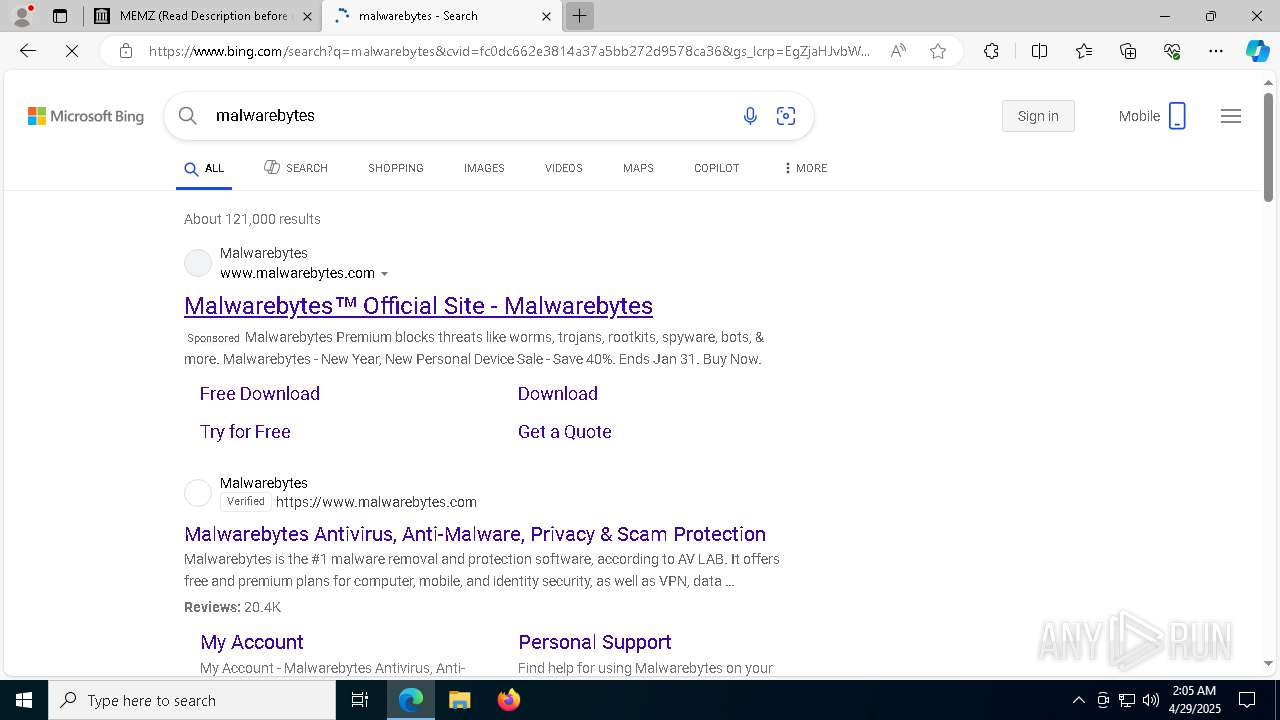
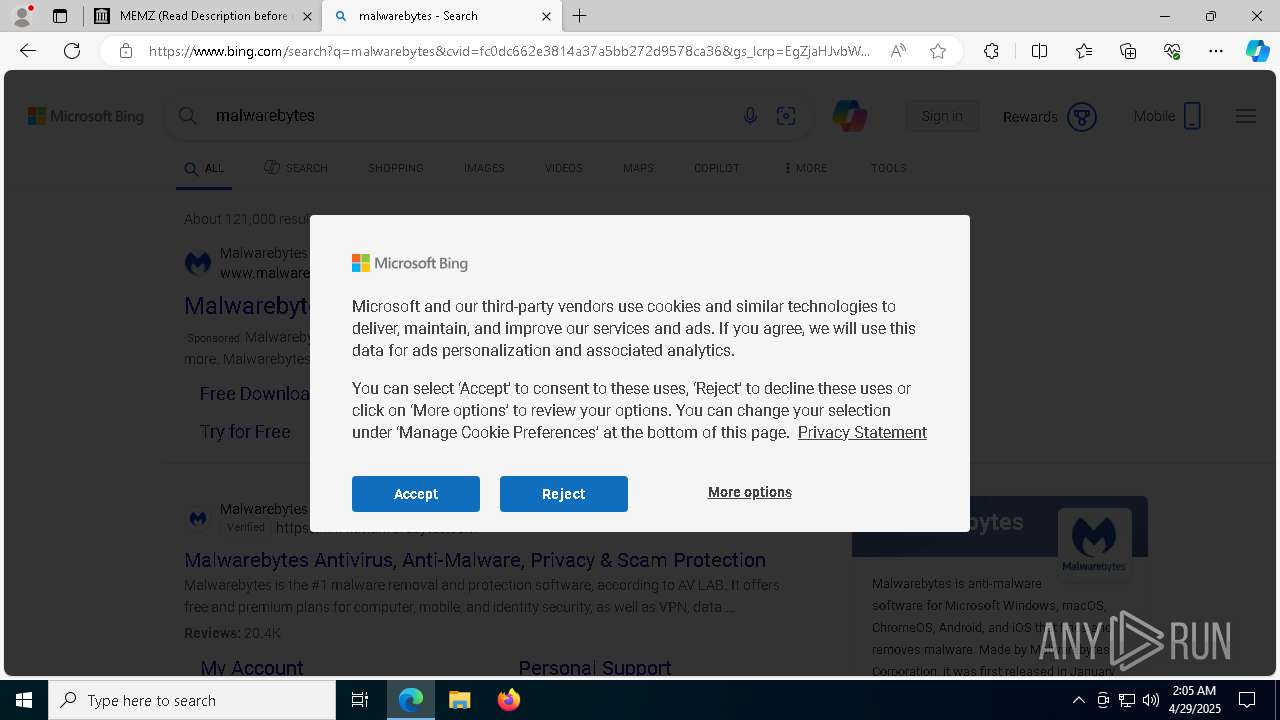
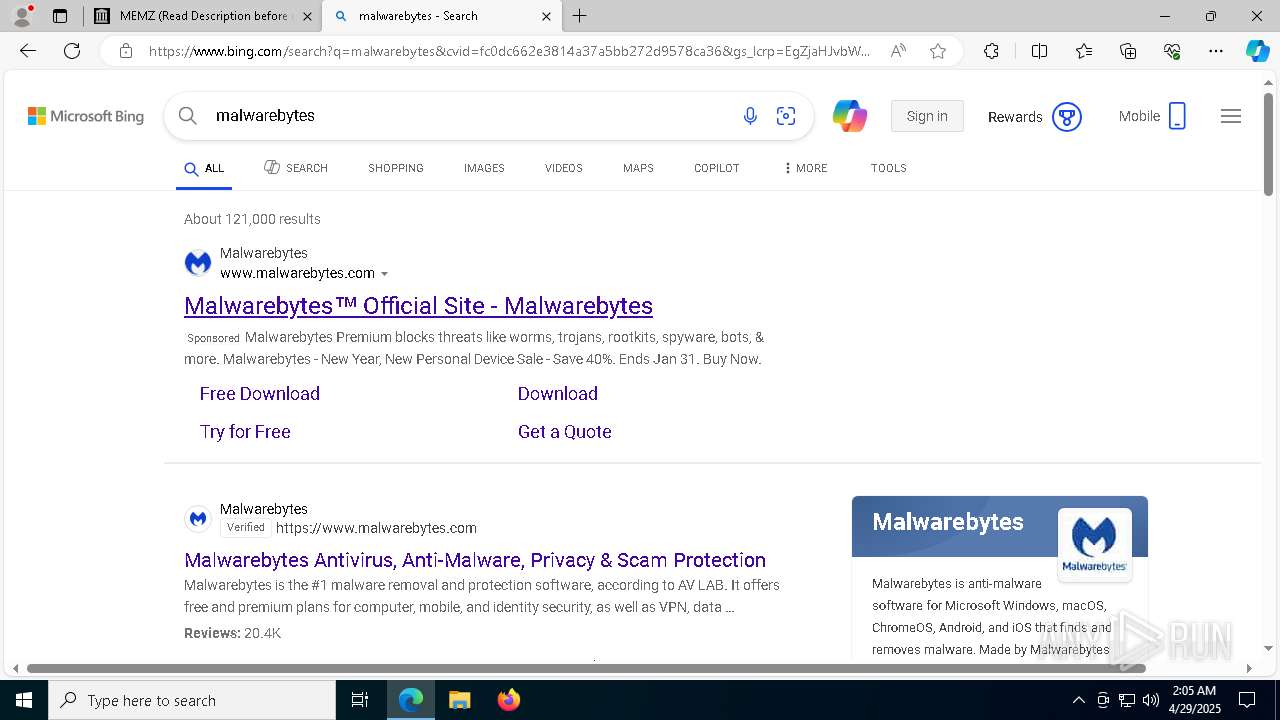
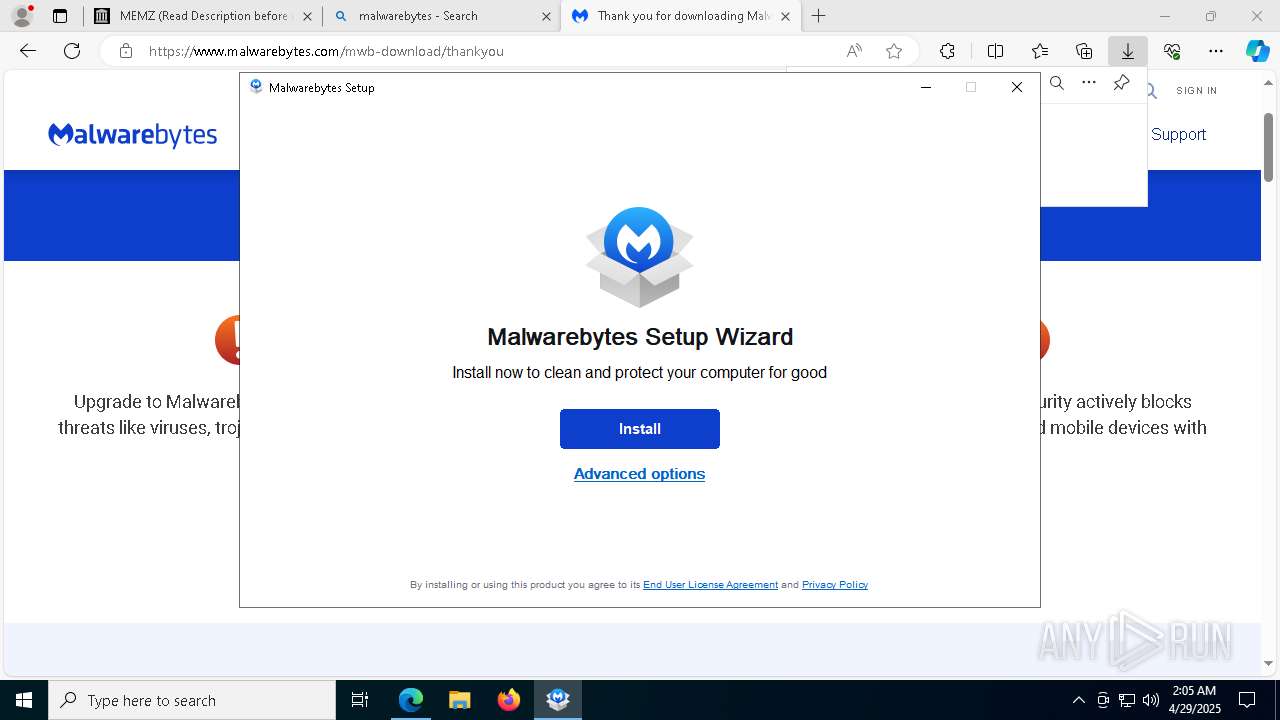
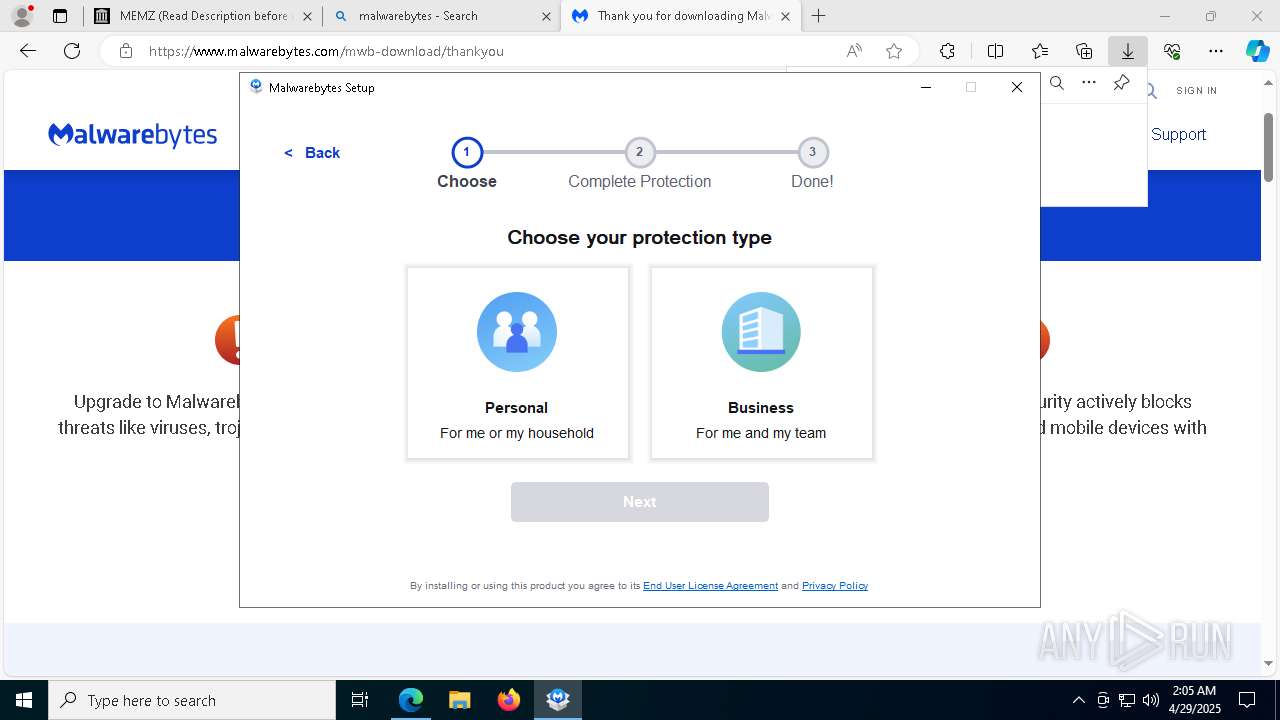
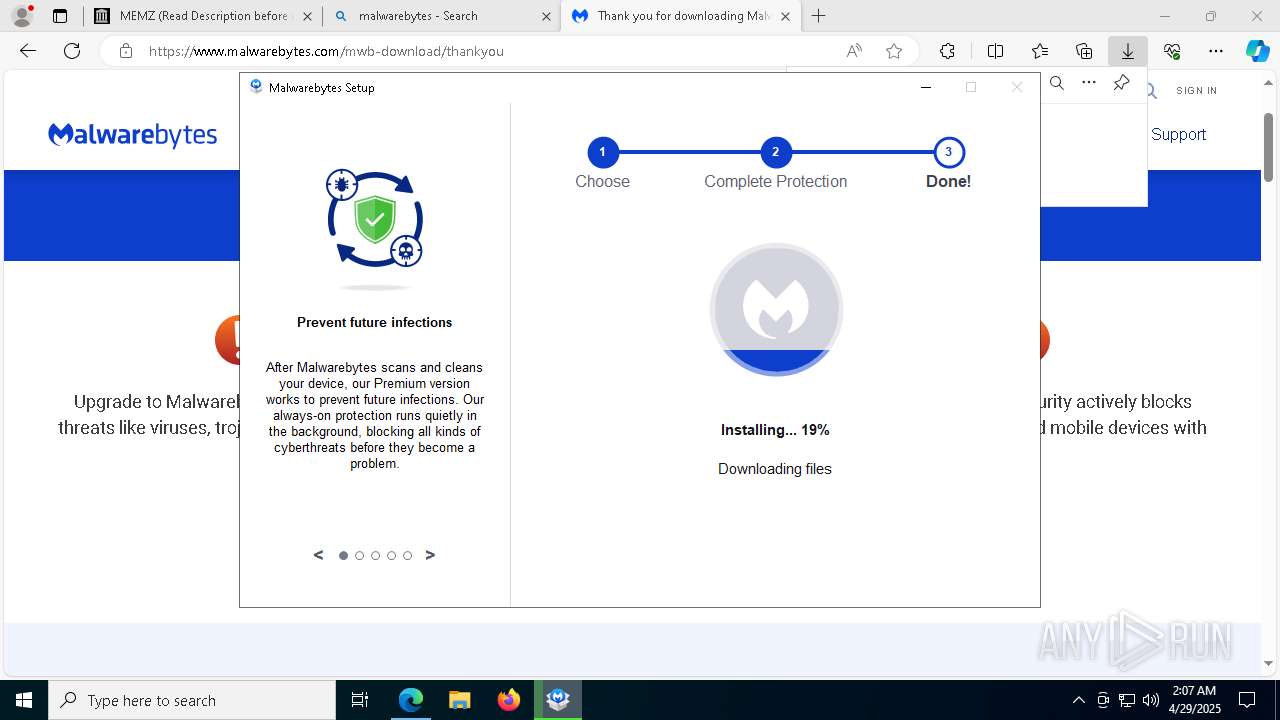
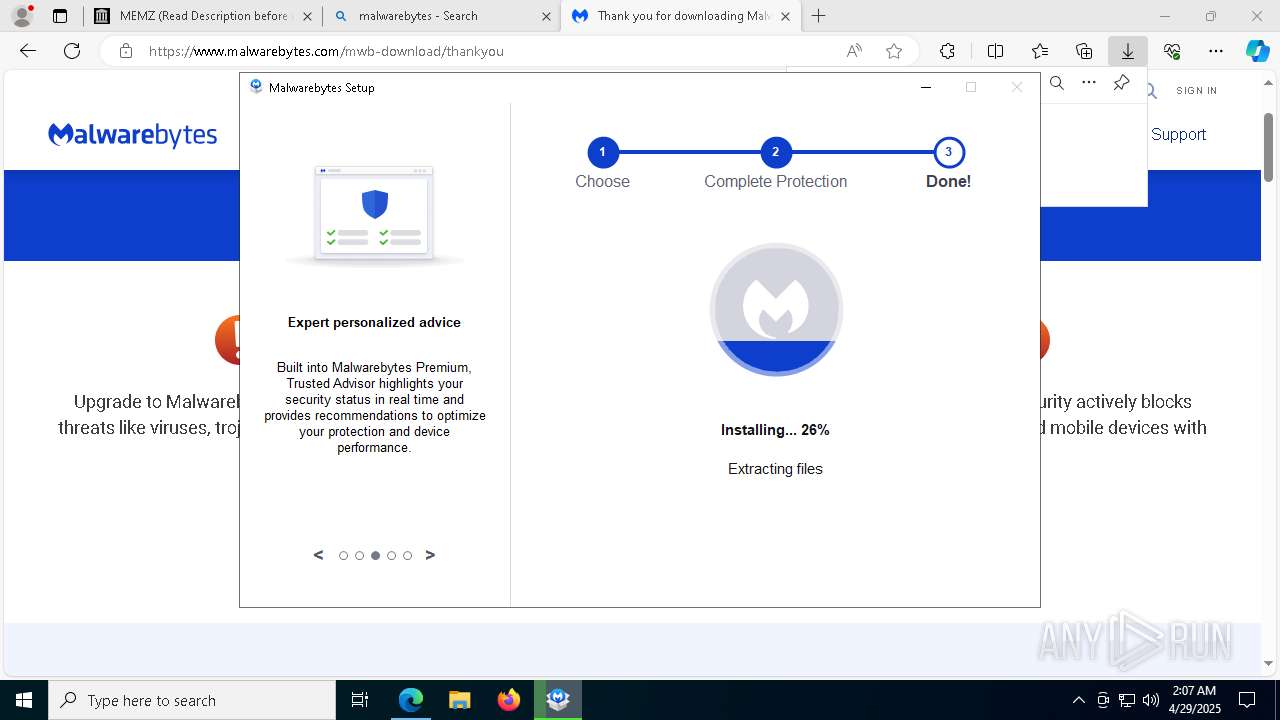
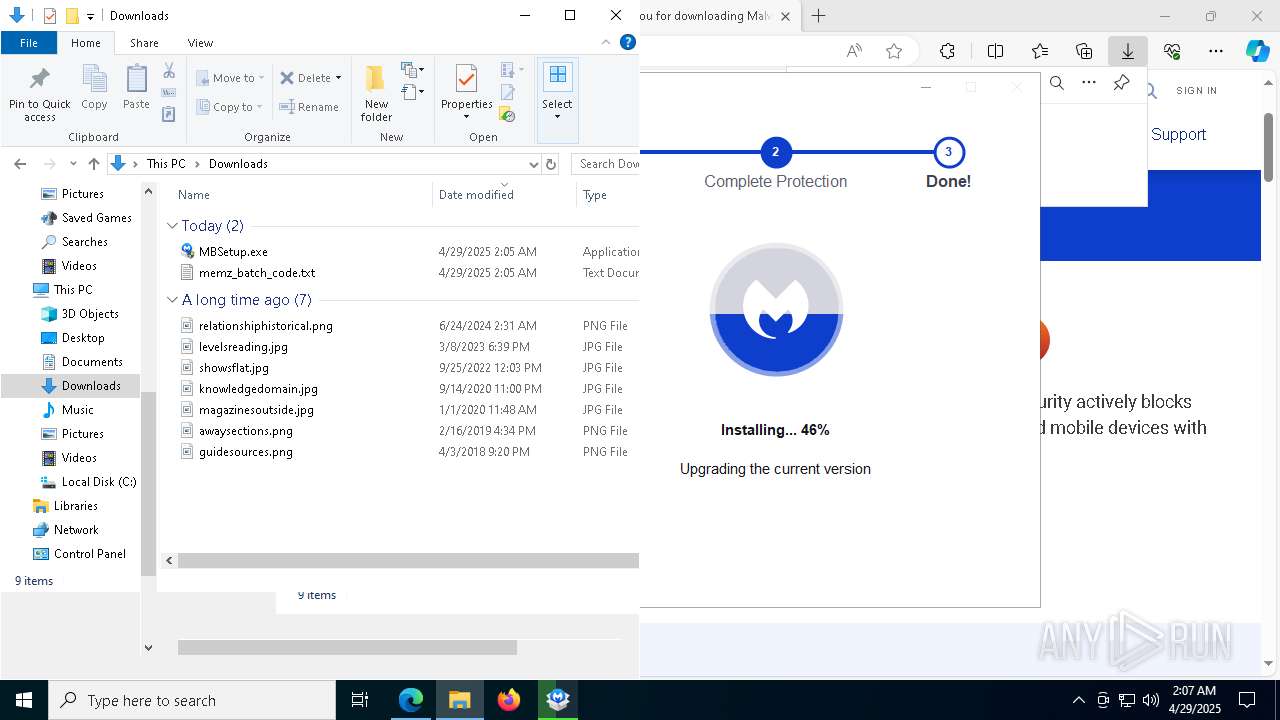
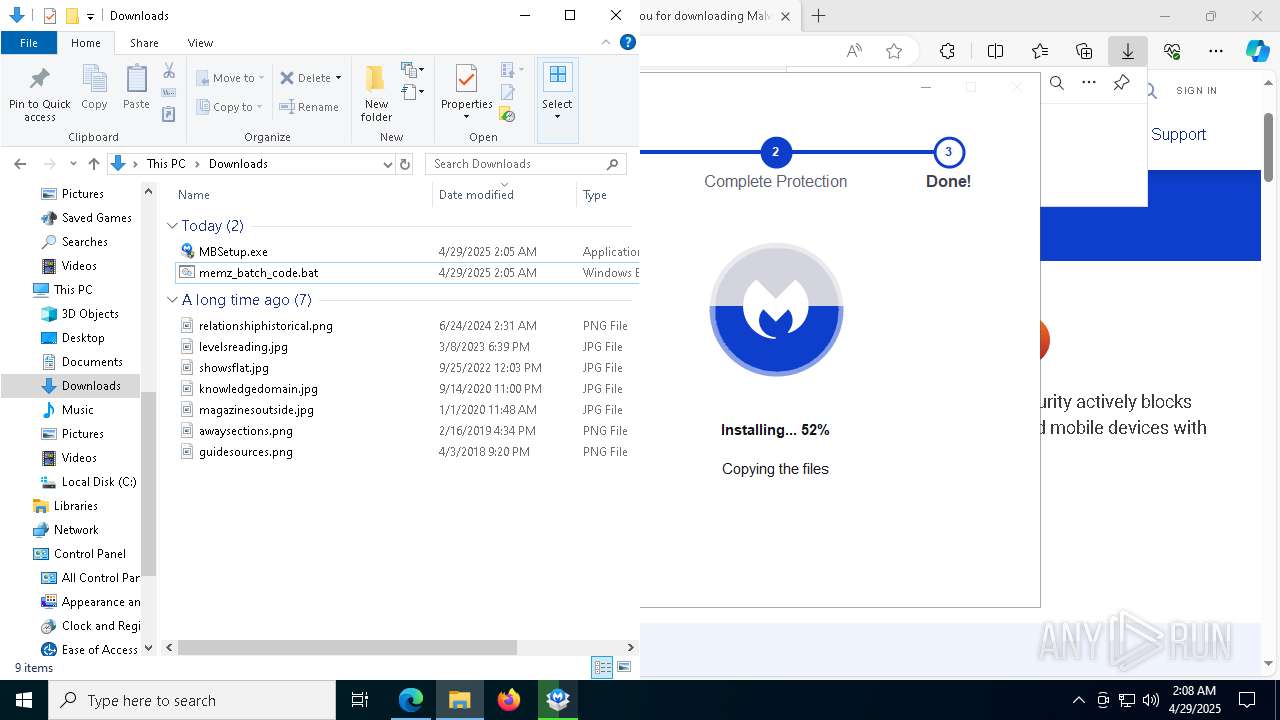
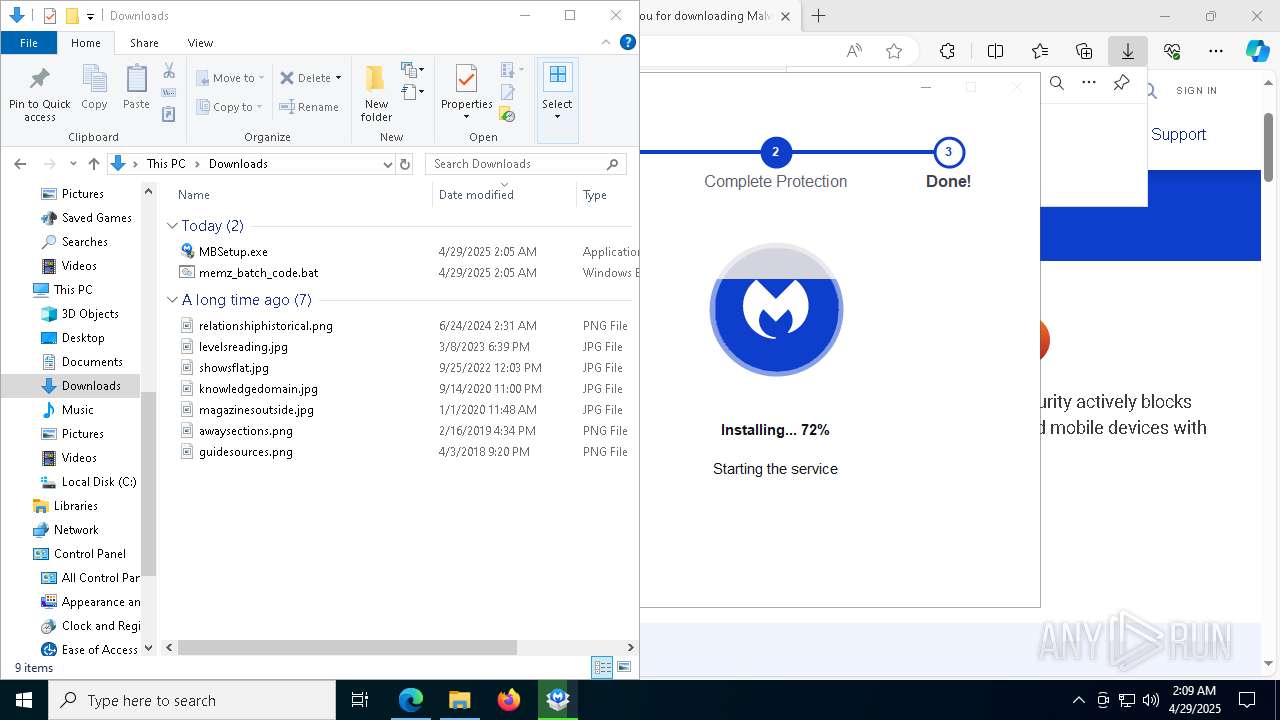
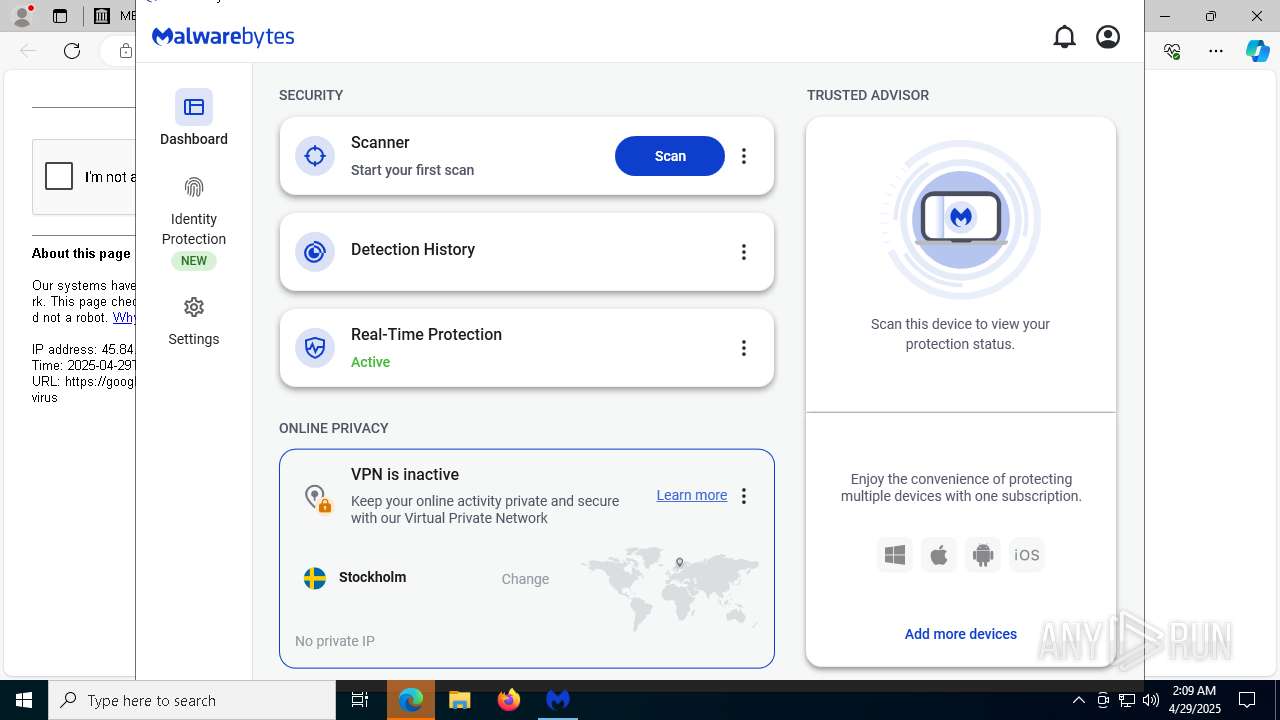
Searches for installed software
- MBSetup.exe (PID: 2096)
- MBAMInstallerService.exe (PID: 4944)
Reads the BIOS version
- MBSetup.exe (PID: 2096)
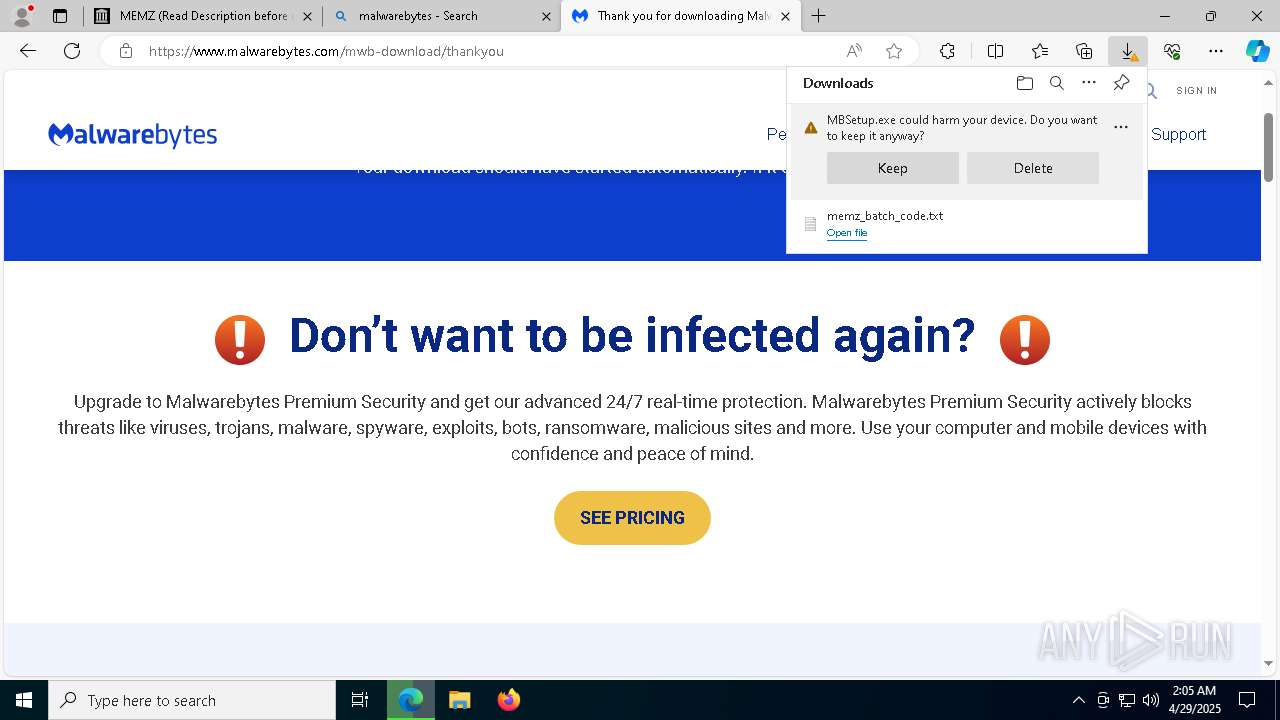
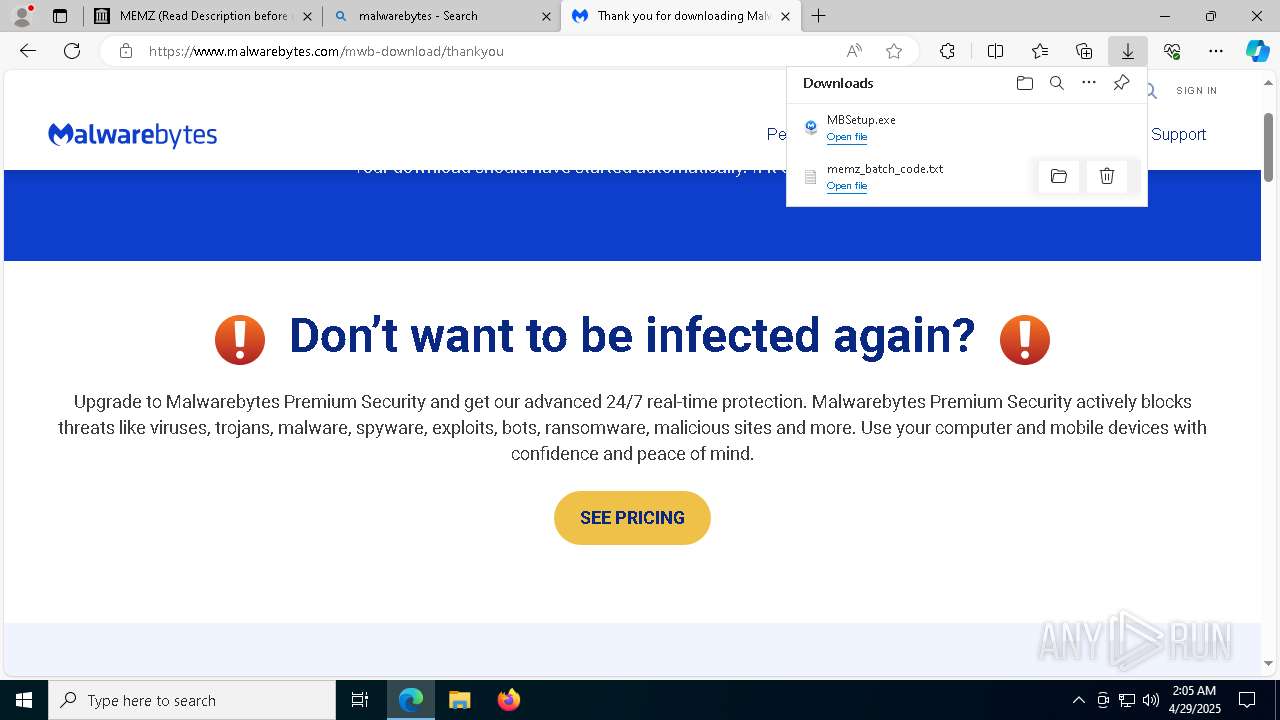
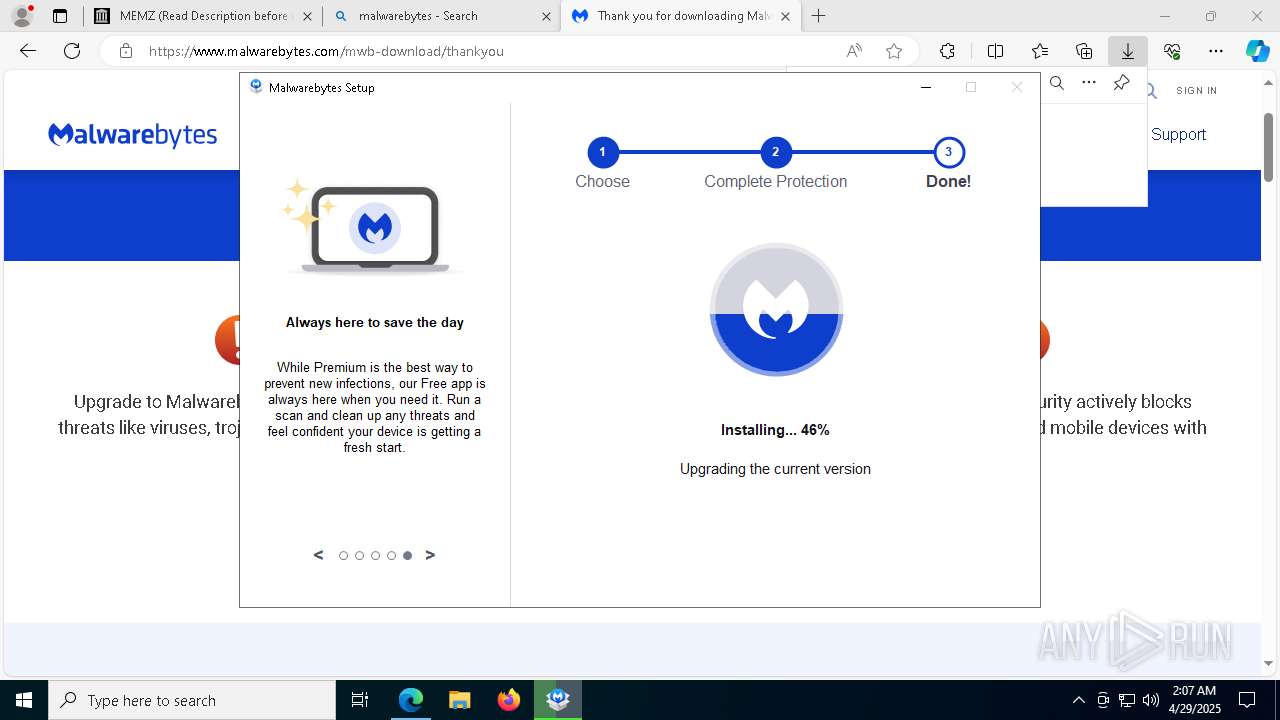
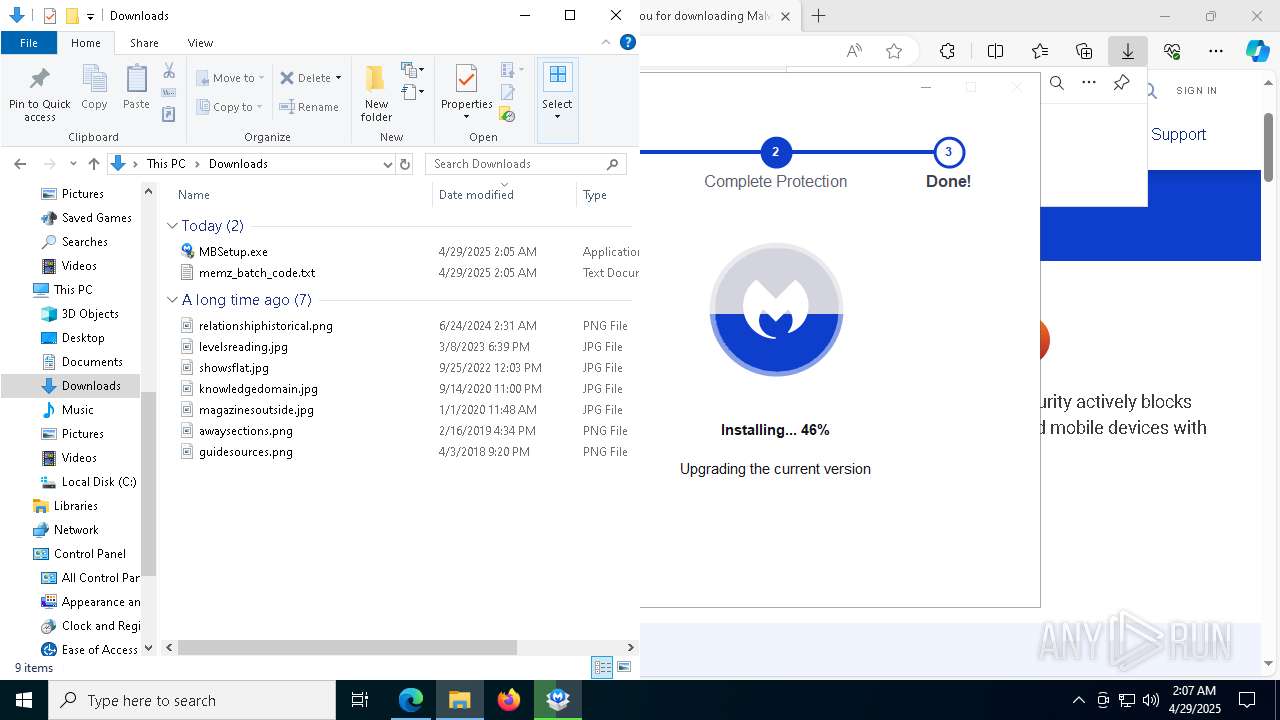
Executable content was dropped or overwritten
- MBSetup.exe (PID: 2096)
- cscript.exe (PID: 5332)
- MBVpnTunnelService.exe (PID: 4980)
- drvinst.exe (PID: 3332)
- MBAMService.exe (PID: 5376)
- MBAMService.exe (PID: 3164)
- MBAMInstallerService.exe (PID: 4944)
The process verifies whether the antivirus software is installed
- MBAMInstallerService.exe (PID: 4944)
- MBSetup.exe (PID: 2096)
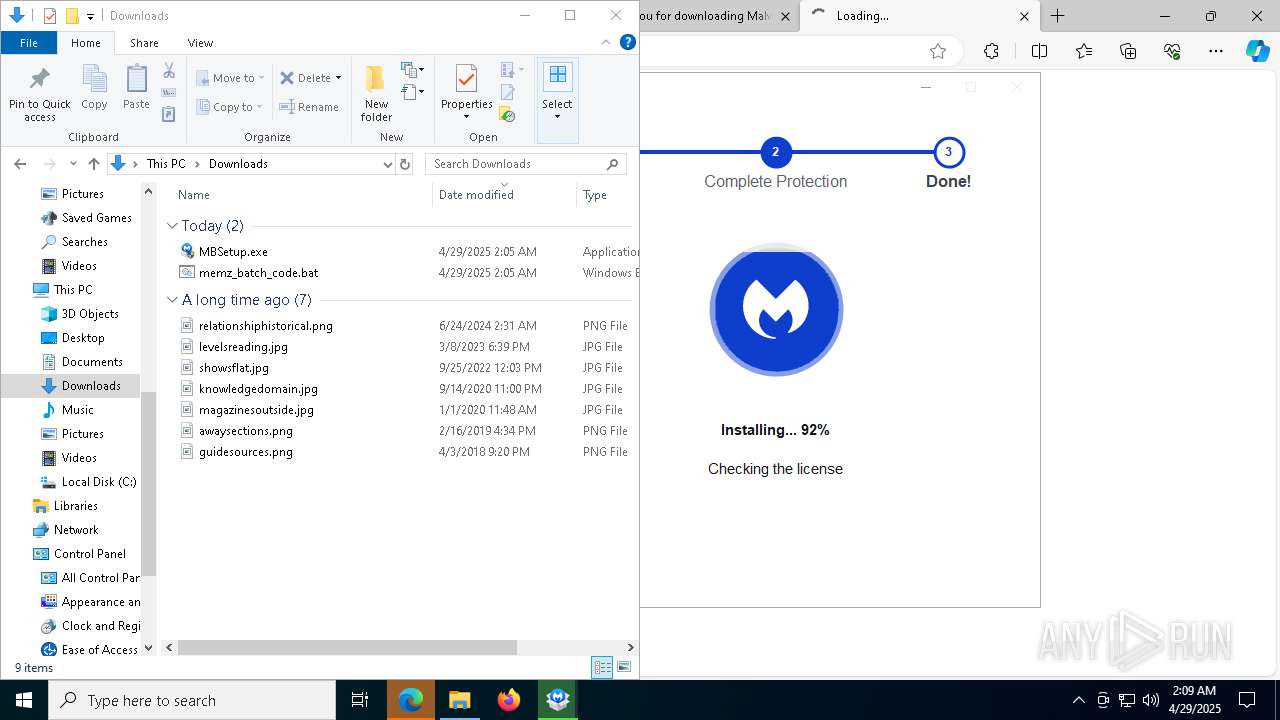
Executes as Windows Service
- MBAMInstallerService.exe (PID: 4944)
- MBAMService.exe (PID: 3164)
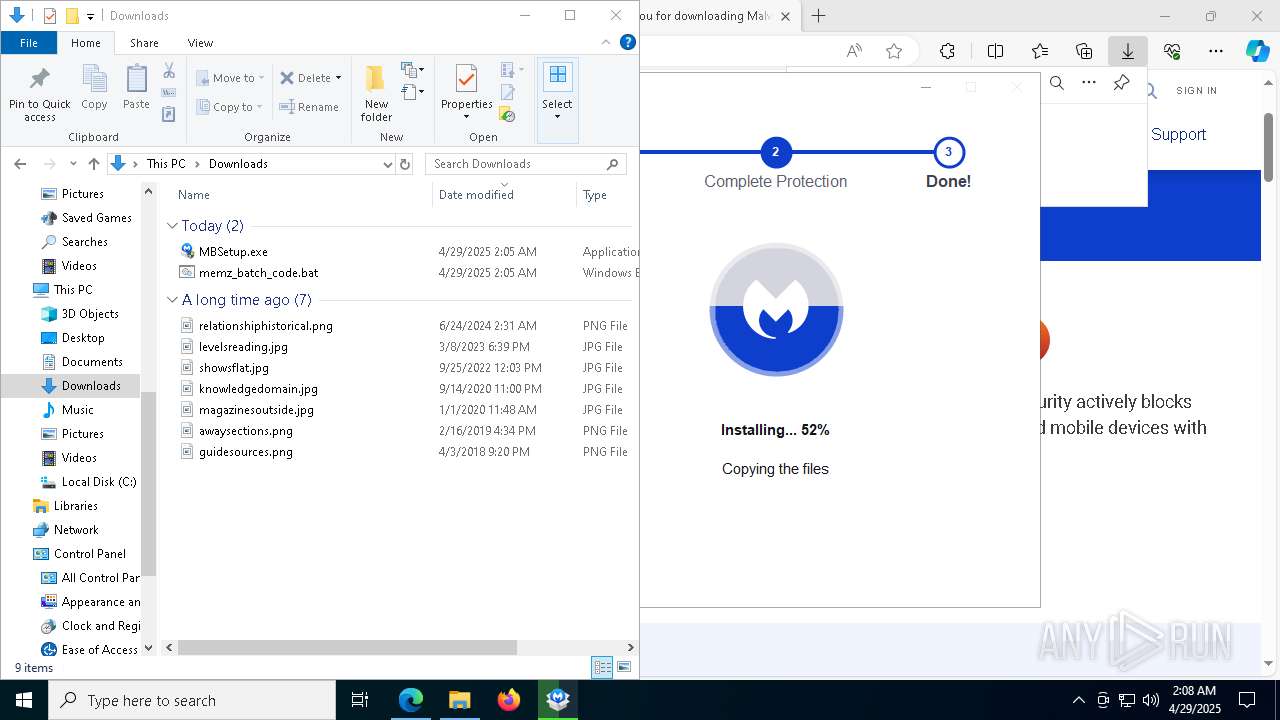
Drops 7-zip archiver for unpacking
- MBAMInstallerService.exe (PID: 4944)
Drops a system driver (possible attempt to evade defenses)
- MBAMInstallerService.exe (PID: 4944)
- MBVpnTunnelService.exe (PID: 4980)
- drvinst.exe (PID: 3332)
- MBAMService.exe (PID: 5376)
- MBAMService.exe (PID: 3164)
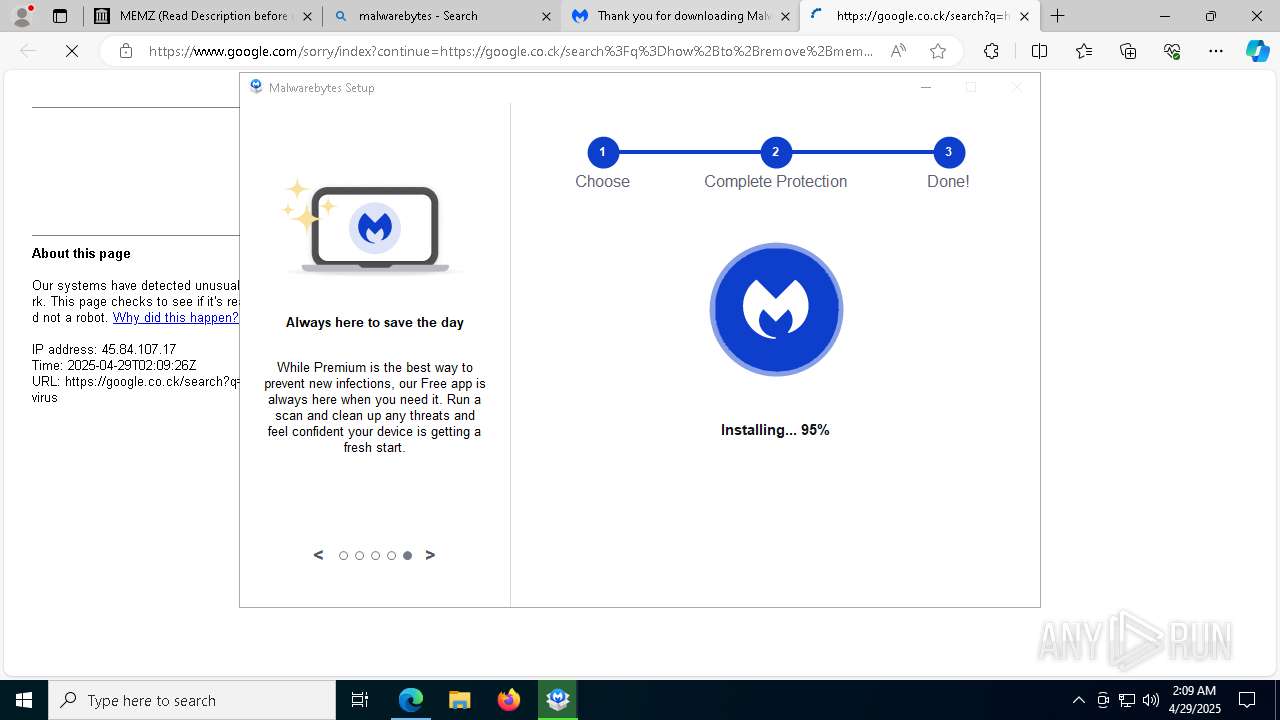
Process drops legitimate windows executable
- MBAMInstallerService.exe (PID: 4944)
- MBAMService.exe (PID: 3164)
The process drops C-runtime libraries
- MBAMInstallerService.exe (PID: 4944)
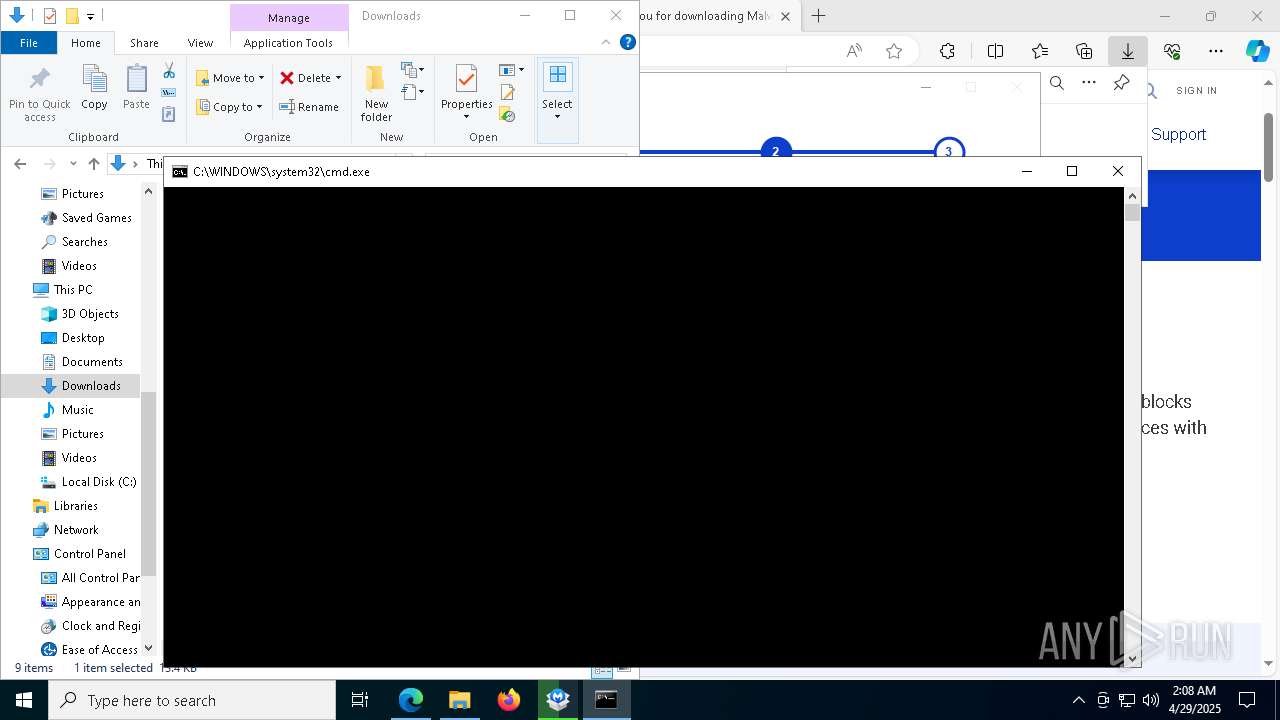
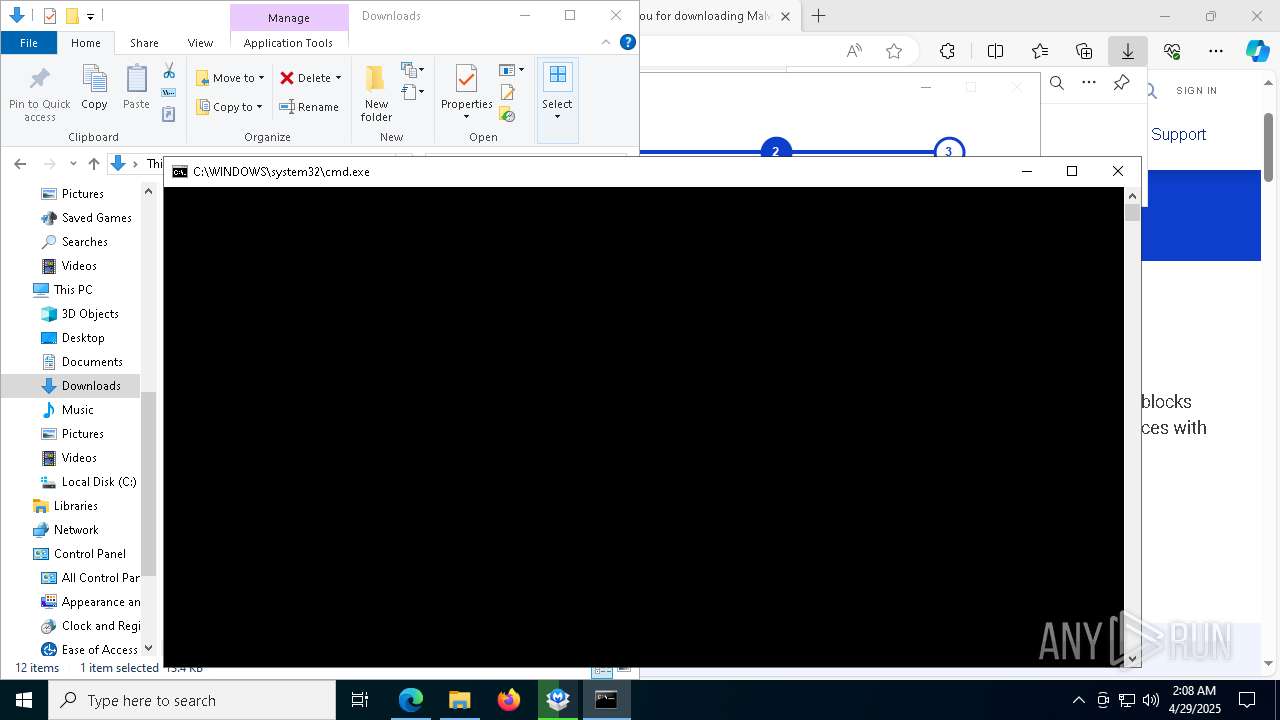
The process executes JS scripts
- cmd.exe (PID: 4448)
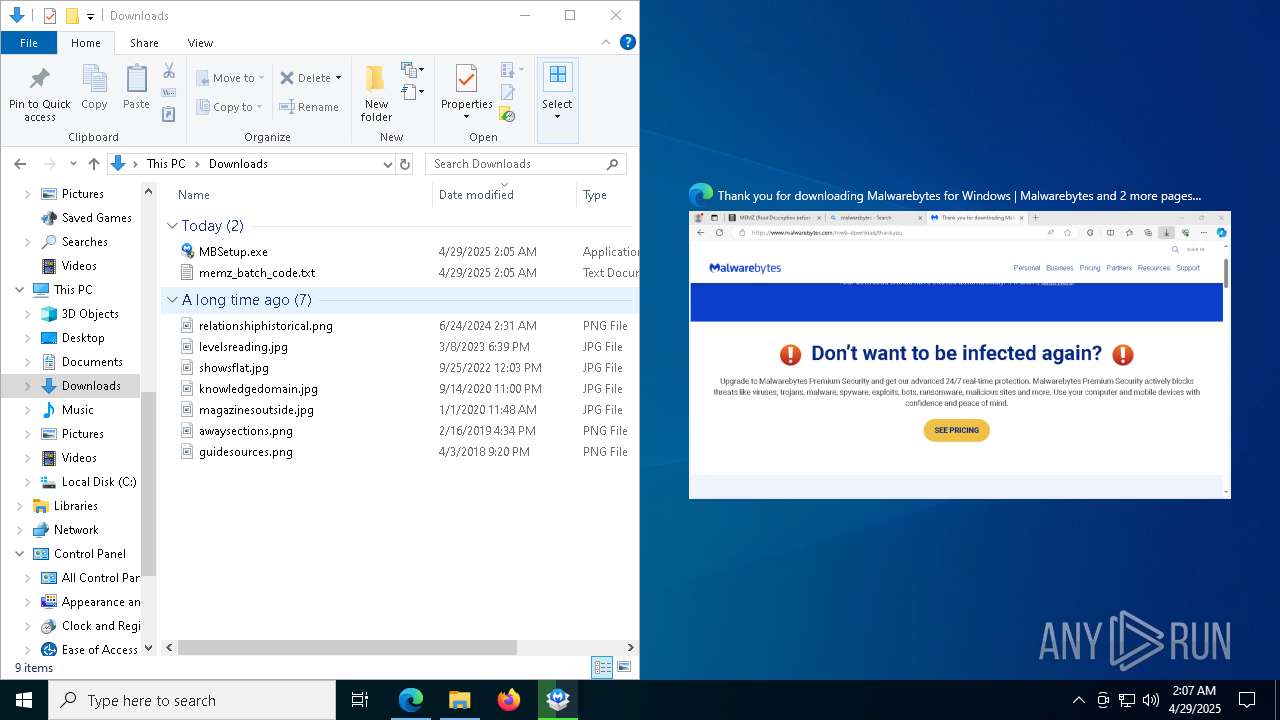
Application launched itself
- MEMZ.exe (PID: 3024)
- Malwarebytes.exe (PID: 9072)
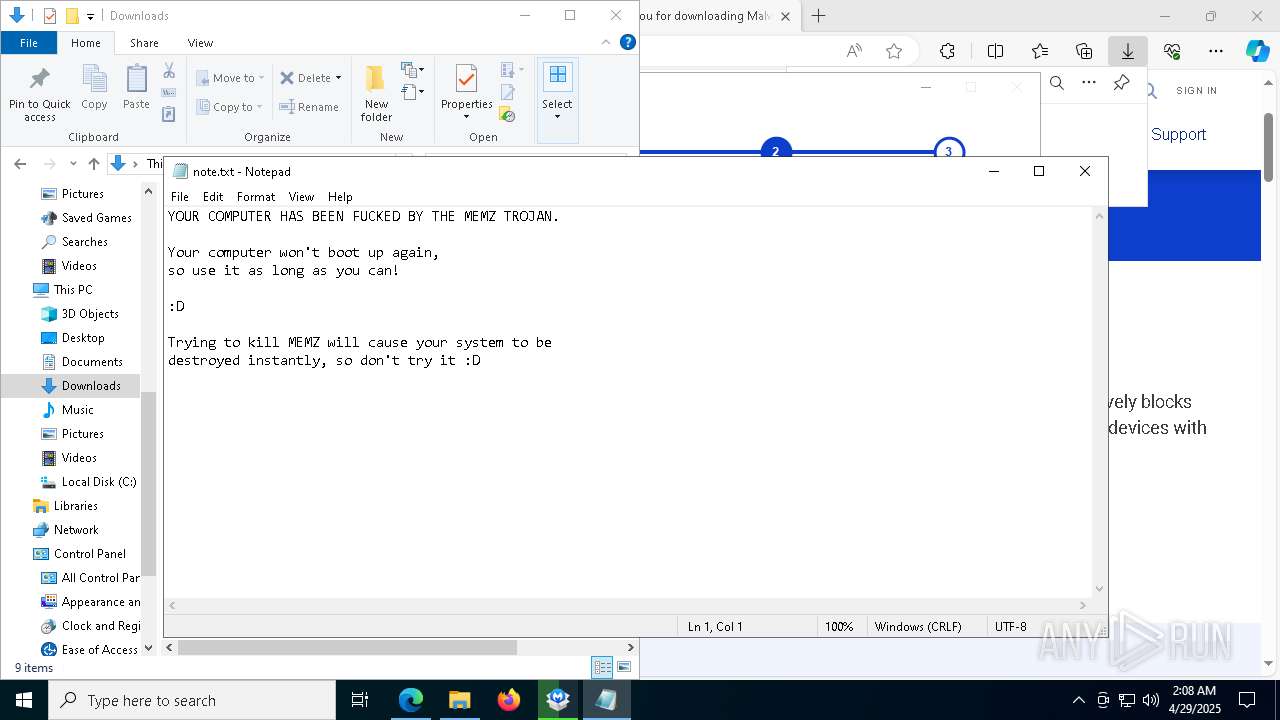
Start notepad (likely ransomware note)
- MEMZ.exe (PID: 5776)
There is functionality for taking screenshot (YARA)
- MEMZ.exe (PID: 7000)
- MEMZ.exe (PID: 1004)
- MEMZ.exe (PID: 472)
- MEMZ.exe (PID: 8136)
- MEMZ.exe (PID: 5384)
- MEMZ.exe (PID: 5776)
Creates files in the driver directory
- MBSetup.exe (PID: 2096)
INFO
Application launched itself
- msedge.exe (PID: 7216)
Checks supported languages
- identity_helper.exe (PID: 1244)
- MBAMInstallerService.exe (PID: 4944)
- MBSetup.exe (PID: 2096)
Reads Environment values
- identity_helper.exe (PID: 1244)
Reads the computer name
- identity_helper.exe (PID: 1244)
- MBSetup.exe (PID: 2096)
- MBAMInstallerService.exe (PID: 4944)
The sample compiled with english language support
- msedge.exe (PID: 7532)
- MBSetup.exe (PID: 2096)
- MBAMInstallerService.exe (PID: 4944)
- msedge.exe (PID: 924)
- MBVpnTunnelService.exe (PID: 4980)
- MBAMService.exe (PID: 5376)
- drvinst.exe (PID: 3332)
- msedge.exe (PID: 7216)
- MBAMService.exe (PID: 3164)
Executable content was dropped or overwritten
- msedge.exe (PID: 7216)
- msedge.exe (PID: 924)
- msedge.exe (PID: 7532)
Reads the machine GUID from the registry
- MBSetup.exe (PID: 2096)
Reads the software policy settings
- MBSetup.exe (PID: 2096)
- slui.exe (PID: 1132)
- MBAMInstallerService.exe (PID: 4944)
Checks proxy server information
- MBSetup.exe (PID: 2096)
Creates files in the program directory
- MBSetup.exe (PID: 2096)
- MBAMInstallerService.exe (PID: 4944)
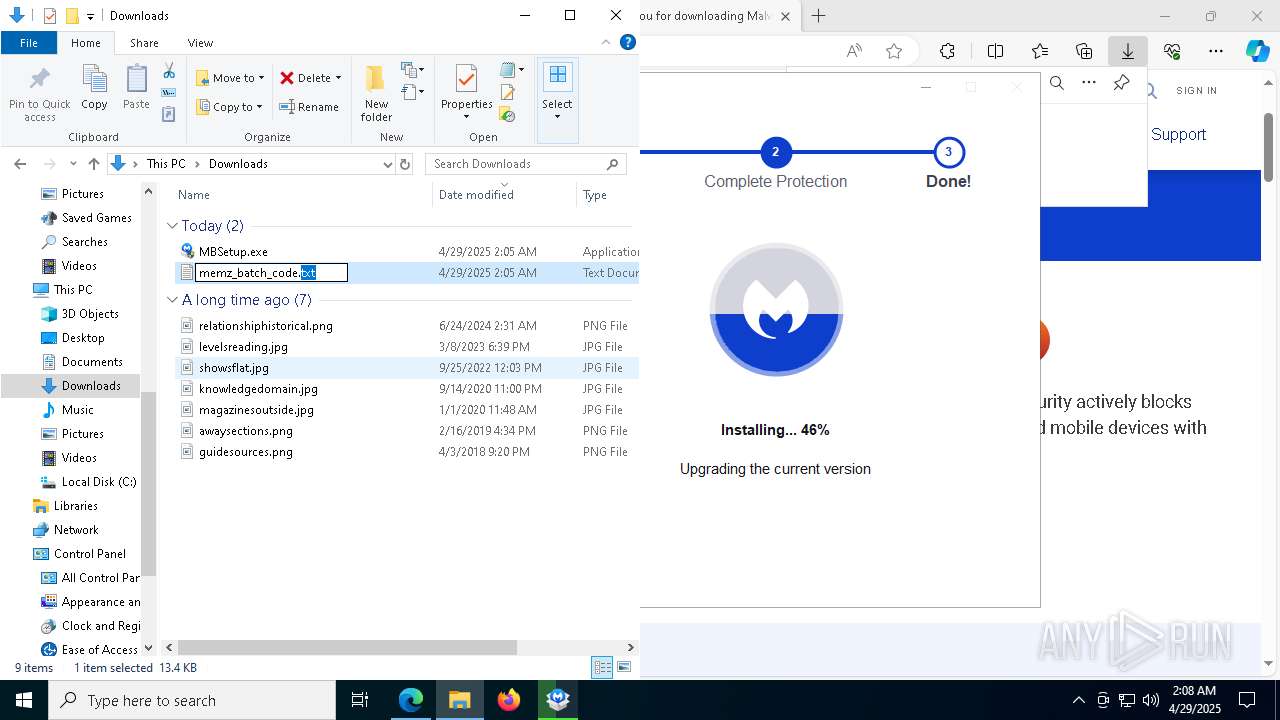
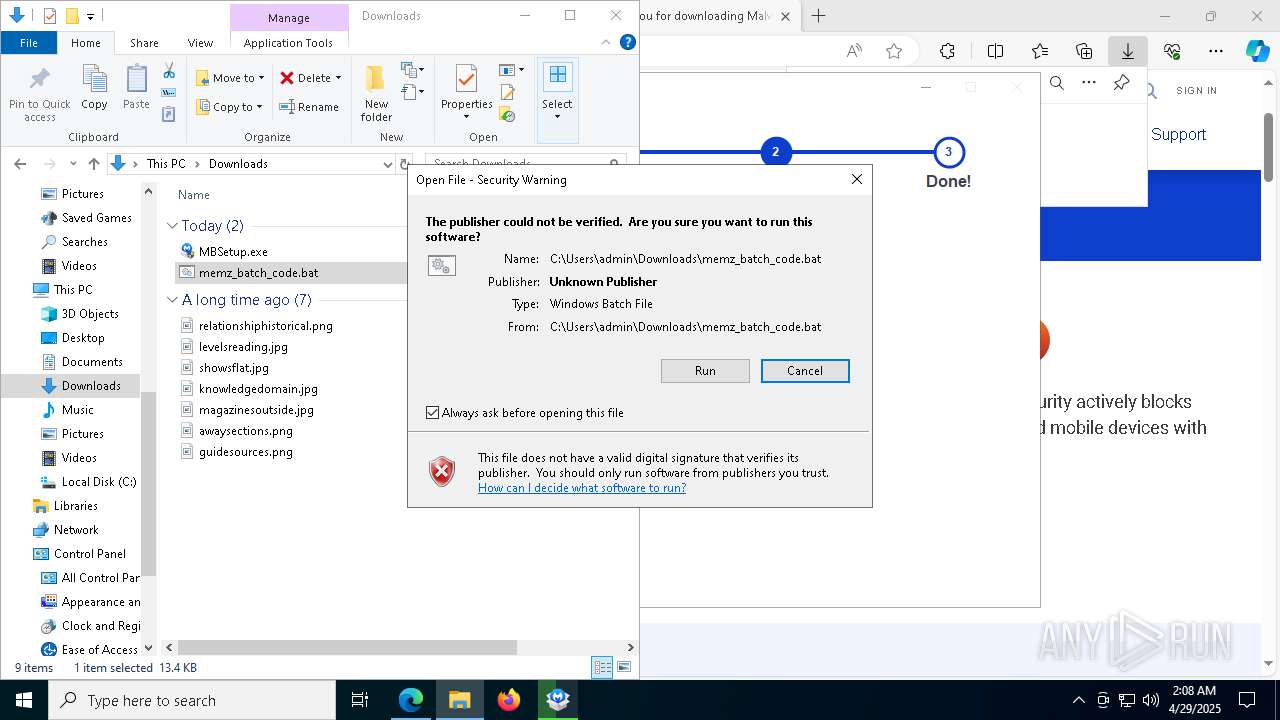
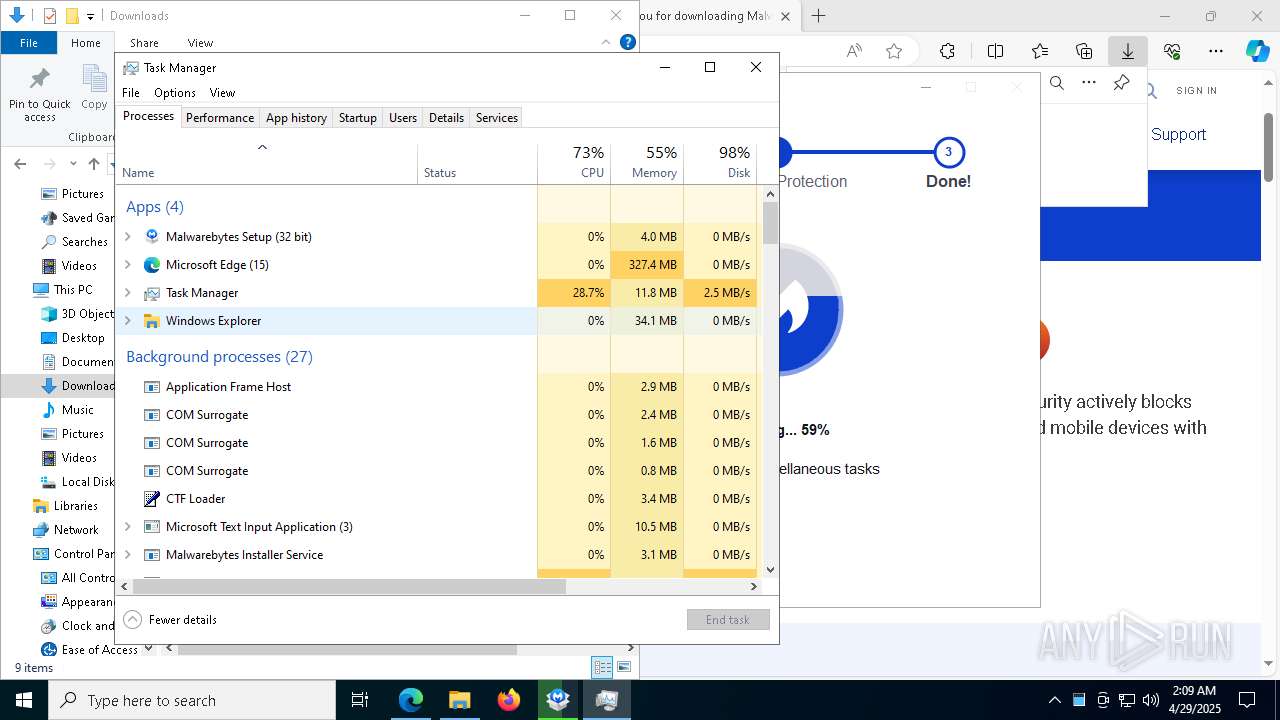
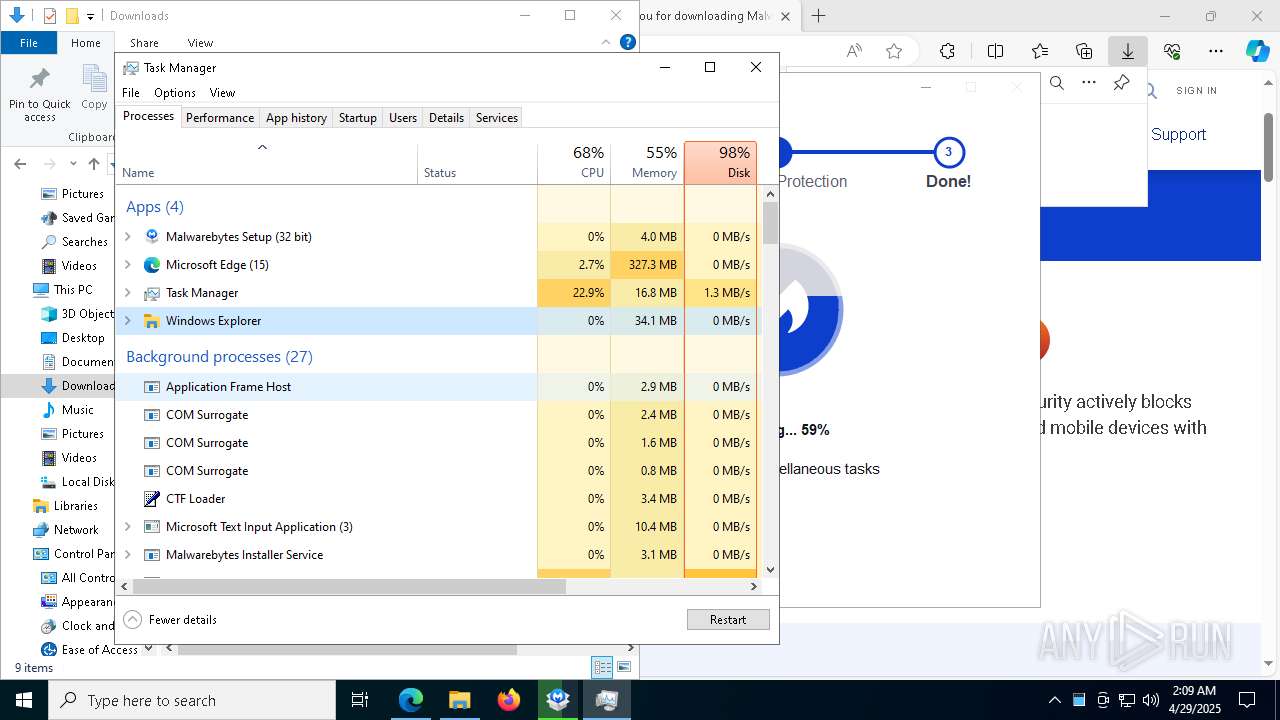
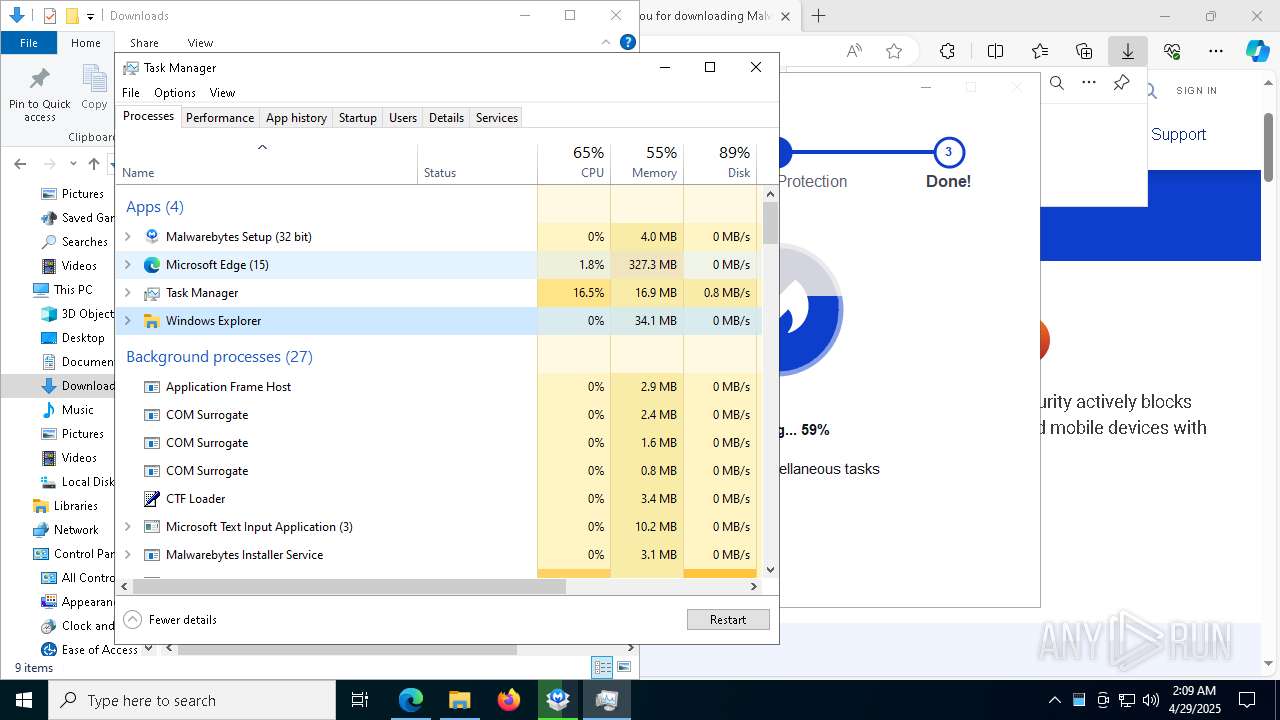
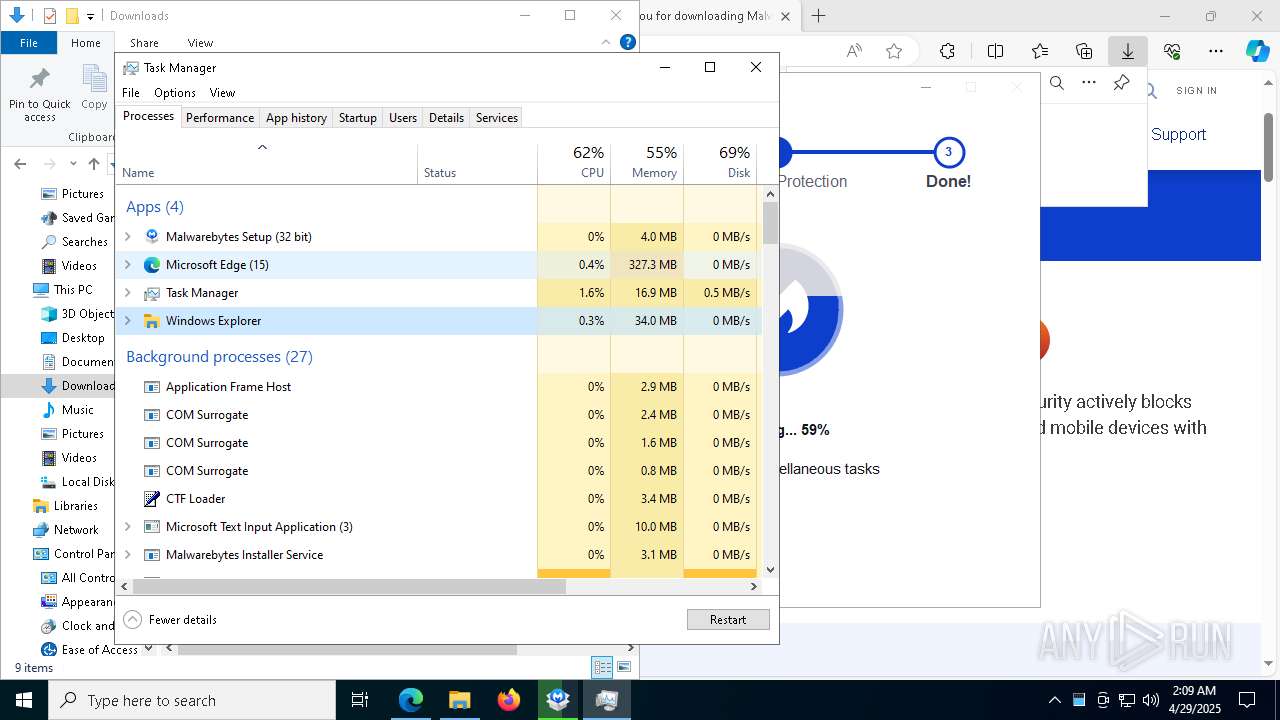
Manual execution by a user
- cmd.exe (PID: 4448)
- Taskmgr.exe (PID: 1704)
- Taskmgr.exe (PID: 8160)
- Malwarebytes.exe (PID: 9072)
The sample compiled with spanish language support
- MBAMInstallerService.exe (PID: 4944)
Create files in a temporary directory
- MBSetup.exe (PID: 2096)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
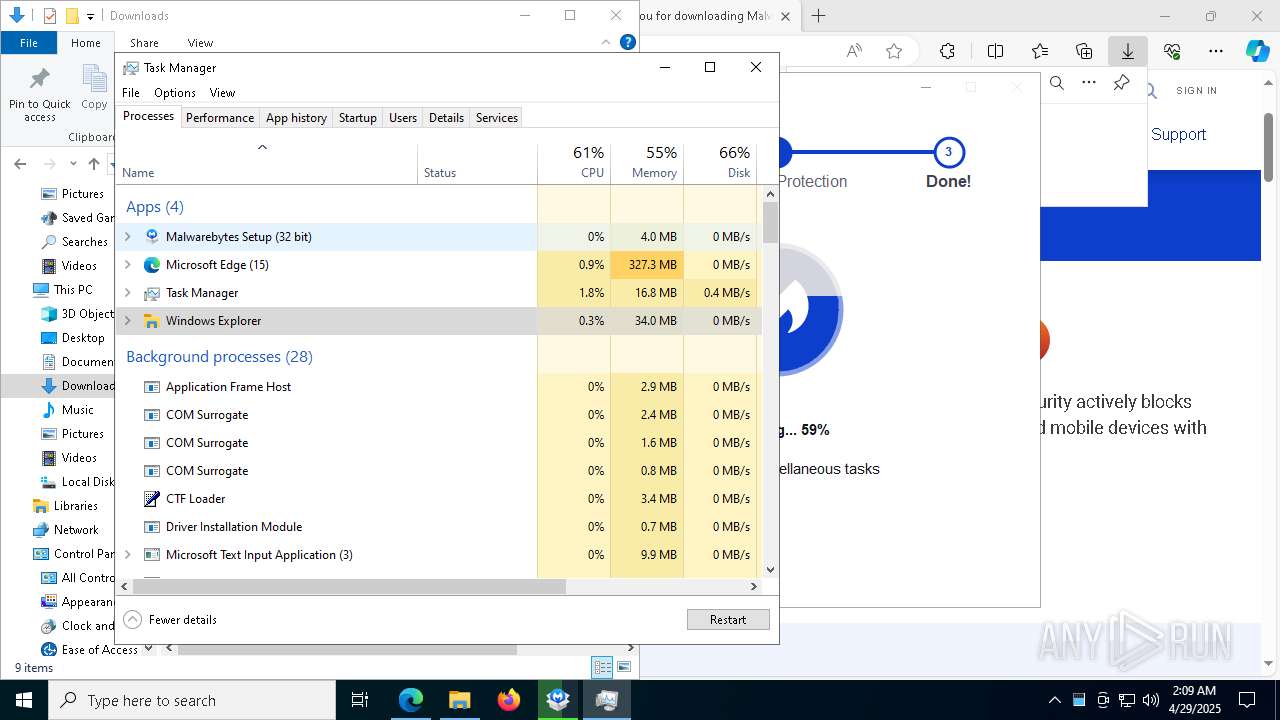
Total processes
259
Monitored processes
112
Malicious processes
12
Suspicious processes
1
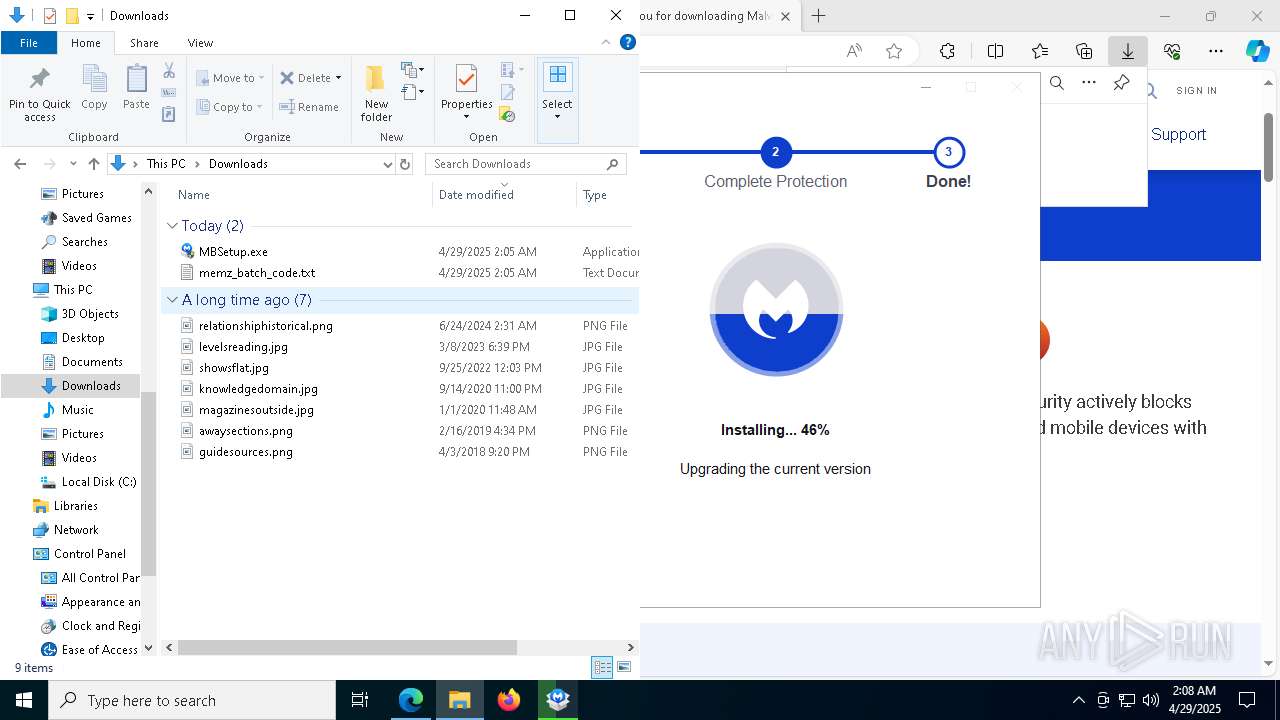
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 472 | "C:\Users\admin\AppData\Roaming\MEMZ.exe" /watchdog | C:\Users\admin\AppData\Roaming\MEMZ.exe | MEMZ.exe | ||||||||||||
User: admin Integrity Level: HIGH Modules
| |||||||||||||||
| 728 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5072 --field-trial-handle=2248,i,12536092094652008346,4300311200561382251,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 872 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=quarantine.mojom.Quarantine --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=1608 --field-trial-handle=2248,i,12536092094652008346,4300311200561382251,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 924 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=chrome.mojom.UtilReadIcon --lang=en-US --service-sandbox-type=icon_reader --no-appcompat-clear --mojo-platform-channel-handle=8288 --field-trial-handle=2248,i,12536092094652008346,4300311200561382251,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 924 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=7896 --field-trial-handle=2248,i,12536092094652008346,4300311200561382251,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | msedge.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1004 | "C:\Users\admin\AppData\Roaming\MEMZ.exe" /watchdog | C:\Users\admin\AppData\Roaming\MEMZ.exe | MEMZ.exe | ||||||||||||
User: admin Integrity Level: HIGH Modules
| |||||||||||||||
| 1040 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=quarantine.mojom.Quarantine --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=5876 --field-trial-handle=2248,i,12536092094652008346,4300311200561382251,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1052 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=6188 --field-trial-handle=2248,i,12536092094652008346,4300311200561382251,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1116 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1132 | "C:\WINDOWS\System32\SLUI.exe" RuleId=3482d82e-ca2c-4e1f-8864-da0267b484b2;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=4de7cb65-cdf1-4de9-8ae8-e3cce27b9f2c;NotificationInterval=1440;Trigger=TimerEvent | C:\Windows\System32\slui.exe | SppExtComObj.Exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
272 685
Read events
271 640
Write events
1 022
Delete events
23
Modification events
| (PID) Process: | (7216) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (7216) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (7216) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (7216) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (7216) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: FA59188277922F00 | |||
| (PID) Process: | (7216) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 33BD248277922F00 | |||
| (PID) Process: | (7216) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\197234 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {0C406DA1-6A99-4D86-91E8-8B5348E548E7} | |||
| (PID) Process: | (7216) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\197234 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {57FF680B-A1DB-40A2-AFE9-9070AF58B400} | |||
| (PID) Process: | (7216) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\197234 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {C719668A-3FF1-49AD-96E2-250E150850A1} | |||
| (PID) Process: | (7216) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 5118988277922F00 | |||
Executable files
1 306
Suspicious files
1 048
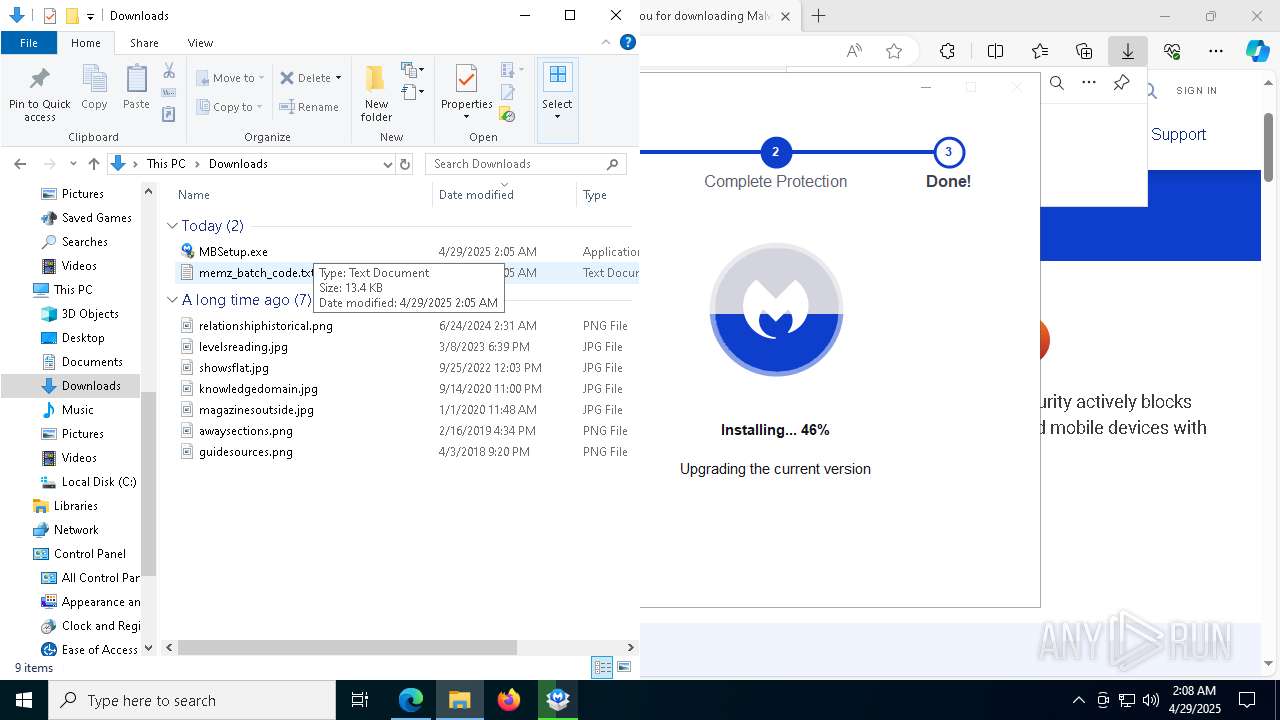
Text files
194
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7216 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF10b901.TMP | — | |
MD5:— | SHA256:— | |||
| 7216 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7216 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF10b901.TMP | — | |
MD5:— | SHA256:— | |||
| 7216 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7216 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF10b911.TMP | — | |
MD5:— | SHA256:— | |||
| 7216 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7216 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF10b920.TMP | — | |
MD5:— | SHA256:— | |||
| 7216 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7216 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF10b930.TMP | — | |
MD5:— | SHA256:— | |||
| 7216 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
52
TCP/UDP connections
241
DNS requests
269
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5496 | MoUsoCoreWorker.exe | GET | 200 | 95.100.171.17:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.200.189.225:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
4244 | RUXIMICS.exe | GET | 200 | 95.100.171.17:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
4244 | RUXIMICS.exe | GET | 200 | 23.200.189.225:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
7288 | svchost.exe | GET | 206 | 23.45.233.36:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/9b9f8fb4-8a65-41e4-bda3-5416858f0aeb?P1=1746418467&P2=404&P3=2&P4=VOik5XK2CugyNuNH%2fcwK8x6nugH%2fau%2bOQcRm7c5k4mRw%2f%2fmBa3AkJG1U2PNq%2bu6q%2fuqkoBxMJPLTIb%2fOVvqscw%3d%3d | unknown | — | — | whitelisted |
7288 | svchost.exe | GET | 206 | 23.45.233.36:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/9b9f8fb4-8a65-41e4-bda3-5416858f0aeb?P1=1746418467&P2=404&P3=2&P4=VOik5XK2CugyNuNH%2fcwK8x6nugH%2fau%2bOQcRm7c5k4mRw%2f%2fmBa3AkJG1U2PNq%2bu6q%2fuqkoBxMJPLTIb%2fOVvqscw%3d%3d | unknown | — | — | whitelisted |
7288 | svchost.exe | GET | 206 | 23.45.233.36:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/9b9f8fb4-8a65-41e4-bda3-5416858f0aeb?P1=1746418467&P2=404&P3=2&P4=VOik5XK2CugyNuNH%2fcwK8x6nugH%2fau%2bOQcRm7c5k4mRw%2f%2fmBa3AkJG1U2PNq%2bu6q%2fuqkoBxMJPLTIb%2fOVvqscw%3d%3d | unknown | — | — | whitelisted |
4996 | SIHClient.exe | GET | 200 | 23.200.189.225:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
7288 | svchost.exe | GET | 206 | 23.45.233.36:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/a575cead-e662-4f4d-b0c3-81f1438d0388?P1=1746418468&P2=404&P3=2&P4=P%2b0fSNX3PFXHrw3IVwvKfagCFwLhgskA3%2fYV7jziDo3RySUcsQNBVtIpF3IO3ymnVhJX0ct6c%2fUVCIF3BjwLjg%3d%3d | unknown | — | — | whitelisted |
7288 | svchost.exe | GET | 206 | 23.45.233.36:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/a575cead-e662-4f4d-b0c3-81f1438d0388?P1=1746418468&P2=404&P3=2&P4=P%2b0fSNX3PFXHrw3IVwvKfagCFwLhgskA3%2fYV7jziDo3RySUcsQNBVtIpF3IO3ymnVhJX0ct6c%2fUVCIF3BjwLjg%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
2104 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5496 | MoUsoCoreWorker.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4244 | RUXIMICS.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5496 | MoUsoCoreWorker.exe | 95.100.171.17:80 | crl.microsoft.com | Akamai International B.V. | FR | whitelisted |
4244 | RUXIMICS.exe | 95.100.171.17:80 | crl.microsoft.com | Akamai International B.V. | FR | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.200.189.225:80 | www.microsoft.com | Moratelindo Internet Exchange Point | ID | whitelisted |
4244 | RUXIMICS.exe | 23.200.189.225:80 | www.microsoft.com | Moratelindo Internet Exchange Point | ID | whitelisted |
5496 | MoUsoCoreWorker.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
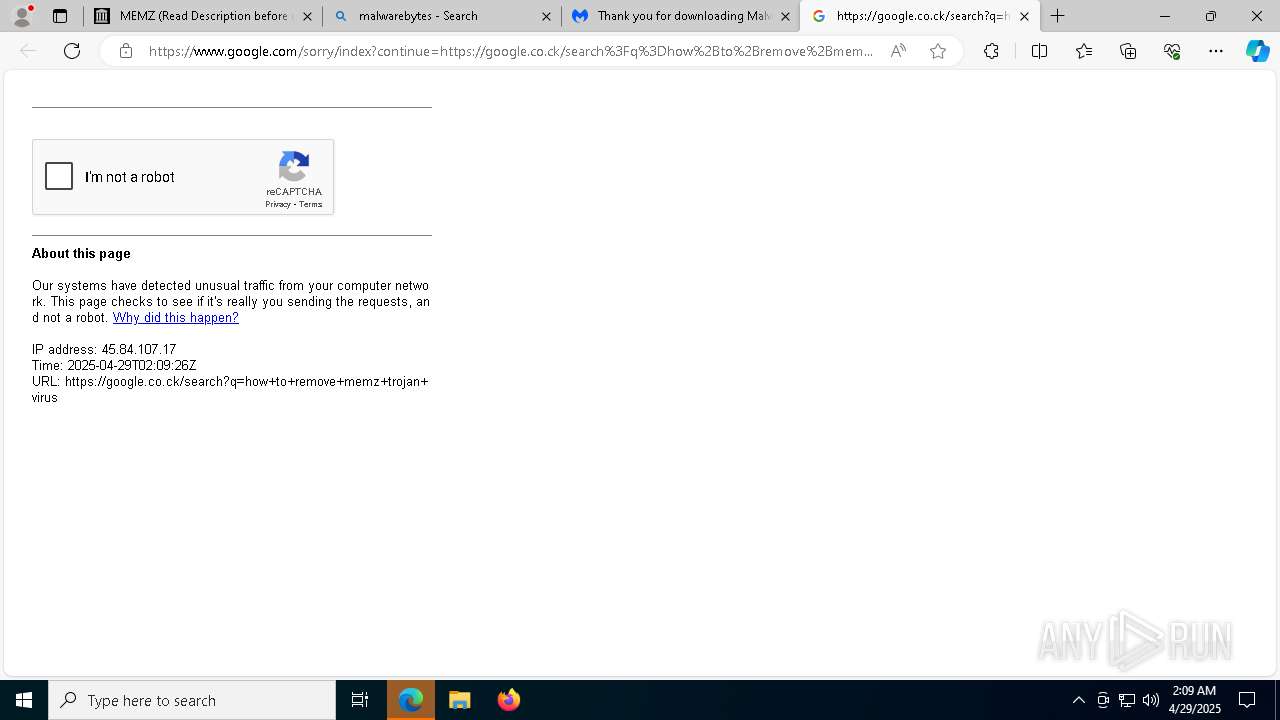
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
archive.org |
| whitelisted |
business.bing.com |
| whitelisted |
bzib.nelreports.net |
| whitelisted |