analyze malware
- Huge database of samples and IOCs
- Custom VM setup
- Unlimited submissions
- Interactive approach
| download: | mcdonalds.exe |
| Full analysis: | https://app.any.run/tasks/4b374c9e-b512-4306-86b3-bc7089c5df33 |
| Verdict: | Malicious activity |
| Threats: | GandCrab is probably one of the most famous Ransomware. A Ransomware is a malware that asks the victim to pay money in order to restore access to encrypted files. If the user does not cooperate the files are forever lost. |
| Analysis date: | January 17, 2019, 21:51:40 |
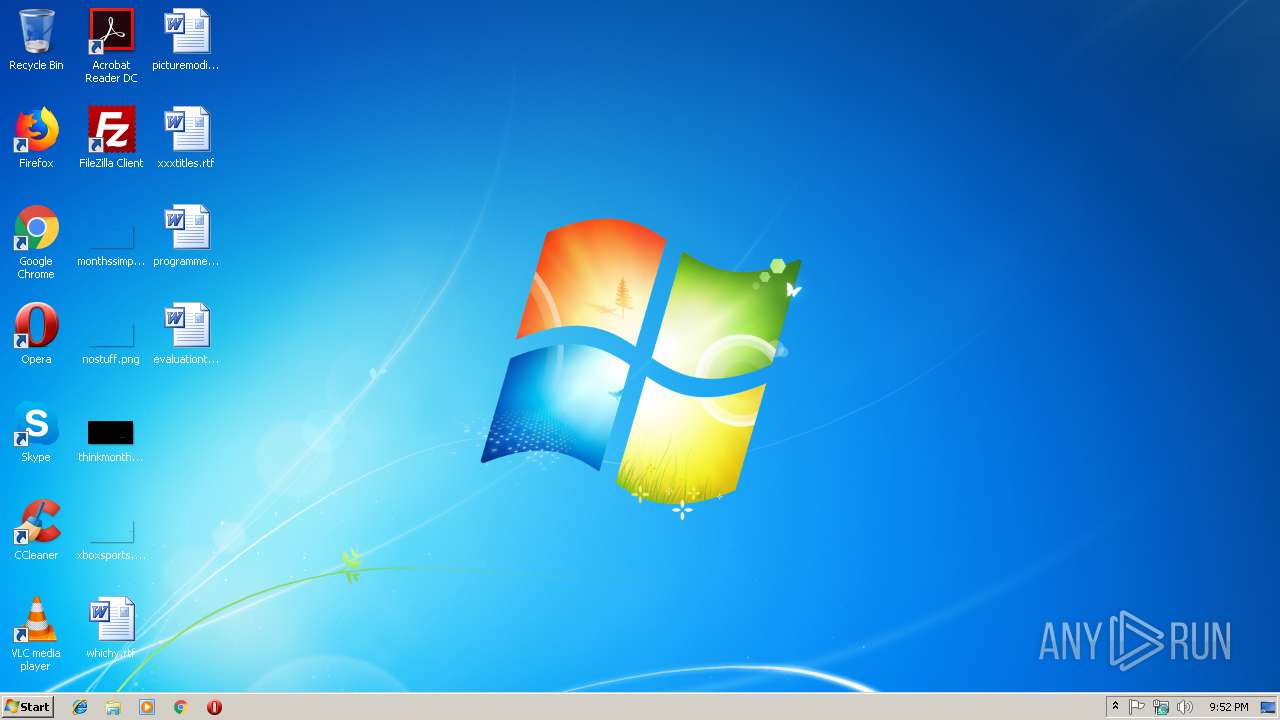
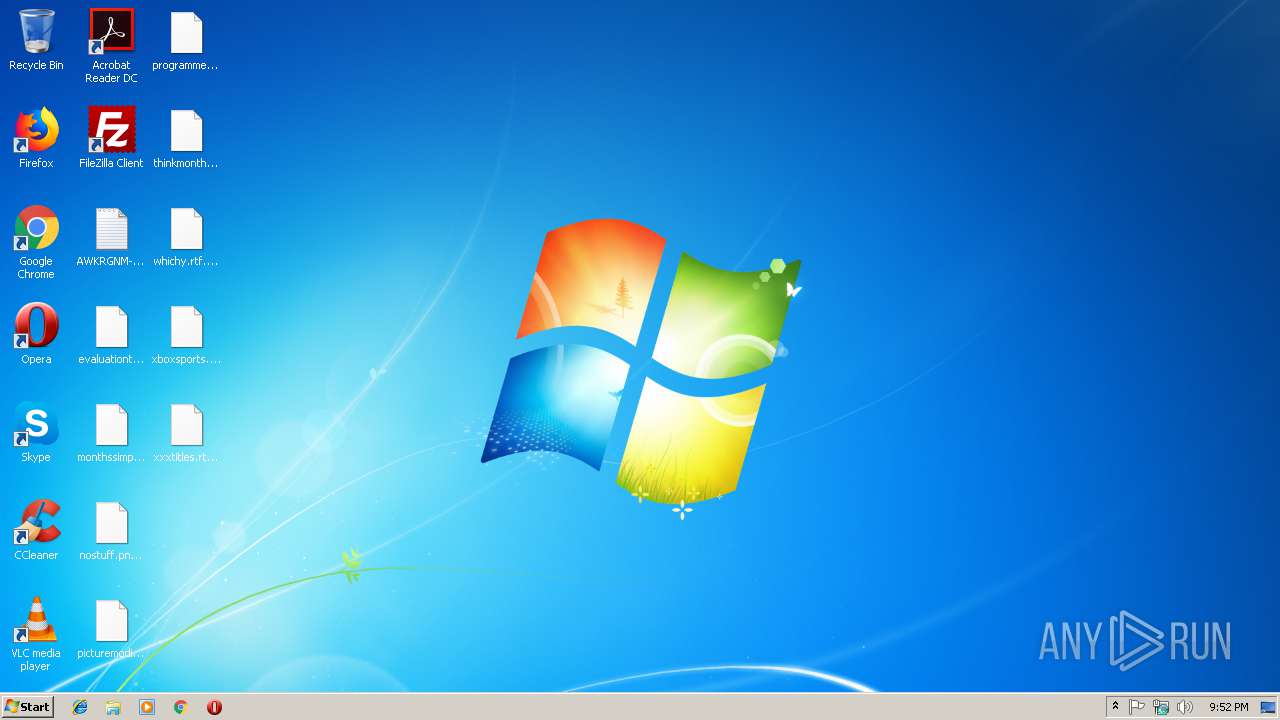
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 0673B159C2F01FADEADC3306F2BB5390 |
| SHA1: | 34F0DB8012DEFB9078BCA6170844E4CA1A1888A3 |
| SHA256: | 5DF55A2D3F688735E0D530A7639DADAC3817D4B3F2972276FB3B046D381A9121 |
| SSDEEP: | 3072:QSzpCgMLAxIJY5GEmj1GHBTfFhTWkCvaTdmGlpbZSzDnL7hOtbf:Qw6LAxivBIdfJC6BtZtb |
MALICIOUS
Changes the autorun value in the registry
- mcdonalds.exe (PID: 3612)
Disables Windows Defender Real-time monitoring
- winsvcs.exe (PID: 2920)
Changes Security Center notification settings
- winsvcs.exe (PID: 2920)
Application was dropped or rewritten from another process
- 1367330637.exe (PID: 2852)
Disables Windows System Restore
- winsvcs.exe (PID: 2920)
GandCrab keys found
- 1367330637.exe (PID: 2852)
Actions looks like stealing of personal data
- 1367330637.exe (PID: 2852)
Renames files like Ransomware
- 1367330637.exe (PID: 2852)
Downloads executable files from the Internet
- winsvcs.exe (PID: 2920)
Writes file to Word startup folder
- 1367330637.exe (PID: 2852)
Downloads executable files from IP
- winsvcs.exe (PID: 2920)
Dropped file may contain instructions of ransomware
- 1367330637.exe (PID: 2852)
Changes settings of System certificates
- 1367330637.exe (PID: 2852)
Deletes shadow copies
- 1367330637.exe (PID: 2852)
SUSPICIOUS
Starts itself from another location
- mcdonalds.exe (PID: 3612)
Executable content was dropped or overwritten
- mcdonalds.exe (PID: 3612)
- winsvcs.exe (PID: 2920)
Creates files in the program directory
- 1367330637.exe (PID: 2852)
Reads the cookies of Mozilla Firefox
- 1367330637.exe (PID: 2852)
Creates files like Ransomware instruction
- 1367330637.exe (PID: 2852)
Creates files in the user directory
- 1367330637.exe (PID: 2852)
Adds / modifies Windows certificates
- 1367330637.exe (PID: 2852)
INFO
Dropped object may contain TOR URL's
- 1367330637.exe (PID: 2852)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2017:07:26 06:13:38+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 9 |
| CodeSize: | 65536 |
| InitializedDataSize: | 222208 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x5072 |
| OSVersion: | 5 |
| ImageVersion: | - |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.45.8.4 |
| ProductVersionNumber: | 7.32.568.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (British) |
| CharacterSet: | Unicode |
| FileVersion: | 1.6.8.23 |
| ProductVersion: | 1.6.8.23 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 26-Jul-2017 04:13:38 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000F0 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 26-Jul-2017 04:13:38 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0000FECB | 0x00010000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.54119 |
.rdata | 0x00011000 | 0x00004122 | 0x00004200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.17314 |
.data | 0x00016000 | 0x0000873C | 0x00006C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.52834 |
.rsrc | 0x0001F000 | 0x00028BCA | 0x00028C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.29626 |
.reloc | 0x00048000 | 0x00001A0C | 0x00001C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 4.66871 |
Imports
KERNEL32.dll |
Exports
Title | Ordinal | Address |
|---|---|---|
135718 | 0x00000000 |
Total processes
38
Monitored processes
5
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process |
|---|---|---|---|---|
| 3612 | "C:\Users\admin\AppData\Local\Temp\mcdonalds.exe" | C:\Users\admin\AppData\Local\Temp\mcdonalds.exe | explorer.exe | |
User: admin Integrity Level: MEDIUM Exit code: 0 | ||||
| 2920 | C:\Users\admin\66087085470750\winsvcs.exe | C:\Users\admin\66087085470750\winsvcs.exe | mcdonalds.exe | |
User: admin Integrity Level: MEDIUM | ||||
| 2852 | C:\Users\admin\AppData\Local\Temp\1367330637.exe | C:\Users\admin\AppData\Local\Temp\1367330637.exe | winsvcs.exe | |
User: admin Integrity Level: MEDIUM | ||||
| 3940 | "C:\Windows\system32\wbem\wmic.exe" shadowcopy delete | C:\Windows\system32\wbem\wmic.exe | 1367330637.exe | |
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: WMI Commandline Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) | ||||
| 2156 | C:\Windows\system32\vssvc.exe | C:\Windows\system32\vssvc.exe | — | services.exe |
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Volume Shadow Copy Service Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) | ||||
Total events
181
Read events
112
Write events
69
Delete events
0
Modification events
| (PID) Process: | (3612) mcdonalds.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | Microsoft Windows Services |
Value: C:\Users\admin\66087085470750\winsvcs.exe | |||
| (PID) Process: | (3612) mcdonalds.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | Microsoft Windows Services |
Value: C:\Users\admin\66087085470750\winsvcs.exe | |||
| (PID) Process: | (2920) winsvcs.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Policies\Microsoft\Windows Defender\Real-time Protection |
| Operation: | write | Name: | DisableScanOnRealtimeEnable |
Value: 1 | |||
| (PID) Process: | (2920) winsvcs.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Policies\Microsoft\Windows Defender\Real-time Protection |
| Operation: | write | Name: | DisableOnAccessProtection |
Value: 1 | |||
| (PID) Process: | (2920) winsvcs.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Policies\Microsoft\Windows Defender\Real-time Protection |
| Operation: | write | Name: | DisableBehaviorMonitoring |
Value: 1 | |||
| (PID) Process: | (2920) winsvcs.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Security Center |
| Operation: | write | Name: | AntiVirusOverride |
Value: 1 | |||
| (PID) Process: | (2920) winsvcs.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Security Center |
| Operation: | write | Name: | UpdatesOverride |
Value: 1 | |||
| (PID) Process: | (2920) winsvcs.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Security Center |
| Operation: | write | Name: | FirewallOverride |
Value: 1 | |||
| (PID) Process: | (2920) winsvcs.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Security Center |
| Operation: | write | Name: | AntiVirusDisableNotify |
Value: 1 | |||
| (PID) Process: | (2920) winsvcs.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Security Center |
| Operation: | write | Name: | UpdatesDisableNotify |
Value: 1 | |||
Executable files
3
Suspicious files
424
Text files
318
Unknown types
11
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2852 | 1367330637.exe | C:\Recovery\345b46fe-a9f9-11e7-a83c-e8a4f72b1d33\boot.sdi | — | |
MD5:— | SHA256:— | |||
| 2852 | 1367330637.exe | C:\Recovery\345b46fe-a9f9-11e7-a83c-e8a4f72b1d33\Winre.wim.awkrgnm | — | |
MD5:— | SHA256:— | |||
| 2852 | 1367330637.exe | C:\Recovery\345b46fe-a9f9-11e7-a83c-e8a4f72b1d33\Winre.wim | — | |
MD5:— | SHA256:— | |||
| 2852 | 1367330637.exe | C:\System Volume Information\SPP\OnlineMetadataCache\{05ed3515-06b3-48f6-8cf2-bf24b1bf0727}_OnDiskSnapshotProp | — | |
MD5:— | SHA256:— | |||
| 2852 | 1367330637.exe | C:\$Recycle.Bin\AWKRGNM-DECRYPT.txt | text | |
MD5:36482A3ADBA326BCD2CFB5CC64785AD0 | SHA256:CAD5A223F8C67701F6A2176CFBB746335A4C88362AB0389D53025BC3D7D3E25F | |||
| 2852 | 1367330637.exe | C:\MSOCache\AWKRGNM-DECRYPT.txt | text | |
MD5:36482A3ADBA326BCD2CFB5CC64785AD0 | SHA256:CAD5A223F8C67701F6A2176CFBB746335A4C88362AB0389D53025BC3D7D3E25F | |||
| 2852 | 1367330637.exe | C:\System Volume Information\SPP\OnlineMetadataCache\{16d74681-6bc3-4c44-97f0-8b8dfefe2355}_OnDiskSnapshotProp | — | |
MD5:— | SHA256:— | |||
| 2852 | 1367330637.exe | C:\System Volume Information\SPP\OnlineMetadataCache\{38e8535f-27d0-4352-aa3a-ce4178930102}_OnDiskSnapshotProp | — | |
MD5:— | SHA256:— | |||
| 2852 | 1367330637.exe | C:\AWKRGNM-DECRYPT.txt | text | |
MD5:36482A3ADBA326BCD2CFB5CC64785AD0 | SHA256:CAD5A223F8C67701F6A2176CFBB746335A4C88362AB0389D53025BC3D7D3E25F | |||
| 2852 | 1367330637.exe | C:\Users\AWKRGNM-DECRYPT.txt | text | |
MD5:36482A3ADBA326BCD2CFB5CC64785AD0 | SHA256:CAD5A223F8C67701F6A2176CFBB746335A4C88362AB0389D53025BC3D7D3E25F | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
35
TCP/UDP connections
6
DNS requests
1
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2920 | winsvcs.exe | GET | — | 92.63.197.153:80 | http://92.63.197.153/s/1.exe | RU | — | — | malicious |
2920 | winsvcs.exe | GET | 200 | 92.63.197.153:80 | http://92.63.197.153/s/1.exe | RU | executable | 361 Kb | malicious |
2920 | winsvcs.exe | GET | 404 | 92.63.197.153:80 | http://92.63.197.153/s/5.exe | RU | html | 178 b | malicious |
2920 | winsvcs.exe | GET | 404 | 92.63.197.153:80 | http://92.63.197.153/s/3.exe | RU | html | 178 b | malicious |
2920 | winsvcs.exe | GET | 404 | 92.63.197.153:80 | http://92.63.197.153/s/2.exe | RU | html | 178 b | malicious |
2920 | winsvcs.exe | GET | 404 | 92.63.197.153:80 | http://92.63.197.153/s/2.exe | RU | html | 178 b | malicious |
2920 | winsvcs.exe | GET | 404 | 92.63.197.153:80 | http://92.63.197.153/s/4.exe | RU | html | 178 b | malicious |
2920 | winsvcs.exe | GET | 404 | 92.63.197.153:80 | http://92.63.197.153/s/3.exe | RU | html | 178 b | malicious |
2920 | winsvcs.exe | GET | 404 | 92.63.197.153:80 | http://92.63.197.153/s/5.exe | RU | html | 178 b | malicious |
2920 | winsvcs.exe | GET | 404 | 92.63.197.153:80 | http://92.63.197.153/s/4.exe | RU | html | 178 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2852 | 1367330637.exe | 138.201.162.99:443 | www.kakaocorp.link | Hetzner Online GmbH | DE | malicious |
2852 | 1367330637.exe | 138.201.162.99:80 | www.kakaocorp.link | Hetzner Online GmbH | DE | malicious |
2920 | winsvcs.exe | 92.63.197.153:80 | — | — | RU | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.kakaocorp.link |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2920 | winsvcs.exe | A Network Trojan was detected | ET INFO Executable Download from dotted-quad Host |
2920 | winsvcs.exe | A Network Trojan was detected | ET TROJAN Single char EXE direct download likely trojan (multiple families) |
2920 | winsvcs.exe | A Network Trojan was detected | ET INFO Executable Download from dotted-quad Host |
2920 | winsvcs.exe | A Network Trojan was detected | ET TROJAN Single char EXE direct download likely trojan (multiple families) |
2920 | winsvcs.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
2920 | winsvcs.exe | Potentially Bad Traffic | ET INFO SUSPICIOUS Dotted Quad Host MZ Response |
2920 | winsvcs.exe | Misc activity | ET INFO EXE IsDebuggerPresent (Used in Malware Anti-Debugging) |
2920 | winsvcs.exe | A Network Trojan was detected | ET INFO Executable Download from dotted-quad Host |
2920 | winsvcs.exe | A Network Trojan was detected | ET TROJAN Single char EXE direct download likely trojan (multiple families) |
2920 | winsvcs.exe | A Network Trojan was detected | ET INFO Executable Download from dotted-quad Host |