| download: | M4PeopleNetStart.application |
| Full analysis: | https://app.any.run/tasks/b325f9cd-00cf-4434-8abd-26956c2c0e28 |
| Verdict: | No threats detected |
| Analysis date: | September 26, 2020, 01:17:00 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | text/xml |
| File info: | XML 1.0 document, UTF-8 Unicode (with BOM) text, with very long lines, with CRLF, LF line terminators |
| MD5: | EB1D264E313143750754704864889BAF |
| SHA1: | D930811CDCFBA3D74782D85789288BCB80DB7ABC |
| SHA256: | 5DEE94B057CDC769B19FA3F0DFE3685D2464D61635AAE789E4CEA9D7038EC241 |
| SSDEEP: | 384:RbmxM80q0E/2GfIdXoHrRg43k3wknT8yhTzdl6:lP870E/TfIBoHrRK3HnQyNzX6 |
MALICIOUS
No malicious indicators.SUSPICIOUS
Starts Internet Explorer
- MSOXMLED.EXE (PID: 2580)
INFO
Reads Internet Cache Settings
- iexplore.exe (PID: 1144)
- iexplore.exe (PID: 656)
Reads internet explorer settings
- iexplore.exe (PID: 3372)
- iexplore.exe (PID: 656)
Changes internet zones settings
- iexplore.exe (PID: 1144)
Application launched itself
- iexplore.exe (PID: 1144)
Reads settings of System Certificates
- iexplore.exe (PID: 1144)
- iexplore.exe (PID: 3372)
Changes settings of System certificates
- iexplore.exe (PID: 1144)
- iexplore.exe (PID: 3372)
Adds / modifies Windows certificates
- iexplore.exe (PID: 1144)
- iexplore.exe (PID: 3372)
Creates files in the user directory
- iexplore.exe (PID: 1144)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .xml | | | Generic XML (UTF-8) (72.7) |
|---|---|---|
| .txt | | | Text - UTF-8 encoded (27.2) |
EXIF
XMP
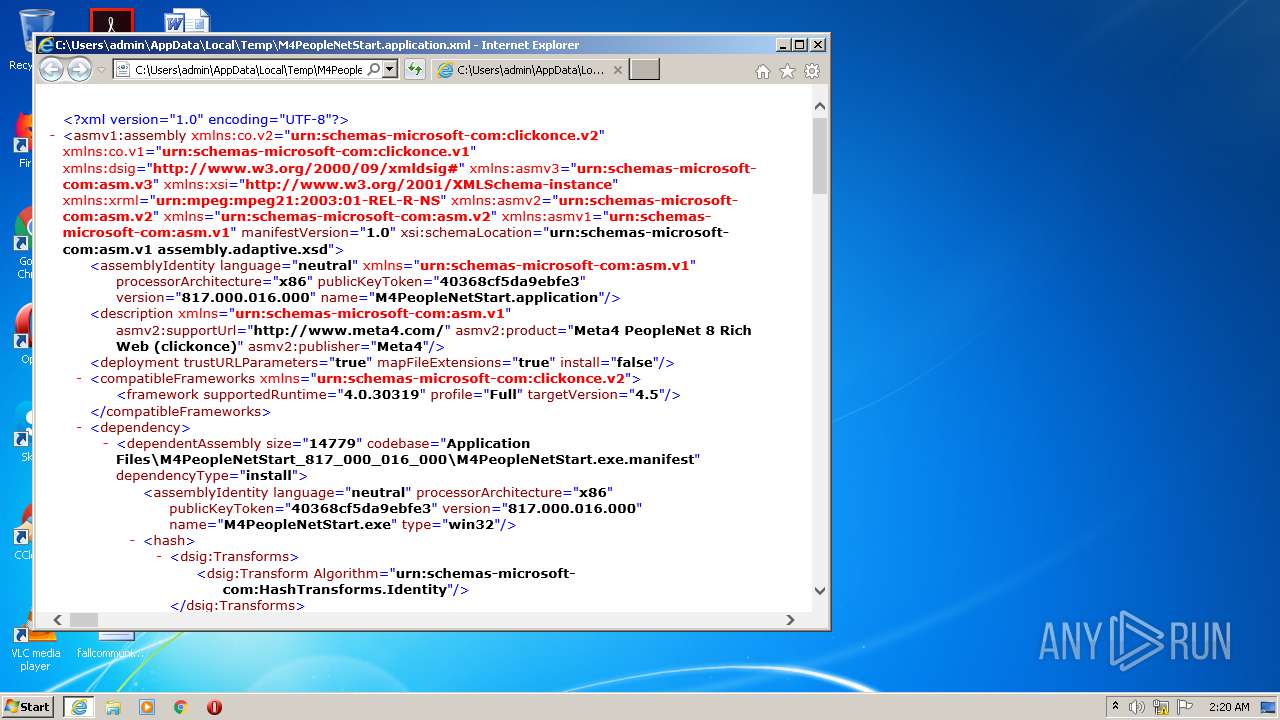
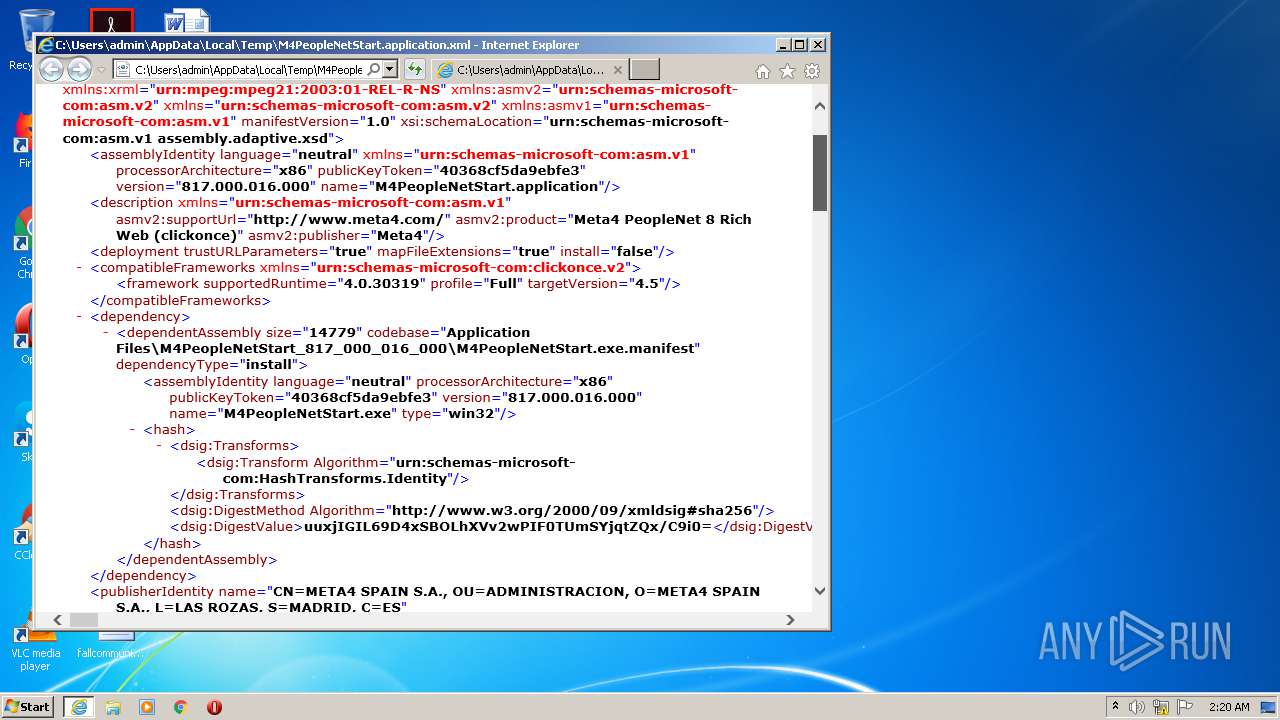
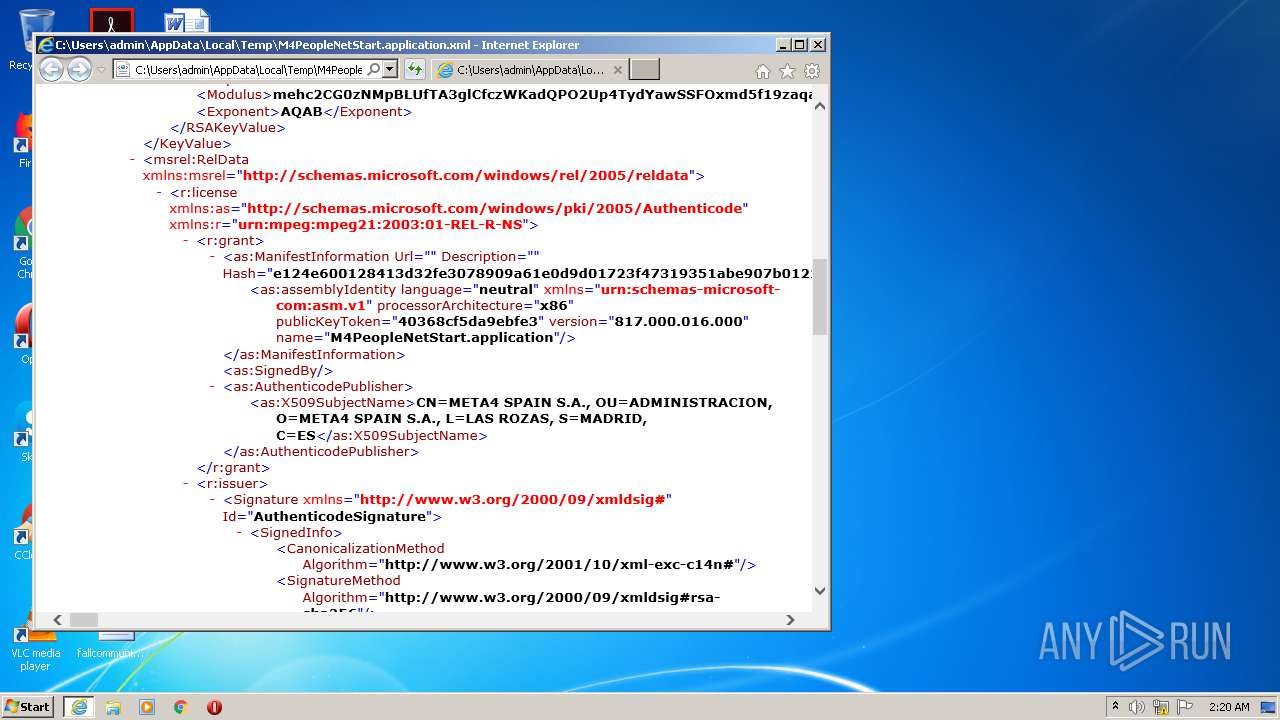
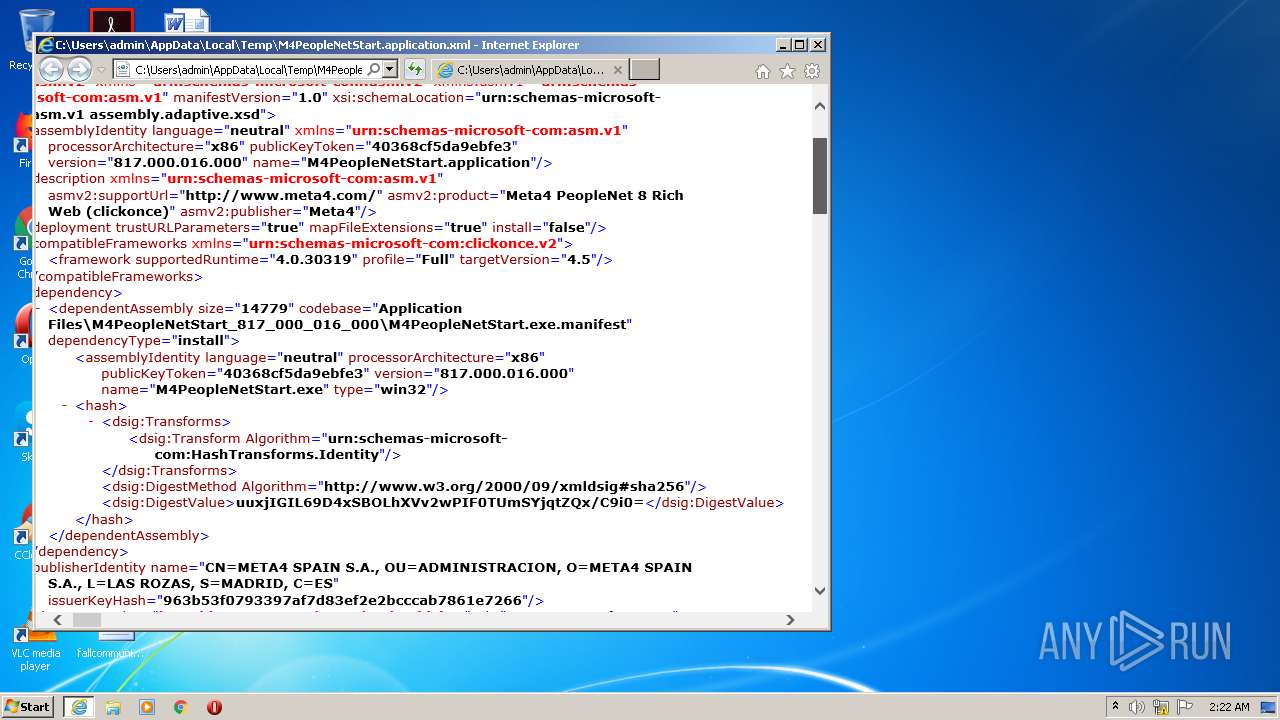
| AssemblySchemaLocation: | urn:schemas-microsoft-com:asm.v1 assembly.adaptive.xsd |
|---|---|
| AssemblyManifestVersion: | 1 |
| AssemblyXmlns: | urn:schemas-microsoft-com:asm.v2 |
| AssemblyAssemblyIdentityName: | M4PeopleNetStart.application |
| AssemblyAssemblyIdentityVersion: | 817.000.016.000 |
| AssemblyAssemblyIdentityPublicKeyToken: | 40368cf5da9ebfe3 |
| AssemblyAssemblyIdentityLanguage: | neutral |
| AssemblyAssemblyIdentityProcessorArchitecture: | x86 |
| AssemblyAssemblyIdentityXmlns: | urn:schemas-microsoft-com:asm.v1 |
| AssemblyDescriptionPublisher: | Meta4 |
| AssemblyDescriptionProduct: | Meta4 PeopleNet 8 Rich Web (clickonce) |
| AssemblyDescriptionSupportUrl: | http://www.meta4.com/ |
| AssemblyDescriptionXmlns: | urn:schemas-microsoft-com:asm.v1 |
| AssemblyDeploymentInstall: | - |
| AssemblyDeploymentMapFileExtensions: | |
| AssemblyDeploymentTrustURLParameters: | |
| AssemblyCompatibleFrameworksXmlns: | urn:schemas-microsoft-com:clickonce.v2 |
| AssemblyCompatibleFrameworksFrameworkTargetVersion: | 4.5 |
| AssemblyCompatibleFrameworksFrameworkProfile: | Full |
| AssemblyCompatibleFrameworksFrameworkSupportedRuntime: | 4.0.30319 |
| AssemblyDependencyDependentAssemblyDependencyType: | install |
| AssemblyDependencyDependentAssemblyCodebase: | Application Files\M4PeopleNetStart_817_000_016_000\M4PeopleNetStart.exe.manifest |
| AssemblyDependencyDependentAssemblySize: | 14779 |
| AssemblyDependencyDependentAssemblyAssemblyIdentityName: | M4PeopleNetStart.exe |
| AssemblyDependencyDependentAssemblyAssemblyIdentityVersion: | 817.000.016.000 |
| AssemblyDependencyDependentAssemblyAssemblyIdentityPublicKeyToken: | 40368cf5da9ebfe3 |
| AssemblyDependencyDependentAssemblyAssemblyIdentityLanguage: | neutral |
| AssemblyDependencyDependentAssemblyAssemblyIdentityProcessorArchitecture: | x86 |
| AssemblyDependencyDependentAssemblyAssemblyIdentityType: | win32 |
| AssemblyDependencyDependentAssemblyHashTransformsTransformAlgorithm: | urn:schemas-microsoft-com:HashTransforms.Identity |
| AssemblyDependencyDependentAssemblyHashDigestMethodAlgorithm: | http://www.w3.org/2000/09/xmldsig#sha256 |
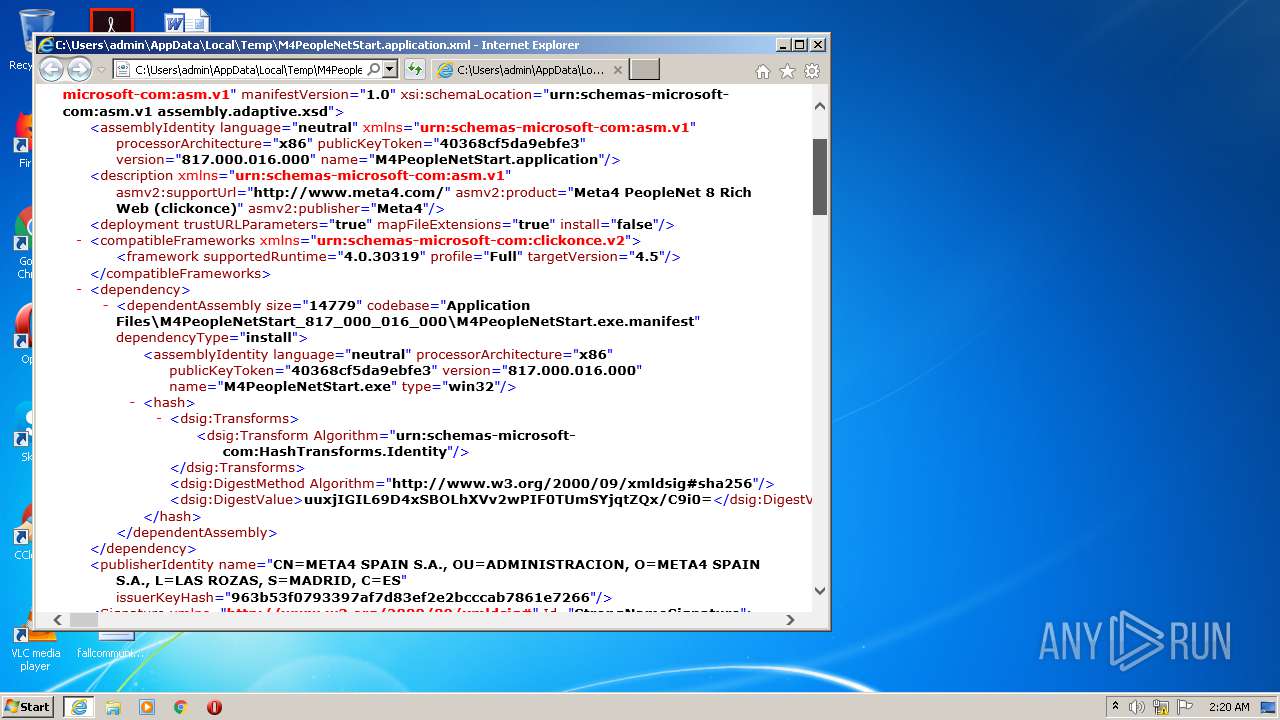
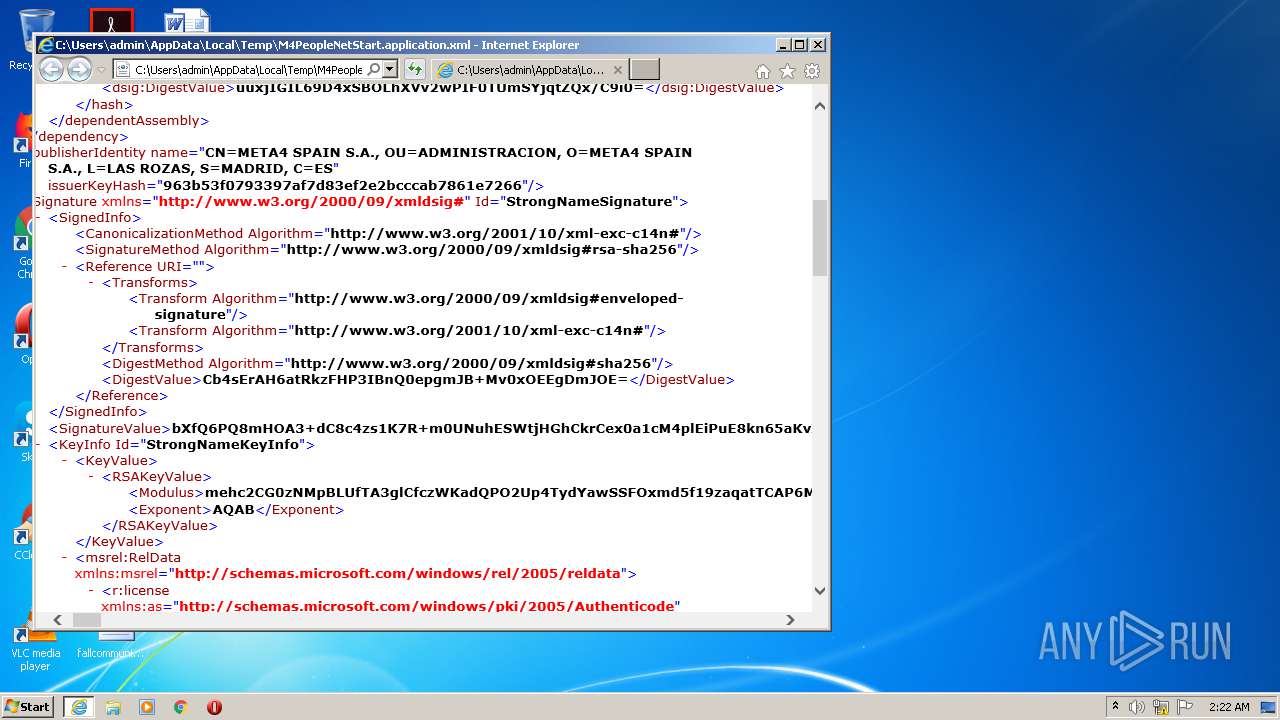
| AssemblyDependencyDependentAssemblyHashDigestValue: | uuxjIGIL69D4xSBOLhXVv2wPIF0TUmSYjqtZQx/C9i0= |
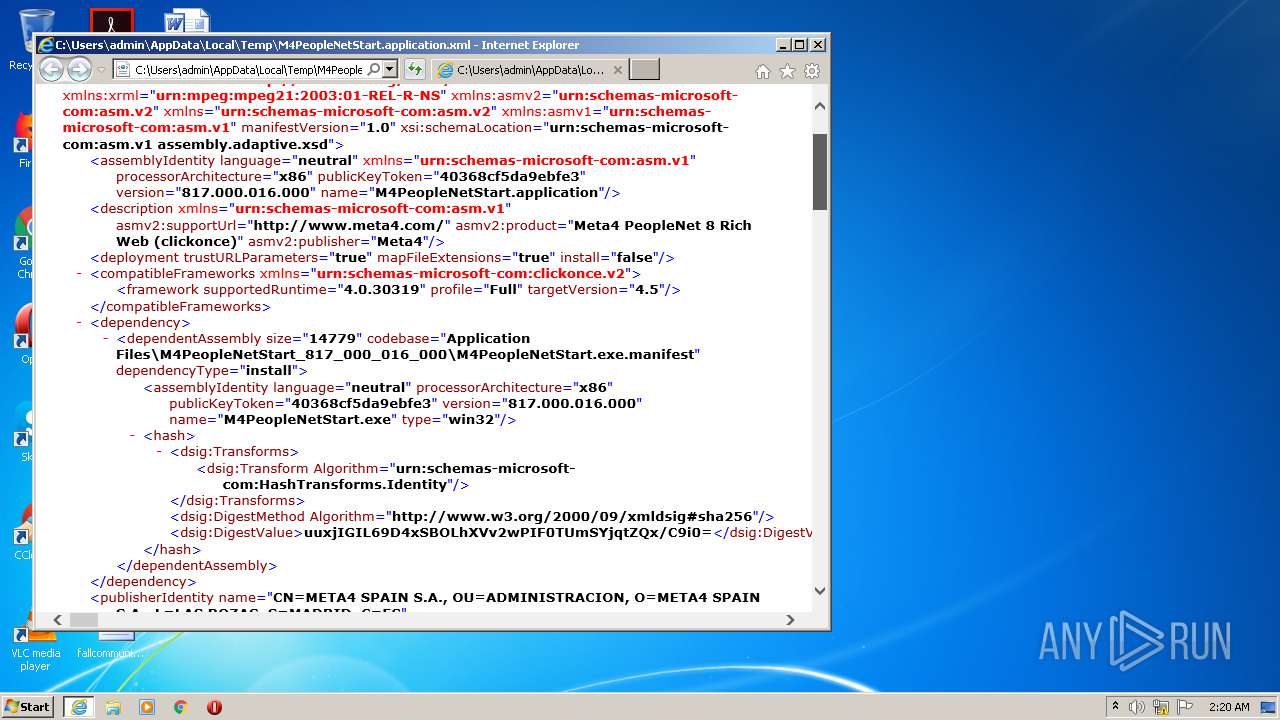
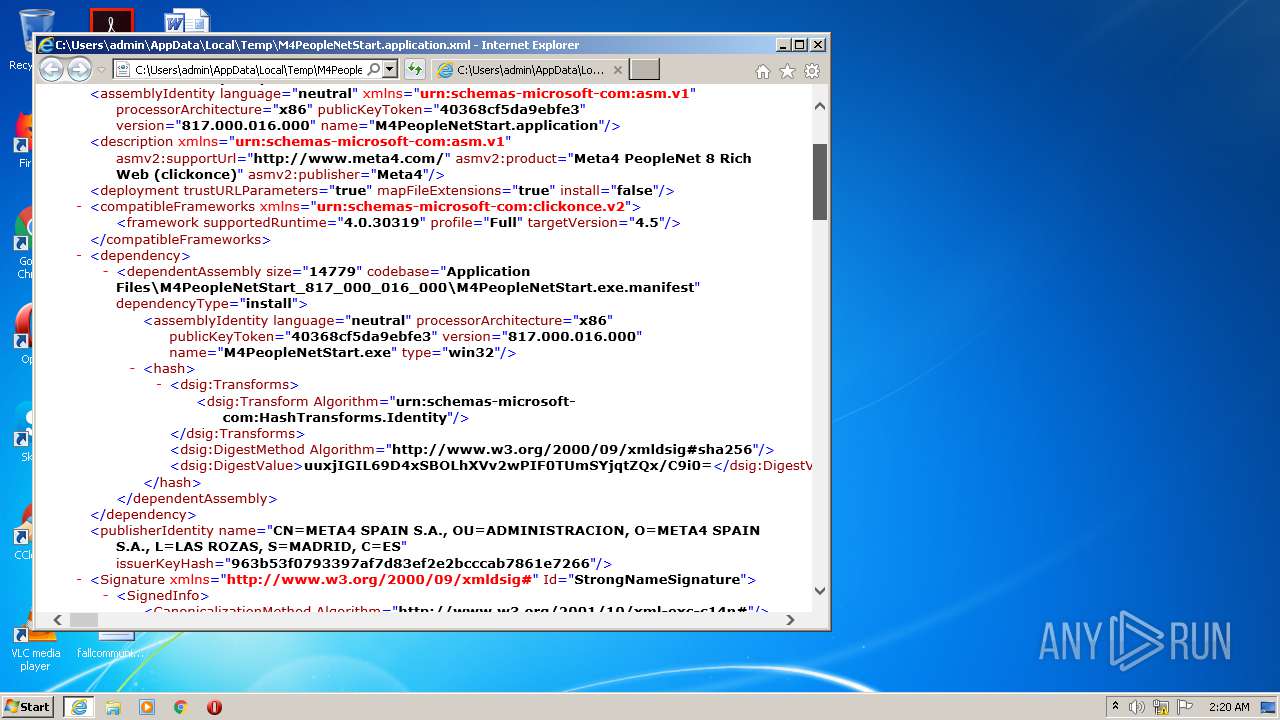
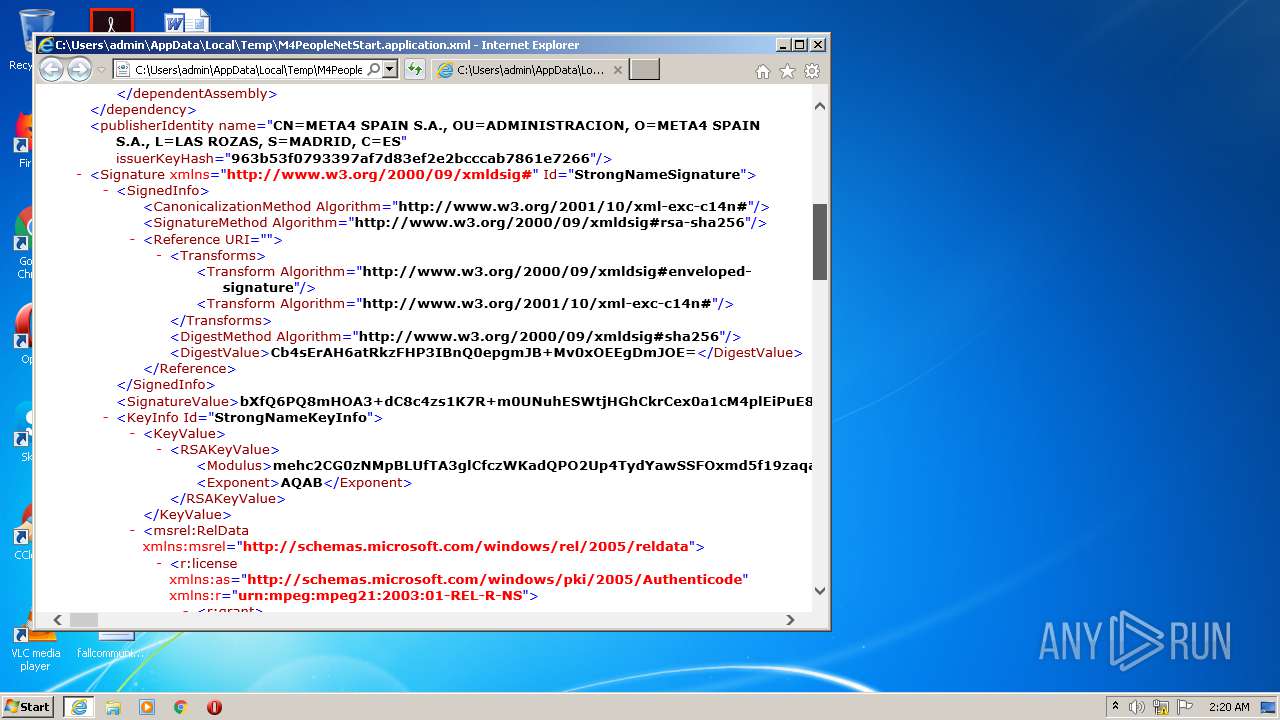
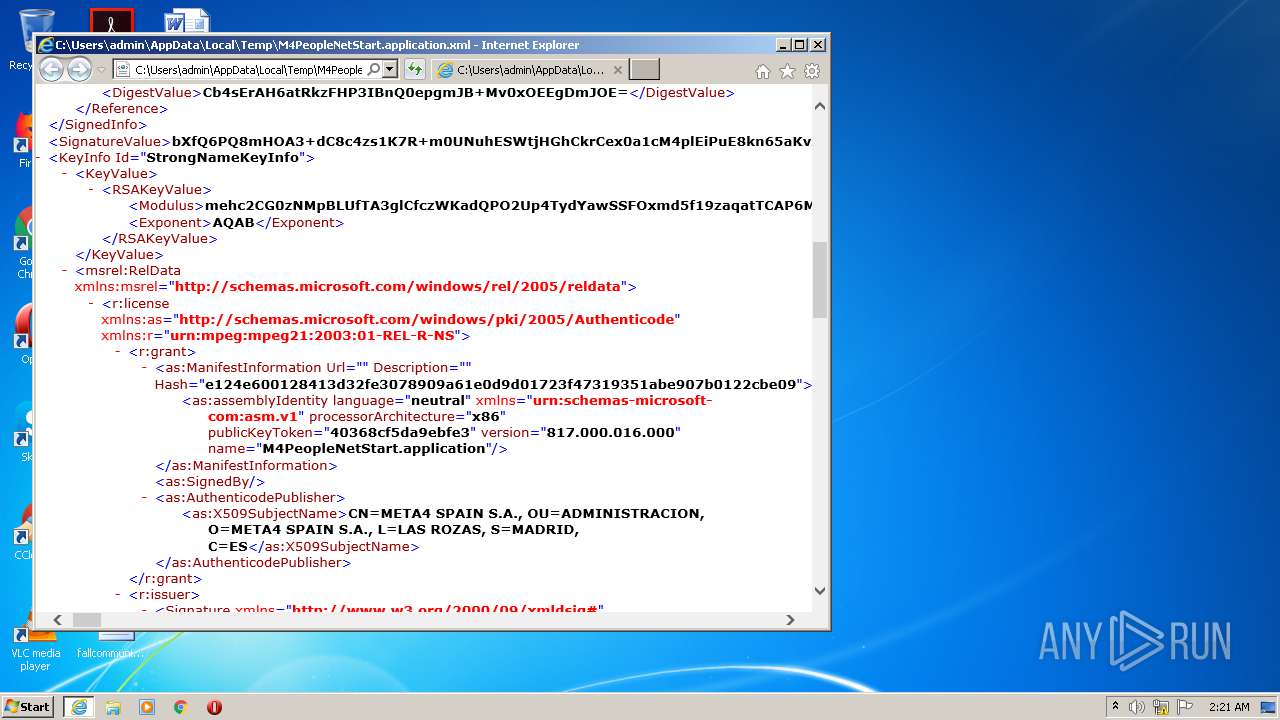
| AssemblyPublisherIdentityName: | CN=META4 SPAIN S.A., OU=ADMINISTRACION, O=META4 SPAIN S.A., L=LAS ROZAS, S=MADRID, C=ES |
| AssemblyPublisherIdentityIssuerKeyHash: | 963b53f0793397af7d83ef2e2bcccab7861e7266 |
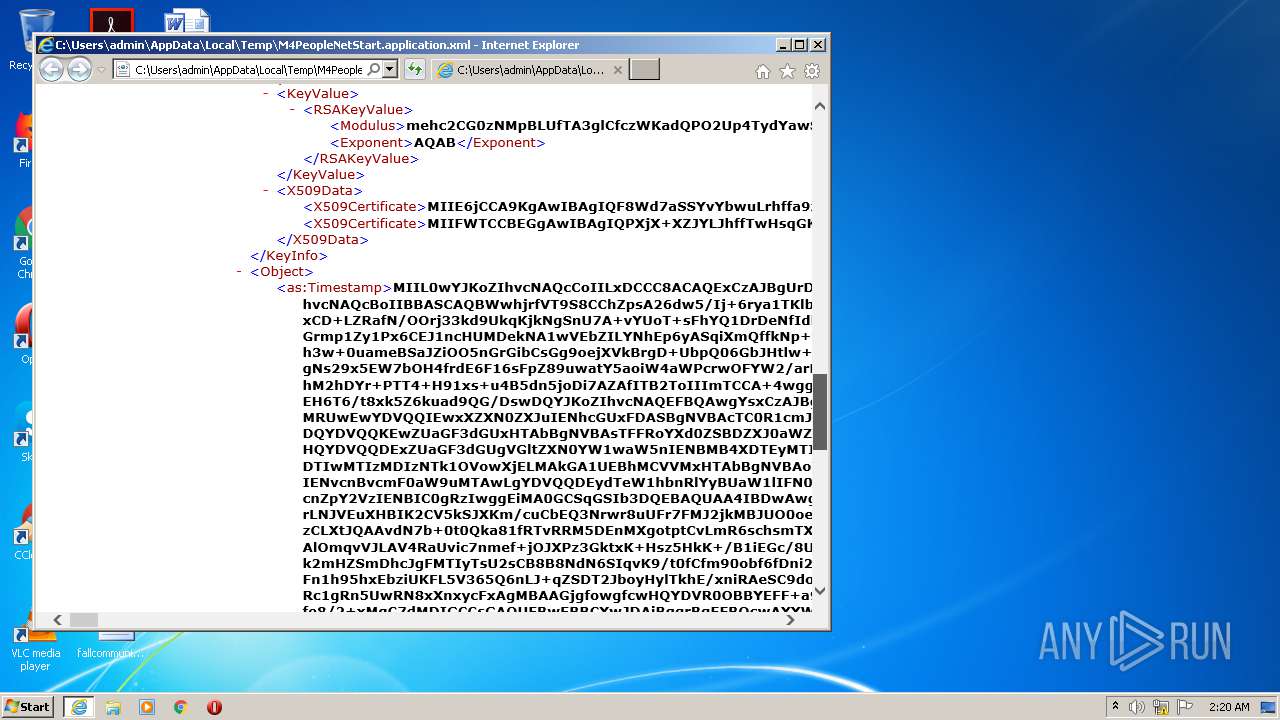
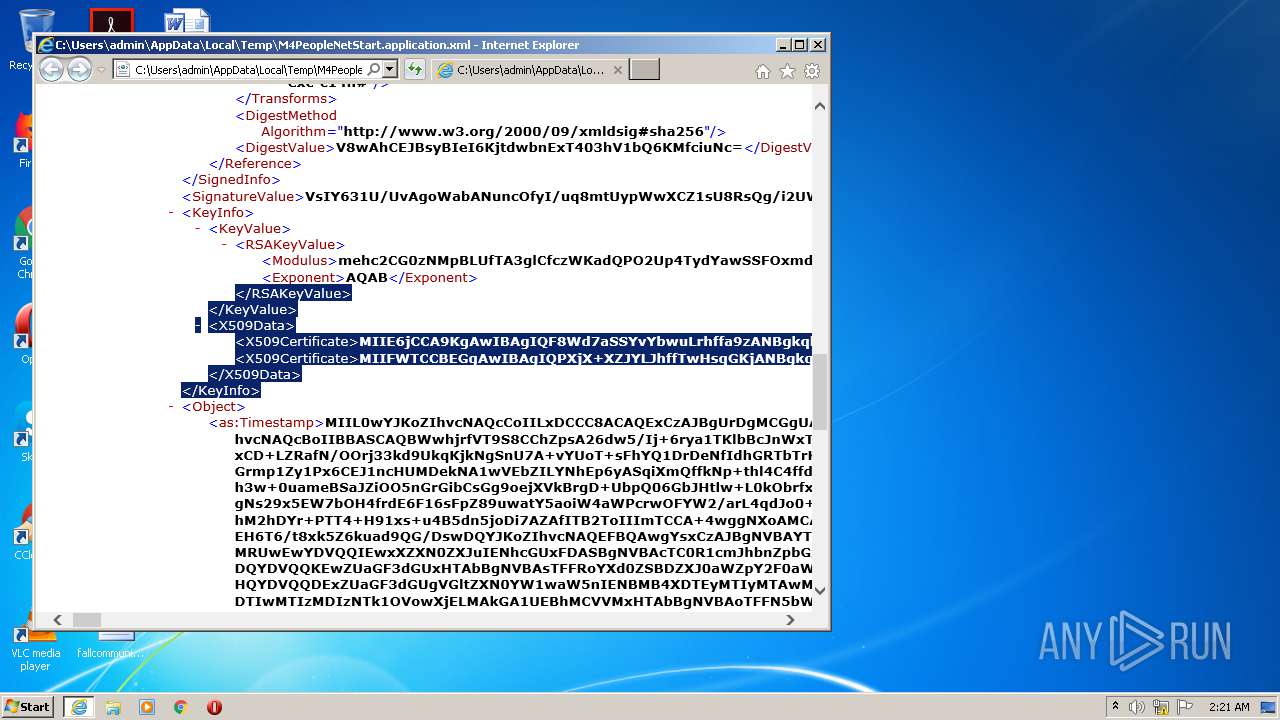
| AssemblySignatureId: | StrongNameSignature |
| AssemblySignatureXmlns: | http://www.w3.org/2000/09/xmldsig# |
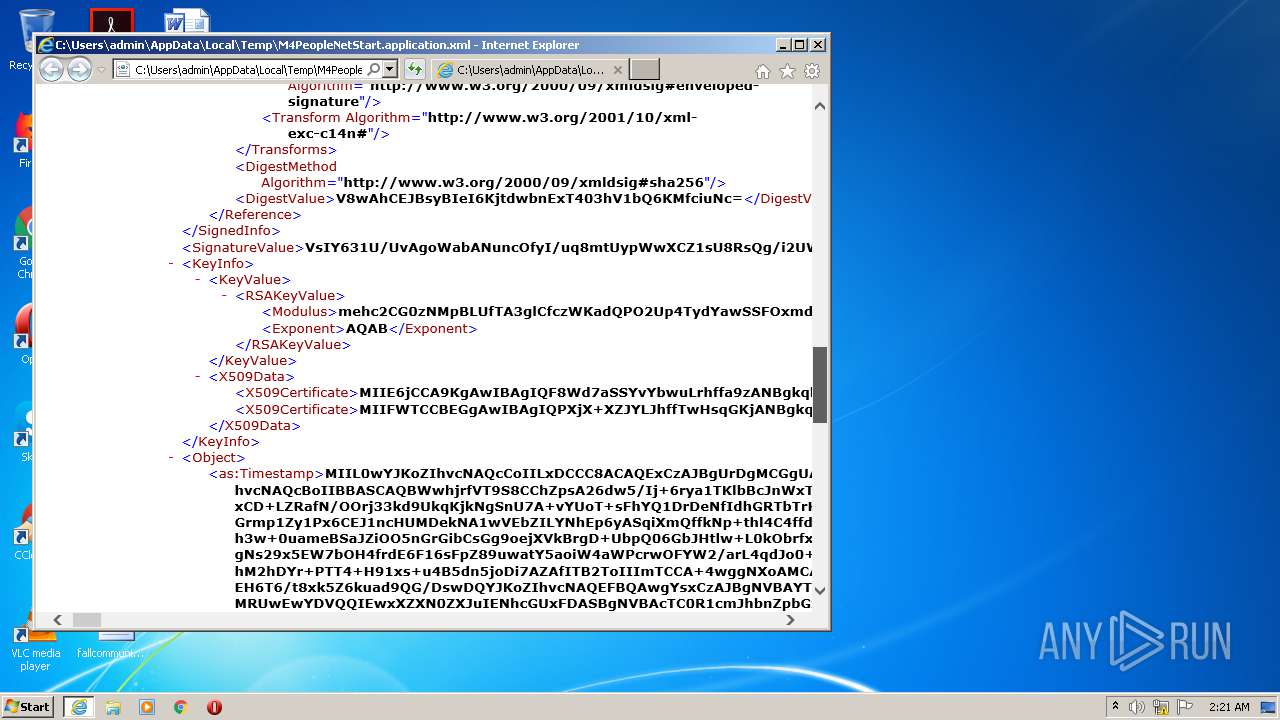
| AssemblySignatureSignedInfoCanonicalizationMethodAlgorithm: | http://www.w3.org/2001/10/xml-exc-c14n# |
| AssemblySignatureSignedInfoSignatureMethodAlgorithm: | http://www.w3.org/2000/09/xmldsig#rsa-sha256 |
| AssemblySignatureSignedInfoReferenceUri: | - |
| AssemblySignatureSignedInfoReferenceTransformsTransformAlgorithm: | http://www.w3.org/2000/09/xmldsig#enveloped-signature |
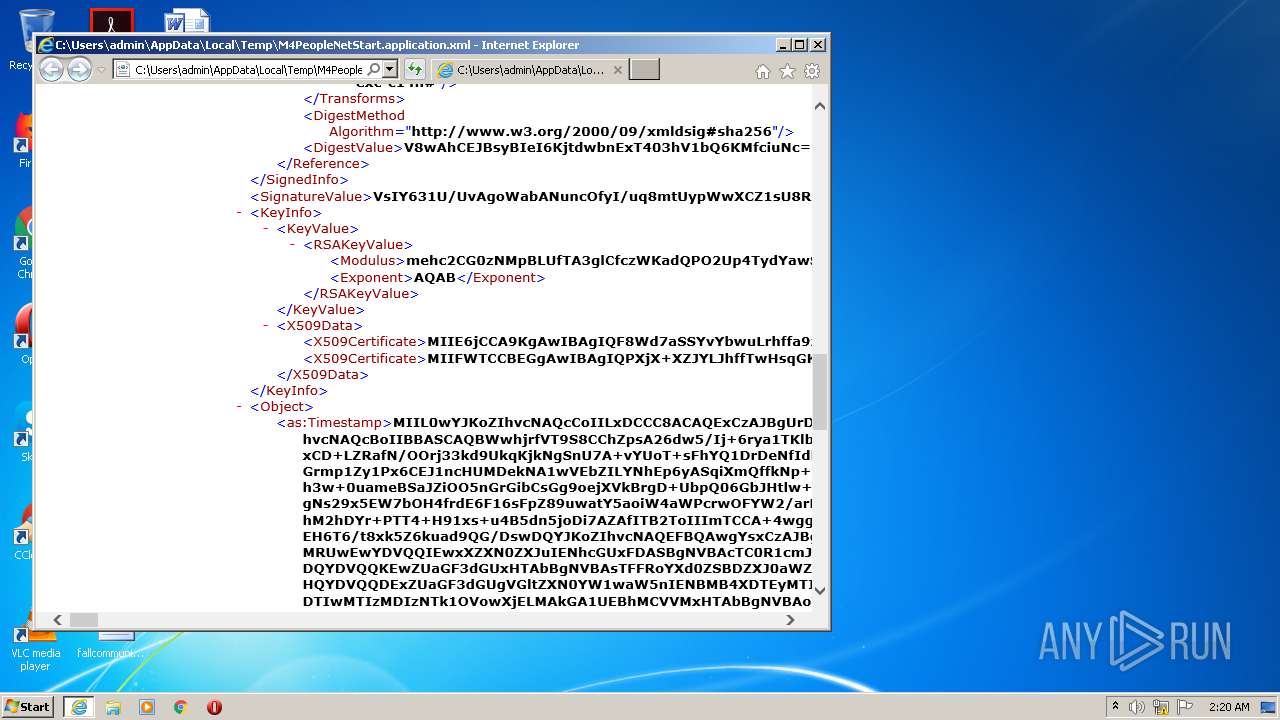
| AssemblySignatureSignedInfoReferenceDigestMethodAlgorithm: | http://www.w3.org/2000/09/xmldsig#sha256 |
| AssemblySignatureSignedInfoReferenceDigestValue: | Cb4sErAH6atRkzFHP3IBnQ0epgmJB+Mv0xOEEgDmJOE= |
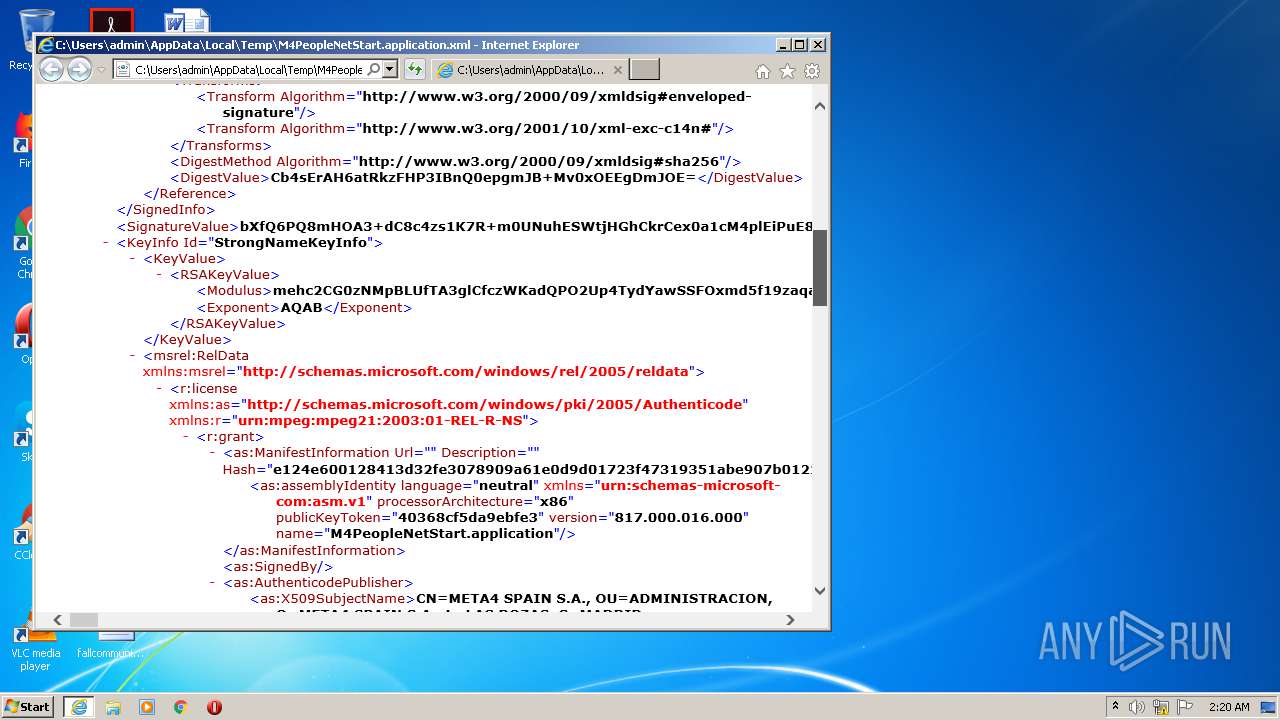
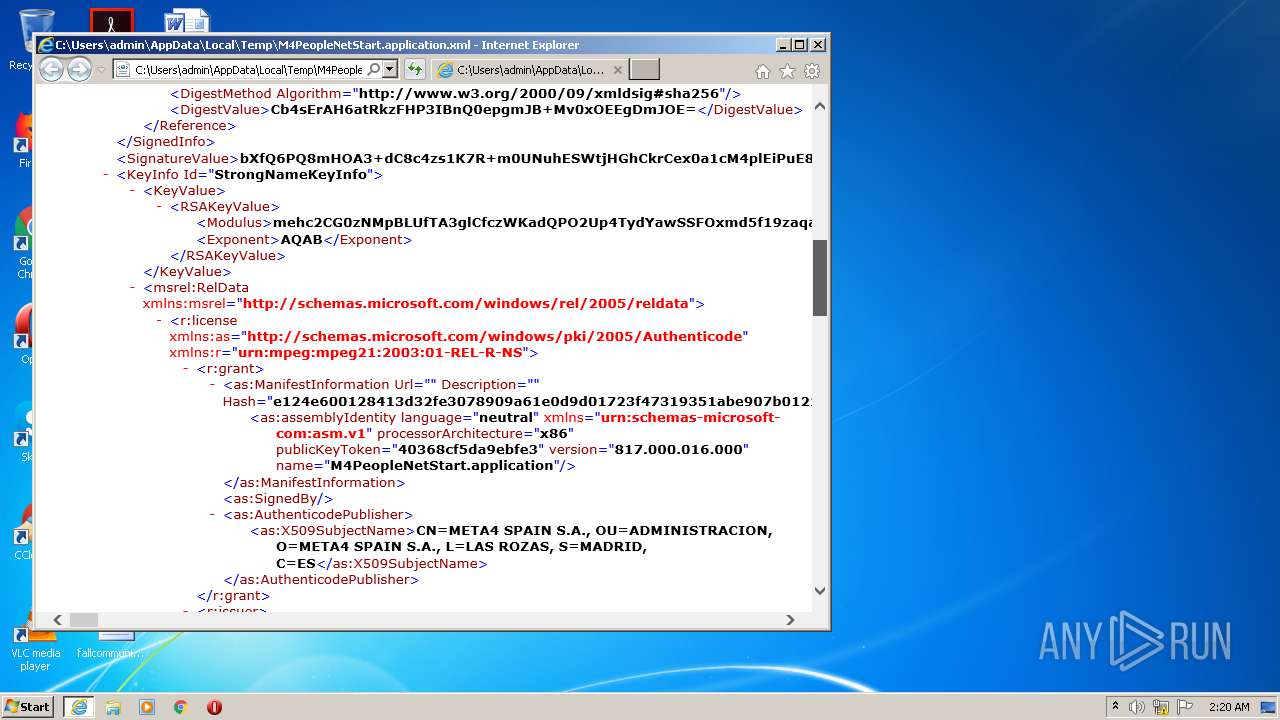
| AssemblySignatureSignatureValue: | bXfQ6PQ8mHOA3+dC8c4zs1K7R+m0UNuhESWtjHGhCkrCex0a1cM4plEiPuE8kn65aKvXt/S68l2SDAGllnRb/2vc+u+YtFHbqYZyW9GKtINKs9CMdy34zN/XqhRK2yRkhbJhBKkktBkf0+HPkJhgU9MjSACZ7lAJP6EjhCi20dUDliIfZY9MOs2dVqtfguDl8EIAEunm1ynlTEXUOOxbYs8VdOMurCJbvvHs9gte30378ya6TB/j5pTH0t2v8NxDzbVEKiIFYDIheMgOvfEIyUEH+A4X1k2lJnuTSJyKwuF59mS2OTCI39m5KkSAgTB+UWKrEyWCpQEBbLk5pnG2gA== |
| AssemblySignatureKeyInfoId: | StrongNameKeyInfo |
| AssemblySignatureKeyInfoKeyValueRSAKeyValueModulus: | mehc2CG0zNMpBLUfTA3glCfczWKadQPO2Up4TydYawSSFOxmd5f19zaqatTCAP6MzYvwkMVALgqzC29zalhCTLdSZdNJwg9IYDS3GJBUEpx/BmhTY385K5p1zF4BU/iBiCDrF8RbkVbxmGVshpW6/I40ii60oirwmbsQ7K+b8TrjfdMN/HtD6Q6IFY1p9muuo4Wkdup5i6v/9+nNsKrBpTV2BGhNP7vYxRldcEdTLXB7E7DyjJllpPvG+QfGAjue+0A6x6a19U9Ovhy02SD/EXW6RX5JJGjPhUWf2ora89BaeGW/tBPSNuARoKGZri8JYSmjhnIZLRncB452X8mghw== |
| AssemblySignatureKeyInfoKeyValueRSAKeyValueExponent: | AQAB |
| AssemblySignatureKeyInfoRelDataLicenseGrantManifestInformationHash: | e124e600128413d32fe3078909a61e0d9d01723f47319351abe907b0122cbe09 |
| AssemblySignatureKeyInfoRelDataLicenseGrantManifestInformationDescription: | - |
| AssemblySignatureKeyInfoRelDataLicenseGrantManifestInformationUrl: | - |
| AssemblySignatureKeyInfoRelDataLicenseGrantManifestInformationAssemblyIdentityName: | M4PeopleNetStart.application |
| AssemblySignatureKeyInfoRelDataLicenseGrantManifestInformationAssemblyIdentityVersion: | 817.000.016.000 |
| AssemblySignatureKeyInfoRelDataLicenseGrantManifestInformationAssemblyIdentityPublicKeyToken: | 40368cf5da9ebfe3 |
| AssemblySignatureKeyInfoRelDataLicenseGrantManifestInformationAssemblyIdentityLanguage: | neutral |
| AssemblySignatureKeyInfoRelDataLicenseGrantManifestInformationAssemblyIdentityProcessorArchitecture: | x86 |
| AssemblySignatureKeyInfoRelDataLicenseGrantManifestInformationAssemblyIdentityXmlns: | urn:schemas-microsoft-com:asm.v1 |
| AssemblySignatureKeyInfoRelDataLicenseGrantSignedBy: | - |
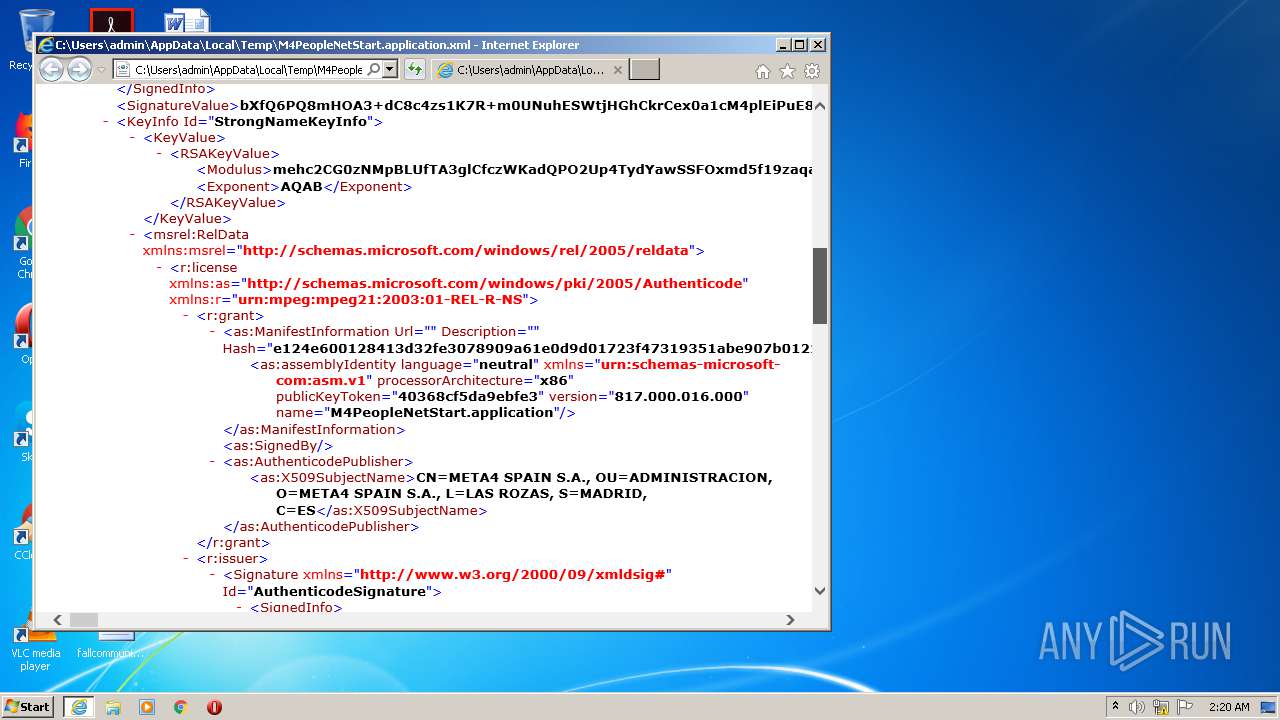
| AssemblySignatureKeyInfoRelDataLicenseGrantAuthenticodePublisherX509SubjectName: | CN=META4 SPAIN S.A., OU=ADMINISTRACION, O=META4 SPAIN S.A., L=LAS ROZAS, S=MADRID, C=ES |
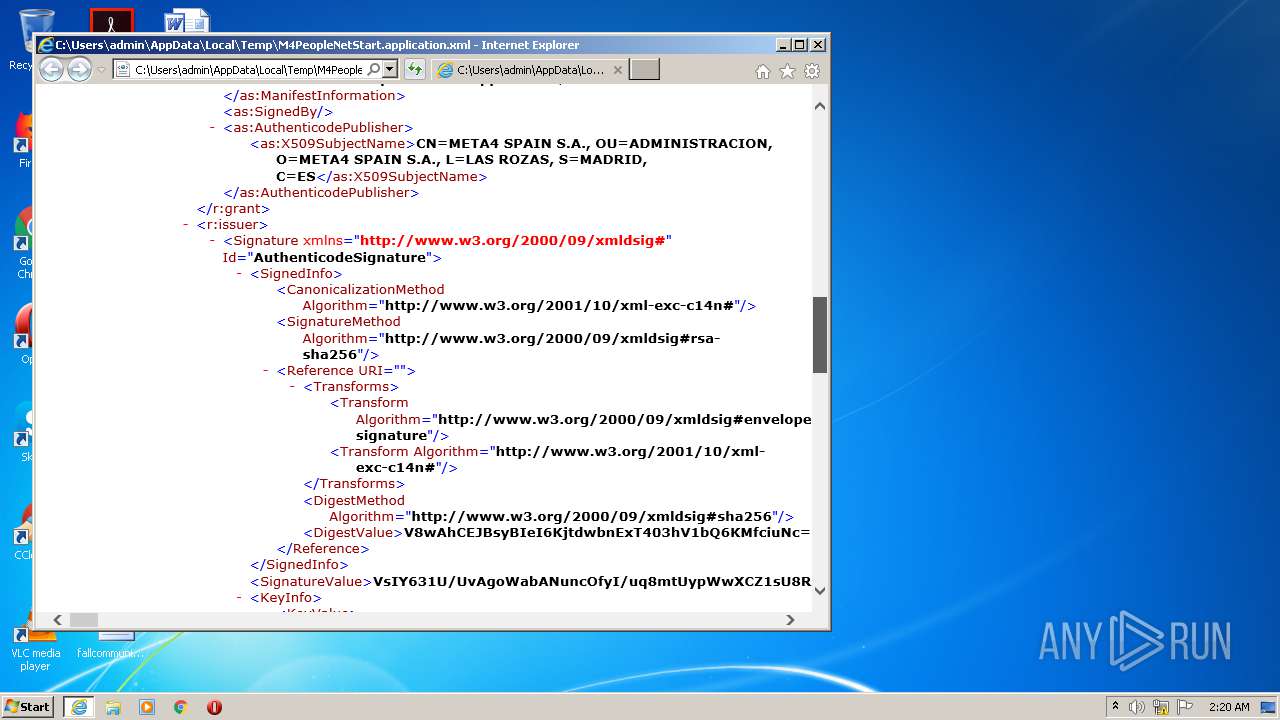
| AssemblySignatureKeyInfoRelDataLicenseIssuerSignatureId: | AuthenticodeSignature |
| AssemblySignatureKeyInfoRelDataLicenseIssuerSignatureXmlns: | http://www.w3.org/2000/09/xmldsig# |
| AssemblySignatureKeyInfoRelDataLicenseIssuerSignatureSignedInfoCanonicalizationMethodAlgorithm: | http://www.w3.org/2001/10/xml-exc-c14n# |
| AssemblySignatureKeyInfoRelDataLicenseIssuerSignatureSignedInfoSignatureMethodAlgorithm: | http://www.w3.org/2000/09/xmldsig#rsa-sha256 |
| AssemblySignatureKeyInfoRelDataLicenseIssuerSignatureSignedInfoReferenceUri: | - |
| AssemblySignatureKeyInfoRelDataLicenseIssuerSignatureSignedInfoReferenceTransformsTransformAlgorithm: | http://www.w3.org/2000/09/xmldsig#enveloped-signature |
| AssemblySignatureKeyInfoRelDataLicenseIssuerSignatureSignedInfoReferenceDigestMethodAlgorithm: | http://www.w3.org/2000/09/xmldsig#sha256 |
| AssemblySignatureKeyInfoRelDataLicenseIssuerSignatureSignedInfoReferenceDigestValue: | V8wAhCEJBsyBIeI6KjtdwbnExT403hV1bQ6KMfciuNc= |
| AssemblySignatureKeyInfoRelDataLicenseIssuerSignatureSignatureValue: | VsIY631U/UvAgoWabANuncOfyI/uq8mtUypWwXCZ1sU8RsQg/i2UWnzfzjq4995HfVJKio5DYEp1OwPr2FKE/rBYWENQ6w3jXyHYRkU206yhyhq5qdWctT8eghCdZ3B1DA3pDQNcFRG2SC2DYRKesgEqol5kH35DafrYZeAuH33X4Yd8PtLmpngUmiWYjjuZxqxomwrBoPaHo11ZAa4A/lG6UNOhmyR7ZcPi9JDm638XfIDbNvceRFu2zh+H63ROhderBaWfPbsGrWOWqIluGlj3K8DhWFtv2qy+KnSaNPm5hYTNoQ2K/j00+Ph/dcbPruAeXZ+Y6A4uwGQHyEwdkw== |
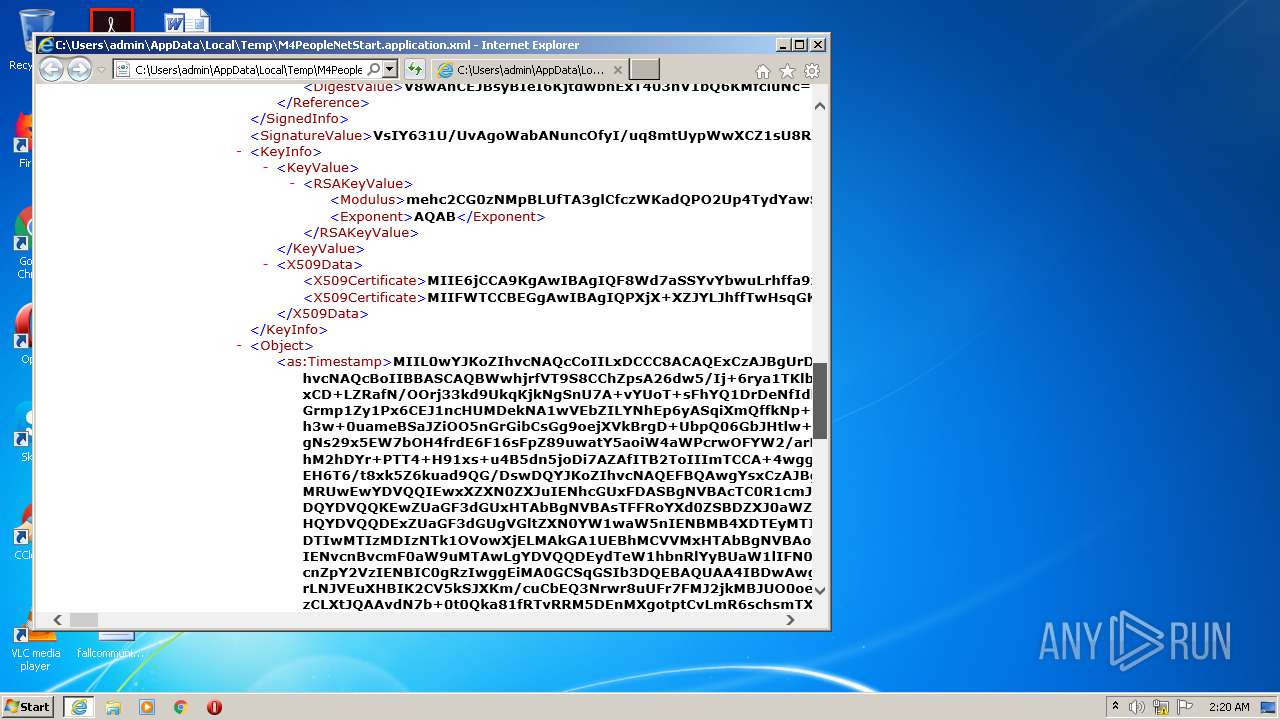
| AssemblySignatureKeyInfoRelDataLicenseIssuerSignatureKeyInfoKeyValueRSAKeyValueModulus: | mehc2CG0zNMpBLUfTA3glCfczWKadQPO2Up4TydYawSSFOxmd5f19zaqatTCAP6MzYvwkMVALgqzC29zalhCTLdSZdNJwg9IYDS3GJBUEpx/BmhTY385K5p1zF4BU/iBiCDrF8RbkVbxmGVshpW6/I40ii60oirwmbsQ7K+b8TrjfdMN/HtD6Q6IFY1p9muuo4Wkdup5i6v/9+nNsKrBpTV2BGhNP7vYxRldcEdTLXB7E7DyjJllpPvG+QfGAjue+0A6x6a19U9Ovhy02SD/EXW6RX5JJGjPhUWf2ora89BaeGW/tBPSNuARoKGZri8JYSmjhnIZLRncB452X8mghw== |
| AssemblySignatureKeyInfoRelDataLicenseIssuerSignatureKeyInfoKeyValueRSAKeyValueExponent: | AQAB |
| AssemblySignatureKeyInfoRelDataLicenseIssuerSignatureKeyInfoX509DataX509Certificate: | MIIE6jCCA9KgAwIBAgIQF8Wd7aSSYvYbwuLrhffa9zANBgkqhkiG9w0BAQsFADB/MQswCQYDVQQGEwJVUzEdMBsGA1UEChMUU3ltYW50ZWMgQ29ycG9yYXRpb24xHzAdBgNVBAsTFlN5bWFudGVjIFRydXN0IE5ldHdvcmsxMDAuBgNVBAMTJ1N5bWFudGVjIENsYXNzIDMgU0hBMjU2IENvZGUgU2lnbmluZyBDQTAeFw0xOTAyMjYwMDAwMDBaFw0yMjA0MTcyMzU5NTlaMIGBMQswCQYDVQQGEwJFUzEPMA0GA1UECAwGTUFEUklEMRIwEAYDVQQHDAlMQVMgUk9aQVMxGTAXBgNVBAoMEE1FVEE0IFNQQUlOIFMuQS4xFzAVBgNVBAsMDkFETUlOSVNUUkFDSU9OMRkwFwYDVQQDDBBNRVRBNCBTUEFJTiBTLkEuMIIBIjANBgkqhkiG9w0BAQEFAAOCAQ8AMIIBCgKCAQEAmehc2CG0zNMpBLUfTA3glCfczWKadQPO2Up4TydYawSSFOxmd5f19zaqatTCAP6MzYvwkMVALgqzC29zalhCTLdSZdNJwg9IYDS3GJBUEpx/BmhTY385K5p1zF4BU/iBiCDrF8RbkVbxmGVshpW6/I40ii60oirwmbsQ7K+b8TrjfdMN/HtD6Q6IFY1p9muuo4Wkdup5i6v/9+nNsKrBpTV2BGhNP7vYxRldcEdTLXB7E7DyjJllpPvG+QfGAjue+0A6x6a19U9Ovhy02SD/EXW6RX5JJGjPhUWf2ora89BaeGW/tBPSNuARoKGZri8JYSmjhnIZLRncB452X8mghwIDAQABo4IBXTCCAVkwCQYDVR0TBAIwADAOBgNVHQ8BAf8EBAMCB4AwKwYDVR0fBCQwIjAgoB6gHIYaaHR0cDovL3N2LnN5bWNiLmNvbS9zdi5jcmwwYQYDVR0gBFowWDBWBgZngQwBBAEwTDAjBggrBgEFBQcCARYXaHR0cHM6Ly9kLnN5bWNiLmNvbS9jcHMwJQYIKwYBBQUHAgIwGQwXaHR0cHM6Ly9kLnN5bWNiLmNvbS9ycGEwEwYDVR0lBAwwCgYIKwYBBQUHAwMwVwYIKwYBBQUHAQEESzBJMB8GCCsGAQUFBzABhhNodHRwOi8vc3Yuc3ltY2QuY29tMCYGCCsGAQUFBzAChhpodHRwOi8vc3Yuc3ltY2IuY29tL3N2LmNydDAfBgNVHSMEGDAWgBSWO1PweTOXr32D7y4rzMq3hh5yZjAdBgNVHQ4EFgQUN1zEdXfB3u8c6lCugDgba9kR46MwDQYJKoZIhvcNAQELBQADggEBAFfdr5bDvSqw2U+QSWGaPYrdQII6yMbYeaw5L+1j7F++gvhtTQhYK6/QZnCTVM0LTOd3/s4T9jbe677kkfMSLD61tXOUxFh89395DUJkwuIQa1QRcjh6Kpvhk0xH9oiFApaUT0YhbroMWxx67cIe9JJNFD5E2eJxojY//M1dwyS45p6HeXIgpwlFkqEbSQyY51Ggk4prpM/LYIYhr2uifoy9CoDBCM9cAJtL5wVNNzzxM8R3v3EZBwwZO4IdmMJy+Rz3ip9E7UNt4teMg4Wi5eudXoiaOhwfozq7q028fMa05o9ZVIoyGRD2YY7jdPXC/mvGp4wSxYhm+NT/TlYMi3M= |
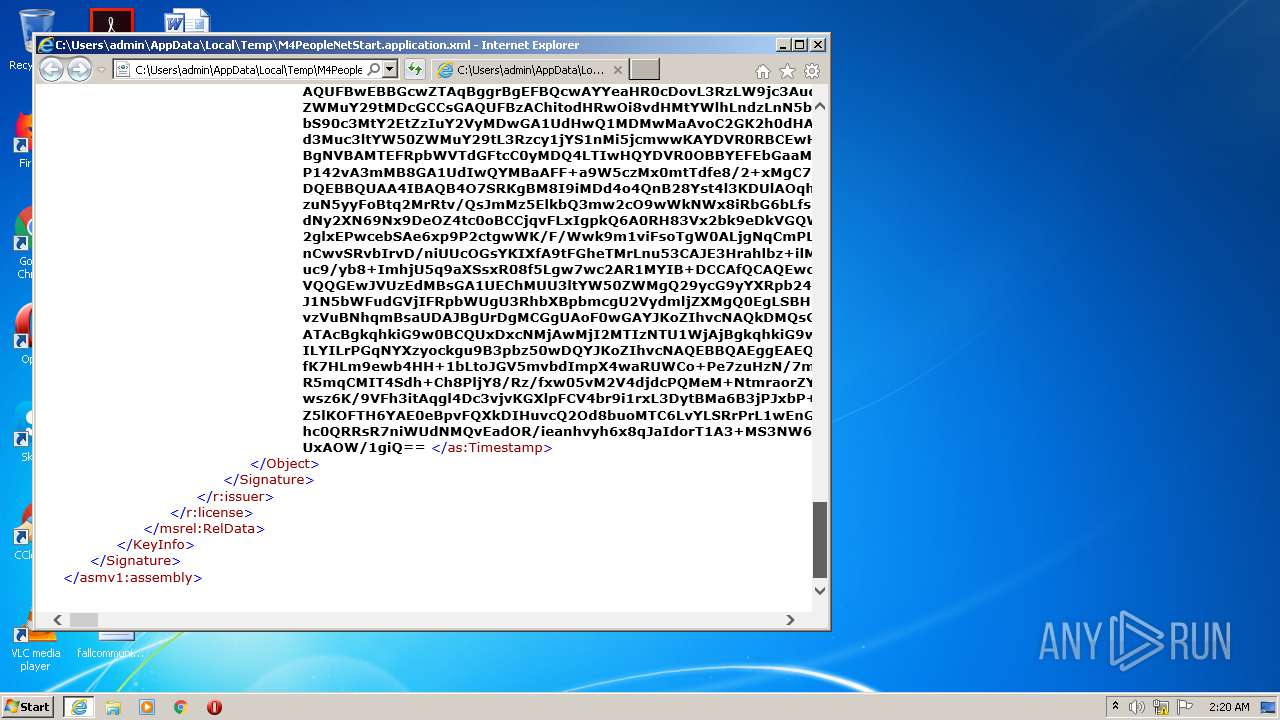
| AssemblySignatureKeyInfoRelDataLicenseIssuerSignatureObjectTimestamp: | MIIL0wYJKoZIhvcNAQcCoIILxDCCC8ACAQExCzAJBgUrDgMCGgUAMIIBEwYJKoZI hvcNAQcBoIIBBASCAQBWwhjrfVT9S8CChZpsA26dw5/Ij+6rya1TKlbBcJnWxTxG xCD+LZRafN/OOrj33kd9UkqKjkNgSnU7A+vYUoT+sFhYQ1DrDeNfIdhGRTbTrKHK Grmp1Zy1Px6CEJ1ncHUMDekNA1wVEbZILYNhEp6yASqiXmQffkNp+thl4C4ffdfh h3w+0uameBSaJZiOO5nGrGibCsGg9oejXVkBrgD+UbpQ06GbJHtlw+L0kObrfxd8 gNs29x5EW7bOH4frdE6F16sFpZ89uwatY5aoiW4aWPcrwOFYW2/arL4qdJo0+bmF hM2hDYr+PTT4+H91xs+u4B5dn5joDi7AZAfITB2ToIIImTCCA+4wggNXoAMCAQIC EH6T6/t8xk5Z6kuad9QG/DswDQYJKoZIhvcNAQEFBQAwgYsxCzAJBgNVBAYTAlpB MRUwEwYDVQQIEwxXZXN0ZXJuIENhcGUxFDASBgNVBAcTC0R1cmJhbnZpbGxlMQ8w DQYDVQQKEwZUaGF3dGUxHTAbBgNVBAsTFFRoYXd0ZSBDZXJ0aWZpY2F0aW9uMR8w HQYDVQQDExZUaGF3dGUgVGltZXN0YW1waW5nIENBMB4XDTEyMTIyMTAwMDAwMFoX DTIwMTIzMDIzNTk1OVowXjELMAkGA1UEBhMCVVMxHTAbBgNVBAoTFFN5bWFudGVj IENvcnBvcmF0aW9uMTAwLgYDVQQDEydTeW1hbnRlYyBUaW1lIFN0YW1waW5nIFNl cnZpY2VzIENBIC0gRzIwggEiMA0GCSqGSIb3DQEBAQUAA4IBDwAwggEKAoIBAQCx rLNJVEuXHBIK2CV5kSJXKm/cuCbEQ3Nrwr8uUFr7FMJ2jkMBJUO0oeJF9Oi3e8N0 zCLXtJQAAvdN7b+0t0Qka81fRTvRRM5DEnMXgotptCvLmR6schsmTXEfsTHd+1Fh AlOmqvVJLAV4RaUvic7nmef+jOJXPz3GktxK+Hsz5HkK+/B1iEGc/8UDUZmq12yf k2mHZSmDhcJgFMTIyTsU2sCB8B8NdN6SIqvK9/t0fCfm90obf6fDni2uiuqm5qon Fn1h95hxEbziUKFL5V365Q6nLJ+qZSDT2JboyHylTkhE/xniRAeSC9dohIBdanhk Rc1gRn5UwRN8xXnxycFxAgMBAAGjgfowgfcwHQYDVR0OBBYEFF+a9W5czMx0mtTd fe8/2+xMgC7dMDIGCCsGAQUFBwEBBCYwJDAiBggrBgEFBQcwAYYWaHR0cDovL29j c3AudGhhd3RlLmNvbTASBgNVHRMBAf8ECDAGAQH/AgEAMD8GA1UdHwQ4MDYwNKAy oDCGLmh0dHA6Ly9jcmwudGhhd3RlLmNvbS9UaGF3dGVUaW1lc3RhbXBpbmdDQS5j cmwwEwYDVR0lBAwwCgYIKwYBBQUHAwgwDgYDVR0PAQH/BAQDAgEGMCgGA1UdEQQh MB+kHTAbMRkwFwYDVQQDExBUaW1lU3RhbXAtMjA0OC0xMA0GCSqGSIb3DQEBBQUA A4GBAAMJm495739ZMKrvaLX64wkdu0+CBl03X6ZSnxaN6hySCURu9W3rWHww6Plp jSNzCxJvR6muORH4KrGbsBrDjutZlgCtzgxNstAxpghcKnr84nodV0yoZRjpeUBi JZZux8c3aoMhCI5B6t3ZVz8dd0mHKhYGXqY4aiISo1EZg362MIIEozCCA4ugAwIB AgIQDs/0OMj+vzVuBNhqmBsaUDANBgkqhkiG9w0BAQUFADBeMQswCQYDVQQGEwJV UzEdMBsGA1UEChMUU3ltYW50ZWMgQ29ycG9yYXRpb24xMDAuBgNVBAMTJ1N5bWFu dGVjIFRpbWUgU3RhbXBpbmcgU2VydmljZXMgQ0EgLSBHMjAeFw0xMjEwMTgwMDAw MDBaFw0yMDEyMjkyMzU5NTlaMGIxCzAJBgNVBAYTAlVTMR0wGwYDVQQKExRTeW1h bnRlYyBDb3Jwb3JhdGlvbjE0MDIGA1UEAxMrU3ltYW50ZWMgVGltZSBTdGFtcGlu ZyBTZXJ2aWNlcyBTaWduZXIgLSBHNDCCASIwDQYJKoZIhvcNAQEBBQADggEPADCC AQoCggEBAKJjCzlEuLsjp0RJuw7/ofBhClOTsJjbrSwPSsVu/4Y8U1UPFc4EPyv9 qZaW2b5heQtbyUyGduXgQ0sile7CK0PBn9hotI5AT+6FOLkRxSPyZFjwFTJvTleh roikAtcqHs1L4d1j1ReJMluwXplaqJ0oUA4X7pbbYTtFUR3PElYLkkf8q672Zj1H rHBy55LnX80QucSDZJQZvSWA4ejSIqXQugJ6oXeTW2XD7hd0vEGGKtwITIySjJEt nndEH2jWqHR32w5bMotWizO92WPISZ06xcXqMwvS8aMb9Iu+2bNXizveBKd6IrIk ri7HcMW+ToMmCPsLvalPmQjhEChyqs0CAwEAAaOCAVcwggFTMAwGA1UdEwEB/wQC MAAwFgYDVR0lAQH/BAwwCgYIKwYBBQUHAwgwDgYDVR0PAQH/BAQDAgeAMHMGCCsG AQUFBwEBBGcwZTAqBggrBgEFBQcwAYYeaHR0cDovL3RzLW9jc3Aud3Muc3ltYW50 ZWMuY29tMDcGCCsGAQUFBzAChitodHRwOi8vdHMtYWlhLndzLnN5bWFudGVjLmNv bS90c3MtY2EtZzIuY2VyMDwGA1UdHwQ1MDMwMaAvoC2GK2h0dHA6Ly90cy1jcmwu d3Muc3ltYW50ZWMuY29tL3Rzcy1jYS1nMi5jcmwwKAYDVR0RBCEwH6QdMBsxGTAX BgNVBAMTEFRpbWVTdGFtcC0yMDQ4LTIwHQYDVR0OBBYEFEbGaaMOShQe1UzaUmMX P142vA3mMB8GA1UdIwQYMBaAFF+a9W5czMx0mtTdfe8/2+xMgC7dMA0GCSqGSIb3 DQEBBQUAA4IBAQB4O7SRKgBM8I9iMDd4o4QnB28Yst4l3KDUlAOqhk4ln5pAAxzd zuN5yyFoBtq2MrRtv/QsJmMz5ElkbQ3mw2cO9wWkNWx8iRbG6bLfsundIMZxD82V dNy2XN69Nx9DeOZ4tc0oBCCjqvFLxIgpkQ6A0RH83Vx2bk9eDkVGQW4NsOo4mrE6 2glxEPwcebSAe6xp9P2ctgwWK/F/Wwk9m1viFsoTgW0ALjgNqCmPLOGy9FqpAa8V nCwvSRvbIrvD/niUUcOGsYKIXfA9tFGheTMrLnu53CAJE3Hrahlbz+ilMFcsiUk/ uc9/yb8+ImhjU5q9aXSsxR08f5Lgw7wc2AR1MYIB+DCCAfQCAQEwcjBeMQswCQYD VQQGEwJVUzEdMBsGA1UEChMUU3ltYW50ZWMgQ29ycG9yYXRpb24xMDAuBgNVBAMT J1N5bWFudGVjIFRpbWUgU3RhbXBpbmcgU2VydmljZXMgQ0EgLSBHMgIQDs/0OMj+ vzVuBNhqmBsaUDAJBgUrDgMCGgUAoF0wGAYJKoZIhvcNAQkDMQsGCSqGSIb3DQEH ATAcBgkqhkiG9w0BCQUxDxcNMjAwMjI2MTIzNTU1WjAjBgkqhkiG9w0BCQQxFgQU ILYILrPGqNYXzyockgu9B3pbz50wDQYJKoZIhvcNAQEBBQAEggEAEQFkCbaBBqlF fK7HLm9ewb4HH+1bLtoJGV5mvbdImpX4waRUWCo+Pe7zuHzN/7mA9cxfLFneDo6h R5mqCMIT4Sdh+Ch8PljY8/Rz/fxw05vM2V4djdcPQMeM+NtmraorZY2fWdPNJJt1 wsz6K/9VFh3itAqgl4Dc3vjvKGXlpFCV4br9i1rxL3DytBMa6B3jPJxbP+BDPvyf Z5lKOFTH6YAE0eBpvFQXkDIHuvcQ2Od8buoMTC6LvYLSRrPrL1wEnGLHgXl/2wpR hc0QRRsR7niWUdNMQvEadOR/ieanhvyh6x8qJaIdorT1A3+MS3NW67XbCoJcjTkt UxAOW/1giQ== |
Total processes
42
Monitored processes
4
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 656 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:1144 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | — | iexplore.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 1144 | "C:\Program Files\Internet Explorer\iexplore.exe" -nohome | C:\Program Files\Internet Explorer\iexplore.exe | MSOXMLED.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2580 | "C:\Program Files\Common Files\Microsoft Shared\OFFICE14\MSOXMLED.EXE" /verb open "C:\Users\admin\AppData\Local\Temp\M4PeopleNetStart.application.xml" | C:\Program Files\Common Files\Microsoft Shared\OFFICE14\MSOXMLED.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: XML Editor Exit code: 0 Version: 14.0.4750.1000 Modules
| |||||||||||||||
| 3372 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:1144 CREDAT:78849 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
1 433
Read events
1 312
Write events
118
Delete events
3
Modification events
| (PID) Process: | (2580) MSOXMLED.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (2580) MSOXMLED.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2580) MSOXMLED.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (1144) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: 3607001656 | |||
| (PID) Process: | (1144) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30839714 | |||
| (PID) Process: | (1144) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (1144) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (1144) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (1144) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (1144) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
Executable files
0
Suspicious files
10
Text files
4
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1144 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 1144 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Cab57EA.tmp | — | |
MD5:— | SHA256:— | |||
| 1144 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Tar57EB.tmp | — | |
MD5:— | SHA256:— | |||
| 1144 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\VersionManager\ver580C.tmp | — | |
MD5:— | SHA256:— | |||
| 3372 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\CabC3D3.tmp | — | |
MD5:— | SHA256:— | |||
| 3372 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\TarC3D4.tmp | — | |
MD5:— | SHA256:— | |||
| 1144 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF49FA377FDC9D7578.TMP | — | |
MD5:— | SHA256:— | |||
| 1144 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\MT3NOZI2.txt | — | |
MD5:— | SHA256:— | |||
| 1144 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\XPL2J6BT.txt | — | |
MD5:— | SHA256:— | |||
| 1144 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\Active\{02BD7755-FF96-11EA-8C46-12A9866C77DE}.dat | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
11
DNS requests
11
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1144 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8sEMlbBsCTf7jUSfg%2BhWk%3D | US | der | 1.47 Kb | whitelisted |
1144 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8sEMlbBsCTf7jUSfg%2BhWk%3D | US | der | 1.47 Kb | whitelisted |
1144 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8sEMlbBsCTf7jUSfg%2BhWk%3D | US | der | 1.47 Kb | whitelisted |
1144 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1144 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
1144 | iexplore.exe | 152.199.19.161:443 | iecvlist.microsoft.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
1144 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3372 | iexplore.exe | 152.199.19.161:443 | iecvlist.microsoft.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
1144 | iexplore.exe | 204.79.197.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
iecvlist.microsoft.com |
| whitelisted |
r20swj13mr.microsoft.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
ieonline.microsoft.com |
| whitelisted |
dns.msftncsi.com |
| shared |