| File name: | image.png |
| Full analysis: | https://app.any.run/tasks/d06f0977-c259-41d4-9c2f-9a219f7420fe |
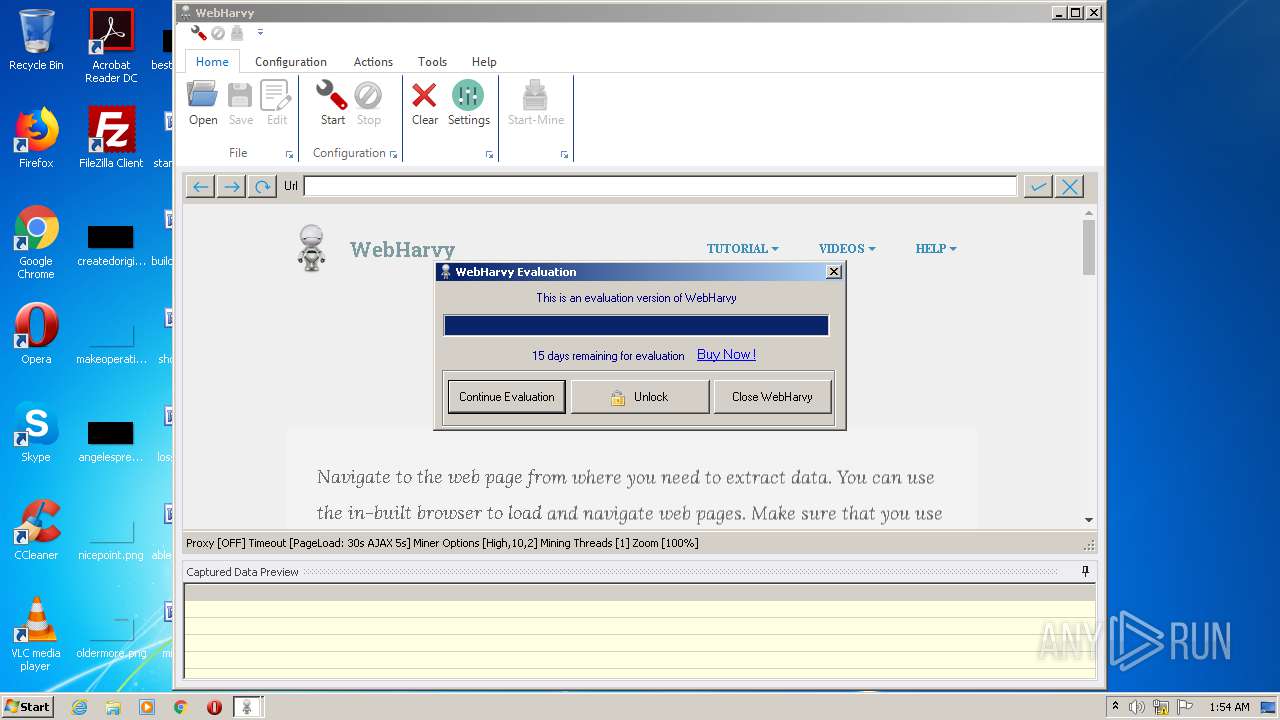
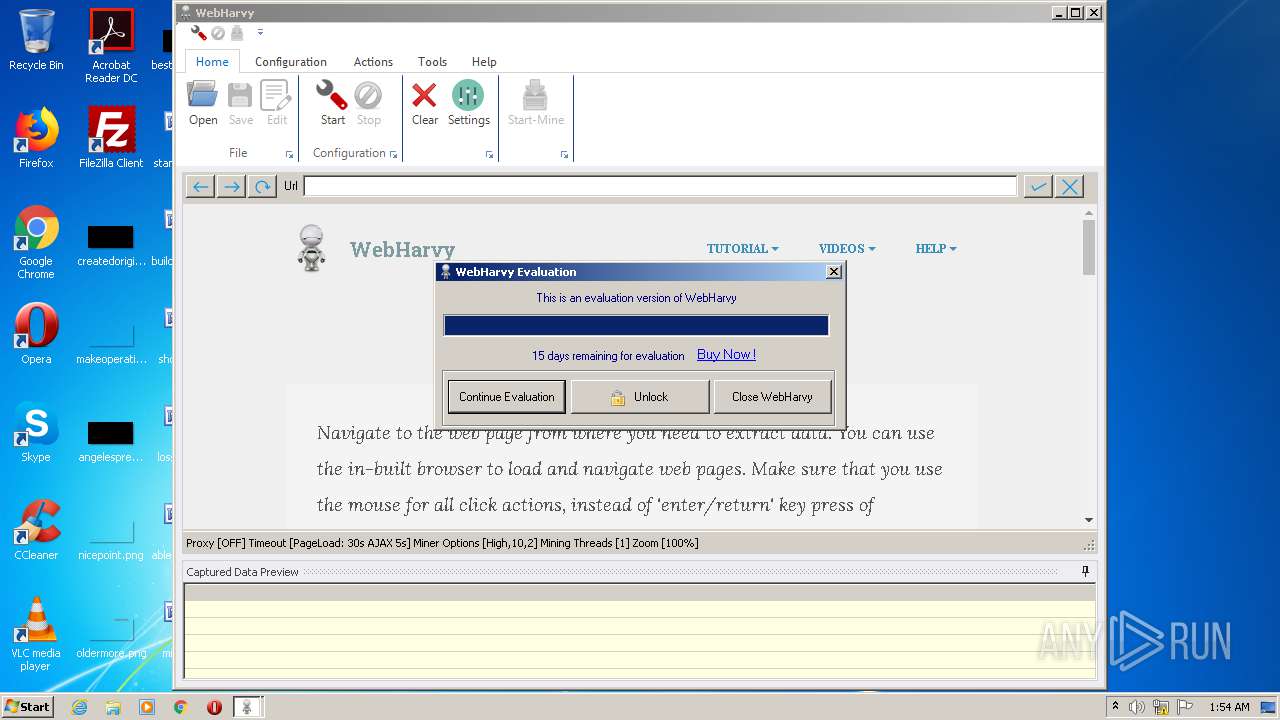
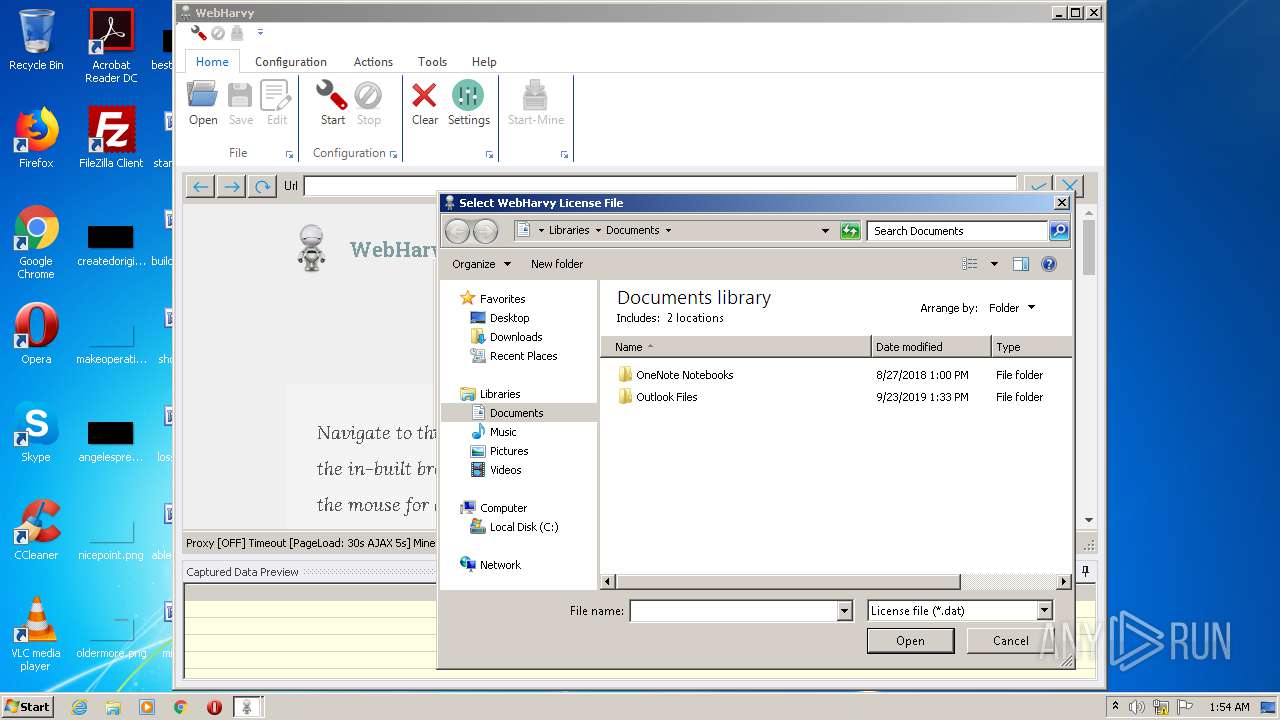
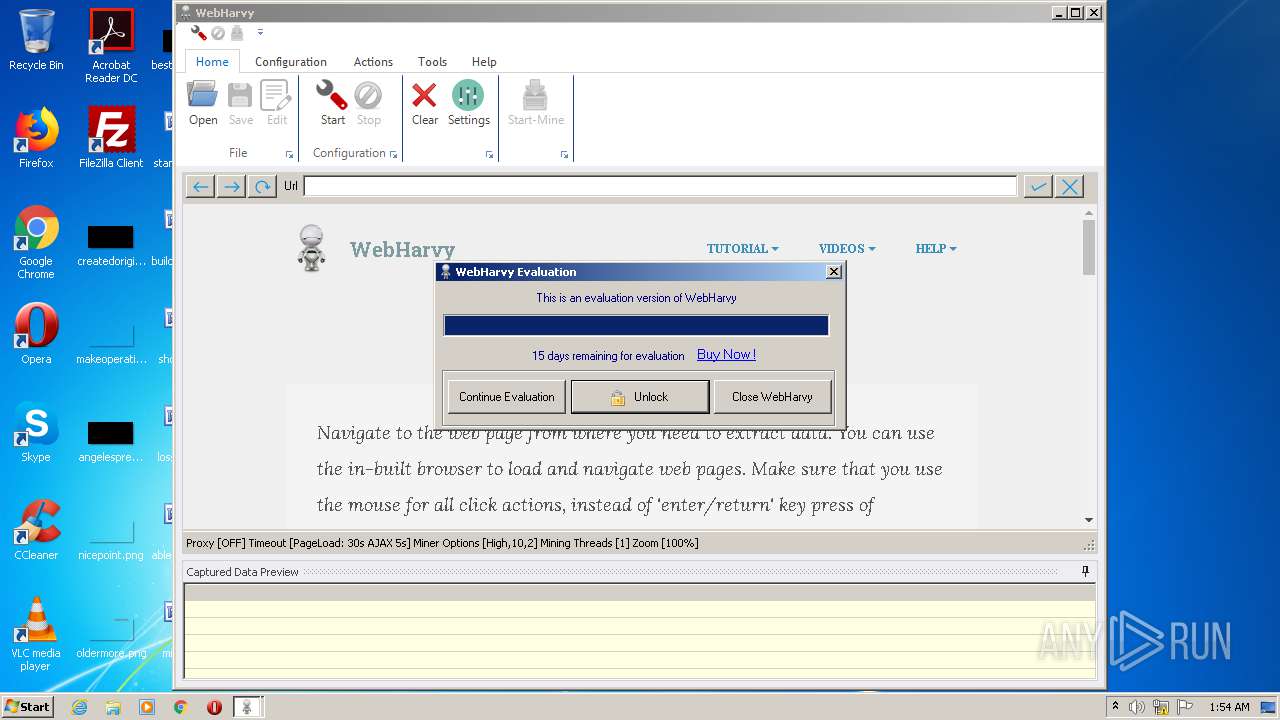
| Verdict: | Malicious activity |
| Analysis date: | August 24, 2020, 00:51:07 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | image/png |
| File info: | PNG image data, 690 x 310, 8-bit/color RGBA, non-interlaced |
| MD5: | D561D27276493DBD72F32F9CF01F9A96 |
| SHA1: | 21F5579AA37AD99B4D0810708BE56DFB84F5E6BB |
| SHA256: | 5DEC9464DBE1DCDC96D546AA27CFA5B1AA1A1DD0974DB8234E99534C7A28231D |
| SSDEEP: | 768:unVaCA6tY15jFPT/iTK5IRw5VQcBmnVkyFYC6oGLHJWbKDgERI0S+pswISX72fWw:utqftT/iTtRw5bBmnVkT6GjJWbull/pc |
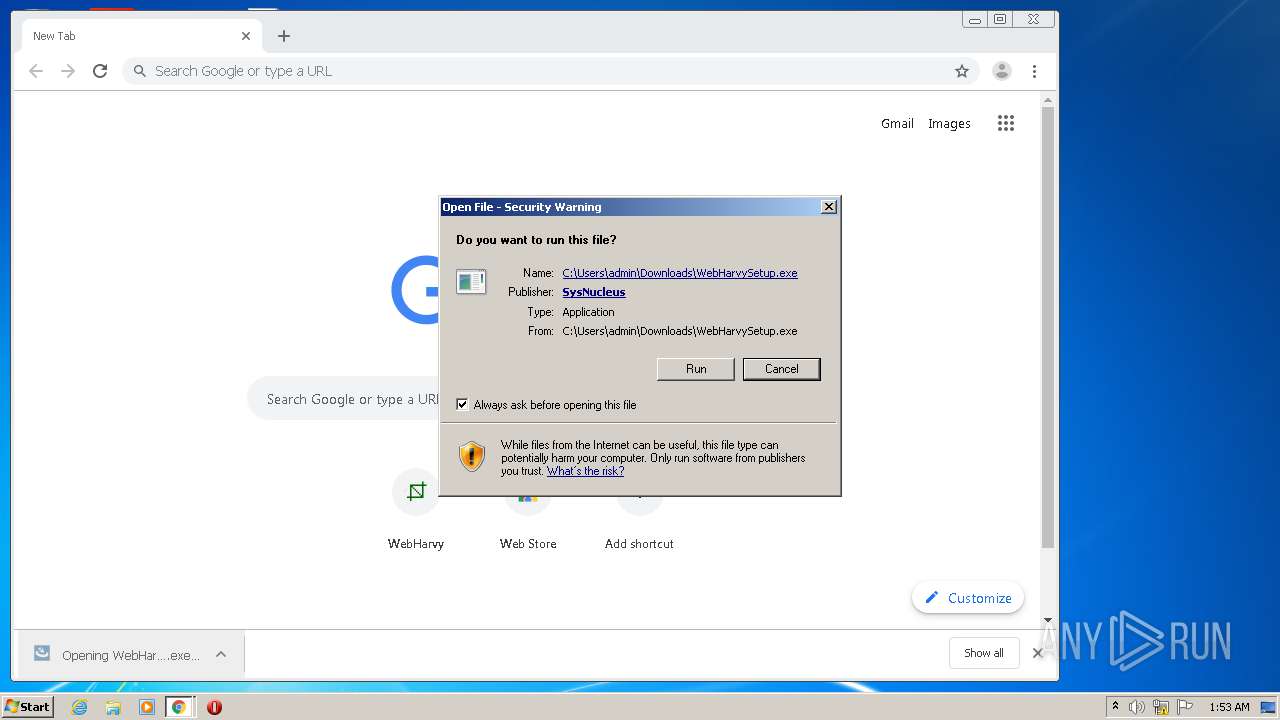
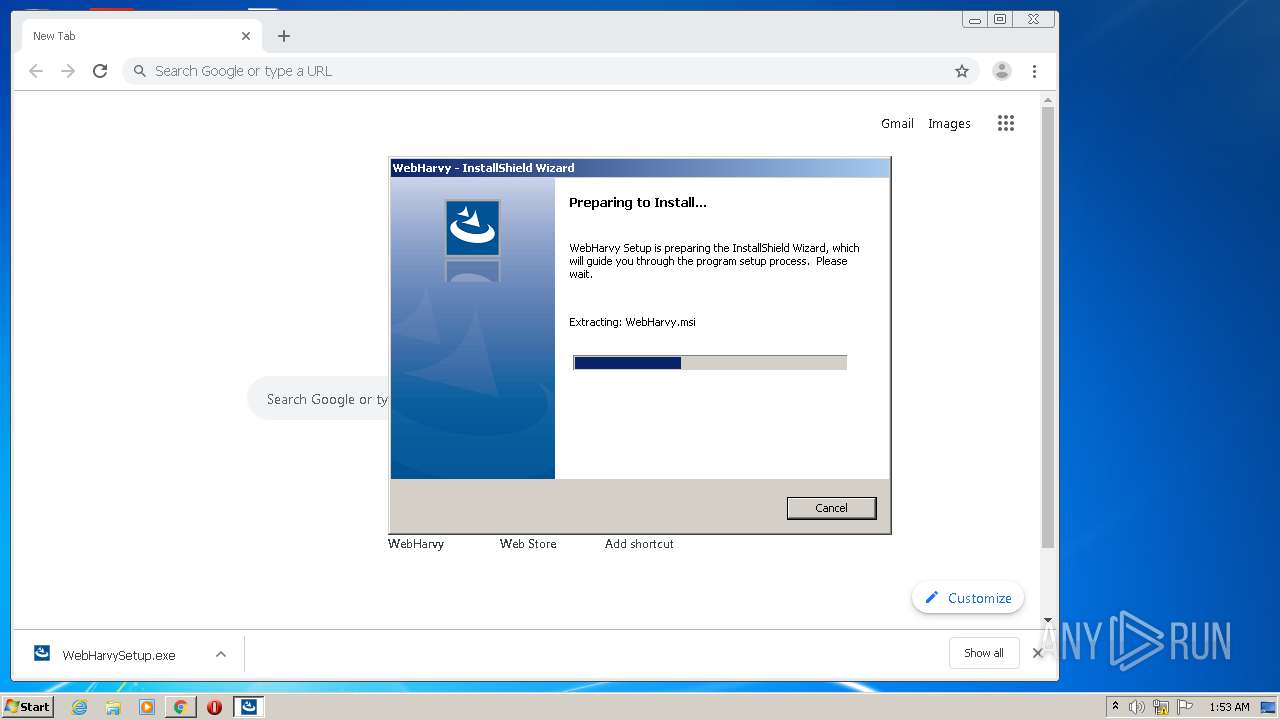
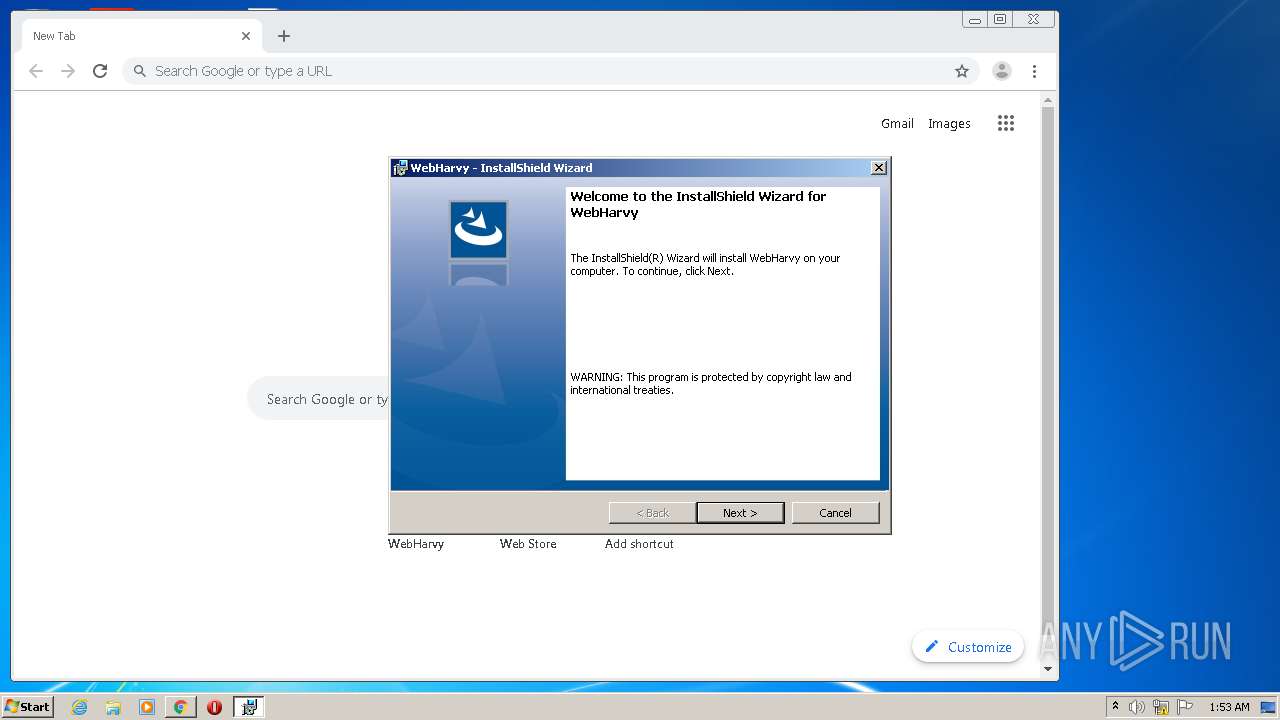
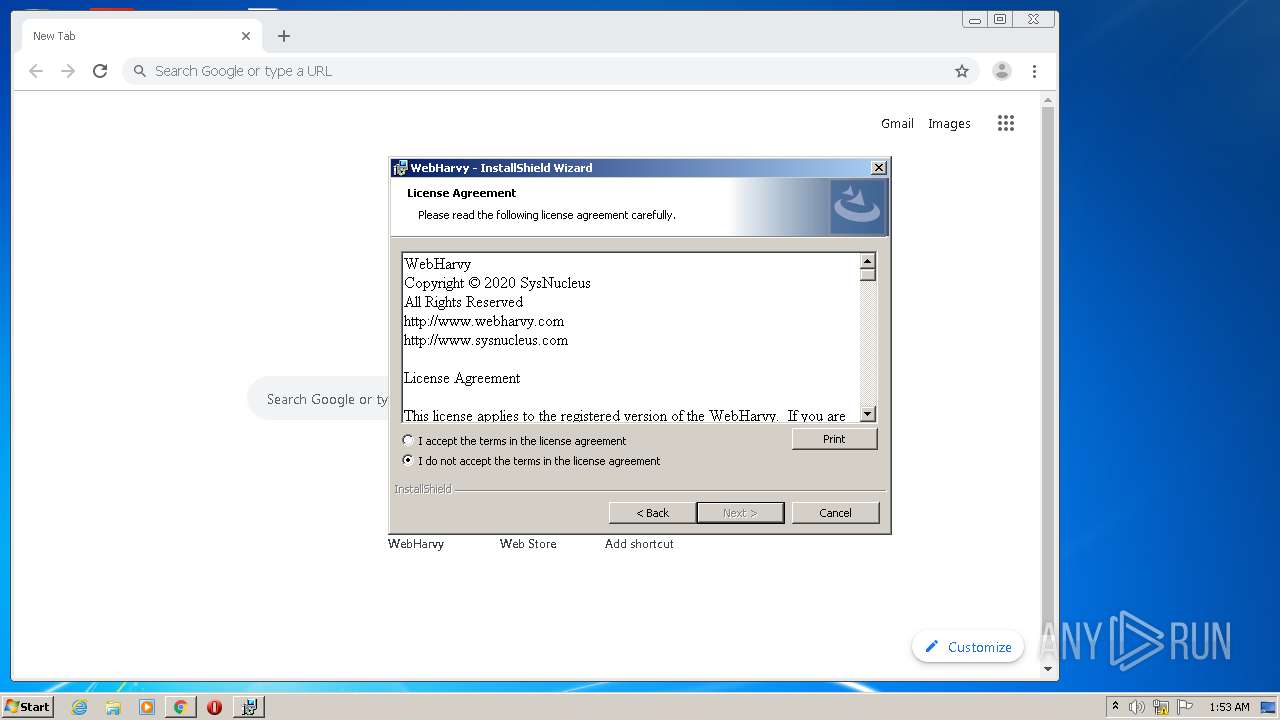
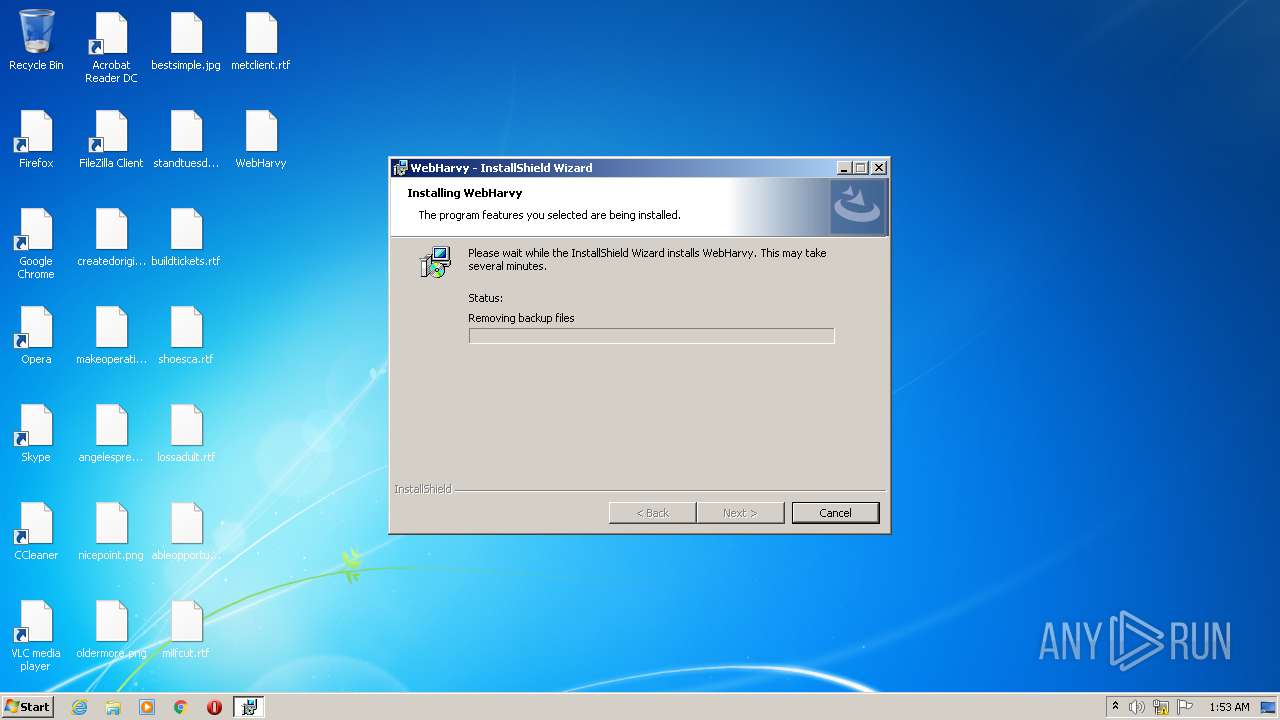
MALICIOUS
Application was dropped or rewritten from another process
- WebHarvySetup.exe (PID: 3828)
- eowp.exe (PID: 1736)
- eowp.exe (PID: 3808)
- WebHarvySetup.exe (PID: 3956)
- WebHarvy.exe (PID: 556)
- eowp.exe (PID: 2416)
- eowp.exe (PID: 2604)
- eowp.exe (PID: 2888)
- eowp.exe (PID: 2608)
- eowp.exe (PID: 2132)
- WebHarvy.exe (PID: 2076)
- eowp.exe (PID: 3944)
- eowp.exe (PID: 3940)
- eowp.exe (PID: 2936)
- eowp.exe (PID: 2540)
- eowp.exe (PID: 3520)
- eowp.exe (PID: 1868)
- eowp.exe (PID: 3732)
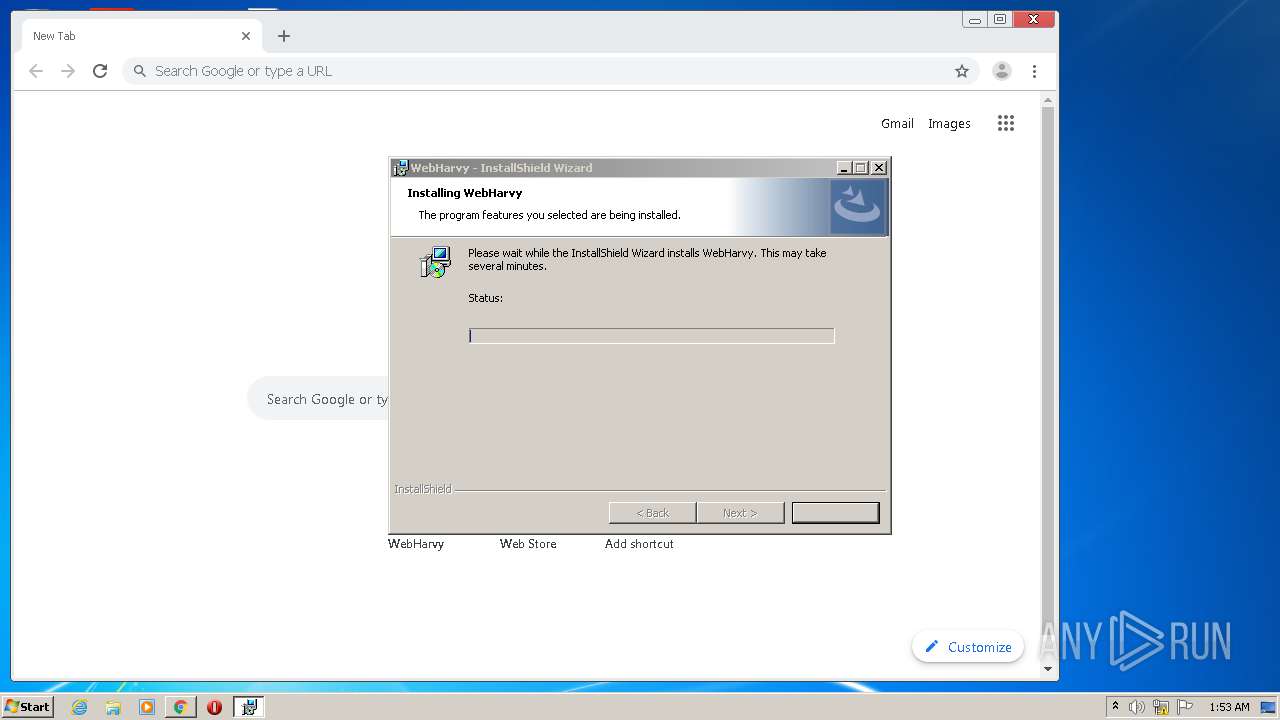
Loads dropped or rewritten executable
- WebHarvy.exe (PID: 556)
- eowp.exe (PID: 1736)
- eowp.exe (PID: 2888)
- eowp.exe (PID: 2416)
- eowp.exe (PID: 2132)
- eowp.exe (PID: 2604)
- WebHarvy.exe (PID: 2076)
- eowp.exe (PID: 3944)
- eowp.exe (PID: 3940)
- eowp.exe (PID: 3520)
- eowp.exe (PID: 3732)
- eowp.exe (PID: 2936)
- eowp.exe (PID: 2540)
- eowp.exe (PID: 1868)
- eowp.exe (PID: 3808)
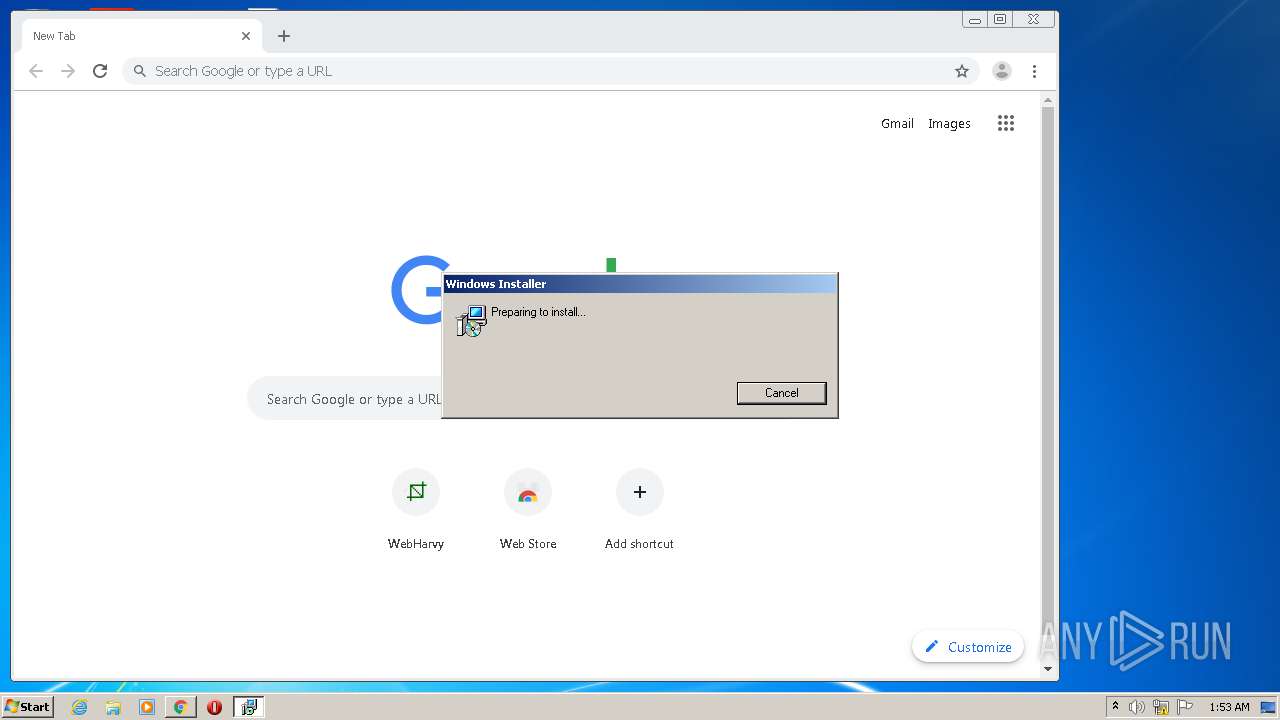
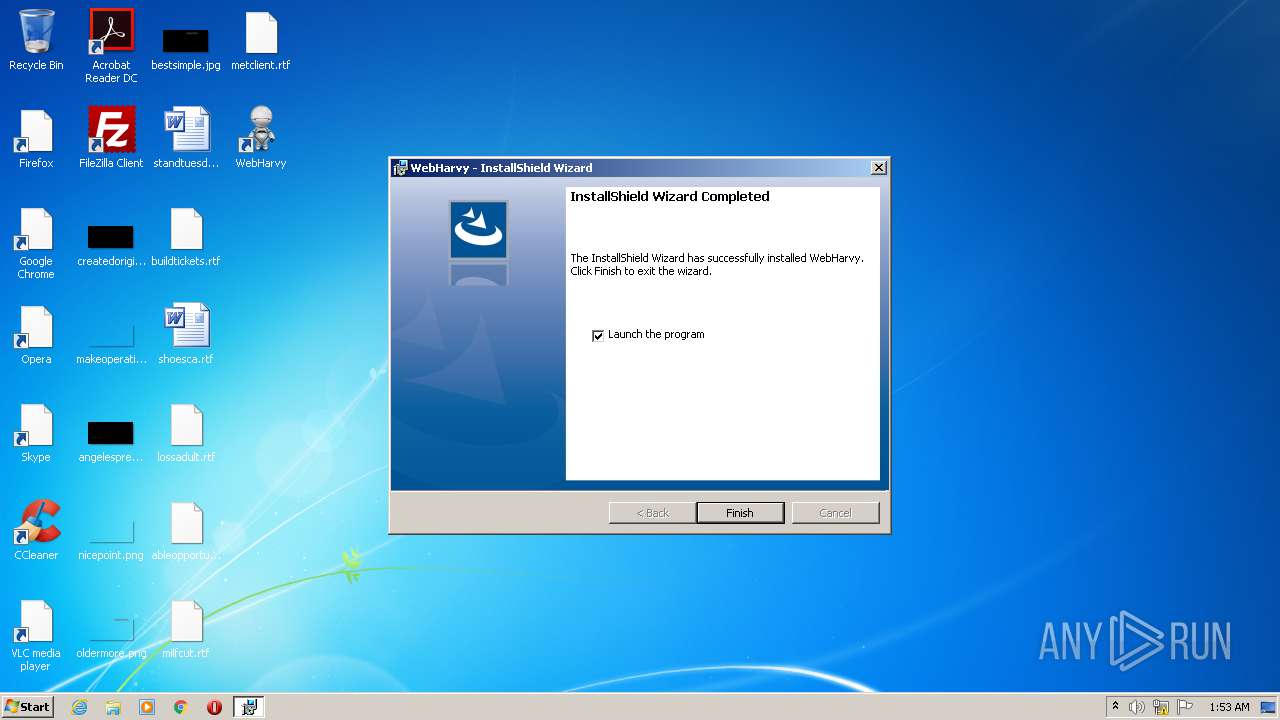
SUSPICIOUS
Executable content was dropped or overwritten
- chrome.exe (PID: 3800)
- MSIEXEC.EXE (PID: 4040)
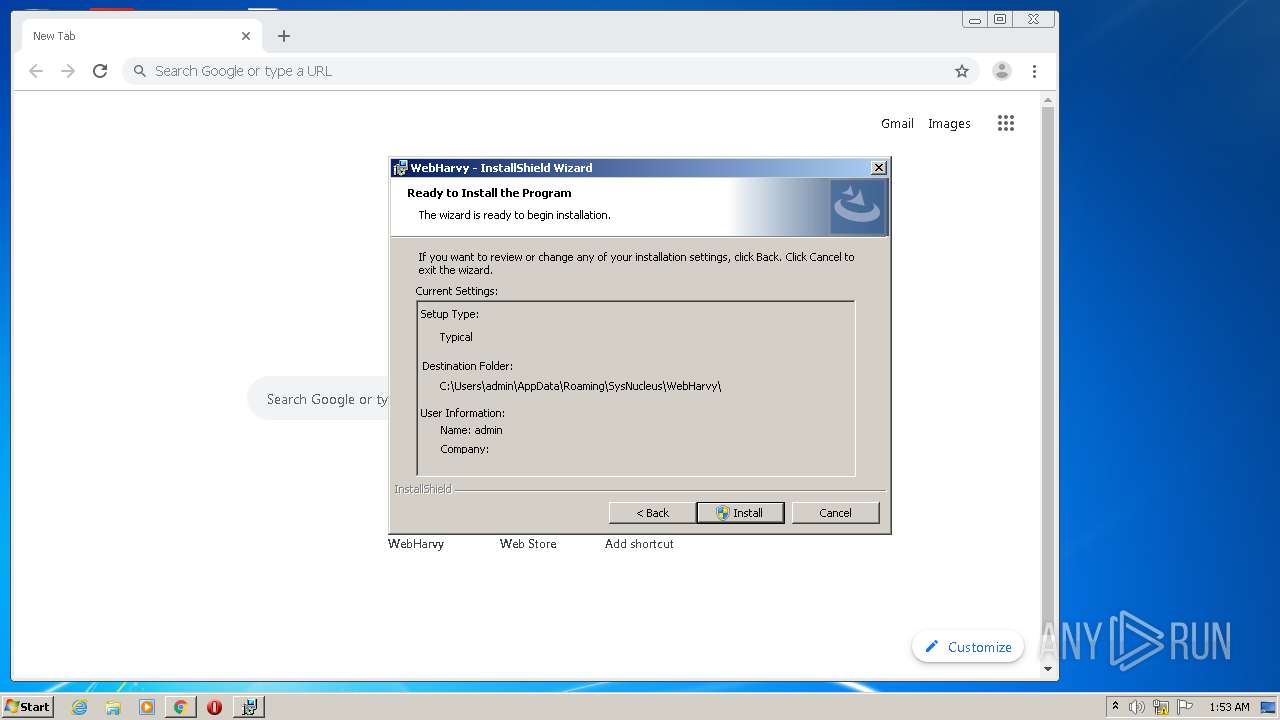
Starts itself from another location
- WebHarvySetup.exe (PID: 3828)
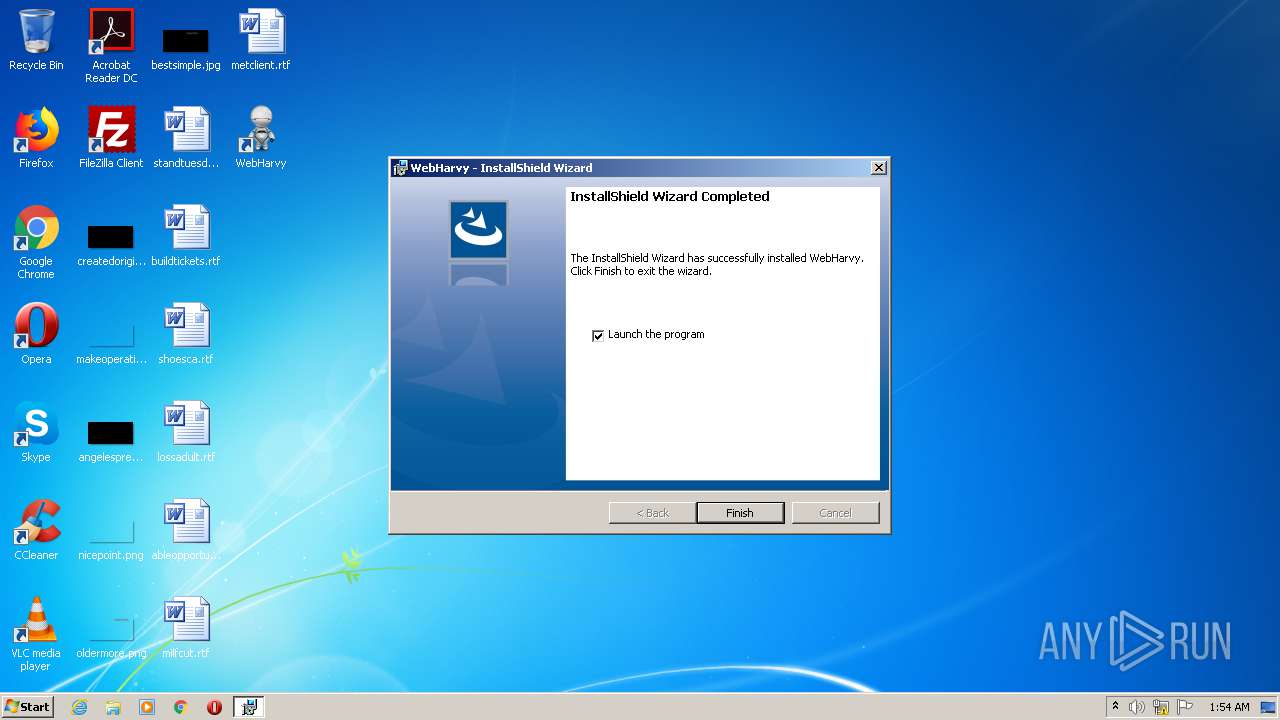
Starts Microsoft Installer
- WebHarvySetup.exe (PID: 3956)
Application launched itself
- eowp.exe (PID: 1736)
- eowp.exe (PID: 3944)
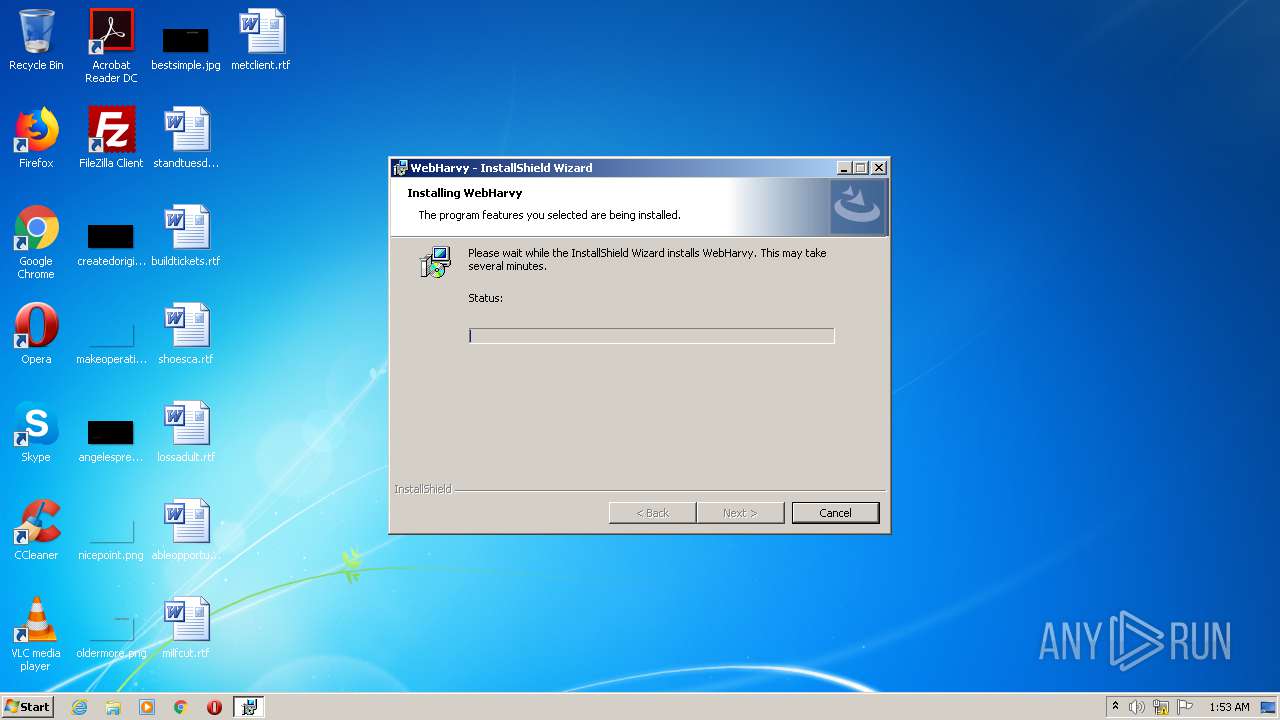
Creates files in the user directory
- WebHarvy.exe (PID: 556)
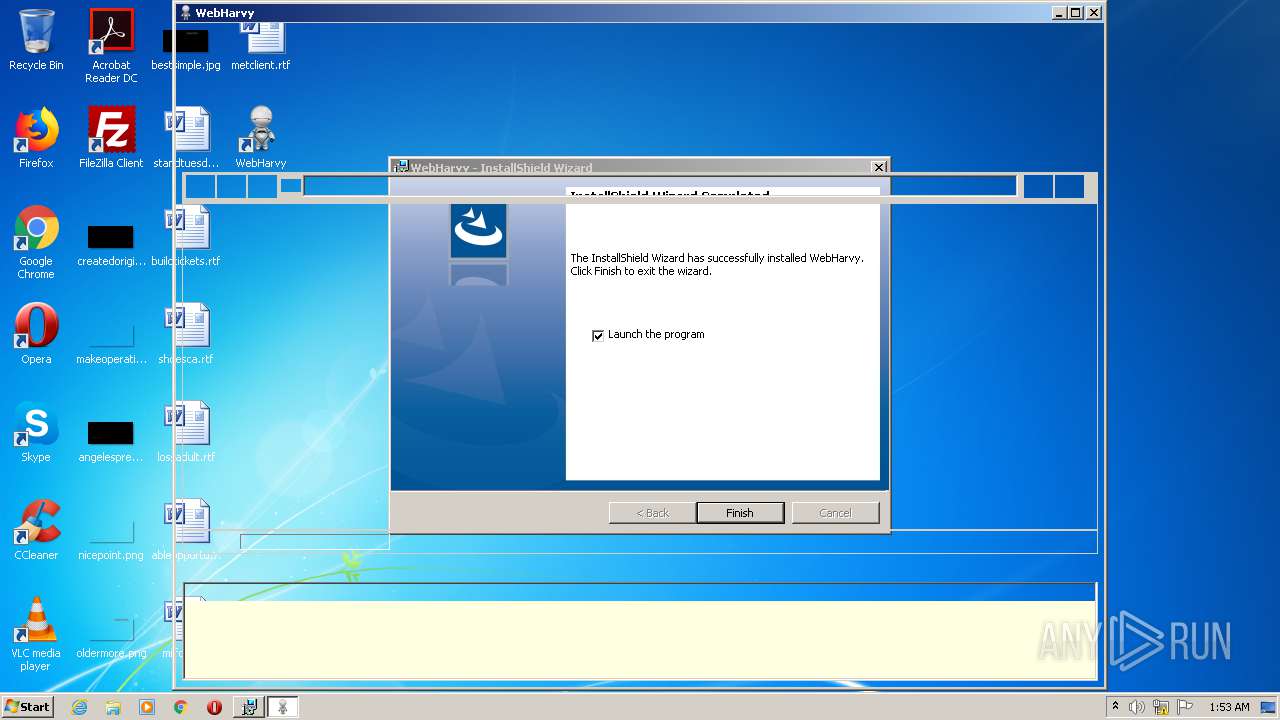
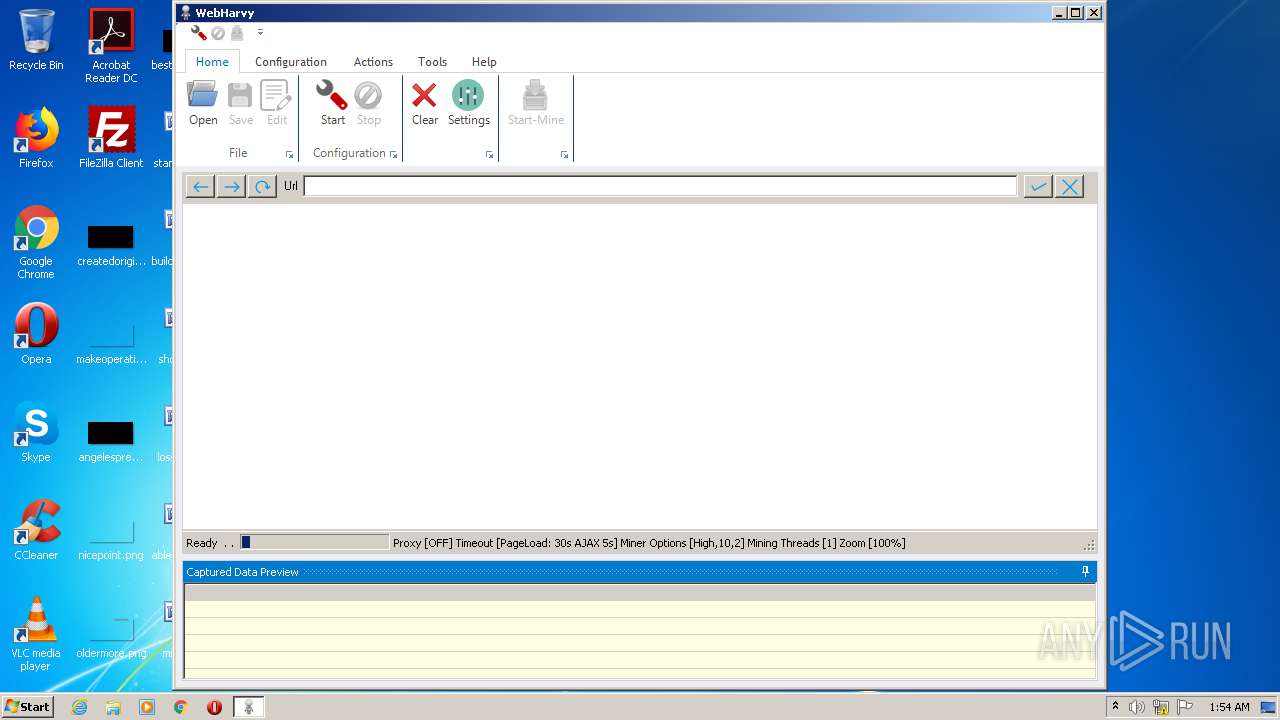
Reads internet explorer settings
- WebHarvy.exe (PID: 2076)
Reads Environment values
- WebHarvy.exe (PID: 2076)
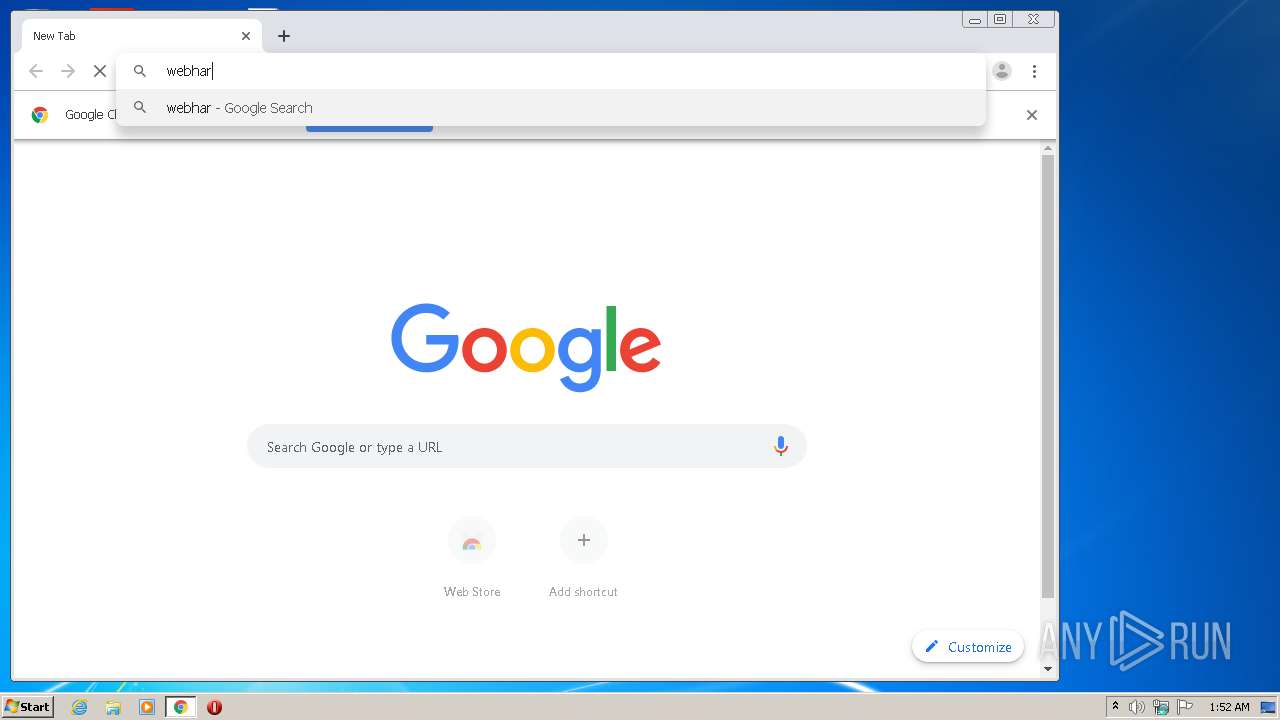
INFO
Reads Internet Cache Settings
- chrome.exe (PID: 3800)
Application launched itself
- chrome.exe (PID: 3800)
Manual execution by user
- chrome.exe (PID: 3800)
Reads the hosts file
- chrome.exe (PID: 3360)
- chrome.exe (PID: 3800)
- eowp.exe (PID: 1736)
- eowp.exe (PID: 2888)
- eowp.exe (PID: 3944)
- eowp.exe (PID: 2936)
Reads settings of System Certificates
- chrome.exe (PID: 3360)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .png | | | Portable Network Graphics (100) |
|---|
EXIF
PNG
| ImageWidth: | 690 |
|---|---|
| ImageHeight: | 310 |
| BitDepth: | 8 |
| ColorType: | RGB with Alpha |
| Compression: | Deflate/Inflate |
| Filter: | Adaptive |
| Interlace: | Noninterlaced |
Composite
| ImageSize: | 690x310 |
|---|---|
| Megapixels: | 0.214 |
Total processes
89
Monitored processes
44
Malicious processes
8
Suspicious processes
1
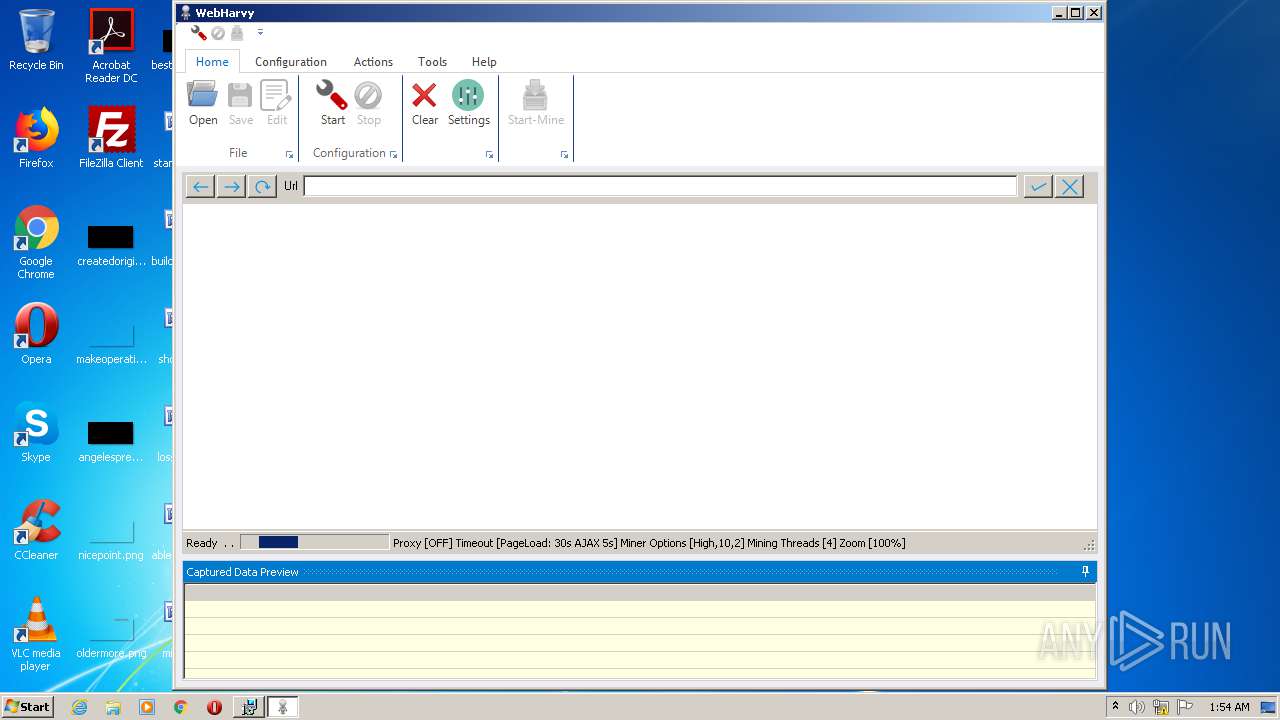
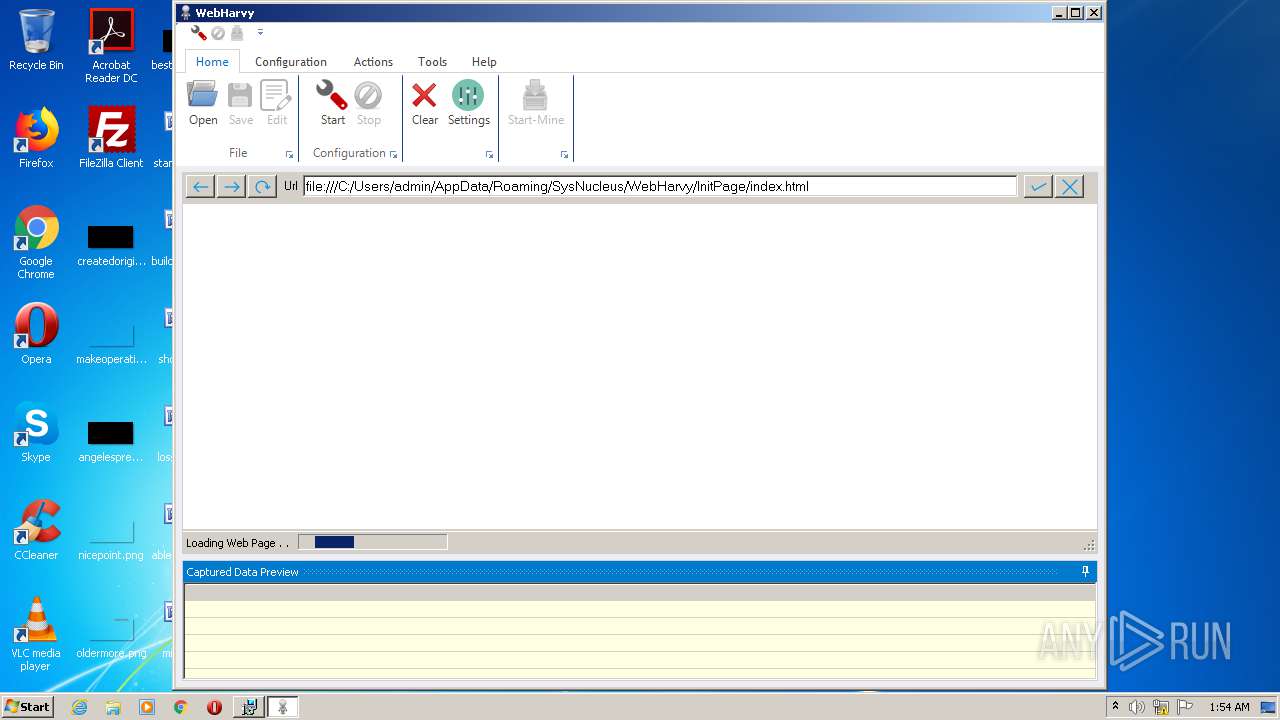
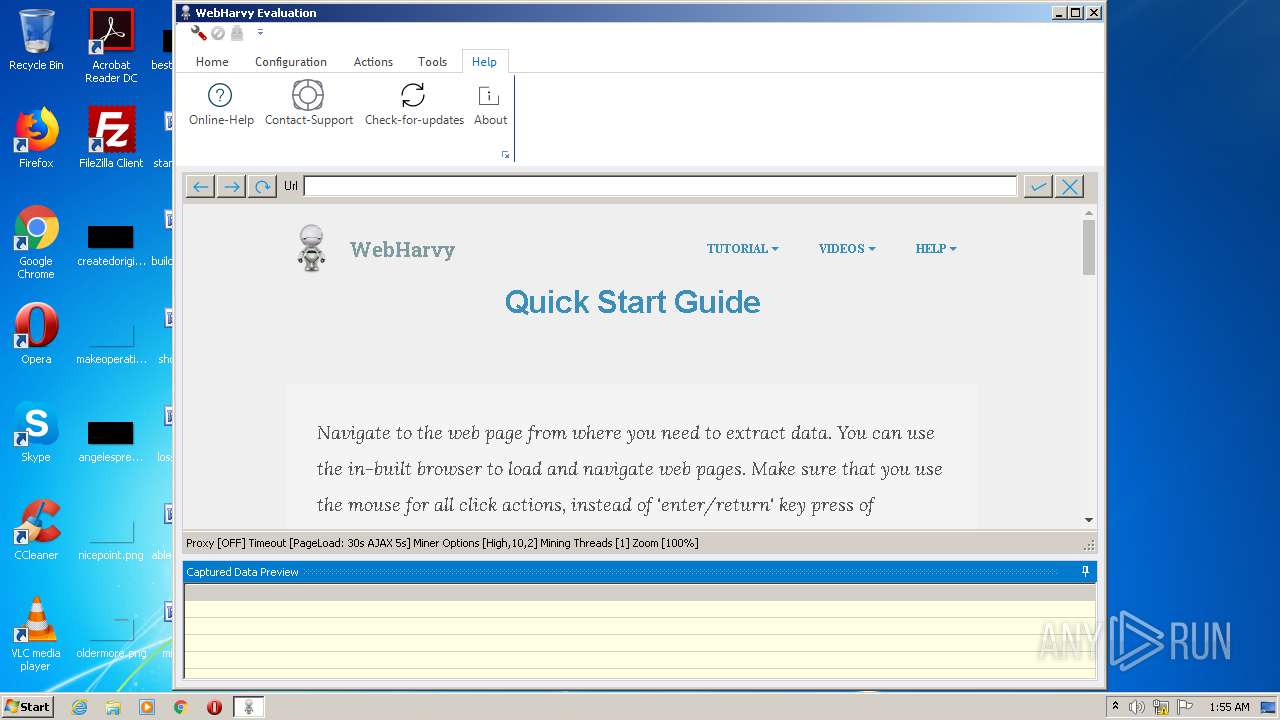
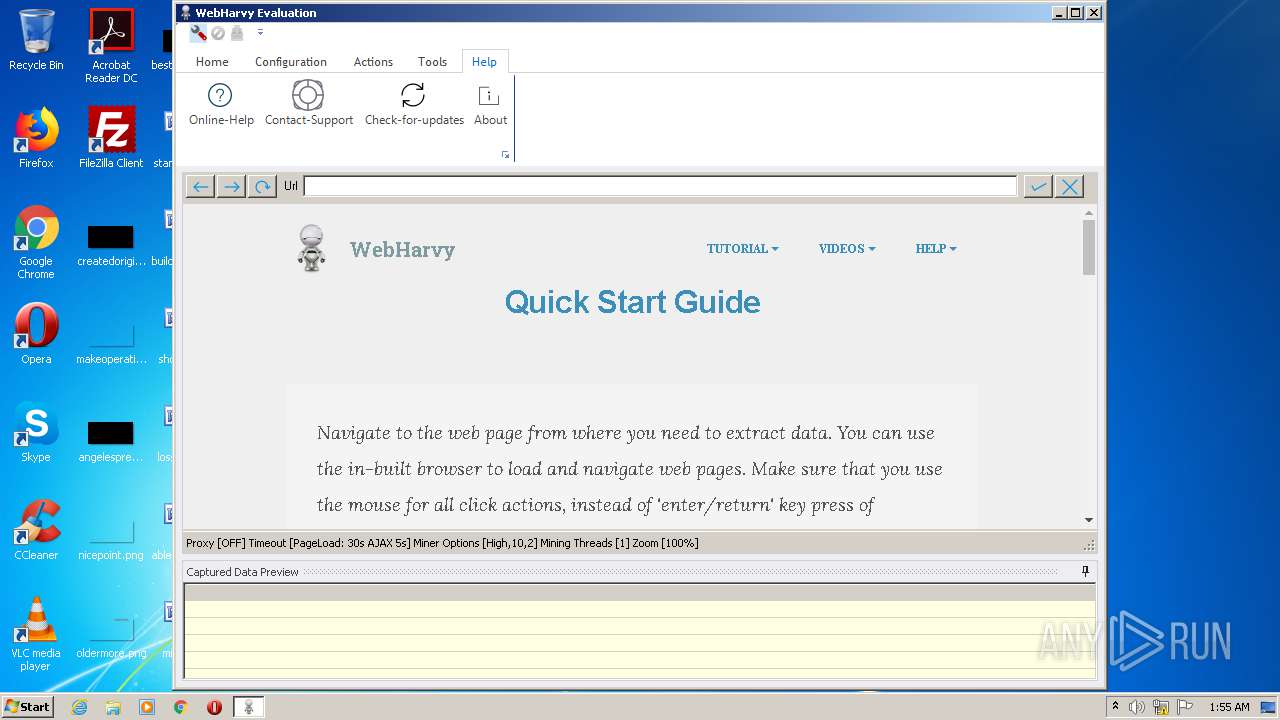
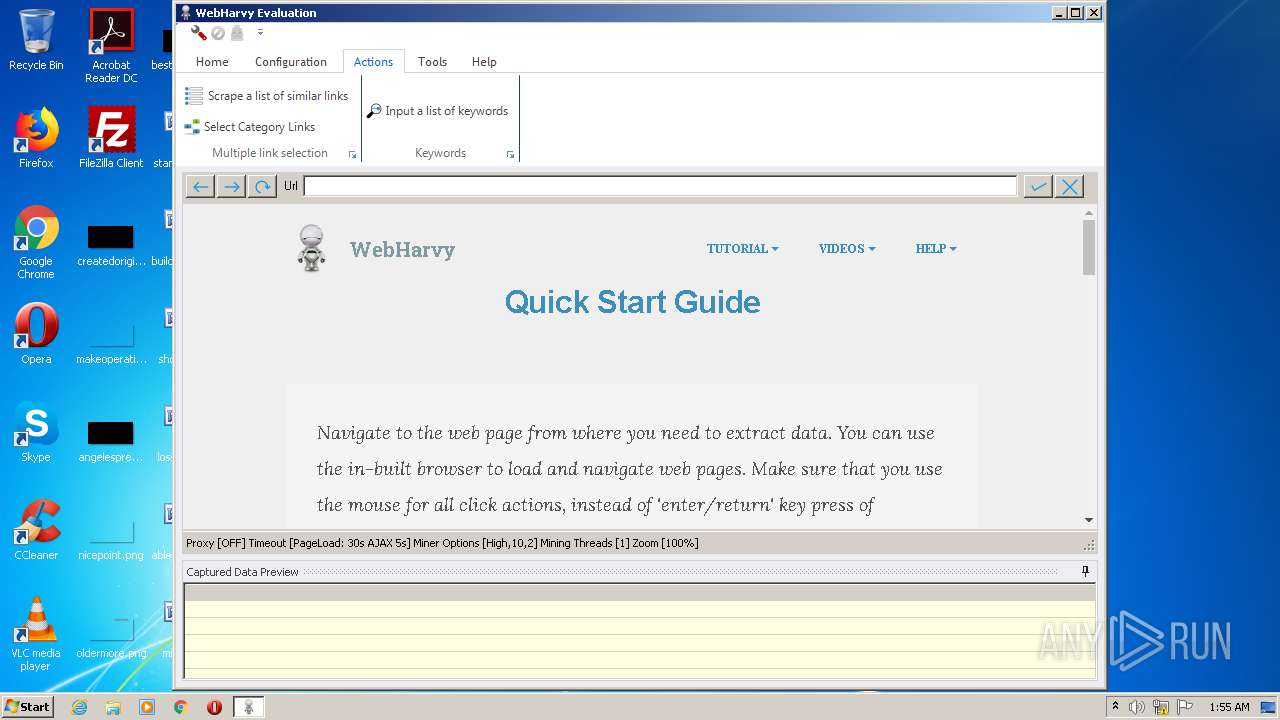
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 556 | "C:\Users\admin\AppData\Roaming\SysNucleus\WebHarvy\WebHarvy.exe" /PROTECTCONNSTRING | C:\Users\admin\AppData\Roaming\SysNucleus\WebHarvy\WebHarvy.exe | — | MSIEXEC.EXE | |||||||||||
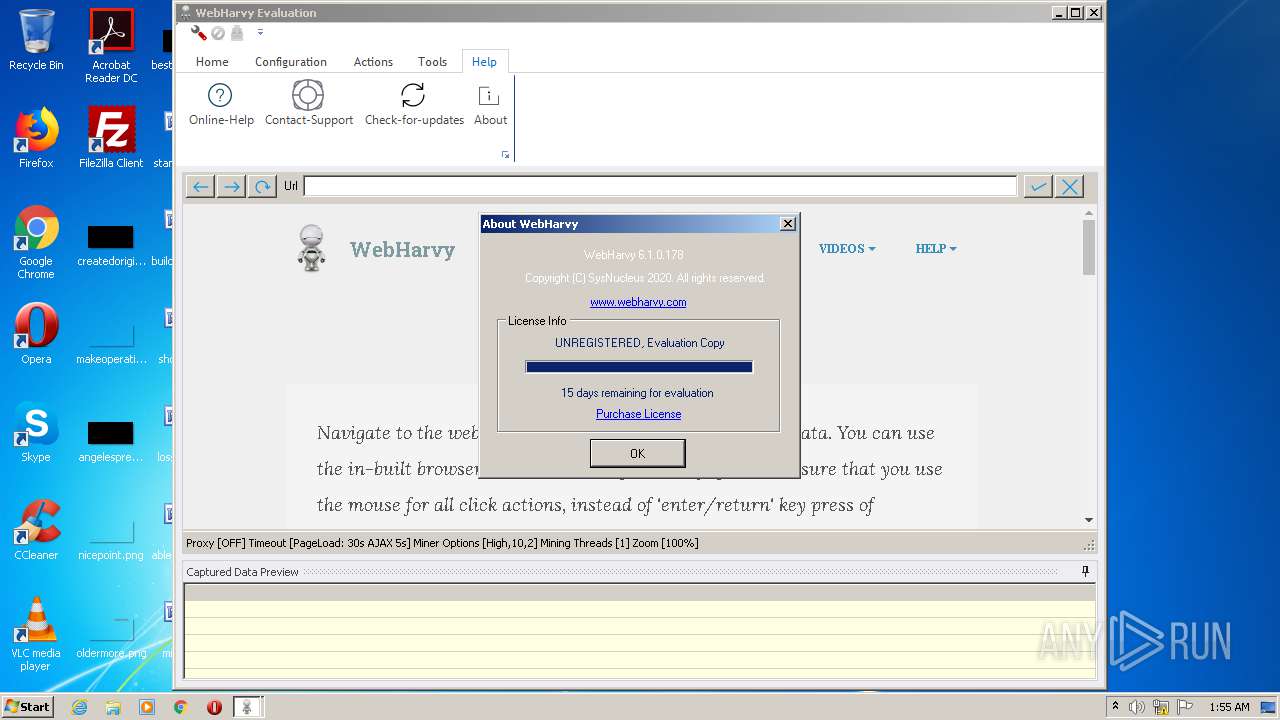
User: admin Company: SysNucleus Integrity Level: MEDIUM Description: WebHarvy Exit code: 0 Version: 6.1.0.178 Modules
| |||||||||||||||
| 1088 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=3820 --on-initialized-event-handle=324 --parent-handle=328 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1248 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=996,10880365258177468391,4177501292889453790,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=17677996135045912533 --mojo-platform-channel-handle=3536 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1656 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=996,10880365258177468391,4177501292889453790,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=3179139765966402857 --mojo-platform-channel-handle=3040 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1736 | "C:\Users\admin\AppData\Roaming\SysNucleus\WebHarvy\eowp.exe" --enable-speech-input --auto-scan-plugin --lang=en-US --enable-media-stream --no-sandbox --eo_init_data=eo.ipc.temp.20.2.19.0.556.1.5 | C:\Users\admin\AppData\Roaming\SysNucleus\WebHarvy\eowp.exe | WebHarvy.exe | ||||||||||||
User: admin Company: Essential Objects, Inc. Integrity Level: MEDIUM Description: Essential Objects Worker Process Exit code: 0 Version: 20.2.19.0 Modules
| |||||||||||||||
| 1868 | "C:\Users\admin\AppData\Roaming\SysNucleus\WebHarvy\eowp.exe" --type=renderer --no-sandbox --log-file="C:\Users\admin\AppData\Local\Temp\debug.log" --field-trial-handle=1164,9536240937049213296,5067477940746774922,131072 --enable-features=CastMediaRouteProvider --disable-features=OutOfBlinkCors --disable-gpu-compositing --lang=en-US --log-file="C:\Users\admin\AppData\Local\Temp\debug.log" --log-severity=disable --enable-speech-input --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=7 --mojo-platform-channel-handle=868 /prefetch:1 --eo_init_data=eo.temp.3944.11 | C:\Users\admin\AppData\Roaming\SysNucleus\WebHarvy\eowp.exe | eowp.exe | ||||||||||||
User: admin Company: Essential Objects, Inc. Integrity Level: MEDIUM Description: Essential Objects Worker Process Exit code: 0 Version: 20.2.19.0 Modules
| |||||||||||||||
| 2076 | "C:\Users\admin\AppData\Roaming\SysNucleus\WebHarvy\WebHarvy.exe" | C:\Users\admin\AppData\Roaming\SysNucleus\WebHarvy\WebHarvy.exe | MsiExec.exe | ||||||||||||
User: admin Company: SysNucleus Integrity Level: MEDIUM Description: WebHarvy Exit code: 0 Version: 6.1.0.178 Modules
| |||||||||||||||
| 2132 | "C:\Users\admin\AppData\Roaming\SysNucleus\WebHarvy\eowp.exe" --type=gpu-process --field-trial-handle=1128,2866544309142765318,9669751133984061412,131072 --enable-features=CastMediaRouteProvider --disable-features=OutOfBlinkCors --no-sandbox --log-file="C:\Users\admin\AppData\Local\Temp\debug.log" --log-severity=disable --lang=en-US --gpu-preferences=MAAAAAAAAADgAAAwAAAAAAAAAAAAAAAAAABgAAAAAAAQAAAAAAAAAAAAAAAAAAAAKAAAAAQAAAAgAAAAAAAAACgAAAAAAAAAMAAAAAAAAAA4AAAAAAAAABAAAAAAAAAAAAAAAAUAAAAQAAAAAAAAAAAAAAAGAAAAEAAAAAAAAAABAAAABQAAABAAAAAAAAAAAQAAAAYAAAA= --use-gl=swiftshader-webgl --log-file="C:\Users\admin\AppData\Local\Temp\debug.log" --mojo-platform-channel-handle=1172 /prefetch:2 --eo_init_data=eo.temp.1736.9 | C:\Users\admin\AppData\Roaming\SysNucleus\WebHarvy\eowp.exe | eowp.exe | ||||||||||||
User: admin Company: Essential Objects, Inc. Integrity Level: MEDIUM Description: Essential Objects Worker Process Exit code: 0 Version: 20.2.19.0 Modules
| |||||||||||||||
| 2264 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=996,10880365258177468391,4177501292889453790,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=17993404893650125900 --mojo-platform-channel-handle=3708 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2368 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=996,10880365258177468391,4177501292889453790,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=3281362021246162064 --mojo-platform-channel-handle=3412 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
2 631
Read events
2 342
Write events
278
Delete events
11
Modification events
| (PID) Process: | (2680) rundll32.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Direct3D\MostRecentApplication |
| Operation: | write | Name: | Name |
Value: rundll32.exe | |||
| (PID) Process: | (2680) rundll32.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows Photo Viewer\Viewer |
| Operation: | write | Name: | MainWndPos |
Value: 6000000034000000A00400008002000000000000 | |||
| (PID) Process: | (3800) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3800) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3800) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (3800) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3800) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3800) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3800) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3800) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 2832-13239195546717773 |
Value: 0 | |||
Executable files
4
Suspicious files
65
Text files
129
Unknown types
17
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3800 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\6c6633ef-4f4d-419b-b529-b5e67be54762.tmp | — | |
MD5:— | SHA256:— | |||
| 3800 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000032.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3800 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3800 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RFe4f35.TMP | text | |
MD5:— | SHA256:— | |||
| 3800 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3800 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3800 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\EventDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3800 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3800 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old~RFe5196.TMP | — | |
MD5:— | SHA256:— | |||
| 3800 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad\settings.dat | binary | |
MD5:9C016064A1F864C8140915D77CF3389A | SHA256:0E7265D4A8C16223538EDD8CD620B8820611C74538E420A88E333BE7F62AC787 | |||
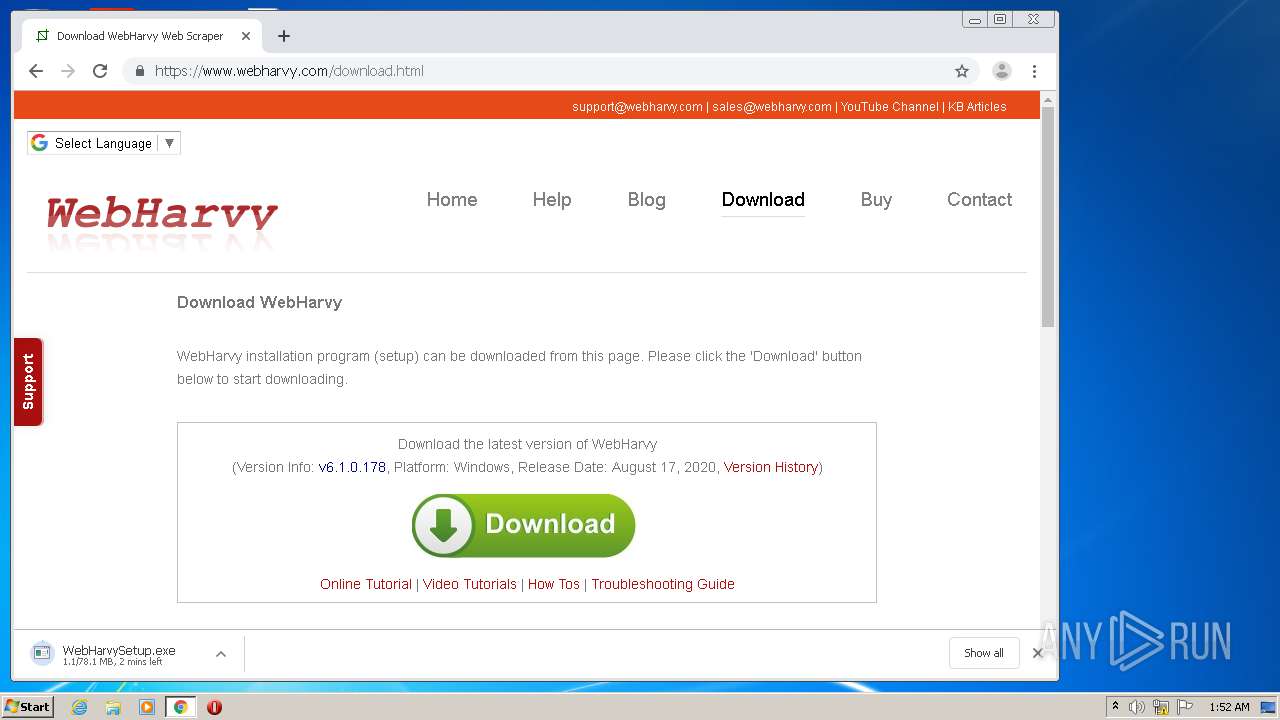
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
48
DNS requests
27
Threats
0
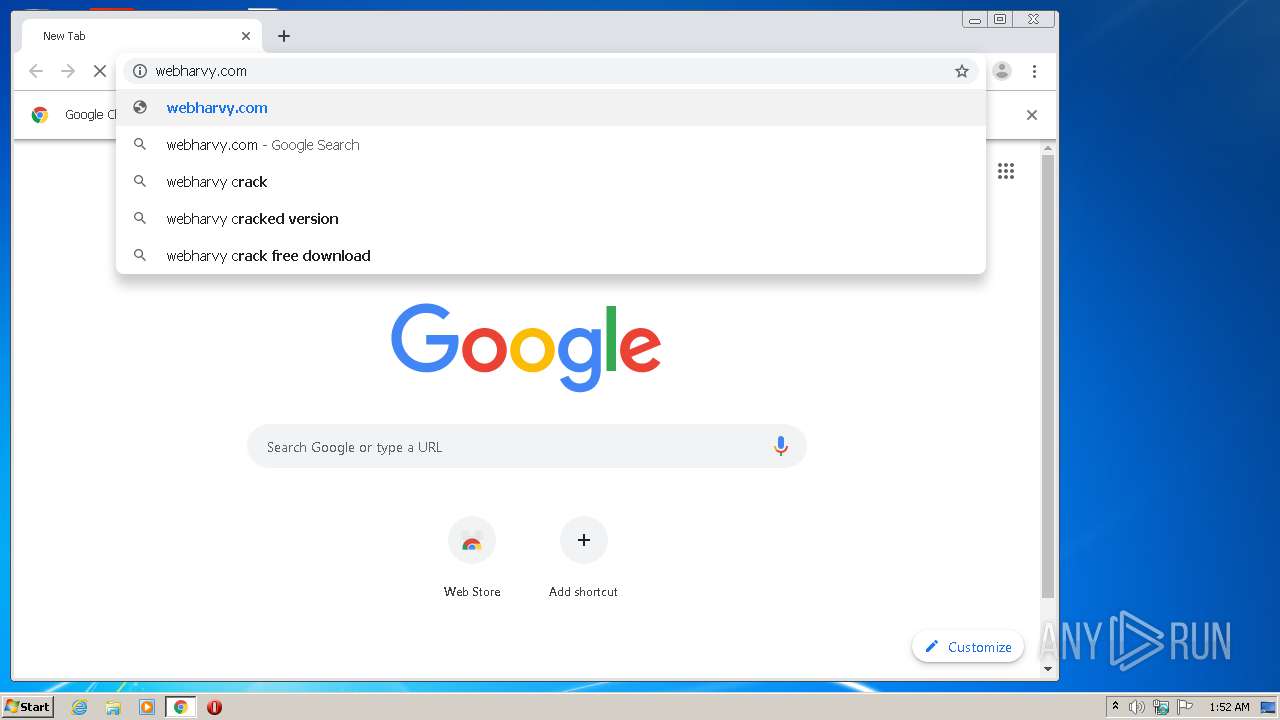
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2076 | WebHarvy.exe | GET | 200 | 118.139.187.22:80 | http://www.webharvy.com/webharvy.xml | SG | xml | 17.3 Kb | unknown |
3360 | chrome.exe | GET | 301 | 118.139.187.22:80 | http://webharvy.com/ | SG | html | 148 b | unknown |
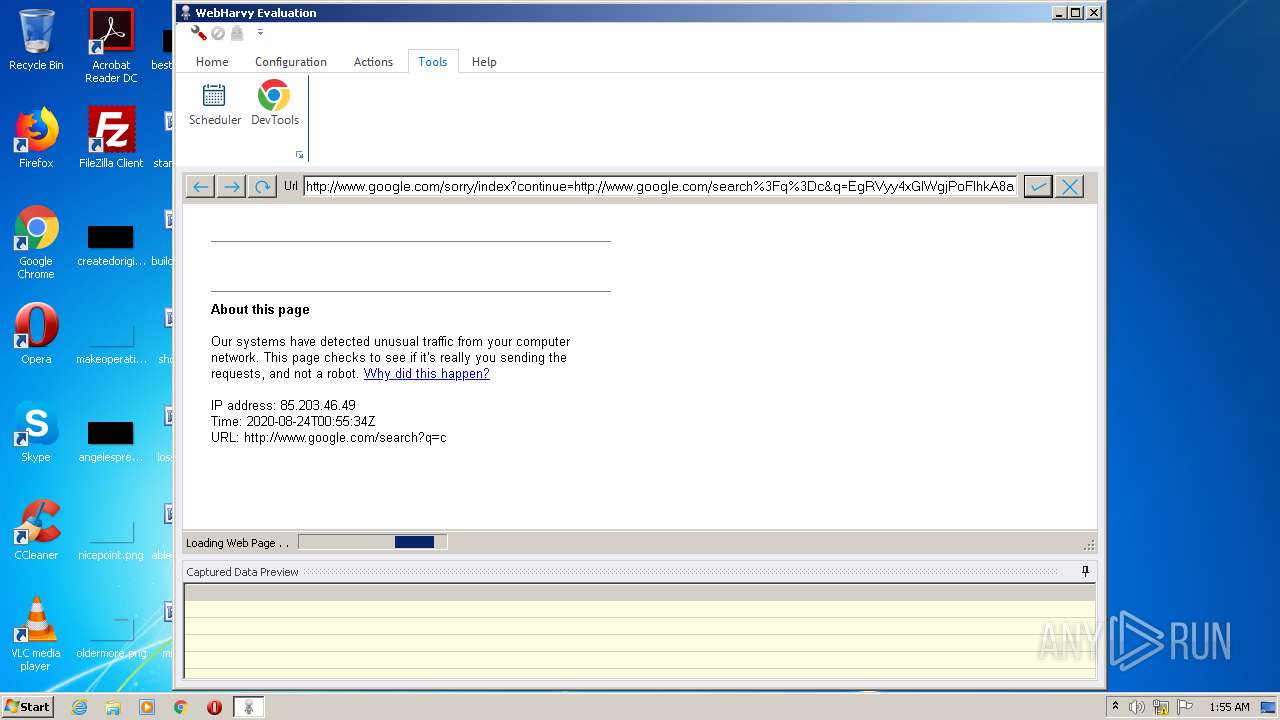
2936 | eowp.exe | GET | 302 | 172.217.21.196:80 | http://www.google.com/search?q=c | US | html | 339 b | malicious |
2936 | eowp.exe | GET | 429 | 172.217.21.196:80 | http://www.google.com/sorry/index?continue=http://www.google.com/search%3Fq%3Dc&q=EgRVyy4xGIWgjPoFIhkA8aeDSxOnQ0uI2AV01A3Ki-HVIQz5HP-FMgFy | US | html | 2.76 Kb | malicious |
2936 | eowp.exe | GET | 200 | 172.217.21.196:80 | http://www.google.com/favicon.ico | US | image | 1.46 Kb | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3360 | chrome.exe | 172.217.18.170:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
3360 | chrome.exe | 216.58.208.35:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
3360 | chrome.exe | 172.217.22.13:443 | accounts.google.com | Google Inc. | US | whitelisted |
3360 | chrome.exe | 216.58.206.3:443 | www.gstatic.com | Google Inc. | US | whitelisted |
3360 | chrome.exe | 172.217.23.131:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
3360 | chrome.exe | 216.58.207.46:443 | apis.google.com | Google Inc. | US | whitelisted |
3360 | chrome.exe | 172.217.16.138:443 | ajax.googleapis.com | Google Inc. | US | whitelisted |
3360 | chrome.exe | 172.217.21.196:443 | www.google.com | Google Inc. | US | whitelisted |
3360 | chrome.exe | 216.58.207.78:443 | www.google-analytics.com | Google Inc. | US | whitelisted |
3360 | chrome.exe | 216.58.212.163:443 | www.google.co.uk | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
www.google.com.ua |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
apis.google.com |
| whitelisted |
ogs.google.com.ua |
| whitelisted |
www.google.com |
| malicious |
www.google.co.uk |
| whitelisted |
Threats
Process | Message |
|---|---|
eowp.exe | |
eowp.exe | PEFile::FixupIAT resolves IAT for module KERNEL32.dll |
eowp.exe | |
eowp.exe | |
eowp.exe | |
eowp.exe | Try fix import table for KERNEL32.dll |
eowp.exe | C:\Users\admin\AppData\Roaming\SysNucleus\WebHarvy\eoloader.dll |
eowp.exe | |
eowp.exe | CodeModule::LoadMemoryModule. dllName = C:\Users\admin\AppData\Roaming\SysNucleus\WebHarvy\eoloader.dll |
eowp.exe | |