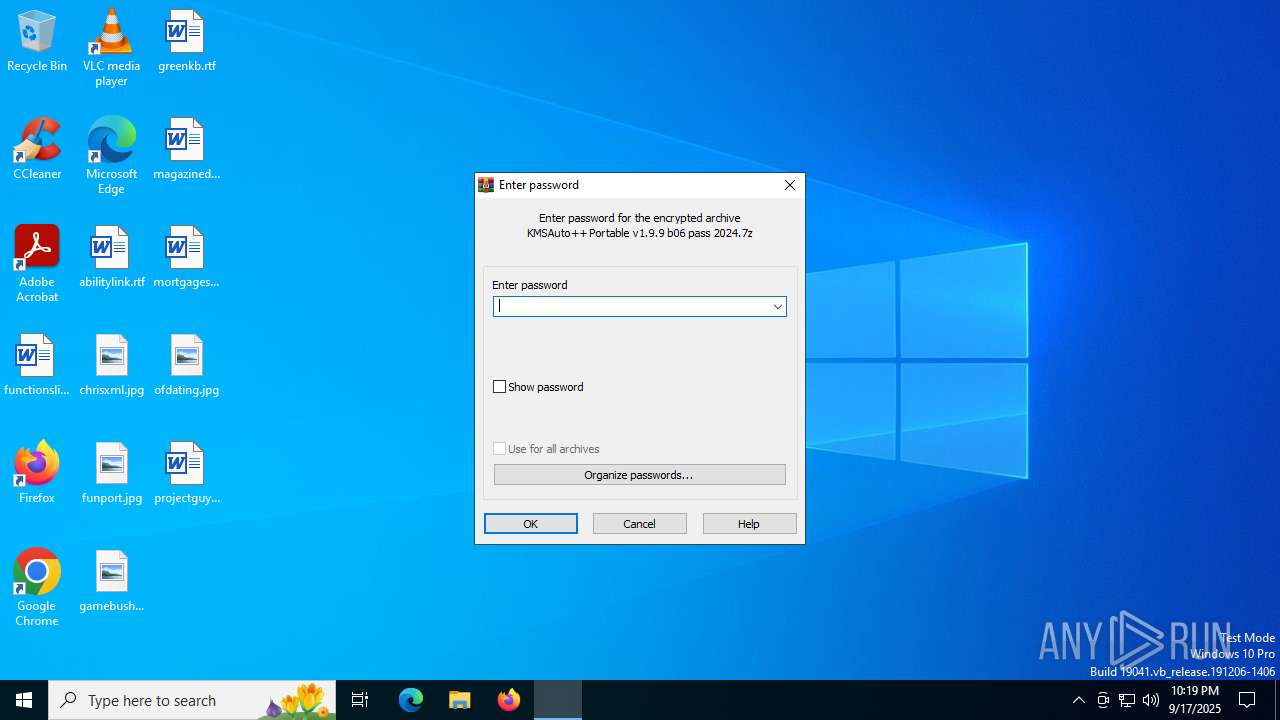
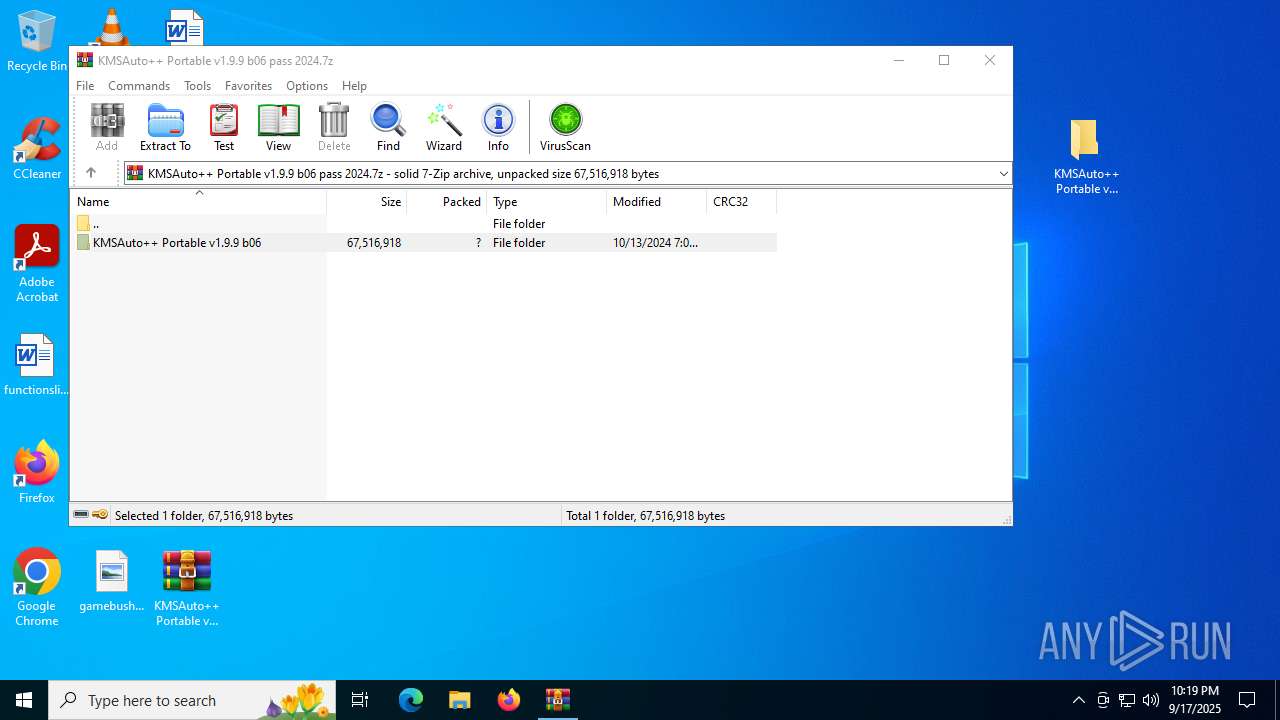
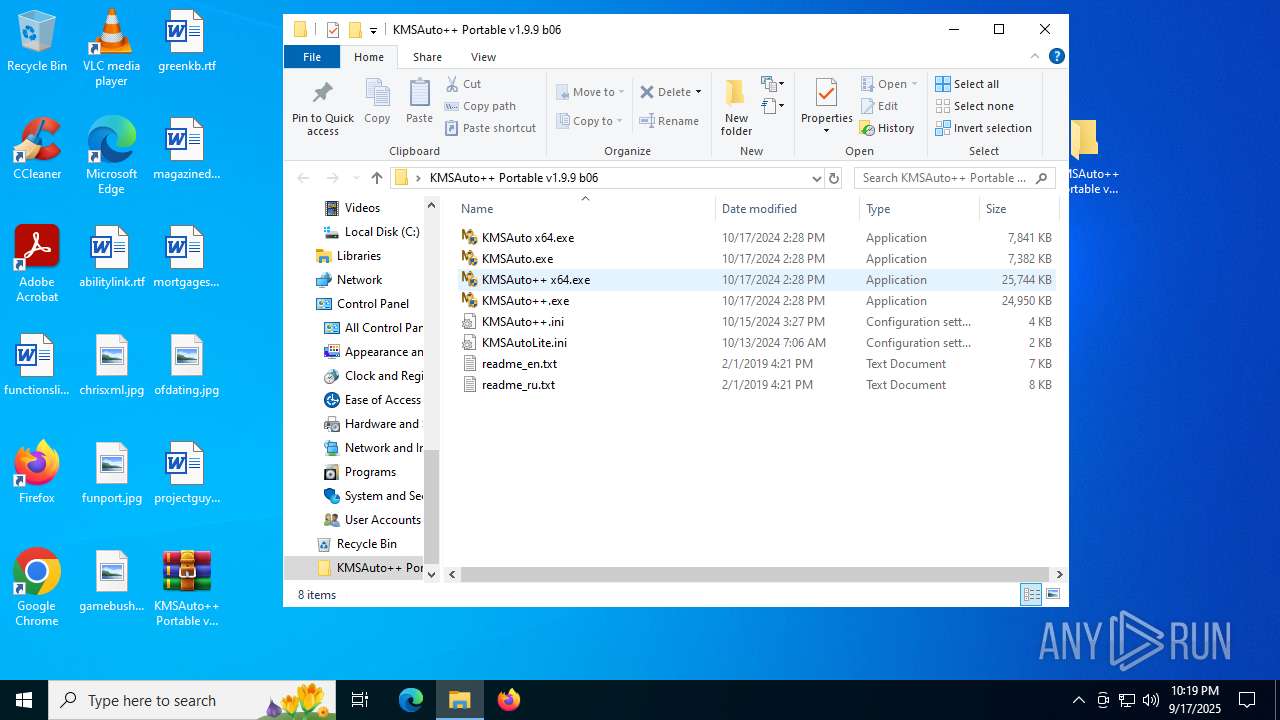
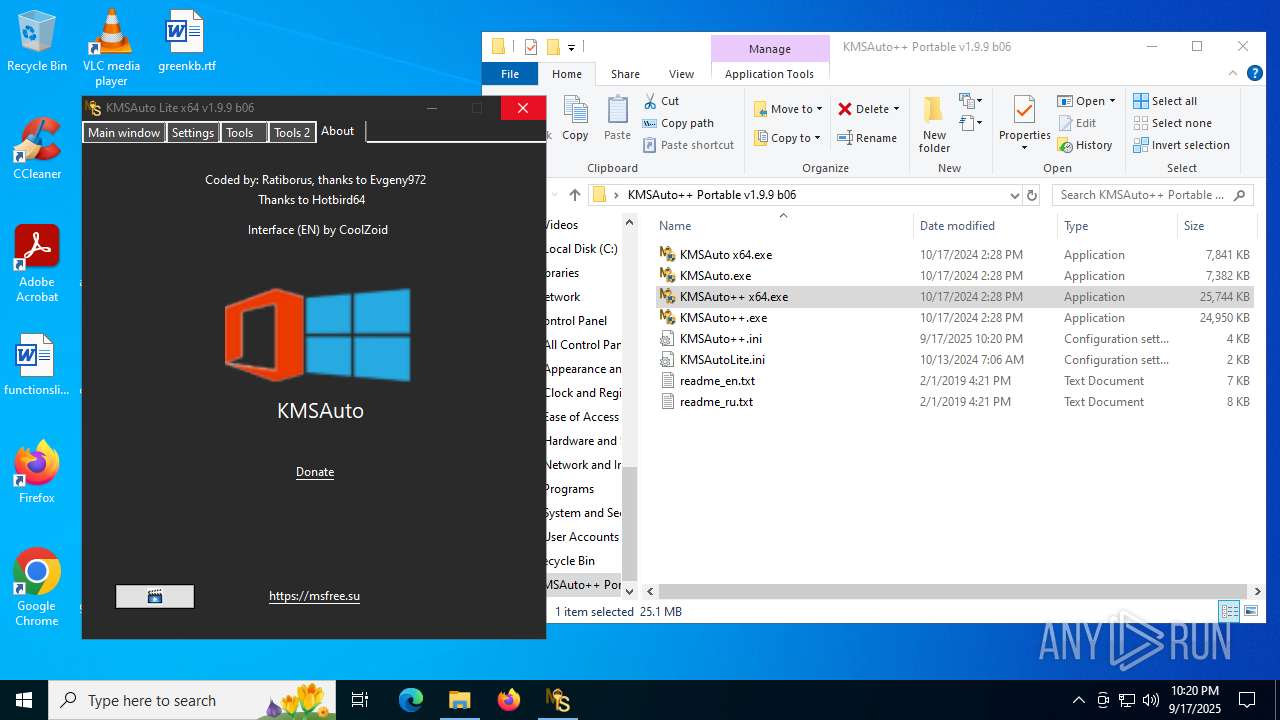
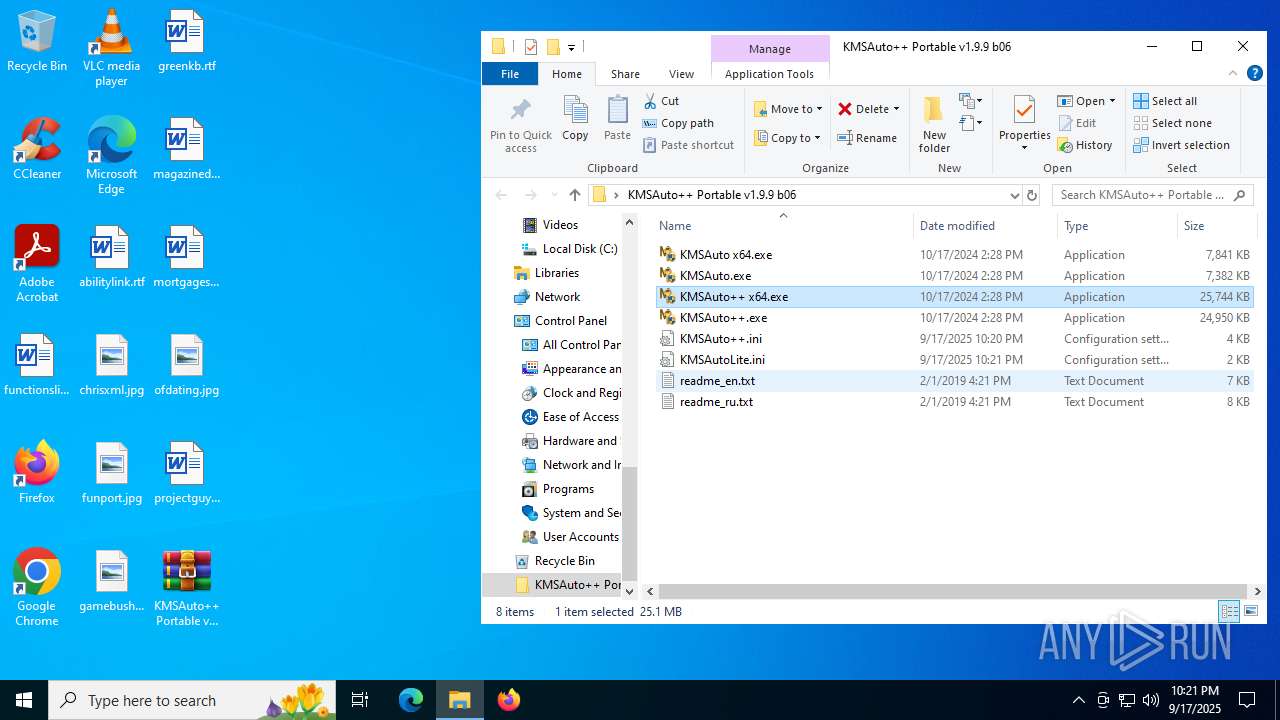
| File name: | KMSAuto++ Portable v1.9.9 b06 pass 2024.7z |
| Full analysis: | https://app.any.run/tasks/7d544615-7612-4d2c-80db-32593715f24a |
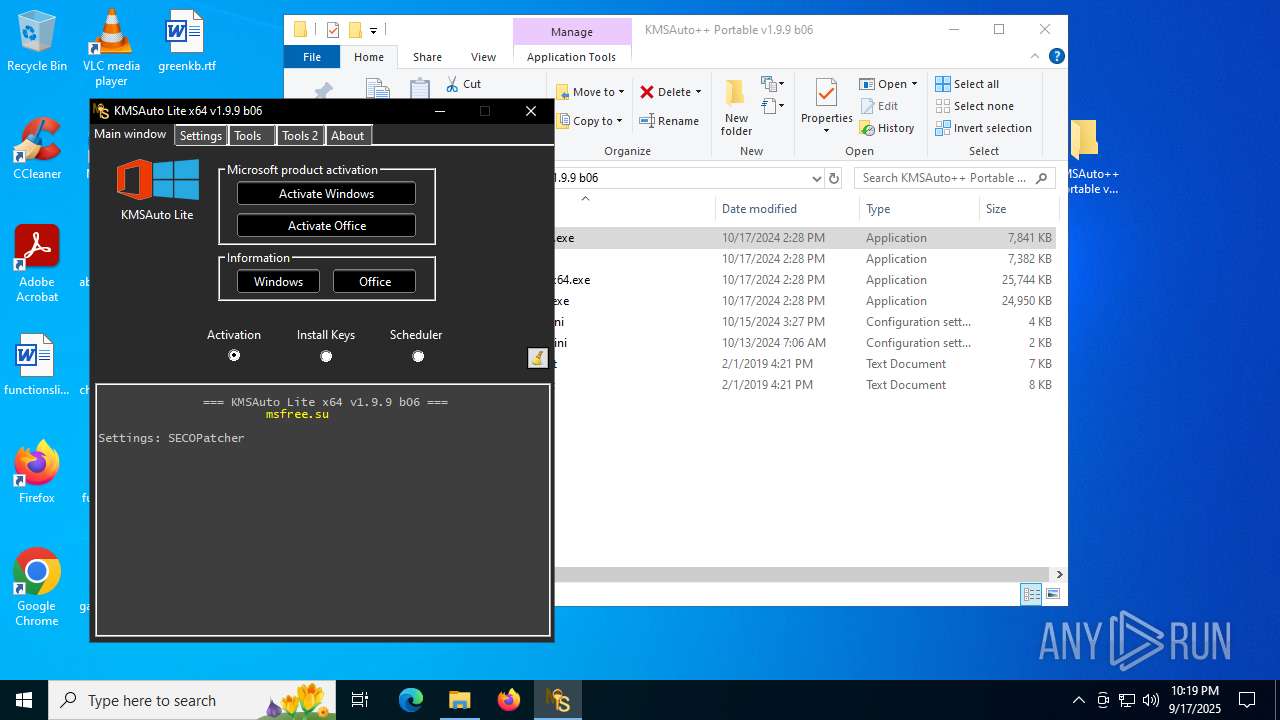
| Verdict: | Malicious activity |
| Analysis date: | September 17, 2025, 22:19:09 |
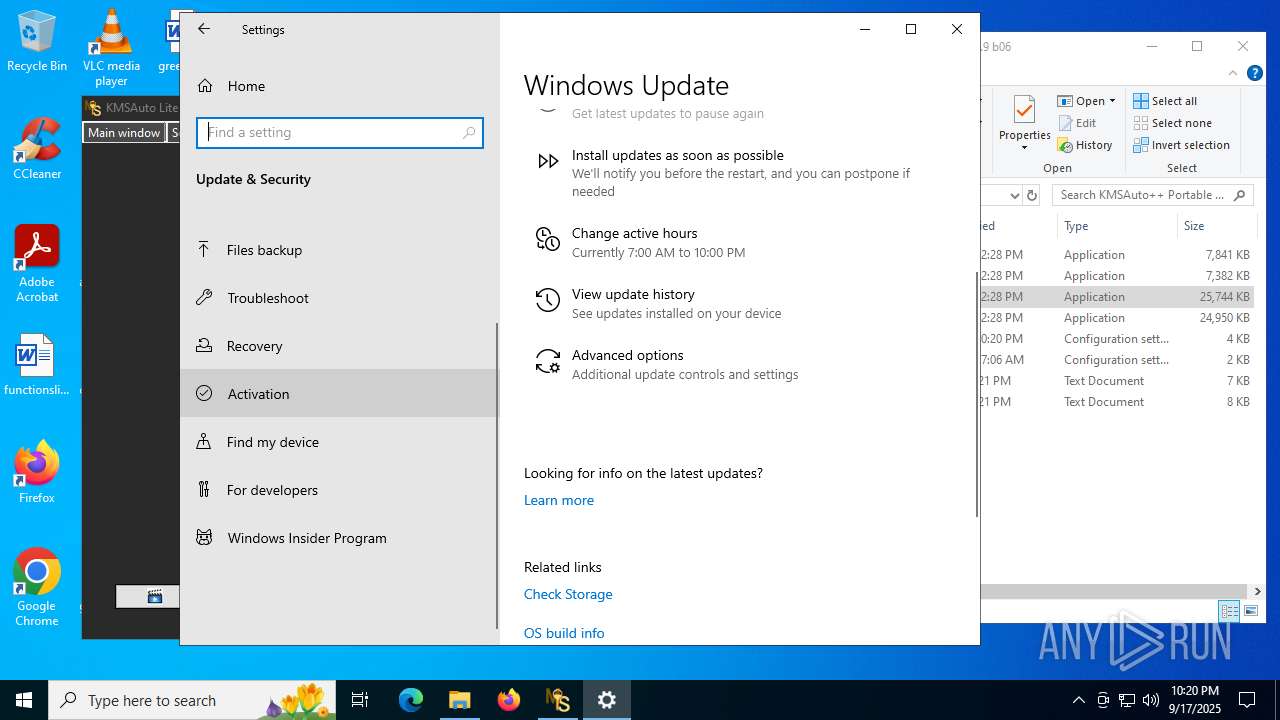
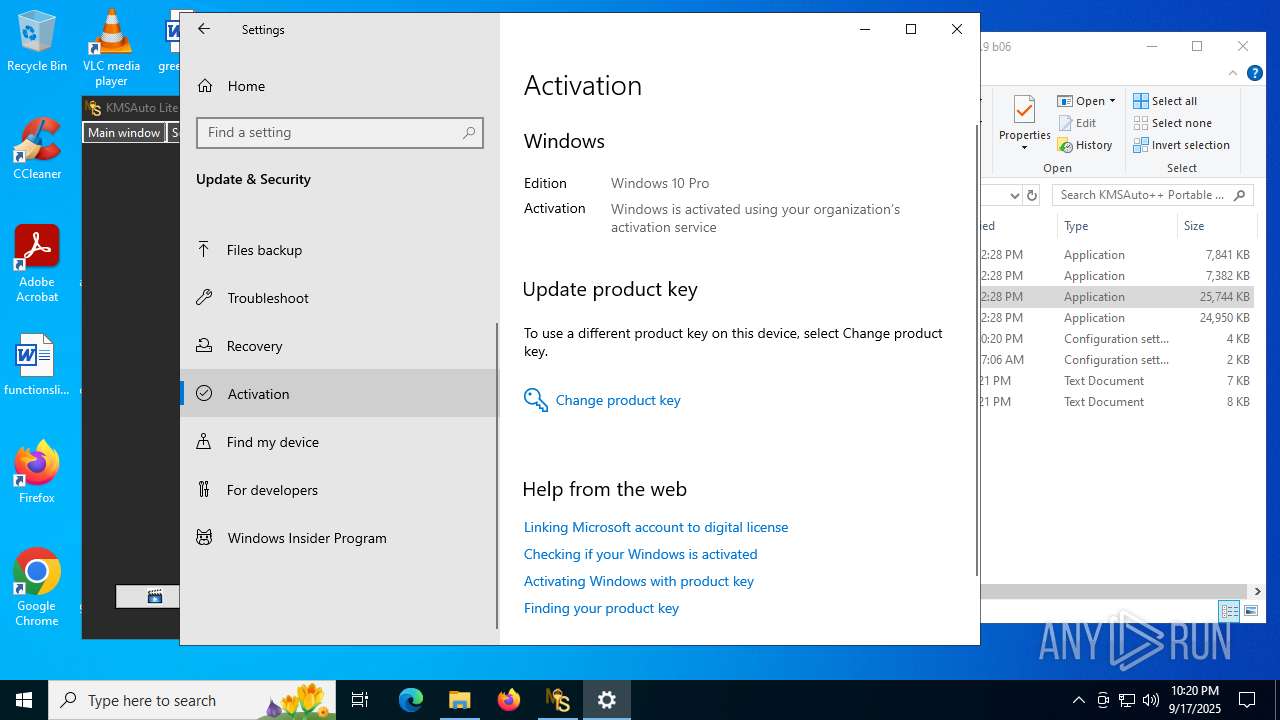
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Indicators: | |
| MIME: | application/x-7z-compressed |
| File info: | 7-zip archive data, version 0.4 |
| MD5: | 423EFB73A631241EC0CBA8190AFD7D3E |
| SHA1: | 579FF2365A9499E0C8EEF4FA1EBCD8BA9E228A08 |
| SHA256: | 5DEC7CD4F7ED331AA36D40CC6BEEDD9606F382334CB39CAE6B4E33E87BC81021 |
| SSDEEP: | 98304:7me5cfyoCMtTUwmyMAYVQyLCp3d9JAH9ul/HmZ7s0XWQHVAHTPUsGXz4CJYGzSjr:C8T06rzVdmIuiuD1xLh |
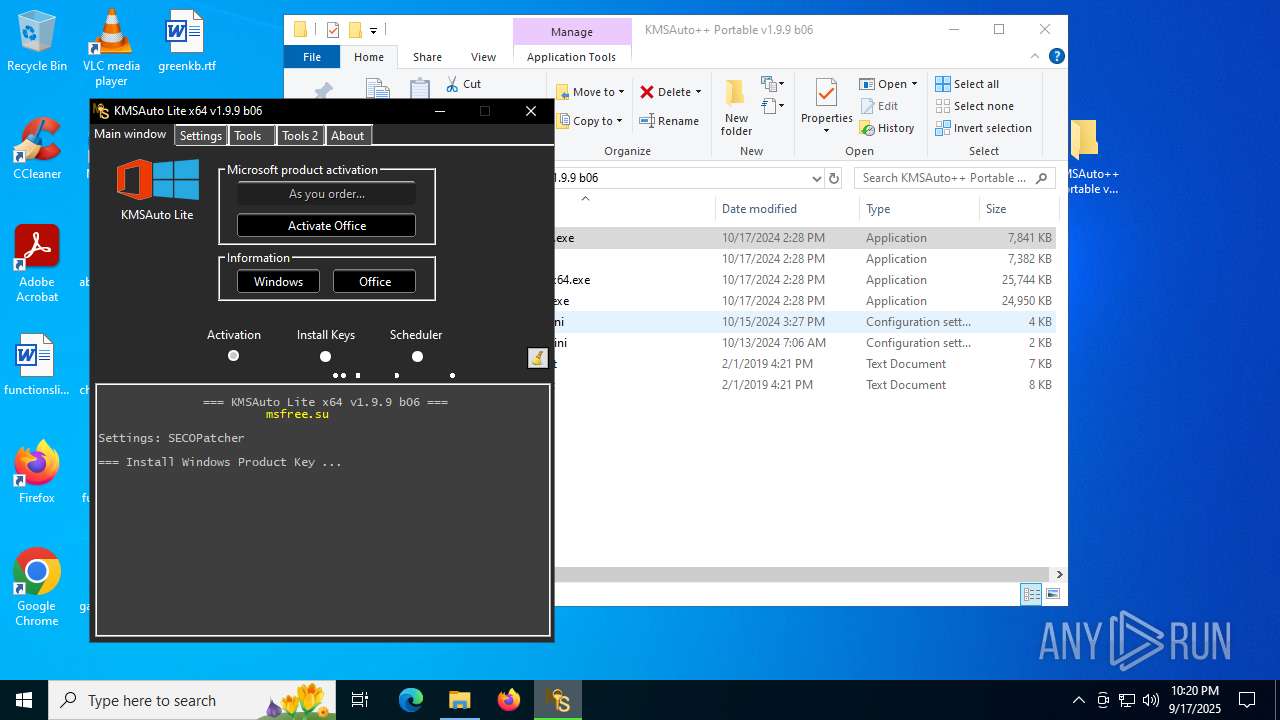
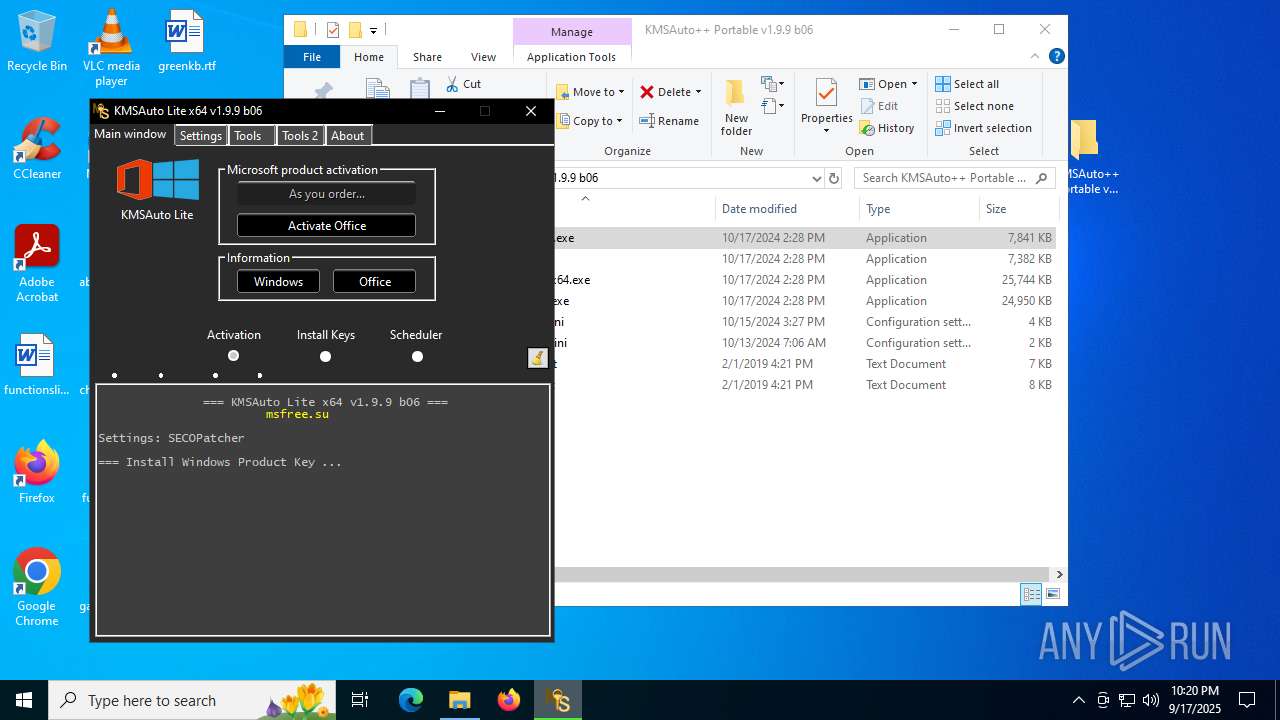
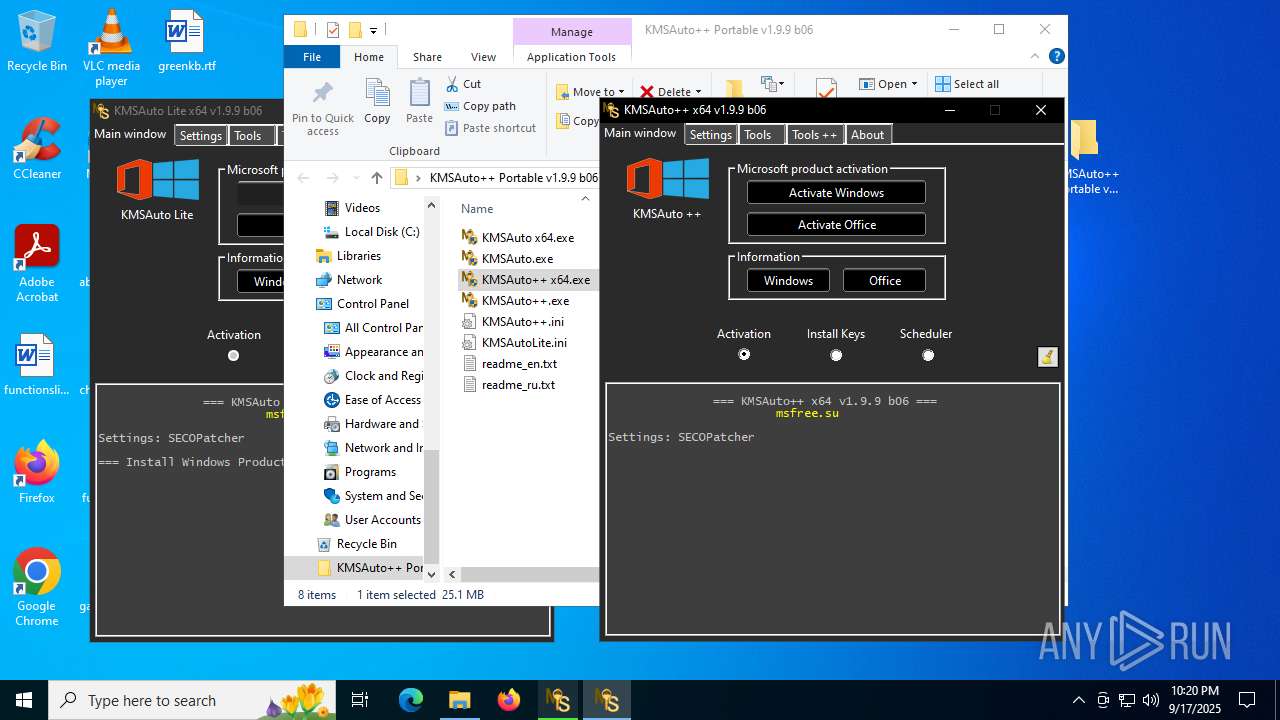
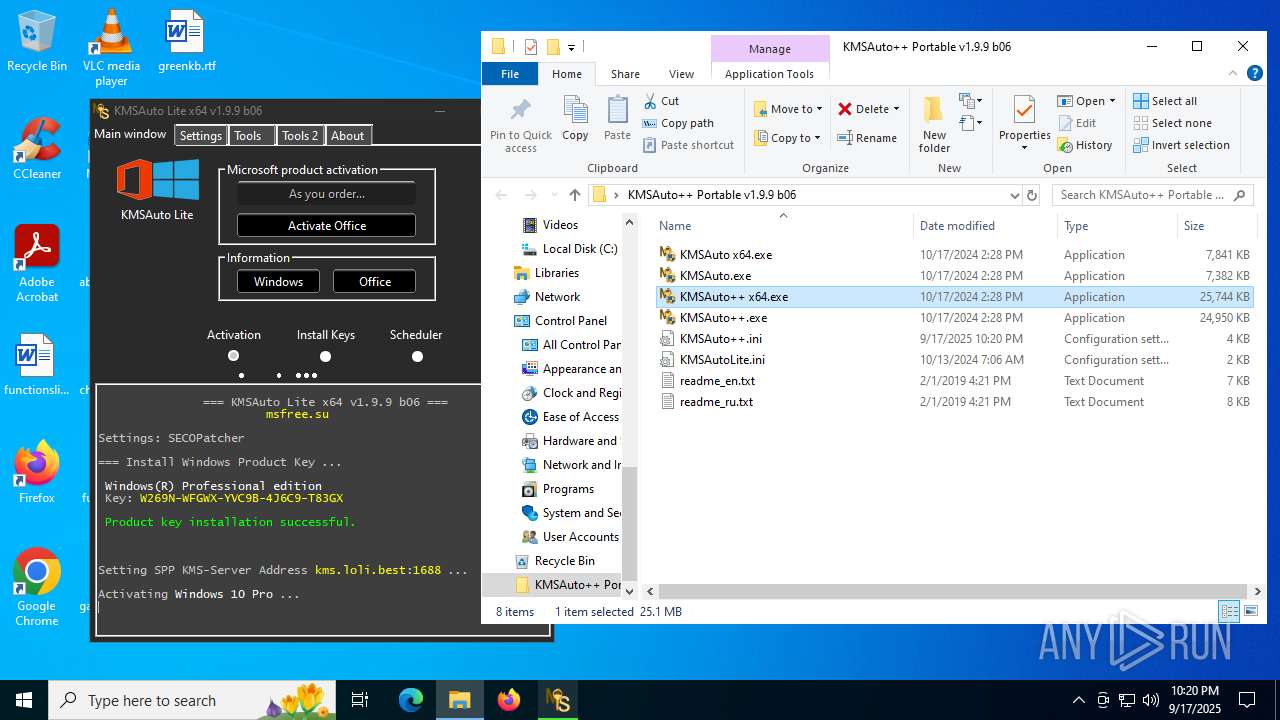
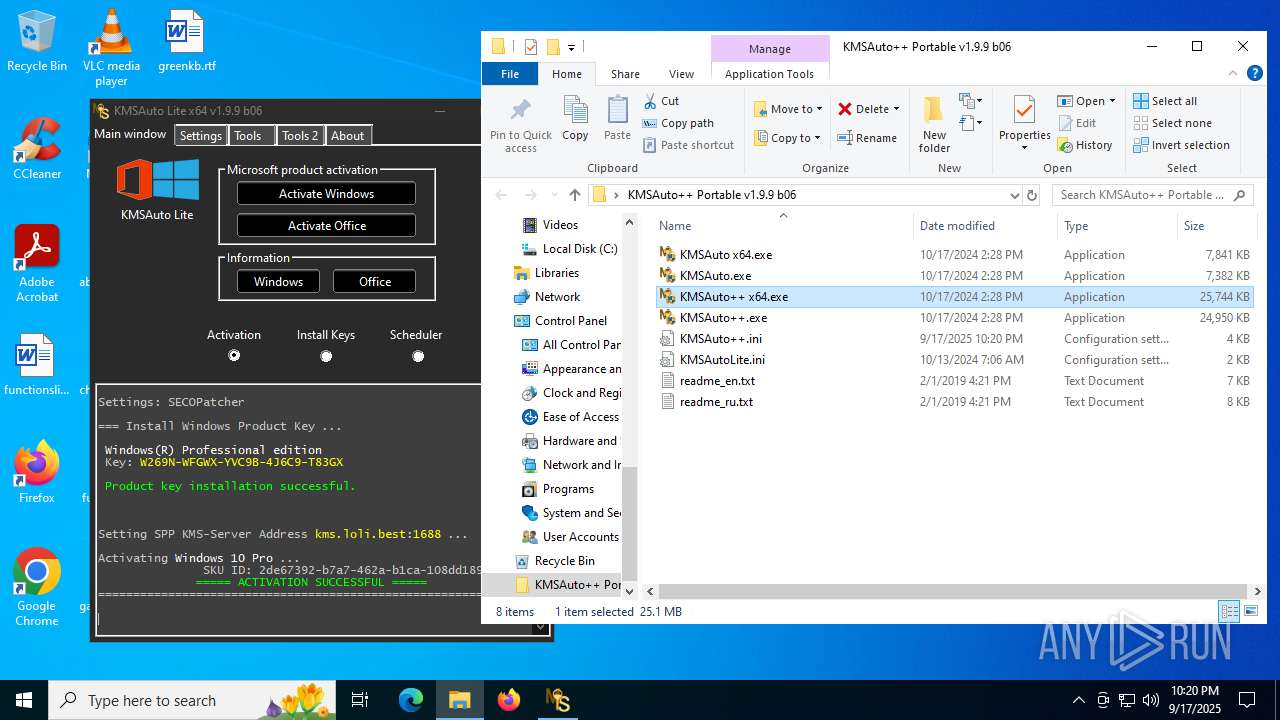
MALICIOUS
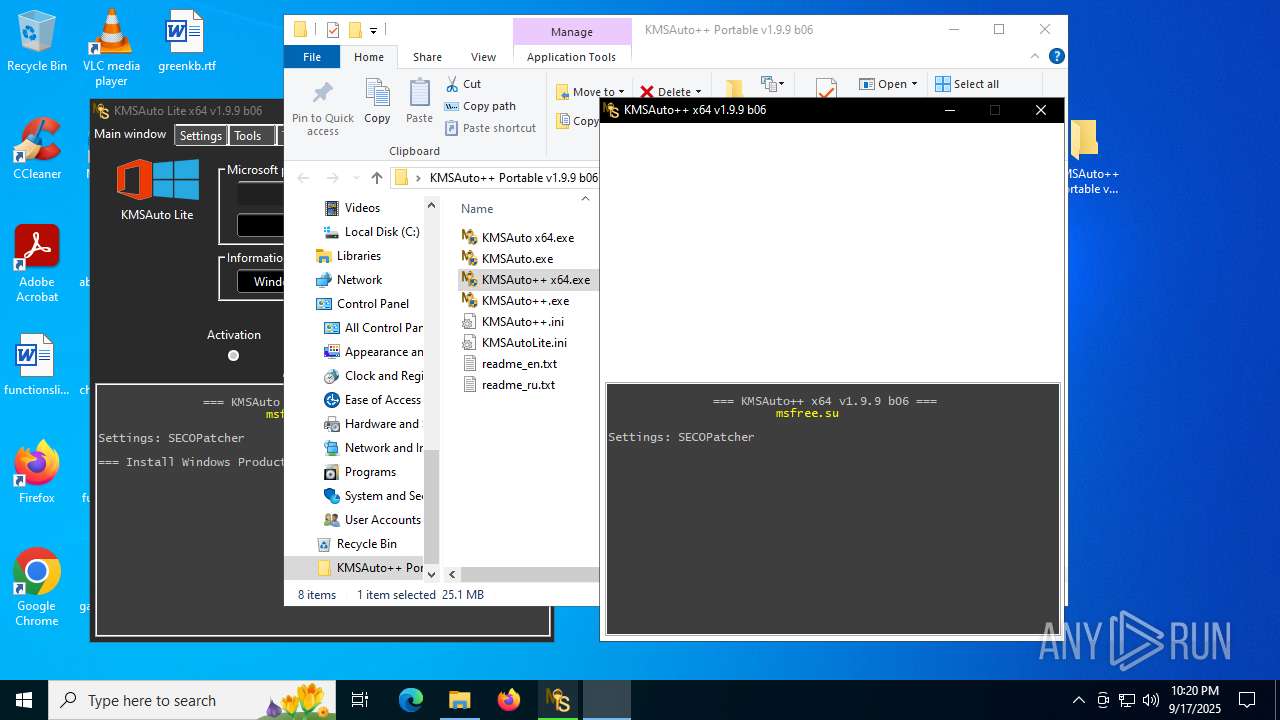
Accesses name of the domain to which a computer belongs via WMI (SCRIPT)
- cscript.exe (PID: 188)
SUSPICIOUS
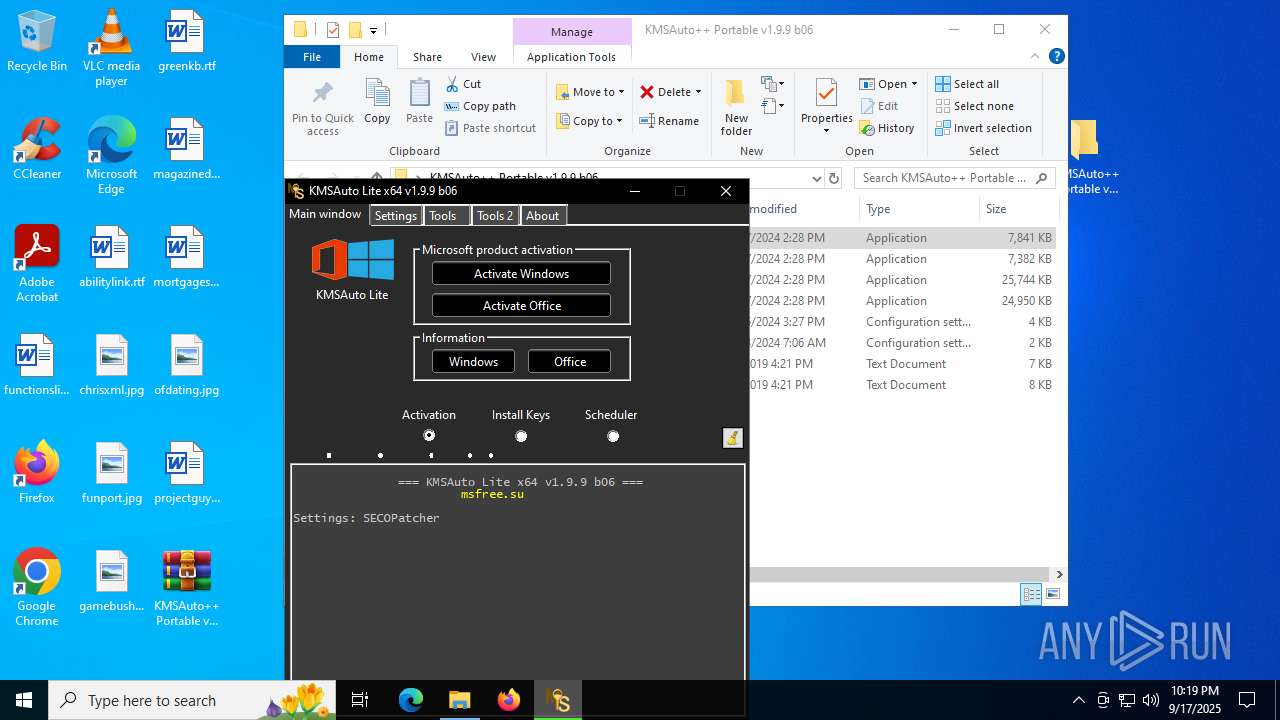
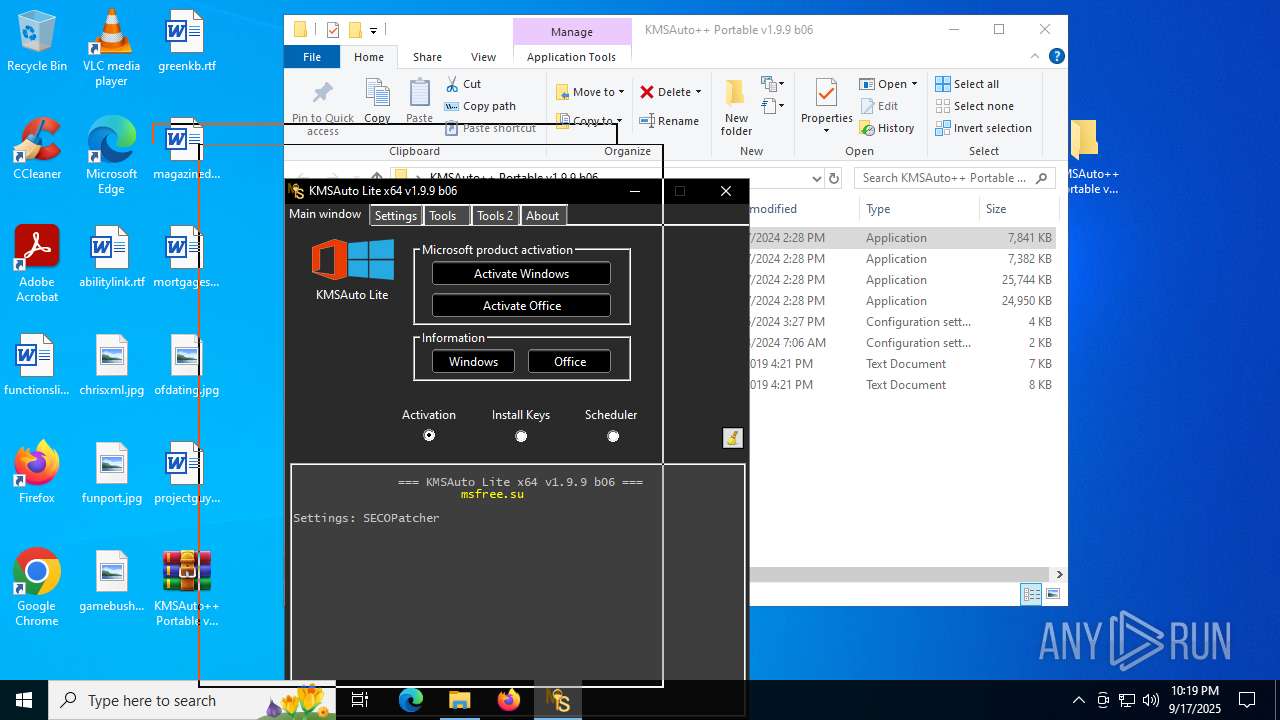
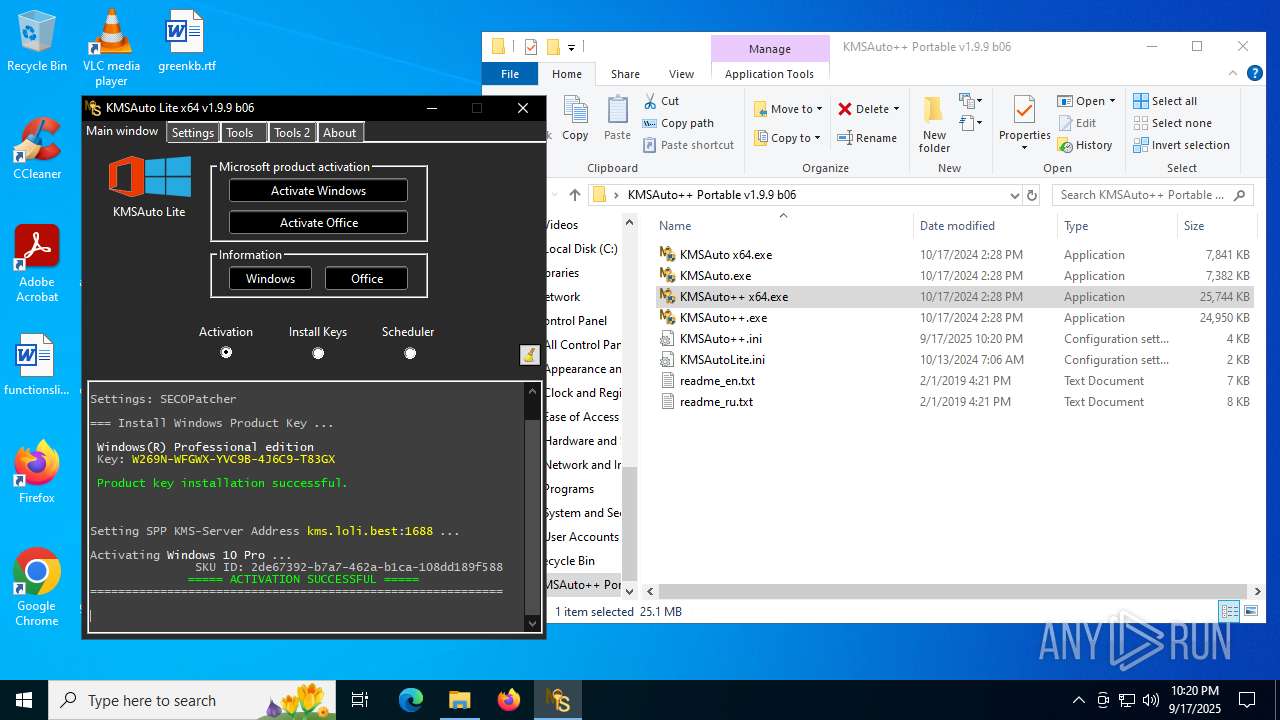
Starts SC.EXE for service management
- KMSAuto x64.exe (PID: 2728)
- KMSAuto++ x64.exe (PID: 4888)
Windows service management via SC.EXE
- sc.exe (PID: 4412)
- sc.exe (PID: 2356)
- sc.exe (PID: 4512)
- sc.exe (PID: 3876)
- sc.exe (PID: 5564)
- sc.exe (PID: 620)
Uses WMI to retrieve WMI-managed resources (SCRIPT)
- cscript.exe (PID: 4820)
- cscript.exe (PID: 5340)
- cscript.exe (PID: 188)
- cscript.exe (PID: 6304)
Checks whether a specific file exists (SCRIPT)
- cscript.exe (PID: 4820)
- cscript.exe (PID: 5340)
- cscript.exe (PID: 6304)
- cscript.exe (PID: 188)
Gets full path of the running script (SCRIPT)
- cscript.exe (PID: 4820)
- cscript.exe (PID: 5340)
- cscript.exe (PID: 188)
- cscript.exe (PID: 6304)
The process executes VB scripts
- cmd.exe (PID: 4892)
- cmd.exe (PID: 1864)
- cmd.exe (PID: 2280)
- cmd.exe (PID: 6808)
Creates FileSystem object to access computer's file system (SCRIPT)
- cscript.exe (PID: 4820)
- cscript.exe (PID: 5340)
- cscript.exe (PID: 6304)
- cscript.exe (PID: 188)
Executes WMI query (SCRIPT)
- cscript.exe (PID: 4820)
- cscript.exe (PID: 5340)
- cscript.exe (PID: 188)
- cscript.exe (PID: 6304)
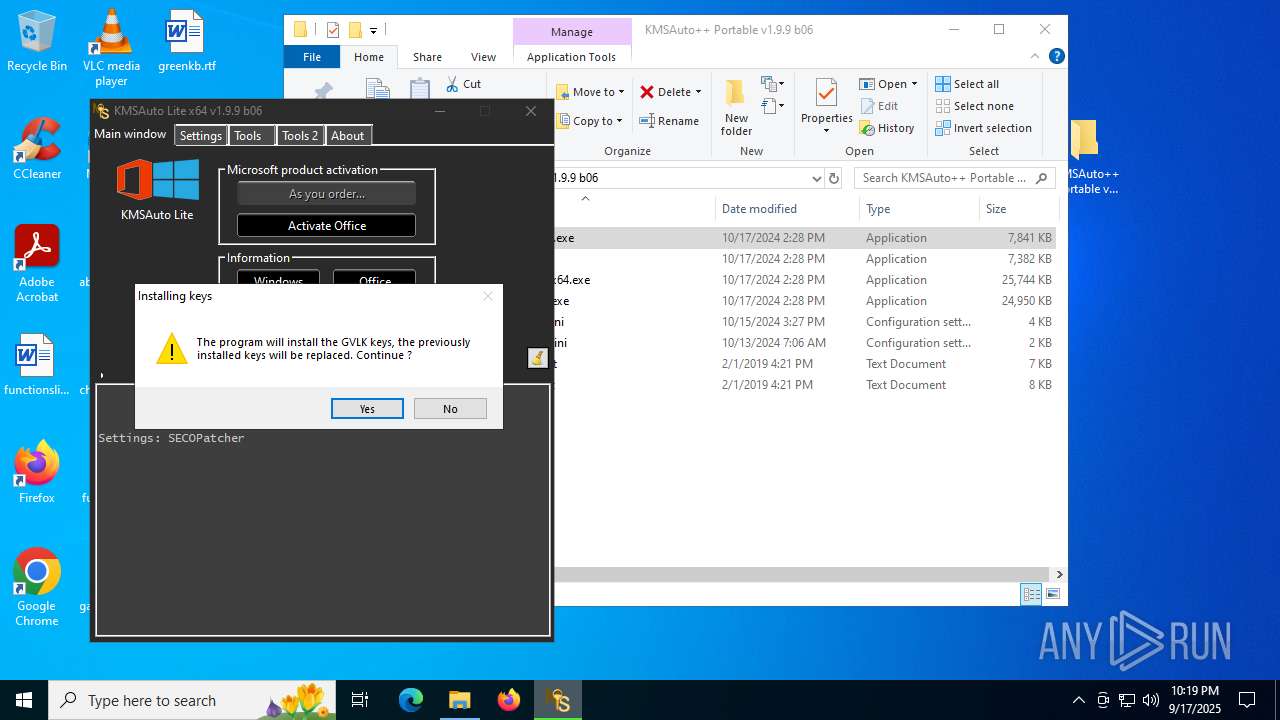
Uses REG/REGEDIT.EXE to modify registry
- cmd.exe (PID: 4912)
- cmd.exe (PID: 5400)
- cmd.exe (PID: 4688)
- cmd.exe (PID: 2168)
INFO
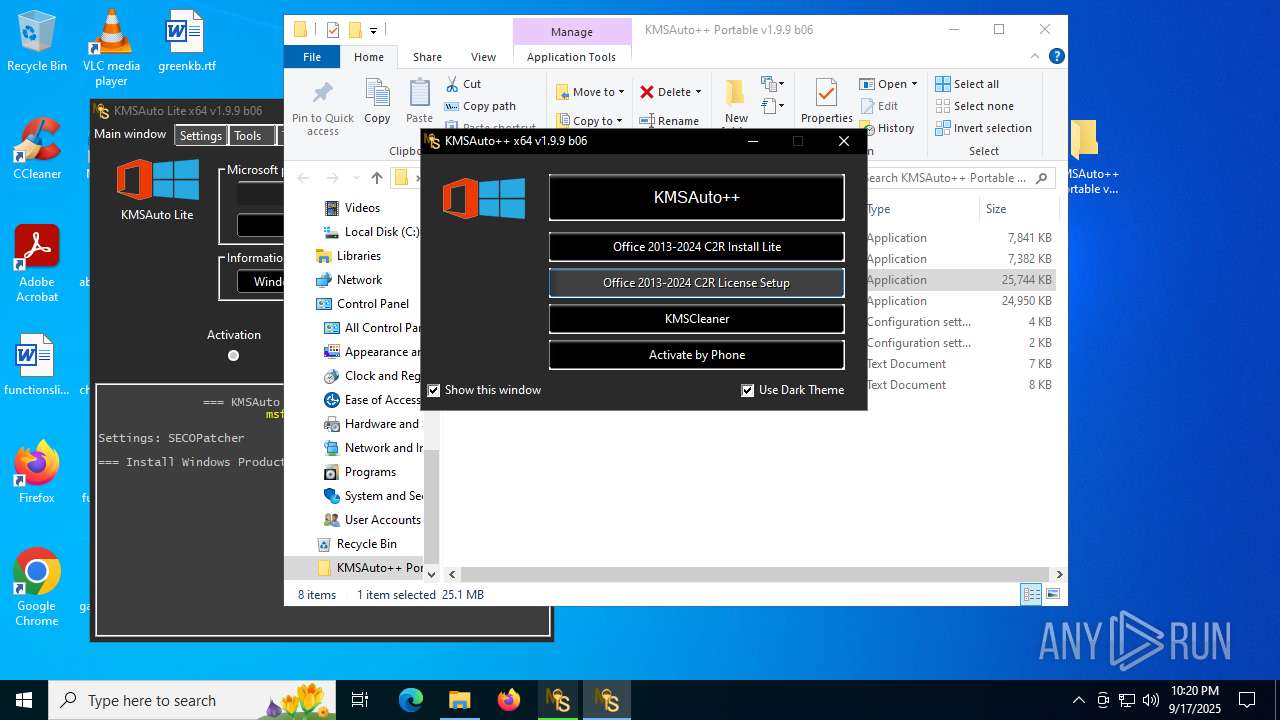
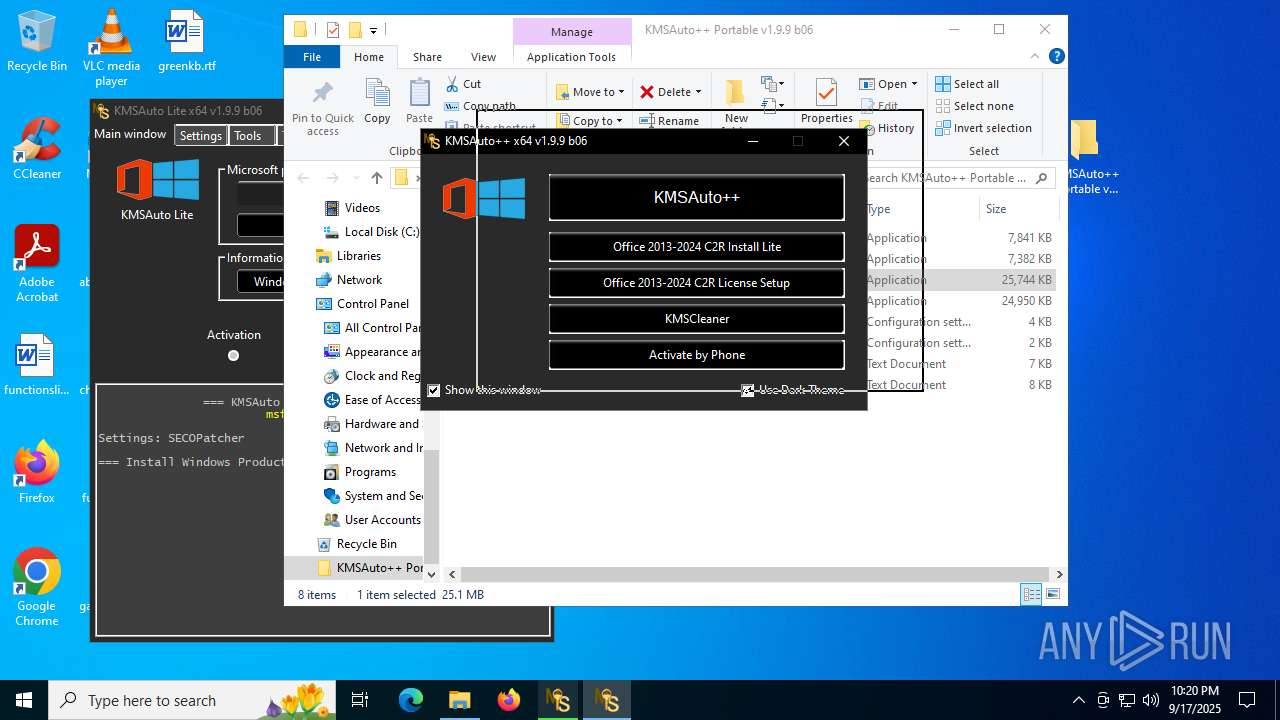
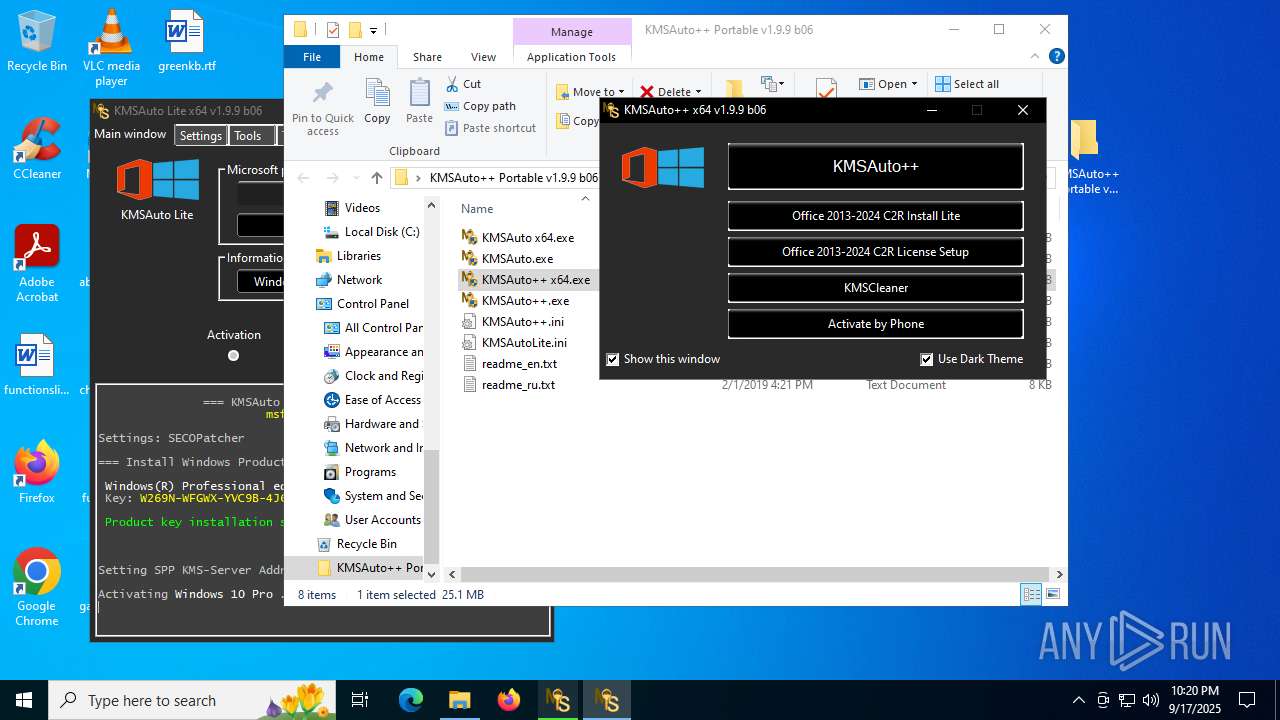
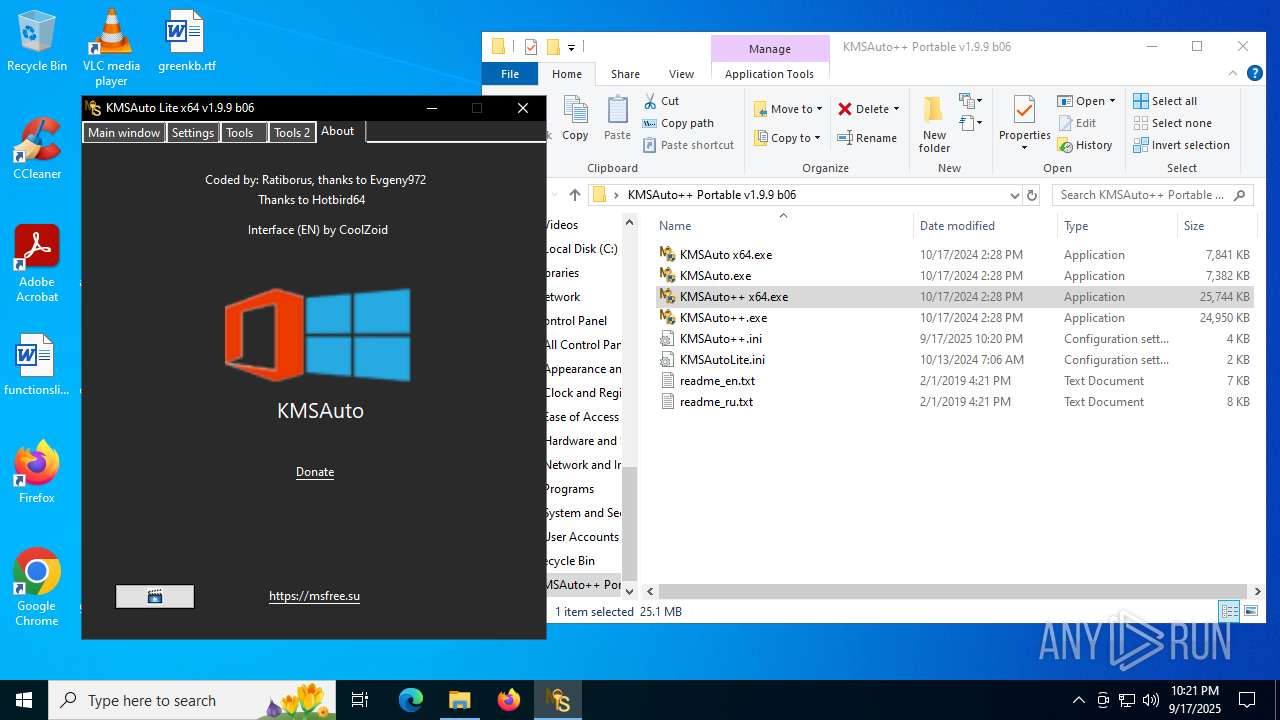
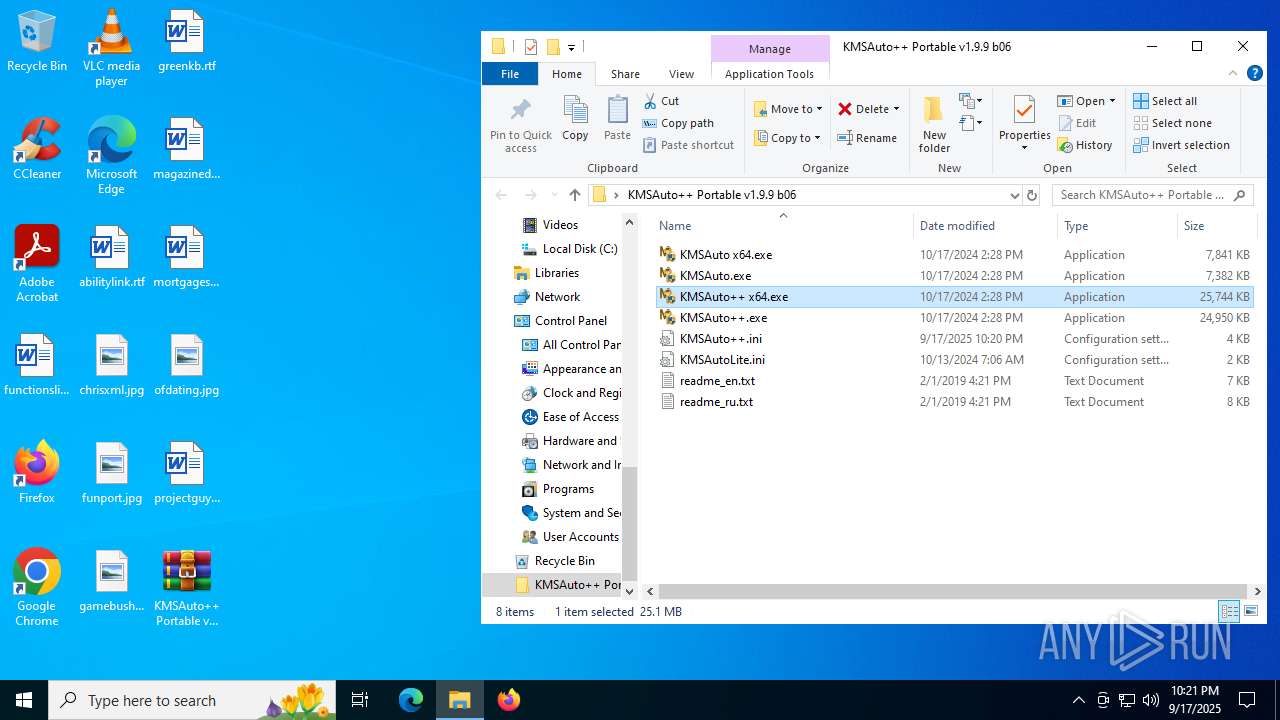
Manual execution by a user
- KMSAuto x64.exe (PID: 5500)
- KMSAuto x64.exe (PID: 2728)
- KMSAuto++ x64.exe (PID: 1468)
- KMSAuto++ x64.exe (PID: 4888)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 236)
Checks supported languages
- KMSAuto x64.exe (PID: 2728)
- KMSAuto++ x64.exe (PID: 4888)
Reads security settings of Internet Explorer
- cscript.exe (PID: 4820)
- cscript.exe (PID: 5340)
- cscript.exe (PID: 6304)
- cscript.exe (PID: 188)
Reads product name
- KMSAuto x64.exe (PID: 2728)
- KMSAuto++ x64.exe (PID: 4888)
Create files in a temporary directory
- KMSAuto x64.exe (PID: 2728)
- KMSAuto++ x64.exe (PID: 4888)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .7z | | | 7-Zip compressed archive (v0.4) (57.1) |
|---|---|---|
| .7z | | | 7-Zip compressed archive (gen) (42.8) |
EXIF
ZIP
| FileVersion: | 7z v0.04 |
|---|
Total processes
209
Monitored processes
62
Malicious processes
9
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 188 | cscript //nologo "C:\Users\admin\AppData\Local\Temp\slmgr.vbs" /skms kms.loli.best:1688 | C:\Windows\System32\cscript.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft ® Console Based Script Host Exit code: 0 Version: 5.812.10240.16384 Modules
| |||||||||||||||
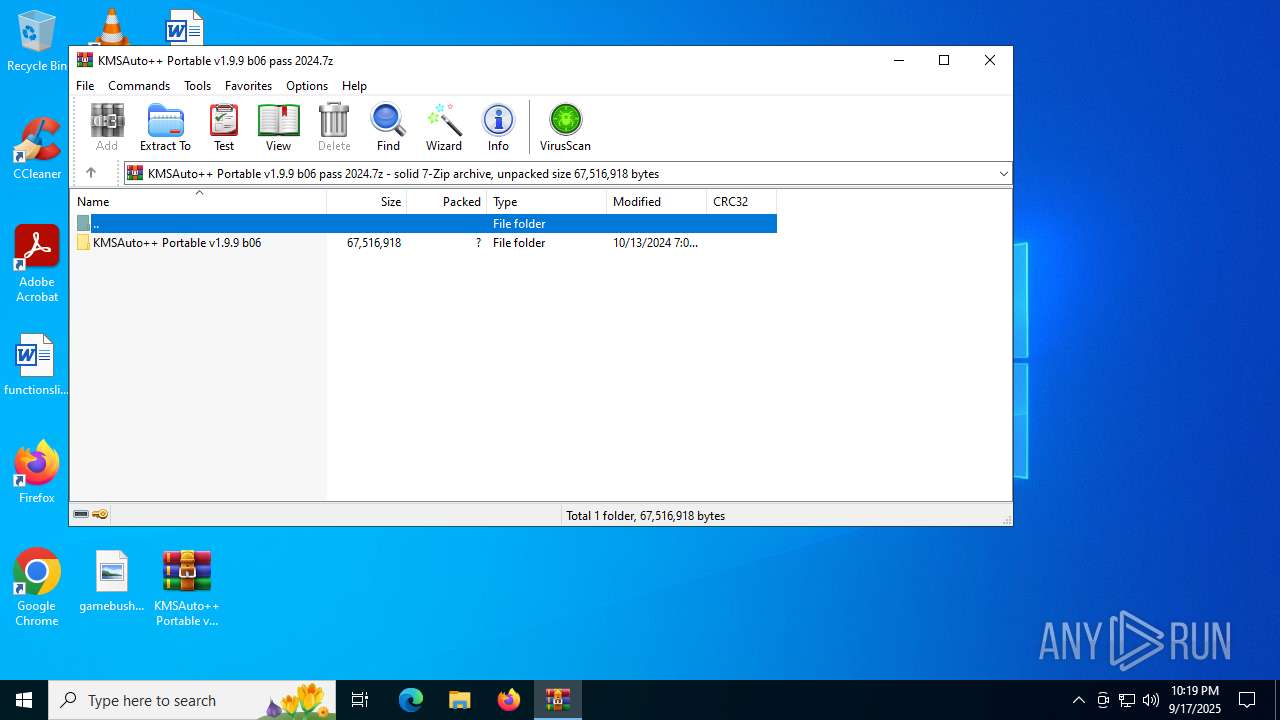
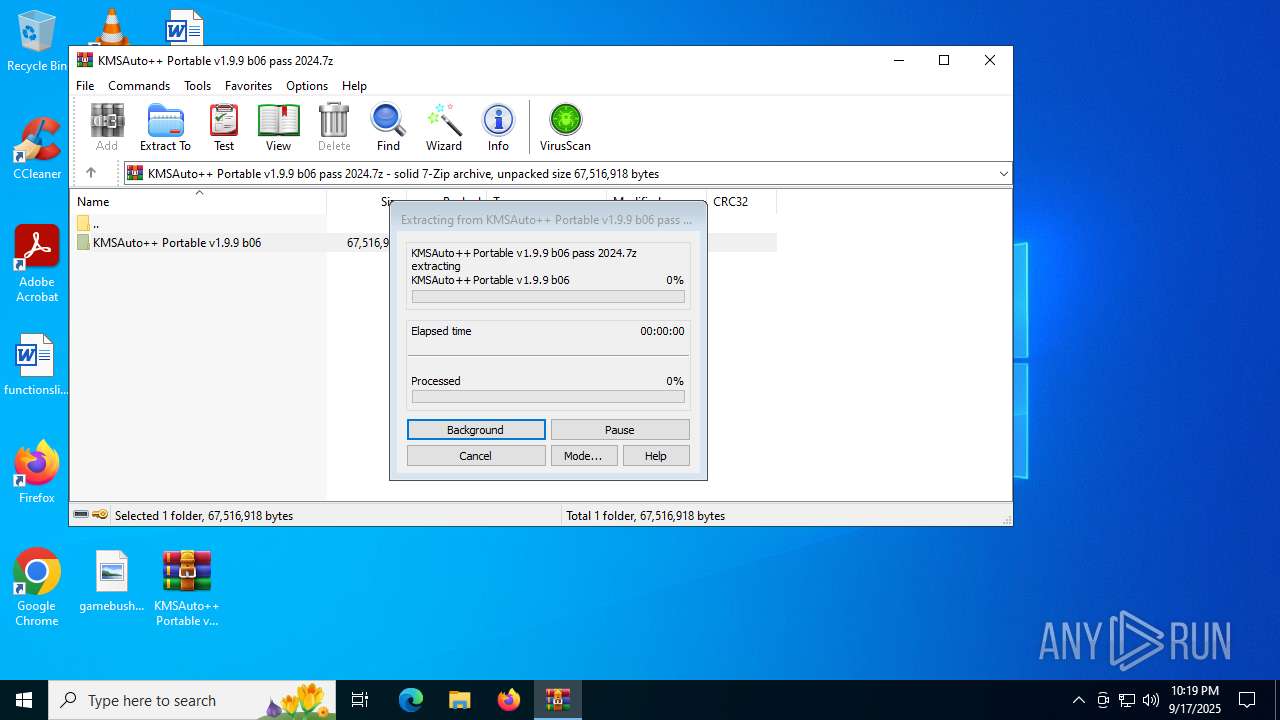
| 236 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Desktop\KMSAuto++ Portable v1.9.9 b06 pass 2024.7z" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 424 | "C:\WINDOWS\System32\reg.exe" query "HKEY_LOCAL_MACHINE\SOFTWARE\Policies\Microsoft\Windows Defender" /v DisableAntiSpyware | C:\Windows\System32\reg.exe | — | KMSAuto++ x64.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 536 | "C:\WINDOWS\System32\reg.exe" query "HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows Defender" /v DisableAntiSpyware | C:\Windows\System32\reg.exe | — | KMSAuto++ x64.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 620 | "C:\WINDOWS\System32\sc.exe" query SecurityHealthService | C:\Windows\System32\sc.exe | — | KMSAuto++ x64.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Service Control Manager Configuration Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
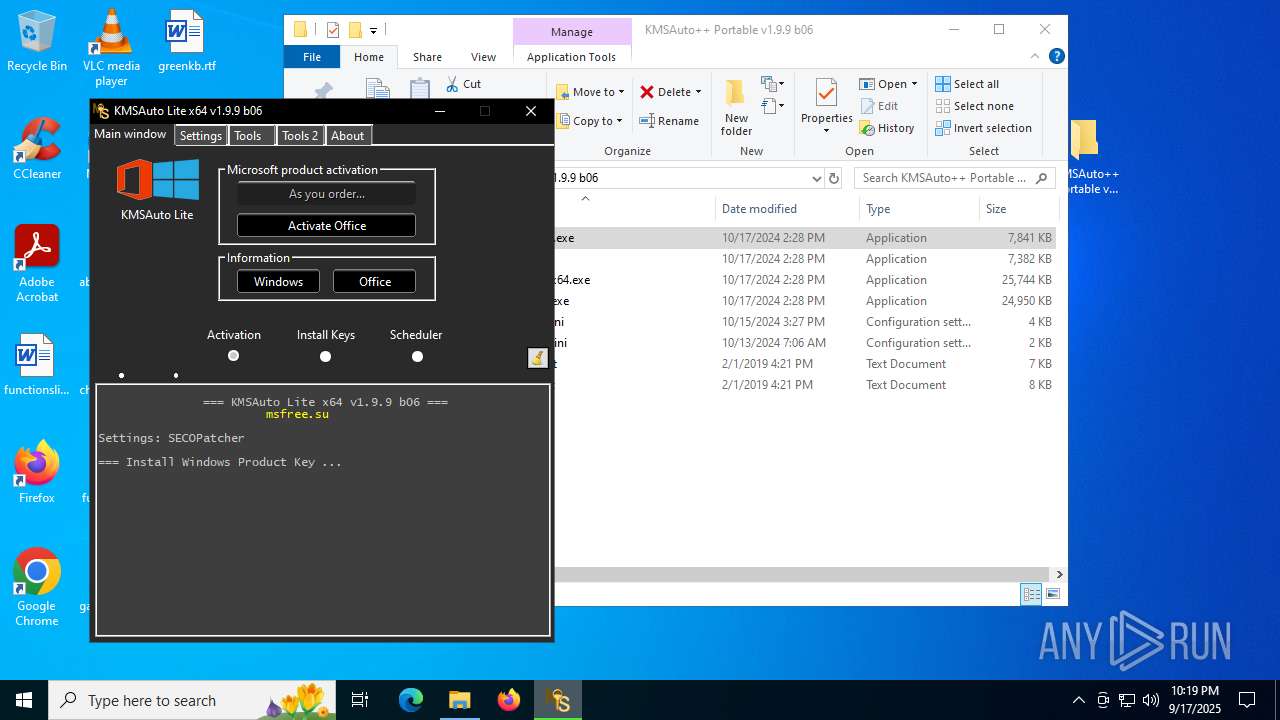
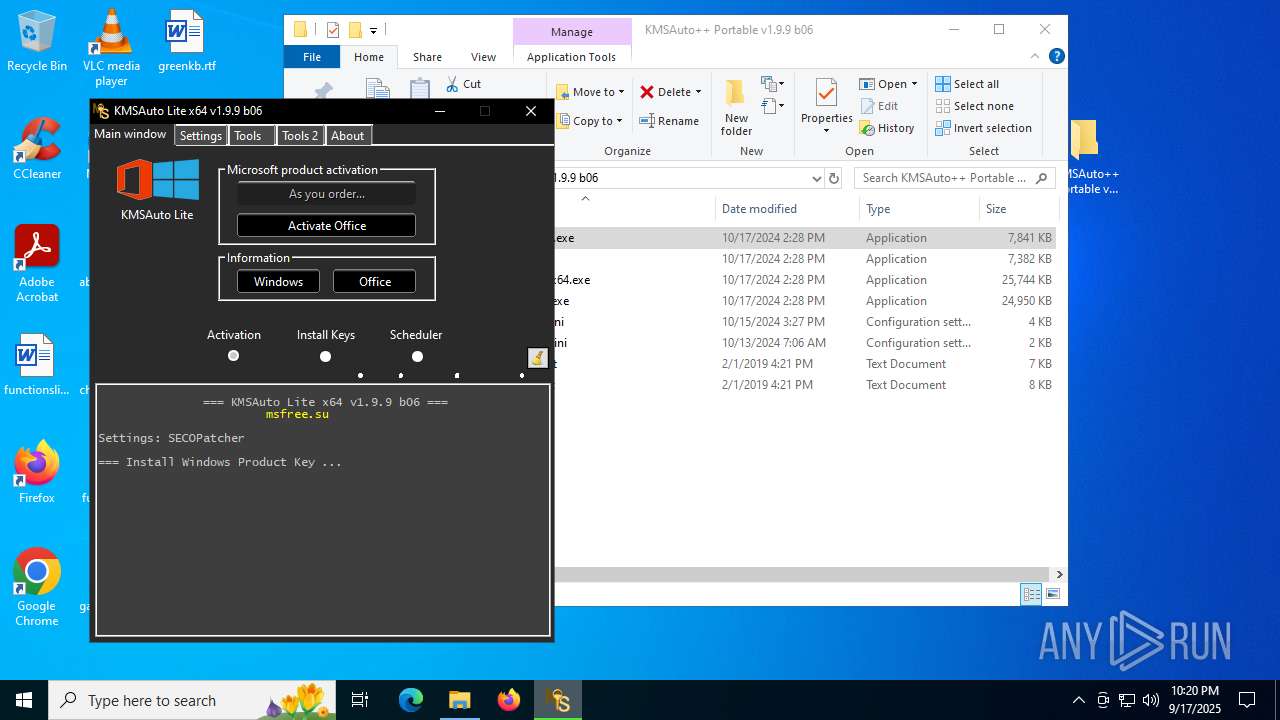
| 700 | reg.exe add "HKEY_LOCAL_MACHINE\Software\Microsoft\Windows NT\CurrentVersion\SoftwareProtectionPlatform" /f /v KeyManagementServicePort /d 1688 /t REG_SZ /reg:32 | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1332 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1468 | "C:\Users\admin\Desktop\KMSAuto++ Portable v1.9.9 b06\KMSAuto++ x64.exe" | C:\Users\admin\Desktop\KMSAuto++ Portable v1.9.9 b06\KMSAuto++ x64.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 1864 | "C:\WINDOWS\System32\cmd.exe" /c cscript //nologo "C:\Users\admin\AppData\Local\Temp\slmgr.vbs" /ipk W269N-WFGWX-YVC9B-4J6C9-T83GX | C:\Windows\System32\cmd.exe | — | KMSAuto x64.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1880 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
4 257
Read events
4 231
Write events
26
Delete events
0
Modification events
| (PID) Process: | (236) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
| (PID) Process: | (236) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (236) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (236) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (236) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\KMSAuto++ Portable v1.9.9 b06 pass 2024.7z | |||
| (PID) Process: | (236) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (236) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (236) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (236) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (236) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\MainWin |
| Operation: | write | Name: | Placement |
Value: 2C0000000000000001000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF3D0000002D000000FD03000016020000 | |||
Executable files
4
Suspicious files
0
Text files
5
Unknown types
0
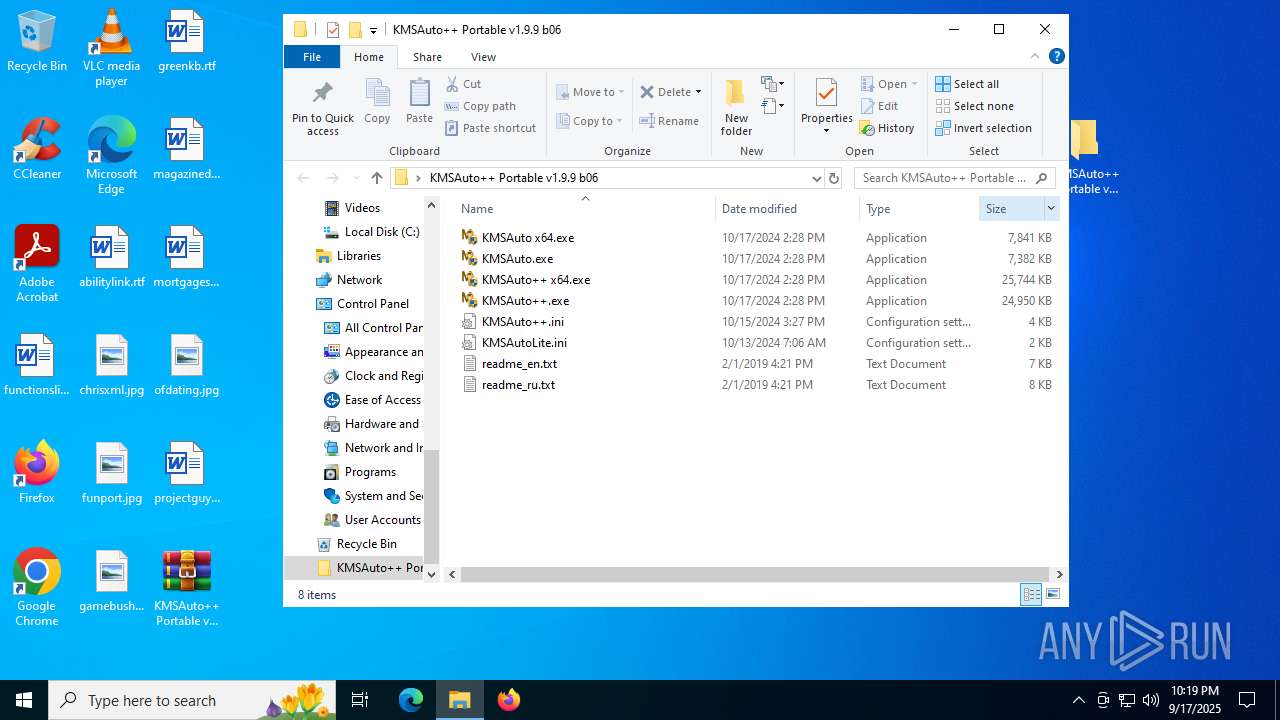
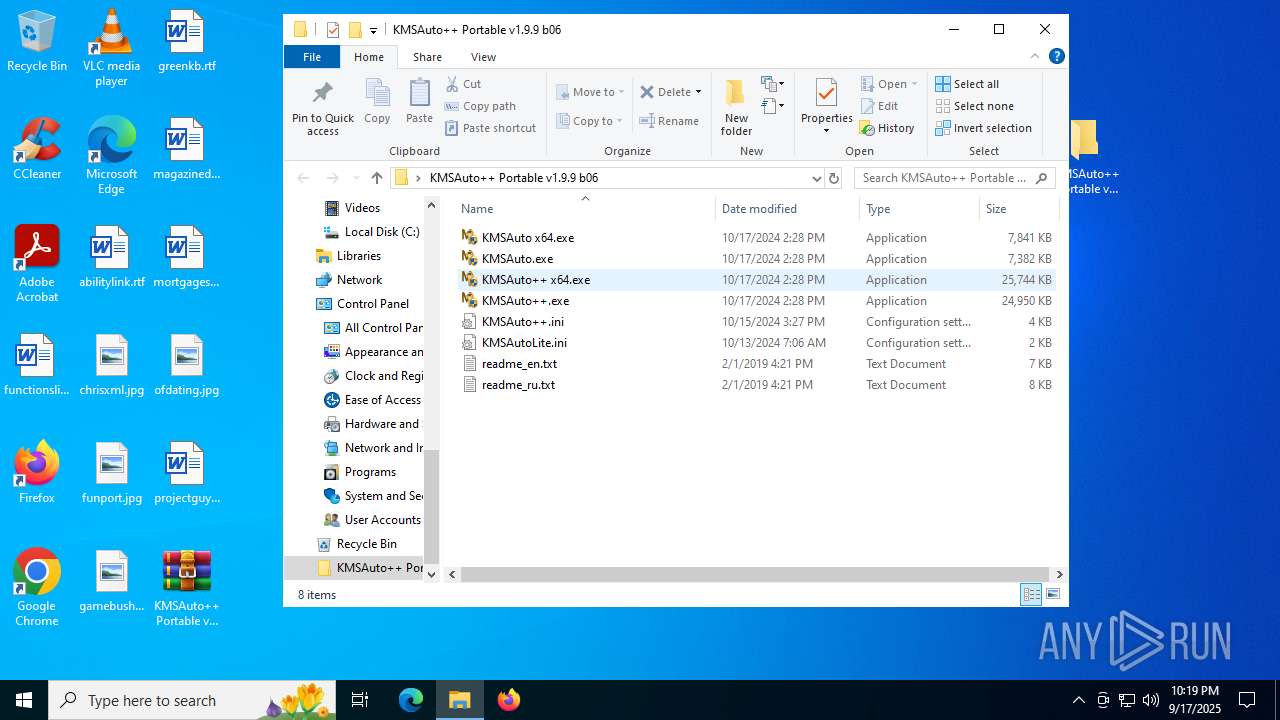
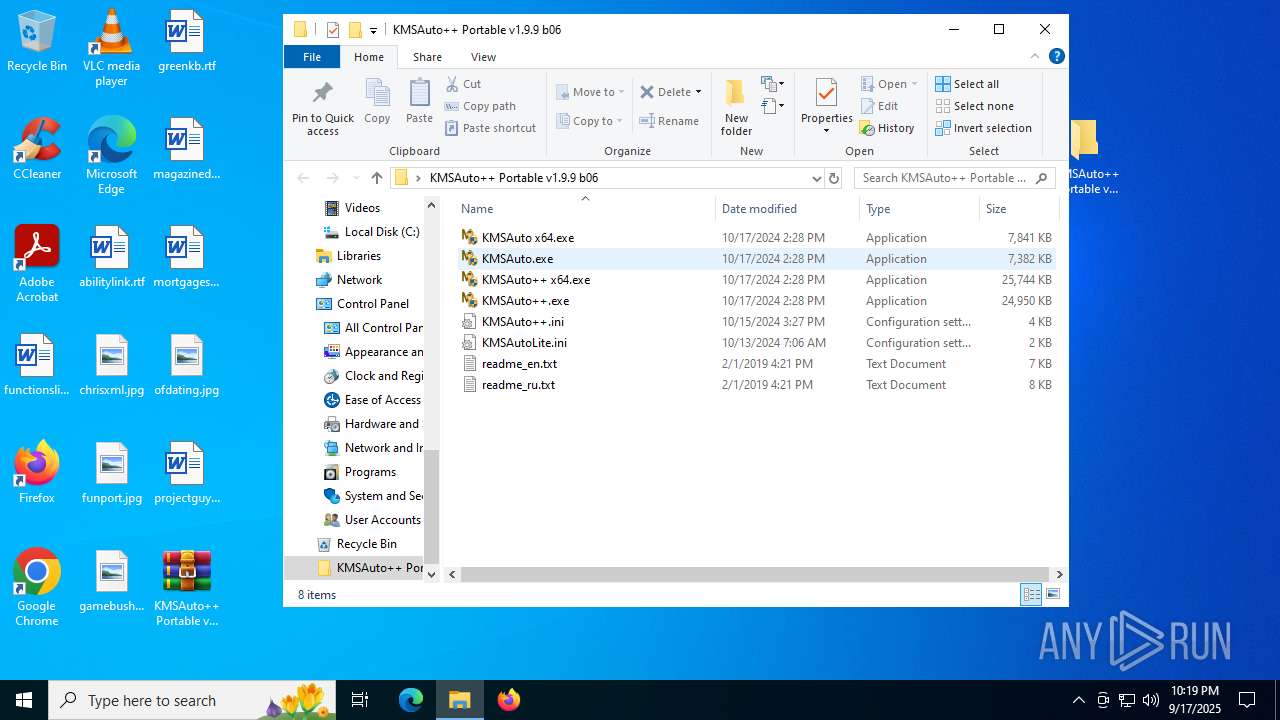
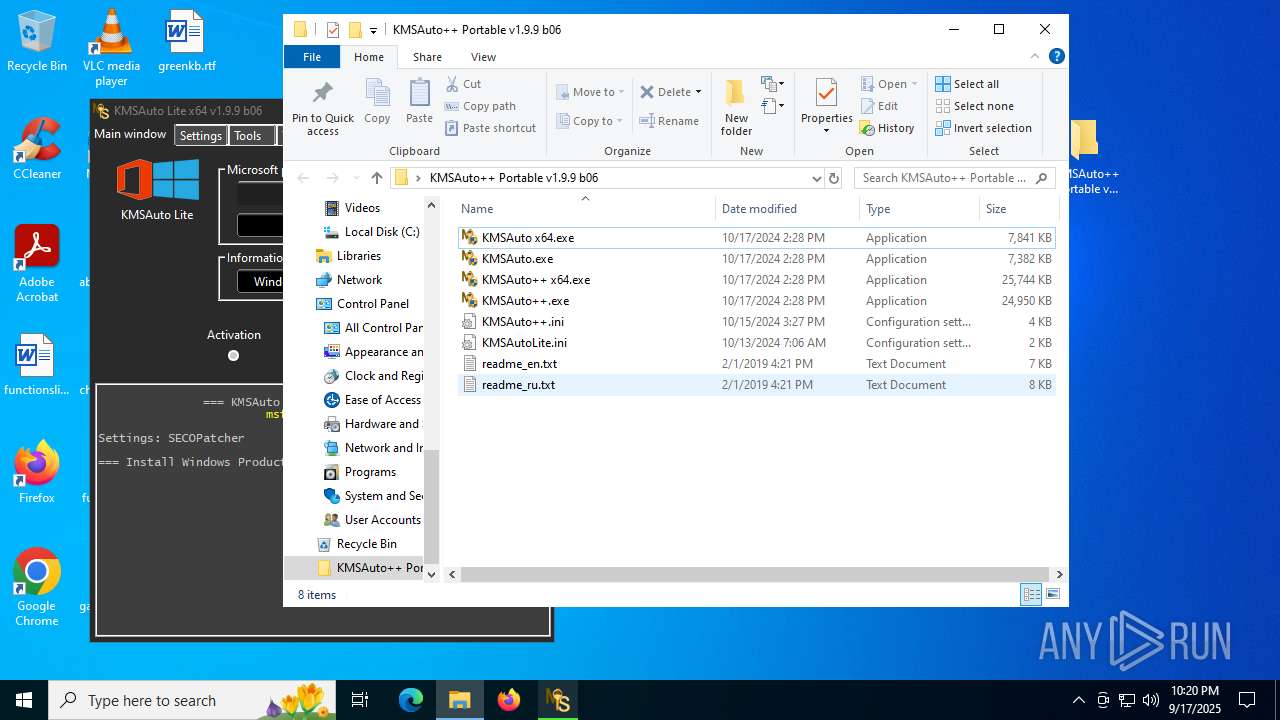
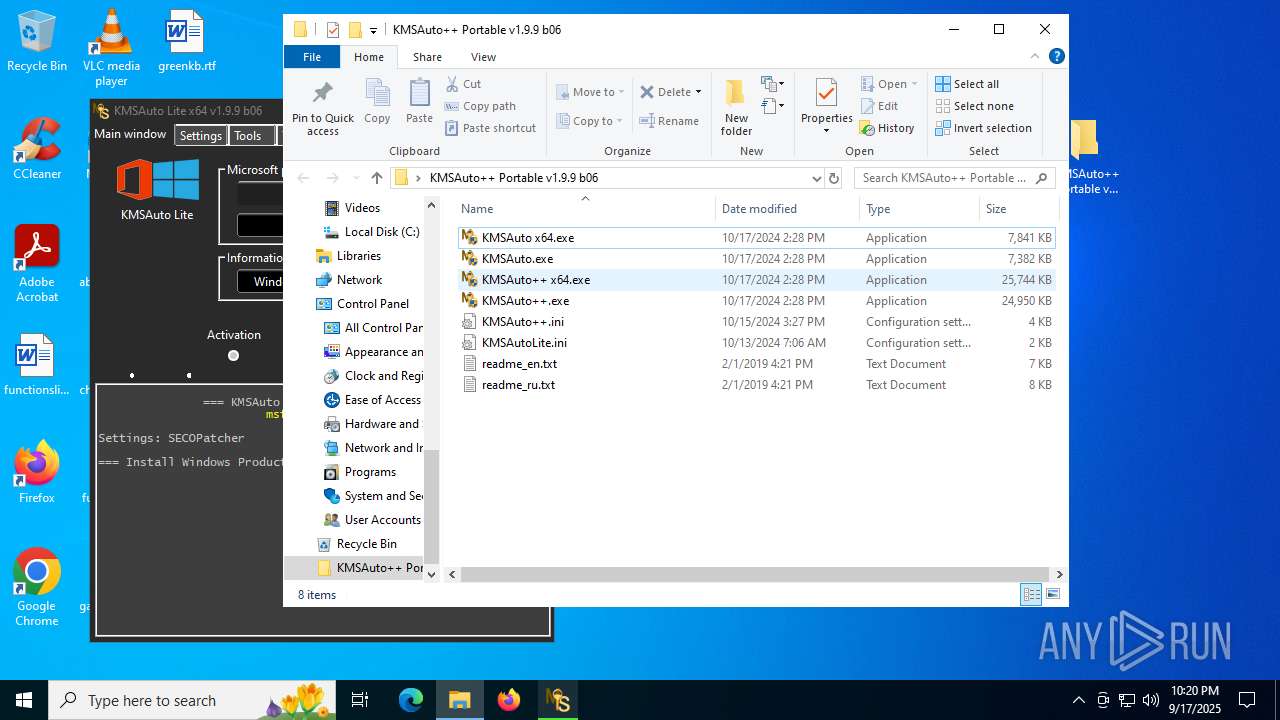
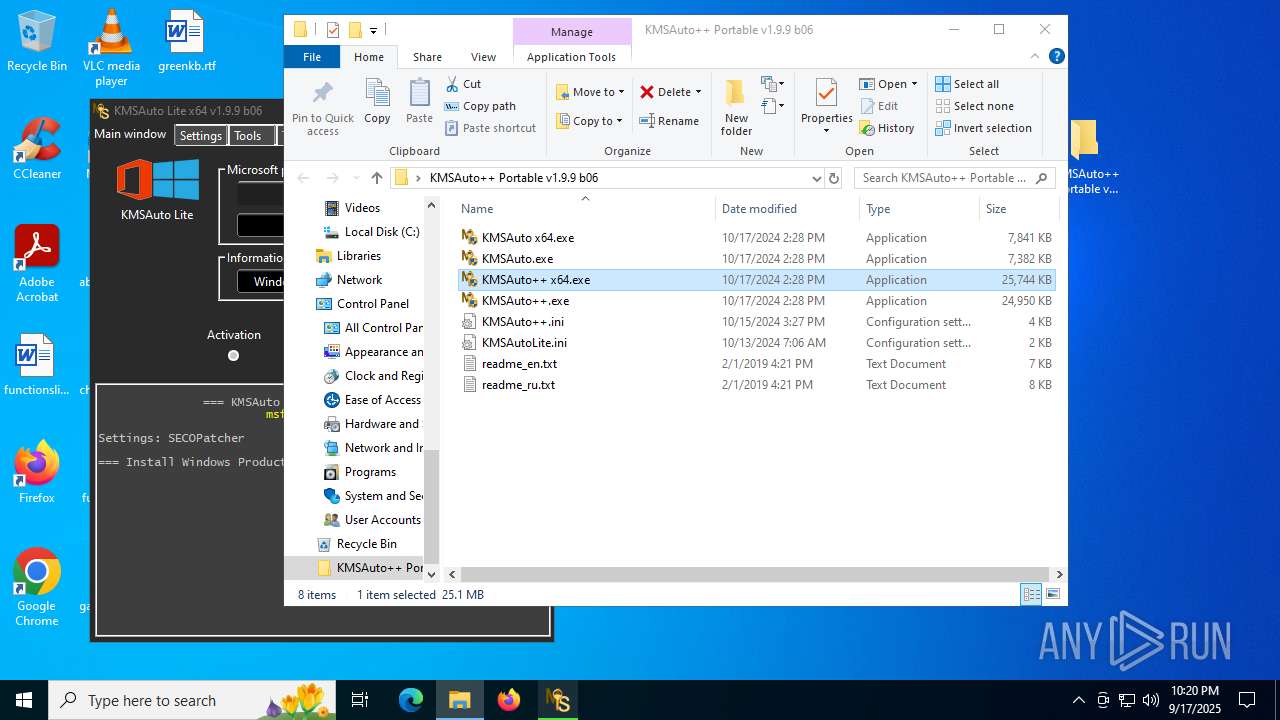
Dropped files
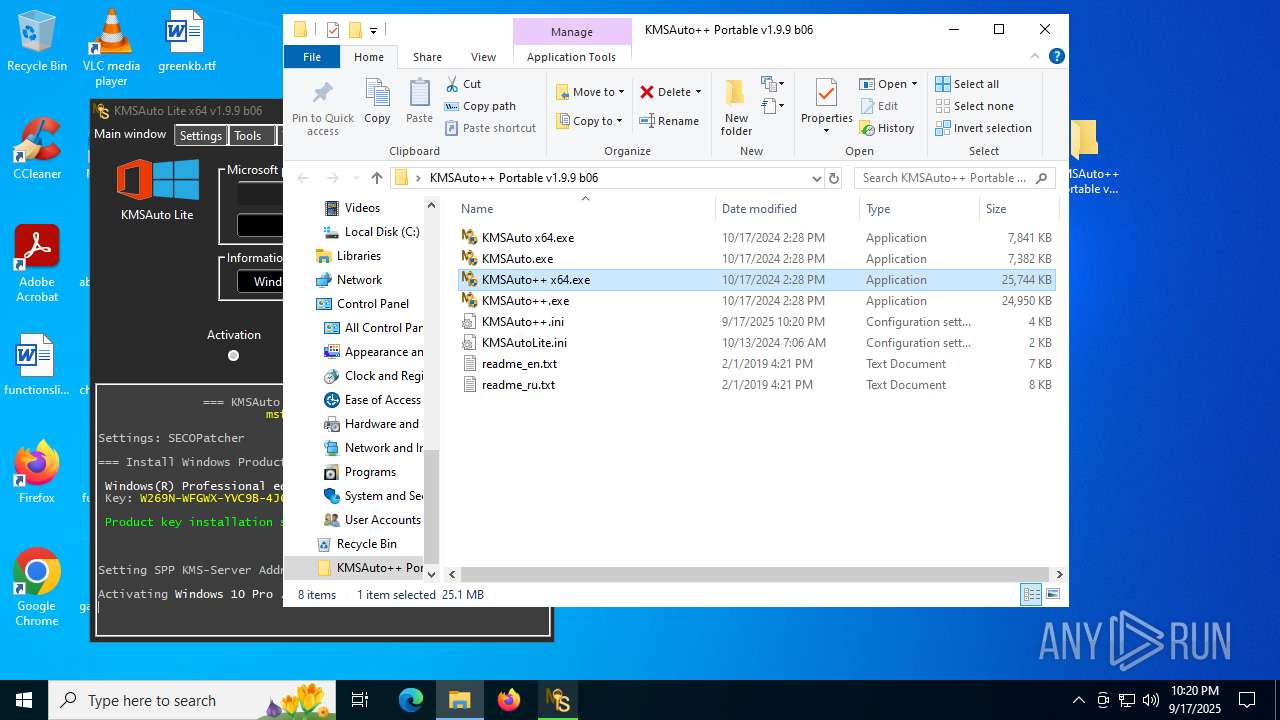
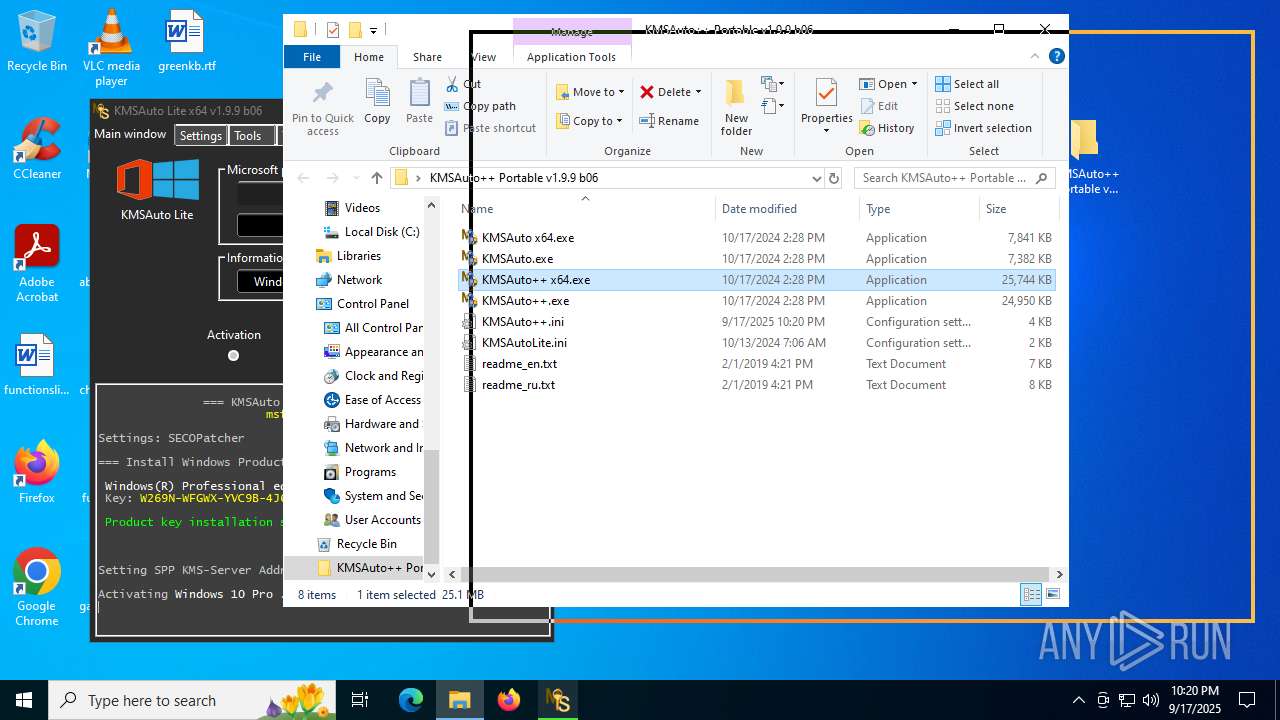
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 236 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb236.20407\KMSAuto++ Portable v1.9.9 b06\KMSAuto x64.exe | executable | |
MD5:79231A73533F237D64BECC7AD95584B9 | SHA256:C2C47FDAFAB559F05907DAB7865EF1F3B84C3B7C6B6E7BEE24CD708A55269CF6 | |||
| 236 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb236.20407\KMSAuto++ Portable v1.9.9 b06\KMSAuto++.ini | text | |
MD5:BC0334923377BD5E30A84695A347BBE8 | SHA256:CE273D0485CEDEF6540F290D0332ADE2A2AC853A723C780BC439B70C37FC8F98 | |||
| 236 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb236.20407\KMSAuto++ Portable v1.9.9 b06\KMSAuto.exe | executable | |
MD5:D798854AC7161951BF8D224F3505A4D7 | SHA256:26145F0E7ED61CDD31C6236D19FD1627B28928D672BBFF09312557C8E57FFCFC | |||
| 236 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb236.20407\KMSAuto++ Portable v1.9.9 b06\KMSAuto++ x64.exe | executable | |
MD5:E228E241AAE4651B107F08179B9E9089 | SHA256:E4FD36E9E3C1ED840A08097AC4DAAA59F9FA9449997DB6A7E0B99EA0C01CDD2B | |||
| 236 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb236.20407\KMSAuto++ Portable v1.9.9 b06\KMSAuto++.exe | executable | |
MD5:324C898621297AF29E77076909BF52F9 | SHA256:6785EC0D7D578777E46016DDB03894B344E30A5025F4A1B9E7A4642CBA14131F | |||
| 2728 | KMSAuto x64.exe | C:\Users\admin\AppData\Local\Temp\slmgr.vbs | text | |
MD5:3903BCAB32A4A853DFA54962112D4D02 | SHA256:95FC646D222D324DB46F603A7F675C329FE59A567ED27FDAED2A572A19206816 | |||
| 236 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb236.20407\KMSAuto++ Portable v1.9.9 b06\readme_ru.txt | text | |
MD5:89921EBFDAC4677B4ECC8972B2880FA8 | SHA256:F82E3B77099BAF8C31F2C6F81F511B049EC5D08D3848834076AFD401FAB143DB | |||
| 236 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb236.20407\KMSAuto++ Portable v1.9.9 b06\readme_en.txt | text | |
MD5:7A4FB804AF171AD041C65E3E46FD00B2 | SHA256:C7A2D7FA7DCF9A08A5179720F81B947221F0E94BC797878352ECAE52D923C939 | |||
| 236 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb236.20407\KMSAuto++ Portable v1.9.9 b06\KMSAutoLite.ini | text | |
MD5:2A86E9EA22AEA5E9045FCE2E3C7BADBA | SHA256:9778EF93C59CA1E6E86F82E2FC01121BD4A76D0176B2D710D7FF64322A6F6567 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
16
TCP/UDP connections
43
DNS requests
27
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2064 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | DE | binary | 471 b | whitelisted |
1268 | svchost.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | NL | binary | 814 b | whitelisted |
1268 | svchost.exe | GET | 200 | 23.55.110.193:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | DE | binary | 825 b | whitelisted |
4916 | SIHClient.exe | GET | 200 | 23.55.110.193:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut_2010-06-23.crl | DE | binary | 824 b | whitelisted |
4916 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | NL | binary | 407 b | whitelisted |
4916 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | NL | binary | 419 b | whitelisted |
4916 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20Update%20Signing%20CA%202.2.crl | NL | binary | 813 b | whitelisted |
4916 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20Time-Stamp%20PCA%202010(1).crl | NL | binary | 814 b | whitelisted |
4916 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Signing%20CA%202.2.crl | NL | binary | 400 b | whitelisted |
4916 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20Update%20Signing%20CA%202.1.crl | NL | binary | 813 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
5944 | MoUsoCoreWorker.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1268 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5288 | RUXIMICS.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2064 | svchost.exe | 20.190.159.128:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2064 | svchost.exe | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
1268 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1268 | svchost.exe | 23.55.110.193:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
1268 | svchost.exe | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
self.events.data.microsoft.com |
| whitelisted |