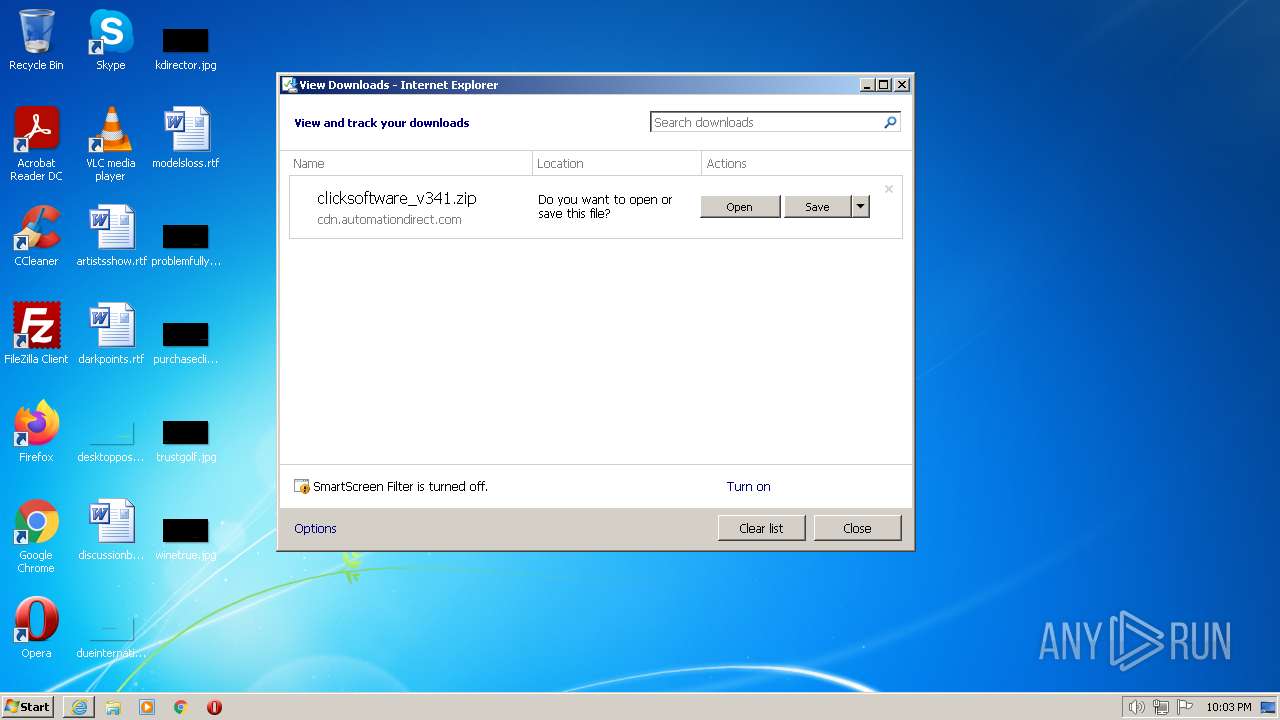
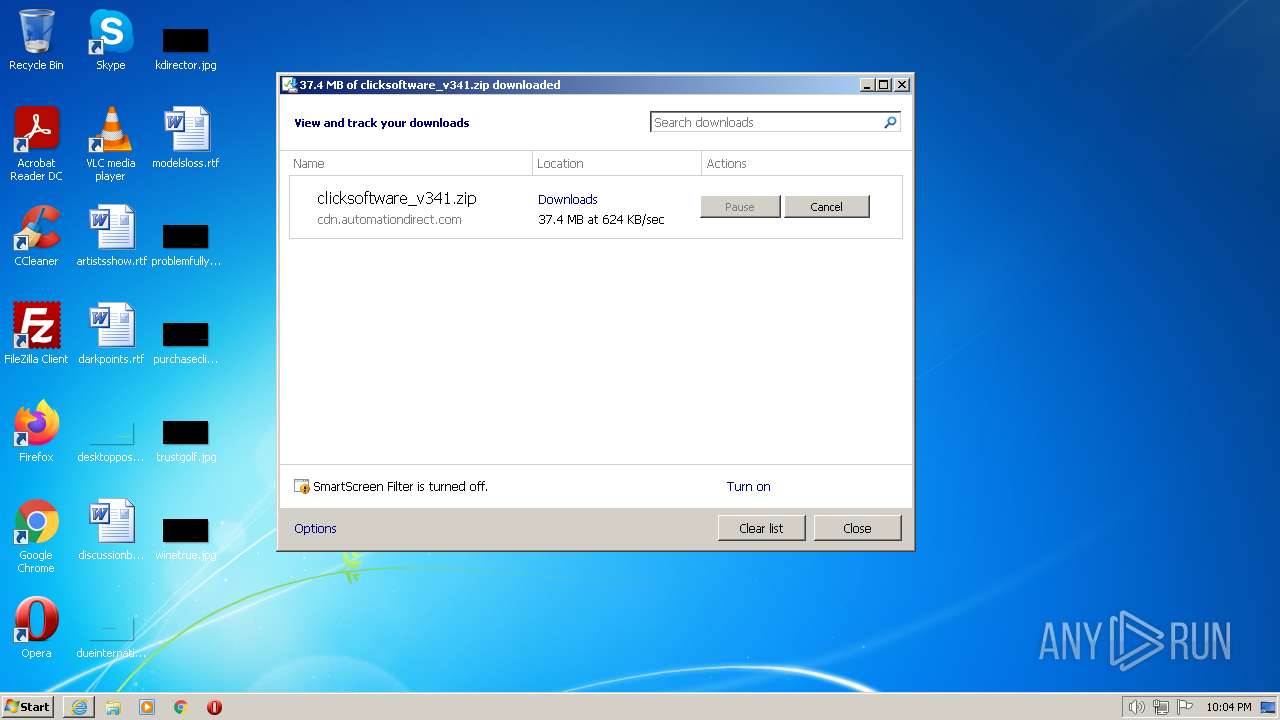
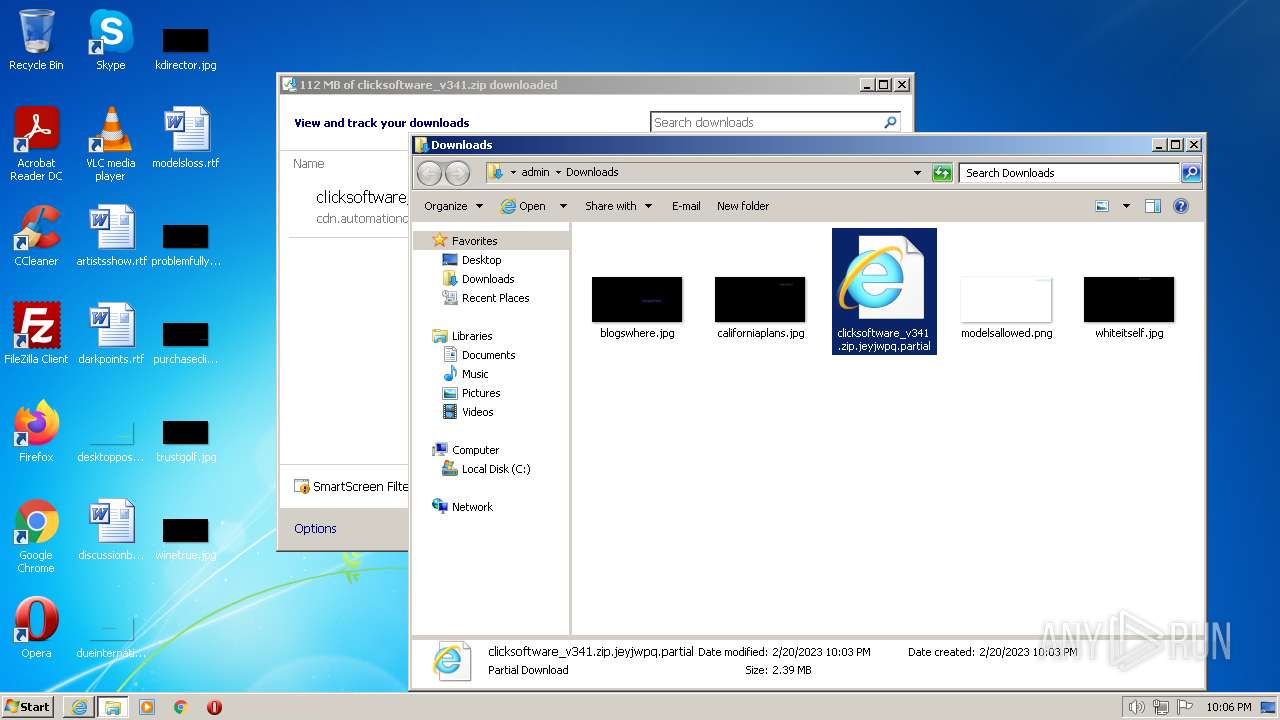
| URL: | https://cdn.automationdirect.com/static/software/clicksoftware_v341.zip |
| Full analysis: | https://app.any.run/tasks/6d82b3c9-3c29-4920-8d1a-9b43eddb8040 |
| Verdict: | Malicious activity |
| Analysis date: | February 20, 2023, 22:02:53 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 6673F1E71289FB65BF894C5078CBD67C |
| SHA1: | 065FCC2A3930D4E66DB2E7B2446318CF47F7FDC4 |
| SHA256: | 5DE01ABE8BAECC41D54068C452CDE75FAFFCB8B3A8829BBFCE2934B6F28B79EA |
| SSDEEP: | 3:N8c6PMKl3nBGKtRRSyTWRUrUn:2cctVR0ya9n |
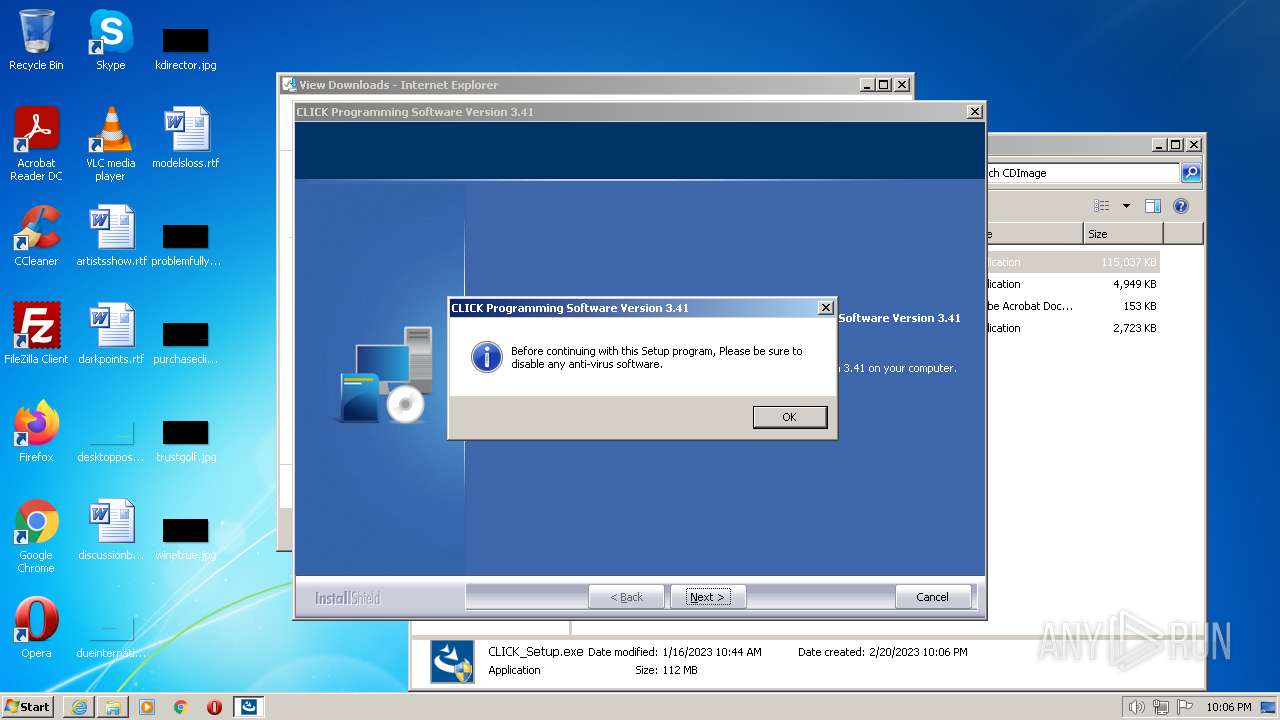
MALICIOUS
Drops the executable file immediately after the start
- CLICK_Setup.exe (PID: 2556)
- CLICK_Setup.exe (PID: 3164)
Loads dropped or rewritten executable
- CLICK_Setup.exe (PID: 3164)
Application was dropped or rewritten from another process
- CLICK_Setup.exe (PID: 3164)
SUSPICIOUS
Executable content was dropped or overwritten
- CLICK_Setup.exe (PID: 2556)
- CLICK_Setup.exe (PID: 3164)
Drops a file with too old compile date
- CLICK_Setup.exe (PID: 2556)
- CLICK_Setup.exe (PID: 3164)
Reads the Windows owner or organization settings
- CLICK_Setup.exe (PID: 3164)
Executes as Windows Service
- vssvc.exe (PID: 3072)
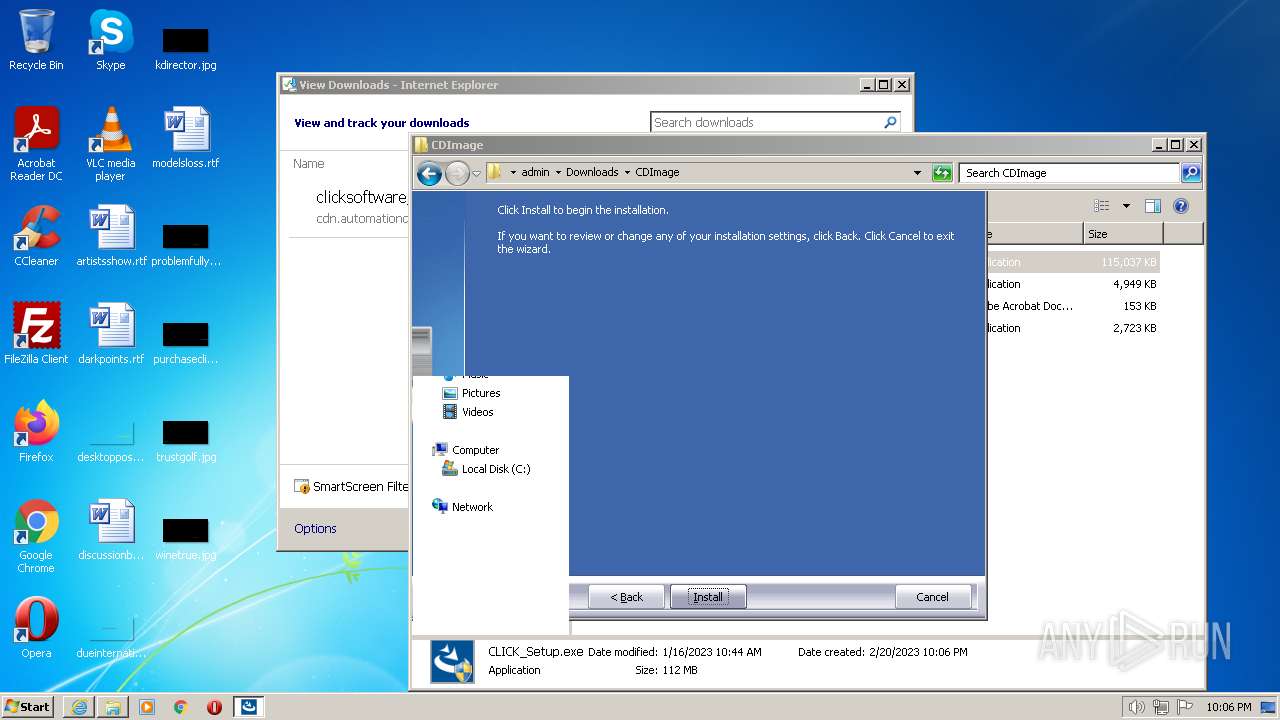
Changes default file association
- CLICK_Setup.exe (PID: 3164)
Searches for installed software
- CLICK_Setup.exe (PID: 3164)
INFO
Create files in a temporary directory
- iexplore.exe (PID: 1240)
- CLICK_Setup.exe (PID: 2556)
- CLICK_Setup.exe (PID: 3164)
Reads the computer name
- wmpnscfg.exe (PID: 912)
- CLICK_Setup.exe (PID: 2556)
- CLICK_Setup.exe (PID: 3164)
Application launched itself
- iexplore.exe (PID: 1240)
Checks supported languages
- wmpnscfg.exe (PID: 912)
- CLICK_Setup.exe (PID: 2556)
- CLICK_Setup.exe (PID: 3164)
Modifies the phishing filter of IE
- iexplore.exe (PID: 1240)
The process uses the downloaded file
- iexplore.exe (PID: 1240)
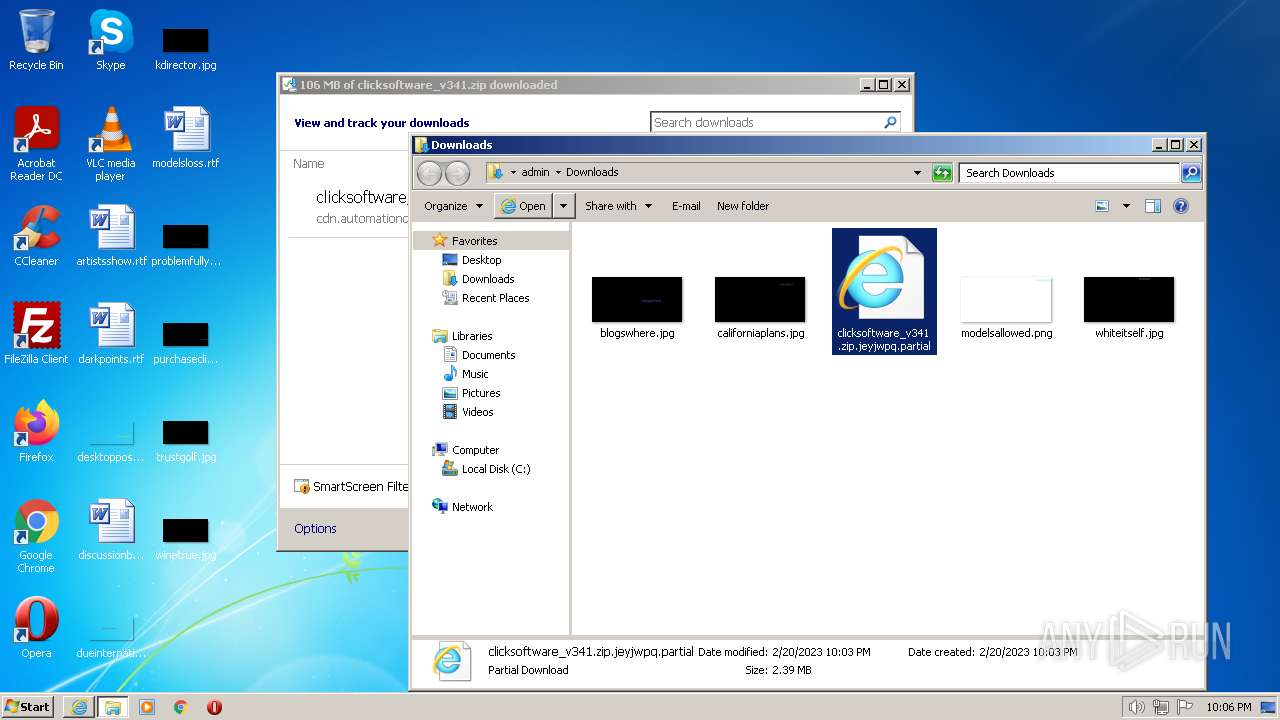
- WinRAR.exe (PID: 3004)
The process checks LSA protection
- wmpnscfg.exe (PID: 912)
- CLICK_Setup.exe (PID: 2556)
- CLICK_Setup.exe (PID: 3164)
- vssvc.exe (PID: 3072)
Reads the machine GUID from the registry
- wmpnscfg.exe (PID: 912)
- CLICK_Setup.exe (PID: 3164)
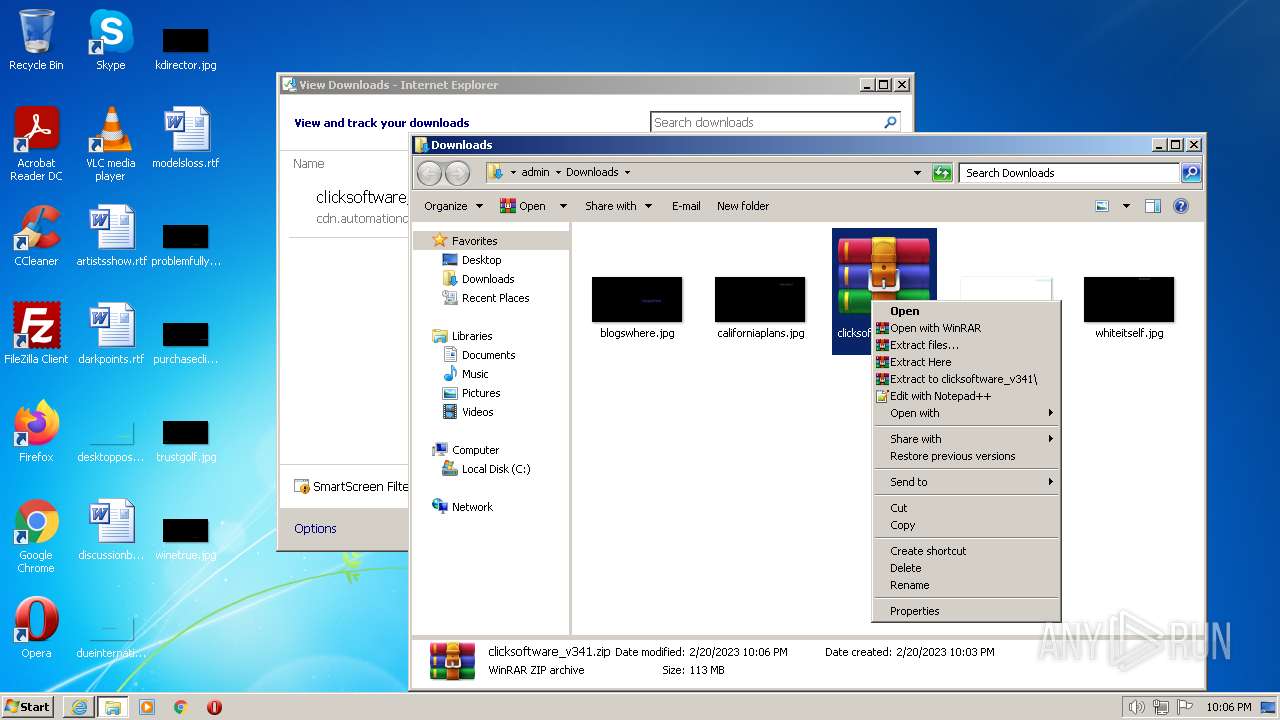
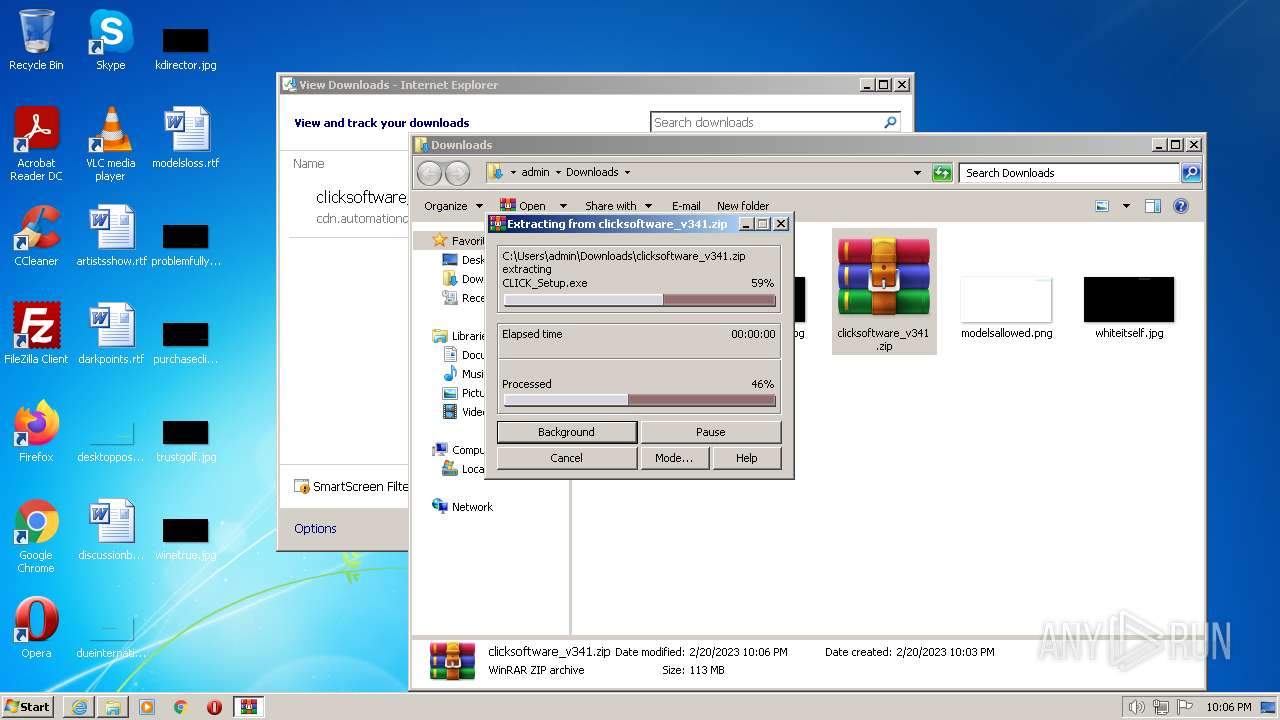
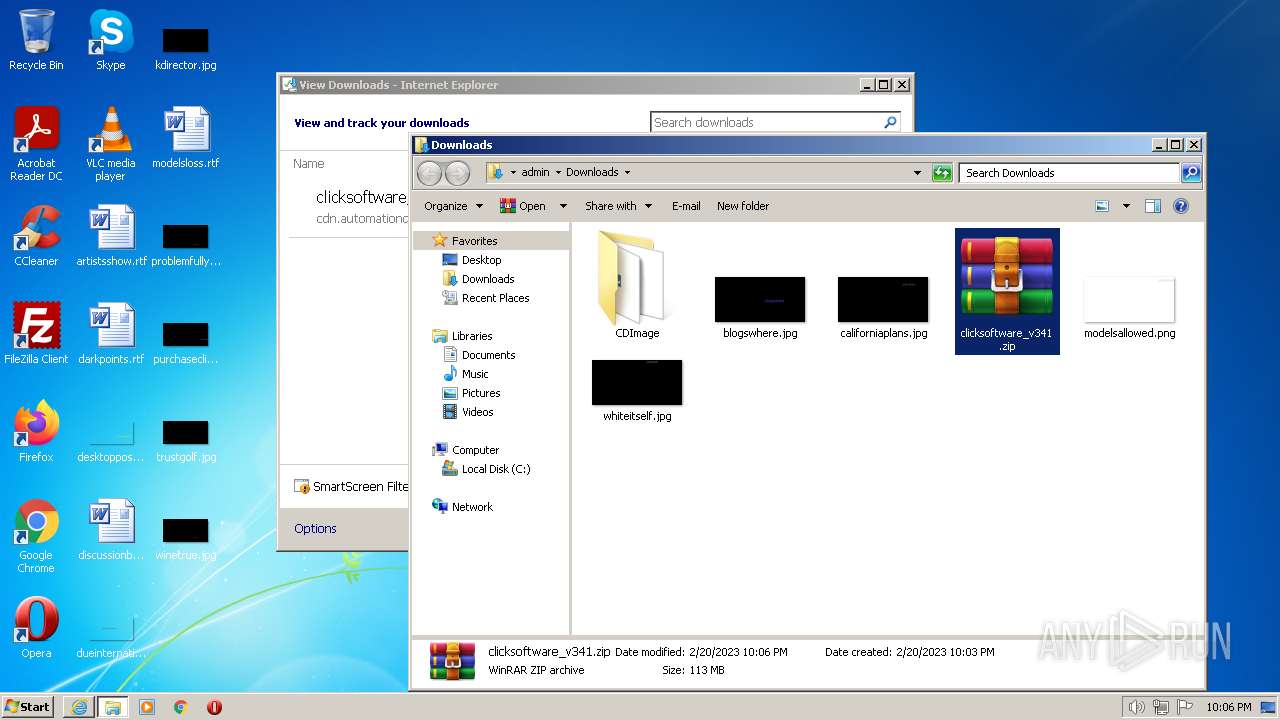
Manual execution by a user
- WinRAR.exe (PID: 3004)
- CLICK_Setup.exe (PID: 2684)
- CLICK_Setup.exe (PID: 2556)
- wmpnscfg.exe (PID: 912)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 3004)
Drops a file that was compiled in debug mode
- WinRAR.exe (PID: 3004)
- CLICK_Setup.exe (PID: 2556)
- CLICK_Setup.exe (PID: 3164)
Drops the executable file immediately after the start
- WinRAR.exe (PID: 3004)
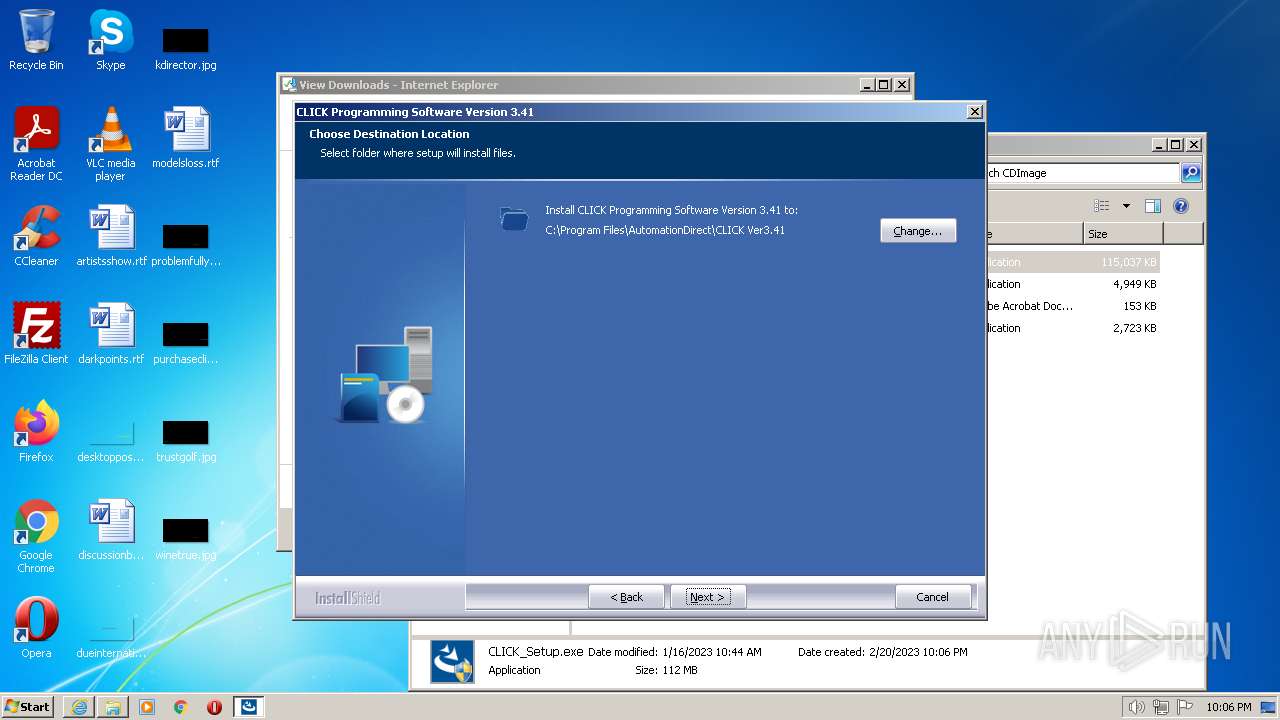
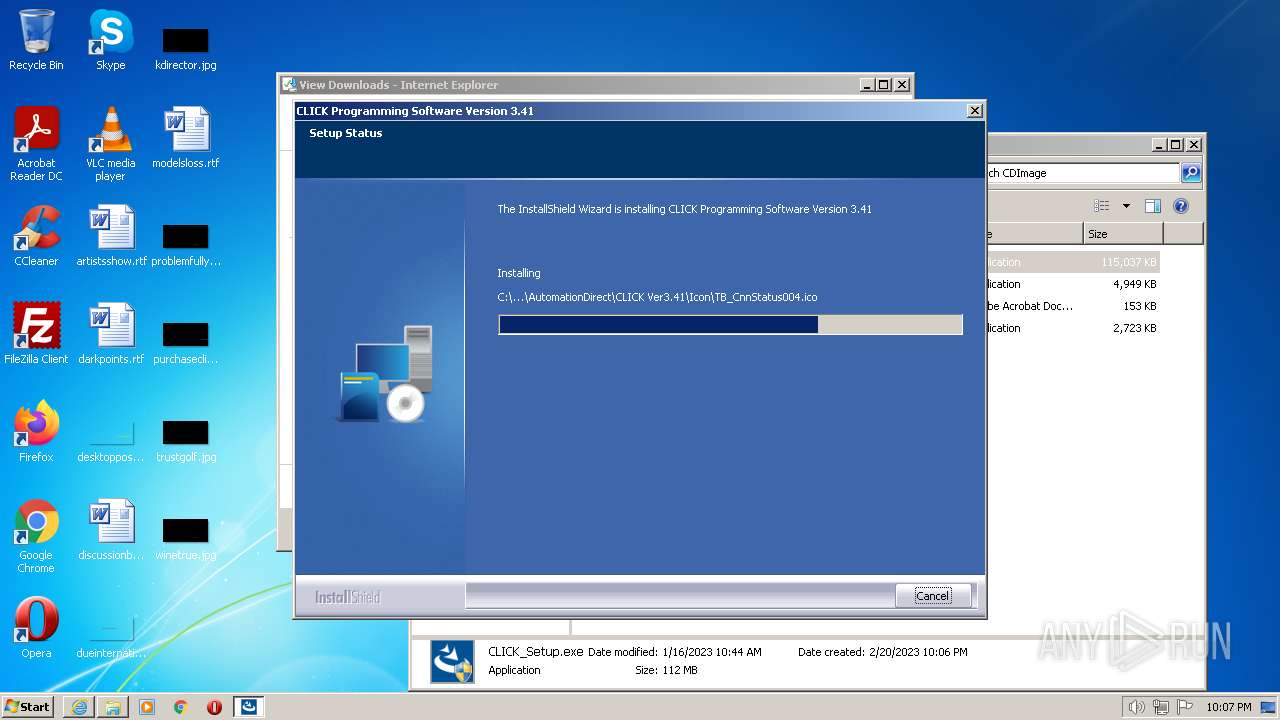
Creates files in the program directory
- CLICK_Setup.exe (PID: 3164)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
54
Monitored processes
8
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 912 | "C:\Program Files\Windows Media Player\wmpnscfg.exe" | C:\Program Files\Windows Media Player\wmpnscfg.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Media Player Network Sharing Service Configuration Application Exit code: 0 Version: 12.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1240 | "C:\Program Files\Internet Explorer\iexplore.exe" "https://cdn.automationdirect.com/static/software/clicksoftware_v341.zip" | C:\Program Files\Internet Explorer\iexplore.exe | Explorer.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
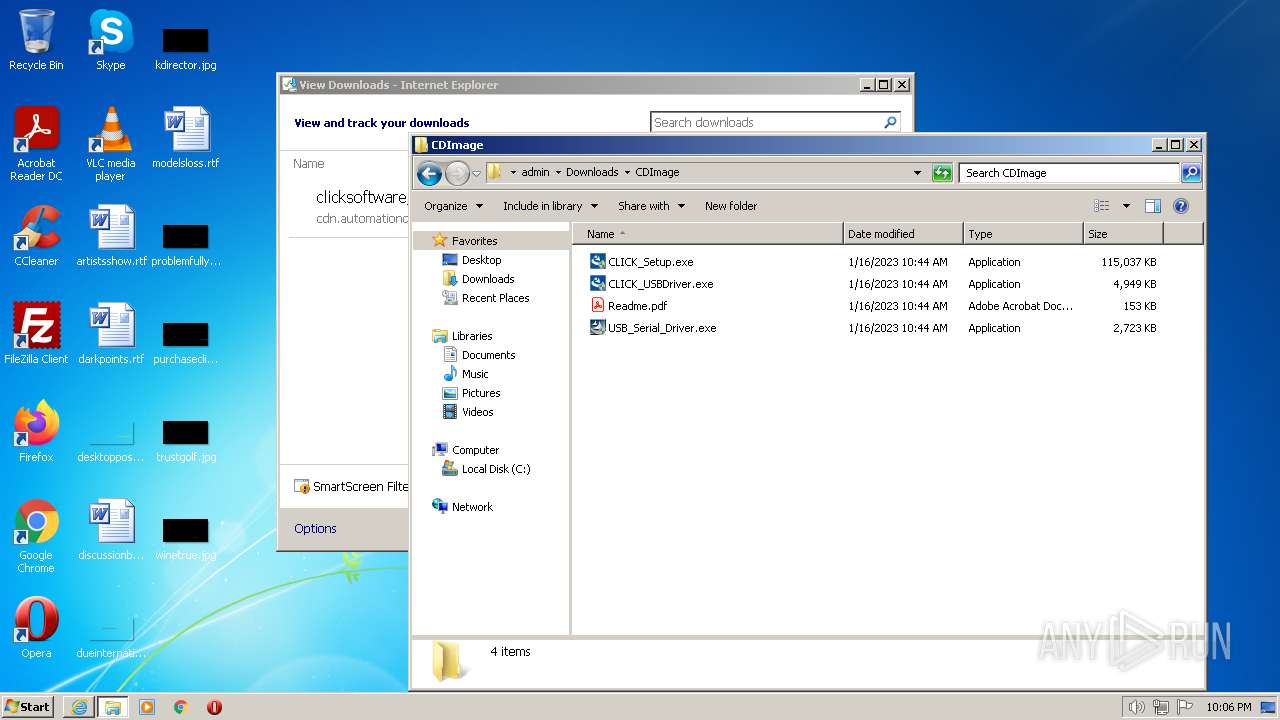
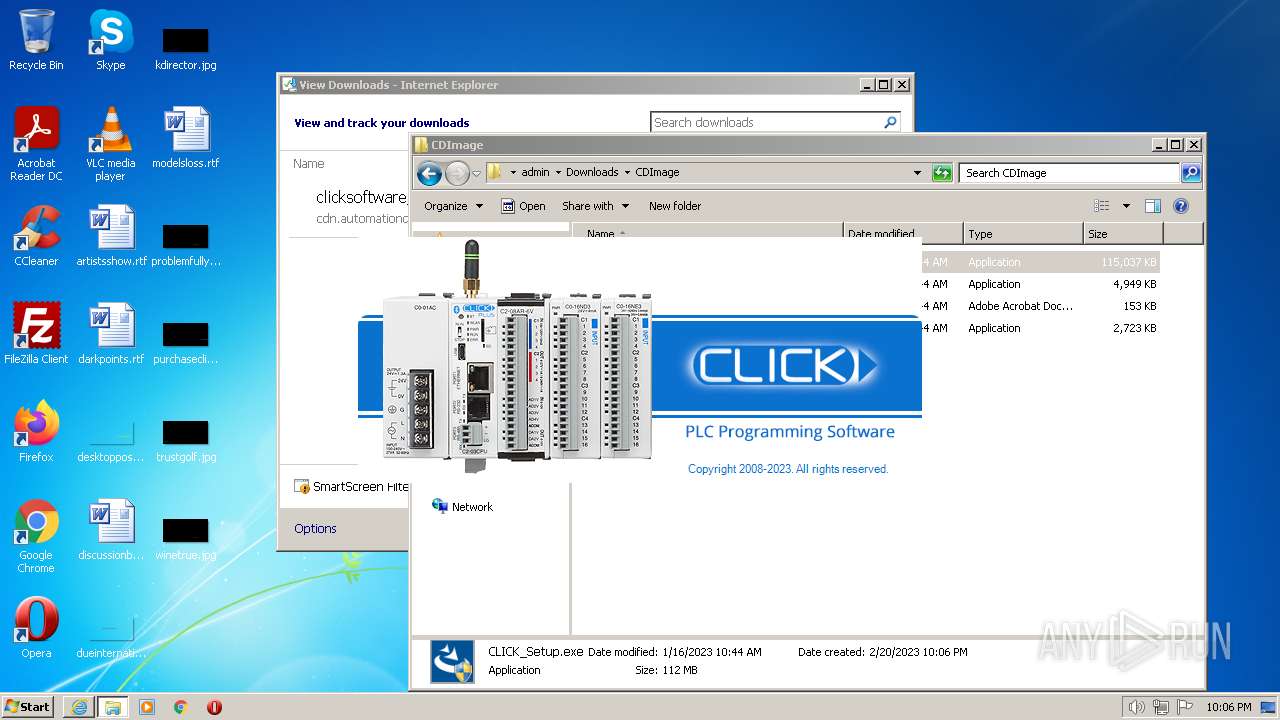
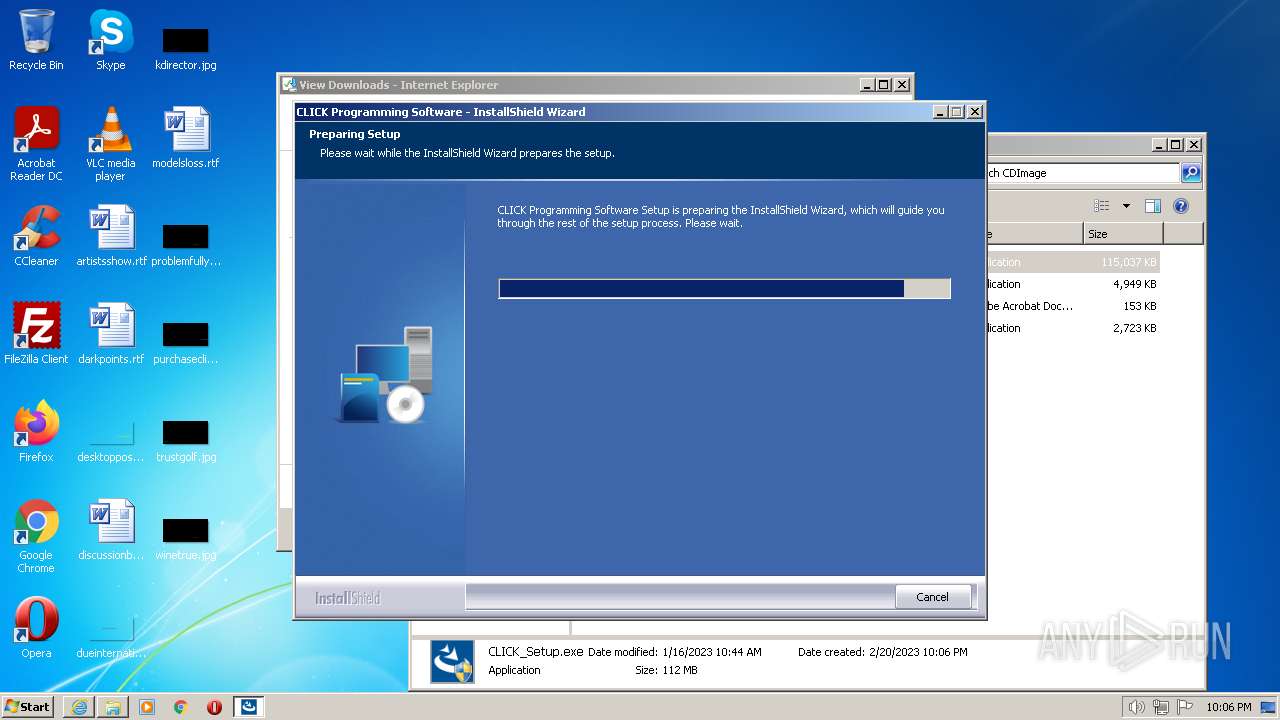
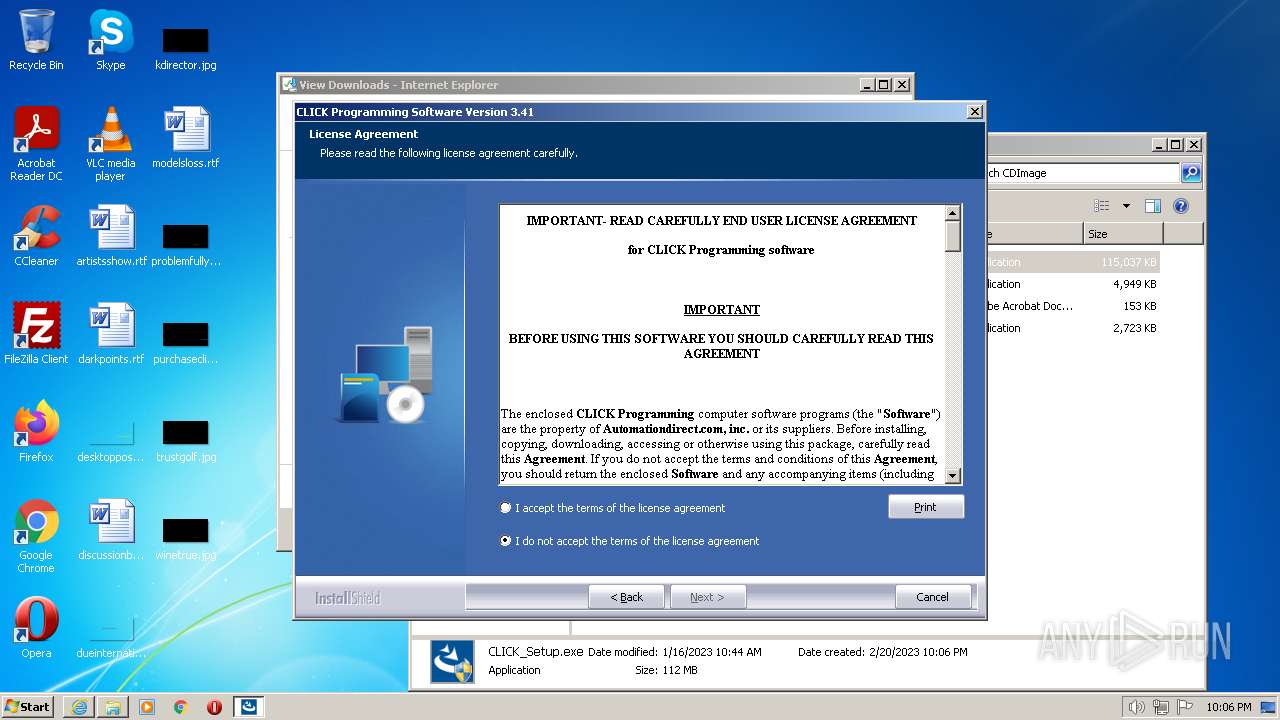
| 2556 | "C:\Users\admin\Downloads\CDImage\CLICK_Setup.exe" | C:\Users\admin\Downloads\CDImage\CLICK_Setup.exe | Explorer.EXE | ||||||||||||
User: admin Company: AutomationDirect Integrity Level: HIGH Description: InstallScript Setup Launcher Unicode Exit code: 0 Version: 3.41.0000 Modules
| |||||||||||||||
| 2684 | "C:\Users\admin\Downloads\CDImage\CLICK_Setup.exe" | C:\Users\admin\Downloads\CDImage\CLICK_Setup.exe | — | Explorer.EXE | |||||||||||
User: admin Company: AutomationDirect Integrity Level: MEDIUM Description: InstallScript Setup Launcher Unicode Exit code: 3221226540 Version: 3.41.0000 Modules
| |||||||||||||||
| 3004 | "C:\Program Files\WinRAR\WinRAR.exe" x -iext -ow -ver -- "C:\Users\admin\Downloads\clicksoftware_v341.zip" C:\Users\admin\Downloads\ | C:\Program Files\WinRAR\WinRAR.exe | Explorer.EXE | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 3072 | C:\Windows\system32\vssvc.exe | C:\Windows\system32\vssvc.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Volume Shadow Copy Service Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3164 | C:\Users\admin\AppData\Local\Temp\{5826D094-5DD2-4D66-8A57-362ECEF3135C}\CLICK_Setup.exe -package:"C:\Users\admin\Downloads\CDImage\CLICK_Setup.exe" -no_selfdeleter -IS_temp -media_path:"C:\Users\admin\AppData\Local\Temp\{5826D094-5DD2-4D66-8A57-362ECEF3135C}\Disk1\" -tempdisk1folder:"C:\Users\admin\AppData\Local\Temp\{5826D094-5DD2-4D66-8A57-362ECEF3135C}\" -IS_OriginalLauncher:"C:\Users\admin\AppData\Local\Temp\{5826D094-5DD2-4D66-8A57-362ECEF3135C}\Disk1\CLICK_Setup.exe" | C:\Users\admin\AppData\Local\Temp\{5826D094-5DD2-4D66-8A57-362ECEF3135C}\CLICK_Setup.exe | CLICK_Setup.exe | ||||||||||||
User: admin Company: AutomationDirect Integrity Level: HIGH Description: InstallScript Setup Launcher Unicode Exit code: 0 Version: 3.41.0000 Modules
| |||||||||||||||
| 3188 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:1240 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
30 812
Read events
30 236
Write events
566
Delete events
10
Modification events
| (PID) Process: | (1240) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 1 | |||
| (PID) Process: | (1240) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: 388624944 | |||
| (PID) Process: | (1240) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 31016311 | |||
| (PID) Process: | (1240) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: 688789944 | |||
| (PID) Process: | (1240) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 31016311 | |||
| (PID) Process: | (1240) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (1240) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (1240) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (1240) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (1240) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
446
Suspicious files
82
Text files
2 002
Unknown types
48
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3188 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\E573CDF4C6D731D56A665145182FD759_7DC49495A2667E8C20AE1452C77263AF | der | |
MD5:— | SHA256:— | |||
| 3188 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\clicksoftware_v341[1].zip | compressed | |
MD5:— | SHA256:— | |||
| 1240 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\LW1O2AIB.txt | text | |
MD5:— | SHA256:— | |||
| 1240 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\7423F88C7F265F0DEFC08EA88C3BDE45_AA1E8580D4EBC816148CE81268683776 | der | |
MD5:— | SHA256:— | |||
| 1240 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\82CB34DD3343FE727DF8890D352E0D8F | der | |
MD5:— | SHA256:— | |||
| 1240 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\7423F88C7F265F0DEFC08EA88C3BDE45_AA1E8580D4EBC816148CE81268683776 | binary | |
MD5:— | SHA256:— | |||
| 3188 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\B398B80134F72209547439DB21AB308D_A4CF52CCA82D7458083F7280801A3A04 | binary | |
MD5:— | SHA256:— | |||
| 1240 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\Active\{5E37803E-B16A-11ED-80DA-12A9866C77DE}.dat | binary | |
MD5:— | SHA256:— | |||
| 1240 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\B6QGX7LP\favicon[1].ico | image | |
MD5:DA597791BE3B6E732F0BC8B20E38EE62 | SHA256:5B2C34B3C4E8DD898B664DBA6C3786E2FF9869EFF55D673AA48361F11325ED07 | |||
| 1240 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
23
DNS requests
15
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3188 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAbY2QTVWENG9oovp1QifsQ%3D | US | der | 471 b | whitelisted |
1240 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | der | 471 b | whitelisted |
1240 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://crl3.digicert.com/Omniroot2025.crl | US | der | 7.78 Kb | whitelisted |
3188 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTk45WiKdPUwcMf8JgMC07ACYqr2AQUt2ui6qiqhIx56rTaD5iyxZV2ufQCEAji95hJFCjmhs8PU%2BMqHZM%3D | US | der | 471 b | whitelisted |
1240 | iexplore.exe | GET | 200 | 209.197.3.8:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?eaa72a3e222567bb | US | compressed | 4.70 Kb | whitelisted |
1240 | iexplore.exe | GET | 200 | 209.197.3.8:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?43de52a9ac8bff4f | US | compressed | 4.70 Kb | whitelisted |
1240 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEALnkXH7gCHpP%2BLZg4NMUMA%3D | US | der | 471 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3188 | iexplore.exe | 205.151.114.46:443 | — | RFC2270-UUNET-CUSTOMER | US | unknown |
3188 | iexplore.exe | 209.197.3.8:80 | ctldl.windowsupdate.com | STACKPATH-CDN | US | whitelisted |
1240 | iexplore.exe | 209.197.3.8:80 | ctldl.windowsupdate.com | STACKPATH-CDN | US | whitelisted |
3188 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | EDGECAST | GB | whitelisted |
1240 | iexplore.exe | 152.199.19.161:443 | iecvlist.microsoft.com | EDGECAST | US | whitelisted |
1240 | iexplore.exe | 204.79.197.200:443 | ieonline.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
1240 | iexplore.exe | 104.64.117.184:443 | go.microsoft.com | AKAMAI-AS | CZ | whitelisted |
1240 | iexplore.exe | 204.79.197.203:443 | www.msn.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | malicious |
1240 | iexplore.exe | 20.25.53.147:443 | query.prod.cms.msn.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | unknown |
1240 | iexplore.exe | 92.123.104.63:443 | www.bing.com | Akamai International B.V. | DE | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
ctldl.windowsupdate.com |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
crl3.digicert.com |
| whitelisted |
iecvlist.microsoft.com |
| whitelisted |
r20swj13mr.microsoft.com |
| whitelisted |
ieonline.microsoft.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
www.msn.com |
| whitelisted |