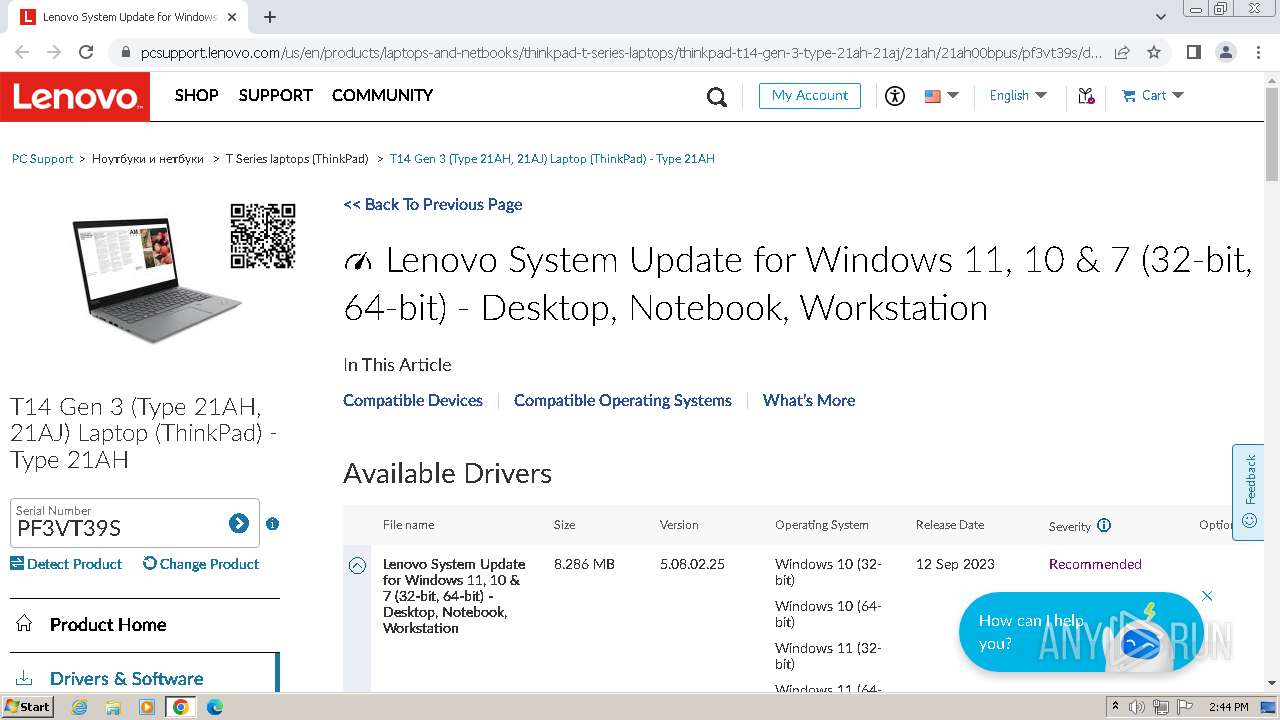
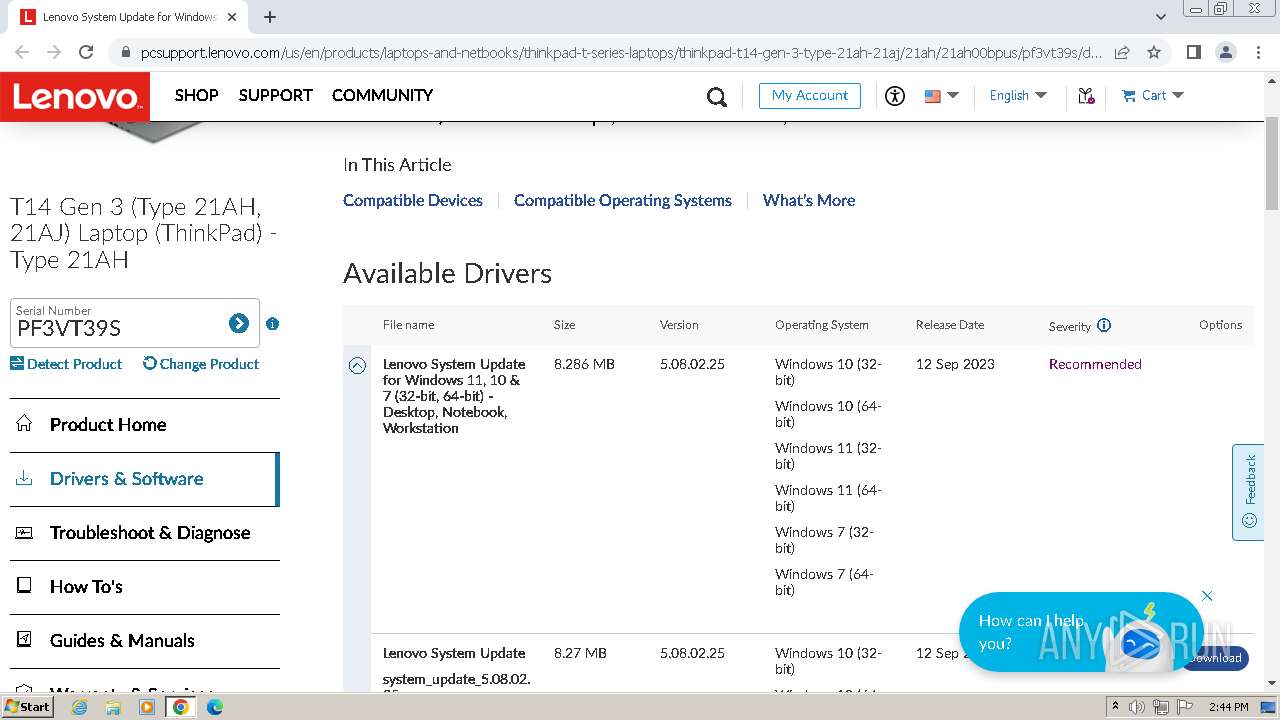
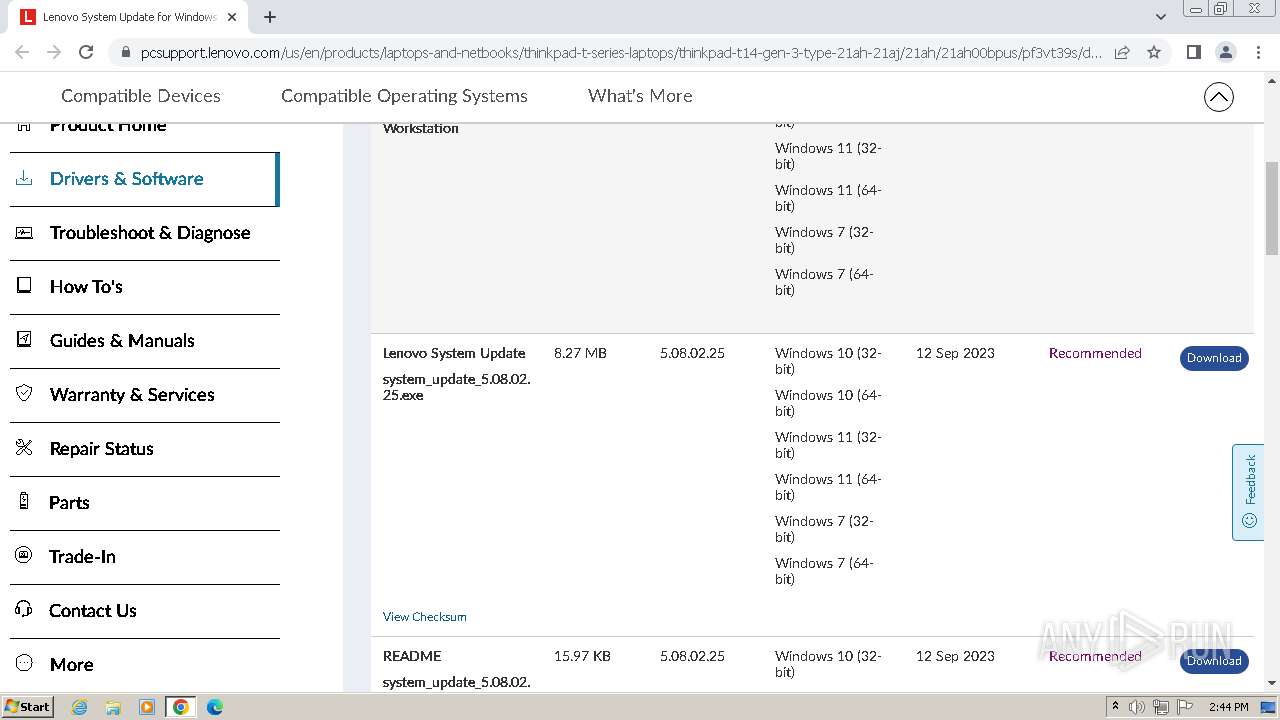
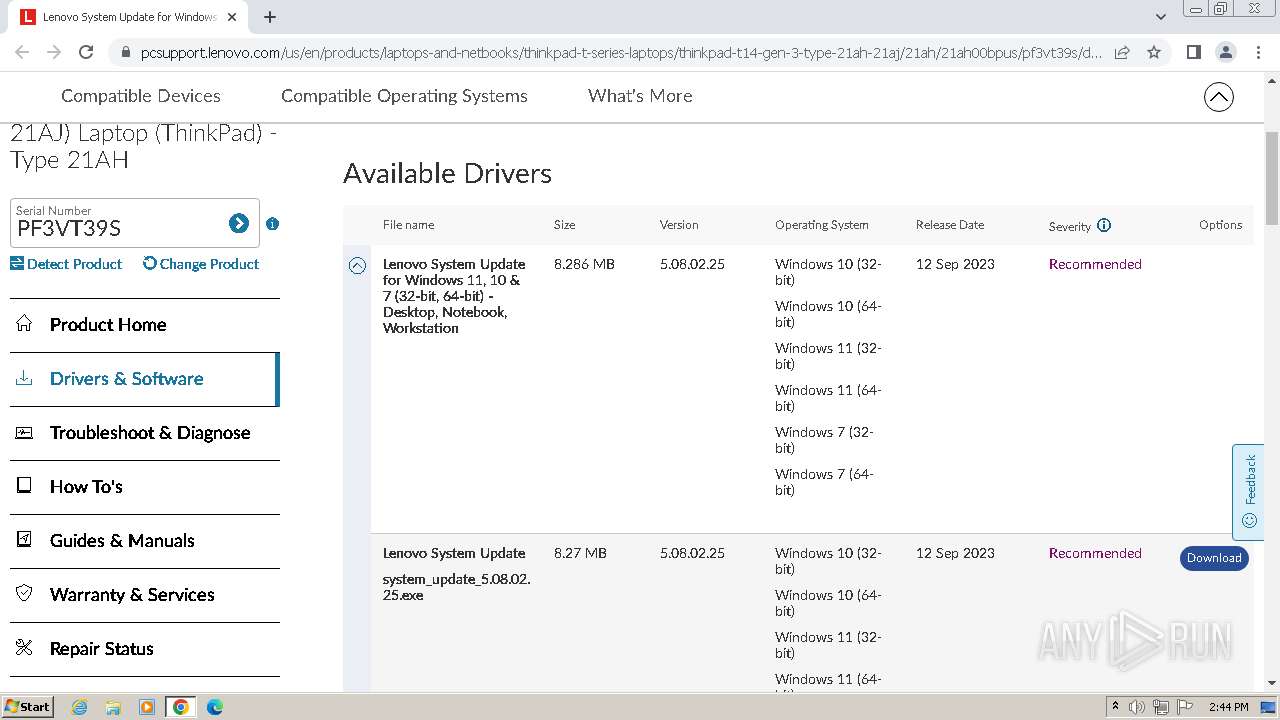
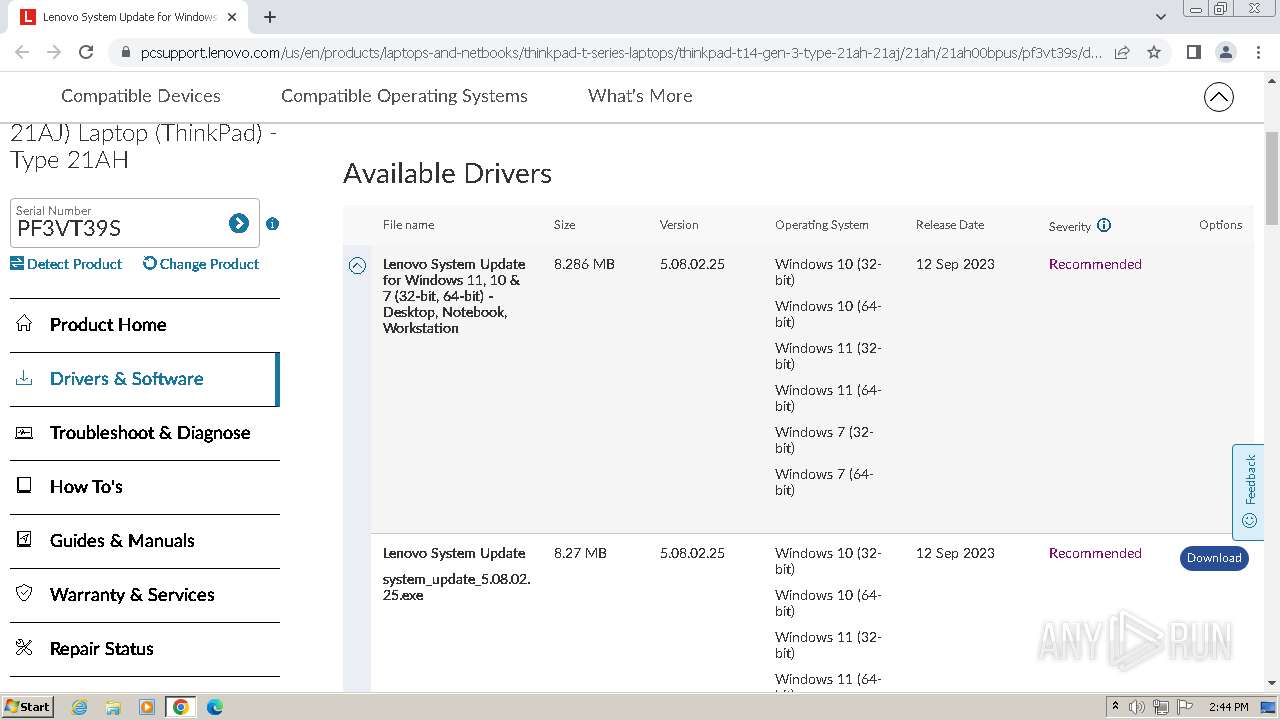
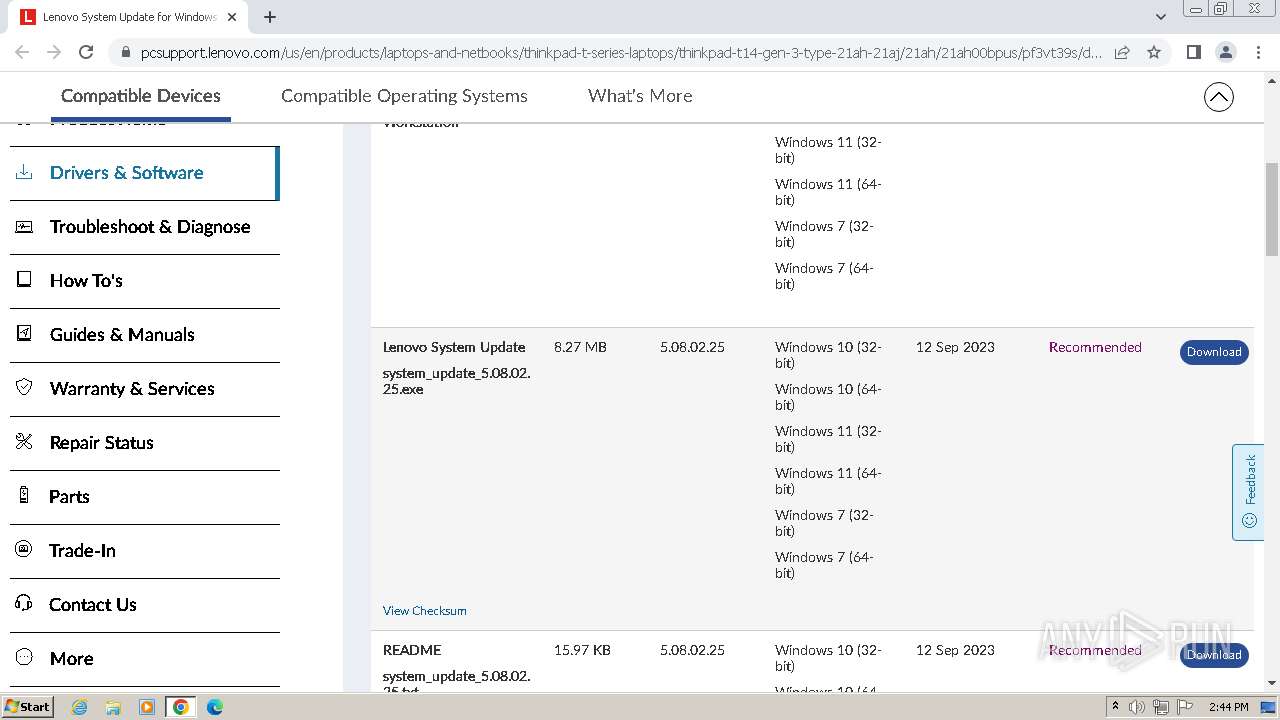
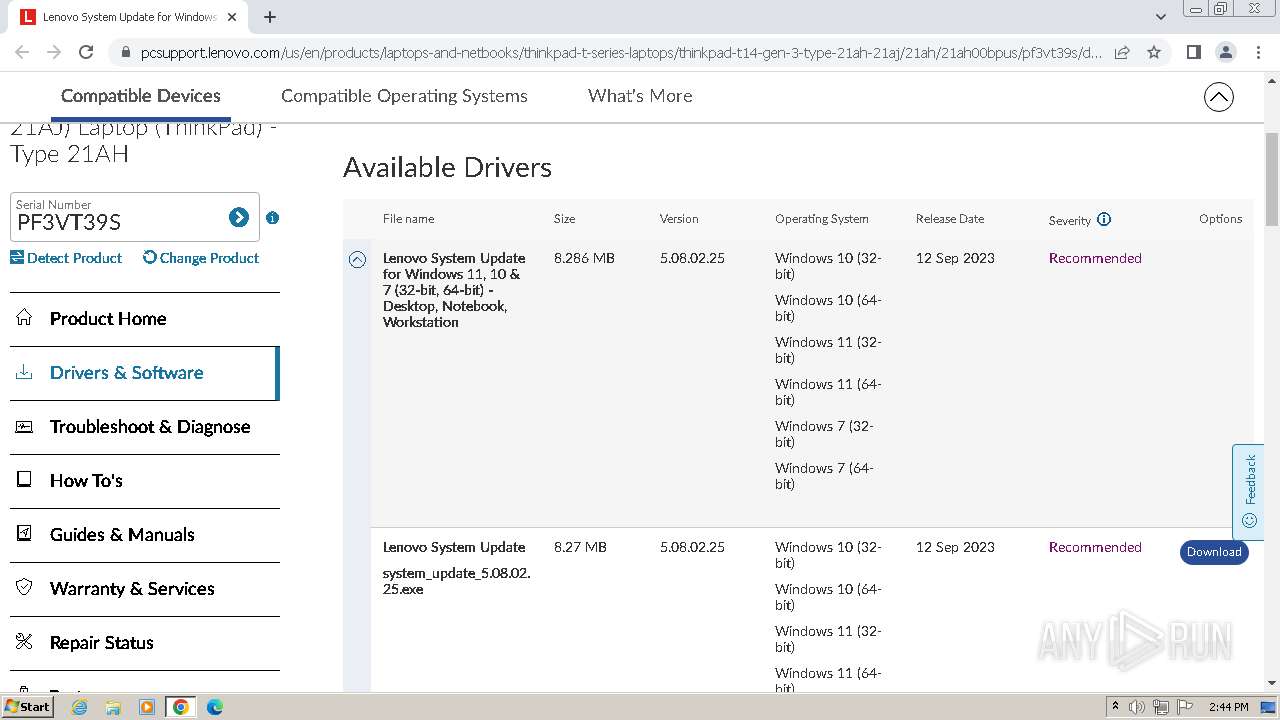
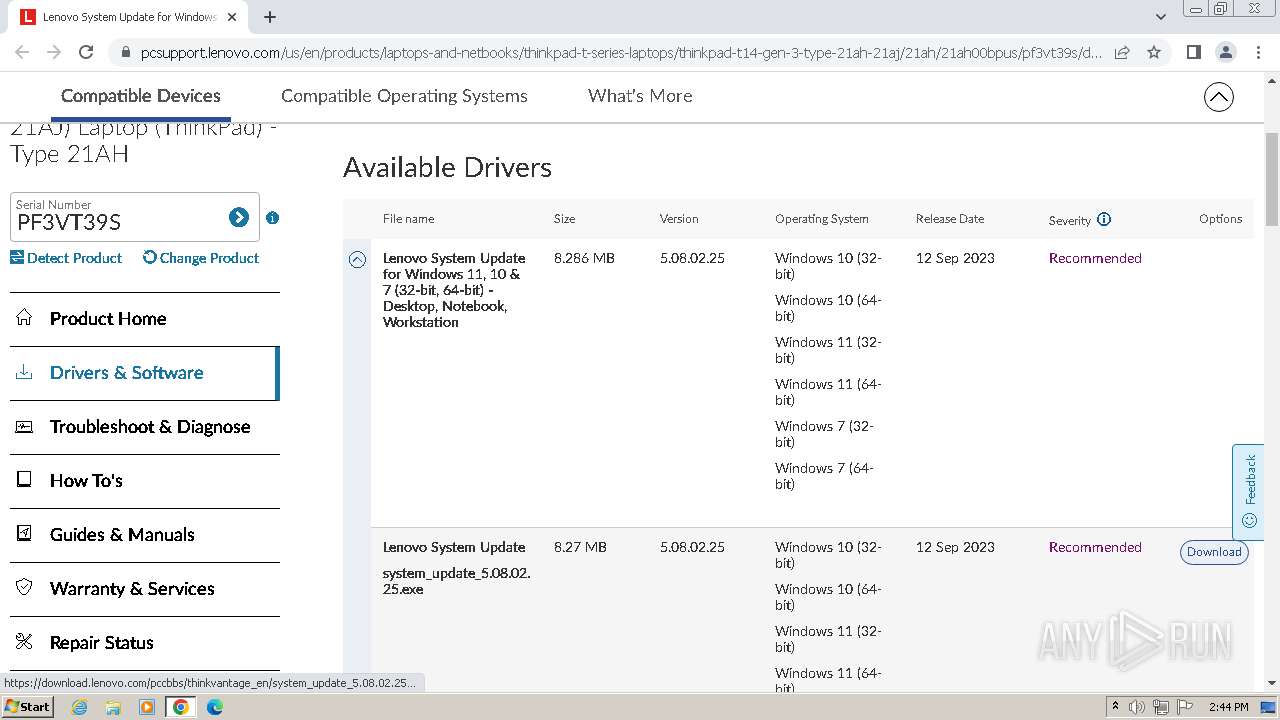
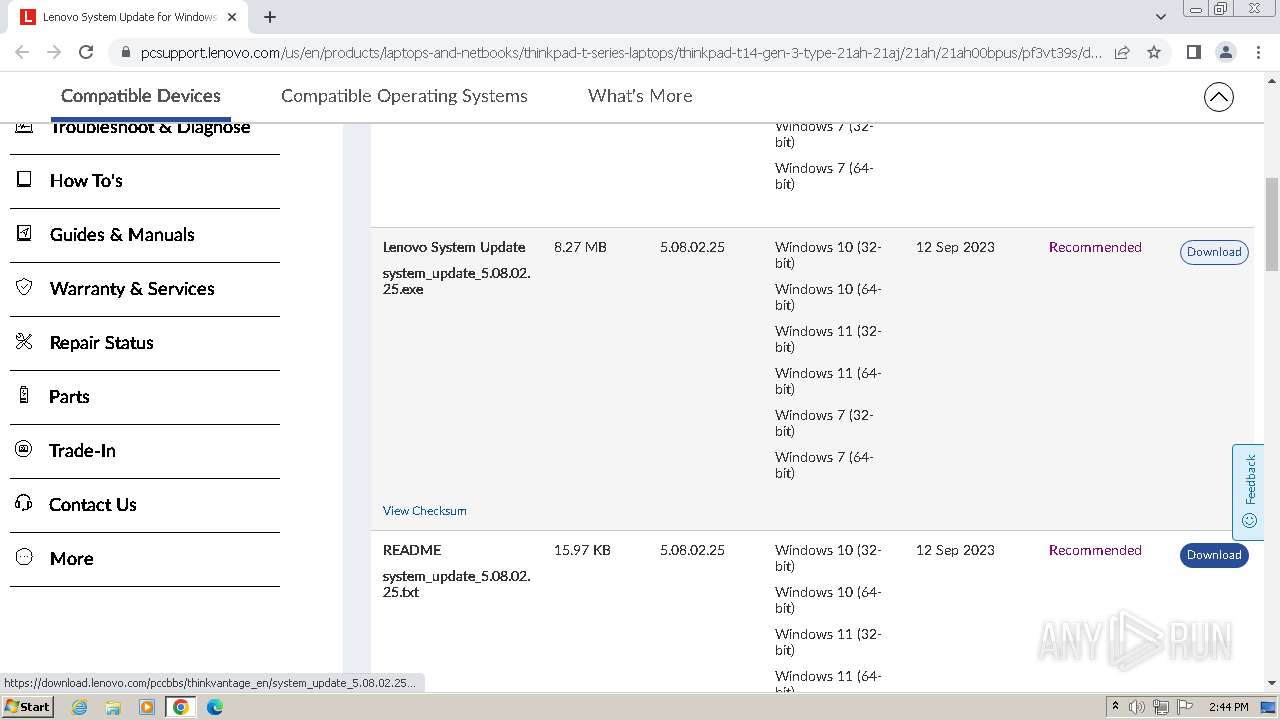
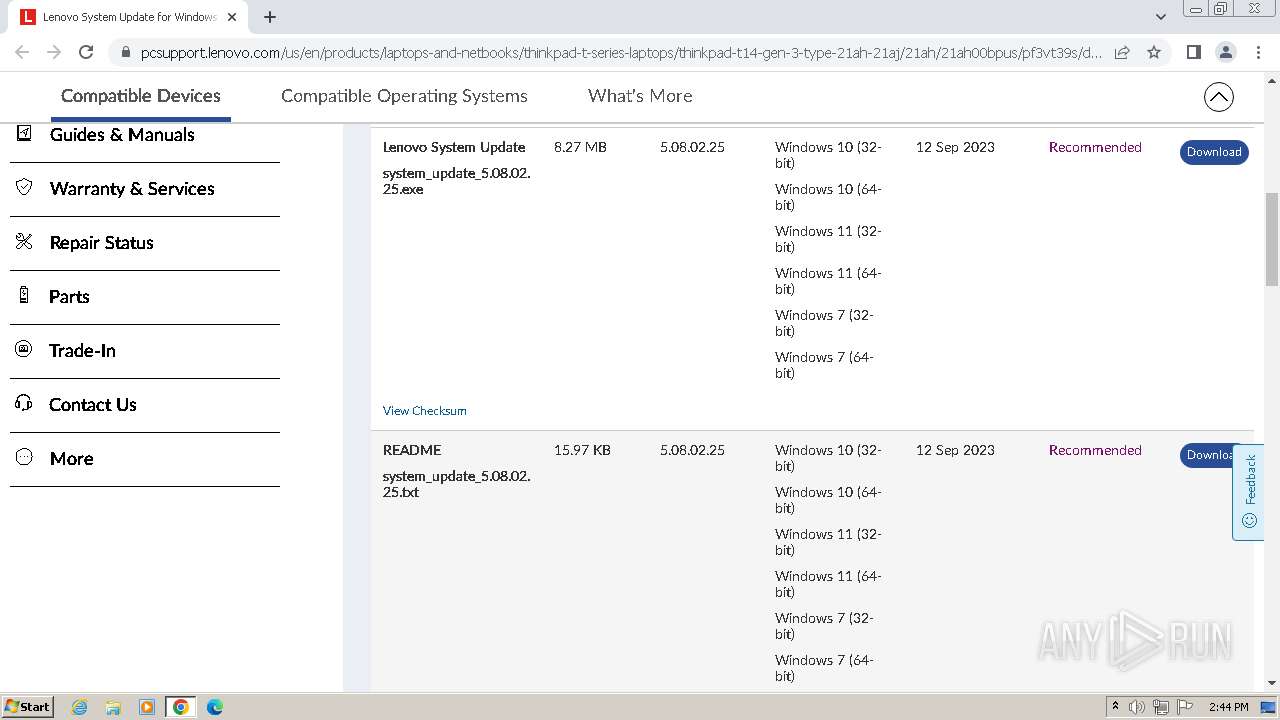
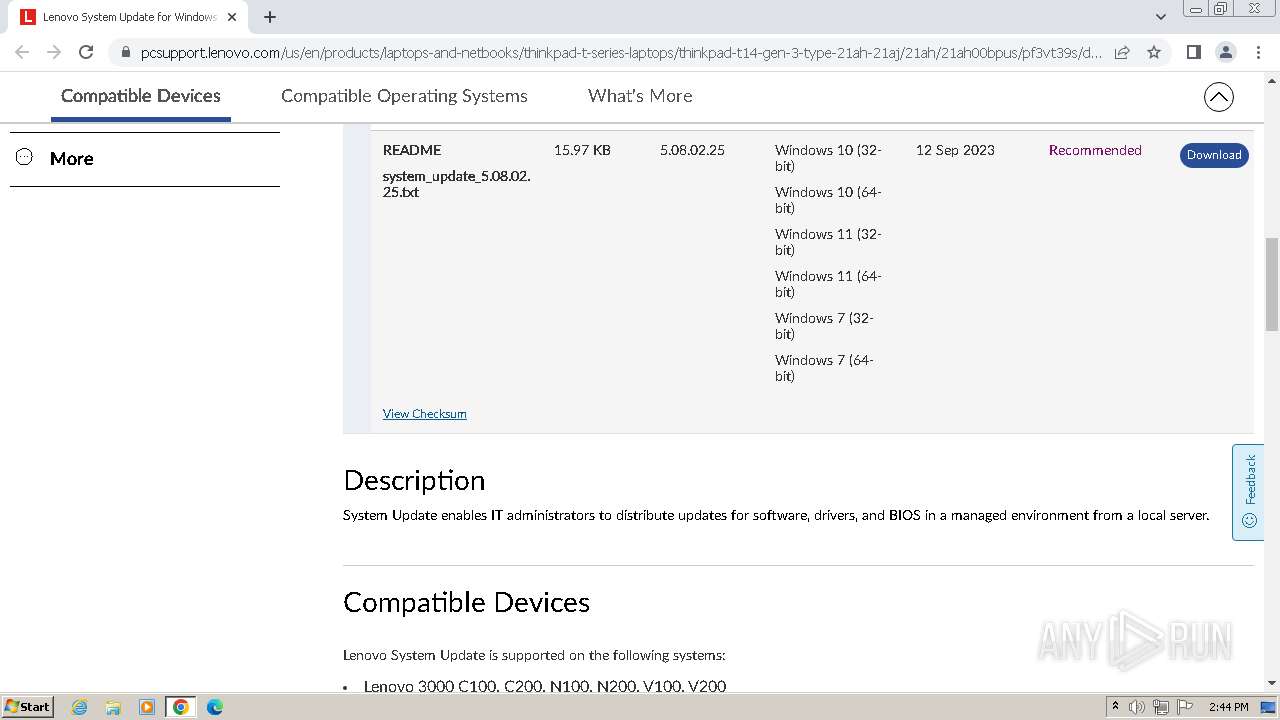
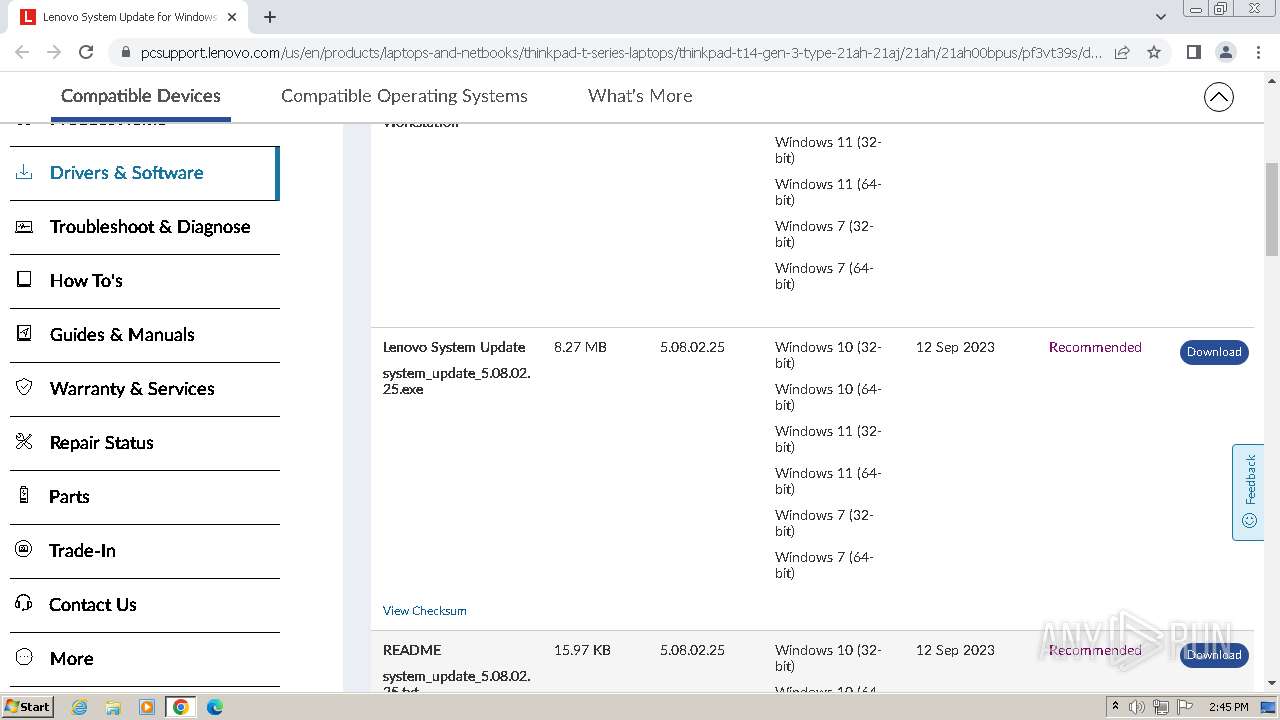
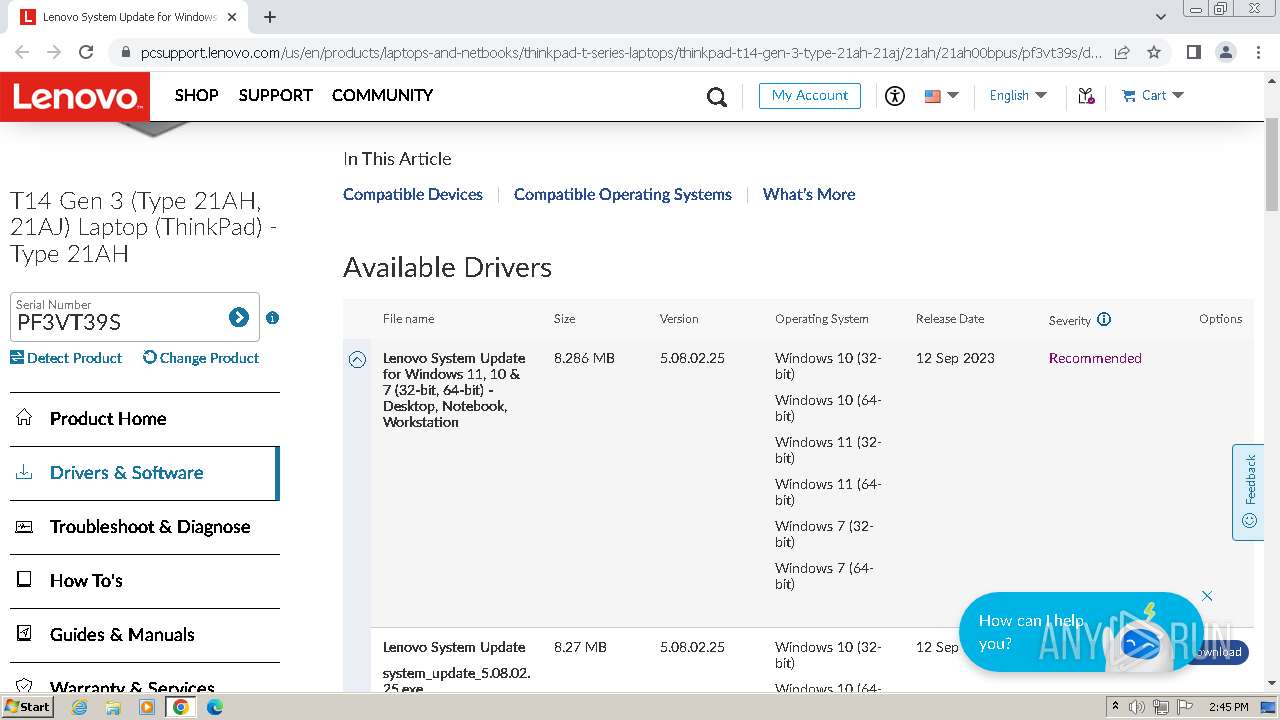
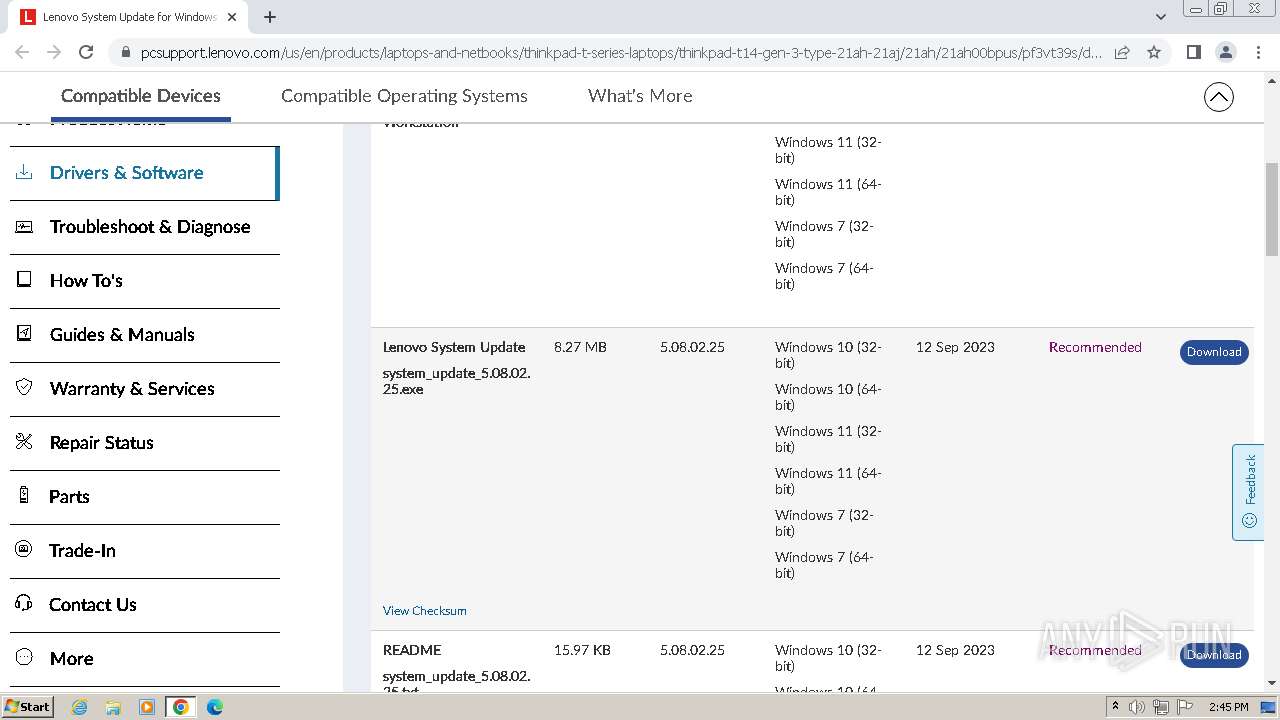
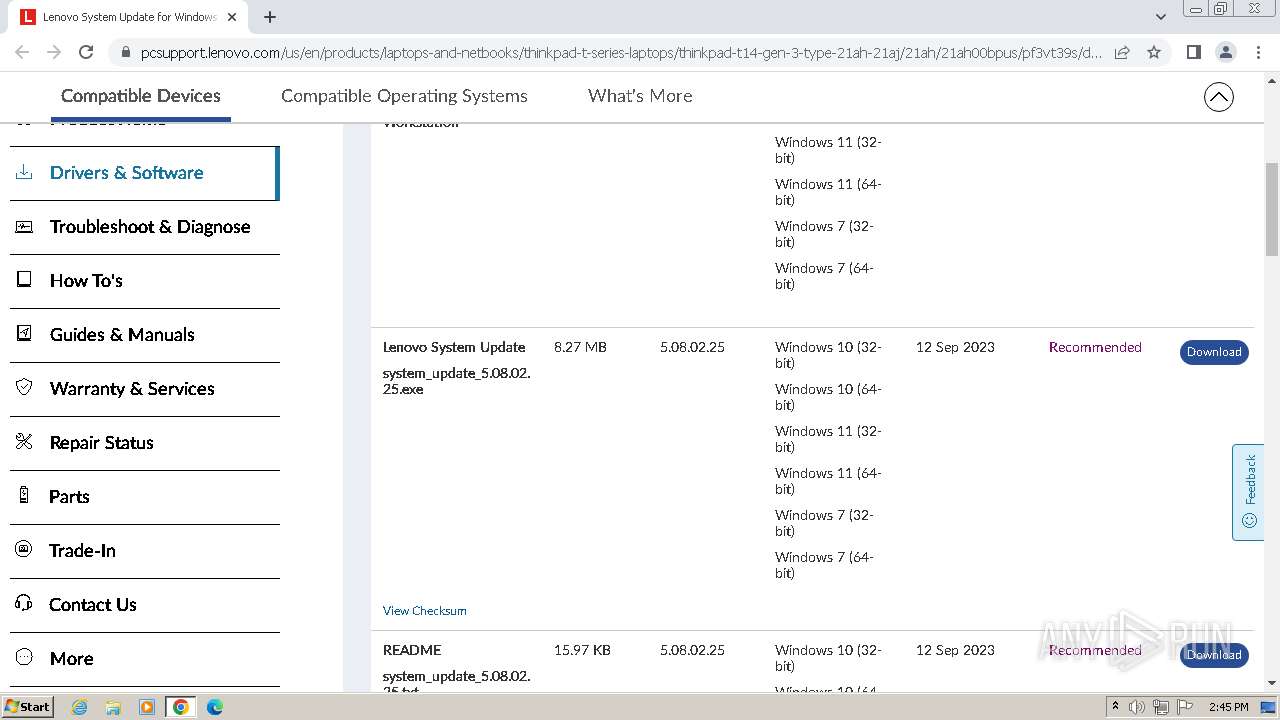
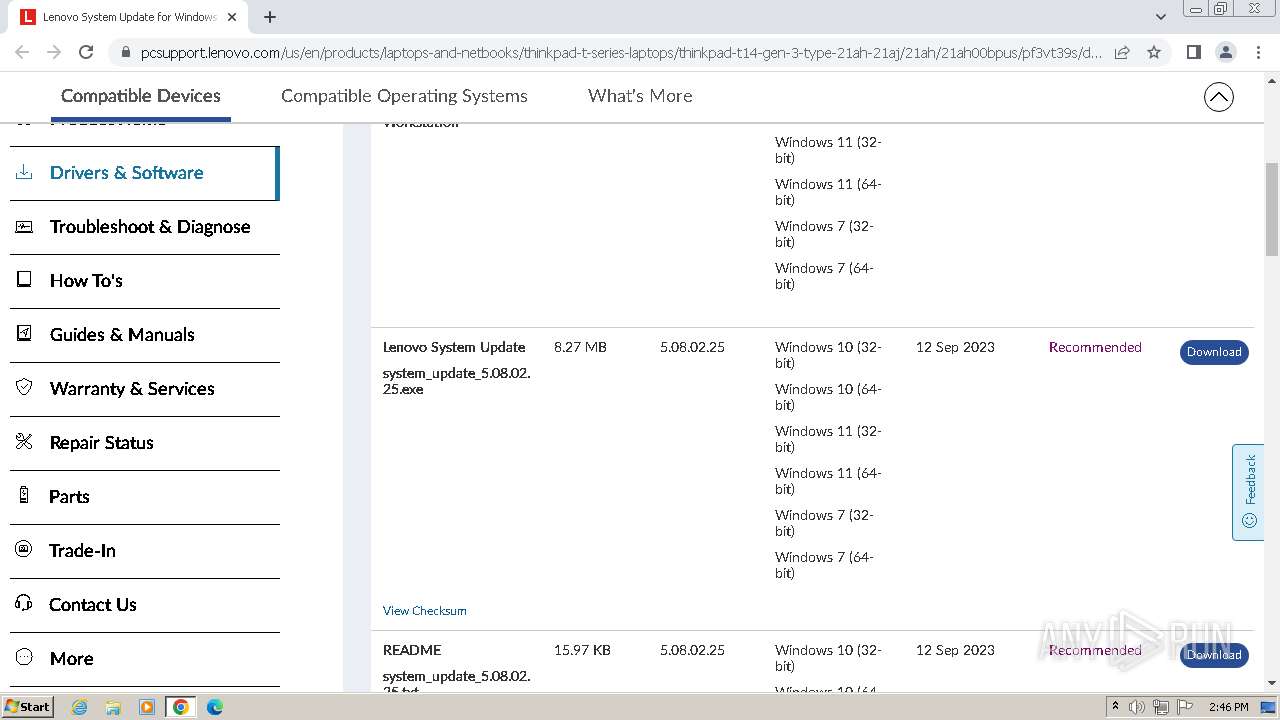
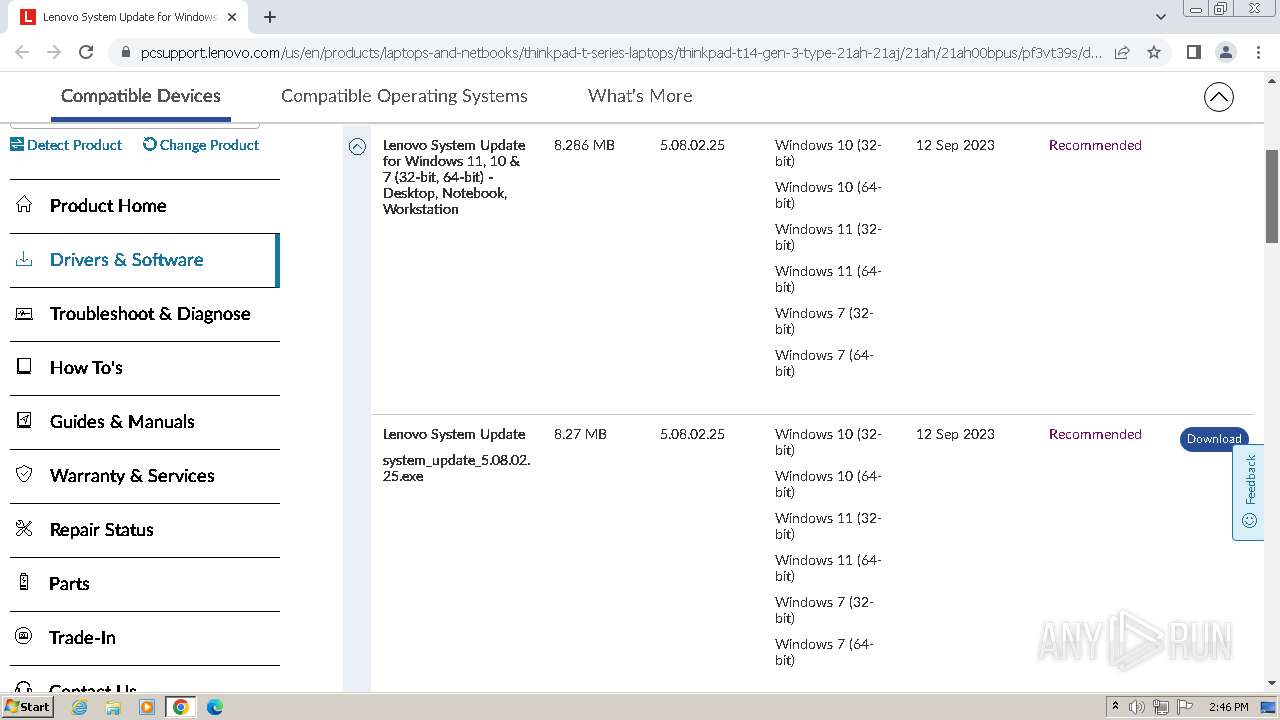
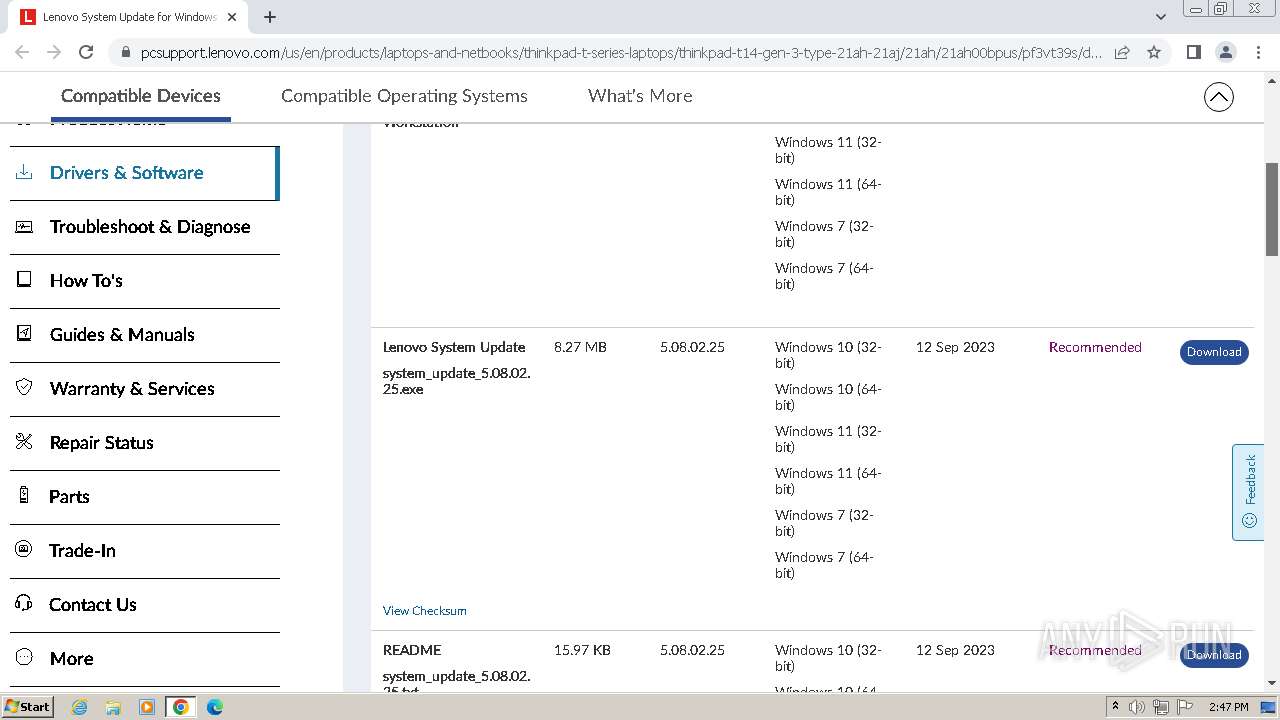
| URL: | https://pcsupport.lenovo.com/us/en/products/laptops-and-netbooks/thinkpad-t-series-laptops/thinkpad-t14-gen-3-type-21ah-21aj/21ah/21ah00bpus/pf3vt39s/downloads/ds012808-lenovo-system-update-for-windows-10-7-32-bit-64-bit-desktop-notebook-workstation |
| Full analysis: | https://app.any.run/tasks/20b360bb-6d0b-4aea-a128-374c593dddb7 |
| Verdict: | Malicious activity |
| Analysis date: | June 10, 2024, 13:44:09 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 8D1EFC9CBBC75670EAAD5A7E6F4662E1 |
| SHA1: | CEDA73D89D7ED83D05D273B1D243DA6B6F91AA43 |
| SHA256: | 5DCABA371E2018F56572AF5172FEBF85CB9FB278978F65AC5ECCF1D922AD62AC |
| SSDEEP: | 6:2CFVQLYocTRW37KhBs7BIRI5iBIRURIMRCacSGAgoYK+LvKSx7dxh2twy:2+VezQwLKhiy2rCRCHyYK+LvKiJ2Wy |
MALICIOUS
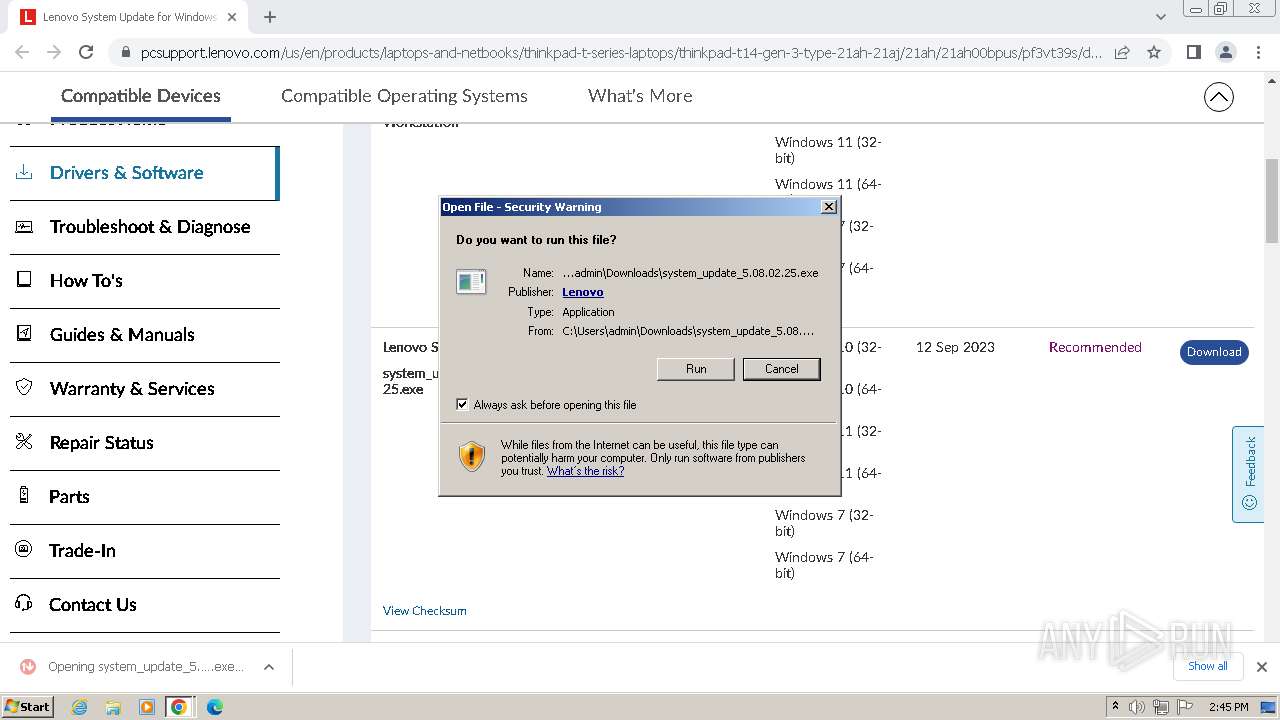
Drops the executable file immediately after the start
- system_update_5.08.02.25.exe (PID: 2644)
- system_update_5.08.02.25.exe (PID: 2824)
- system_update_5.08.02.25.tmp (PID: 2788)
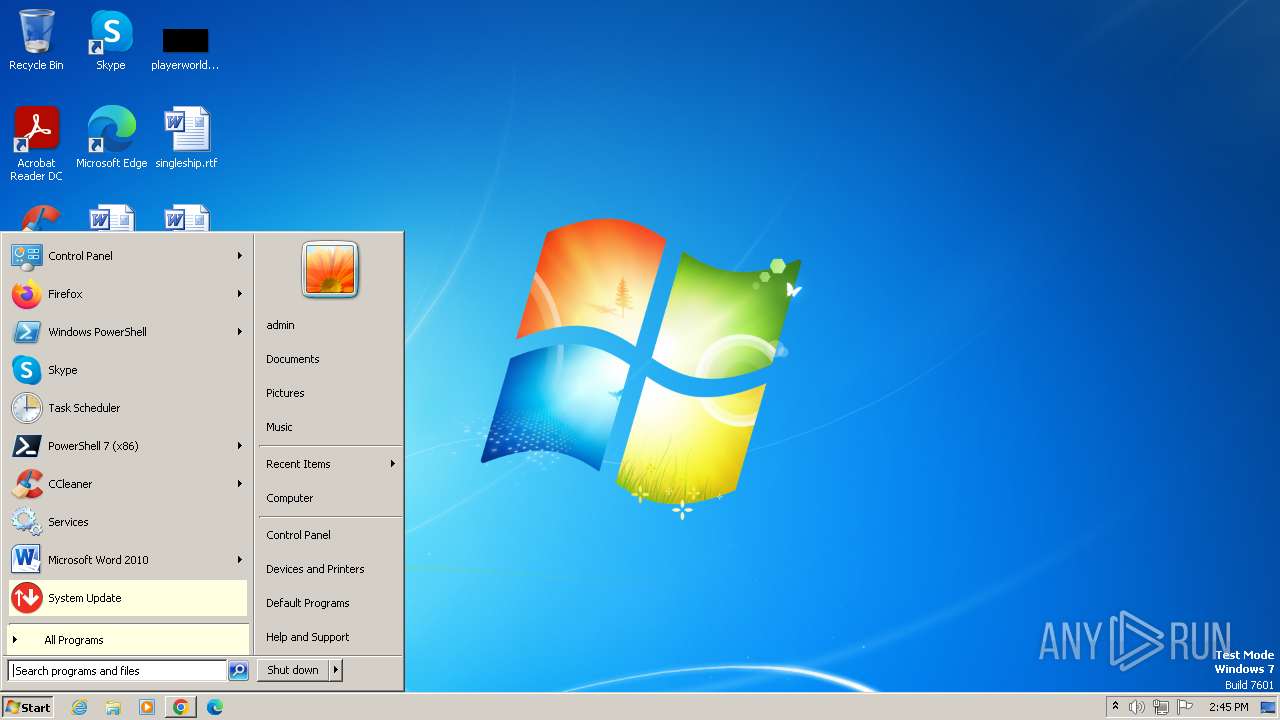
Uses Task Scheduler to run other applications
- ConfigScheduledTask.exe (PID: 3696)
SUSPICIOUS
Executable content was dropped or overwritten
- system_update_5.08.02.25.exe (PID: 2644)
- system_update_5.08.02.25.exe (PID: 2824)
- system_update_5.08.02.25.tmp (PID: 2788)
Starts application with an unusual extension
- system_update_5.08.02.25.exe (PID: 2824)
Reads the Windows owner or organization settings
- system_update_5.08.02.25.tmp (PID: 2788)
Starts CMD.EXE for commands execution
- cmd.exe (PID: 2752)
- system_update_5.08.02.25.tmp (PID: 2788)
Executing commands from ".cmd" file
- system_update_5.08.02.25.tmp (PID: 2788)
Application launched itself
- cmd.exe (PID: 2752)
Using 'findstr.exe' to search for text patterns in files and output
- cmd.exe (PID: 2752)
Drops 7-zip archiver for unpacking
- system_update_5.08.02.25.tmp (PID: 2788)
Creates a software uninstall entry
- system_update_5.08.02.25.tmp (PID: 2788)
Reads the Internet Settings
- InstallUtil.exe (PID: 3260)
- tvsu.exe (PID: 2548)
- Tvsukernel.exe (PID: 2760)
- IA.exe (PID: 3288)
- IA.exe (PID: 2516)
Reads security settings of Internet Explorer
- InstallUtil.exe (PID: 3260)
- SUService.exe (PID: 3404)
- uncsetting.exe (PID: 3580)
- tvsu.exe (PID: 2548)
- Tvsukernel.exe (PID: 2760)
- IA.exe (PID: 3288)
- IA.exe (PID: 2516)
Creates or modifies Windows services
- InstallUtil.exe (PID: 3260)
Executes as Windows Service
- SUService.exe (PID: 3404)
Uses ICACLS.EXE to modify access control lists
- SUService.exe (PID: 3404)
- Tvsukernel.exe (PID: 2760)
Uses NETSH.EXE to add a firewall rule or allowed programs
- uncsetting.exe (PID: 3580)
Adds/modifies Windows certificates
- certutil.exe (PID: 2092)
- certutil.exe (PID: 3844)
- SUService.exe (PID: 3404)
- Tvsukernel.exe (PID: 2760)
Checks Windows Trust Settings
- SUService.exe (PID: 3404)
- Tvsukernel.exe (PID: 2760)
- IA.exe (PID: 2516)
Reads settings of System Certificates
- Tvsukernel.exe (PID: 2760)
- IA.exe (PID: 2516)
Searches for installed software
- IA.exe (PID: 2516)
INFO
Reads the computer name
- wmpnscfg.exe (PID: 1072)
- system_update_5.08.02.25.tmp (PID: 2780)
- system_update_5.08.02.25.tmp (PID: 2788)
- InstallUtil.exe (PID: 3260)
- StartSuService.exe (PID: 3252)
- SUService.exe (PID: 3404)
- susetsched.exe (PID: 3540)
- uncsetting.exe (PID: 3580)
- ConfigService.exe (PID: 3532)
- tvsu.exe (PID: 2548)
- ConfigScheduledTask.exe (PID: 3696)
- uncsetting.exe (PID: 2636)
- uncserver.exe (PID: 2616)
- TvsuCommandLauncher.exe (PID: 2816)
- UACSdk.exe (PID: 972)
- TvsuCommandLauncher.exe (PID: 2324)
- ConfigService.exe (PID: 2916)
- Tvsukernel.exe (PID: 2760)
- ConfigScheduledTask.exe (PID: 3316)
- IA.exe (PID: 3288)
- IA.exe (PID: 2516)
Manual execution by a user
- wmpnscfg.exe (PID: 1072)
- tvsu.exe (PID: 2548)
Checks supported languages
- wmpnscfg.exe (PID: 1072)
- system_update_5.08.02.25.exe (PID: 2644)
- system_update_5.08.02.25.tmp (PID: 2780)
- system_update_5.08.02.25.exe (PID: 2824)
- system_update_5.08.02.25.tmp (PID: 2788)
- InstallUtil.exe (PID: 3260)
- ConfigService.exe (PID: 3532)
- susetsched.exe (PID: 3540)
- uncsetting.exe (PID: 3580)
- StartSuService.exe (PID: 3252)
- SUService.exe (PID: 3404)
- TVSU2DirAllowWriting.exe (PID: 3932)
- tvsu.exe (PID: 2548)
- ConfigService.exe (PID: 1344)
- TvsuCommandLauncher.exe (PID: 2324)
- ConfigScheduledTask.exe (PID: 3696)
- uncserver.exe (PID: 2616)
- uncsetting.exe (PID: 2636)
- UACSdk.exe (PID: 972)
- TvsuCommandLauncher.exe (PID: 2816)
- Tvsukernel.exe (PID: 2760)
- ConfigService.exe (PID: 2876)
- susetsched.exe (PID: 1472)
- ConfigScheduledTask.exe (PID: 3316)
- ConfigService.exe (PID: 2916)
- IA.exe (PID: 3288)
- IA.exe (PID: 2516)
- ConfigService.exe (PID: 3524)
Executable content was dropped or overwritten
- chrome.exe (PID: 3968)
The process uses the downloaded file
- chrome.exe (PID: 2692)
- chrome.exe (PID: 3968)
Drops the executable file immediately after the start
- chrome.exe (PID: 3968)
Create files in a temporary directory
- system_update_5.08.02.25.exe (PID: 2644)
- system_update_5.08.02.25.tmp (PID: 2788)
- IA.exe (PID: 3288)
- IA.exe (PID: 2516)
Application launched itself
- chrome.exe (PID: 3968)
Creates files in the program directory
- system_update_5.08.02.25.tmp (PID: 2788)
- InstallUtil.exe (PID: 3260)
- StartSuService.exe (PID: 3252)
- SUService.exe (PID: 3404)
- ConfigScheduledTask.exe (PID: 3696)
- Tvsukernel.exe (PID: 2760)
- IA.exe (PID: 3288)
- IA.exe (PID: 2516)
Reads Environment values
- system_update_5.08.02.25.tmp (PID: 2788)
- Tvsukernel.exe (PID: 2760)
- IA.exe (PID: 2516)
Reads the machine GUID from the registry
- InstallUtil.exe (PID: 3260)
- uncsetting.exe (PID: 3580)
- ConfigScheduledTask.exe (PID: 3696)
- uncsetting.exe (PID: 2636)
- Tvsukernel.exe (PID: 2760)
- SUService.exe (PID: 3404)
- uncserver.exe (PID: 2616)
- IA.exe (PID: 3288)
- IA.exe (PID: 2516)
Reads the software policy settings
- SUService.exe (PID: 3404)
- Tvsukernel.exe (PID: 2760)
- IA.exe (PID: 2516)
Disables trace logs
- Tvsukernel.exe (PID: 2760)
Checks proxy server information
- Tvsukernel.exe (PID: 2760)
Creates files or folders in the user directory
- Tvsukernel.exe (PID: 2760)
Reads product name
- Tvsukernel.exe (PID: 2760)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
121
Monitored processes
64
Malicious processes
9
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 308 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=5 --mojo-platform-channel-handle=1988 --field-trial-handle=1168,i,5824895032504529617,5229416256517382871,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Version: 109.0.5414.120 Modules
| |||||||||||||||
| 524 | "C:\Windows\system32\schtasks.exe" /Create /TN "TVT\TVSUUpdateTask_UserLogOn" /XML "C:\Program Files\Lenovo\System Update\tmpTVSUUpdateTask_UserLogOn.xml" /F | C:\Windows\System32\schtasks.exe | — | ConfigScheduledTask.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Manages scheduled tasks Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 748 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=storage.mojom.StorageService --lang=en-US --service-sandbox-type=service --disable-quic --mojo-platform-channel-handle=1508 --field-trial-handle=1168,i,5824895032504529617,5229416256517382871,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Version: 109.0.5414.120 Modules
| |||||||||||||||
| 864 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --disable-quic --mojo-platform-channel-handle=1292 --field-trial-handle=1168,i,5824895032504529617,5229416256517382871,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Version: 109.0.5414.120 Modules
| |||||||||||||||
| 972 | "C:\Program Files\Lenovo\System Update\UACSdk.exe" "" | C:\Program Files\Lenovo\System Update\UACSdk.exe | — | SUService.exe | |||||||||||
User: SYSTEM Integrity Level: SYSTEM Description: uacsdk Application Exit code: 4294967295 Version: 5, 08, 02, 25 Modules
| |||||||||||||||
| 1072 | "C:\Program Files\Windows Media Player\wmpnscfg.exe" | C:\Program Files\Windows Media Player\wmpnscfg.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Media Player Network Sharing Service Configuration Application Exit code: 0 Version: 12.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1120 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --gpu-preferences=UAAAAAAAAADgACAYAAAAAAAAAAAAAAAAAABgAAAAAAAwAAAAAAAAAAAAAAAQAAAAAAAAAAAAAAAAAAAAAAAAAEgAAAAAAAAASAAAAAAAAAAYAAAAAgAAABAAAAAAAAAAGAAAAAAAAAAQAAAAAAAAAAAAAAAOAAAAEAAAAAAAAAABAAAADgAAAAgAAAAAAAAACAAAAAAAAAA= --mojo-platform-channel-handle=1084 --field-trial-handle=1168,i,5824895032504529617,5229416256517382871,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1212 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=audio.mojom.AudioService --lang=en-US --service-sandbox-type=audio --disable-quic --mojo-platform-channel-handle=3616 --field-trial-handle=1168,i,5824895032504529617,5229416256517382871,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1344 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilReadIcon --lang=en-US --service-sandbox-type=icon_reader --disable-quic --mojo-platform-channel-handle=3152 --field-trial-handle=1168,i,5824895032504529617,5229416256517382871,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1344 | "C:\Program Files\Lenovo\System Update\ConfigService.exe" start | C:\Program Files\Lenovo\System Update\ConfigService.exe | — | tvsu.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: ConfigService Application Exit code: 0 Version: 5, 08, 02, 25 Modules
| |||||||||||||||
Total events
70 367
Read events
69 793
Write events
522
Delete events
52
Modification events
| (PID) Process: | (3968) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3968) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3968) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (3968) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3968) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3968) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3968) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (3968) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3968) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (3968) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid |
Value: | |||
Executable files
203
Suspicious files
95
Text files
421
Unknown types
22
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3968 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RF104085.TMP | — | |
MD5:— | SHA256:— | |||
| 3968 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3968 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad\settings.dat | binary | |
MD5:9C016064A1F864C8140915D77CF3389A | SHA256:0E7265D4A8C16223538EDD8CD620B8820611C74538E420A88E333BE7F62AC787 | |||
| 3968 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Last Version | text | |
MD5:9F941EA08DBDCA2EB3CFA1DBBBA6F5DC | SHA256:127F71DF0D2AD895D4F293E62284D85971AE047CA15F90B87BF6335898B0B655 | |||
| 3968 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Local Storage\leveldb\LOG.old | text | |
MD5:FA25AF7098FC1571F24F200A9D105D58 | SHA256:4F40C87070B7A151FB241CCF36E7027AA703C15CA0ACB0A1759DA07B2C318574 | |||
| 3968 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF1040a5.TMP | text | |
MD5:ECD3386BCC950E73B86EB128A5F57622 | SHA256:C9A068EAFBC587EDFC89392F64DDD350EEB96C5CF195CDB030BAB8F6DD33833B | |||
| 3968 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old~RF10479a.TMP | — | |
MD5:— | SHA256:— | |||
| 3968 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3968 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Local Storage\leveldb\LOG.old~RF1041be.TMP | text | |
MD5:AD0DB8476493577A67FA94A162B646C4 | SHA256:304FB5B4FD83D4A9FF1EF4CF20232A1783169C148297BFE37ED24A1D22A74F2B | |||
| 3968 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:825B582C78EC88D54C215EFDF1EAD639 | SHA256:367995D01A8F13E5C30C79499F86B034775BFD009D83DC97635DE438D47DFA37 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
60
DNS requests
112
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
884 | svchost.exe | HEAD | — | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvYTBmQUFZUHRkSkgtb01uSGNvRHZ2Tm5HQQ/1.0.0.15_llkgjffcdpffmhiakmfcdcblohccpfmo.crx | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | unknown |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 224.0.0.252:5355 | — | — | — | unknown |
3968 | chrome.exe | 239.255.255.250:1900 | — | — | — | unknown |
864 | chrome.exe | 142.250.145.84:443 | accounts.google.com | GOOGLE | US | unknown |
864 | chrome.exe | 2.19.217.18:443 | pcsupport.lenovo.com | Akamai International B.V. | NL | unknown |
864 | chrome.exe | 84.53.164.75:443 | s2.go-mpulse.net | AKAMAI-AS | NL | unknown |
864 | chrome.exe | 23.32.101.13:443 | download.lenovo.com | AKAMAI-AS | SE | unknown |
864 | chrome.exe | 23.35.236.237:443 | assets.adobedtm.com | AKAMAI-AS | DE | unknown |
864 | chrome.exe | 142.250.181.234:443 | maps.googleapis.com | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
accounts.google.com |
| shared |
pcsupport.lenovo.com |
| unknown |
account.lenovo.com |
| unknown |
s2.go-mpulse.net |
| whitelisted |
assets.adobedtm.com |
| whitelisted |
cdn.quantummetric.com |
| whitelisted |
digitalfeedback.us.confirmit.com |
| unknown |
dntcl.qualaroo.com |
| whitelisted |
download.lenovo.com |
| unknown |
maps.googleapis.com |
| whitelisted |