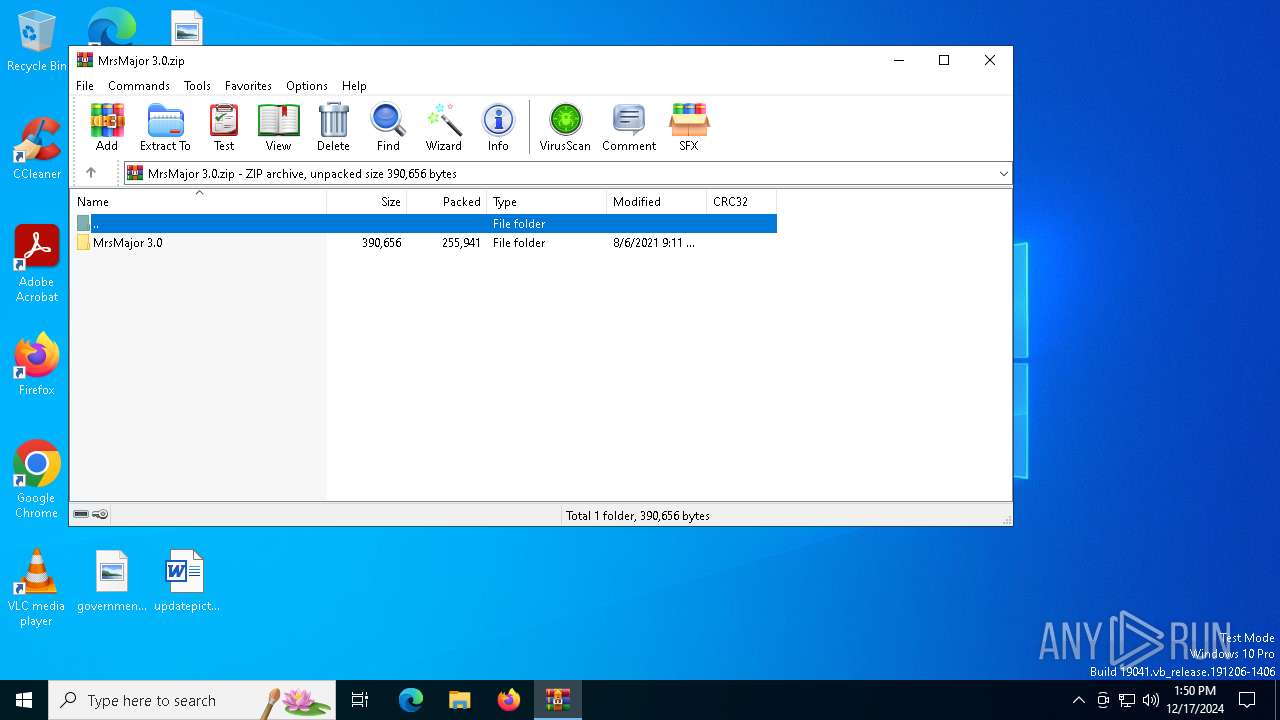
| File name: | MrsMajor 3.0.zip |
| Full analysis: | https://app.any.run/tasks/bc1945d6-5c8e-4f9f-94b1-b1cfea12d9f5 |
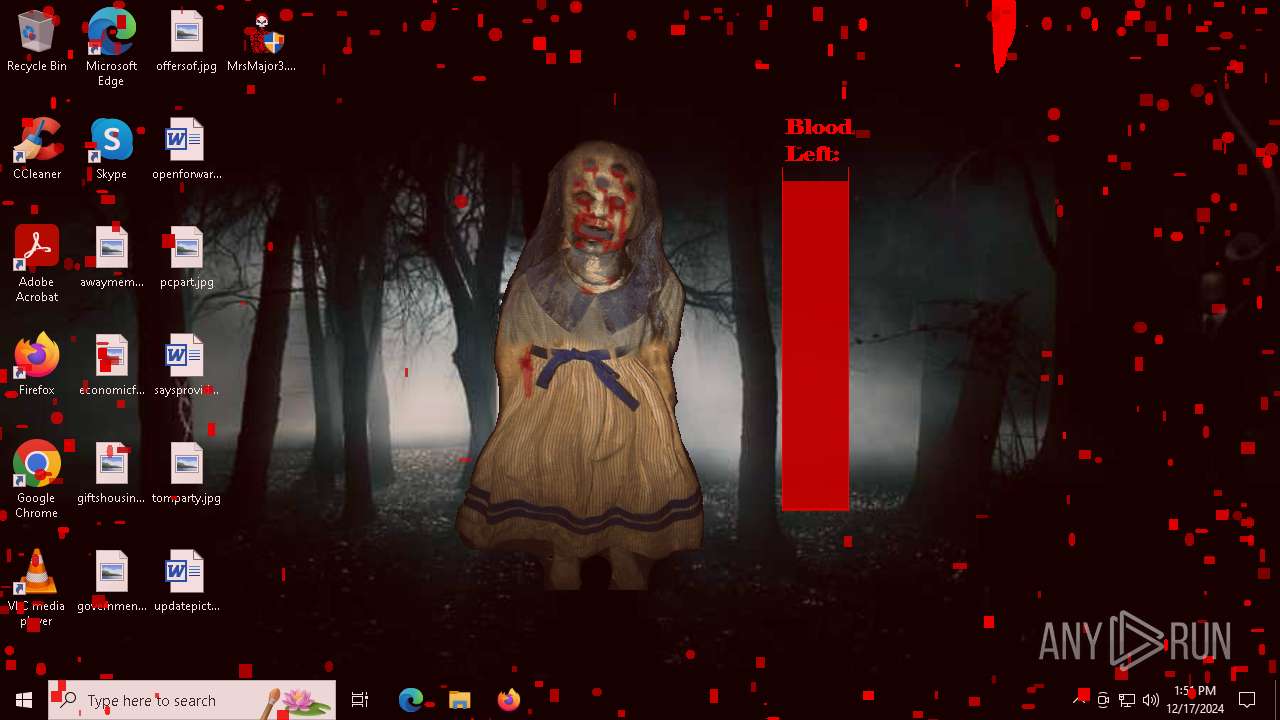
| Verdict: | Malicious activity |
| Analysis date: | December 17, 2024, 13:50:24 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v1.0 to extract, compression method=store |
| MD5: | E8AAE93A4C9F7EF9109C0A2BA74A4A28 |
| SHA1: | 300BB3F34E9E56354D478D1659BA527C1EA464D0 |
| SHA256: | 5DC520E42805780DCD0E8BF690928EE72130D58280B6B8044C5FF9C168575BAE |
| SSDEEP: | 12288:jmw1v6I5CM/wBWrbtG7WQDJliGR31HQS5XFB:jf1v6mx/wBWrZG7WQDJZp9QSxFB |
MALICIOUS
Changes the login/logoff helper path in the registry
- MrsMajor3.0.exe (PID: 6604)
SUSPICIOUS
Reads security settings of Internet Explorer
- MrsMajor3.0.exe (PID: 6604)
- MrsMajor3.0.exe (PID: 5804)
The system shut down or reboot
- MrsMajor3.0.exe (PID: 6604)
Uses ICACLS.EXE to modify access control lists
- cmd.exe (PID: 5456)
- MrsMajor3.0.exe (PID: 6604)
- MrsMajor3.0.exe (PID: 5804)
- MrsMajor3.0.exe (PID: 5576)
- MrsMajor3.0.exe (PID: 6264)
- MrsMajor3.0.exe (PID: 6592)
The process executes via Task Scheduler
- PLUGScheduler.exe (PID: 3280)
Executable content was dropped or overwritten
- cmd.exe (PID: 5456)
- MrsMajor3.0.exe (PID: 6604)
Uses TIMEOUT.EXE to delay execution
- cmd.exe (PID: 5456)
Uses TASKKILL.EXE to kill process
- cmd.exe (PID: 5456)
Reads the date of Windows installation
- MrsMajor3.0.exe (PID: 5804)
- MrsMajor3.0.exe (PID: 6604)
Executes application which crashes
- MrsMajor3.0.exe (PID: 5804)
- MrsMajor3.0.exe (PID: 5576)
- MrsMajor3.0.exe (PID: 6264)
- MrsMajor3.0.exe (PID: 6592)
Takes ownership (TAKEOWN.EXE)
- MrsMajor3.0.exe (PID: 5804)
- MrsMajor3.0.exe (PID: 5576)
- MrsMajor3.0.exe (PID: 6264)
- MrsMajor3.0.exe (PID: 6592)
- MrsMajor3.0.exe (PID: 6604)
- cmd.exe (PID: 5456)
Creates file in the systems drive root
- icacls.exe (PID: 6716)
INFO
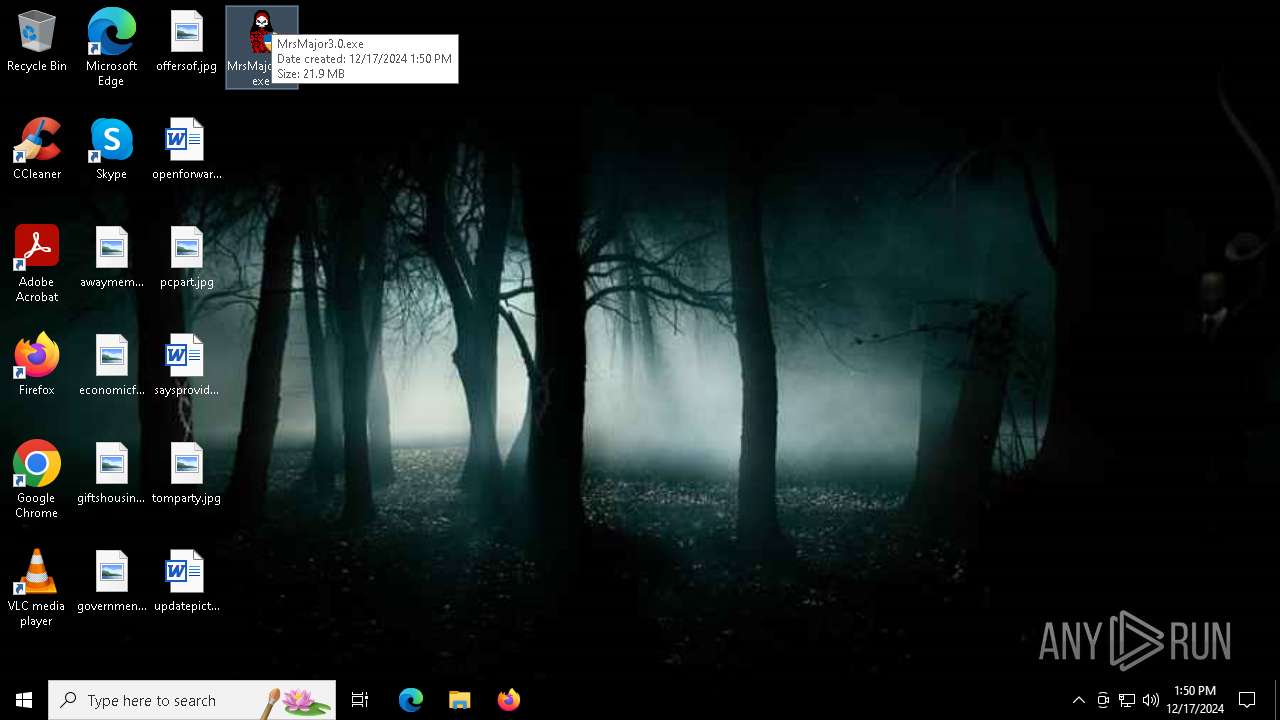
Manual execution by a user
- MrsMajor3.0.exe (PID: 6552)
- MrsMajor3.0.exe (PID: 6604)
- MrsMajor3.0.exe (PID: 4384)
- MrsMajor3.0.exe (PID: 5804)
- MrsMajor3.0.exe (PID: 5576)
- MrsMajor3.0.exe (PID: 3940)
- MrsMajor3.0.exe (PID: 5508)
- MrsMajor3.0.exe (PID: 6264)
- MrsMajor3.0.exe (PID: 6592)
- MrsMajor3.0.exe (PID: 6356)
Checks supported languages
- PLUGScheduler.exe (PID: 3280)
- MrsMajor3.0.exe (PID: 6604)
- MrsMajor3.0.exe (PID: 5804)
Reads the computer name
- MrsMajor3.0.exe (PID: 6604)
- MrsMajor3.0.exe (PID: 6264)
The process uses the downloaded file
- MrsMajor3.0.exe (PID: 6604)
Process checks computer location settings
- MrsMajor3.0.exe (PID: 6604)
- MrsMajor3.0.exe (PID: 5804)
Create files in a temporary directory
- MrsMajor3.0.exe (PID: 6604)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 10 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | None |
| ZipModifyDate: | 2021:08:06 23:11:20 |
| ZipCRC: | 0x00000000 |
| ZipCompressedSize: | - |
| ZipUncompressedSize: | - |
| ZipFileName: | MrsMajor 3.0/ |
Total processes
295
Monitored processes
44
Malicious processes
1
Suspicious processes
1
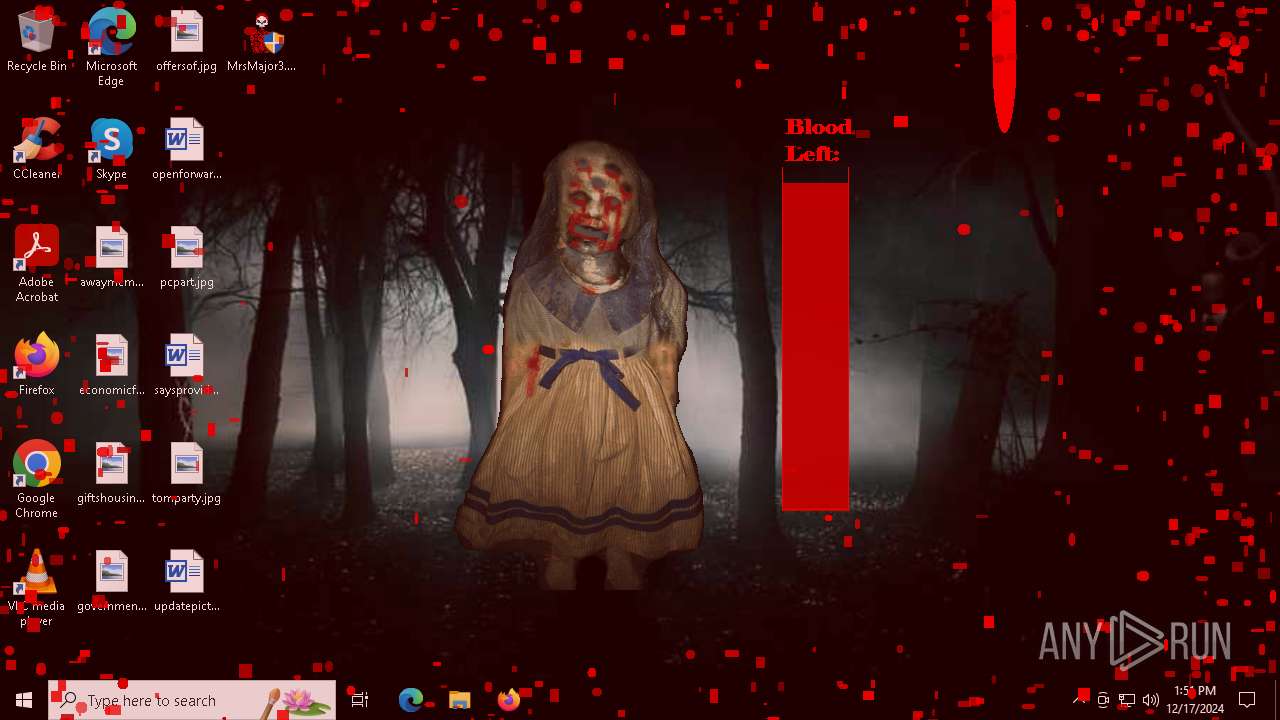
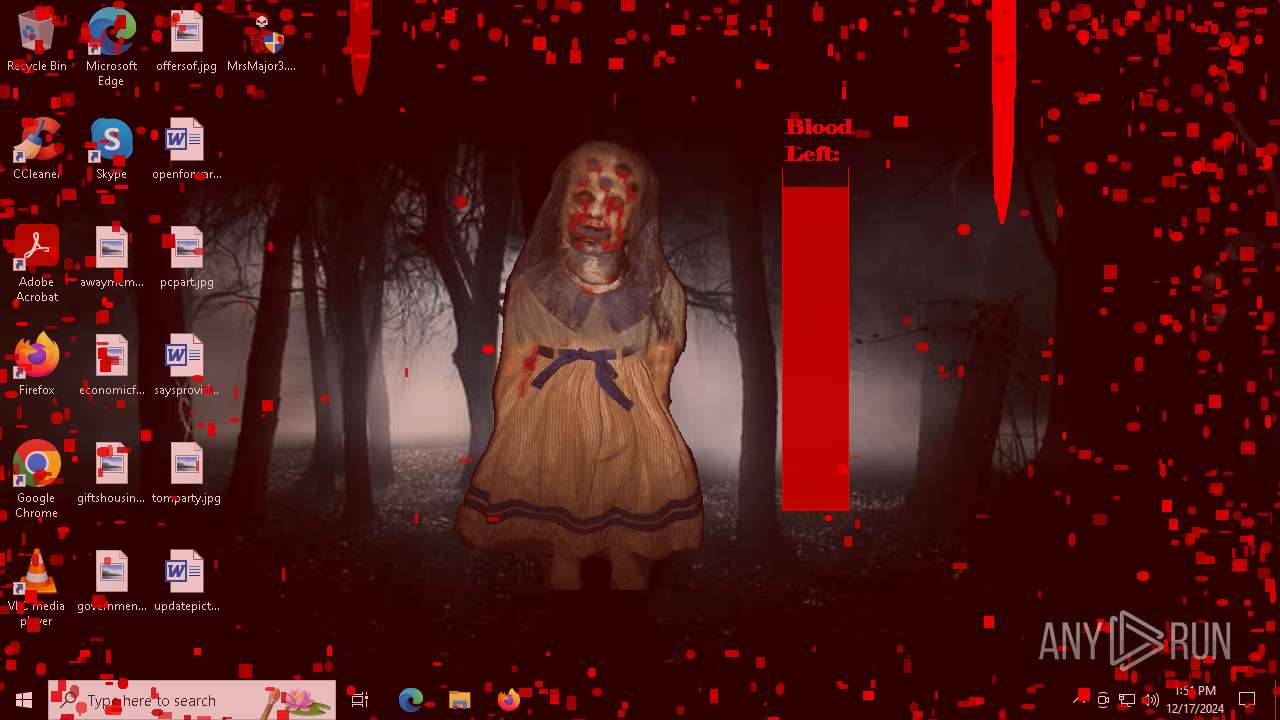
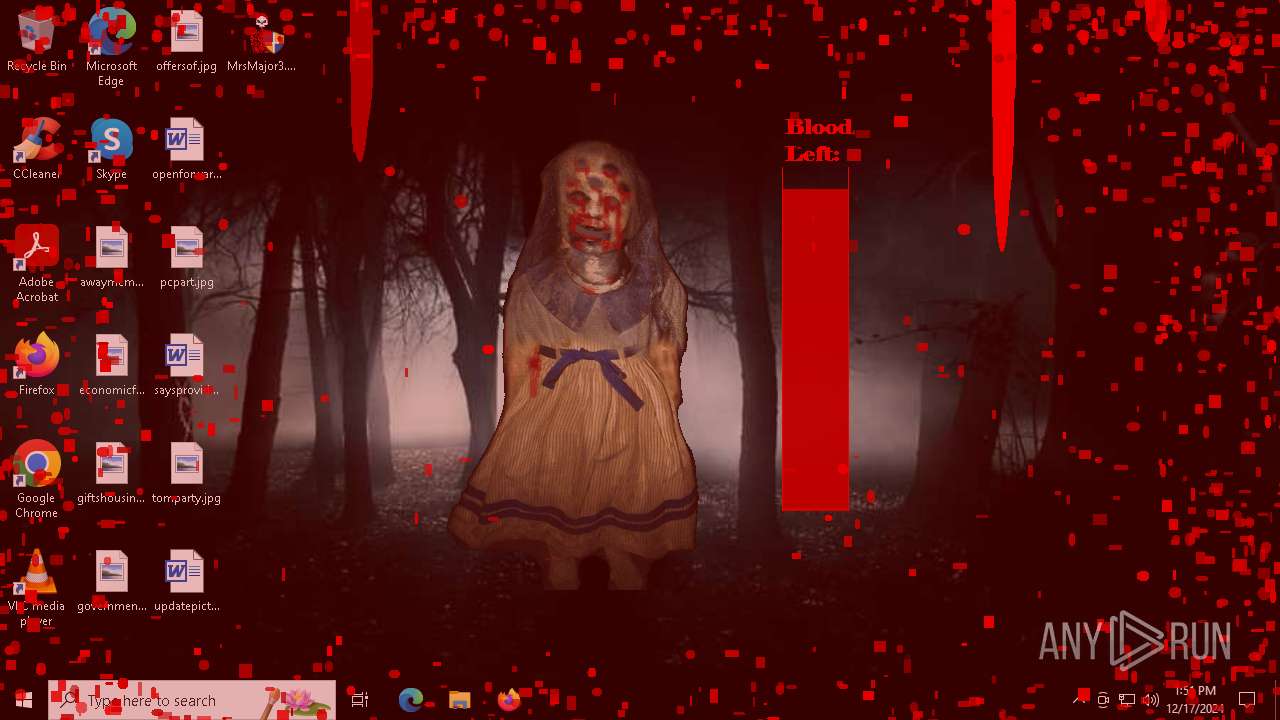
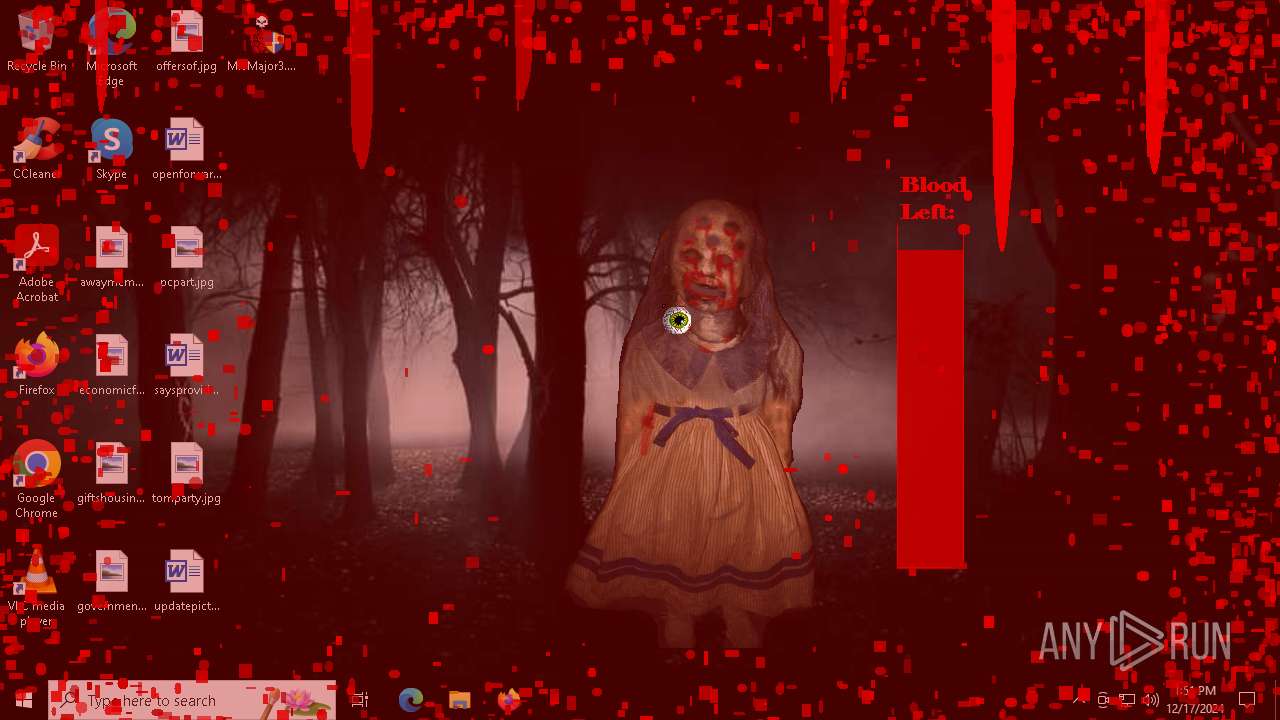
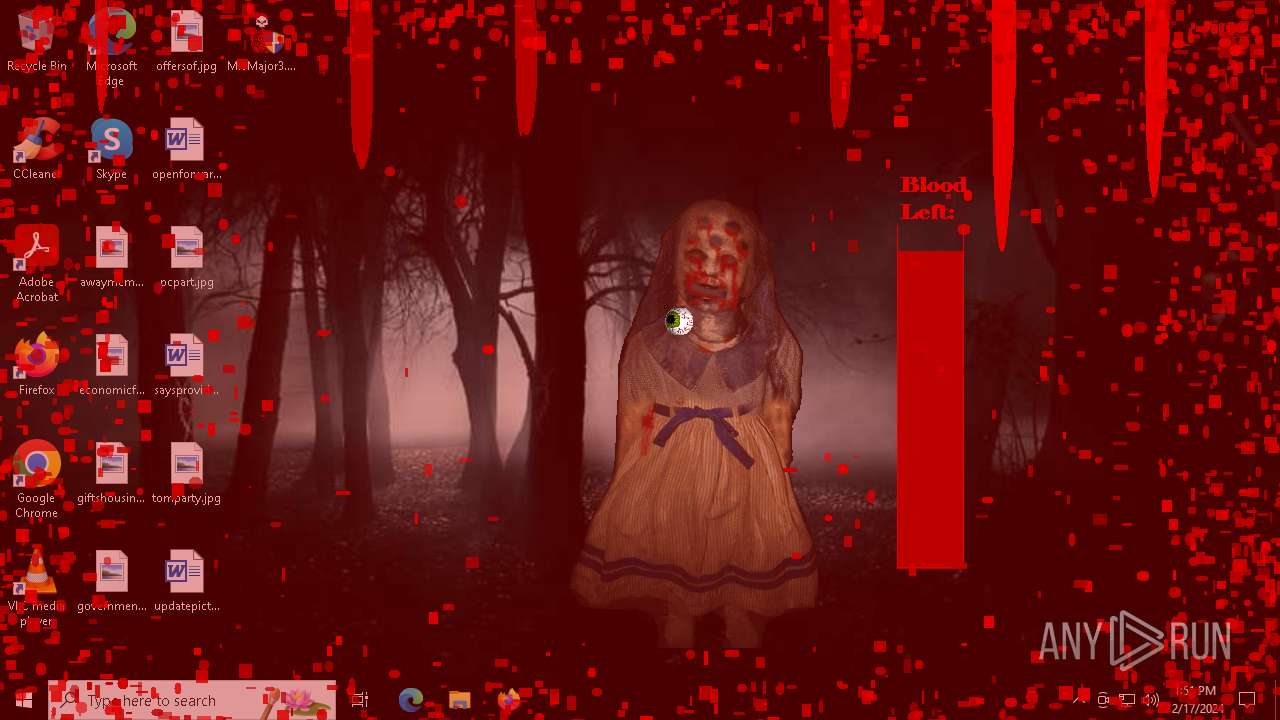
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2088 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\MrsMajor 3.0.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 3280 | "C:\Program Files\RUXIM\PLUGscheduler.exe" | C:\Program Files\RUXIM\PLUGScheduler.exe | — | svchost.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Update LifeCycle Component Scheduler Exit code: 0 Version: 10.0.19041.3623 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3940 | "C:\Users\admin\Desktop\MrsMajor3.0.exe" | C:\Users\admin\Desktop\MrsMajor3.0.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 4384 | "C:\Users\admin\Desktop\MrsMajor3.0.exe" | C:\Users\admin\Desktop\MrsMajor3.0.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 5176 | taskkill /f /im "tobi0a0c.exe" | C:\Windows\System32\taskkill.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Terminates Processes Exit code: 128 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5272 | "C:\windows\system32\takeown.exe" /f C:\ | C:\Windows\System32\takeown.exe | — | MrsMajor3.0.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Takes ownership of a file Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5284 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | icacls.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5316 | "C:\windows\system32\icacls.exe" C:\ /granted "admin":F | C:\Windows\System32\icacls.exe | — | MrsMajor3.0.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5456 | "C:\Windows\System32\cmd.exe" /c cd\&cd Windows\system32&takeown /f LogonUI.exe&icacls LogonUI.exe /granted "%username%":F&cd..&cd winbase_base_procid_none&cd secureloc0x65© "ui65.exe" "C:\windows\system32\LogonUI.exe" /Y&echo WinLTDRStartwinpos > "c:\windows\WinAttr.gci"&timeout 2&taskkill /f /im "tobi0a0c.exe"&exit | C:\Windows\System32\cmd.exe | logonuiOWR.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 128 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5464 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | icacls.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
2 427
Read events
2 403
Write events
24
Delete events
0
Modification events
| (PID) Process: | (2088) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (2088) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (2088) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (2088) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\MrsMajor 3.0.zip | |||
| (PID) Process: | (2088) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2088) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2088) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2088) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2088) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\MainWin |
| Operation: | write | Name: | Placement |
Value: 2C0000000000000001000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF3D0000002D000000FD03000016020000 | |||
| (PID) Process: | (2088) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\ArcColumnWidths |
| Operation: | write | Name: | name |
Value: 256 | |||
Executable files
4
Suspicious files
44
Text files
11
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6604 | MrsMajor3.0.exe | C:\Windows\winbase_base_procid_none\secureloc0x65\mainbgtheme.wav | — | |
MD5:— | SHA256:— | |||
| 6604 | MrsMajor3.0.exe | C:\Windows\winbase_base_procid_none\secureloc0x65\gdifuncs.exe | executable | |
MD5:FE67FFB85D13A17579511F9C42EE2E17 | SHA256:4B715BCFD0F4DB63A7F96939048B38E60E0CD29B73953AFC81FE107EB10707A3 | |||
| 6604 | MrsMajor3.0.exe | C:\Windows\winbase_base_procid_none\secureloc0x65\WinRapistI386.vbs | text | |
MD5:8DF277AA3459FBE66FB0C06179390ACD | SHA256:2287E91B9372B33B48890A52E54007B1EB9A488A9E9FE0330639698AECF2576A | |||
| 6604 | MrsMajor3.0.exe | C:\Windows\winbase_base_procid_none\secureloc0x65\rcur.cur | binary | |
MD5:289624A46BB7EC6D91D5B099343B7F24 | SHA256:B93B0CB2BB965F5758CB0C699FBC827A64712D6F248AAF810CDE5FA5EF3227EB | |||
| 3280 | PLUGScheduler.exe | C:\ProgramData\PLUG\Logs\RUXIMLog.047.etl | binary | |
MD5:FA358BFEE9B4E1FFB7394D13CBBC4898 | SHA256:6FF97BBF8A56286A4C71623829514CC14B7F8CBBCF09748D939F733968478A22 | |||
| 3280 | PLUGScheduler.exe | C:\ProgramData\PLUG\Logs\RUXIMLog.043.etl | binary | |
MD5:2F36C598EBFF5B5CDD898C9691D6BCCB | SHA256:8900C5931ED8E0D1B68082B45CF2F4E8C1025D36825508E0804C916D781B9F50 | |||
| 3280 | PLUGScheduler.exe | C:\ProgramData\PLUG\Logs\RUXIMLog.041.etl | binary | |
MD5:44A0E917AD0C126931B1BCD959285A9A | SHA256:DDFBE47E7DFD6D8B7517F2F6FF9808ECF3C0A25F588A9F96D04F4E2B4A578573 | |||
| 3280 | PLUGScheduler.exe | C:\ProgramData\PLUG\Logs\RUXIMLog.044.etl | etl | |
MD5:079890A8EC8D5CB6523FCEC2209780AA | SHA256:0E12D2D76DD738CE196BED522E35F75E2CC91294F78CDDCBE8CE7787AAA70049 | |||
| 3280 | PLUGScheduler.exe | C:\ProgramData\PLUG\Logs\RUXIMLog.032.etl | binary | |
MD5:8A2BDE0EAFA7E946196A1B114AB636E9 | SHA256:1C338CBDD9316D7FD8F208341466FEDC554A04D489B3A86C736EC3831A2F2BA2 | |||
| 3280 | PLUGScheduler.exe | C:\ProgramData\PLUG\Logs\RUXIMLog.042.etl | binary | |
MD5:868E79A00A8204448B2FFC4F4D5C08EA | SHA256:148FE324431CB4C826BCF0436147D946AC389A877732612CF40629048B8517DC | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
27
DNS requests
8
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5064 | SearchApp.exe | 104.126.37.186:443 | — | Akamai International B.V. | DE | unknown |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
440 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
3976 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 224.0.0.251:5353 | — | — | — | unknown |
— | — | 224.0.0.252:5355 | — | — | — | whitelisted |
2956 | OfficeClickToRun.exe | 52.109.28.46:443 | officeclient.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | GB | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
self.events.data.microsoft.com |
| whitelisted |
officeclient.microsoft.com |
| whitelisted |
ecs.office.com |
| whitelisted |
www.bing.com |
| whitelisted |
watson.events.data.microsoft.com |
| whitelisted |