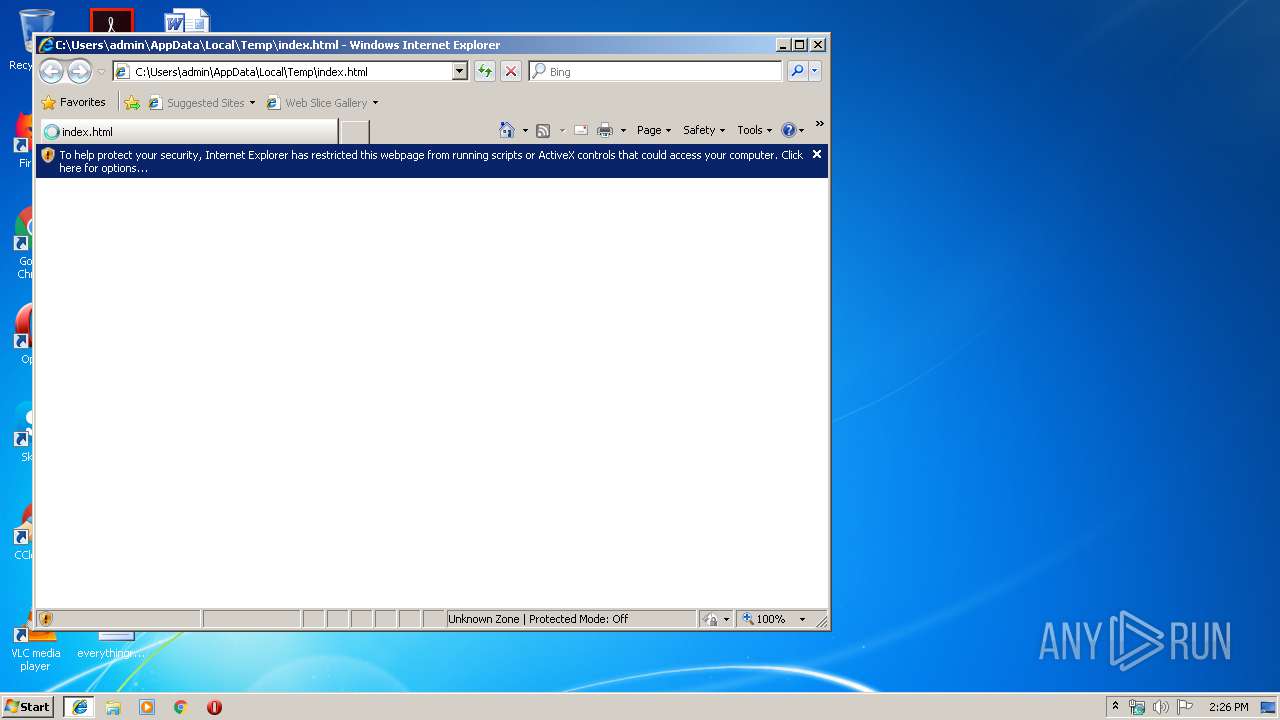
| download: | index.html |
| Full analysis: | https://app.any.run/tasks/dd5988b6-c9d7-4544-901a-96a0effd093b |
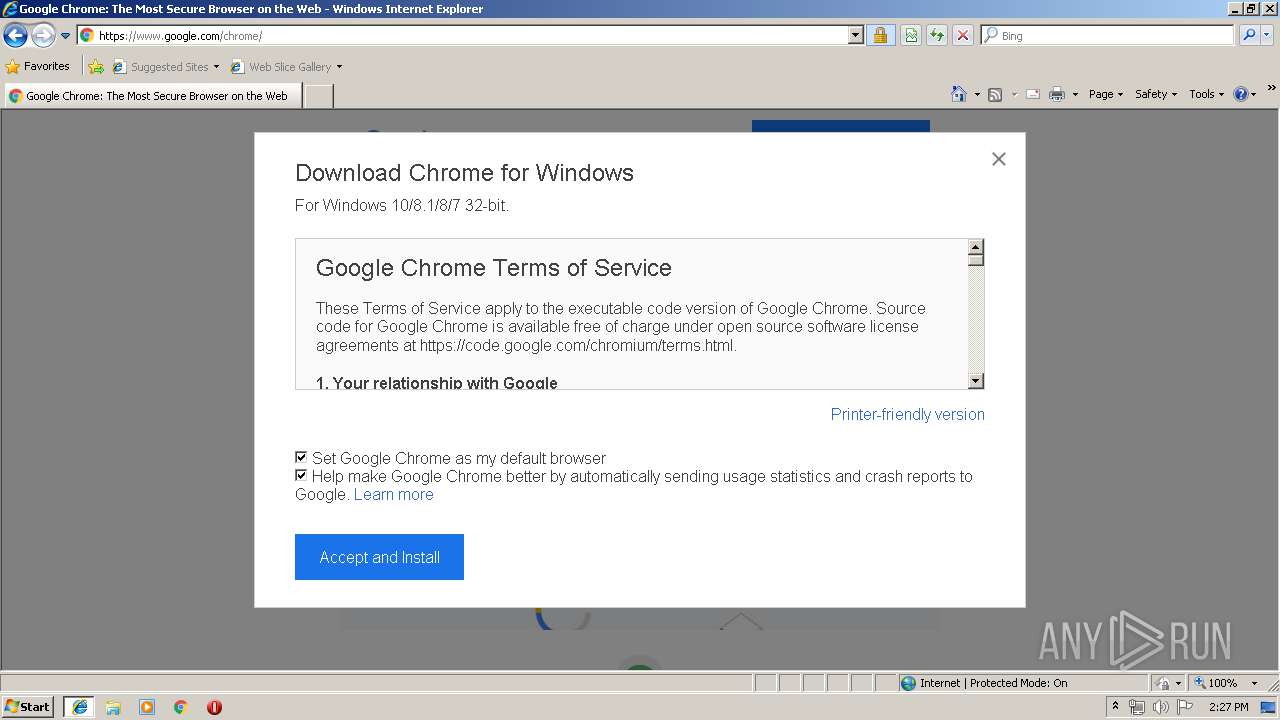
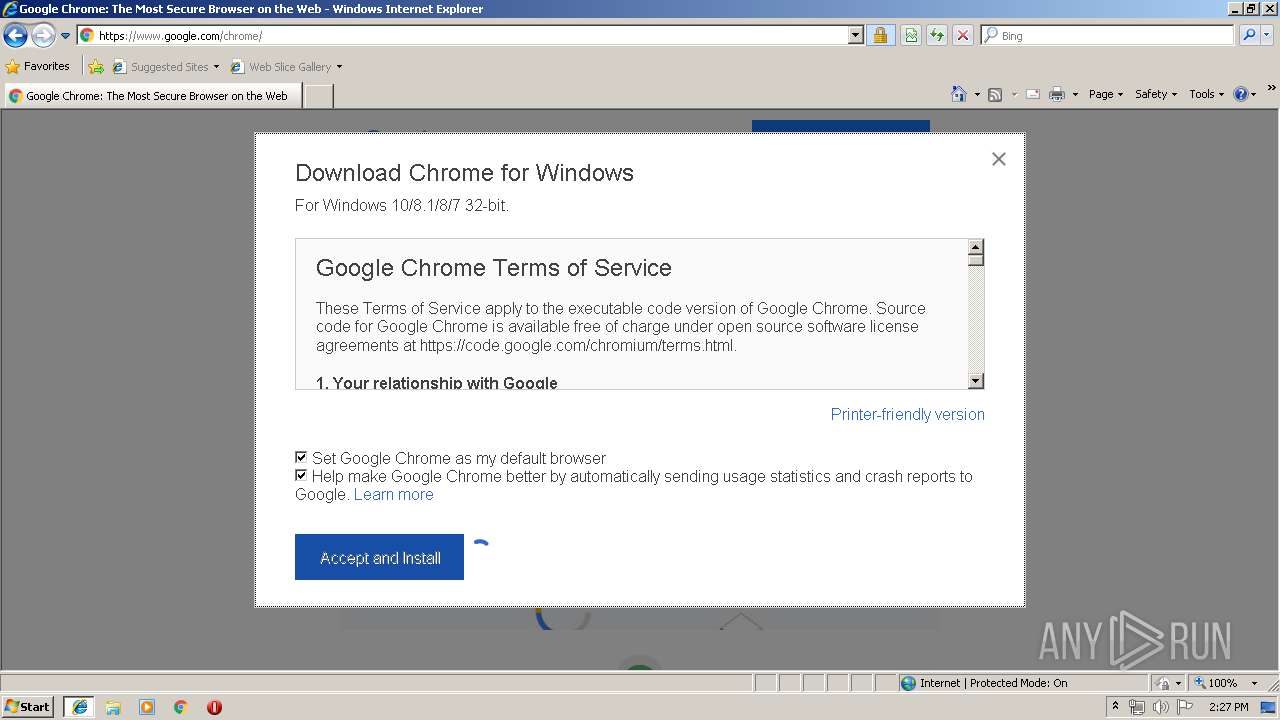
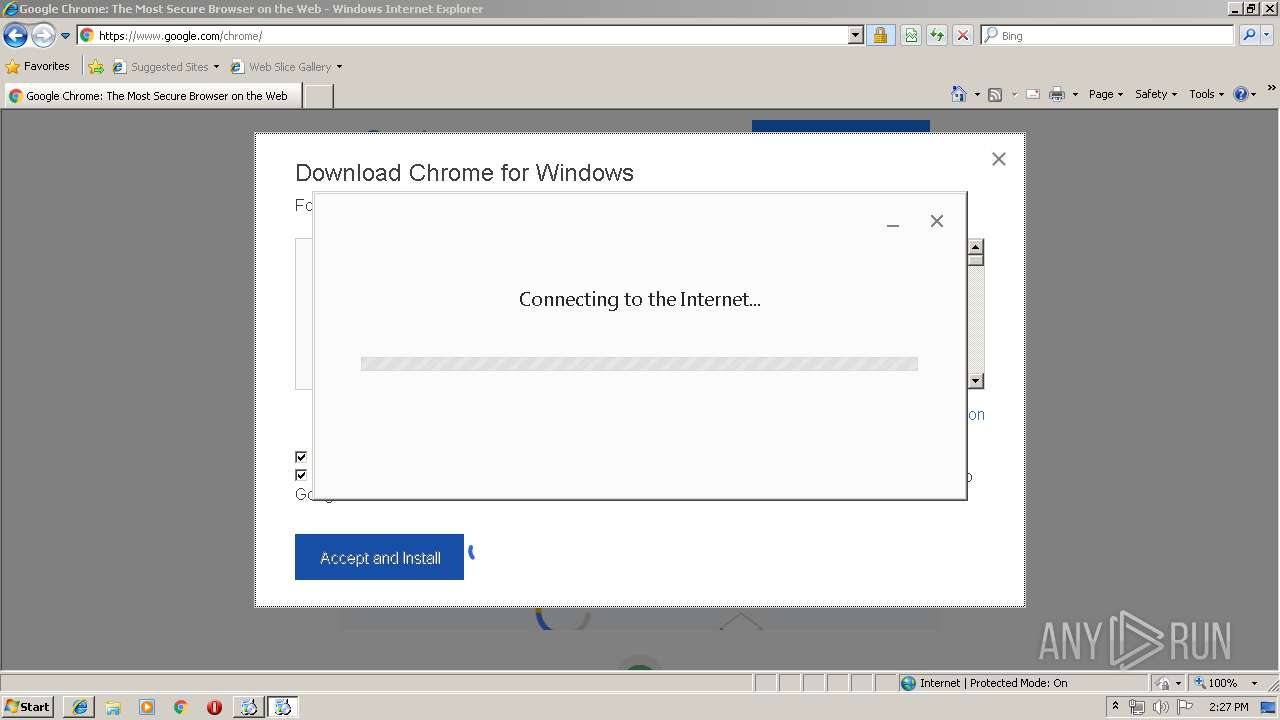
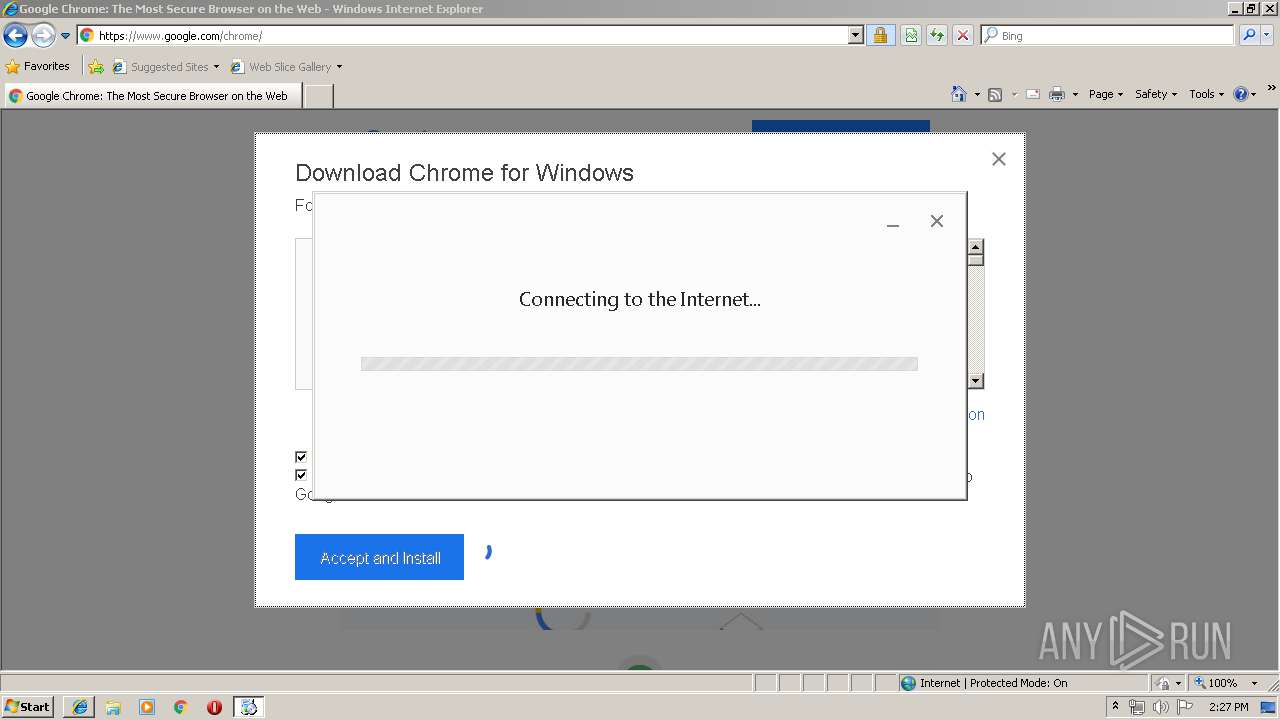
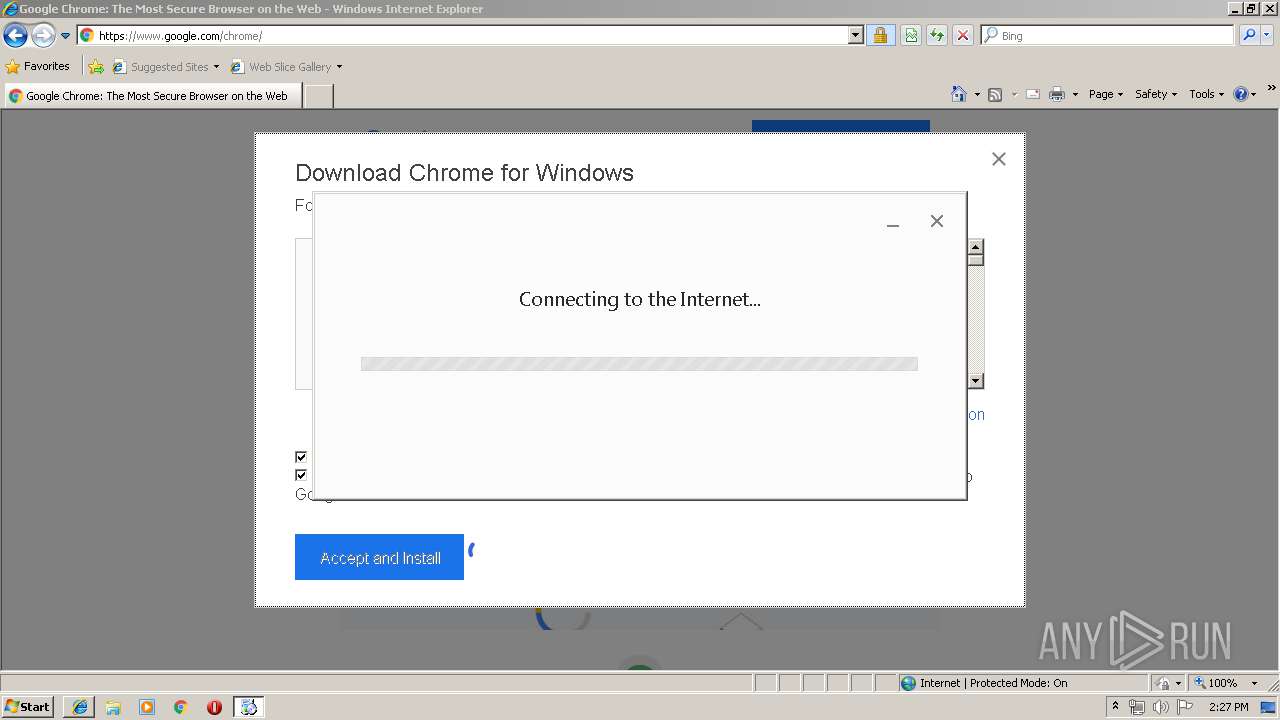
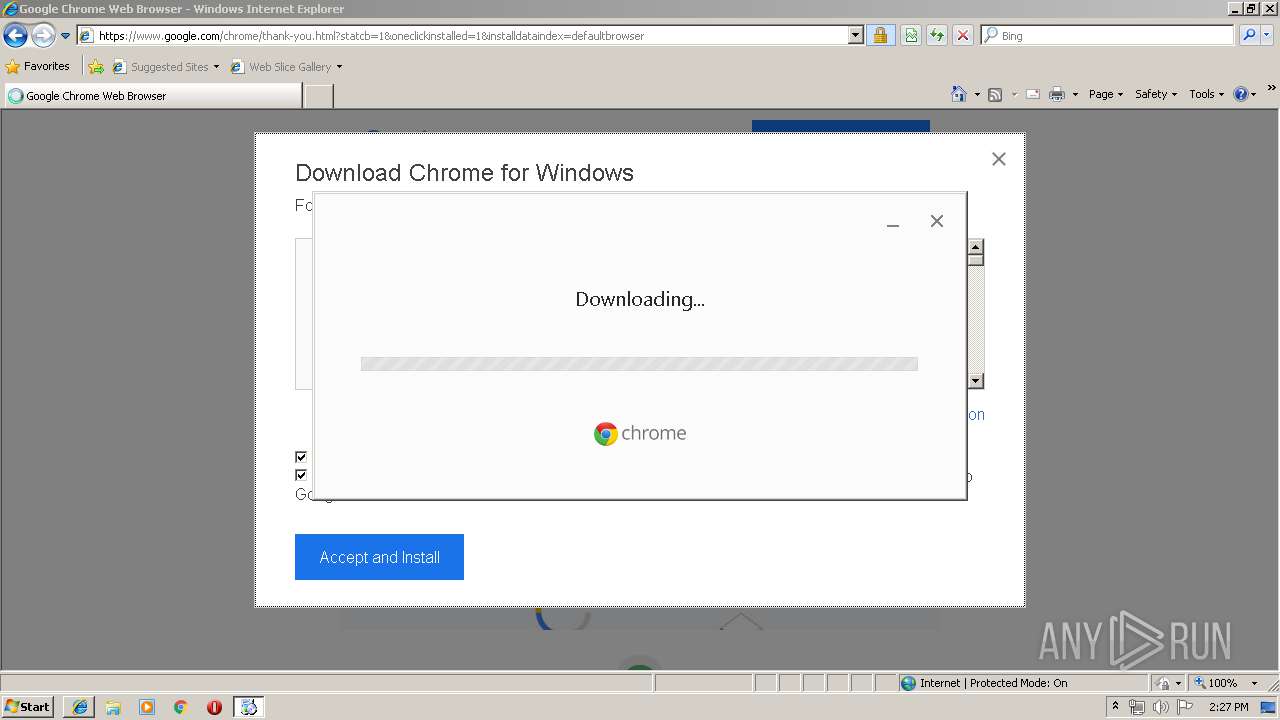
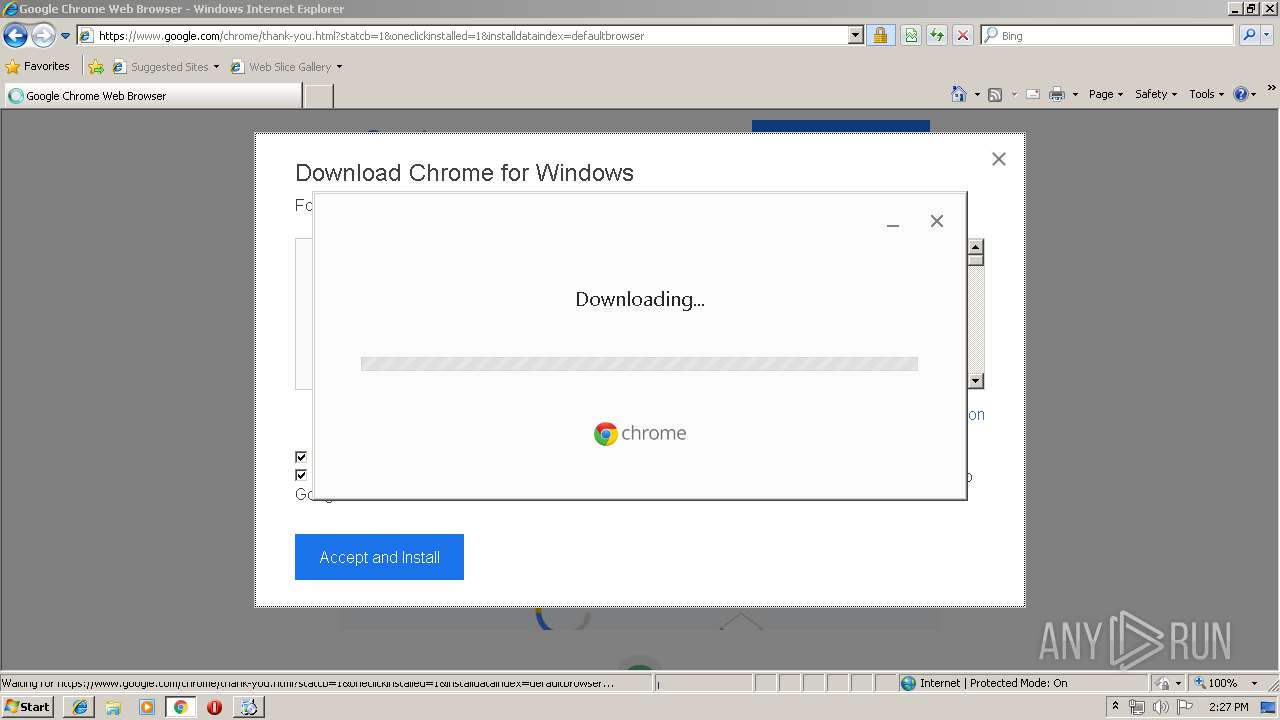
| Verdict: | Malicious activity |
| Analysis date: | March 21, 2019, 14:26:39 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | text/html |
| File info: | HTML document, ASCII text, with very long lines |
| MD5: | B10F518A97ABA067F69F5E355F87FB99 |
| SHA1: | 98345CC2D262AC9E02CC67CB6D1F3372F1B1B9F5 |
| SHA256: | 5DBD2DE34EB40487496E1C58277459BE0F14403CA0090007C099E48F84A91014 |
| SSDEEP: | 384:9GbohIjRQzb/I0v2hR9gNk88mXfugQJEE:9oohIjazb/I0u1gD8AUt |
MALICIOUS
Application was dropped or rewritten from another process
- GoogleUpdateSetup.exe (PID: 2708)
- GoogleUpdate.exe (PID: 2856)
- GoogleUpdate.exe (PID: 540)
- GoogleUpdate.exe (PID: 1376)
- GoogleUpdate.exe (PID: 3548)
- GoogleUpdateWebPlugin.exe (PID: 1660)
- GoogleUpdateWebPlugin.exe (PID: 3152)
- GoogleUpdate.exe (PID: 4032)
- GoogleUpdate.exe (PID: 1552)
Loads dropped or rewritten executable
- GoogleUpdate.exe (PID: 2856)
- GoogleUpdate.exe (PID: 1376)
- GoogleUpdate.exe (PID: 4032)
- GoogleUpdate.exe (PID: 540)
- GoogleUpdate.exe (PID: 3548)
- GoogleUpdate.exe (PID: 1552)
- iexplore.exe (PID: 2396)
Changes settings of System certificates
- GoogleUpdate.exe (PID: 1552)
SUSPICIOUS
Executable content was dropped or overwritten
- GoogleUpdate.exe (PID: 540)
- GoogleUpdateSetup.exe (PID: 2708)
Starts itself from another location
- GoogleUpdate.exe (PID: 540)
Creates files in the program directory
- GoogleUpdateSetup.exe (PID: 2708)
Adds / modifies Windows certificates
- GoogleUpdate.exe (PID: 1552)
INFO
Changes internet zones settings
- iexplore.exe (PID: 128)
- iexplore.exe (PID: 2076)
Creates files in the user directory
- iexplore.exe (PID: 2076)
- FlashUtil32_26_0_0_131_ActiveX.exe (PID: 716)
- iexplore.exe (PID: 2396)
Adds / modifies Windows certificates
- iexplore.exe (PID: 2076)
- iexplore.exe (PID: 2716)
Dropped object may contain Bitcoin addresses
- iexplore.exe (PID: 2396)
Reads internet explorer settings
- iexplore.exe (PID: 2716)
- iexplore.exe (PID: 2396)
Reads settings of System Certificates
- iexplore.exe (PID: 2716)
- iexplore.exe (PID: 2076)
- iexplore.exe (PID: 2396)
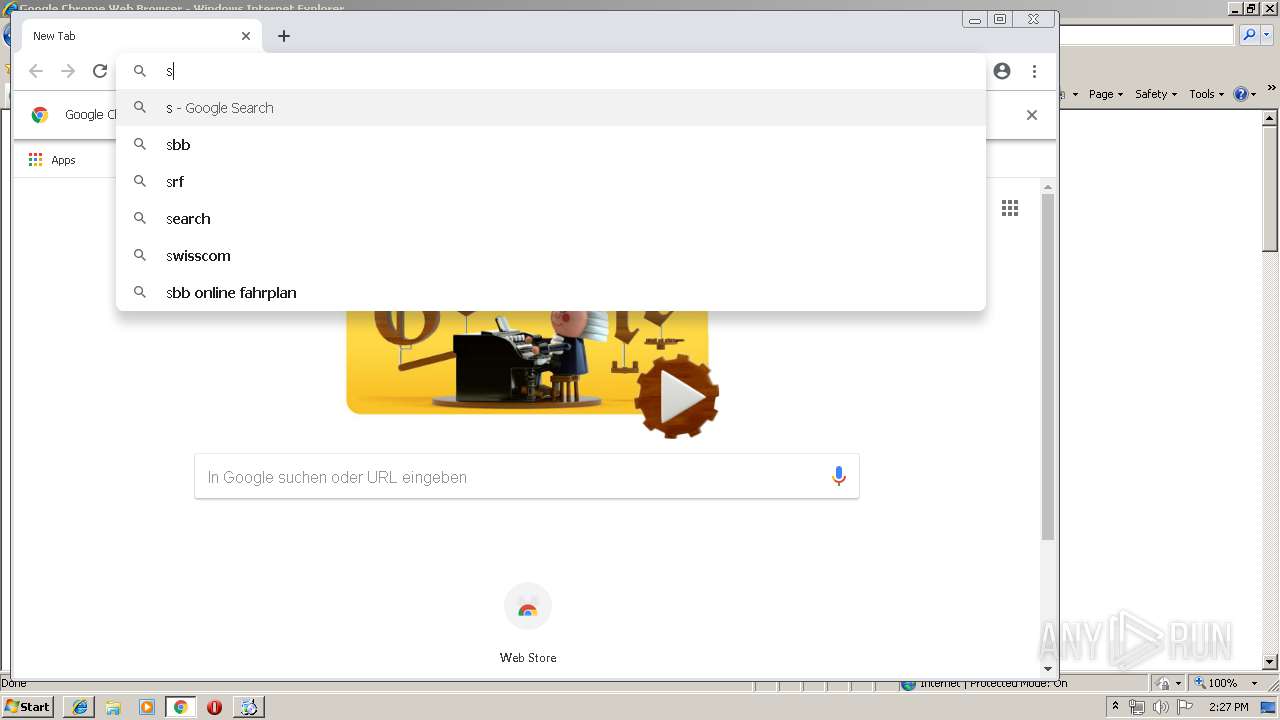
- chrome.exe (PID: 2160)
Application launched itself
- iexplore.exe (PID: 128)
- iexplore.exe (PID: 2076)
- chrome.exe (PID: 1332)
Changes settings of System certificates
- iexplore.exe (PID: 2716)
- iexplore.exe (PID: 2076)
Reads Internet Cache Settings
- iexplore.exe (PID: 2076)
- iexplore.exe (PID: 2396)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .html | | | HyperText Markup Language (100) |
|---|
Total processes
63
Monitored processes
27
Malicious processes
7
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 128 | "C:\Program Files\Internet Explorer\iexplore.exe" C:\Users\admin\AppData\Local\Temp\index.html | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 540 | "C:\Program Files\Google\Update\GoogleUpdate.exe" /pi "https:%2F%2Fwww.google.com%2F" "%2Finstall%20%22appguid=%7B8A69D345-D564-463C-AFF1-A69D9E530F96%7D%26iid=%7B2303C001-BE25-CEBA-2BE7-468B3168CB20%7D%26lang=en%26browser=2%26usagestats=1%26appname=Google%2520Chrome%26needsadmin=true%26ap=stable-arch_x86-statsdef_1%26installdataindex=defaultbrowser%22" /installsource oneclick | C:\Program Files\Google\Update\GoogleUpdate.exe | GoogleUpdateWebPlugin.exe | ||||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Installer Exit code: 0 Version: 1.3.33.23 Modules
| |||||||||||||||
| 716 | C:\Windows\system32\Macromed\Flash\FlashUtil32_26_0_0_131_ActiveX.exe -Embedding | C:\Windows\system32\Macromed\Flash\FlashUtil32_26_0_0_131_ActiveX.exe | — | svchost.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: MEDIUM Description: Adobe® Flash® Player Installer/Uninstaller 26.0 r0 Exit code: 0 Version: 26,0,0,131 Modules
| |||||||||||||||
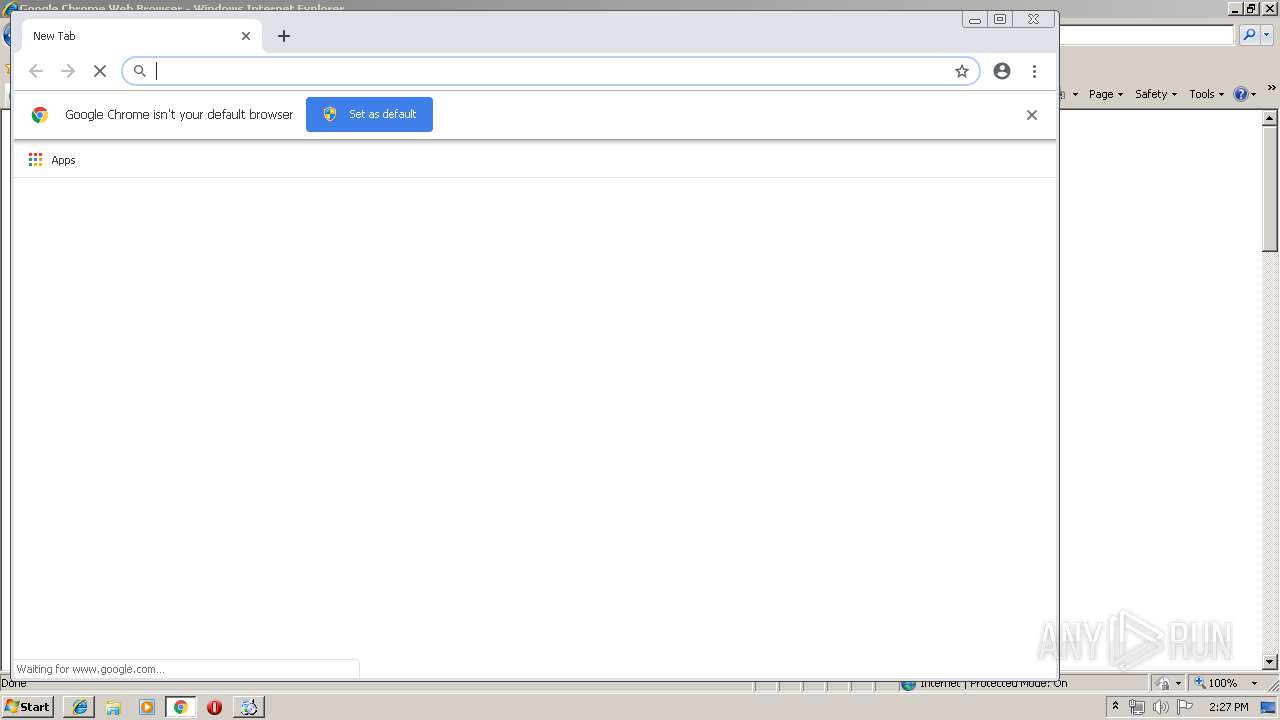
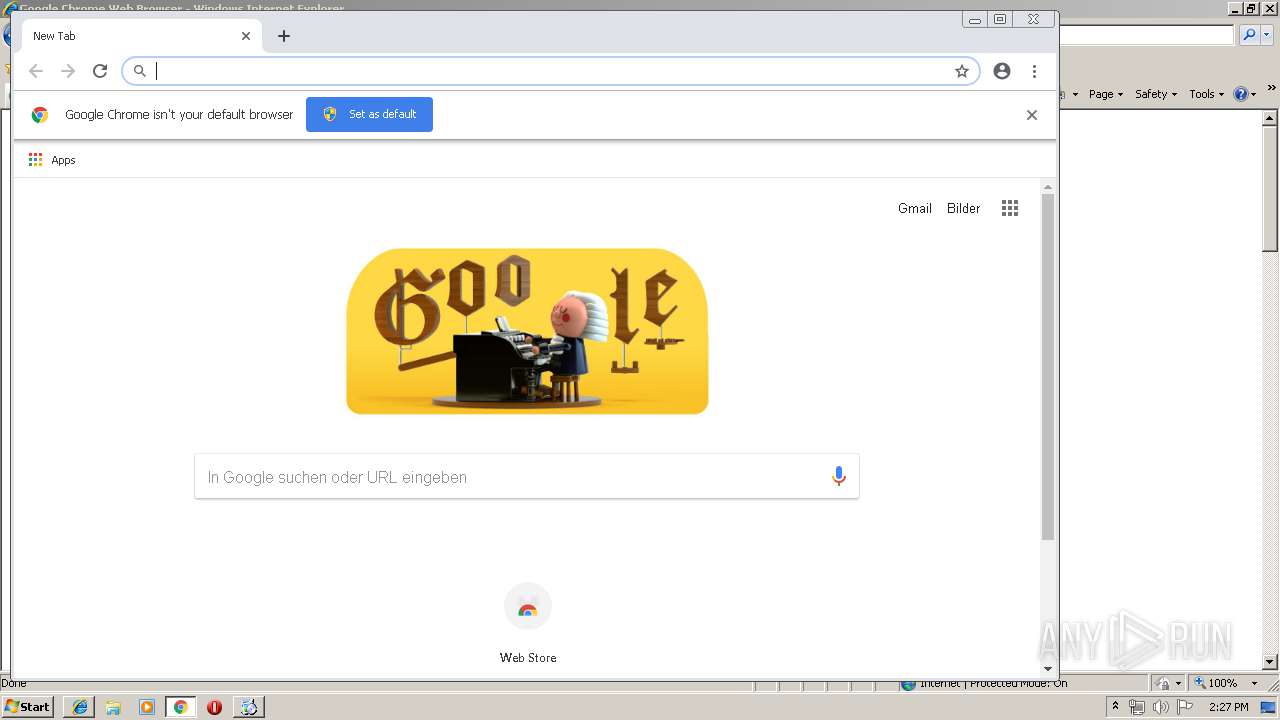
| 1332 | "C:\Program Files\Google\Chrome\Application\chrome.exe" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1376 | "C:\Users\admin\AppData\Local\Temp\{344267BA-41C6-4B6F-B07A-E951EFD1AF8B}\GoogleUpdate.exe" /install "appguid={8A69D345-D564-463C-AFF1-A69D9E530F96}&iid={2303C001-BE25-CEBA-2BE7-468B3168CB20}&lang=en&browser=2&usagestats=1&appname=Google%20Chrome&needsadmin=true&ap=stable-arch_x86-statsdef_1&installdataindex=defaultbrowser" /installsource oneclick | C:\Users\admin\AppData\Local\Temp\{344267BA-41C6-4B6F-B07A-E951EFD1AF8B}\GoogleUpdate.exe | — | GoogleUpdate.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Installer Exit code: 0 Version: 1.3.33.23 Modules
| |||||||||||||||
| 1552 | "C:\Program Files\Google\Update\GoogleUpdate.exe" /handoff "appguid={8A69D345-D564-463C-AFF1-A69D9E530F96}&iid={2303C001-BE25-CEBA-2BE7-468B3168CB20}&lang=en&browser=2&usagestats=1&appname=Google%20Chrome&needsadmin=true&ap=stable-arch_x86-statsdef_1&installdataindex=defaultbrowser" /installsource oneclick /sessionid "{7292EACF-4621-4696-B5EB-C7C0507FB99B}" | C:\Program Files\Google\Update\GoogleUpdate.exe | GoogleUpdate.exe | ||||||||||||
User: admin Company: Google Inc. Integrity Level: HIGH Description: Google Installer Exit code: 0 Version: 1.3.33.23 Modules
| |||||||||||||||
| 1624 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=968,1628737454637458858,316635844183184766,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=2260458184508256433 --mojo-platform-channel-handle=2740 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1660 | "C:\Program Files\Google\Update\1.3.33.23\GoogleUpdateWebPlugin.exe" "https:%2F%2Fwww.google.com%2F" "%2Finstall%20%22appguid=%7B8A69D345-D564-463C-AFF1-A69D9E530F96%7D%26iid=%7B2303C001-BE25-CEBA-2BE7-468B3168CB20%7D%26lang=en%26browser=2%26usagestats=1%26appname=Google%2520Chrome%26needsadmin=true%26ap=stable-arch_x86-statsdef_1%26installdataindex=defaultbrowser%22" /installsource oneclick | C:\Program Files\Google\Update\1.3.33.23\GoogleUpdateWebPlugin.exe | — | iexplore.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Update Exit code: 0 Version: 1.3.33.23 Modules
| |||||||||||||||
| 2056 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=968,1628737454637458858,316635844183184766,131072 --enable-features=PasswordImport --service-pipe-token=2982812357097176361 --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=2982812357097176361 --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2288 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2076 | "C:\Program Files\Internet Explorer\iexplore.exe" | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
2 336
Read events
1 696
Write events
624
Delete events
16
Modification events
| (PID) Process: | (128) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (128) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (128) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (128) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Zones |
| Operation: | write | Name: | SecuritySafe |
Value: 1 | |||
| (PID) Process: | (128) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (128) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 460000006E000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (128) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Recovery\Active |
| Operation: | write | Name: | {60C15DF3-4BE5-11E9-A302-5254004A04AF} |
Value: 0 | |||
| (PID) Process: | (128) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Type |
Value: 4 | |||
| (PID) Process: | (128) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Count |
Value: 1 | |||
| (PID) Process: | (128) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Time |
Value: E3070300040015000E001A003800D903 | |||
Executable files
142
Suspicious files
54
Text files
115
Unknown types
14
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 128 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\H6QNMHE9\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 128 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 2716 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Cab9F73.tmp | — | |
MD5:— | SHA256:— | |||
| 2716 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Cab9F74.tmp | — | |
MD5:— | SHA256:— | |||
| 2716 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Tar9F75.tmp | — | |
MD5:— | SHA256:— | |||
| 2716 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Tar9F76.tmp | — | |
MD5:— | SHA256:— | |||
| 2716 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Cab9F87.tmp | — | |
MD5:— | SHA256:— | |||
| 2716 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Tar9F88.tmp | — | |
MD5:— | SHA256:— | |||
| 2716 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Cab9F98.tmp | — | |
MD5:— | SHA256:— | |||
| 2716 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Tar9F99.tmp | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
15
TCP/UDP connections
104
DNS requests
51
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
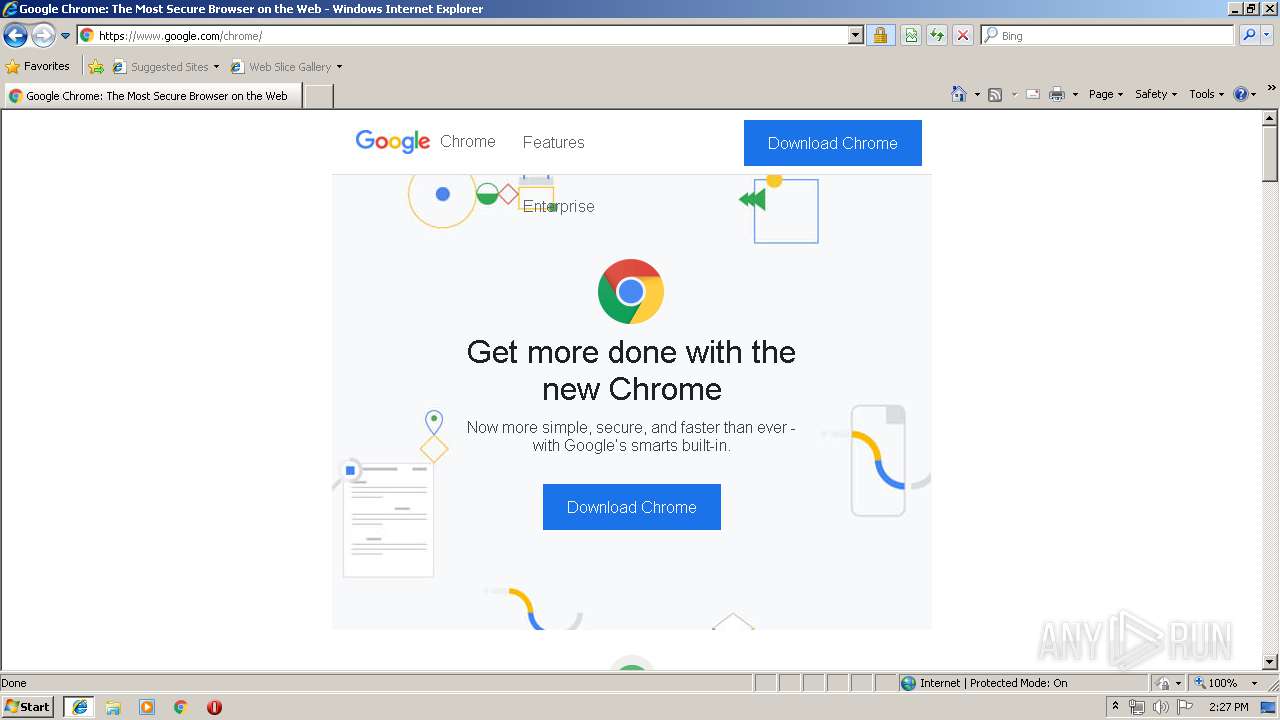
— | — | HEAD | 200 | 173.194.160.71:80 | http://r2---sn-1gi7znes.gvt1.com/edgedl/release2/chrome/GGX-dnQvK4Q_73.0.3683.86/73.0.3683.86_chrome_installer.exe?mip=136.0.0.150&pl=20&shardbypass=yes&redirect_counter=1&cm2rm=sn-oun-1gie7l&req_id=ac497e3aa6cf5cea&cms_redirect=yes&mm=42&mn=sn-1gi7znes&ms=onc&mt=1553177791&mv=u | US | — | — | whitelisted |
— | — | HEAD | 302 | 216.58.207.78:80 | http://redirector.gvt1.com/edgedl/release2/chrome/GGX-dnQvK4Q_73.0.3683.86/73.0.3683.86_chrome_installer.exe | US | — | — | whitelisted |
— | — | HEAD | 302 | 217.146.165.205:80 | http://r2---sn-oun-1gie.gvt1.com/edgedl/release2/chrome/GGX-dnQvK4Q_73.0.3683.86/73.0.3683.86_chrome_installer.exe?cms_redirect=yes&mip=136.0.0.150&mm=28&mn=sn-oun-1gie&ms=nvh&mt=1553177509&mv=u&pl=20&shardbypass=yes | CH | — | — | whitelisted |
— | — | GET | — | 173.194.160.71:80 | http://r2---sn-1gi7znes.gvt1.com/edgedl/release2/chrome/GGX-dnQvK4Q_73.0.3683.86/73.0.3683.86_chrome_installer.exe?mip=136.0.0.150&pl=20&shardbypass=yes&redirect_counter=1&cm2rm=sn-oun-1gie7l&req_id=ac497e3aa6cf5cea&cms_redirect=yes&mm=42&mn=sn-1gi7znes&ms=onc&mt=1553177791&mv=u | US | — | — | whitelisted |
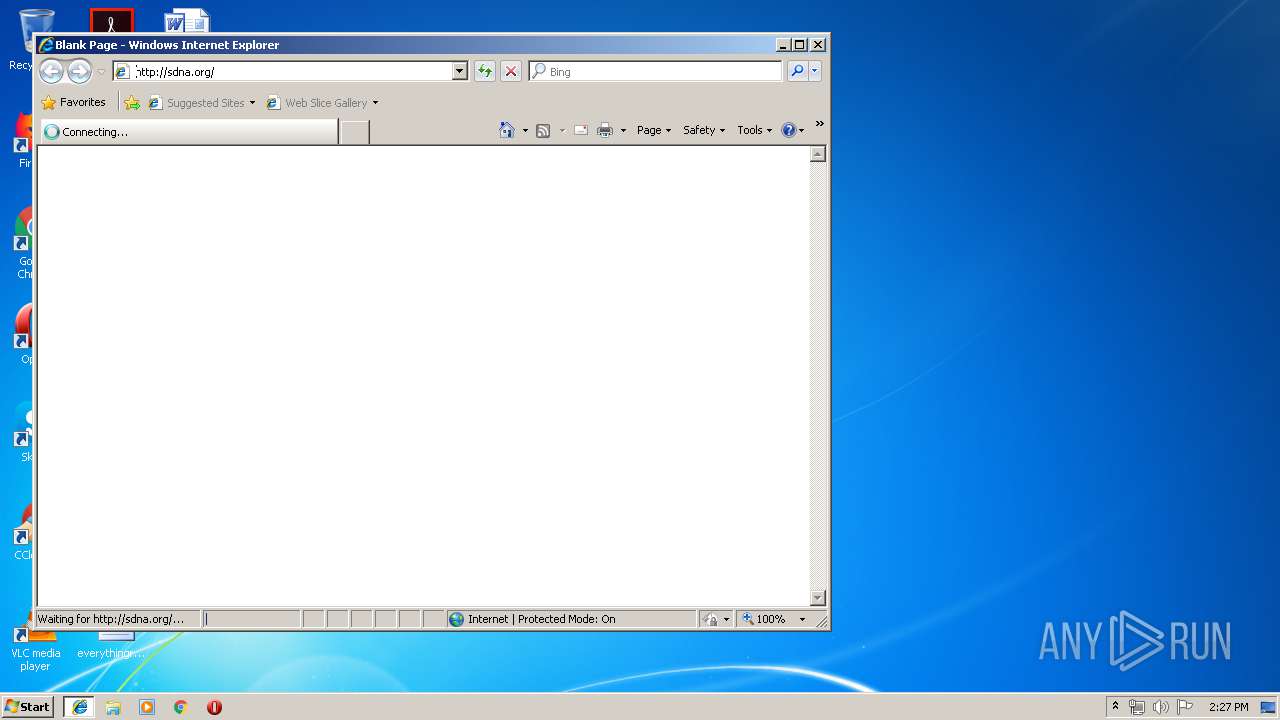
2396 | iexplore.exe | GET | 302 | 54.208.77.124:80 | http://sdna.org/ | US | html | 194 b | malicious |
2160 | chrome.exe | GET | 302 | 216.58.207.78:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvMjJlQUFXRC12Ny1ldUFnMXF3SDlXZDlFZw/7319.128.0.1_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 502 b | whitelisted |
2716 | iexplore.exe | GET | 200 | 205.185.216.10:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 55.2 Kb | whitelisted |
2716 | iexplore.exe | GET | 200 | 205.185.216.10:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 55.2 Kb | whitelisted |
2160 | chrome.exe | GET | 200 | 217.146.165.205:80 | http://r2---sn-oun-1gie.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvMjJlQUFXRC12Ny1ldUFnMXF3SDlXZDlFZw/7319.128.0.1_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mip=136.0.0.150&mm=28&mn=sn-oun-1gie&ms=nvh&mt=1553177509&mv=u&pl=20&shardbypass=yes | CH | crx | 842 Kb | whitelisted |
2160 | chrome.exe | GET | 302 | 35.169.58.188:80 | http://sdna.org/ | US | html | 194 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 104.109.68.8:445 | img1.wsimg.com | Akamai International B.V. | NL | whitelisted |
— | — | 104.109.68.8:137 | img1.wsimg.com | Akamai International B.V. | NL | whitelisted |
2716 | iexplore.exe | 104.109.68.8:443 | img1.wsimg.com | Akamai International B.V. | NL | whitelisted |
2716 | iexplore.exe | 205.185.216.10:80 | www.download.windowsupdate.com | Highwinds Network Group, Inc. | US | whitelisted |
128 | iexplore.exe | 13.107.21.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
2396 | iexplore.exe | 54.208.77.124:80 | sdna.org | Amazon.com, Inc. | US | malicious |
2076 | iexplore.exe | 13.107.21.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
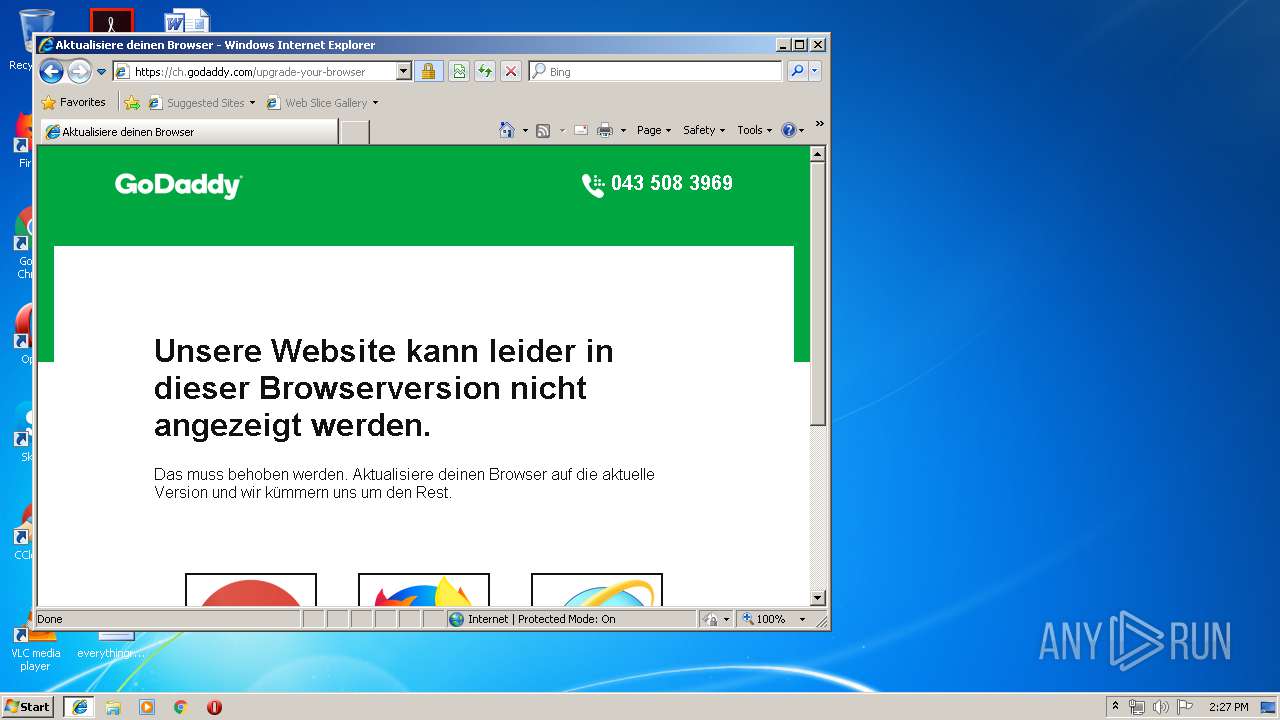
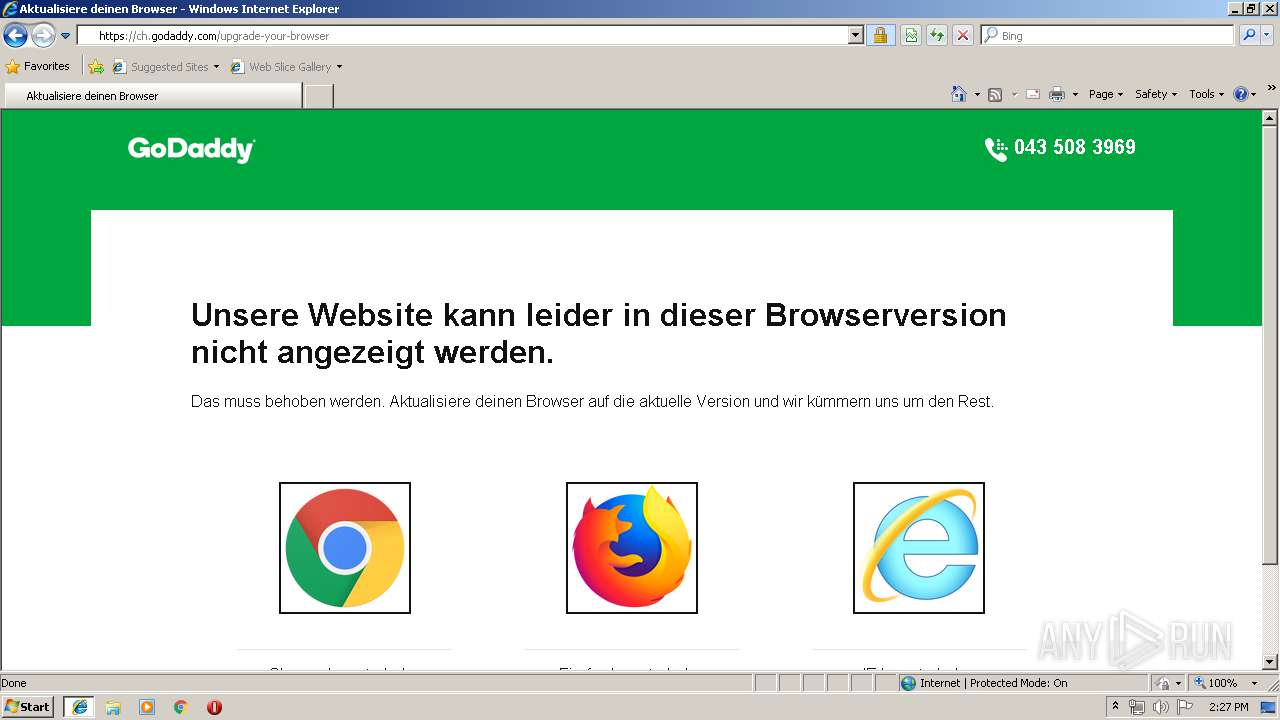
2396 | iexplore.exe | 184.31.82.100:443 | www.afternic.com | Akamai International B.V. | NL | whitelisted |
2396 | iexplore.exe | 184.30.217.247:443 | www.godaddy.com | Akamai International B.V. | NL | whitelisted |
2396 | iexplore.exe | 104.109.68.8:443 | img1.wsimg.com | Akamai International B.V. | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
img1.wsimg.com |
| whitelisted |
www.bing.com |
| whitelisted |
www.download.windowsupdate.com |
| whitelisted |
sdna.org |
| malicious |
www.afternic.com |
| whitelisted |
www.godaddy.com |
| whitelisted |
ch.godaddy.com |
| unknown |
www.google.com |
| malicious |
www.gstatic.com |
| whitelisted |
ssl.google-analytics.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |