| File name: | 5da1c60670a91a14b156c53e5578a2be80febec7ee6e7755b16121fc83413c5c.exe |
| Full analysis: | https://app.any.run/tasks/3252a732-ffbc-4e3c-a106-4863a109b8ab |
| Verdict: | Malicious activity |
| Analysis date: | February 21, 2026, 09:58:10 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, UPX compressed, 3 sections |
| MD5: | C86CA4692E3409A9DA1A0A1BA0685A72 |
| SHA1: | 4F98B602C480FC12A3846ADFBF3FF9F82D091A70 |
| SHA256: | 5DA1C60670A91A14B156C53E5578A2BE80FEBEC7EE6E7755B16121FC83413C5C |
| SSDEEP: | 98304:0B465c9t84spPMWbuhxokY+M132uqu7t1YWqr53BVcha9fB1jrbUrwZrKtpNCn85:+4DWRcwADyVBUp2pSY |
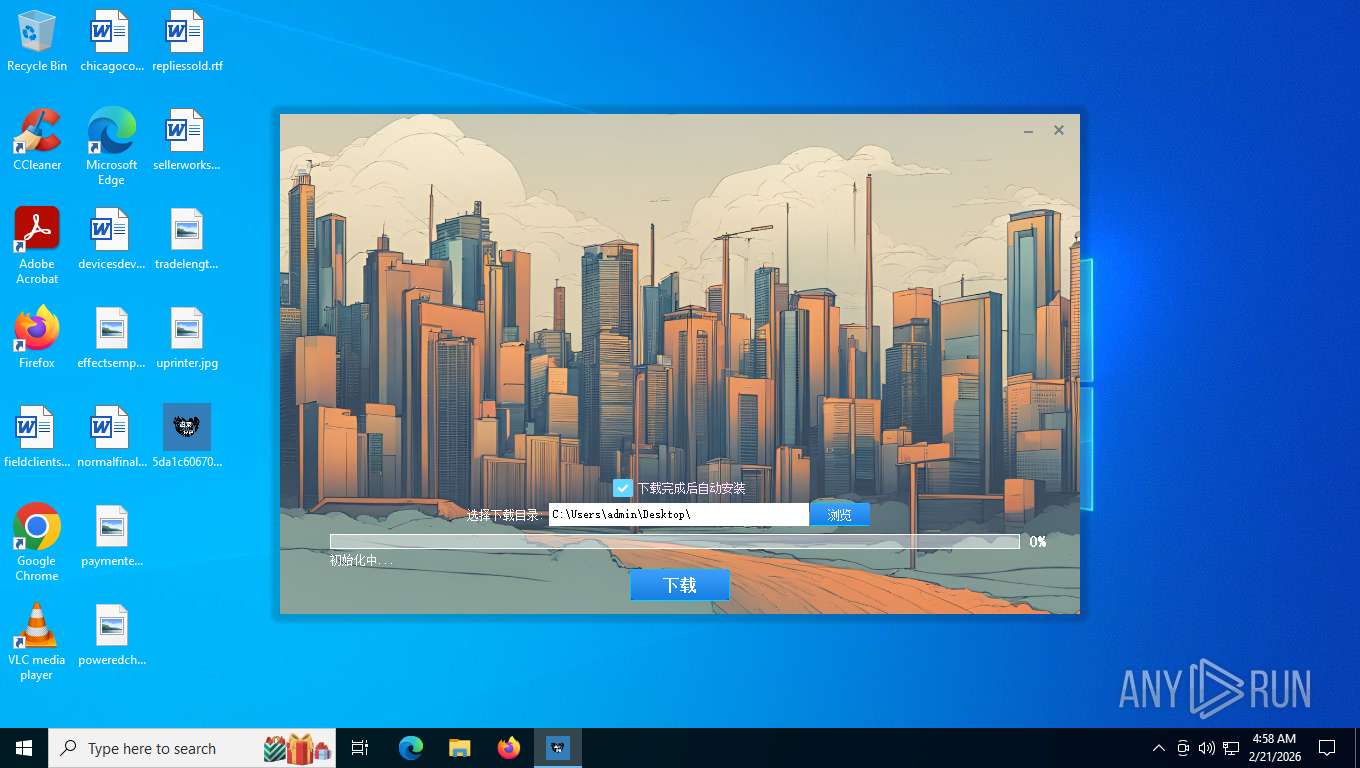
MALICIOUS
Executing a file with an untrusted certificate
- 5da1c60670a91a14b156c53e5578a2be80febec7ee6e7755b16121fc83413c5c.exe (PID: 1848)
SUSPICIOUS
Contacting a server suspected of hosting an CnC
- svchost.exe (PID: 2292)
INFO
Checks supported languages
- 5da1c60670a91a14b156c53e5578a2be80febec7ee6e7755b16121fc83413c5c.exe (PID: 1848)
The sample compiled with chinese language support
- 5da1c60670a91a14b156c53e5578a2be80febec7ee6e7755b16121fc83413c5c.exe (PID: 1848)
Reads the computer name
- 5da1c60670a91a14b156c53e5578a2be80febec7ee6e7755b16121fc83413c5c.exe (PID: 1848)
UPX packer has been detected
- 5da1c60670a91a14b156c53e5578a2be80febec7ee6e7755b16121fc83413c5c.exe (PID: 1848)
Checks proxy server information
- slui.exe (PID: 4700)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | UPX compressed Win32 Executable (76) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (12.6) |
| .exe | | | Generic Win/DOS Executable (5.6) |
| .exe | | | DOS Executable Generic (5.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2025:10:17 13:54:38+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 14.16 |
| CodeSize: | 9351168 |
| InitializedDataSize: | 73728 |
| UninitializedDataSize: | 1794048 |
| EntryPoint: | 0xaa1960 |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.1 |
| ProductVersionNumber: | 1.0.0.1 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Chinese (Simplified) |
| CharacterSet: | Unicode |
| CompanyName: | ToDayPor |
| FileDescription: | 专业版Ver0.1.9 (250893) |
| FileVersion: | 1.0.0.1 |
| InternalName: | C_ToDown.exe |
| LegalCopyright: | Copyright (C) 2025 |
| OriginalFileName: | C_ToDown.exe |
| ProductName: | ToDayPor |
| ProductVersion: | 1.0.0.1 |
Total processes
139
Monitored processes
3
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1848 | "C:\Users\admin\Desktop\5da1c60670a91a14b156c53e5578a2be80febec7ee6e7755b16121fc83413c5c.exe" | C:\Users\admin\Desktop\5da1c60670a91a14b156c53e5578a2be80febec7ee6e7755b16121fc83413c5c.exe | explorer.exe | ||||||||||||
User: admin Company: ToDayPor Integrity Level: MEDIUM Description: 专业版Ver0.1.9 (250893) Version: 1.0.0.1 Modules
| |||||||||||||||
| 2292 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4700 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
4 391
Read events
4 391
Write events
0
Delete events
0
Modification events
Executable files
0
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
17
TCP/UDP connections
26
DNS requests
14
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
7544 | svchost.exe | GET | 200 | 2.16.164.49:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | NL | binary | 825 b | whitelisted |
— | — | GET | 200 | 2.16.164.49:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | NL | binary | 825 b | whitelisted |
6768 | MoUsoCoreWorker.exe | GET | 200 | 2.16.164.49:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | NL | binary | 825 b | whitelisted |
7544 | svchost.exe | GET | 200 | 23.52.181.212:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | US | binary | 814 b | whitelisted |
— | — | GET | 200 | 23.52.181.212:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | US | binary | 814 b | whitelisted |
6768 | MoUsoCoreWorker.exe | GET | 200 | 23.52.181.212:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | US | binary | 814 b | whitelisted |
4404 | slui.exe | POST | 500 | 48.192.1.64:443 | https://activation-v2.sls.microsoft.com/SLActivateProduct/SLActivateProduct.asmx?configextension=Retail | US | text | 512 b | whitelisted |
1848 | 5da1c60670a91a14b156c53e5578a2be80febec7ee6e7755b16121fc83413c5c.exe | POST | 200 | 211.93.211.158:80 | http://aria2c.vip/vc/SelectListOne.php | CN | text | 2.92 Kb | malicious |
— | — | POST | 500 | 48.192.1.64:443 | https://activation-v2.sls.microsoft.com/SLActivateProduct/SLActivateProduct.asmx?configextension=Retail | US | text | 512 b | whitelisted |
3292 | svchost.exe | GET | 200 | 23.52.181.212:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Signing%20CA%202.2.crl | US | binary | 401 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:137 | — | Not routed | — | whitelisted |
— | — | 92.123.104.19:443 | www.bing.com | AKAMAI-ASN1 | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | Not routed | — | whitelisted |
— | — | 2.16.164.49:80 | crl.microsoft.com | AKAMAI-ASN1 | NL | whitelisted |
7544 | svchost.exe | 2.16.164.49:80 | crl.microsoft.com | AKAMAI-ASN1 | NL | whitelisted |
6768 | MoUsoCoreWorker.exe | 2.16.164.49:80 | crl.microsoft.com | AKAMAI-ASN1 | NL | whitelisted |
— | — | 23.52.181.212:80 | www.microsoft.com | AKAMAI-AS | US | whitelisted |
7544 | svchost.exe | 23.52.181.212:80 | www.microsoft.com | AKAMAI-AS | US | whitelisted |
6768 | MoUsoCoreWorker.exe | 23.52.181.212:80 | www.microsoft.com | AKAMAI-AS | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
self.events.data.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
aria2c.vip |
| malicious |
activation-v2.sls.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2292 | svchost.exe | Domain Observed Used for C2 Detected | MALWARE [ANY.RUN] Win32/Nymaim related domain (aria2c .vip) |
1848 | 5da1c60670a91a14b156c53e5578a2be80febec7ee6e7755b16121fc83413c5c.exe | A Network Trojan was detected | MALWARE [ANY.RUN] Win32/Nymaim activity observed |