| File name: | doc.hwp |
| Full analysis: | https://app.any.run/tasks/b4381901-3a3b-4055-8304-f0870a8d3c7c |
| Verdict: | No threats detected |
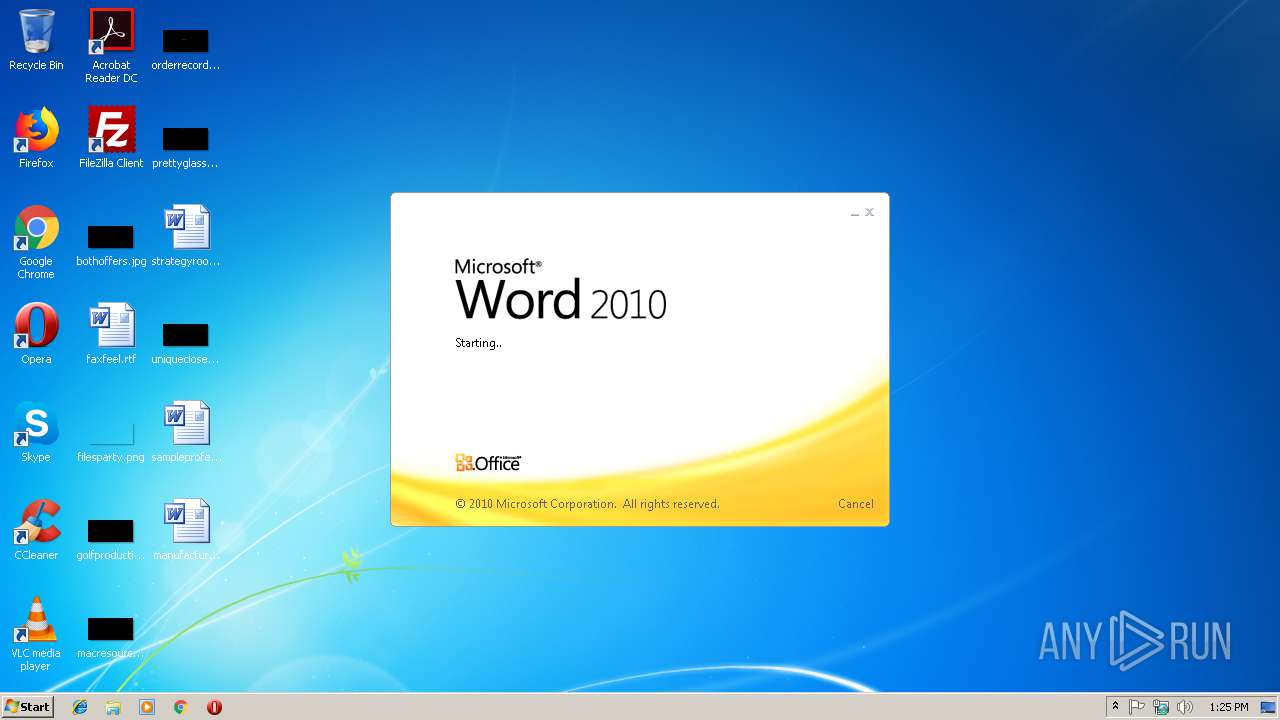
| Analysis date: | March 01, 2019, 13:25:22 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
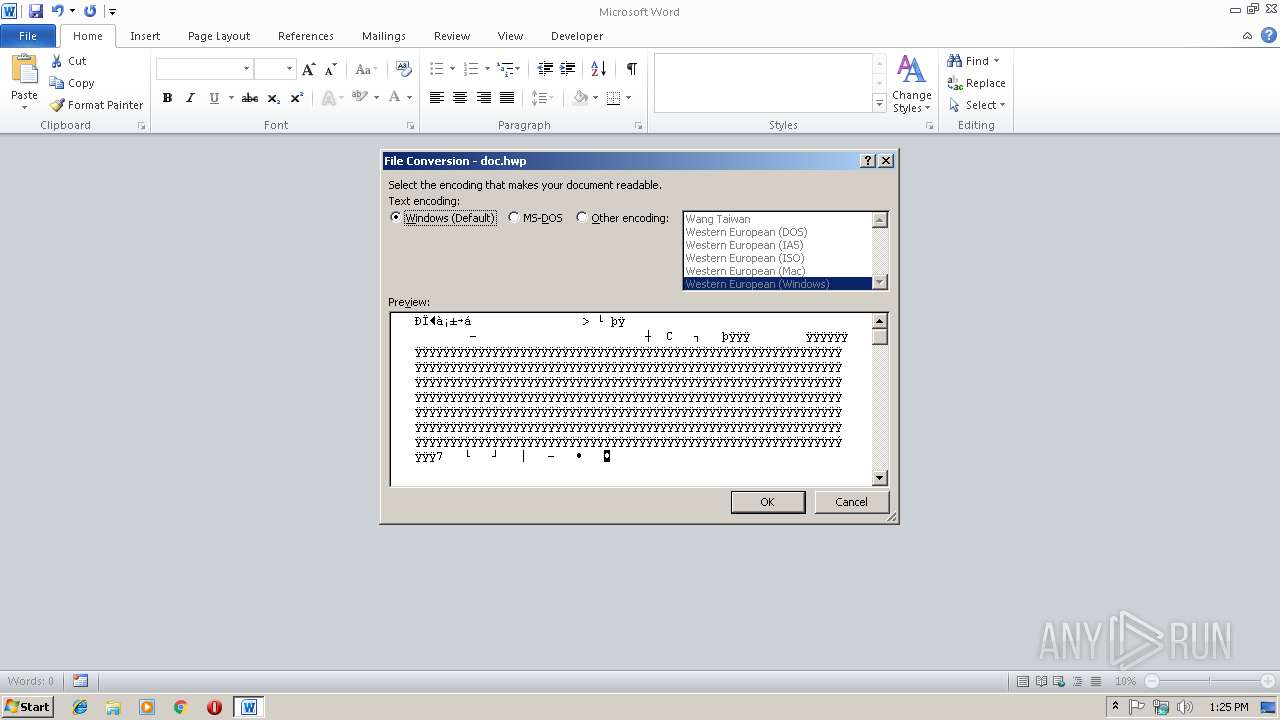
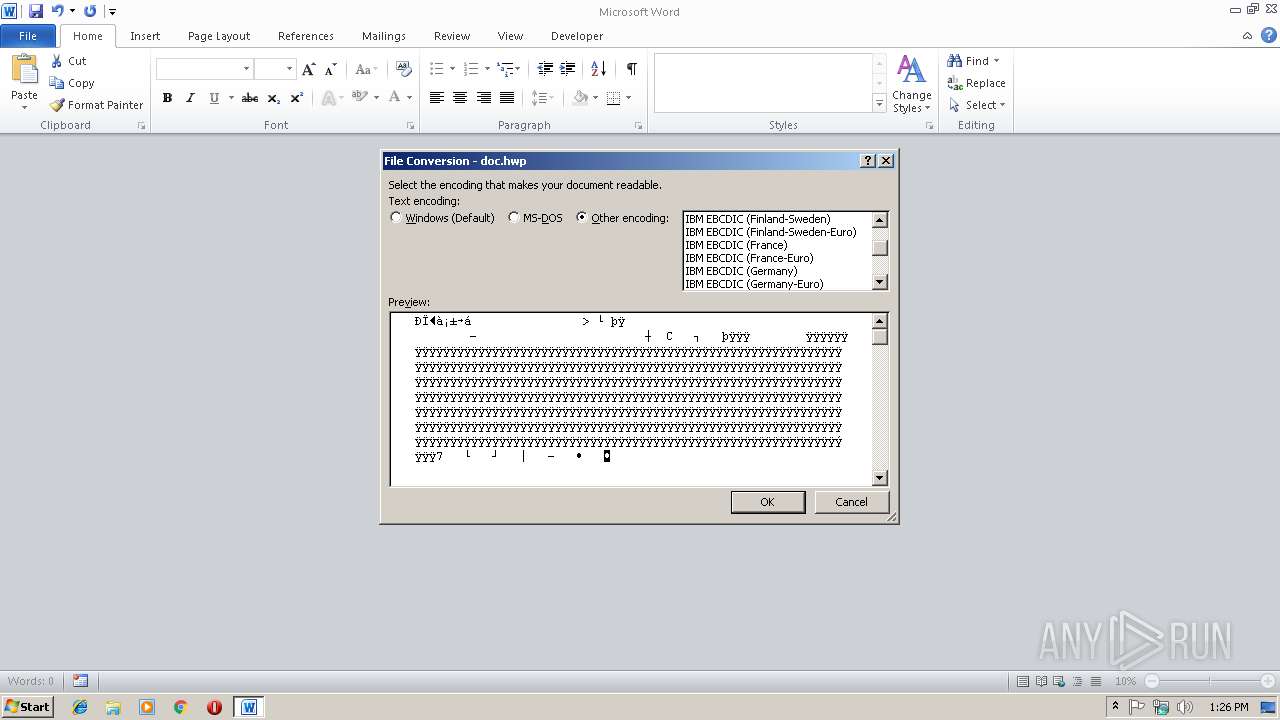
| MIME: | application/x-hwp |
| File info: | Hangul (Korean) Word Processor File 5.x |
| MD5: | F2E936FF1977D123809D167A2A51CDEB |
| SHA1: | 7A86E6BFFBA91997553AC4CF0BAEC407BC255212 |
| SHA256: | 5D9E5C7B1B71AF3C5F058F8521D383DBEE88C99EBE8D509EBC8AEB52D4B6267B |
| SSDEEP: | 768:95AUVOrYGRGcIzwzBsqjjvIPm9ovo5WWAXkWTYcAxerar0MwnhRfTEwkU8y2i:9x4rYlnzMsqjjvIjogRk7cAonZX8y |
MALICIOUS
No malicious indicators.SUSPICIOUS
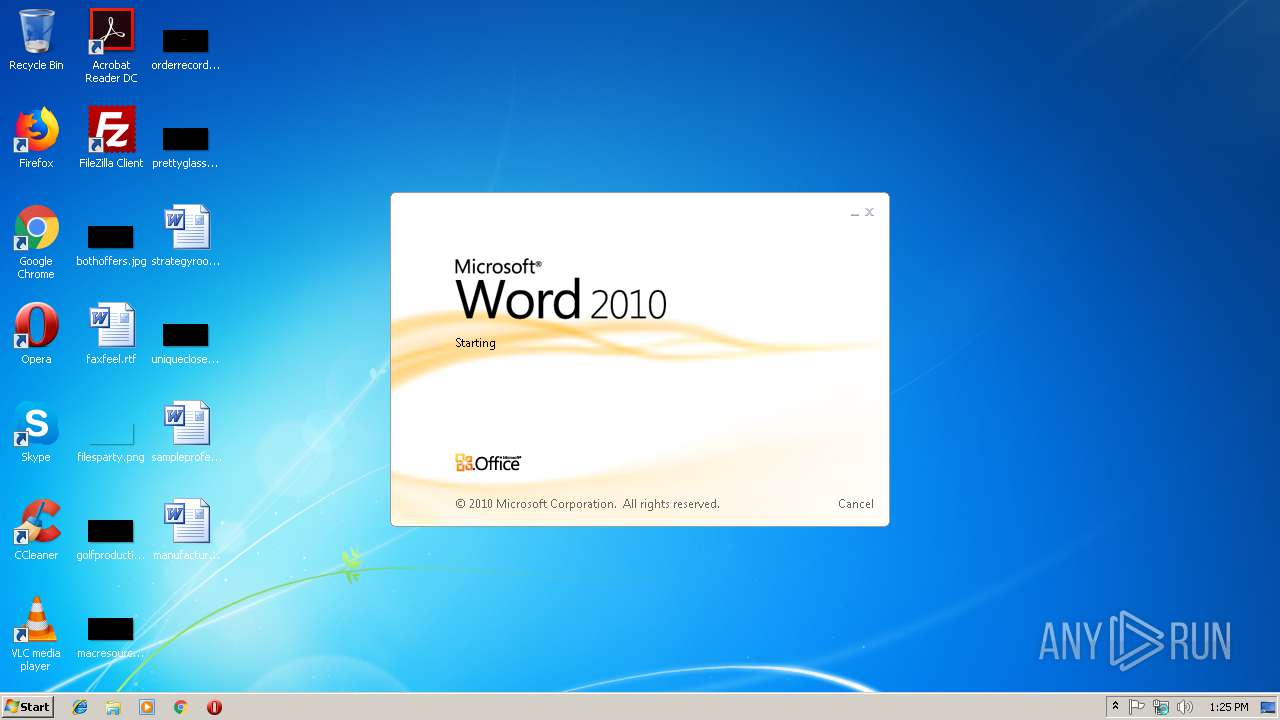
Starts Microsoft Office Application
- rundll32.exe (PID: 3512)
INFO
Creates files in the user directory
- WINWORD.EXE (PID: 3572)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 3572)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .hwp | | | Hangul (Korean) Word Processor document (alternate) (67.3) |
|---|
Total processes
32
Monitored processes
2
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
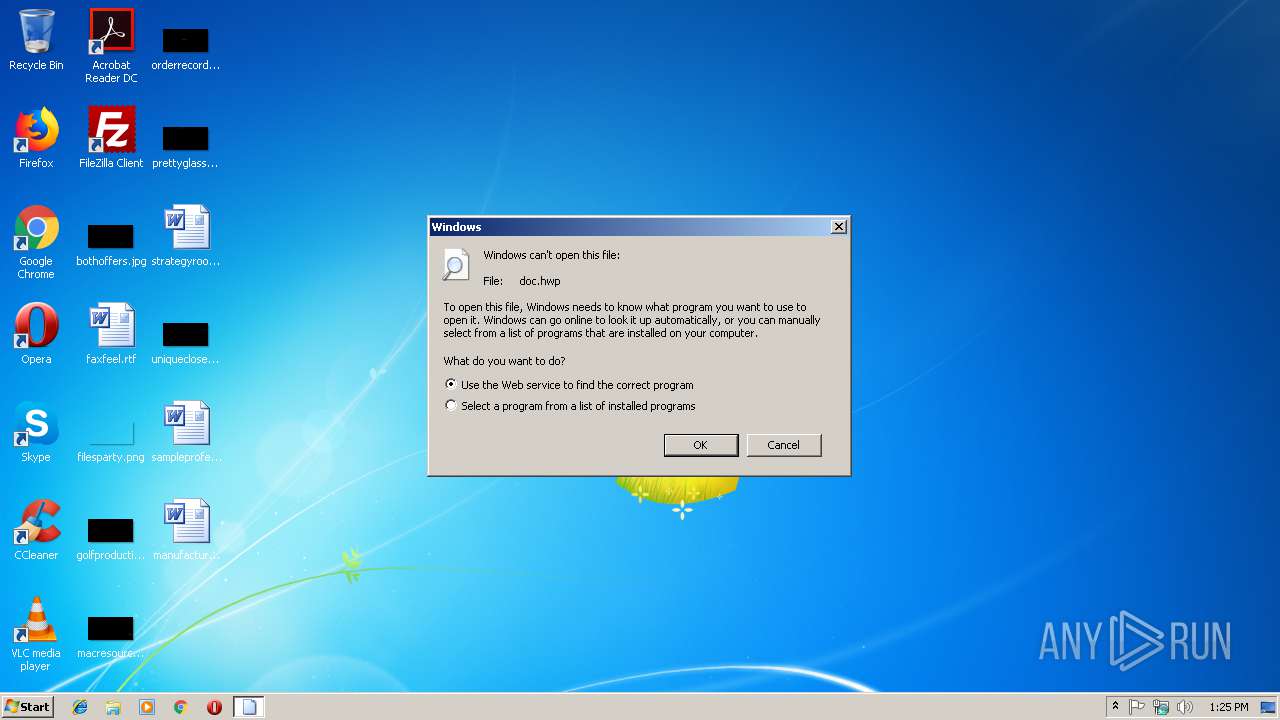
| 3512 | "C:\Windows\system32\rundll32.exe" C:\Windows\system32\shell32.dll,OpenAs_RunDLL C:\Users\admin\AppData\Local\Temp\doc.hwp | C:\Windows\system32\rundll32.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3572 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\doc.hwp" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | rundll32.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
Total events
1 421
Read events
1 293
Write events
119
Delete events
9
Modification events
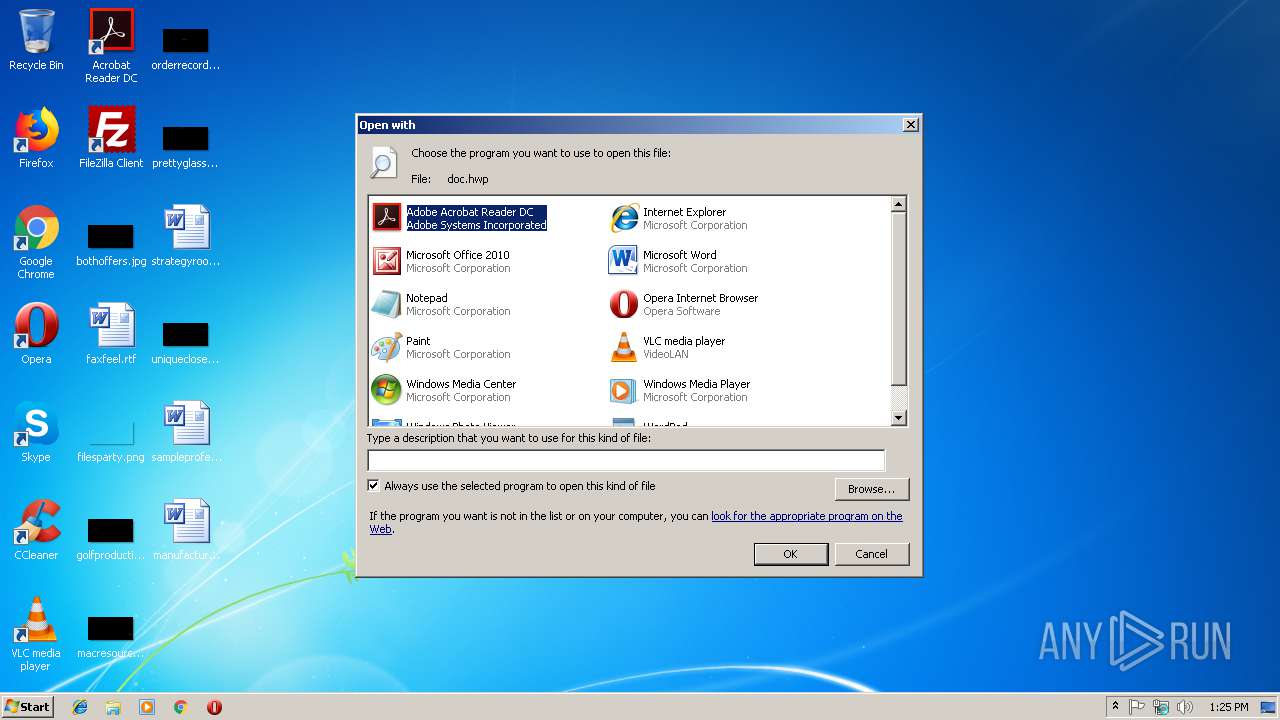
| (PID) Process: | (3512) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroRd32.exe |
Value: Adobe Acrobat Reader DC | |||
| (PID) Process: | (3512) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\Windows\eHome\ehshell.exe |
Value: Windows Media Center | |||
| (PID) Process: | (3512) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\Windows\system32\mspaint.exe |
Value: Paint | |||
| (PID) Process: | (3512) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\Windows\system32\NOTEPAD.EXE |
Value: Notepad | |||
| (PID) Process: | (3512) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\PROGRA~1\MICROS~1\Office14\OIS.EXE |
Value: Microsoft Office 2010 | |||
| (PID) Process: | (3512) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\Program Files\Opera\Opera.exe |
Value: Opera Internet Browser | |||
| (PID) Process: | (3512) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\Program Files\Windows Photo Viewer\PhotoViewer.dll |
Value: Windows Photo Viewer | |||
| (PID) Process: | (3512) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\Program Files\VideoLAN\VLC\vlc.exe |
Value: VLC media player | |||
| (PID) Process: | (3512) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE |
Value: Microsoft Word | |||
| (PID) Process: | (3512) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\5F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
Executable files
0
Suspicious files
0
Text files
0
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3572 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVRF8D.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3572 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DF9D8699E2B7140FBD.TMP | — | |
MD5:— | SHA256:— | |||
| 3572 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DFC951D2D998FD81F6.TMP | — | |
MD5:— | SHA256:— | |||
| 3572 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DF043106BB5138C9F0.TMP | — | |
MD5:— | SHA256:— | |||
| 3572 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRD0001.doc | — | |
MD5:— | SHA256:— | |||
| 3572 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRD0000.doc | — | |
MD5:— | SHA256:— | |||
| 3572 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRD0002.doc | — | |
MD5:— | SHA256:— | |||
| 3572 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRS{05CEDACD-D26D-4CA8-81F7-0AAE10BD1FE9}.tmp | — | |
MD5:— | SHA256:— | |||
| 3572 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRS{A653E7D8-A82F-4EE4-8E3C-0C81276CC02D}.tmp | — | |
MD5:— | SHA256:— | |||
| 3572 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~$doc.hwp | pgc | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report