| File name: | Leitostrap.exe |
| Full analysis: | https://app.any.run/tasks/8bcf1b85-4058-4d4a-b259-16512e978973 |
| Verdict: | Malicious activity |
| Analysis date: | April 03, 2026, 03:10:46 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32+ executable (GUI) x86-64 (stripped to external PDB), for MS Windows, 12 sections |
| MD5: | 4F885F21B362BEEAFF735EDCA1100384 |
| SHA1: | D9D6A71A2C1438AB4AC4EB1216714FE8DF3C67B0 |
| SHA256: | 5D9CBFEE81C0A894358F16D8C9D135F6AAA357B5115FA1A92B2D63CBBA9CFD02 |
| SSDEEP: | 196608:TDoA2oDGEgyn6UhlUAIE1CPwDvt3uFlDCH7zLQDESG7rAdYJTy:BDGk6UhGAZ1CPwDvt3uFhCH7zLQDB |
MALICIOUS
No malicious indicators.SUSPICIOUS
Process drops python dynamic module
- Leitostrap.exe (PID: 7684)
The process drops C-runtime libraries
- Leitostrap.exe (PID: 7684)
Executable content was dropped or overwritten
- Leitostrap.exe (PID: 7684)
NUITKA compiler has been detected
- Leitostrap.exe (PID: 7684)
Application launched itself
- Leitostrap.exe (PID: 7684)
Loads Python modules
- Leitostrap.exe (PID: 5800)
Reads Microsoft Outlook installation path
- Leitostrap.exe (PID: 5800)
Reads Internet Explorer settings
- Leitostrap.exe (PID: 5800)
INFO
Checks supported languages
- Leitostrap.exe (PID: 7684)
- Leitostrap.exe (PID: 5800)
The sample compiled with english language support
- Leitostrap.exe (PID: 7684)
Create files in a temporary directory
- Leitostrap.exe (PID: 7684)
Reads the computer name
- Leitostrap.exe (PID: 5800)
Reads security settings of Internet Explorer
- Leitostrap.exe (PID: 5800)
Reads the machine GUID from the registry
- Leitostrap.exe (PID: 5800)
There is functionality for taking screenshot (YARA)
- Leitostrap.exe (PID: 5800)
PyInstaller has been detected (YARA)
- Leitostrap.exe (PID: 5800)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (76.4) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (12.4) |
| .exe | | | Generic Win/DOS Executable (5.5) |
| .exe | | | DOS Executable Generic (5.5) |
EXIF
EXE
| MachineType: | AMD AMD64 |
|---|---|
| TimeStamp: | 2026:03:30 15:31:47+00:00 |
| ImageFileCharacteristics: | Executable, No line numbers, No symbols, Large address aware, No debug |
| PEType: | PE32+ |
| LinkerVersion: | 2.43 |
| CodeSize: | 56320 |
| InitializedDataSize: | 48910848 |
| UninitializedDataSize: | 163328 |
| EntryPoint: | 0x10f6 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 5.2 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.6.0.0 |
| ProductVersionNumber: | 1.6.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
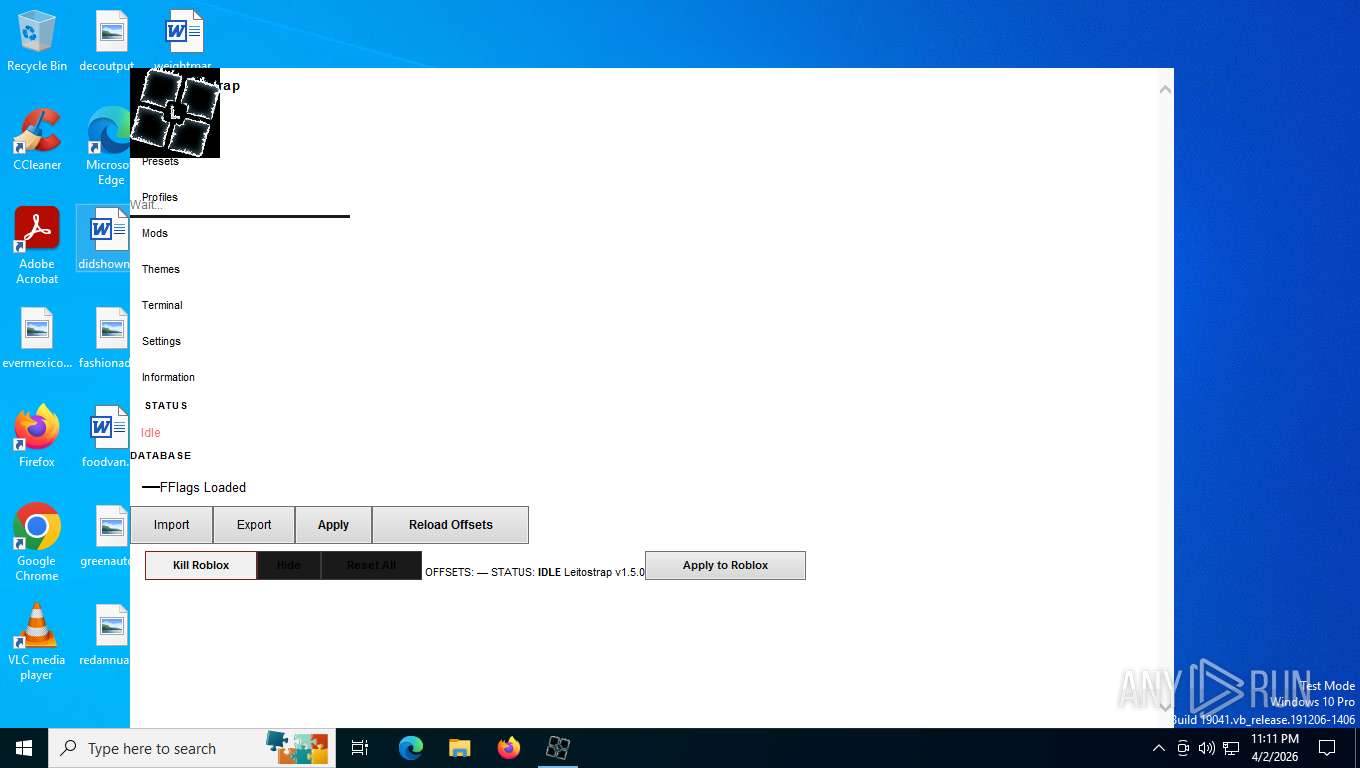
| CompanyName: | Leitostrap |
| ProductName: | Leitostrap |
| FileDescription: | Leitostrap FFlag Injector |
| ProductVersion: | 1.6.0.0 |
| FileVersion: | 1.6.0.0 |
| OriginalFileName: | Leitostrap.exe |
| InternalName: | Leitostrap |
Total processes
129
Monitored processes
3
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2692 | "C:\Users\admin\Desktop\Leitostrap.exe" | C:\Users\admin\Desktop\Leitostrap.exe | — | explorer.exe | |||||||||||
User: admin Company: Leitostrap Integrity Level: MEDIUM Description: Leitostrap FFlag Injector Exit code: 3221226540 Version: 1.6.0.0 Modules
| |||||||||||||||
| 5800 | C:\Users\admin\Desktop\Leitostrap.exe | C:\Users\admin\Desktop\Leitostrap.exe | — | Leitostrap.exe | |||||||||||
User: admin Company: Leitostrap Integrity Level: HIGH Description: Leitostrap FFlag Injector Version: 1.6.0.0 Modules
| |||||||||||||||
| 7684 | "C:\Users\admin\Desktop\Leitostrap.exe" | C:\Users\admin\Desktop\Leitostrap.exe | explorer.exe | ||||||||||||
User: admin Company: Leitostrap Integrity Level: HIGH Description: Leitostrap FFlag Injector Version: 1.6.0.0 Modules
| |||||||||||||||
Total events
1 188
Read events
1 182
Write events
6
Delete events
0
Modification events
| (PID) Process: | (5800) Leitostrap.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\Main\FeatureControl\FEATURE_96DPI_PIXEL |
| Operation: | write | Name: | python.exe |
Value: 1 | |||
| (PID) Process: | (5800) Leitostrap.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (5800) Leitostrap.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (5800) Leitostrap.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (5800) Leitostrap.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\DirectDraw\MostRecentApplication |
| Operation: | write | Name: | Name |
Value: Leitostrap.exe | |||
| (PID) Process: | (5800) Leitostrap.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\DirectDraw\MostRecentApplication |
| Operation: | write | Name: | ID |
Value: | |||
Executable files
37
Suspicious files
3
Text files
931
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7684 | Leitostrap.exe | C:\Users\admin\AppData\Local\Temp\onefile_7684_134196594671871356\Leitostrap.dll | executable | |
MD5:F5E23310A8383F31A3AA14B6AACE4BF7 | SHA256:BCF8685B5B4C4CF9A1B0A16C3E39281B328B4CE22BE9E0AF888B8374419DCEC2 | |||
| 7684 | Leitostrap.exe | C:\Users\admin\AppData\Local\Temp\onefile_7684_134196594671871356\_multiprocessing.pyd | executable | |
MD5:32150BED522E6C151FEF8027AD4691E0 | SHA256:75CB11E3884F408016177B17D1717B066DDF71A59FD07836808703EDF5683B62 | |||
| 7684 | Leitostrap.exe | C:\Users\admin\AppData\Local\Temp\onefile_7684_134196594671871356\_asyncio.pyd | executable | |
MD5:A577FF6DE2ADD83120127061D7C294A8 | SHA256:8A12F0E5EF034F5C9FF5C506F701A00E3CD16009E2D3431F54EAD15BC138629F | |||
| 7684 | Leitostrap.exe | C:\Users\admin\AppData\Local\Temp\onefile_7684_134196594671871356\_decimal.pyd | executable | |
MD5:5D54C76A09515D513AAB1DD43C401418 | SHA256:E8861C23B443F846CF25F06B6F49BA20CFDD0C383C890F9F60C7A0AC376AC22E | |||
| 7684 | Leitostrap.exe | C:\Users\admin\AppData\Local\Temp\onefile_7684_134196594671871356\_lzma.pyd | executable | |
MD5:9EC7F84B1976B469C4FA4001D5FF4412 | SHA256:14762C570A210D196F5FC8F89C792E093B0875695251D490CBD4BA79C8F64999 | |||
| 7684 | Leitostrap.exe | C:\Users\admin\AppData\Local\Temp\onefile_7684_134196594671871356\_queue.pyd | executable | |
MD5:2CE0E1816468940A4025EFB31CD75150 | SHA256:0746DAB0FEAB5AB709FDF888A9A15B050B0FAF6C934C61788249B32E344D38F7 | |||
| 7684 | Leitostrap.exe | C:\Users\admin\AppData\Local\Temp\onefile_7684_134196594671871356\_cffi_backend.pyd | executable | |
MD5:429D90ECF87F4D8DF562BAE6B6157718 | SHA256:53DE34AFC3939D81BF2498B77425C52E2C3F3164F8CFE2543D3ACC8F24134488 | |||
| 7684 | Leitostrap.exe | C:\Users\admin\AppData\Local\Temp\onefile_7684_134196594671871356\_ctypes.pyd | executable | |
MD5:FC2DA679024ED27F02ECD1B05CF14CDA | SHA256:AB0A527BEDFD18E11B2FACC003407B6E565F114E010499F73DE35E1B01B6D340 | |||
| 7684 | Leitostrap.exe | C:\Users\admin\AppData\Local\Temp\onefile_7684_134196594671871356\_hashlib.pyd | executable | |
MD5:D0A2127B7AA88B6A47C170C933402438 | SHA256:2598B1D5AF9606A85CF8BA00EB5E0EFB5C405BE3AD852D1B070D08E0EE34C526 | |||
| 7684 | Leitostrap.exe | C:\Users\admin\AppData\Local\Temp\onefile_7684_134196594671871356\libssl-3.dll | executable | |
MD5:4FF168AAA6A1D68E7957175C8513F3A2 | SHA256:2E4D35B681A172D3298CAF7DC670451BE7A8BA27C26446EFC67470742497A950 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
44
TCP/UDP connections
38
DNS requests
20
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6536 | SIHClient.exe | GET | 304 | 74.178.76.128:443 | https://slscr.update.microsoft.com/SLS/%7B522D76A4-93E1-47F8-B8CE-07C937AD1A1E%7D/x64/10.0.19045.4046/0?CH=686&L=en-US&P=&PT=0x30&WUA=10.0.19041.3996&MK=DELL&MD=DELL | US | — | — | whitelisted |
6536 | SIHClient.exe | GET | 200 | 74.178.76.54:443 | https://fe3cr.delivery.mp.microsoft.com/clientwebservice/ping | US | — | — | whitelisted |
5484 | svchost.exe | GET | 200 | 23.216.77.28:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | NL | binary | 825 b | whitelisted |
5276 | MoUsoCoreWorker.exe | GET | 200 | 23.52.181.212:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | US | binary | 814 b | whitelisted |
5484 | svchost.exe | GET | 200 | 23.52.181.212:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | US | binary | 814 b | whitelisted |
6536 | SIHClient.exe | GET | 200 | 74.178.76.128:443 | https://slscr.update.microsoft.com/sls/ping | US | — | — | whitelisted |
— | — | POST | 500 | 48.192.1.64:443 | https://activation-v2.sls.microsoft.com/SLActivateProduct/SLActivateProduct.asmx?configextension=Retail | US | text | 512 b | whitelisted |
6536 | SIHClient.exe | GET | 304 | 74.178.76.128:443 | https://slscr.update.microsoft.com/SLS/%7B522D76A4-93E1-47F8-B8CE-07C937AD1A1E%7D/x64/10.0.19045.4046/0?CH=686&L=en-US&P=&PT=0x30&WUA=10.0.19041.3996&MK=DELL&MD=DELL | US | — | — | whitelisted |
— | — | POST | 200 | 20.190.160.65:443 | https://login.live.com/RST2.srf | US | — | — | whitelisted |
— | — | POST | 400 | 20.190.160.64:443 | https://login.live.com/ppsecure/deviceaddcredential.srf | US | binary | 203 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:137 | — | Not routed | — | whitelisted |
— | — | 48.192.1.64:443 | activation-v2.sls.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:138 | — | Not routed | — | whitelisted |
5484 | svchost.exe | 23.216.77.28:80 | crl.microsoft.com | AKAMAI-ASN1 | NL | whitelisted |
5484 | svchost.exe | 23.52.181.212:80 | www.microsoft.com | AKAMAI-AS | US | whitelisted |
5276 | MoUsoCoreWorker.exe | 23.52.181.212:80 | www.microsoft.com | AKAMAI-AS | US | whitelisted |
— | — | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
— | — | 172.211.123.250:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
— | — | 20.190.160.65:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
activation-v2.sls.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
self.events.data.microsoft.com |
| whitelisted |