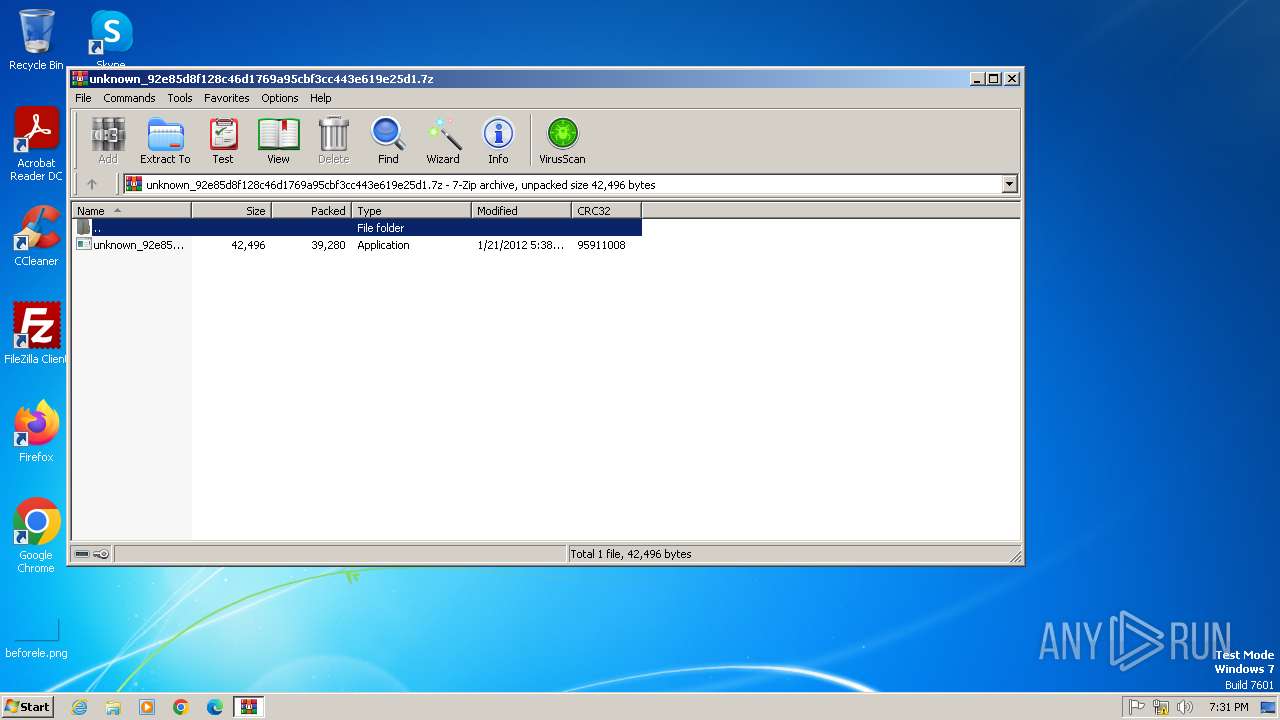
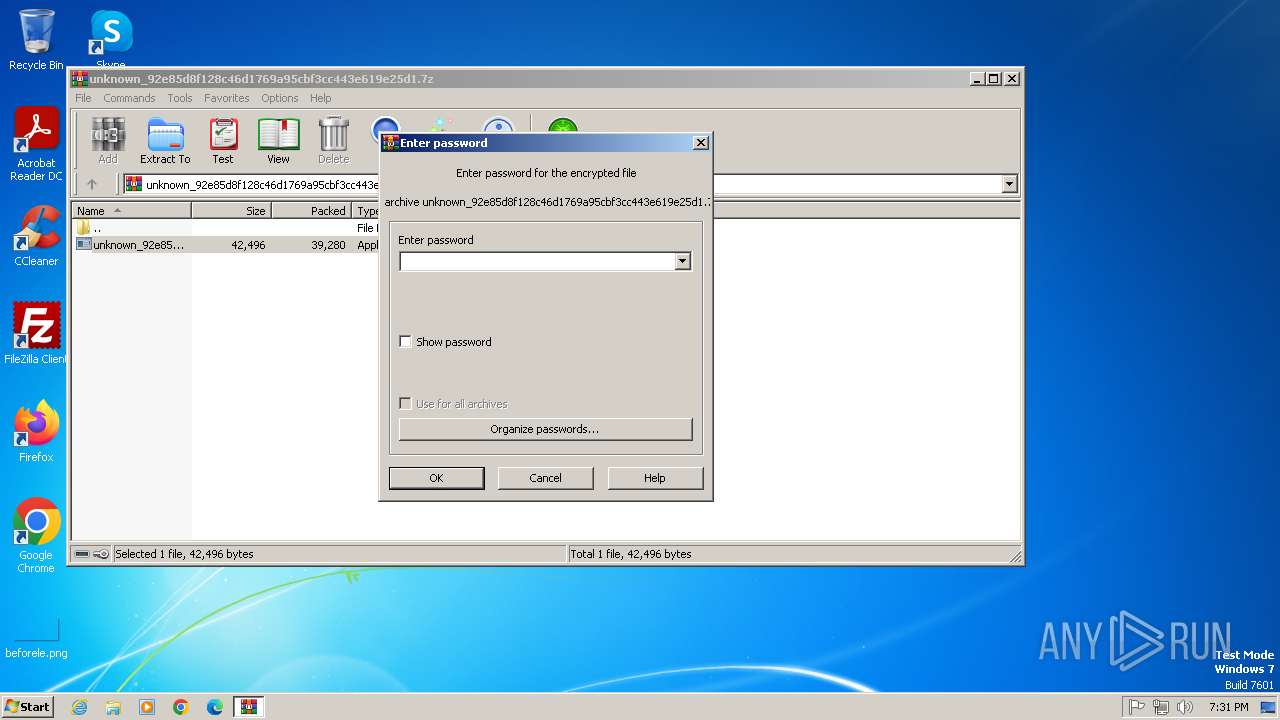
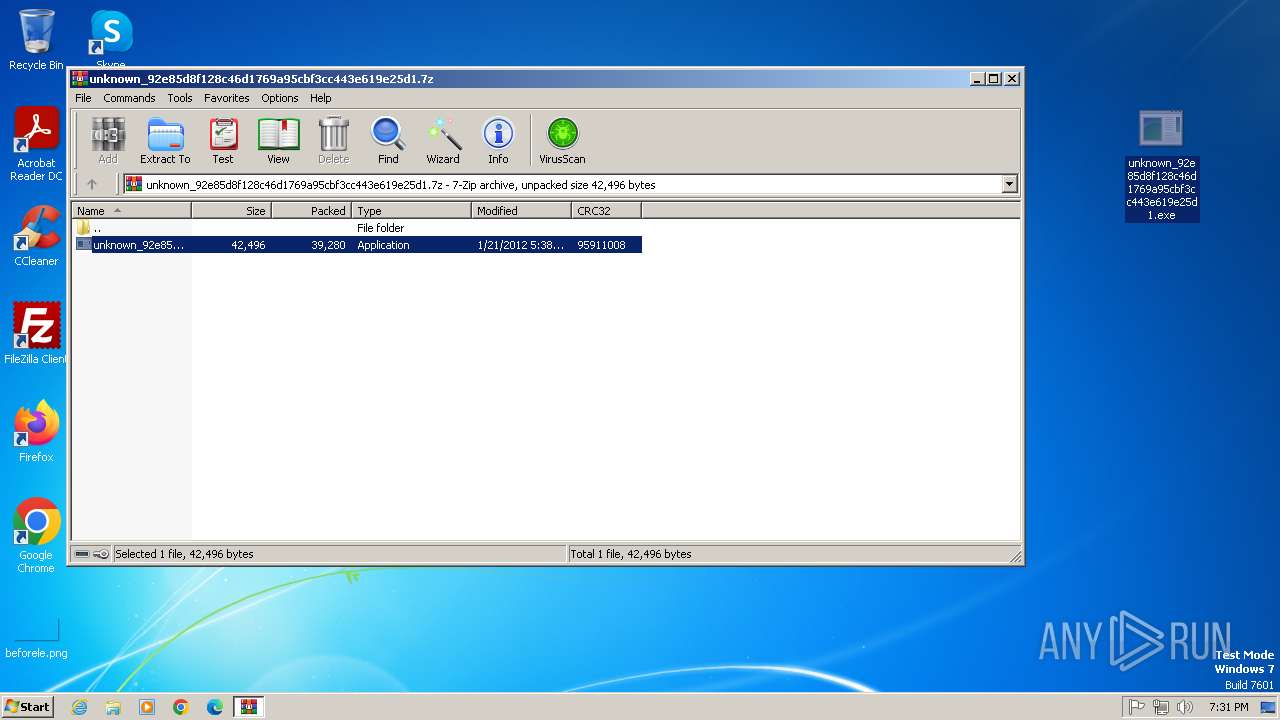
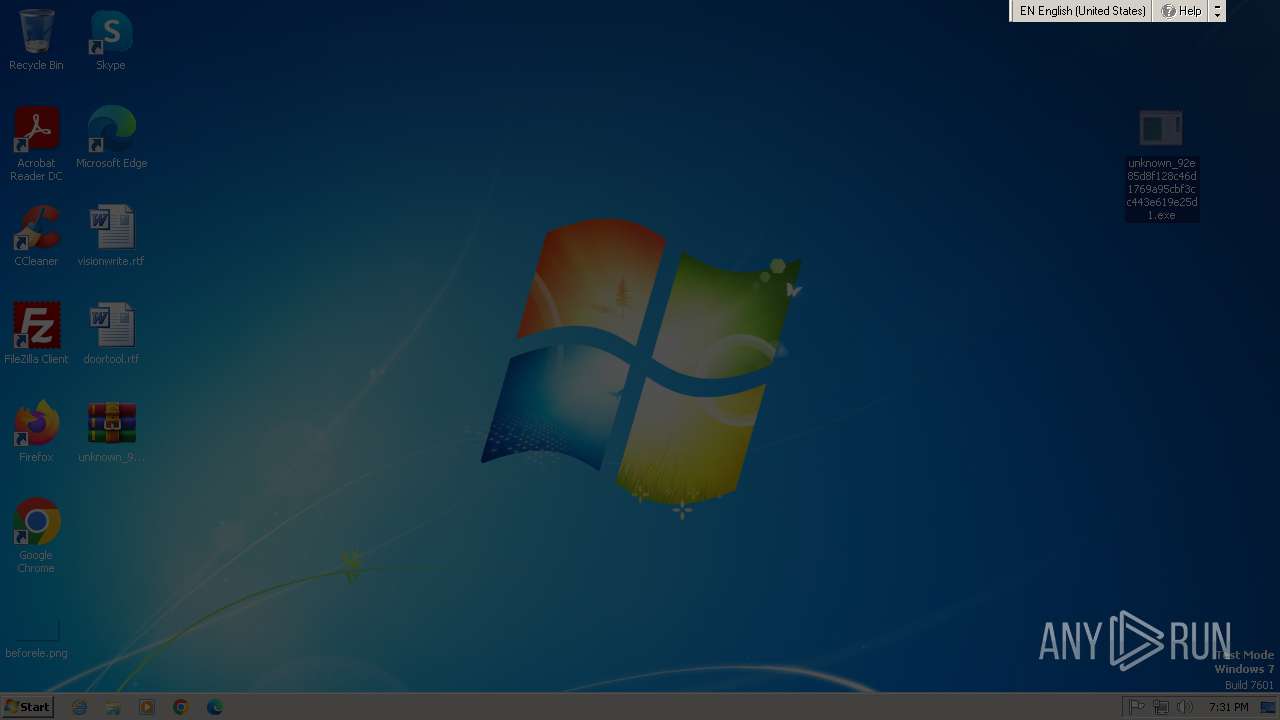
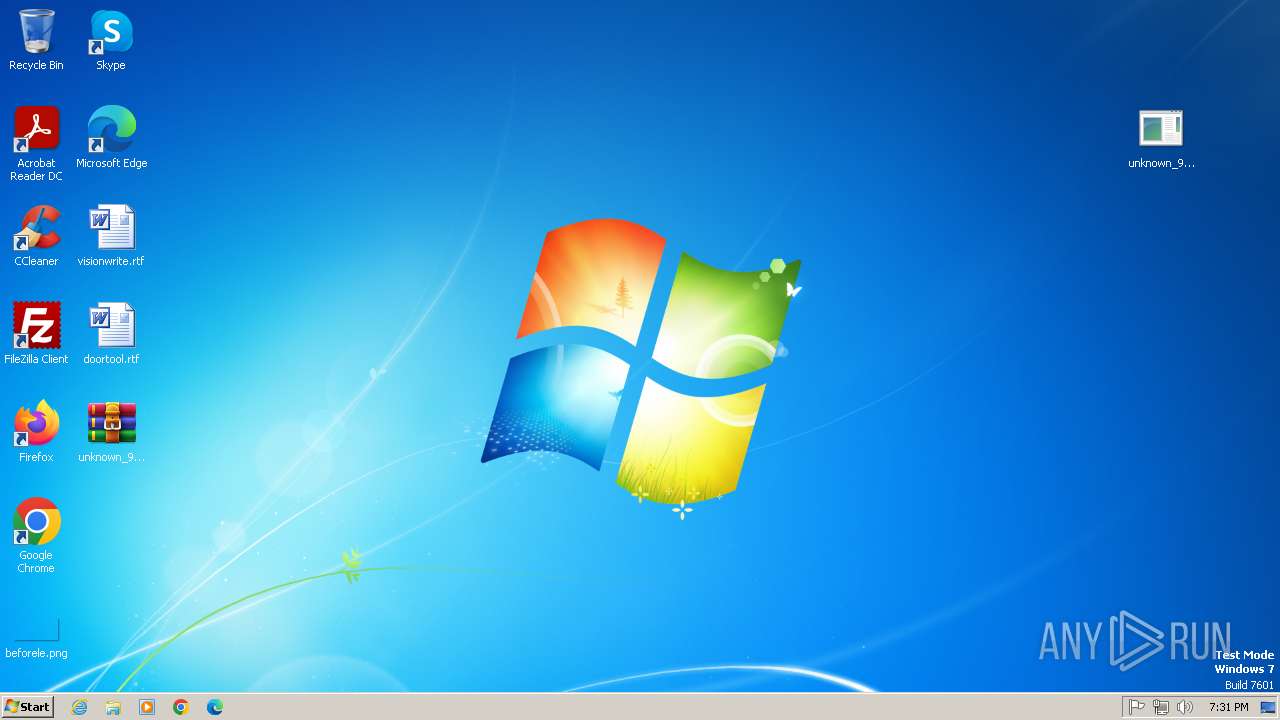
| File name: | unknown_92e85d8f128c46d1769a95cbf3cc443e619e25d1.7z |
| Full analysis: | https://app.any.run/tasks/66f97d4c-8b3d-4ac0-bb5e-58bfee171d84 |
| Verdict: | Malicious activity |
| Analysis date: | May 15, 2025, 18:31:01 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-7z-compressed |
| File info: | 7-zip archive data, version 0.4 |
| MD5: | 7FCA0C7B8AE9CC5571DC57C4E11384D0 |
| SHA1: | 74B398AD4D52FA704A76439FC6439899AD384BE7 |
| SHA256: | 5D79B29723B6058181CE0DFBB7FE3103C91704B75A4C59FFD37880CAB42F16E2 |
| SSDEEP: | 768:SdjzsloMg7wnnFh+ZYGxJuNQ9uJl2IyupecKoB4kurfl3xo13G8:8jIWMFnnFE1ZuJl5XKoeh7lBo13R |
MALICIOUS
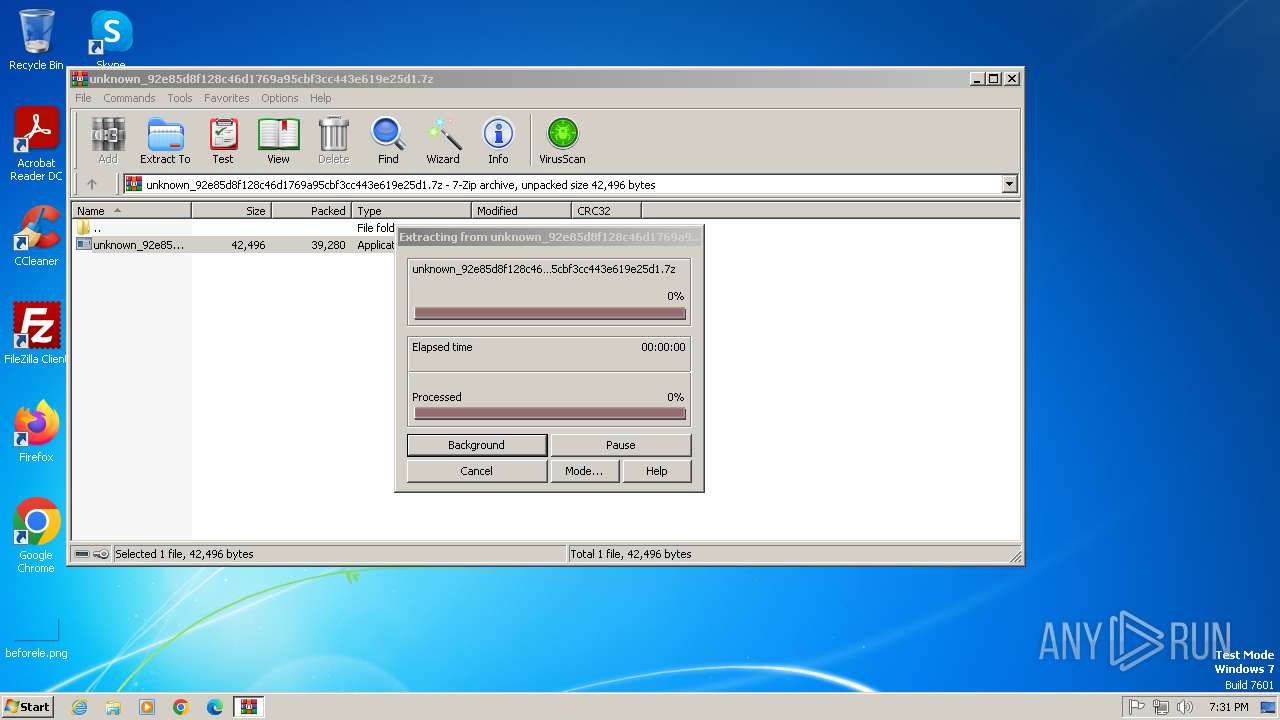
Generic archive extractor
- WinRAR.exe (PID: 2736)
Changes the login/logoff helper path in the registry
- svchost.exe (PID: 1648)
Changes image file execution options
- reg.exe (PID: 988)
- reg.exe (PID: 2204)
- reg.exe (PID: 676)
SUSPICIOUS
Executable content was dropped or overwritten
- svchost.exe (PID: 1648)
Uses REG/REGEDIT.EXE to modify registry
- svchost.exe (PID: 1648)
Searches for installed software
- svchost.exe (PID: 1648)
- dllhost.exe (PID: 3180)
Executes as Windows Service
- VSSVC.exe (PID: 3552)
INFO
Executable content was dropped or overwritten
- WinRAR.exe (PID: 2736)
The sample compiled with english language support
- WinRAR.exe (PID: 2736)
- svchost.exe (PID: 1648)
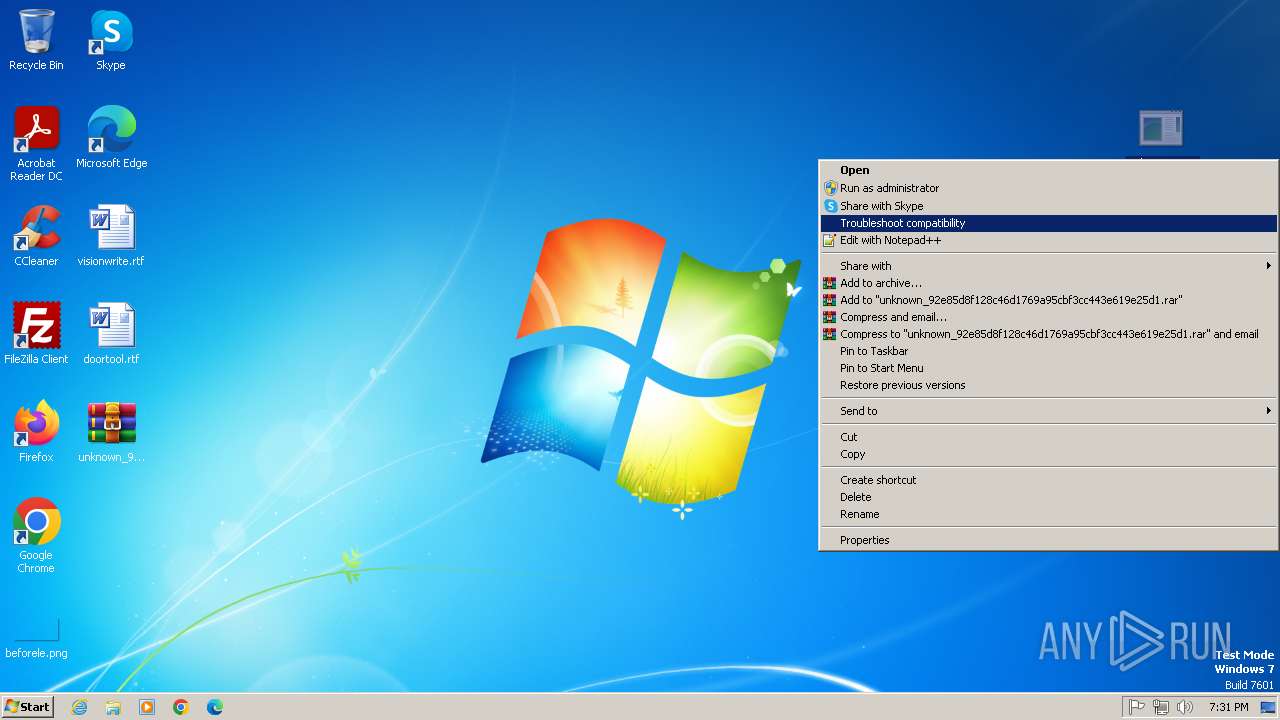
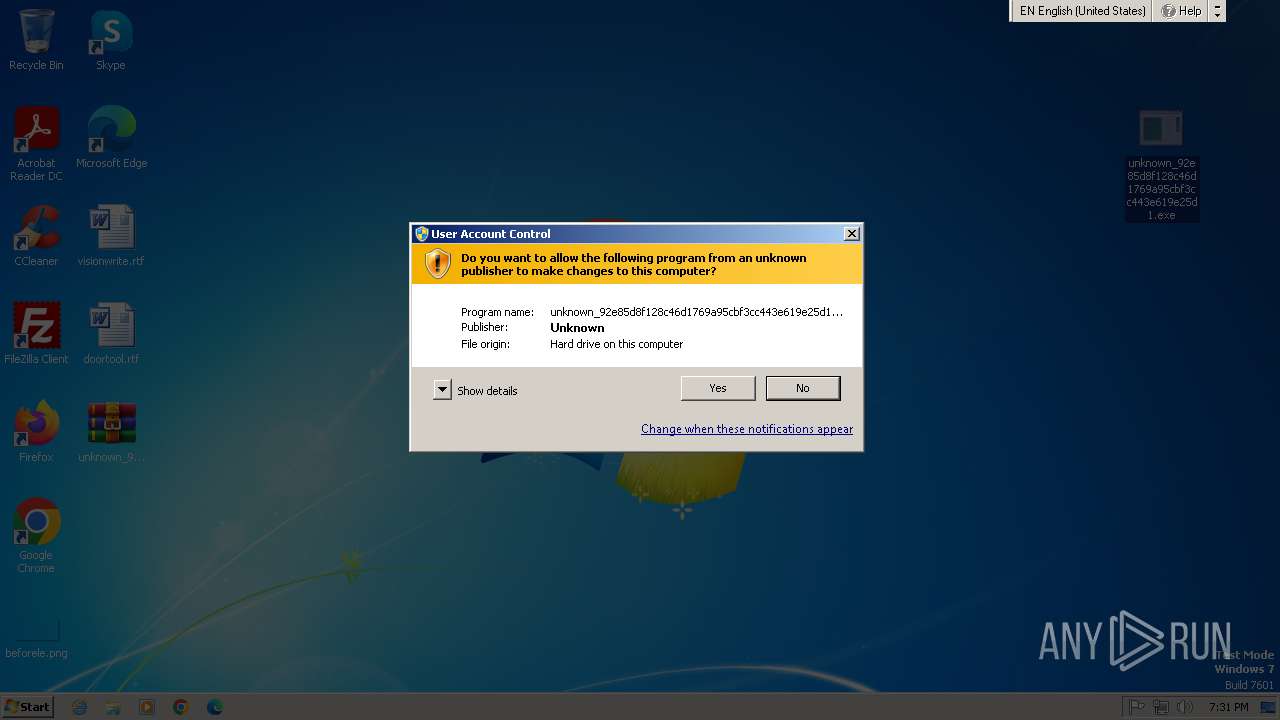
Manual execution by a user
- unknown_92e85d8f128c46d1769a95cbf3cc443e619e25d1.exe (PID: 1400)
Checks supported languages
- unknown_92e85d8f128c46d1769a95cbf3cc443e619e25d1.exe (PID: 1400)
- 67CCE47EC4BA364718F5.exe (PID: 2976)
Create files in a temporary directory
- svchost.exe (PID: 1648)
- svchost.exe (PID: 2600)
Reads security settings of Internet Explorer
- svchost.exe (PID: 2600)
Checks proxy server information
- svchost.exe (PID: 2600)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .7z | | | 7-Zip compressed archive (v0.4) (57.1) |
|---|---|---|
| .7z | | | 7-Zip compressed archive (gen) (42.8) |
EXIF
ZIP
| FileVersion: | 7z v0.04 |
|---|---|
| ModifyDate: | 2012:01:21 17:38:28+00:00 |
| ArchivedFileName: | unknown_92e85d8f128c46d1769a95cbf3cc443e619e25d1.exe |
Total processes
63
Monitored processes
16
Malicious processes
3
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 676 | reg.exe add "HKEY_LOCAL_MACHINE\Software\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\msconfig.exe" /t REG_SZ /f /v Debugger /d P9KDMF.EXE | C:\Windows\System32\reg.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 988 | reg.exe add "HKEY_LOCAL_MACHINE\Software\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\taskmgr.exe" /t REG_SZ /f /v Debugger /d P9KDMF.EXE | C:\Windows\System32\reg.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1080 | C:\Windows\system32\svchost.exe -k NetworkService | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1400 | "C:\Users\admin\Desktop\unknown_92e85d8f128c46d1769a95cbf3cc443e619e25d1.exe" | C:\Users\admin\Desktop\unknown_92e85d8f128c46d1769a95cbf3cc443e619e25d1.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 1 Modules
| |||||||||||||||
| 1504 | reg.exe add "HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\System" /t REG_DWORD /f /v DisableRegedit /d "1" | C:\Windows\System32\reg.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1548 | reg.exe delete "HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Control\SafeBoot" /f | C:\Windows\System32\reg.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1648 | svchost.exe | C:\Windows\System32\svchost.exe | unknown_92e85d8f128c46d1769a95cbf3cc443e619e25d1.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Host Process for Windows Services Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2100 | reg.exe add "HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\System" /t REG_DWORD /f /v DisableTaskMgr /d "1" | C:\Windows\System32\reg.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2204 | reg.exe add "HKEY_LOCAL_MACHINE\Software\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\regedit.exe" /t REG_SZ /f /v Debugger /d P9KDMF.EXE | C:\Windows\System32\reg.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2600 | svchost.exe | C:\Windows\System32\svchost.exe | — | 67CCE47EC4BA364718F5.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Host Process for Windows Services Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
7 734
Read events
7 286
Write events
430
Delete events
18
Modification events
| (PID) Process: | (2736) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2736) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2736) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\Win7-KB3191566-x86.zip | |||
| (PID) Process: | (2736) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\curl-8.5.0_1-win32-mingw.zip | |||
| (PID) Process: | (2736) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (2736) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\unknown_92e85d8f128c46d1769a95cbf3cc443e619e25d1.7z | |||
| (PID) Process: | (2736) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2736) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2736) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2736) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
Executable files
3
Suspicious files
12
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3180 | dllhost.exe | C:\System Volume Information\SPP\metadata-2 | — | |
MD5:— | SHA256:— | |||
| 1080 | svchost.exe | C:\Windows\System32\catroot2\{F750E6C3-38EE-11D1-85E5-00C04FC295EE}\catdb | — | |
MD5:— | SHA256:— | |||
| 1648 | svchost.exe | C:\Users\admin\AppData\Local\Temp\48380016C4BA3647C1C1.exe | executable | |
MD5:A68AAB742E12DAD8E6F04497EFA0EAA7 | SHA256:FC5FC09ED049881D9274F37EB3AA3446868E20B21D863D63873D2A5F53564FE8 | |||
| 1080 | svchost.exe | C:\Windows\System32\catroot2\edb.chk | binary | |
MD5:396057103A53871FB02CC430ECEE4FB1 | SHA256:D11C549A4868E8A1B11193A7967ABC2AD5C4BDD9EE72539CF3AF22EBEF6DA939 | |||
| 1648 | svchost.exe | C:\Windows\System32\67CCE47EC4BA364718F5.exe | executable | |
MD5:A68AAB742E12DAD8E6F04497EFA0EAA7 | SHA256:FC5FC09ED049881D9274F37EB3AA3446868E20B21D863D63873D2A5F53564FE8 | |||
| 1080 | svchost.exe | C:\Windows\System32\catroot2\edb.log | binary | |
MD5:D26C12960BF99AB9559E77CBA3EF6FCA | SHA256:834537EEAF504D53255CB4CFB2D98B71B0E11C13EA97FF0A967FB490E613C639 | |||
| 1080 | svchost.exe | C:\Windows\System32\catroot2\edbtmp.log | binary | |
MD5:A11B51F85ACEF5C1D753D3473EE0979D | SHA256:75725D835DE481654942B0B7B746CA1807E17F98E7F46D04B01365BA27009C19 | |||
| 1080 | svchost.exe | C:\Windows\System32\catroot2\edb004F2.log | binary | |
MD5:D6E9618DCDDB397BF4E1F19EBE71EABA | SHA256:45769A34D841B26E904D0EFB61C850D545A508B1A54D158962F03B57726F90D9 | |||
| 2600 | svchost.exe | C:\Users\admin\AppData\Local\Temp\C4BA36475245535564616461 | binary | |
MD5:D73D5928DC9E4BCEF4E3A4C2914F7C23 | SHA256:1791D8DB9F22168560EA8D7F79C6D5F17B792E7FAB39C67939433BDB3AF4561B | |||
| 3180 | dllhost.exe | C:\System Volume Information\SPP\OnlineMetadataCache\{a573a5f7-166b-41a3-8d6b-6e41dce1f477}_OnDiskSnapshotProp | binary | |
MD5:72C5F1469E5673ED8534484729798862 | SHA256:080216DEDCE73B45B1CE8D401DB3525173AE0D3767AF0D09EF944D348097944F | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
6
DNS requests
5
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 224.0.0.252:5355 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
haubagartenan.com |
| unknown |
bienenstichhs.com |
| unknown |
fensterbaubanns.com |
| unknown |
hv673hv573hv53h7khv57.com |
| malicious |