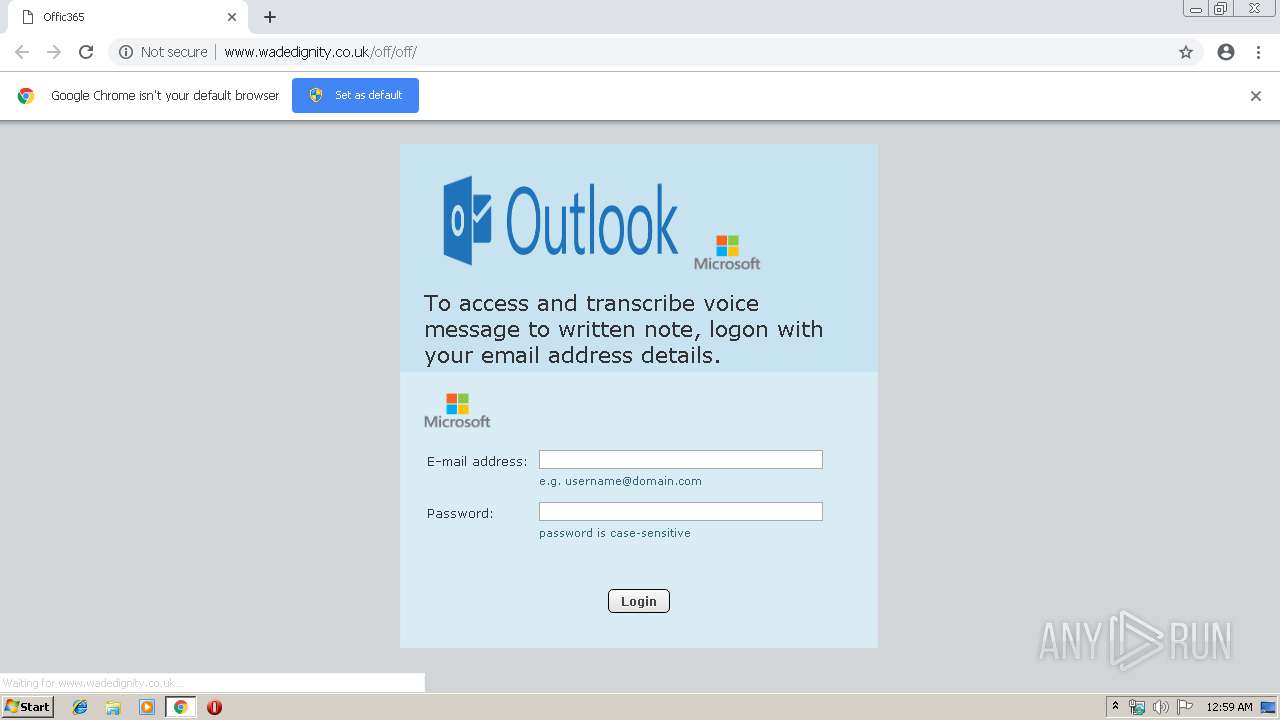
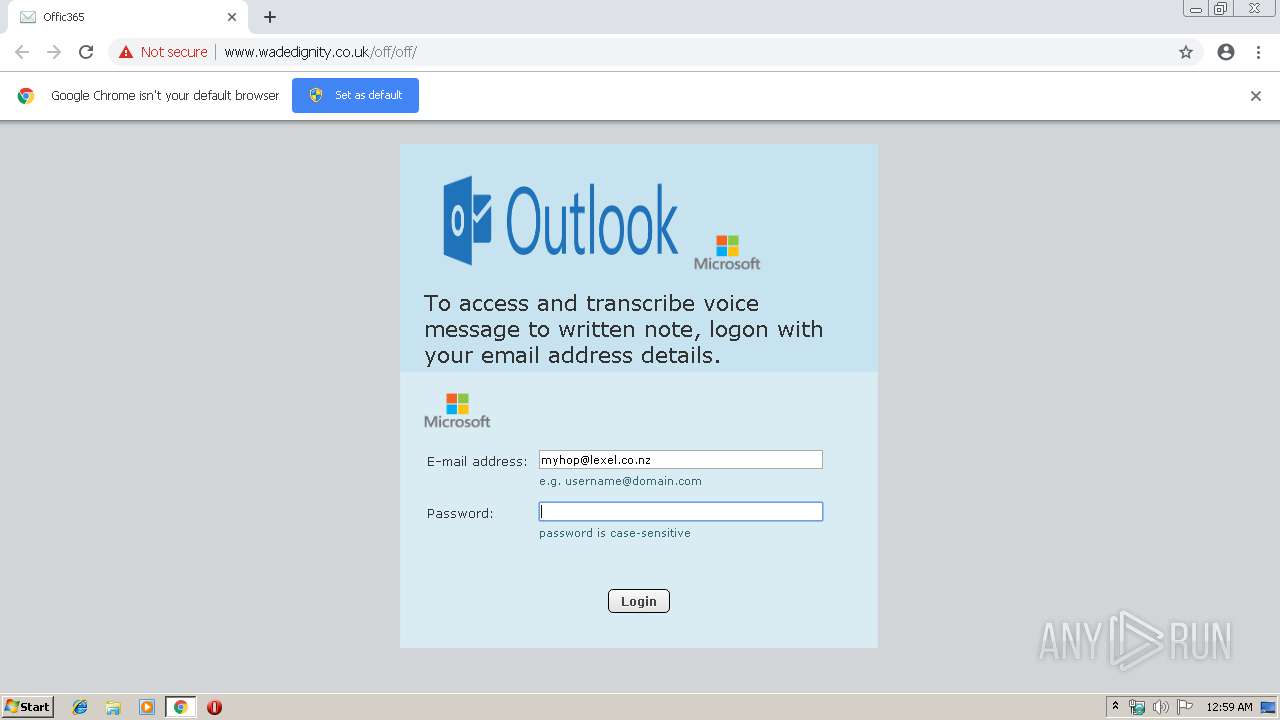
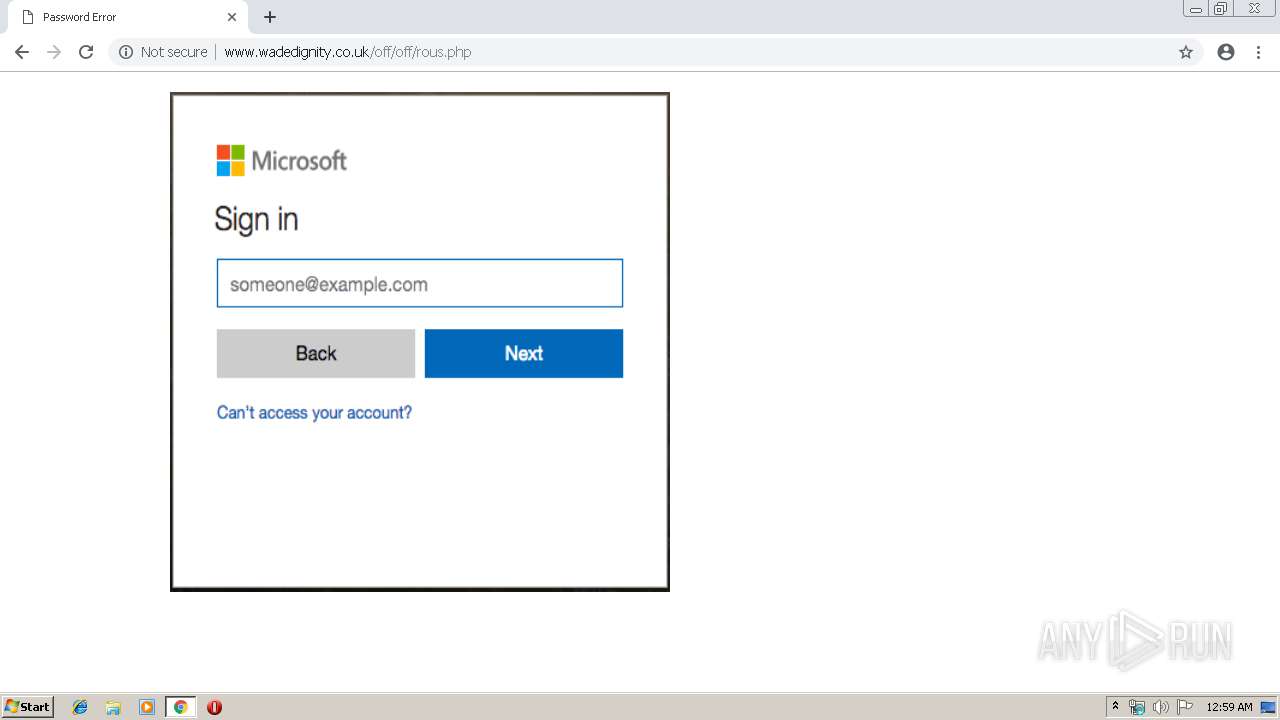
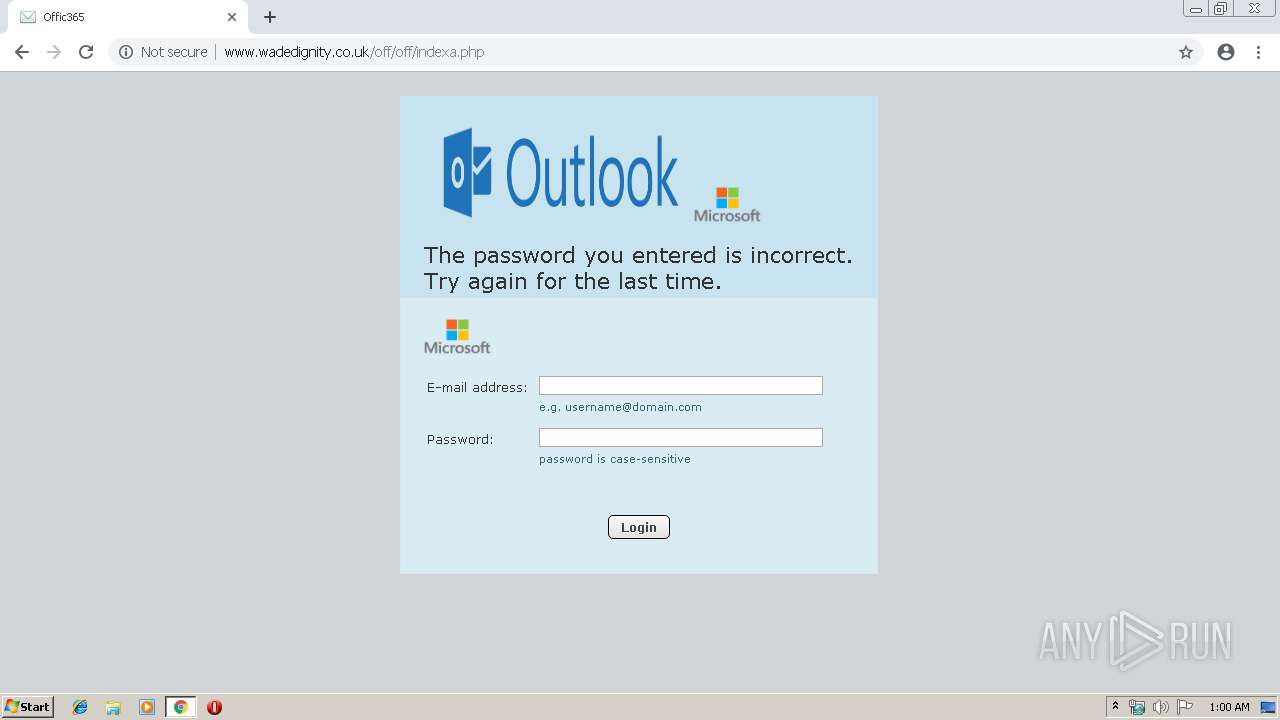
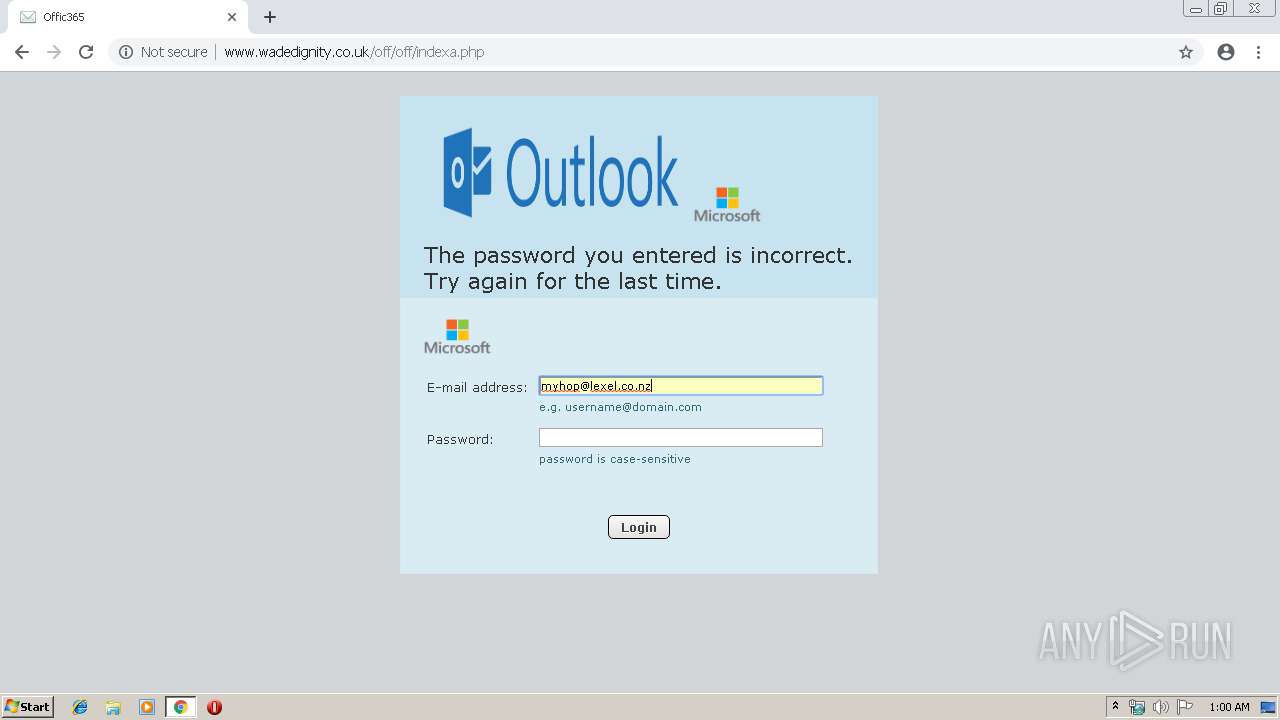
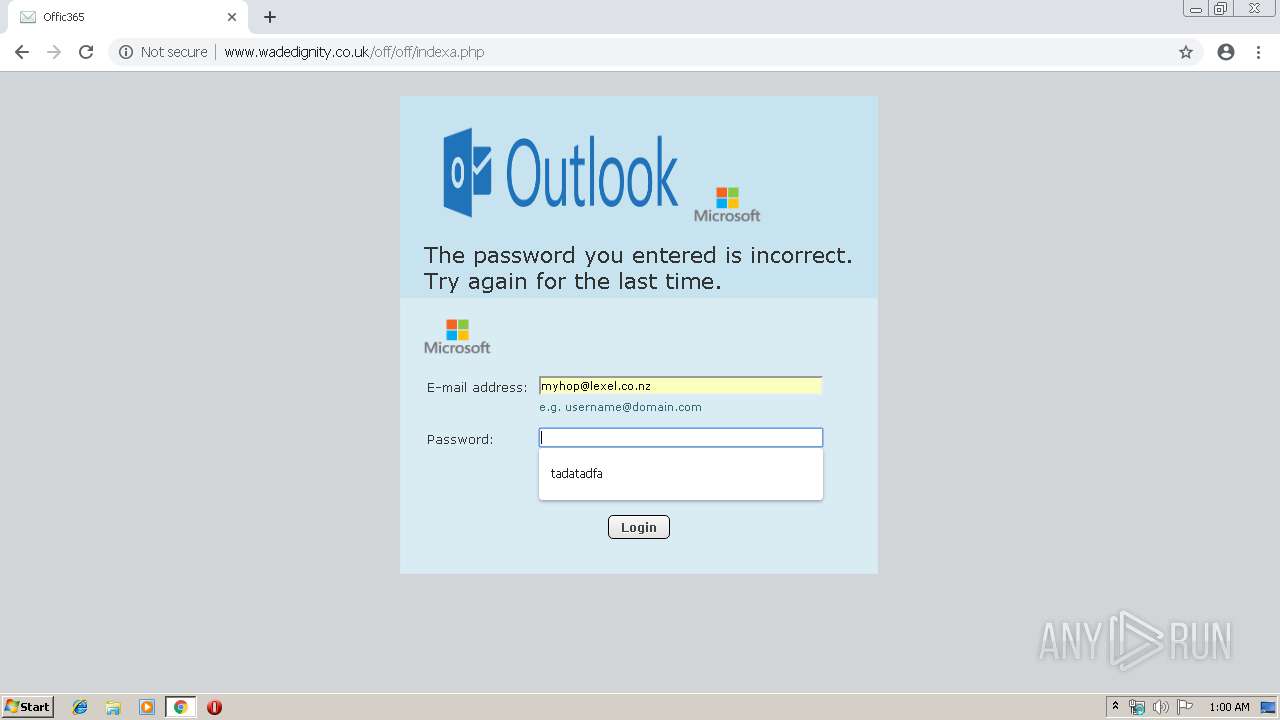
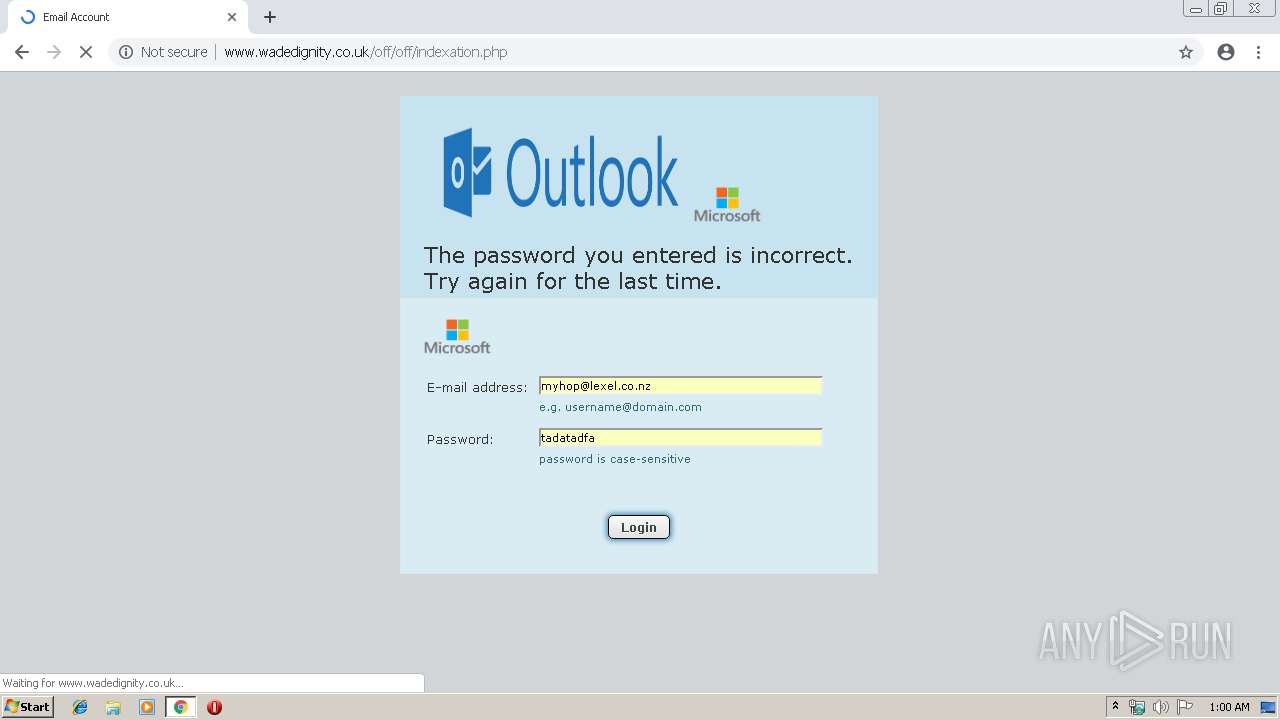
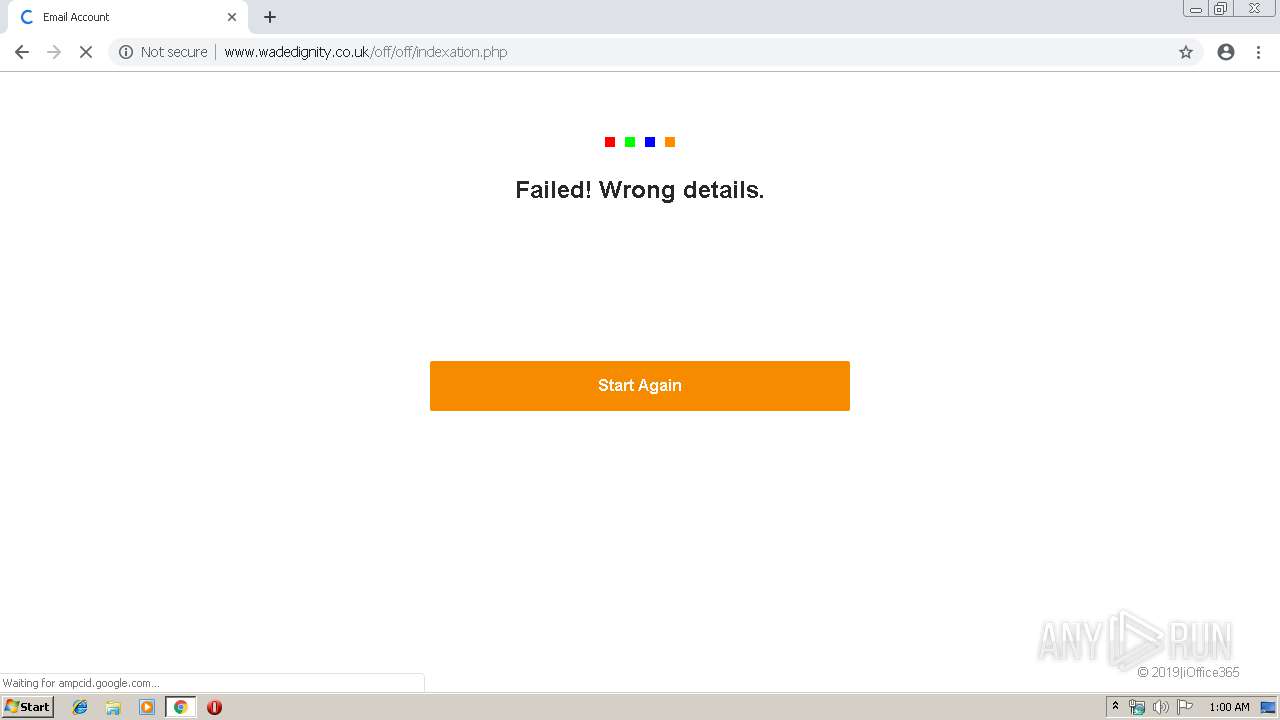
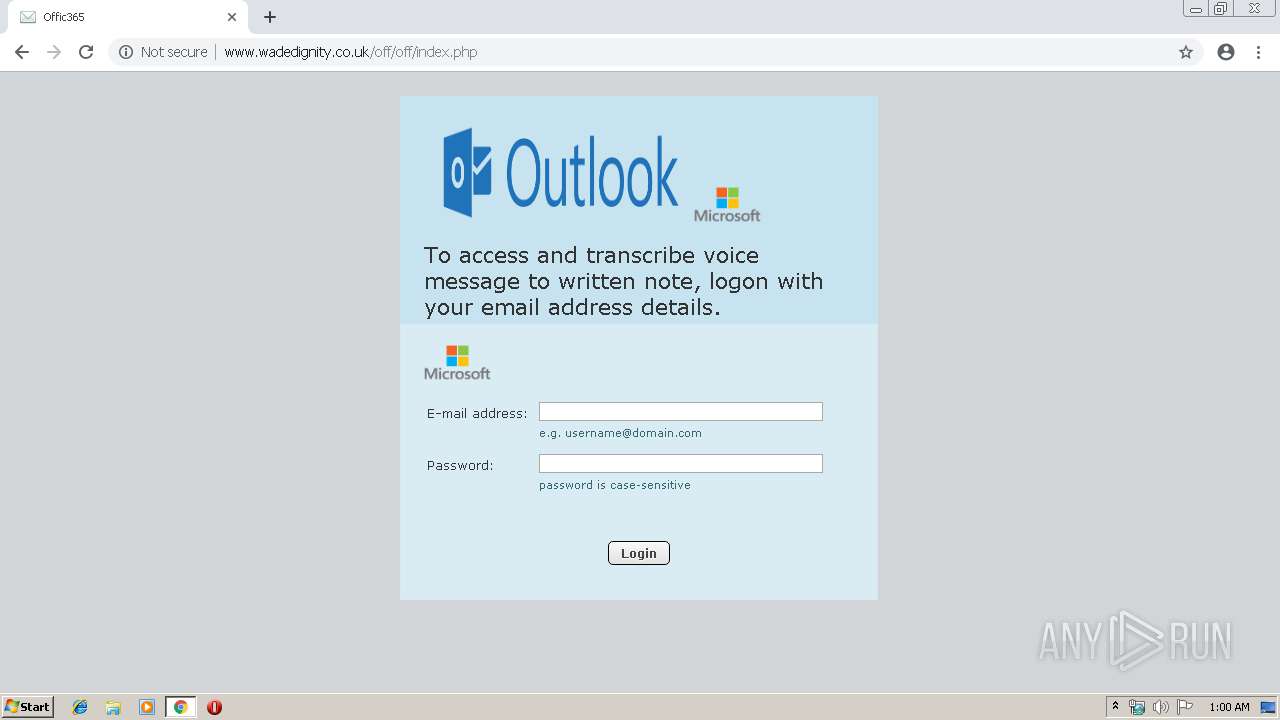
| URL: | http://www.wadedignity.co.uk/off/off/ |
| Full analysis: | https://app.any.run/tasks/d7c876ce-a819-401d-afbb-2b605058735b |
| Verdict: | Malicious activity |
| Analysis date: | May 20, 2019, 23:59:18 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | F1783BA9C5AC8EB68AE8FC0AE14E61E4 |
| SHA1: | 3DC1AD02DF4F70E10A2FCA163485FFD21BA7D95B |
| SHA256: | 5D7802B00059CB173B93B402C18FD632BD9F06D4449145AC4EAD9633B54EAD10 |
| SSDEEP: | 3:N1KJS4LC4WkORDWYW:Cc4tRO0F |
MALICIOUS
No malicious indicators.SUSPICIOUS
Modifies files in Chrome extension folder
- chrome.exe (PID: 2964)
INFO
Application launched itself
- chrome.exe (PID: 2964)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
52
Monitored processes
20
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 992 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=940,10658757632699496643,17954541270075751283,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=536742348314380887 --mojo-platform-channel-handle=3920 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2188 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=940,10658757632699496643,17954541270075751283,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=778498149890897721 --mojo-platform-channel-handle=3892 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2280 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=940,10658757632699496643,17954541270075751283,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=563801660148350501 --mojo-platform-channel-handle=3896 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2492 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=940,10658757632699496643,17954541270075751283,131072 --enable-features=PasswordImport --service-pipe-token=4813355302925983638 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=4813355302925983638 --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1988 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2720 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=2968 --on-initialized-event-handle=308 --parent-handle=312 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2764 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=940,10658757632699496643,17954541270075751283,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=5518989977442631369 --mojo-platform-channel-handle=3924 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2804 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=940,10658757632699496643,17954541270075751283,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=2399307312692267631 --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=2399307312692267631 --renderer-client-id=16 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3244 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2816 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=940,10658757632699496643,17954541270075751283,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=13706456899286365907 --mojo-platform-channel-handle=4272 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2936 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=940,10658757632699496643,17954541270075751283,131072 --enable-features=PasswordImport --service-pipe-token=12735527877377163818 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=12735527877377163818 --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2004 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2964 | "C:\Program Files\Google\Chrome\Application\chrome.exe" http://www.wadedignity.co.uk/off/off/ | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
Total events
546
Read events
459
Write events
82
Delete events
5
Modification events
| (PID) Process: | (2964) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2964) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2964) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2964) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2720) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2964-13202870373263125 |
Value: 259 | |||
| (PID) Process: | (2964) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2964) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2964) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2964) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3488-13197474229333984 |
Value: 0 | |||
| (PID) Process: | (2964) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
0
Suspicious files
61
Text files
218
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2964 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\index | — | |
MD5:— | SHA256:— | |||
| 2964 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_0 | — | |
MD5:— | SHA256:— | |||
| 2964 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 2964 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_2 | — | |
MD5:— | SHA256:— | |||
| 2964 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_3 | — | |
MD5:— | SHA256:— | |||
| 2964 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000018.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2964 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\bba3b1ae-e562-4241-8ad6-5251d14aeb71.tmp | — | |
MD5:— | SHA256:— | |||
| 2964 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\index | — | |
MD5:— | SHA256:— | |||
| 2964 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\data_0 | — | |
MD5:— | SHA256:— | |||
| 2964 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
60
TCP/UDP connections
53
DNS requests
32
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2964 | chrome.exe | GET | 200 | 46.32.240.45:80 | http://www.wadedignity.co.uk/off/off/scic_files/styles.css | GB | text | 61.0 Kb | suspicious |
2964 | chrome.exe | GET | 200 | 46.32.240.45:80 | http://www.wadedignity.co.uk/off/off/scic_files/webmail.css | GB | text | 6.68 Kb | suspicious |
2964 | chrome.exe | GET | 200 | 46.32.240.45:80 | http://www.wadedignity.co.uk/off/off/scic_files/webmail_002.css | GB | text | 3.35 Kb | suspicious |
2964 | chrome.exe | GET | 200 | 46.32.240.45:80 | http://www.wadedignity.co.uk/off/off/ | GB | html | 10.4 Kb | suspicious |
2964 | chrome.exe | GET | 404 | 46.32.240.45:80 | http://www.wadedignity.co.uk/off/off/scic_files/jstz.htm | GB | html | 310 b | suspicious |
2964 | chrome.exe | GET | 404 | 46.32.240.45:80 | http://www.wadedignity.co.uk/off/off/scic_files/images/linen.jpg?v=0382.14157 | GB | html | 318 b | suspicious |
2964 | chrome.exe | GET | 200 | 46.32.240.45:80 | http://www.wadedignity.co.uk/off/off/scic_files/app.js | GB | text | 276 Kb | suspicious |
2964 | chrome.exe | GET | 200 | 46.32.240.45:80 | http://www.wadedignity.co.uk/off/off/scic_files/fontsize_hacks.js | GB | text | 468 b | suspicious |
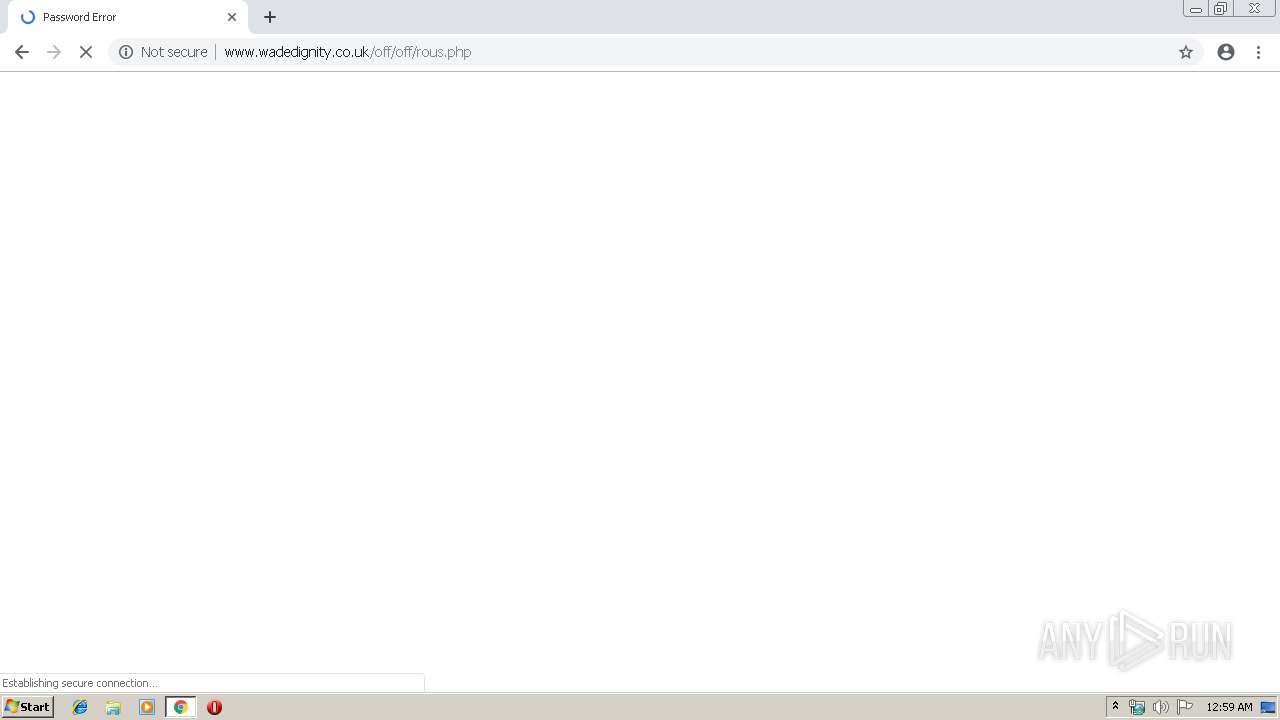
2964 | chrome.exe | POST | 200 | 46.32.240.45:80 | http://www.wadedignity.co.uk/off/off/rous.php | GB | html | 1.84 Kb | suspicious |
2964 | chrome.exe | GET | 200 | 46.32.240.45:80 | http://www.wadedignity.co.uk/off/off/scic_files/delta.css | GB | text | 339 b | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2964 | chrome.exe | 172.217.21.205:443 | accounts.google.com | Google Inc. | US | whitelisted |
2964 | chrome.exe | 172.217.16.163:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2964 | chrome.exe | 91.134.128.42:443 | www.graphland.fr | OVH SAS | FR | unknown |
2964 | chrome.exe | 46.32.240.45:80 | www.wadedignity.co.uk | Host Europe GmbH | GB | suspicious |
2964 | chrome.exe | 95.213.195.222:443 | logonoid.com | OOO Network of data-centers Selectel | RU | suspicious |
2964 | chrome.exe | 64.98.36.218:443 | mail.scicable.com | Tucows.com Co. | CA | unknown |
2964 | chrome.exe | 172.217.18.110:443 | clients1.google.com | Google Inc. | US | whitelisted |
2964 | chrome.exe | 216.58.207.36:443 | www.google.com | Google Inc. | US | whitelisted |
2964 | chrome.exe | 216.58.208.46:443 | clients2.google.com | Google Inc. | US | whitelisted |
2964 | chrome.exe | 216.58.207.67:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
www.wadedignity.co.uk |
| suspicious |
accounts.google.com |
| shared |
www.graphland.fr |
| unknown |
logonoid.com |
| suspicious |
clients1.google.com |
| whitelisted |
mail.scicable.com |
| unknown |
www.google.com |
| malicious |
clients4.google.com |
| whitelisted |
clients2.google.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2964 | chrome.exe | Generic Protocol Command Decode | SURICATA HTTP unable to match response to request |
2 ETPRO signatures available at the full report