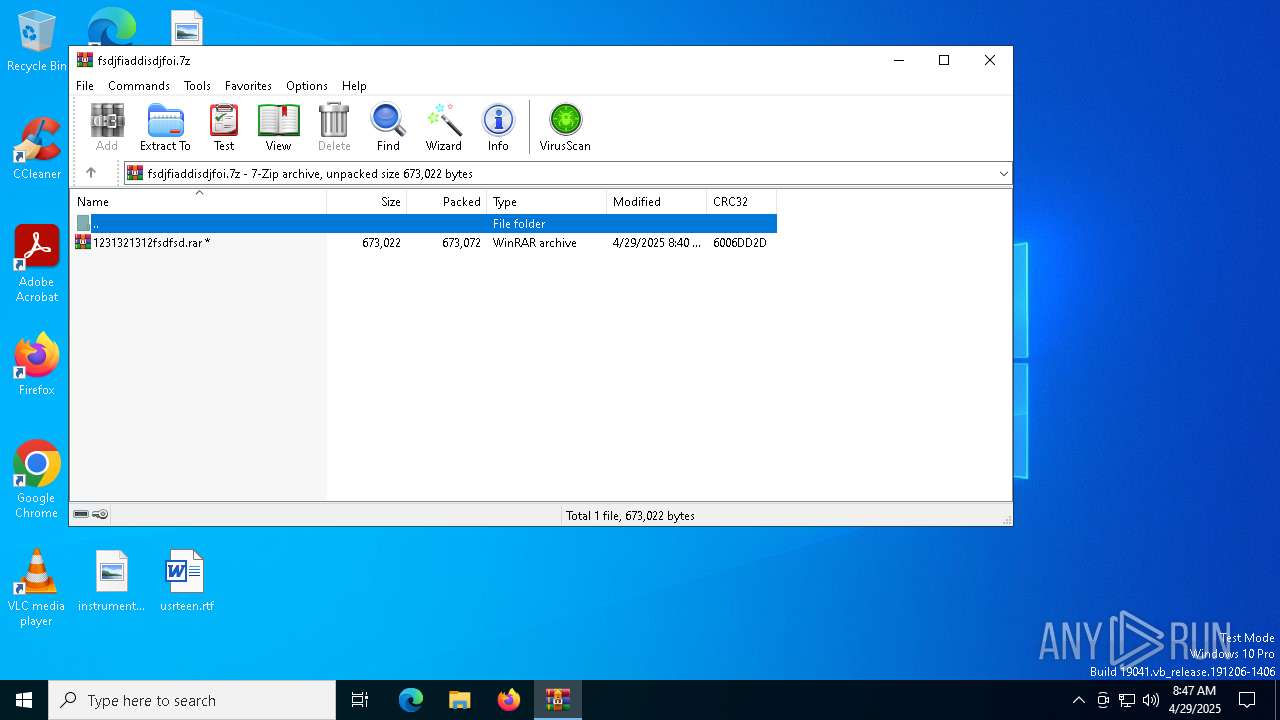
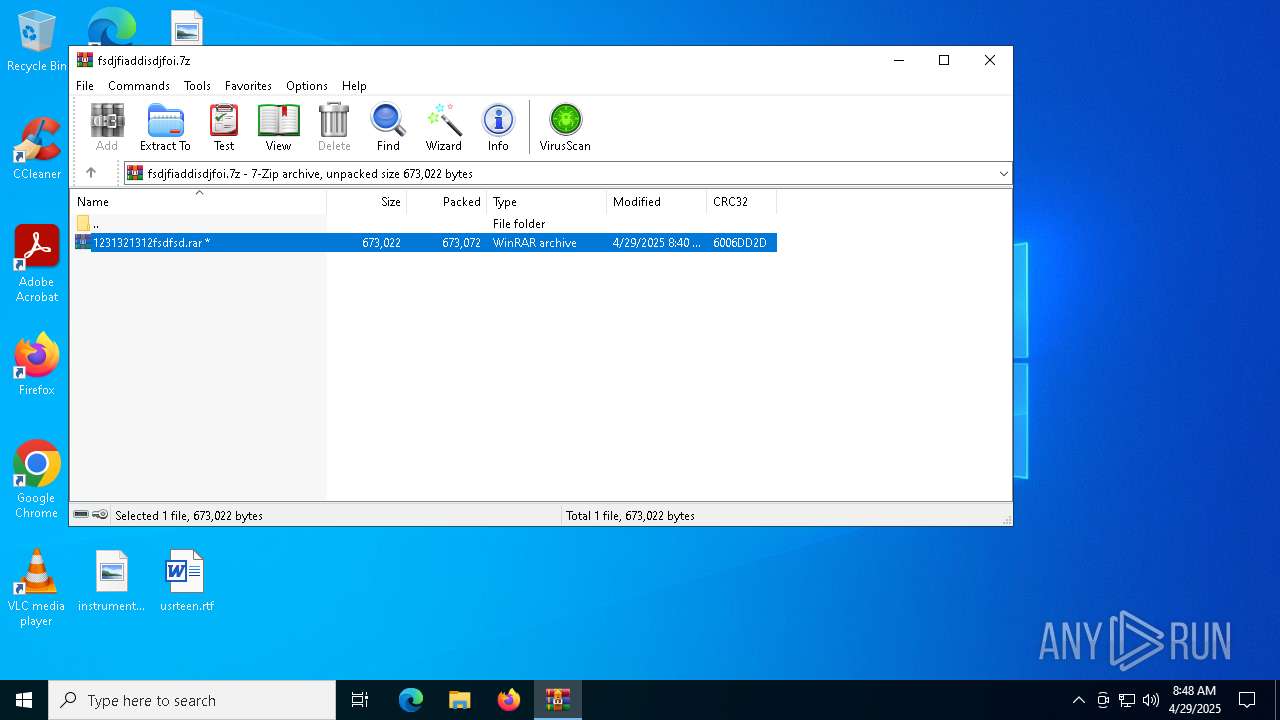
| File name: | fsdjfiaddisdjfoi.7z |
| Full analysis: | https://app.any.run/tasks/df92cdd6-2372-45ba-93dd-9a90b63895fe |
| Verdict: | Malicious activity |
| Analysis date: | April 29, 2025, 08:47:43 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Indicators: | |
| MIME: | application/x-7z-compressed |
| File info: | 7-zip archive data, version 0.4 |
| MD5: | 250F41CCED07361520C06E8C005F1309 |
| SHA1: | 9422BE16FF254CAFD5CE29ADD42BC7D19EC8C69E |
| SHA256: | 5D691108079A12F6EF9AFF73F09F8587C5C1AF37165C486BE9DC1611362D27C0 |
| SSDEEP: | 24576:5Dl0TaTnN9mXgUfacdP3M87UN5pyrTBfib7LvNOQRo2d2wtWlqEhkpcXfpcuI+:5Dl0TarN9mXgUfa63M87UDpyrTBfib7q |
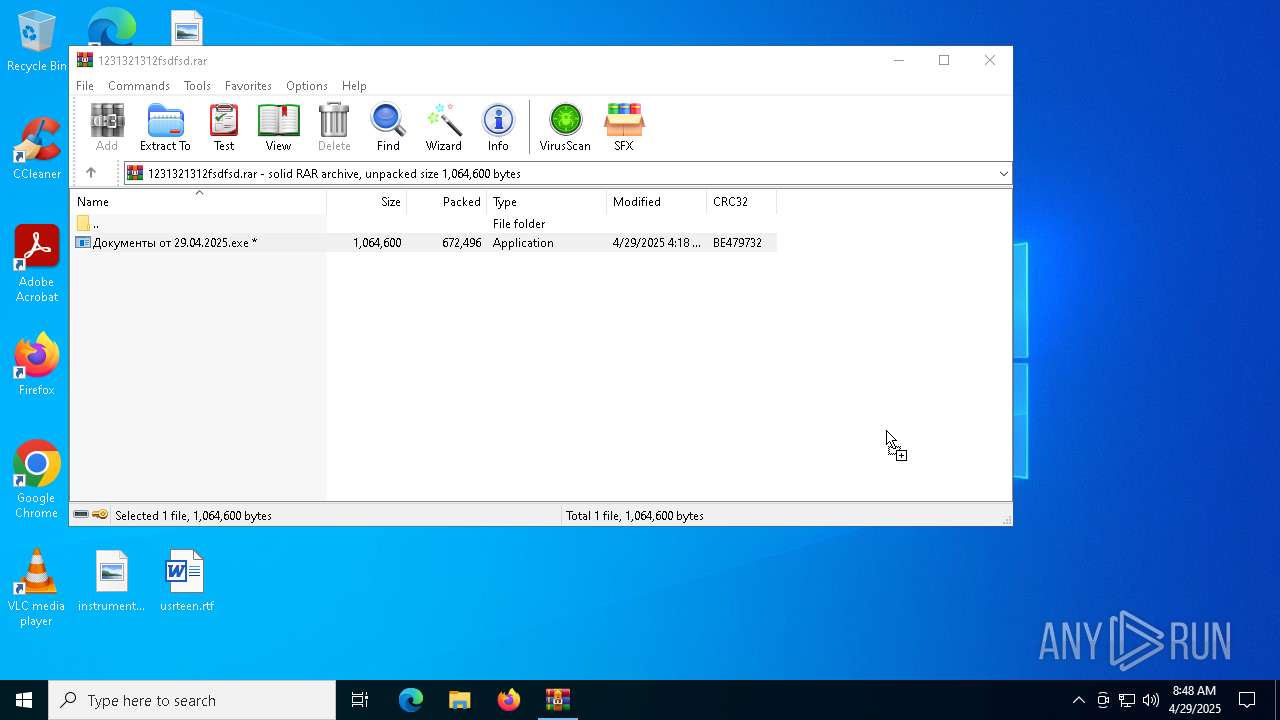
MALICIOUS
Executing a file with an untrusted certificate
- Документы от 29.04.2025.exe (PID: 1052)
SUSPICIOUS
Executes application which crashes
- Документы от 29.04.2025.exe (PID: 1052)
INFO
Executable content was dropped or overwritten
- WinRAR.exe (PID: 6712)
Reads the software policy settings
- slui.exe (PID: 4756)
- slui.exe (PID: 4212)
Checks proxy server information
- slui.exe (PID: 4212)
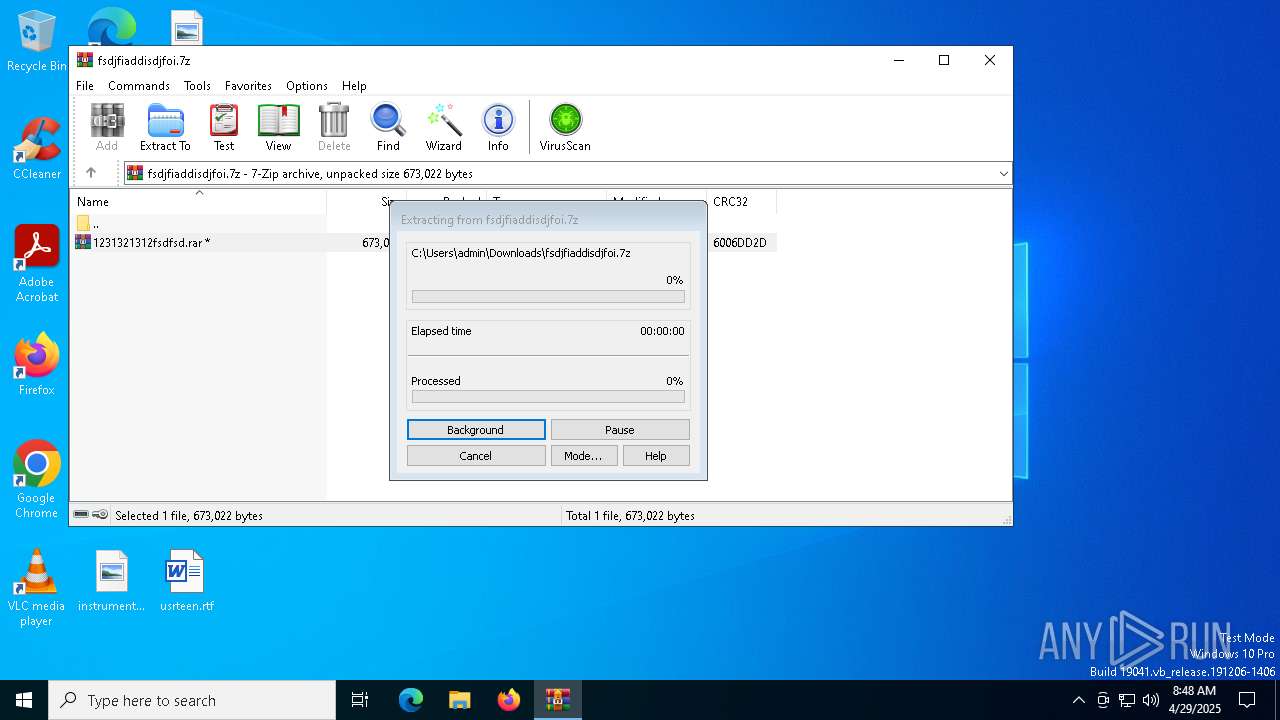
Manual execution by a user
- WinRAR.exe (PID: 6712)
- Документы от 29.04.2025.exe (PID: 1052)
Reads the machine GUID from the registry
- Документы от 29.04.2025.exe (PID: 1052)
Reads the computer name
- Документы от 29.04.2025.exe (PID: 1052)
Creates files or folders in the user directory
- WerFault.exe (PID: 5668)
Checks supported languages
- Документы от 29.04.2025.exe (PID: 1052)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .7z | | | 7-Zip compressed archive (v0.4) (57.1) |
|---|---|---|
| .7z | | | 7-Zip compressed archive (gen) (42.8) |
EXIF
ZIP
| FileVersion: | 7z v0.04 |
|---|---|
| ModifyDate: | 2025:04:29 08:40:57+00:00 |
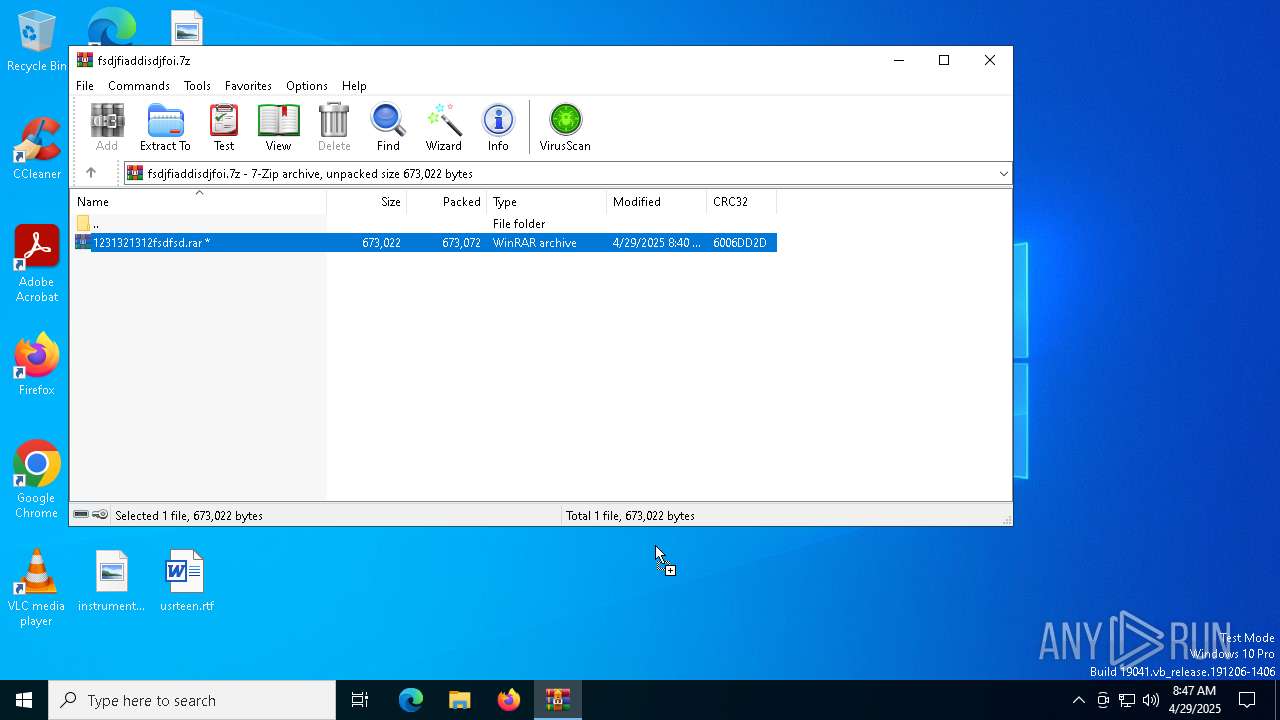
| ArchivedFileName: | 1231321312fsdfsd.rar |
Total processes
139
Monitored processes
7
Malicious processes
0
Suspicious processes
1
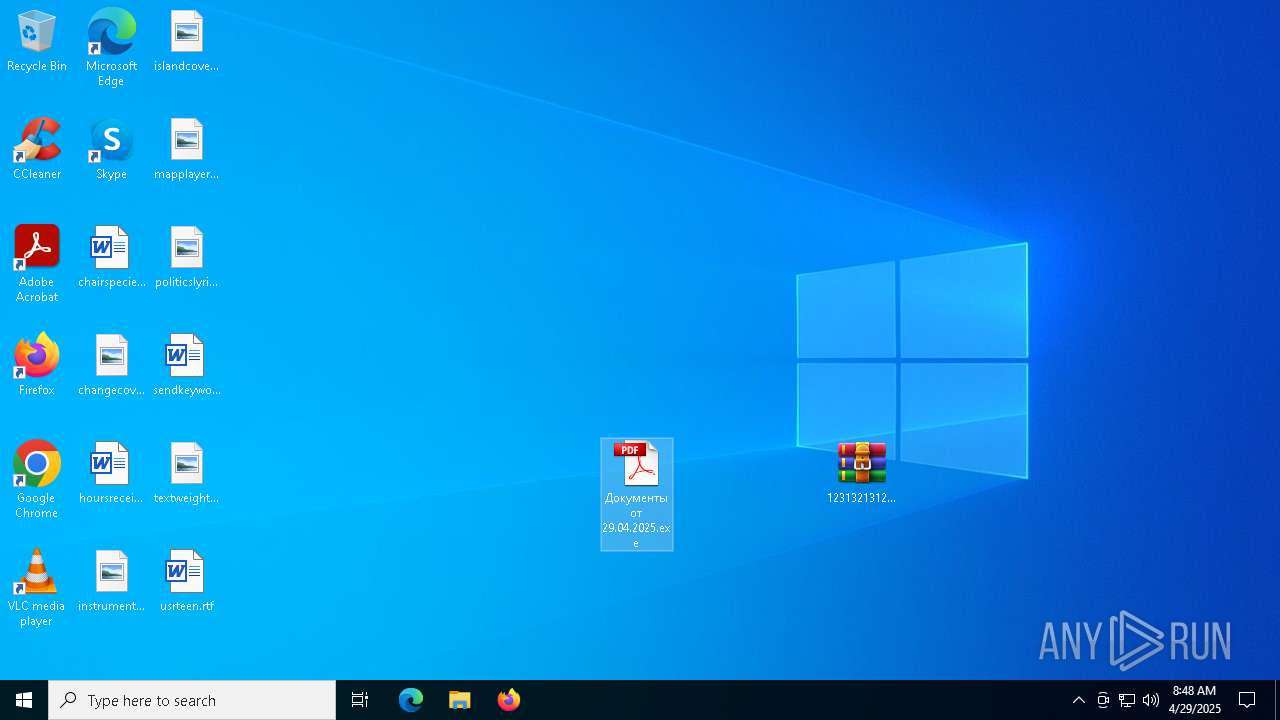
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1052 | "C:\Users\admin\Desktop\Документы от 29.04.2025.exe" | C:\Users\admin\Desktop\Документы от 29.04.2025.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3762504530 Modules
| |||||||||||||||
| 2148 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Exit code: 0 Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4212 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4756 | "C:\WINDOWS\System32\SLUI.exe" RuleId=3482d82e-ca2c-4e1f-8864-da0267b484b2;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=4de7cb65-cdf1-4de9-8ae8-e3cce27b9f2c;NotificationInterval=1440;Trigger=TimerEvent | C:\Windows\System32\slui.exe | SppExtComObj.Exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5668 | C:\WINDOWS\SysWOW64\WerFault.exe -u -p 1052 -s 1300 | C:\Windows\SysWOW64\WerFault.exe | — | Документы от 29.04.2025.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Problem Reporting Exit code: 0 Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6708 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\Downloads\fsdjfiaddisdjfoi.7z | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 6712 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Desktop\1231321312fsdfsd.rar" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
Total events
5 295
Read events
5 257
Write events
38
Delete events
0
Modification events
| (PID) Process: | (6708) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (6708) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (6708) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (6708) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Downloads\fsdjfiaddisdjfoi.7z | |||
| (PID) Process: | (6708) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (6708) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (6708) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (6708) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
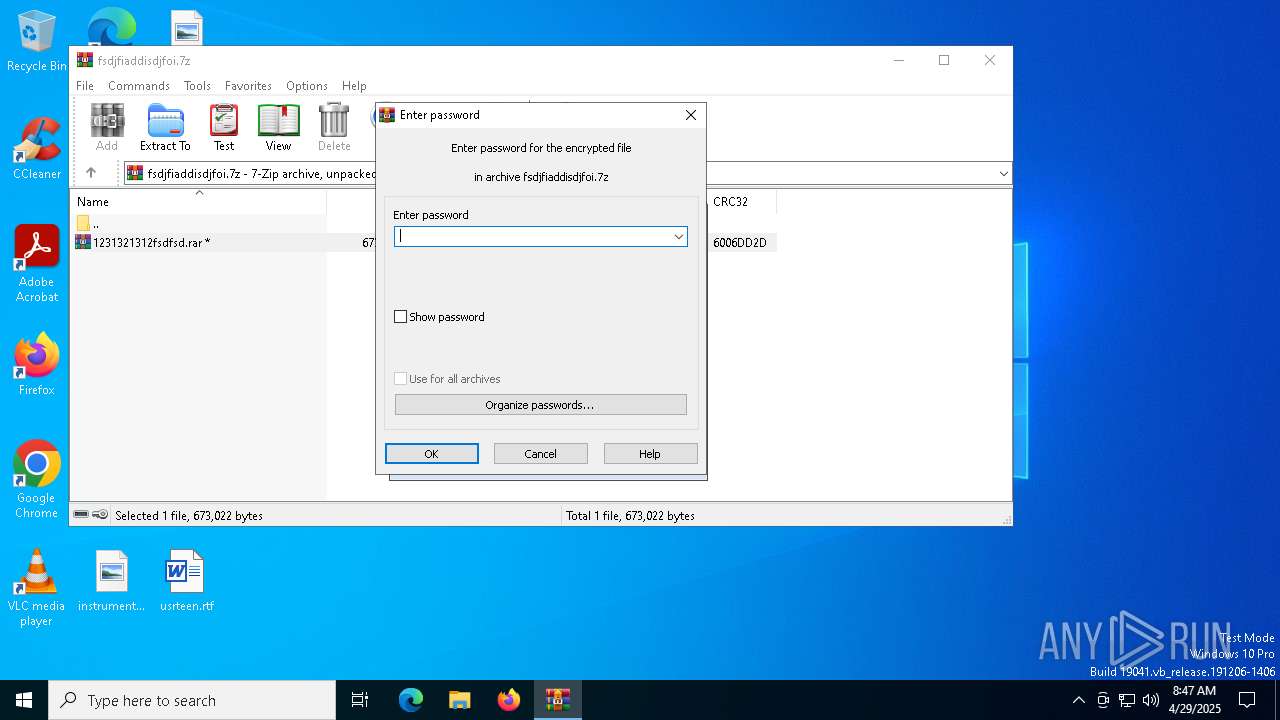
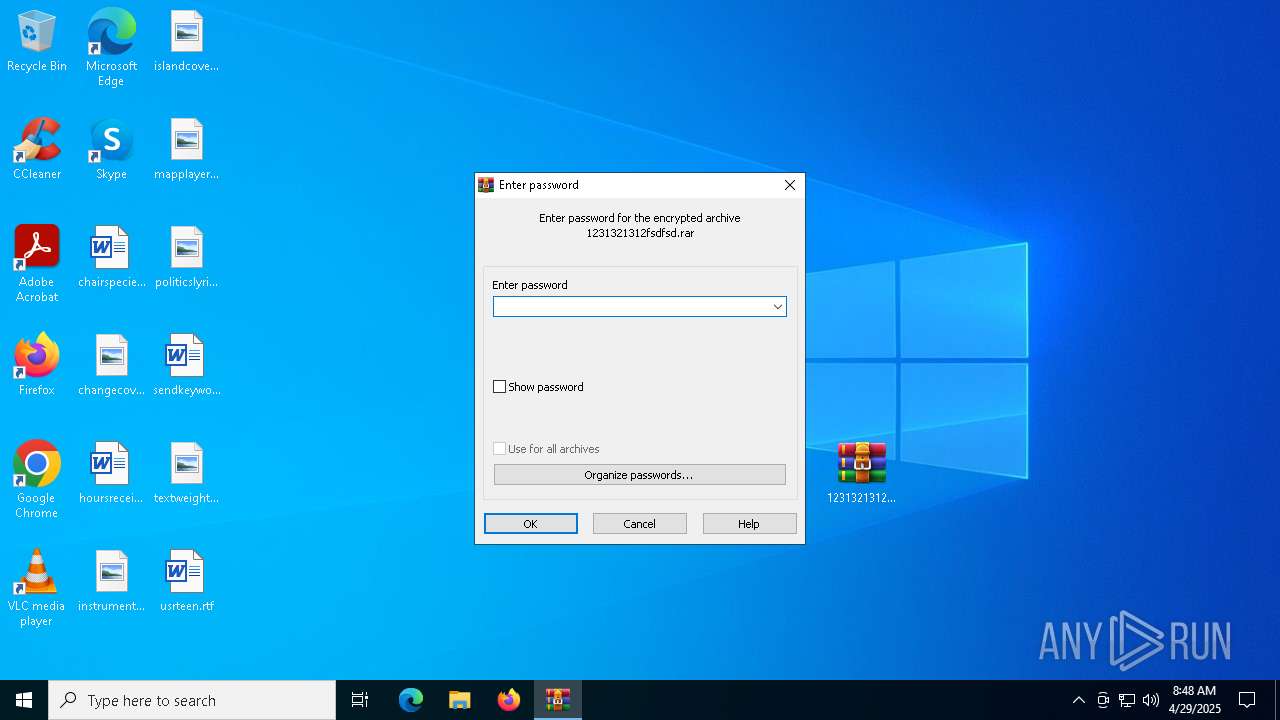
| (PID) Process: | (6708) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
| (PID) Process: | (6708) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\ArcColumnWidths |
| Operation: | write | Name: | name |
Value: 256 | |||
Executable files
1
Suspicious files
3
Text files
1
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5668 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\ReportQueue\AppCrash_ADVVZV3XZWT4XRMQ_2bc37148df531a393affca896f7cdda810f14380_c3ac41ce_0f5b927e-16eb-4937-8ea3-6a4c4a689016\Report.wer | — | |
MD5:— | SHA256:— | |||
| 5668 | WerFault.exe | C:\Users\admin\AppData\Local\CrashDumps\Документы от 29.04.2025.exe.1052.dmp | — | |
MD5:— | SHA256:— | |||
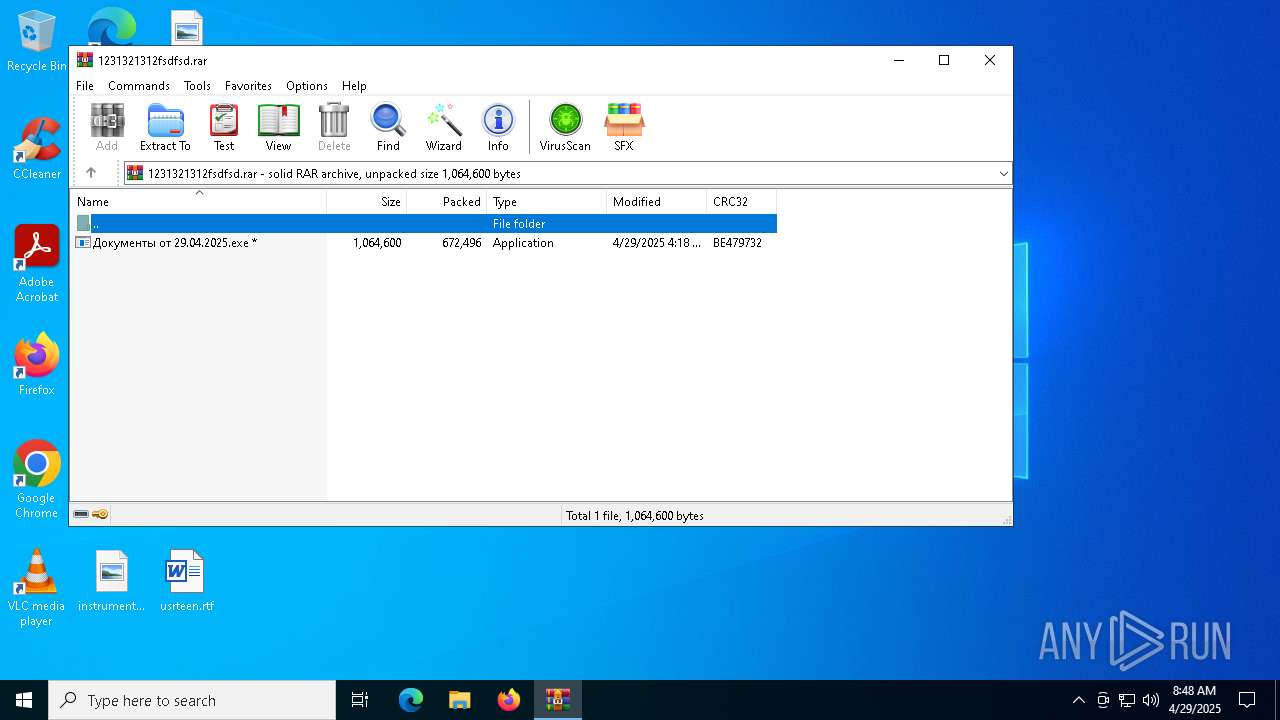
| 6708 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb6708.28956\1231321312fsdfsd.rar | compressed | |
MD5:91E85F333CE0A8547F438C98F158E685 | SHA256:4B884EF88B610061F154FA7E98F49FE708F8A6646CA00A002E441AF4033E7F98 | |||
| 5668 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\Temp\WER8CBC.tmp.dmp | binary | |
MD5:7D4F234FEF12C0E861237EA7887C21C5 | SHA256:29769F36E17EED234784722F1E4C1D9E9C93471240228765812B3CBF4B8CBDFF | |||
| 6712 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb6712.30796\Документы от 29.04.2025.exe | executable | |
MD5:692D6023668B811FC67ECDE3E521253E | SHA256:8C92DDB704BBC6FC2E1070D3BC26C1E0AEB2D12F26DE1113A9168EE461BB1E6A | |||
| 5668 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\Temp\WER8E74.tmp.xml | xml | |
MD5:BDE56B7531F191C231134FC17F107DE0 | SHA256:E5F61EAA4F417A69A79B603906ED4EF07750650B4EC3BE701663036DCA0B8848 | |||
| 5668 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\Temp\WER8E44.tmp.WERInternalMetadata.xml | binary | |
MD5:AFE40ED1FBAADDC24847C10F18E2BDB3 | SHA256:15AD93E5B8A0F296177F3E8E191B153226FCCFC3C45CC78F310DA719604D0213 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
25
DNS requests
20
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 23.53.40.176:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | DE | binary | 825 b | whitelisted |
6544 | svchost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | binary | 471 b | whitelisted |
1228 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | NL | binary | 419 b | whitelisted |
— | — | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | QA | binary | 868 b | whitelisted |
1228 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | NL | binary | 407 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2104 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 23.53.40.176:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
— | — | 2.23.246.101:80 | www.microsoft.com | Ooredoo Q.S.C. | QA | whitelisted |
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
3216 | svchost.exe | 172.211.123.250:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
6544 | svchost.exe | 40.126.32.72:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6544 | svchost.exe | 184.30.131.245:80 | ocsp.digicert.com | AKAMAI-AS | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
activation-v2.sls.microsoft.com |
| whitelisted |