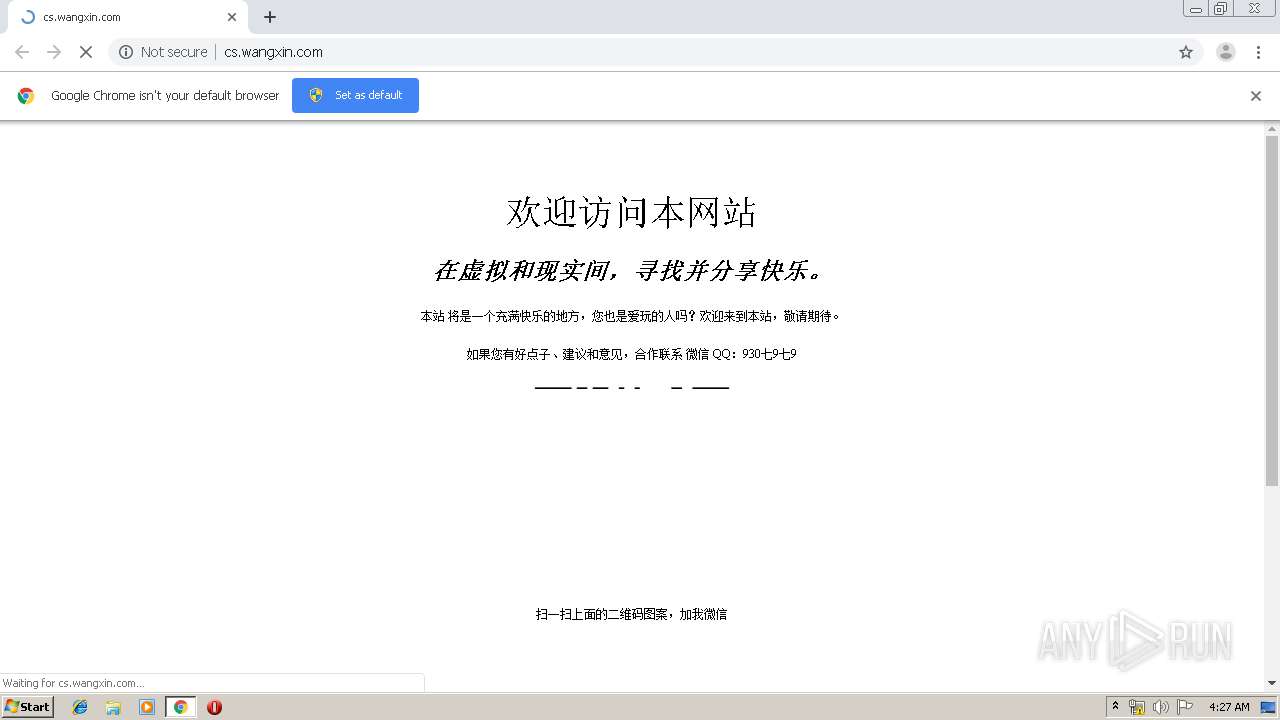
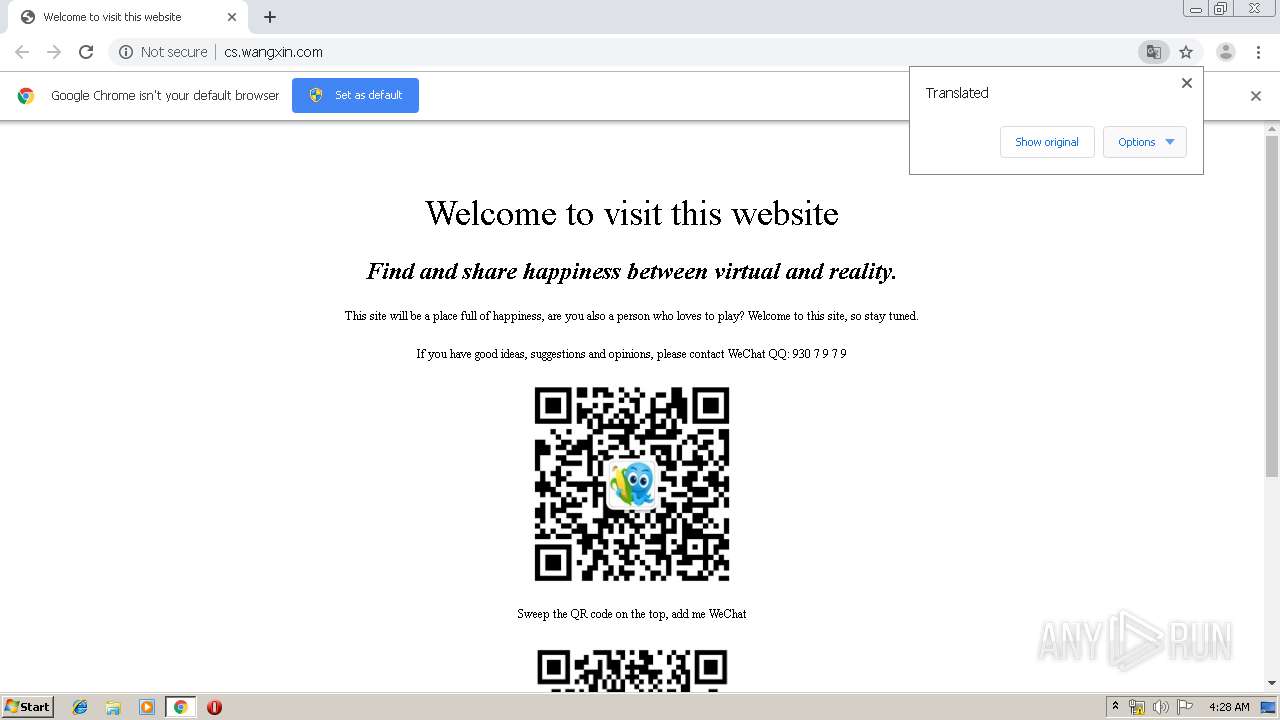
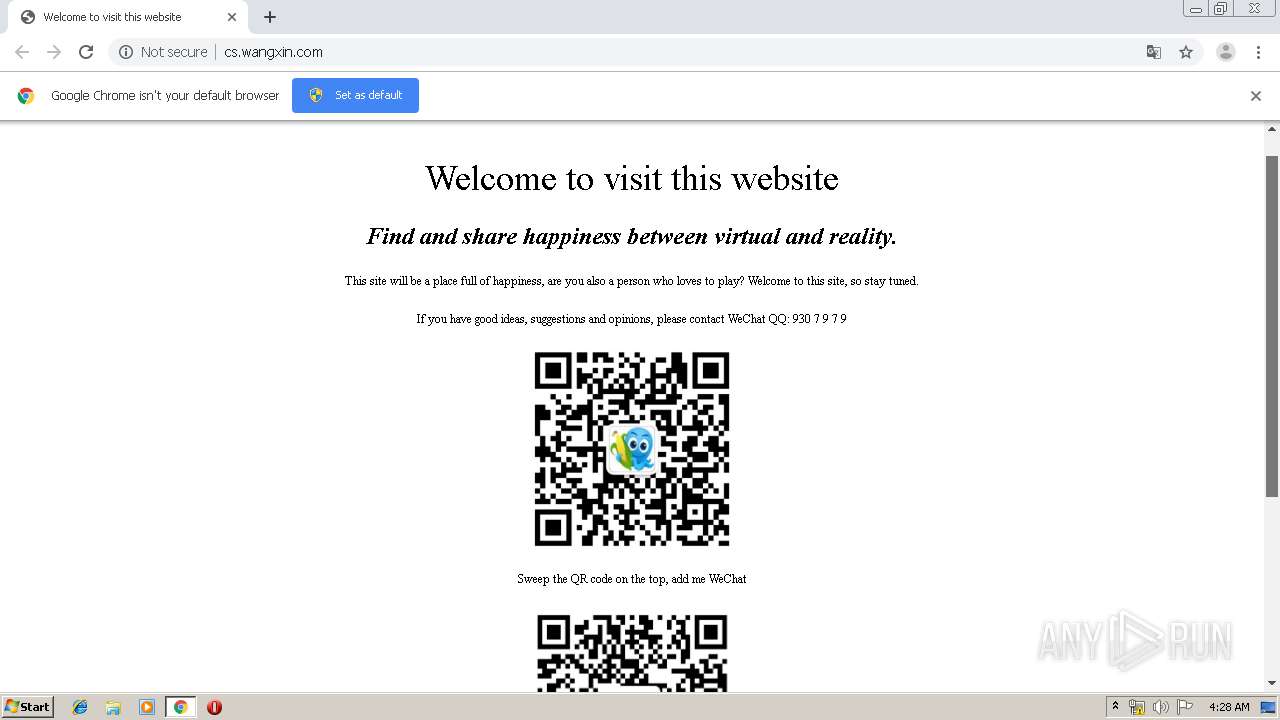
| URL: | http://cs.wangxin.com/ |
| Full analysis: | https://app.any.run/tasks/4be34b85-856f-40cc-9907-e2a7e1dd9d1e |
| Verdict: | Malicious activity |
| Analysis date: | July 18, 2019, 03:27:37 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 1649EDE0BB0B8AA740748850A84A0658 |
| SHA1: | 5175D51098F8D5EC346235B8DC76218D12F80A67 |
| SHA256: | 5D6481C167014470126C51E51F4AB95B19C3ADF02C5FAFB4BE0A694EB4FBB41E |
| SSDEEP: | 3:N1KdWmLMLZIK:CUmG2K |
MALICIOUS
No malicious indicators.SUSPICIOUS
Modifies files in Chrome extension folder
- chrome.exe (PID: 3772)
INFO
Creates files in the user directory
- chrome.exe (PID: 3772)
Application launched itself
- chrome.exe (PID: 3772)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
63
Monitored processes
29
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 804 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1020,15616831890248526632,3444700272354206935,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=9851295426465754888 --mojo-platform-channel-handle=3584 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 952 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=75.0.3770.100 --initial-client-data=0x7c,0x80,0x84,0x78,0x88,0x6f9ba9d0,0x6f9ba9e0,0x6f9ba9ec | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 988 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1020,15616831890248526632,3444700272354206935,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=17608294294469460607 --renderer-client-id=21 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1032 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1092 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1020,15616831890248526632,3444700272354206935,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=3487718754416189433 --mojo-platform-channel-handle=3472 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1160 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1020,15616831890248526632,3444700272354206935,131072 --enable-features=PasswordImport --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=16182951673067601114 --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2468 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1752 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=3776 --on-initialized-event-handle=312 --parent-handle=316 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1860 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1020,15616831890248526632,3444700272354206935,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=5208238633254868212 --mojo-platform-channel-handle=1036 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1940 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1020,15616831890248526632,3444700272354206935,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=16075564958837619605 --renderer-client-id=24 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3156 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2028 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1020,15616831890248526632,3444700272354206935,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=16168733259064223244 --mojo-platform-channel-handle=3808 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2064 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1020,15616831890248526632,3444700272354206935,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=9260784625613352839 --mojo-platform-channel-handle=3560 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
626
Read events
529
Write events
92
Delete events
5
Modification events
| (PID) Process: | (3772) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3772) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3772) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (3772) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3772) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (1752) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 3772-13207894073122375 |
Value: 259 | |||
| (PID) Process: | (3772) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3772) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3772) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 1512-13197841398593750 |
Value: 0 | |||
| (PID) Process: | (3772) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
0
Suspicious files
14
Text files
141
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3772 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\c038e87c-b352-4697-98d4-2e3ca4b10c52.tmp | — | |
MD5:— | SHA256:— | |||
| 3772 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000020.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3772 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\AvailabilityDB\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3772 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3772 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3772 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\EventDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3772 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RFdfa10.TMP | text | |
MD5:— | SHA256:— | |||
| 3772 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 3772 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3772 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
31
TCP/UDP connections
29
DNS requests
19
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3104 | chrome.exe | GET | 200 | 183.131.207.66:80 | http://ia.51.la/go1?id=2475175&rt=1563420476486&rl=1280*720&lang=en-US&ct=unknow&pf=1&ins=1&vd=1&ce=1&cd=24&ds=&ing=1&ekc=&sid=1563420476486&tt=%25E6%25AC%25A2%25E8%25BF%258E%25E8%25AE%25BF%25E9%2597%25AE%25E6%259C%25AC%25E7%25BD%2591%25E7%25AB%2599&kw=&cu=http%253A%252F%252Fcs.wangxin.com%252F&pu= | CN | — | — | whitelisted |
3104 | chrome.exe | GET | 204 | 172.217.16.174:80 | http://translate.google.com/gen204?nca=te_li&client=te_lib&logld=vTE_20190506_00 | US | — | — | whitelisted |
3104 | chrome.exe | GET | 204 | 172.217.16.174:80 | http://translate.google.com/gen204?sl=zh-CN&tl=en&textlen=7&sp=nmt&ttt=63&ttl=161&ttf=24&sr=1&nca=te_time&client=te_lib&logld=vTE_20190506_00 | US | — | — | whitelisted |
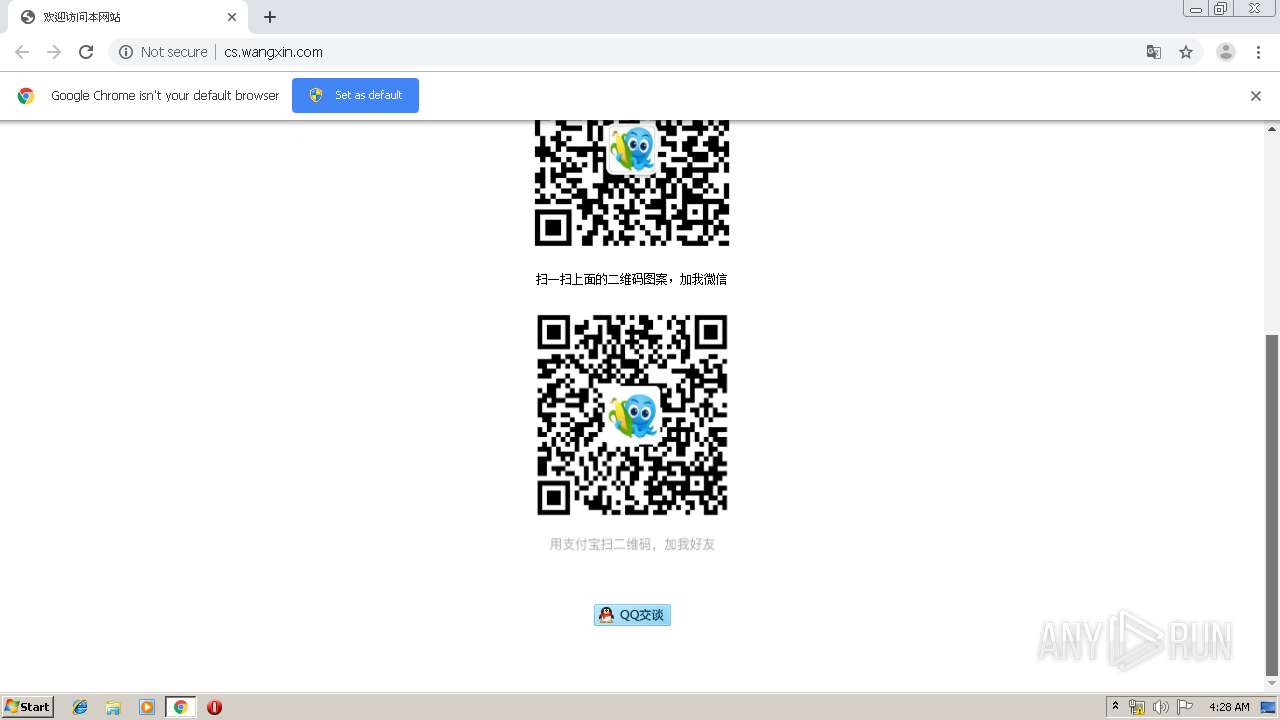
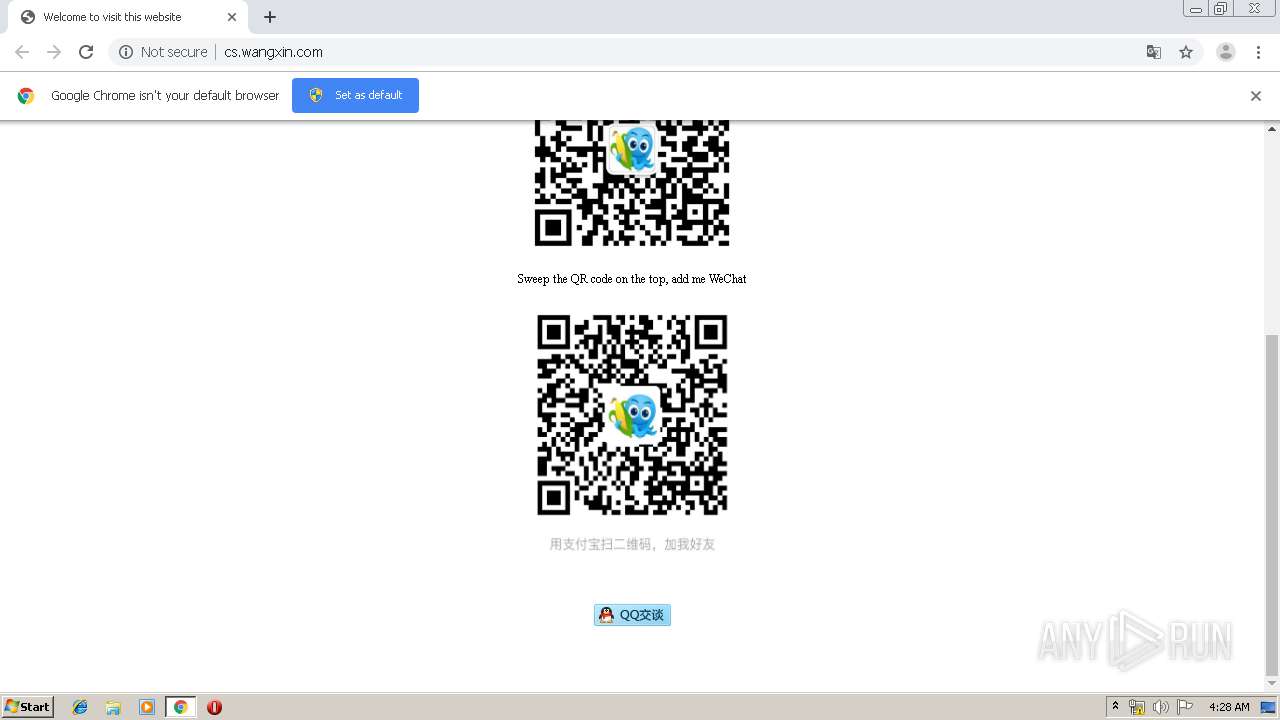
3104 | chrome.exe | GET | 200 | 182.61.186.59:80 | http://cs.wangxin.com/weixin.jpg | CN | image | 87.6 Kb | unknown |
3104 | chrome.exe | GET | 200 | 182.61.186.59:80 | http://cs.wangxin.com/ | CN | html | 1.78 Kb | unknown |
3104 | chrome.exe | GET | 200 | 220.242.140.187:80 | http://js.users.51.la/2475175.js | CN | text | 2.29 Kb | whitelisted |
3104 | chrome.exe | GET | 200 | 182.61.186.59:80 | http://cs.wangxin.com/alipaywxj.png | CN | image | 78.7 Kb | unknown |
3104 | chrome.exe | GET | 404 | 182.61.186.59:80 | http://cs.wangxin.com/favicon.ico | CN | html | 1.36 Kb | unknown |
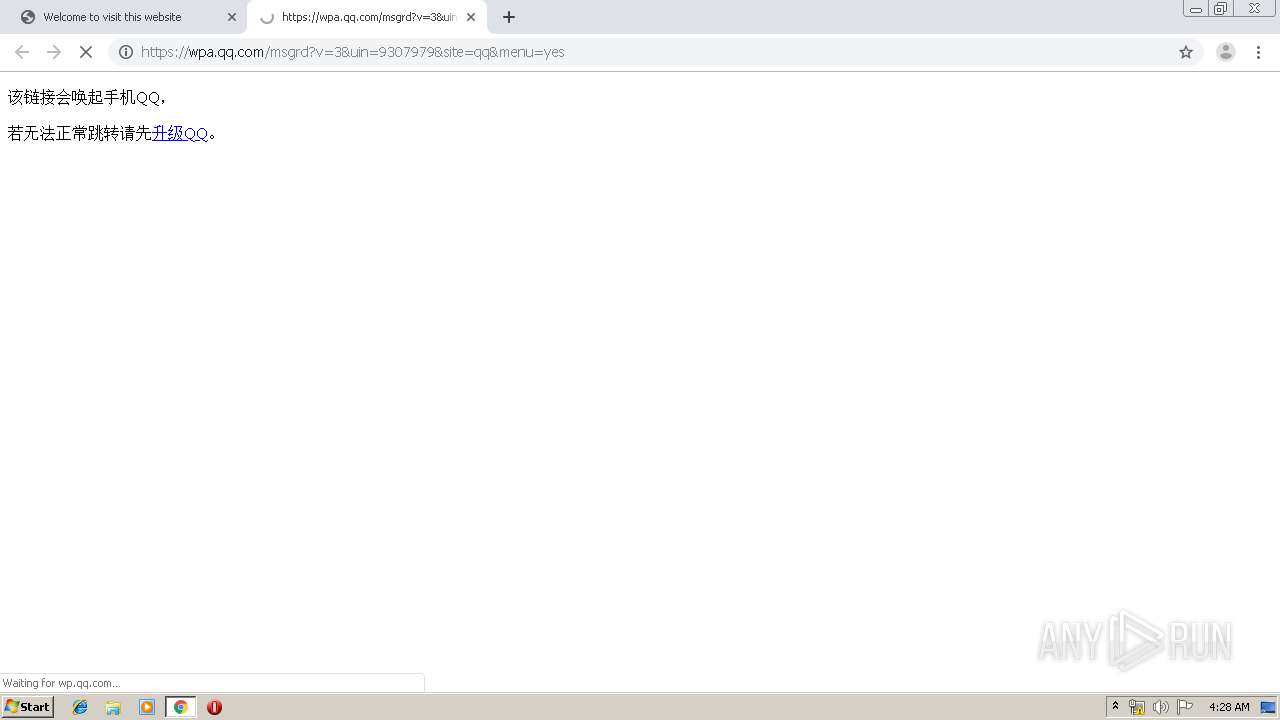
3104 | chrome.exe | GET | 301 | 58.251.100.24:80 | http://wp.qq.com/cgi-bin/api_attr?id=2&SigT=9243c0b348201953ec1b76004a765cfbf514340a30279b903d60b9216749a913e449a17e0a6f080f363d05d8277a5206 | CN | html | 193 b | whitelisted |
3104 | chrome.exe | GET | 200 | 203.205.151.21:80 | http://cgi.connect.qq.com/report/wpa/report?strValue=9307979&nValue=10582&tag=0&t=1563420507902 | CN | text | 21 b | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3104 | chrome.exe | 182.61.186.59:80 | cs.wangxin.com | Beijing Baidu Netcom Science and Technology Co., Ltd. | CN | unknown |
— | — | 220.242.140.187:80 | js.users.51.la | — | CN | suspicious |
3104 | chrome.exe | 58.251.100.24:443 | wpa.qq.com | China Unicom Shenzen network | CN | suspicious |
3104 | chrome.exe | 172.217.23.138:443 | translate.googleapis.com | Google Inc. | US | whitelisted |
3104 | chrome.exe | 183.131.207.66:80 | ia.51.la | DaLi | CN | malicious |
3104 | chrome.exe | 203.205.138.19:80 | pub.idqqimg.com | Tencent Building, Kejizhongyi Avenue | CN | unknown |
3104 | chrome.exe | 172.217.18.100:443 | www.google.com | Google Inc. | US | whitelisted |
3104 | chrome.exe | 58.251.100.24:80 | wpa.qq.com | China Unicom Shenzen network | CN | suspicious |
3104 | chrome.exe | 173.194.188.169:80 | r4---sn-4g5edns6.gvt1.com | Google Inc. | US | whitelisted |
3104 | chrome.exe | 216.58.206.3:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
cs.wangxin.com |
| unknown |
accounts.google.com |
| shared |
js.users.51.la |
| whitelisted |
wpa.qq.com |
| whitelisted |
ia.51.la |
| whitelisted |
translate.googleapis.com |
| whitelisted |
pub.idqqimg.com |
| suspicious |
www.google.com |
| malicious |
clients2.google.com |
| whitelisted |