| File name: | Swatbot.exe |
| Full analysis: | https://app.any.run/tasks/d977de79-52b3-4cd4-8002-a22d3d31e5c2 |
| Verdict: | Malicious activity |
| Analysis date: | April 22, 2025, 20:49:03 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386 (stripped to external PDB), for MS Windows, 4 sections |
| MD5: | 0574BF766E6CD055AE3149B8C245F76A |
| SHA1: | B9F6D623805D13AE58DF1B8E662DF2B49119BB3F |
| SHA256: | 5D5203454ADA7D8A680B29971BB2C54DC02150F1EF2984AEF63B3B31547B55CD |
| SSDEEP: | 1536:K9Lxbiq4ZmIAC9yT2ysr6pzuXHhAMMrtqx//WP:K9LJivZm15T2yy6BuXd7xWP |
MALICIOUS
Changes Windows Defender settings
- SystemAntiMalware.exe (PID: 7224)
Bypass execution policy to execute commands
- powershell.exe (PID: 7476)
- powershell.exe (PID: 8036)
- powershell.exe (PID: 7176)
- powershell.exe (PID: 5988)
Changes powershell execution policy (Bypass)
- SystemAntiMalware.exe (PID: 7224)
Adds path to the Windows Defender exclusion list
- SystemAntiMalware.exe (PID: 7224)
Adds process to the Windows Defender exclusion list
- SystemAntiMalware.exe (PID: 7224)
Uses Task Scheduler to run other applications
- SystemAntiMalware.exe (PID: 7224)
Changes the autorun value in the registry
- SystemAntiMalware.exe (PID: 7224)
Create files in the Startup directory
- SystemAntiMalware.exe (PID: 7224)
SUSPICIOUS
BASE64 encoded PowerShell command has been detected
- Swatbot.exe (PID: 2136)
Starts POWERSHELL.EXE for commands execution
- Swatbot.exe (PID: 2136)
- SystemAntiMalware.exe (PID: 7224)
Base64-obfuscated command line is found
- Swatbot.exe (PID: 2136)
Reads security settings of Internet Explorer
- Swatbot.exe (PID: 2136)
- SystemAntiMalware.exe (PID: 7224)
Executable content was dropped or overwritten
- Swatbot.exe (PID: 2136)
Reads the date of Windows installation
- SystemAntiMalware.exe (PID: 7224)
Script adds exclusion path to Windows Defender
- SystemAntiMalware.exe (PID: 7224)
Script adds exclusion process to Windows Defender
- SystemAntiMalware.exe (PID: 7224)
Potential Corporate Privacy Violation
- svchost.exe (PID: 2196)
INFO
Process checks computer location settings
- Swatbot.exe (PID: 2136)
- SystemAntiMalware.exe (PID: 7224)
Checks supported languages
- Swatbot.exe (PID: 2136)
- SystemAntiMalware.exe (PID: 7224)
Reads the computer name
- Swatbot.exe (PID: 2136)
- SystemAntiMalware.exe (PID: 7224)
Reads the machine GUID from the registry
- SystemAntiMalware.exe (PID: 7224)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 7476)
- powershell.exe (PID: 5988)
- powershell.exe (PID: 8036)
- powershell.exe (PID: 7176)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 7476)
- powershell.exe (PID: 8036)
- powershell.exe (PID: 7176)
- powershell.exe (PID: 5988)
Creates files or folders in the user directory
- SystemAntiMalware.exe (PID: 7224)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (61.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (14.6) |
| .exe | | | Win32 Executable (generic) (10) |
| .exe | | | Win16/32 Executable Delphi generic (4.6) |
| .exe | | | Generic Win/DOS Executable (4.4) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 0000:00:00 00:00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, 32-bit, No debug |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 2048 |
| InitializedDataSize: | 70144 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1499 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Total processes
147
Monitored processes
18
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2136 | "C:\Users\admin\Desktop\Swatbot.exe" | C:\Users\admin\Desktop\Swatbot.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 2196 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2284 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4408 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | schtasks.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5156 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5892 | "C:\Windows\System32\schtasks.exe" /create /f /RL HIGHEST /sc minute /mo 1 /tn "SystemAntiMalware" /tr "C:\Users\admin\SystemAntiMalware.exe" | C:\Windows\System32\schtasks.exe | — | SystemAntiMalware.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Task Scheduler Configuration Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5988 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -ExecutionPolicy Bypass Add-MpPreference -ExclusionProcess 'SystemAntiMalware.exe' | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | SystemAntiMalware.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 3221225547 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6044 | "C:\Users\admin\Desktop\Swatbot.exe" | C:\Users\admin\Desktop\Swatbot.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
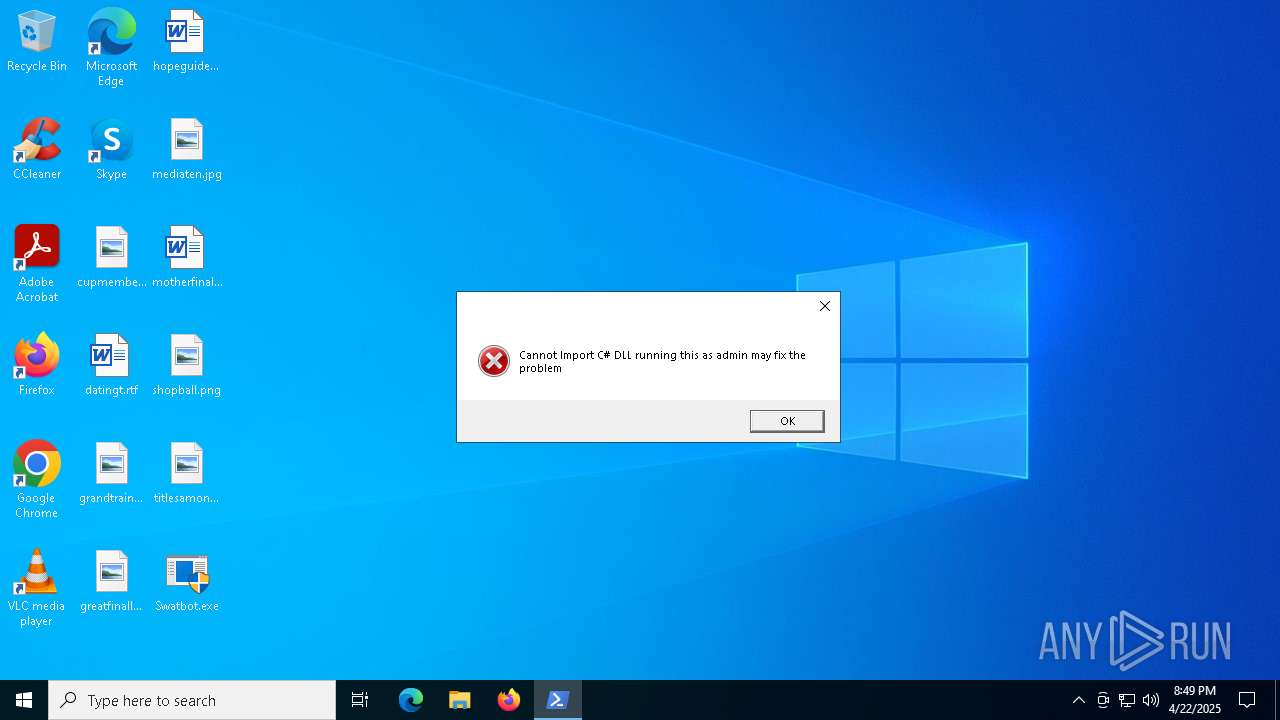
| 6516 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -EncodedCommand "PAAjAGgAbQBtACMAPgBBAGQAZAAtAFQAeQBwAGUAIAAtAEEAcwBzAGUAbQBiAGwAeQBOAGEAbQBlACAAUwB5AHMAdABlAG0ALgBXAGkAbgBkAG8AdwBzAC4ARgBvAHIAbQBzADsAPAAjAHgAdABtACMAPgBbAFMAeQBzAHQAZQBtAC4AVwBpAG4AZABvAHcAcwAuAEYAbwByAG0AcwAuAE0AZQBzAHMAYQBnAGUAQgBvAHgAXQA6ADoAUwBoAG8AdwAoACcAQwBhAG4AbgBvAHQAIABJAG0AcABvAHIAdAAgAEMAIwAgAEQATABMACAAcgB1AG4AbgBpAG4AZwAgAHQAaABpAHMAIABhAHMAIABhAGQAbQBpAG4AIABtAGEAeQAgAGYAaQB4ACAAdABoAGUAIABwAHIAbwBiAGwAZQBtACcALAAnACcALAAnAE8ASwAnACwAJwBFAHIAcgBvAHIAJwApADwAIwBrAHAAcwAjAD4A" | C:\Windows\SysWOW64\WindowsPowerShell\v1.0\powershell.exe | — | Swatbot.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7172 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
27 227
Read events
27 226
Write events
1
Delete events
0
Modification events
| (PID) Process: | (7224) SystemAntiMalware.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | SystemAntiMalware |
Value: C:\Users\admin\SystemAntiMalware.exe | |||
Executable files
1
Suspicious files
3
Text files
10
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2136 | Swatbot.exe | C:\Users\admin\SystemAntiMalware.exe | executable | |
MD5:C6BDF97E229CEEA82E8C0F4A76163778 | SHA256:BC9755F4AA4E6B30C62B4C729A7ACBFF1438DBFD0E2639E87C7092706A3E3A2D | |||
| 8036 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_3sx45pfc.5rj.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 6516 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_or5fkytu.p23.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 7176 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_wnfzeynv.oc3.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 5988 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_vjdzo0ka.hcy.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 6516 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\ModuleAnalysisCache | binary | |
MD5:8B8A832FCE2174C8FEE26B70F2483FBB | SHA256:0FBA3A37EF443507F533A7C3F31C0B5826EA416B95FDE43479E02D4E0C29400B | |||
| 5988 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_ymkjheme.0gs.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 7224 | SystemAntiMalware.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup\SystemAntiMalware.lnk | binary | |
MD5:AE89123B6B45B5075506449F5146921F | SHA256:9E7607BF171926C7E2F5D4D4FD5063C91B1FC467686FD11F93C9708CD0111B6C | |||
| 6516 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_u3nfefgz.jjg.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 8036 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_ecjcjvwt.wqz.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
18
DNS requests
13
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 88.221.110.114:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 92.123.22.101:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 92.123.22.101:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
6032 | SIHClient.exe | GET | 200 | 23.219.150.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
6032 | SIHClient.exe | GET | 200 | 23.219.150.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 88.221.110.114:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
— | — | 92.123.22.101:80 | www.microsoft.com | AKAMAI-AS | AT | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
6544 | svchost.exe | 20.190.177.20:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
6544 | svchost.exe | 184.30.131.245:80 | ocsp.digicert.com | AKAMAI-AS | US | whitelisted |
2104 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6032 | SIHClient.exe | 52.149.20.212:443 | slscr.update.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6032 | SIHClient.exe | 23.219.150.101:80 | www.microsoft.com | AKAMAI-AS | CL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
cmon2347-35906.portmap.io |
| malicious |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2196 | svchost.exe | Potential Corporate Privacy Violation | ET INFO DNS Query to a Reverse Proxy Service Observed |
2196 | svchost.exe | Misc activity | ET INFO DNS Query for Port Mapping/Tunneling Service Domain (.portmap .io) |