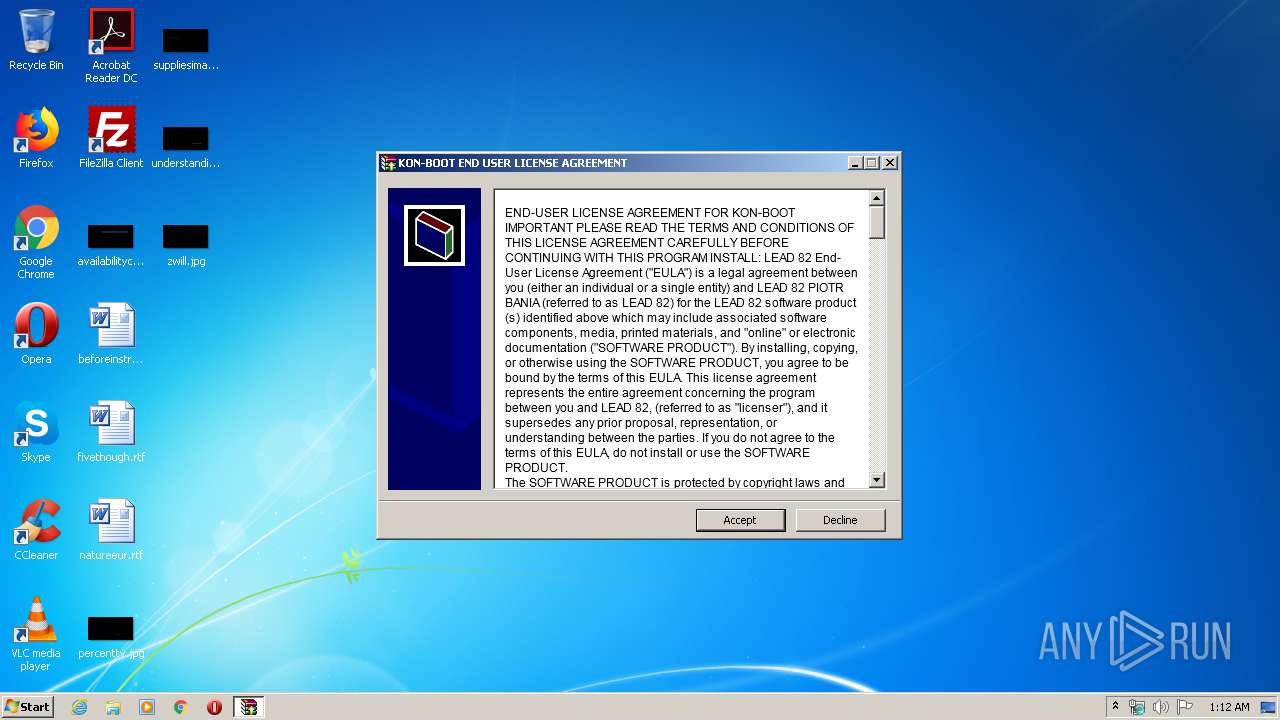
| File name: | konboot_2in1_3.3.exe |
| Full analysis: | https://app.any.run/tasks/6c7c5a96-d8dc-49c7-98ca-2d101060fc7e |
| Verdict: | Suspicious activity |
| Analysis date: | April 18, 2020, 00:12:26 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, RAR self-extracting archive |
| MD5: | ED3D2B96C4FA631655CCD94B0B7D8868 |
| SHA1: | 40D5C90F7955AB29AFA2D21BD87F530F6CD6D234 |
| SHA256: | 5D4236B4BDF4F9AC8B9E5373FD819371CC3A9BDA832B052DA85B7BDD86D51989 |
| SSDEEP: | 49152:30yJWbnBzbgamsNx9LX8SDDUrfkRZW+GtGUWm+ujus6uidltCDf+TZPdAxFob7c:30yEbBzEamsNTtDUsGtGnPs6LdSm1Wx1 |
MALICIOUS
Application was dropped or rewritten from another process
- KonBootInstaller.exe (PID: 2544)
SUSPICIOUS
Executable content was dropped or overwritten
- konboot_2in1_3.3.exe (PID: 3764)
Reads internet explorer settings
- konboot_2in1_3.3.exe (PID: 3764)
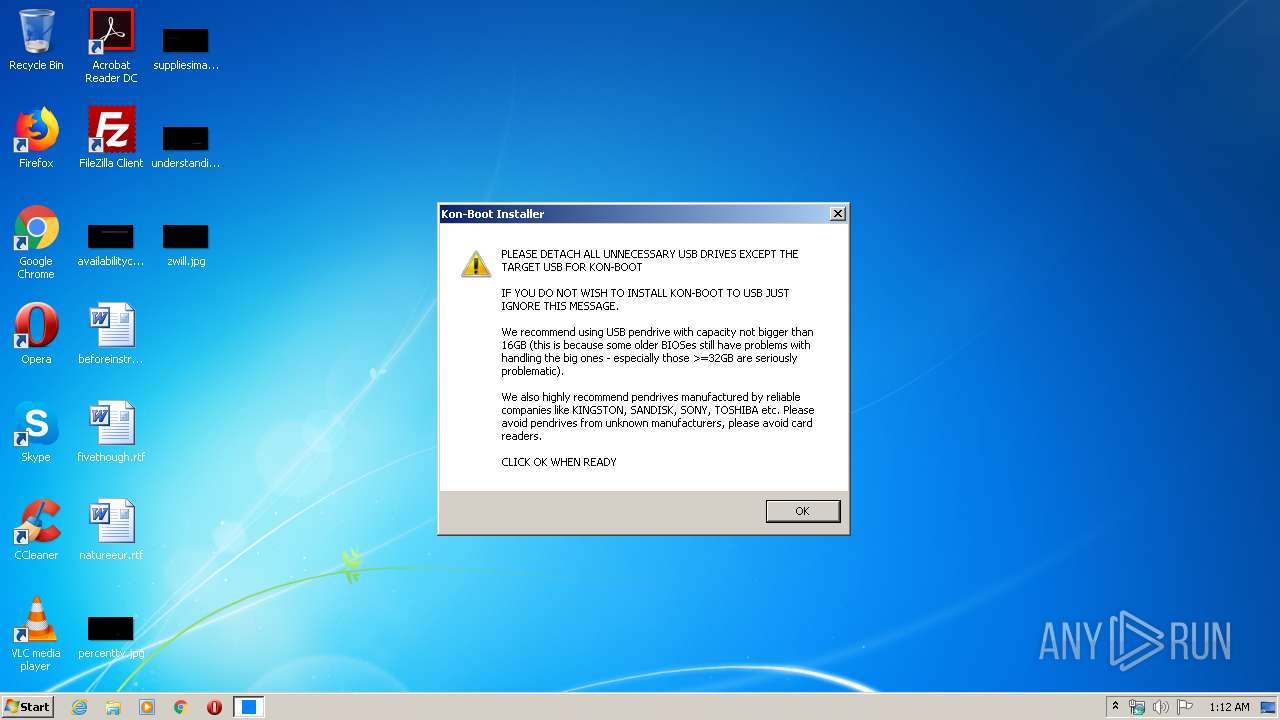
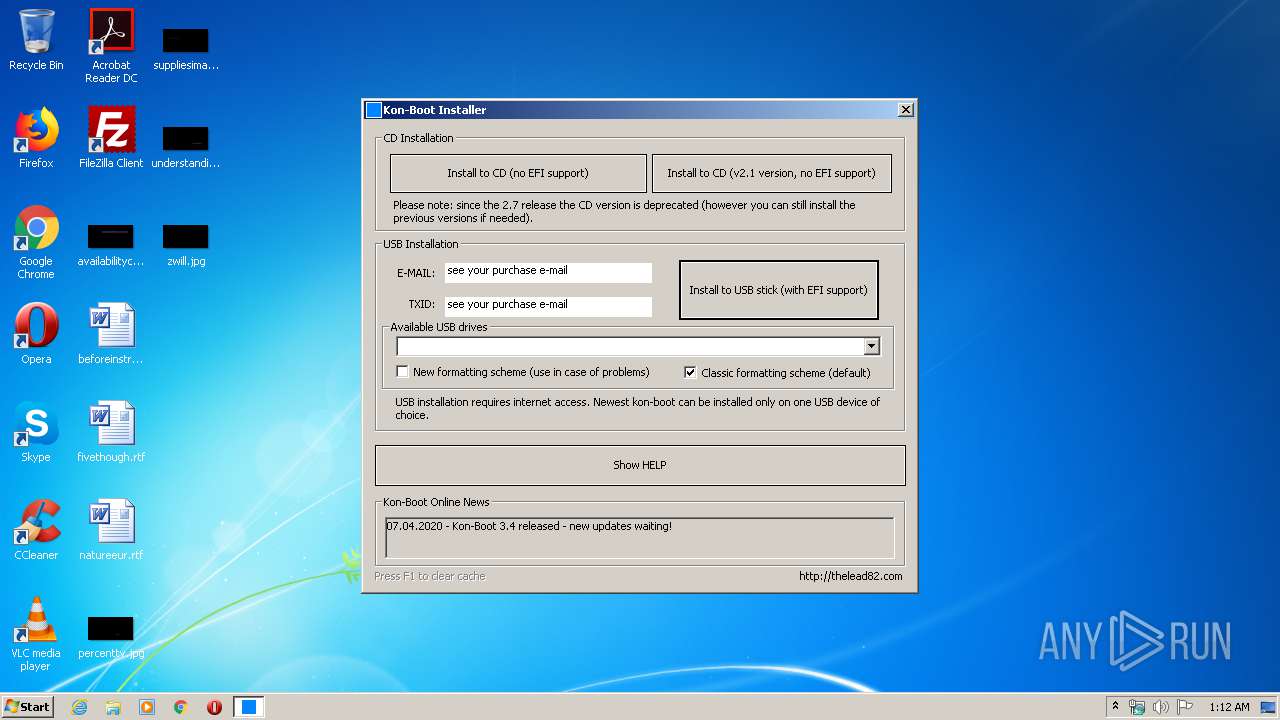
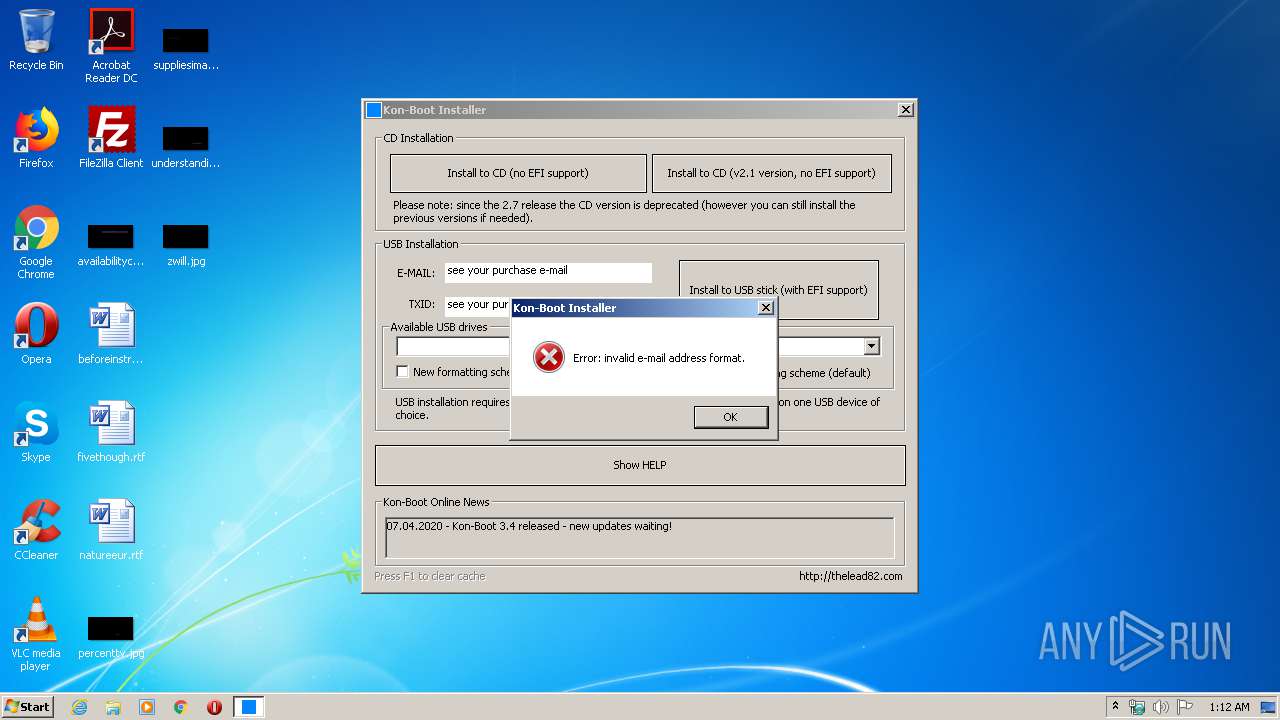
Uses NETSH.EXE for network configuration
- KonBootInstaller.exe (PID: 2544)
Reads Internet Cache Settings
- konboot_2in1_3.3.exe (PID: 3764)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2015:11:12 09:15:33+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 9 |
| CodeSize: | 166912 |
| InitializedDataSize: | 44544 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1da9b |
| OSVersion: | 5 |
| ImageVersion: | - |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 12-Nov-2015 08:15:33 |
| Detected languages: |
|
| Debug artifacts: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000E0 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 4 |
| Time date stamp: | 12-Nov-2015 08:15:33 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00028A64 | 0x00028C00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.71665 |
.rdata | 0x0002A000 | 0x000050D3 | 0x00005200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.34354 |
.data | 0x00030000 | 0x00021428 | 0x00001600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.46613 |
.rsrc | 0x00052000 | 0x00004554 | 0x00004600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.7995 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.26192 | 1875 | Latin 1 / Western European | English - United States | RT_MANIFEST |
2 | 3.88998 | 1384 | Latin 1 / Western European | English - United States | RT_ICON |
3 | 4.12176 | 744 | Latin 1 / Western European | English - United States | RT_ICON |
4 | 4.68705 | 2216 | Latin 1 / Western European | English - United States | RT_ICON |
7 | 3.1586 | 482 | Latin 1 / Western European | English - United States | RT_STRING |
8 | 3.11685 | 460 | Latin 1 / Western European | English - United States | RT_STRING |
9 | 3.15447 | 494 | Latin 1 / Western European | English - United States | RT_STRING |
10 | 2.99727 | 326 | Latin 1 / Western European | English - United States | RT_STRING |
11 | 3.2036 | 1094 | Latin 1 / Western European | English - United States | RT_STRING |
12 | 3.12889 | 358 | Latin 1 / Western European | English - United States | RT_STRING |
Imports
ADVAPI32.dll |
COMCTL32.dll |
COMDLG32.dll |
GDI32.dll |
KERNEL32.dll |
SHELL32.dll |
SHLWAPI.dll |
USER32.dll |
ole32.dll |
Total processes
45
Monitored processes
7
Malicious processes
0
Suspicious processes
1
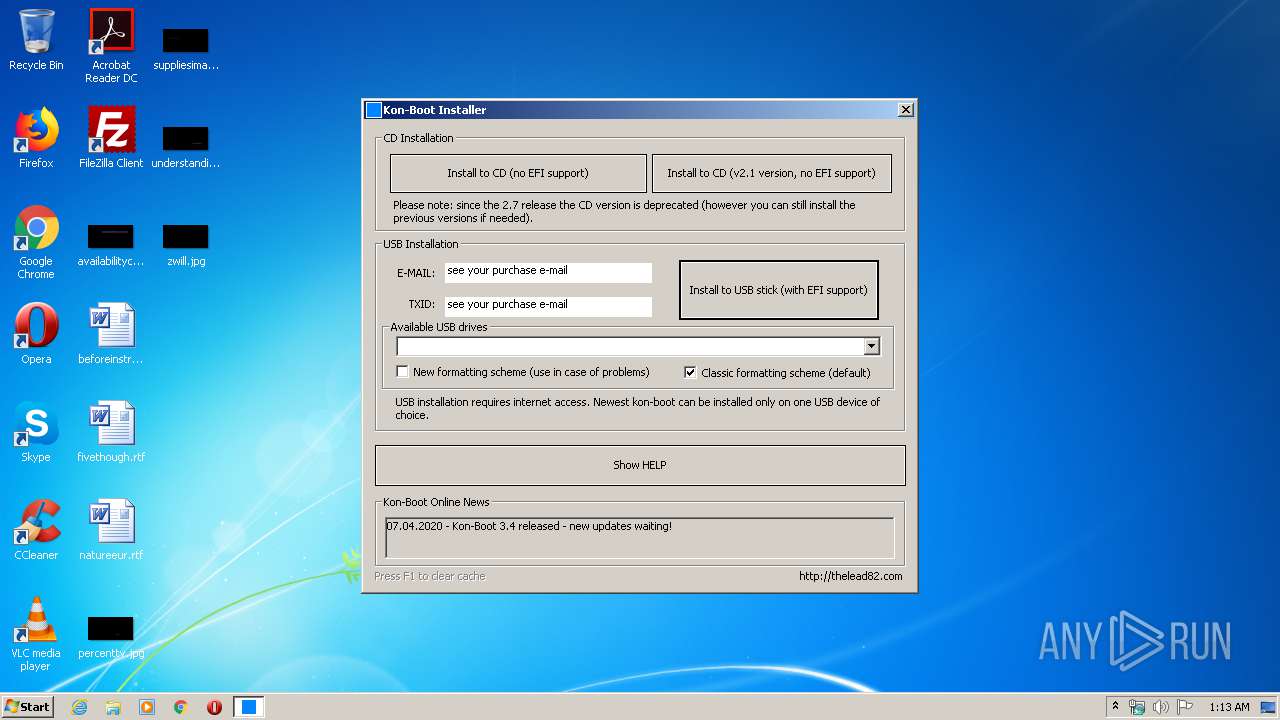
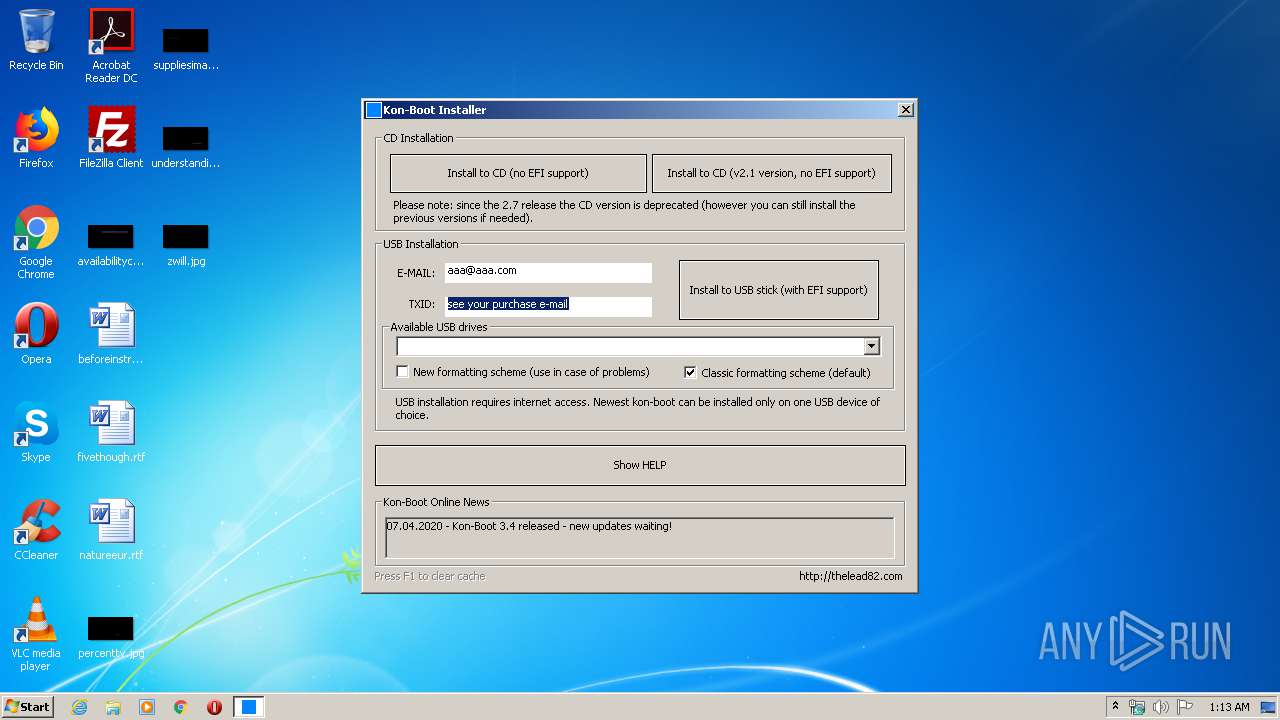
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
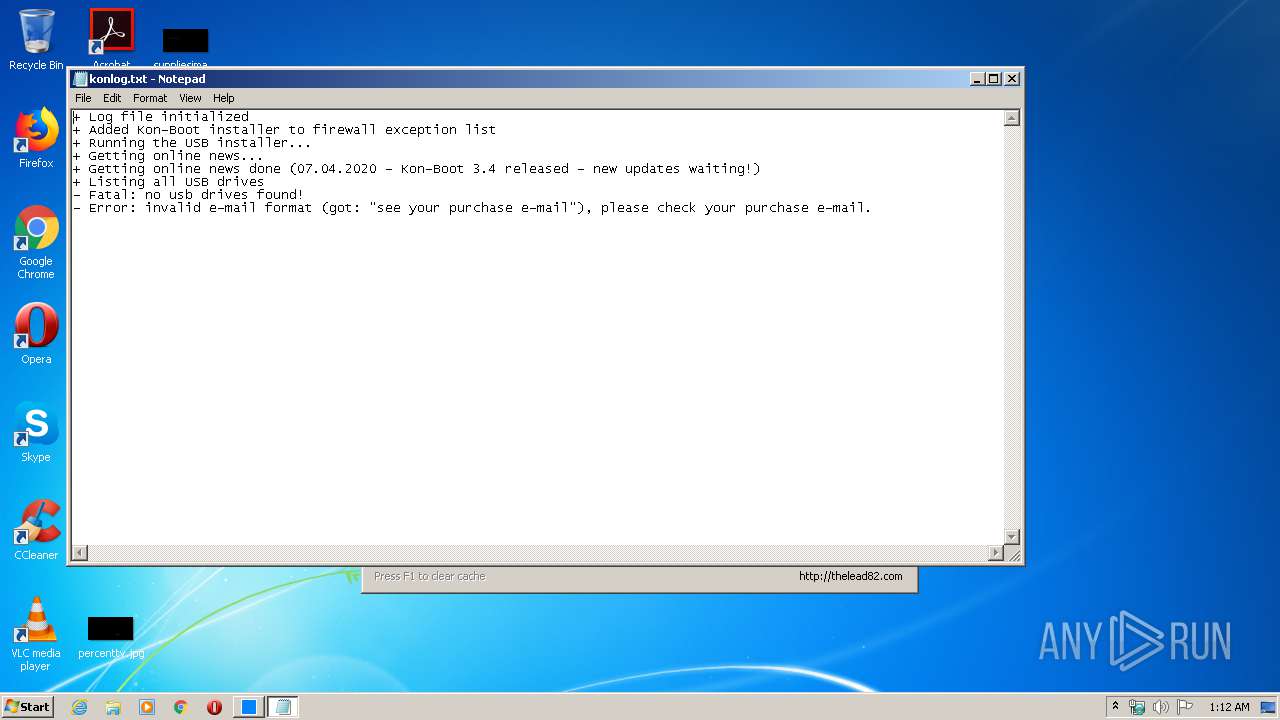
| 608 | "C:\Windows\System32\notepad.exe" konlog.txt | C:\Windows\System32\notepad.exe | — | KonBootInstaller.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Notepad Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1732 | netsh advfirewall firewall add rule name="Kon-Boot Installer" dir=out action=allow program="C:\kon-boot\KonBootInstaller.exe" enable=yes | C:\Windows\system32\netsh.exe | — | KonBootInstaller.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Network Command Shell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
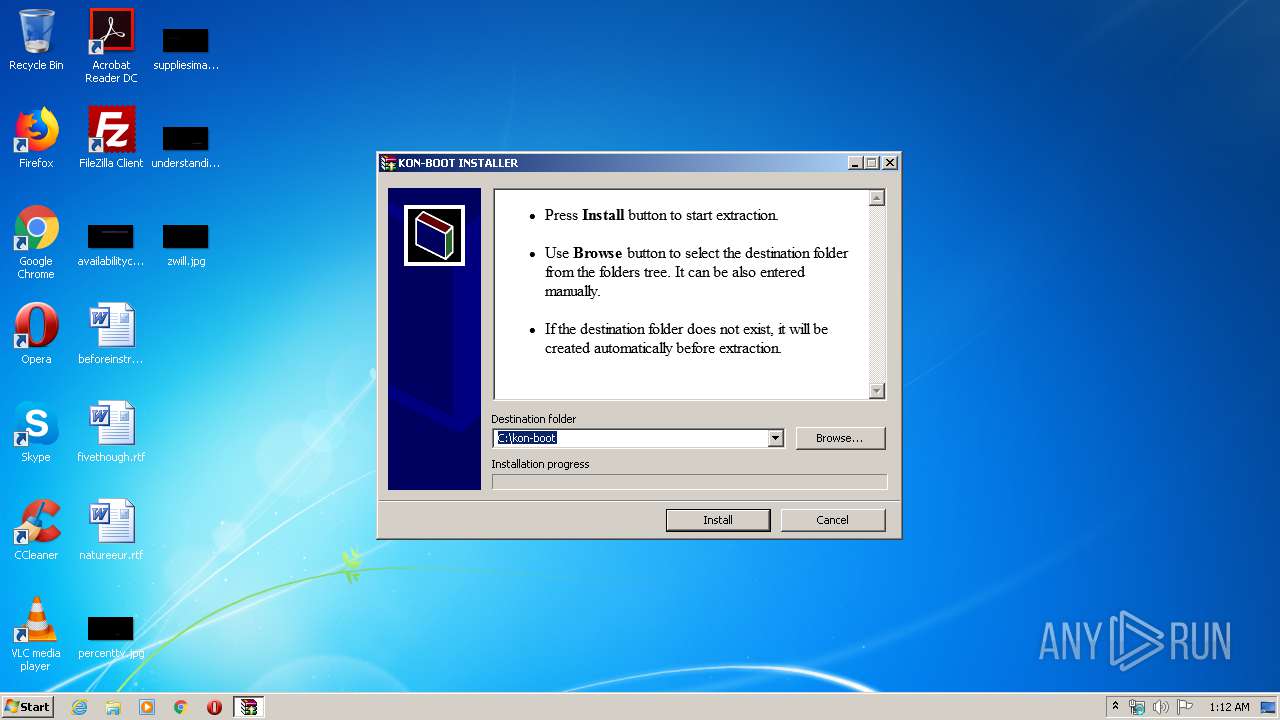
| 2544 | "C:\kon-boot\KonBootInstaller.exe" | C:\kon-boot\KonBootInstaller.exe | konboot_2in1_3.3.exe | ||||||||||||
User: admin Company: LEAD 82 - http://thelead82.com Integrity Level: HIGH Description: Kon-Boot Windows Installer Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
| 2572 | "C:\Users\admin\AppData\Local\Temp\konboot_2in1_3.3.exe" | C:\Users\admin\AppData\Local\Temp\konboot_2in1_3.3.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 2868 | netsh advfirewall firewall delete rule name="Kon-Boot Installer" | C:\Windows\system32\netsh.exe | — | KonBootInstaller.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Network Command Shell Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3620 | "C:\Windows\System32\notepad.exe" konlog.txt | C:\Windows\System32\notepad.exe | — | KonBootInstaller.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Notepad Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3764 | "C:\Users\admin\AppData\Local\Temp\konboot_2in1_3.3.exe" | C:\Users\admin\AppData\Local\Temp\konboot_2in1_3.3.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
Total events
324
Read events
209
Write events
115
Delete events
0
Modification events
| (PID) Process: | (3764) konboot_2in1_3.3.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3764) konboot_2in1_3.3.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3764) konboot_2in1_3.3.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (3764) konboot_2in1_3.3.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (3764) konboot_2in1_3.3.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2868) netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2868) netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\dhcpqec.dll,-100 |
Value: DHCP Quarantine Enforcement Client | |||
| (PID) Process: | (2868) netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\dhcpqec.dll,-101 |
Value: Provides DHCP based enforcement for NAP | |||
| (PID) Process: | (2868) netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\dhcpqec.dll,-103 |
Value: 1.0 | |||
| (PID) Process: | (2868) netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\dhcpqec.dll,-102 |
Value: Microsoft Corporation | |||
Executable files
14
Suspicious files
1
Text files
11
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3764 | konboot_2in1_3.3.exe | C:\kon-boot\kon-bootUSB\EFI\boot\bootMX64.efi | executable | |
MD5:37335FDDA8C92D31E8404D986121CF50 | SHA256:0B667FE6177740D9AE2C1957B949B1D25C79D867665FEEFB78A900F53E396366 | |||
| 3764 | konboot_2in1_3.3.exe | C:\kon-boot\kon-bootUSB\EFI\boot\bootia32.efi | executable | |
MD5:CA35843F20D6218219C4A5BB5AE39772 | SHA256:74B5D08F30239F12C266D67CEBF2C69F808A1D4E28F408D423A7E2464241AB7C | |||
| 3764 | konboot_2in1_3.3.exe | C:\kon-boot\kon-bootUSB\auto.ps1 | text | |
MD5:0811B1C1C8618A79F7448FC391BAAE09 | SHA256:C441DD8AA08E7BD7481A8F7A0907EF38562BC6E3E3A9C1183095F27DC08FA74F | |||
| 3764 | konboot_2in1_3.3.exe | C:\kon-boot\kon-bootUSB\README.txt | text | |
MD5:9DEFE5F30ED23B5E2F711FEF43D25C6D | SHA256:AC7AECE9B2709A695490E85E44BA6305FE49672F10B010C36E9E061076E96055 | |||
| 3764 | konboot_2in1_3.3.exe | C:\kon-boot\kon-bootUSB\EFI\boot\KonBootDxeX64.efi | executable | |
MD5:E14E28F4E83643553818ABE13BA08F65 | SHA256:6FBE364489FAA7152ACA61BC3F79BAF277391F7531A1A5C06E50445A18968BD9 | |||
| 3764 | konboot_2in1_3.3.exe | C:\kon-boot\kon-bootUSB\EFI\boot\bootx64.efi | executable | |
MD5:038D12877C20DFF9194745BDB41689AB | SHA256:3A253CED370CF28B0198BD35AF94B68B94C96E01D34C0833ACCB637828AAD11C | |||
| 3764 | konboot_2in1_3.3.exe | C:\kon-boot\kon-bootUSB\EFI\boot\bootWIA32.efi | executable | |
MD5:A1760F6809EED5DB6048BD35B6CFE573 | SHA256:72D9B027C211F18A7594F42DE5D44E8A927A0DFADFD7FDF9D8112260B06107EA | |||
| 3764 | konboot_2in1_3.3.exe | C:\kon-boot\kon-bootUSB\EFI\boot\bootWX64.efi | executable | |
MD5:F000F513C2BE29A8C7C7F5181FB93EE5 | SHA256:EAF08D53B08EFB80BABE163F1B1559751E3E53A86EBB8FDDECD5E187E819E147 | |||
| 3764 | konboot_2in1_3.3.exe | C:\kon-boot\kon-bootUSB\USBFILES\grldr | binary | |
MD5:6477737E9467FBC6DA2905E6277DAE62 | SHA256:2D000B88D510DE75E40DA75F0908BD3DCE56B6CCD59428781009D2779A821458 | |||
| 3764 | konboot_2in1_3.3.exe | C:\kon-boot\kon-bootUSB\EFI\boot\KonMacDxe.efi | executable | |
MD5:BD70EBEEA91C4B89B8EB0BB585AEB46F | SHA256:AE31EF5AC032354D87DFF3BEFD5FBA8C9086F5E6232FBAE9A2C628B966A3322C | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
3
DNS requests
2
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2544 | KonBootInstaller.exe | GET | 200 | 18.194.160.188:80 | http://thelead82.com/konboot_web_addr/konboot_centralS.txt | DE | text | 49 b | suspicious |
2544 | KonBootInstaller.exe | GET | 200 | 18.194.160.188:80 | http://thelead82.com/konboot_web_addr/konboot_centralS.txt | DE | text | 49 b | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2544 | KonBootInstaller.exe | 18.194.160.188:443 | kon-boot.com | Amazon.com, Inc. | DE | unknown |
2544 | KonBootInstaller.exe | 18.194.160.188:80 | kon-boot.com | Amazon.com, Inc. | DE | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
kon-boot.com |
| unknown |
thelead82.com |
| suspicious |