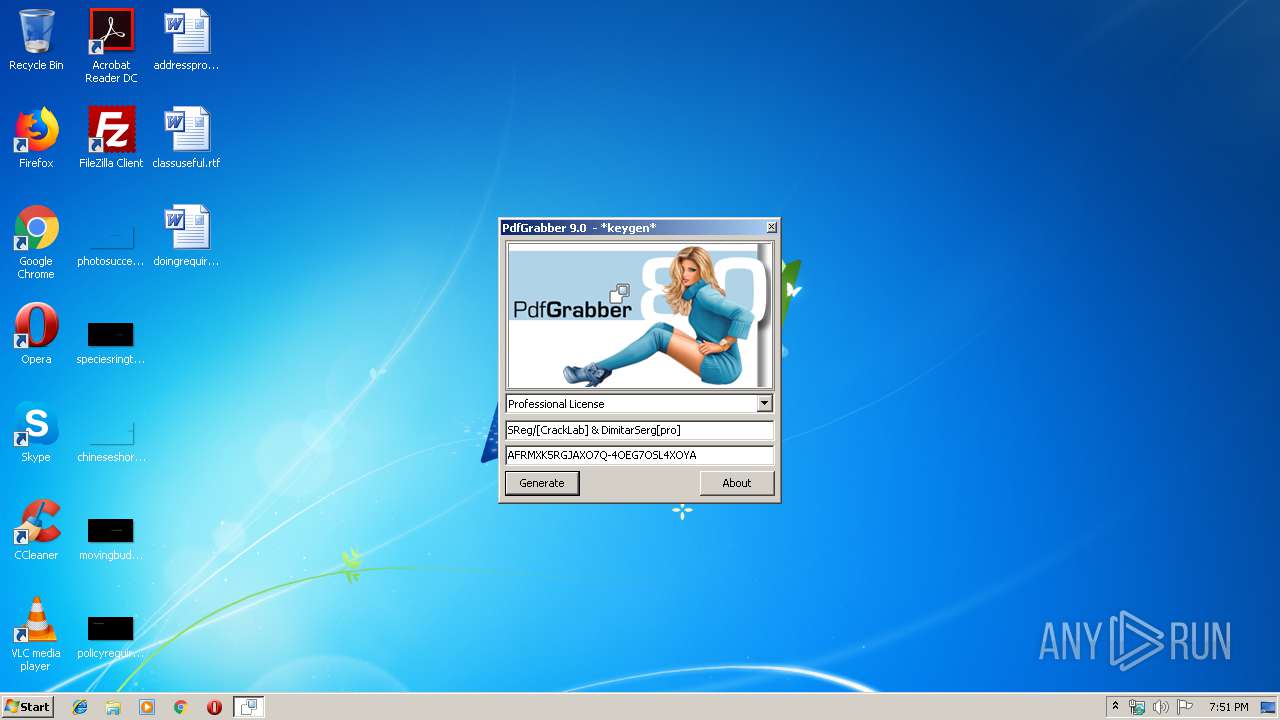
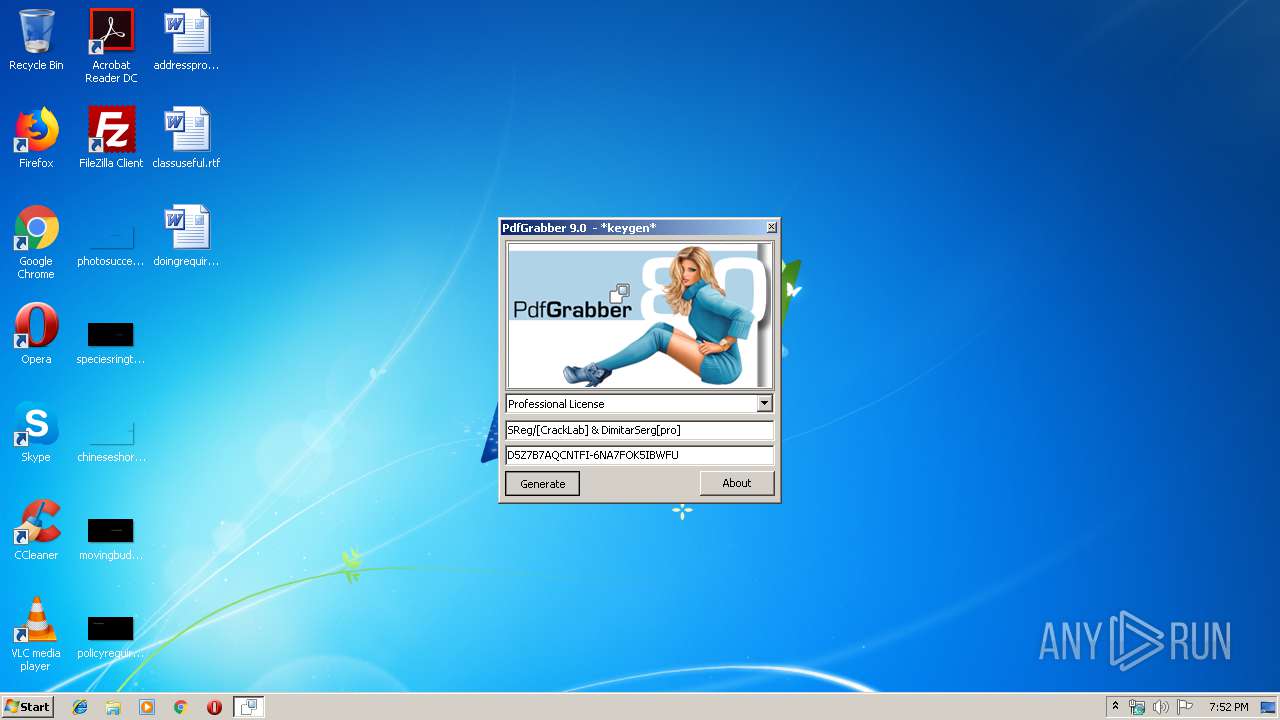
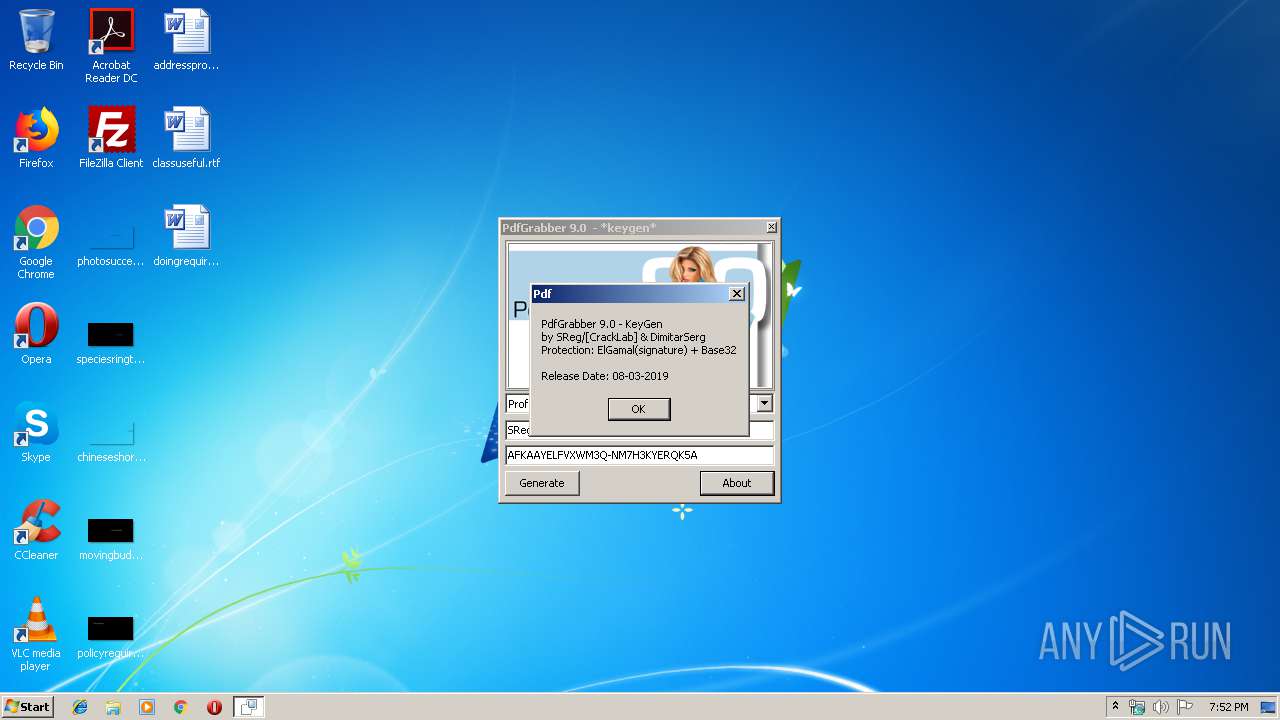
| File name: | Pdf.Grabber.v.9.kg.by.SReg.exe |
| Full analysis: | https://app.any.run/tasks/7838db8e-1ad8-4f24-b7c4-854e53ee48c4 |
| Verdict: | No threats detected |
| Analysis date: | September 26, 2019, 18:51:03 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 7E717522128C857C337FA7EBC2E2233E |
| SHA1: | C340A2CA9DD012735AE324430E9935B7452E6240 |
| SHA256: | 5D08EA283DEC809C032F0BD66EFB2CFD676C6205247723C2CE2C7D57969DB7AC |
| SSDEEP: | 24576:Gi6QTbxhthK+PBgWTn8+Qzu1BQZPaFEU9krXZYaUyJ3B1ruNBOUwWQhnvYD8/af:/hXR+u1OaFEUufJ3B1kBOqQhgDaa |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .scr | | | Windows screen saver (43.2) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (21.7) |
| .exe | | | Win32 Executable (generic) (14.8) |
| .exe | | | Win16/32 Executable Delphi generic (6.8) |
| .exe | | | Generic Win/DOS Executable (6.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2019:03:08 05:58:44+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 484352 |
| InitializedDataSize: | 193024 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x306057 |
| OSVersion: | 5 |
| ImageVersion: | - |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 08-Mar-2019 04:58:44 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0050 |
| Pages in file: | 0x0002 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x000F |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x001A |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 11 |
| Time date stamp: | 08-Mar-2019 04:58:44 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
Fyf=C[:\(Y\x07 | 0x00001000 | 0x00075928 | 0x00000000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 0 |
wHRrEYXo\x10\x08 | 0x00077000 | 0x00000810 | 0x00000000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 0 |
_O.UpZLu\x10i | 0x00078000 | 0x00006910 | 0x00000000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
_\0Ny(8(\xb4s\x01 | 0x0007F000 | 0x000173B4 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
7f+'B&TE\xce* | 0x00097000 | 0x00002ACE | 0x00000000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
5qceu.bG8 | 0x0009A000 | 0x00000038 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
bF0mlT+b\x18 | 0x0009B000 | 0x00000018 | 0x00000000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 0 |
xuw@q*:N | 0x0009C000 | 0x00117400 | 0x00000000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
[Qiu4HoF\xaek\x15 | 0x001B4000 | 0x00156BAE | 0x00156C00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.89525 |
Md/r7)H6\x08\x01 | 0x0030B000 | 0x00000108 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 3.05712 |
Imports
advapi32.dll |
comctl32.dll |
gdi32.dll |
kernel32.dll |
ole32.dll |
oleaut32.dll |
user32.dll |
version.dll |
winmm.dll |
Total processes
33
Monitored processes
1
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 3008 | "C:\Users\admin\AppData\Local\Temp\Pdf.Grabber.v.9.kg.by.SReg.exe" | C:\Users\admin\AppData\Local\Temp\Pdf.Grabber.v.9.kg.by.SReg.exe | — | explorer.exe | |||||||||||
User: admin Company: SReg/[CrackLab] Integrity Level: MEDIUM Description: PdfGrabber 9.0 - KeyGen by SReg/[CrackLab] & DimitarSerg Exit code: 3221225547 Version: 1.0.0.0 Modules
| |||||||||||||||
Total events
12
Read events
12
Write events
0
Delete events
0
Modification events
Executable files
0
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report