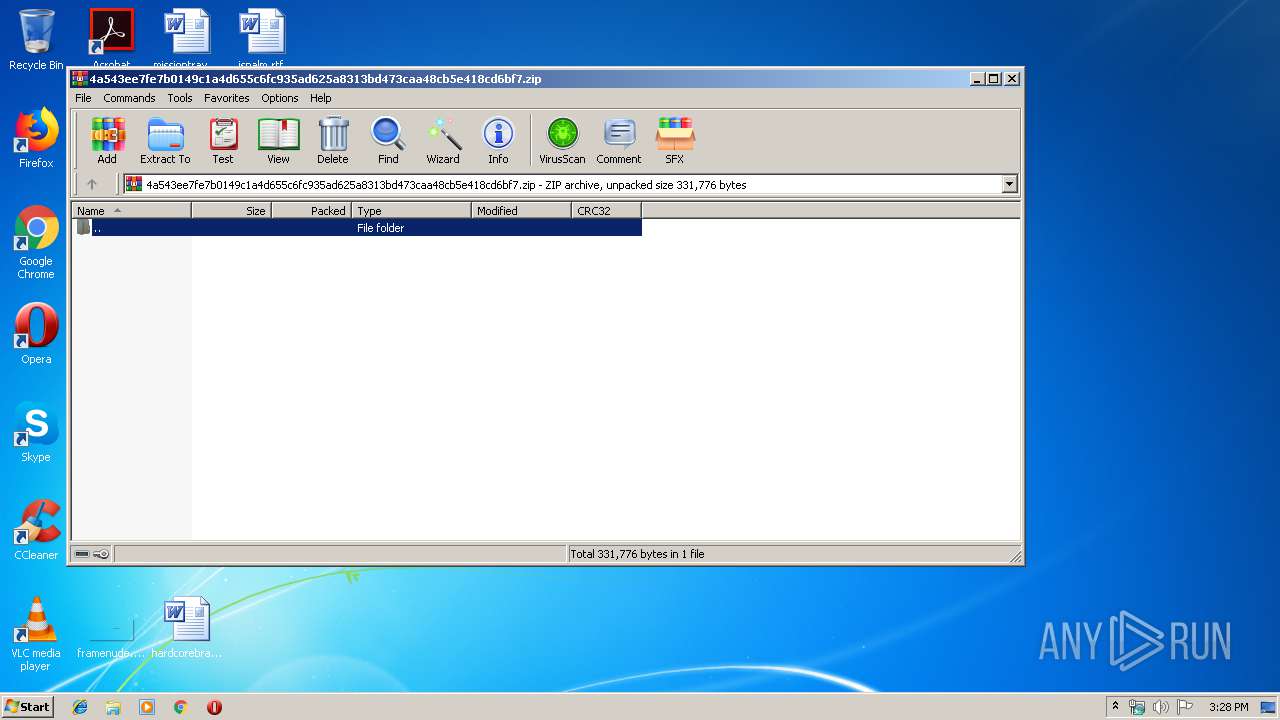
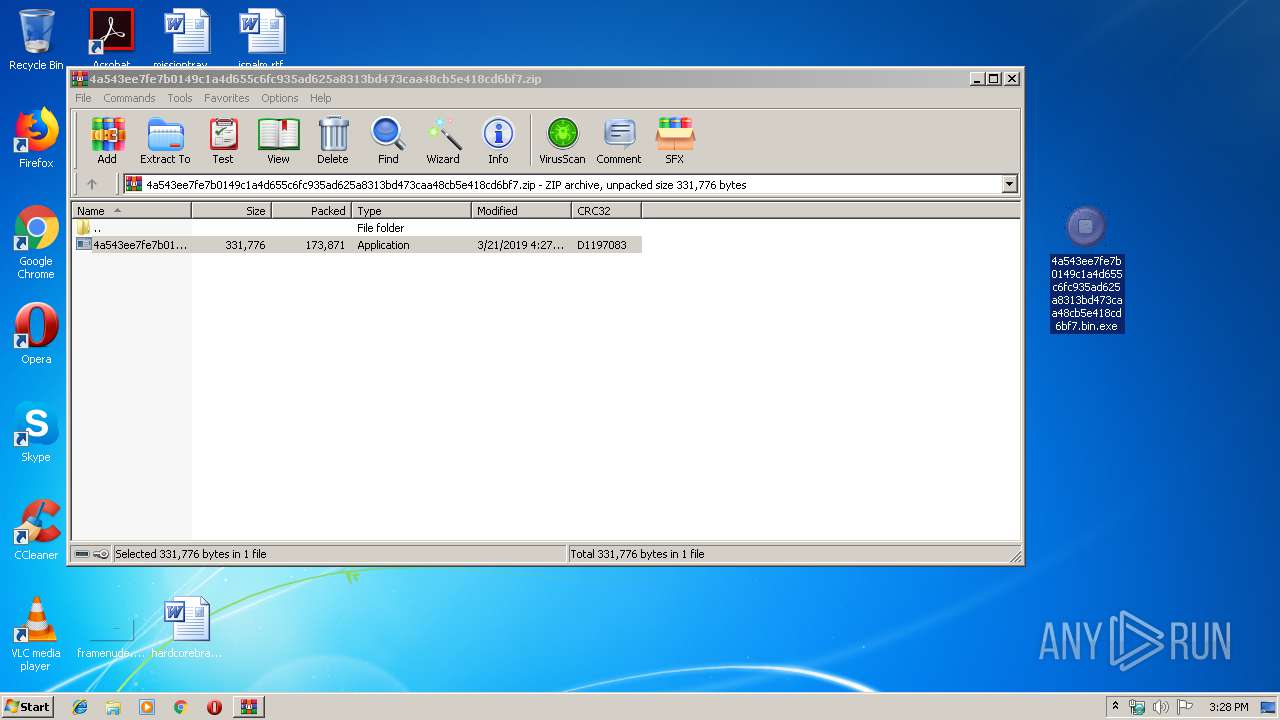
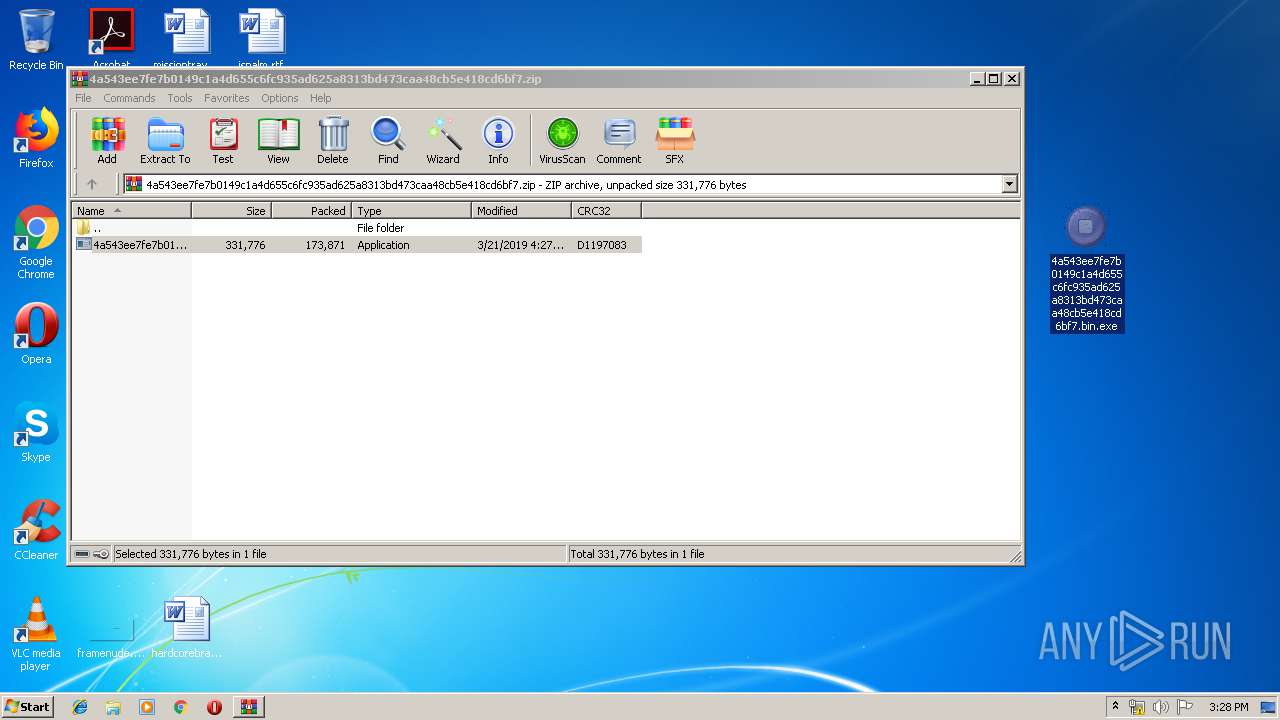
| File name: | 4a543ee7fe7b0149c1a4d655c6fc935ad625a8313bd473caa48cb5e418cd6bf7.zip |
| Full analysis: | https://app.any.run/tasks/65b53f2b-a946-4667-8e9b-492d38eaa8b0 |
| Verdict: | Malicious activity |
| Analysis date: | March 21, 2019, 15:27:47 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | 67C1723E66B03570775C7302B6455FE2 |
| SHA1: | 4BB4C6938C6C03CC1B0AED3C07B8316EB6D7AAE9 |
| SHA256: | 5CFDE117EB5BC9E5B26560D477948355EF70C73FC15FBF518D9EDF7BE741C46A |
| SSDEEP: | 3072:pL4sCbwEQ/dQ9xHDybRrI9/GoEJw8ZeUgMz111UvhiyJ5GNHmuk:pLLCbwKrHurY22MiMP1Fy3GNGv |
MALICIOUS
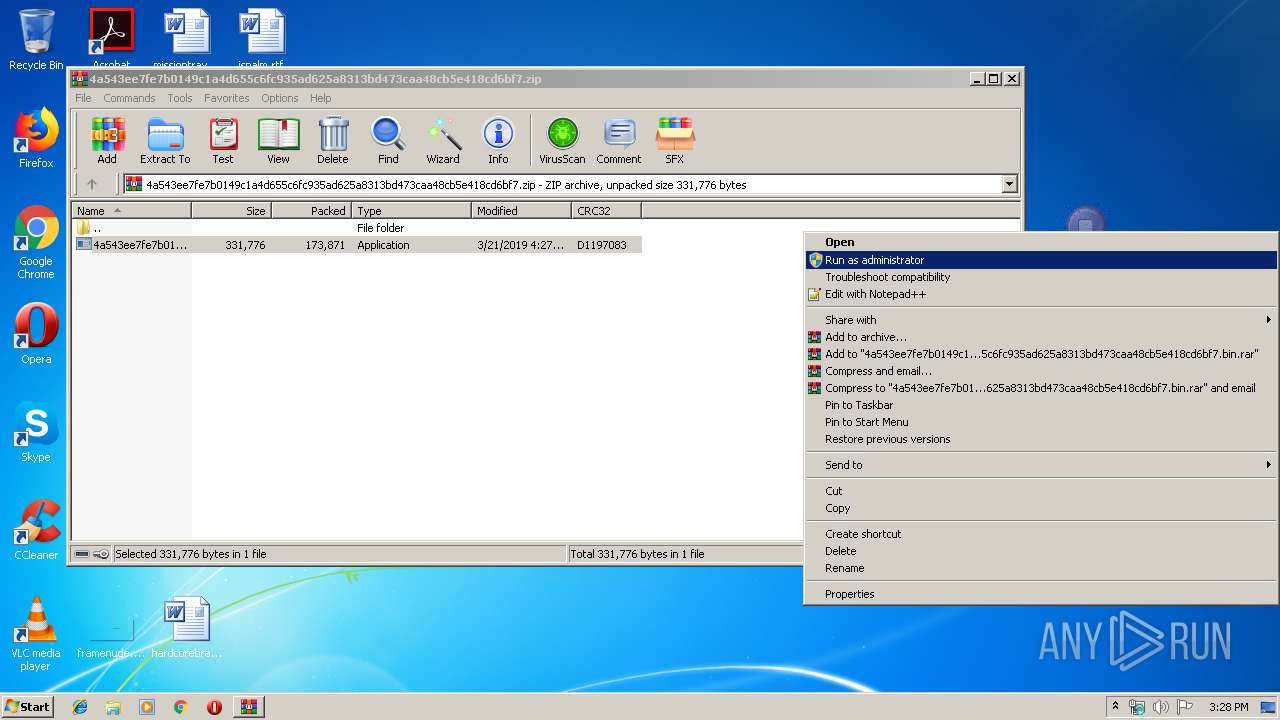
Application was dropped or rewritten from another process
- 4a543ee7fe7b0149c1a4d655c6fc935ad625a8313bd473caa48cb5e418cd6bf7.bin.exe (PID: 2208)
- Rem4.exe (PID: 3808)
Uses SVCHOST.EXE for hidden code execution
- Rem4.exe (PID: 3808)
Changes the autorun value in the registry
- 4a543ee7fe7b0149c1a4d655c6fc935ad625a8313bd473caa48cb5e418cd6bf7.bin.exe (PID: 2208)
- Rem4.exe (PID: 3808)
SUSPICIOUS
Executes scripts
- 4a543ee7fe7b0149c1a4d655c6fc935ad625a8313bd473caa48cb5e418cd6bf7.bin.exe (PID: 2208)
Creates files in the user directory
- 4a543ee7fe7b0149c1a4d655c6fc935ad625a8313bd473caa48cb5e418cd6bf7.bin.exe (PID: 2208)
- Rem4.exe (PID: 3808)
Starts CMD.EXE for commands execution
- WScript.exe (PID: 3768)
Executable content was dropped or overwritten
- 4a543ee7fe7b0149c1a4d655c6fc935ad625a8313bd473caa48cb5e418cd6bf7.bin.exe (PID: 2208)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 788 |
|---|---|
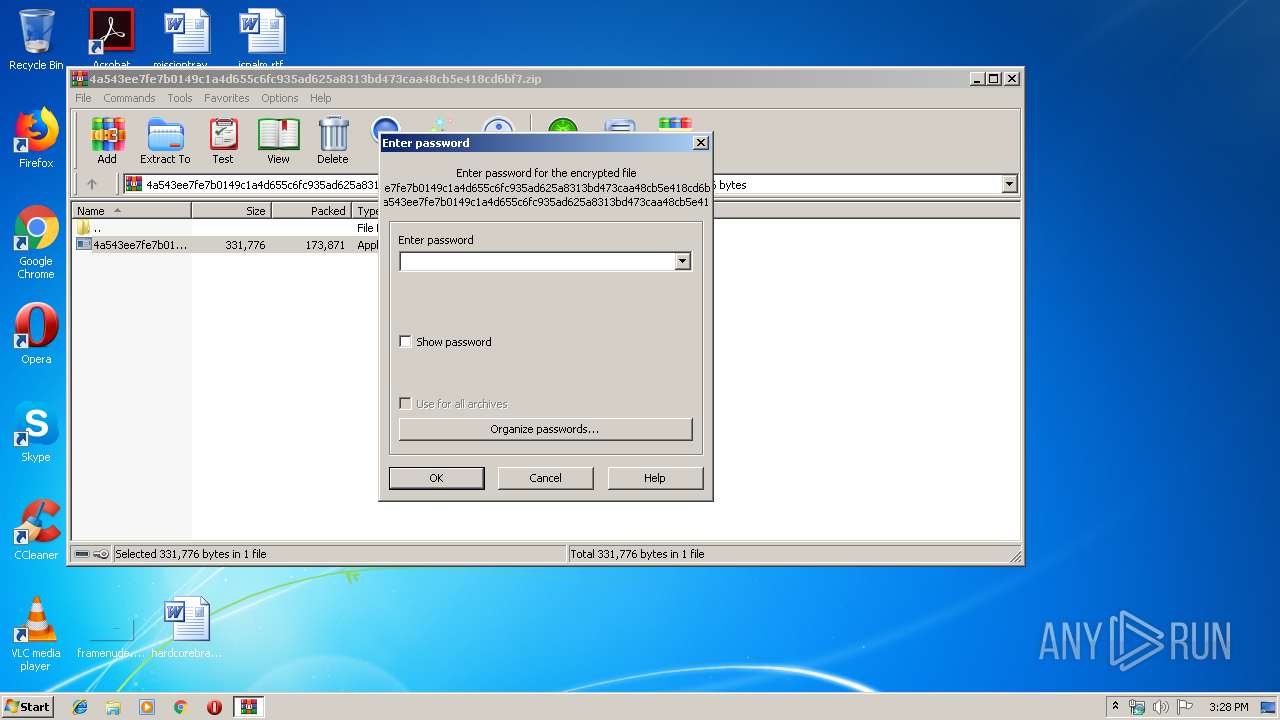
| ZipBitFlag: | 0x0801 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2019:03:21 16:27:15 |
| ZipCRC: | 0xd1197083 |
| ZipCompressedSize: | 173871 |
| ZipUncompressedSize: | 331776 |
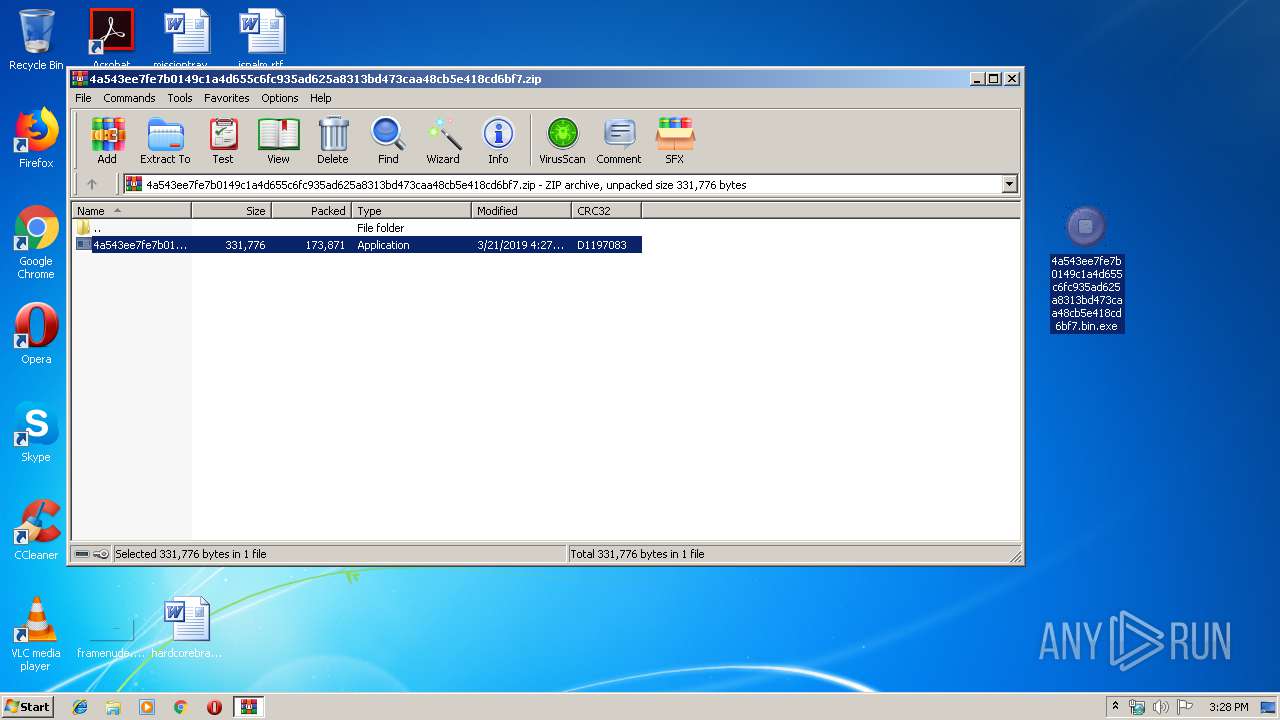
| ZipFileName: | 4a543ee7fe7b0149c1a4d655c6fc935ad625a8313bd473caa48cb5e418cd6bf7.bin.exe |
Total processes
41
Monitored processes
6
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2208 | "C:\Users\admin\Desktop\4a543ee7fe7b0149c1a4d655c6fc935ad625a8313bd473caa48cb5e418cd6bf7.bin.exe" | C:\Users\admin\Desktop\4a543ee7fe7b0149c1a4d655c6fc935ad625a8313bd473caa48cb5e418cd6bf7.bin.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: INTevATion GmbH Exit code: 0 Version: 1.00 Modules
| |||||||||||||||
| 2628 | C:\Windows\system32\svchost.exe | C:\Windows\system32\svchost.exe | — | Rem4.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Host Process for Windows Services Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3124 | "C:\Windows\System32\cmd.exe" /c "C:\Users\admin\AppData\Roaming\Rem4\Rem4.exe" | C:\Windows\System32\cmd.exe | — | WScript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3344 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Desktop\4a543ee7fe7b0149c1a4d655c6fc935ad625a8313bd473caa48cb5e418cd6bf7.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 3768 | "C:\Windows\System32\WScript.exe" "C:\Users\admin\AppData\Local\Temp\install.vbs" | C:\Windows\System32\WScript.exe | — | 4a543ee7fe7b0149c1a4d655c6fc935ad625a8313bd473caa48cb5e418cd6bf7.bin.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 3808 | C:\Users\admin\AppData\Roaming\Rem4\Rem4.exe | C:\Users\admin\AppData\Roaming\Rem4\Rem4.exe | cmd.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: INTevATion GmbH Exit code: 0 Version: 1.00 Modules
| |||||||||||||||
Total events
858
Read events
730
Write events
128
Delete events
0
Modification events
| (PID) Process: | (3344) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (3344) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (3344) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3344) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\4a543ee7fe7b0149c1a4d655c6fc935ad625a8313bd473caa48cb5e418cd6bf7.zip | |||
| (PID) Process: | (3344) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3344) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3344) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (3344) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (3344) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
| (PID) Process: | (2208) 4a543ee7fe7b0149c1a4d655c6fc935ad625a8313bd473caa48cb5e418cd6bf7.bin.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | fghjkjnh |
Value: "C:\Users\admin\AppData\Roaming\Rem4\Rem4.exe" | |||
Executable files
1
Suspicious files
2
Text files
3
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3344 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb3344.9370\4a543ee7fe7b0149c1a4d655c6fc935ad625a8313bd473caa48cb5e418cd6bf7.bin.exe | — | |
MD5:— | SHA256:— | |||
| 2208 | 4a543ee7fe7b0149c1a4d655c6fc935ad625a8313bd473caa48cb5e418cd6bf7.bin.exe | C:\Users\admin\AppData\Roaming\Rem4\Rem4.exe | executable | |
MD5:— | SHA256:— | |||
| 3808 | Rem4.exe | C:\Users\admin\AppData\Roaming\Rem4\logs.dat | binary | |
MD5:— | SHA256:— | |||
| 2208 | 4a543ee7fe7b0149c1a4d655c6fc935ad625a8313bd473caa48cb5e418cd6bf7.bin.exe | C:\Windows\win.ini | text | |
MD5:— | SHA256:— | |||
| 2208 | 4a543ee7fe7b0149c1a4d655c6fc935ad625a8313bd473caa48cb5e418cd6bf7.bin.exe | C:\Users\admin\AppData\Local\Temp\install.vbs | binary | |
MD5:— | SHA256:— | |||
| 3808 | Rem4.exe | C:\Windows\win.ini | text | |
MD5:— | SHA256:— | |||
| 2628 | svchost.exe | C:\Windows\win.ini | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
1
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
DNS requests
Domain | IP | Reputation |
|---|---|---|
allmyfwds.ddns.net |
| malicious |