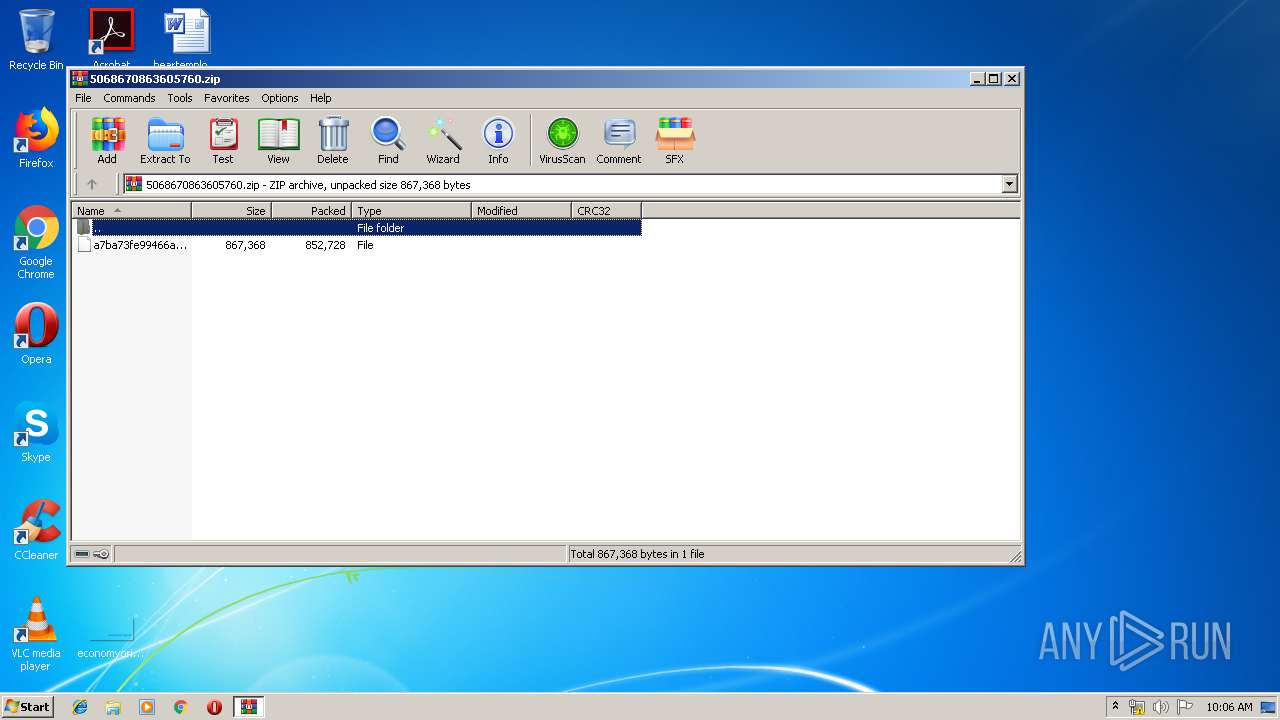
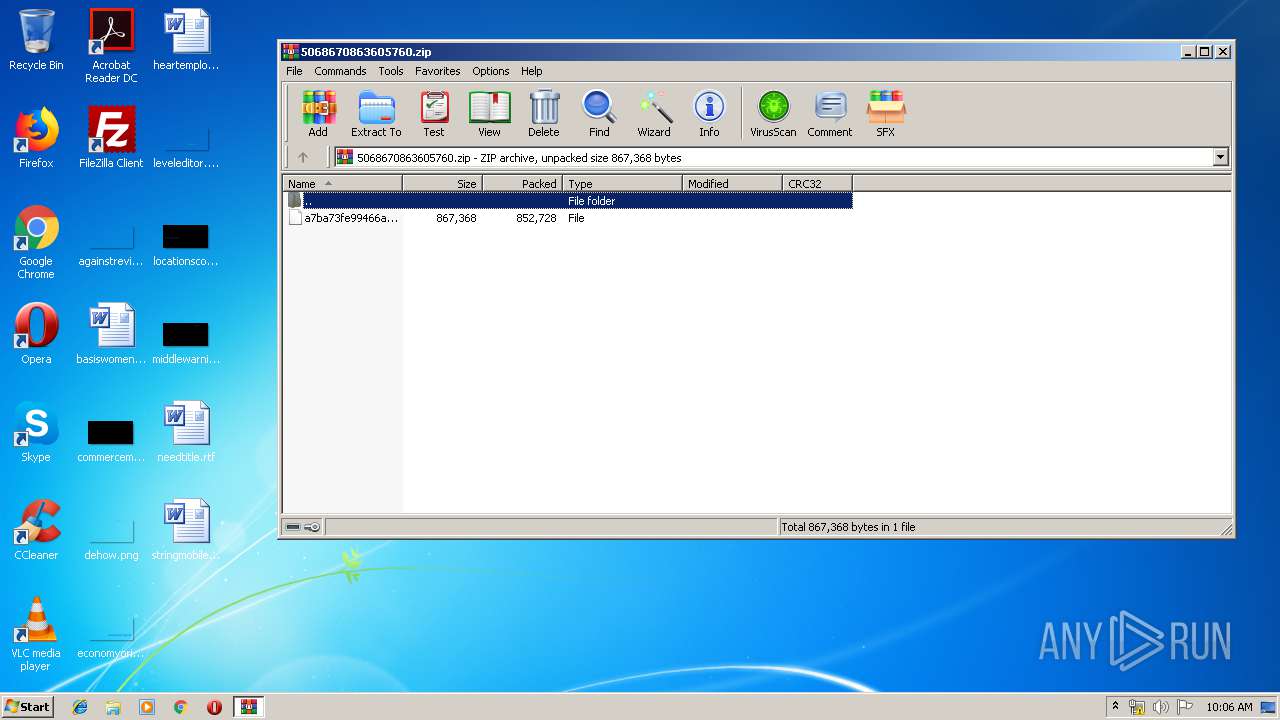
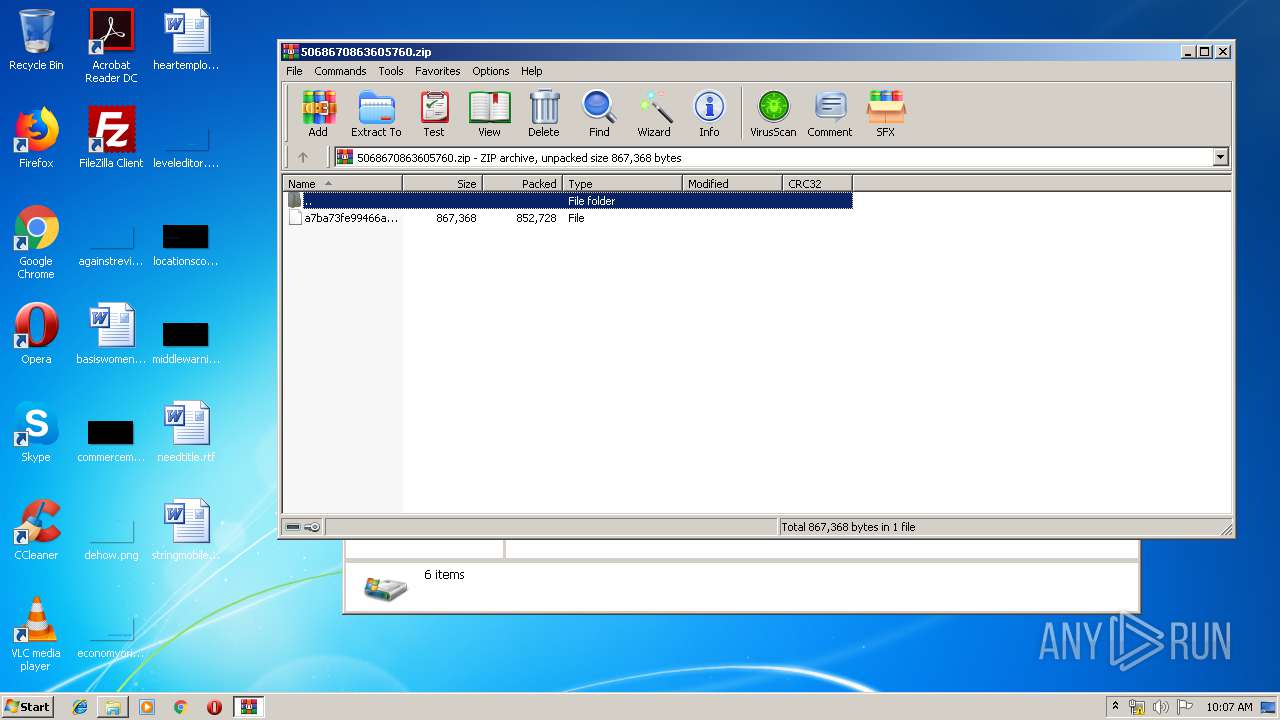
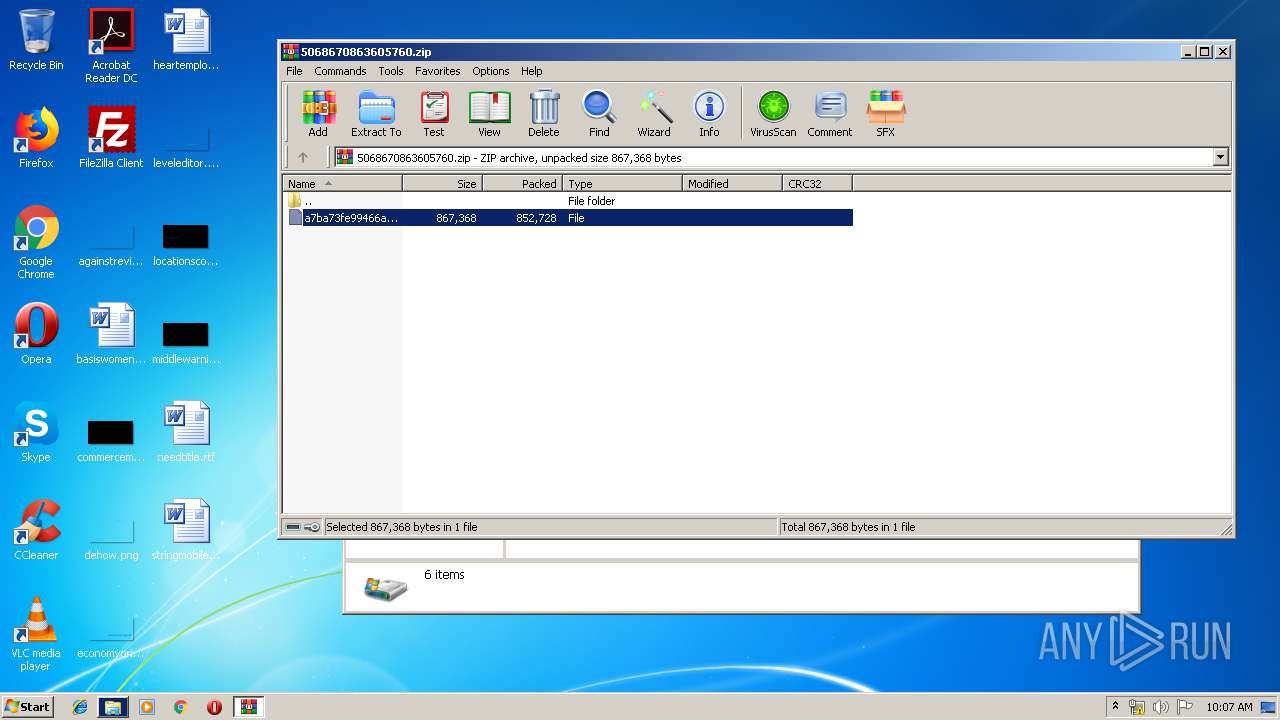
| File name: | 5068670863605760.zip |
| Full analysis: | https://app.any.run/tasks/a368a1b6-8d2c-41dd-8e27-46b239e059ce |
| Verdict: | Malicious activity |
| Analysis date: | September 18, 2019, 09:06:32 |
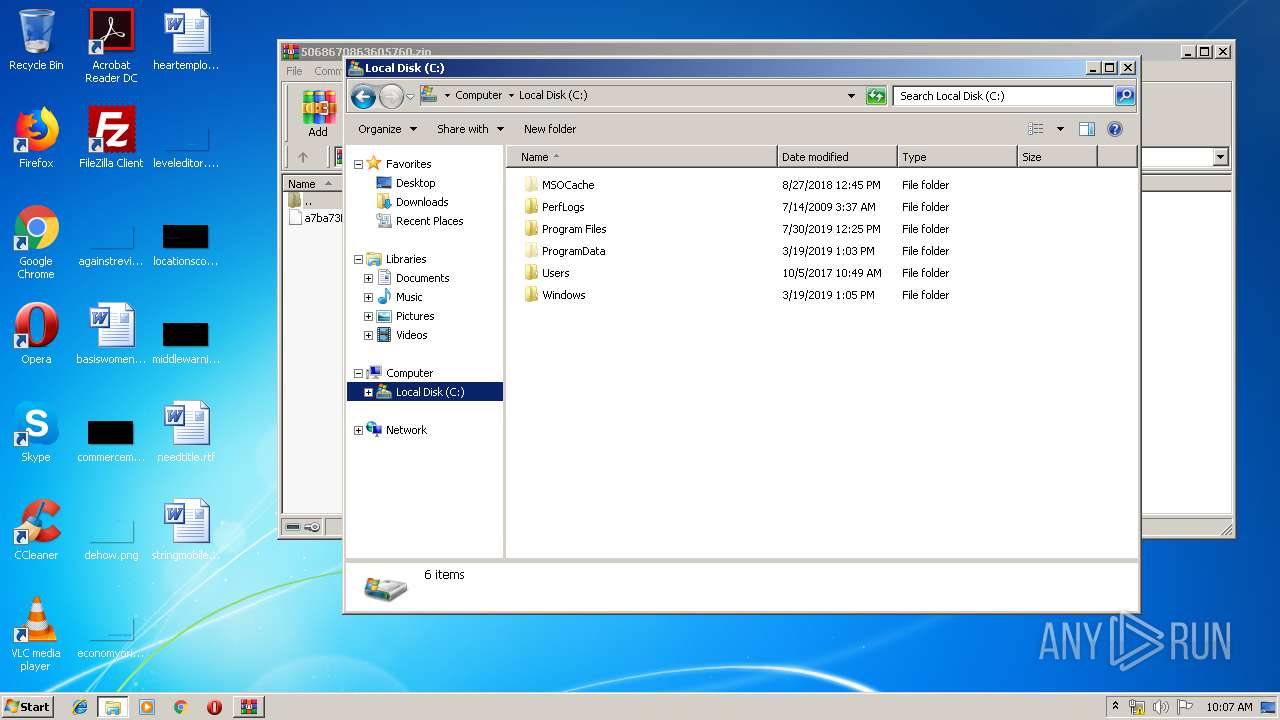
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | A4689247E868DE2254142C93773AA83B |
| SHA1: | D75D769084ACCC786E2657BBF38B90CB47891BBD |
| SHA256: | 5CEF6785646751A04C9CEBEA53127F291CB7DED4B27EB01E9F9C1747755121CD |
| SSDEEP: | 24576:rNdRSvk+eBZfxB5FSXXlSWj57gF2An1I0CbOqdHQ3GNUwlX:xmveBZP5FY1V7cG0CbsGPX |
MALICIOUS
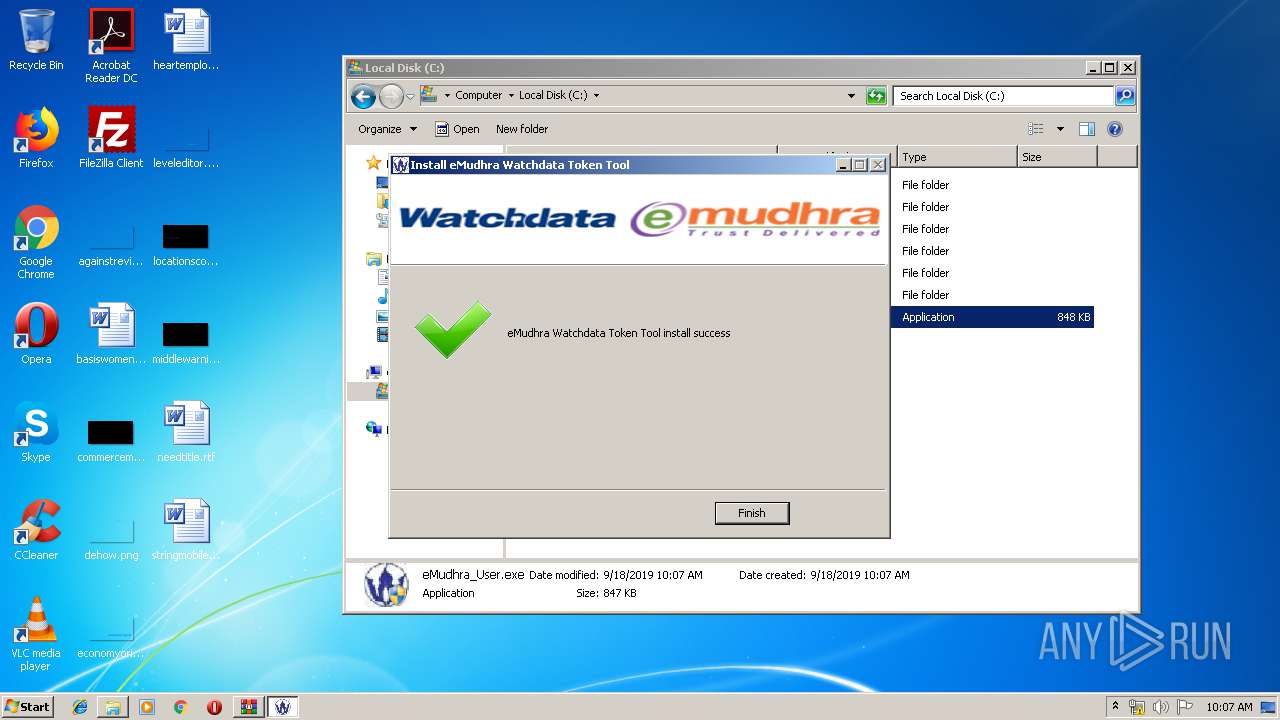
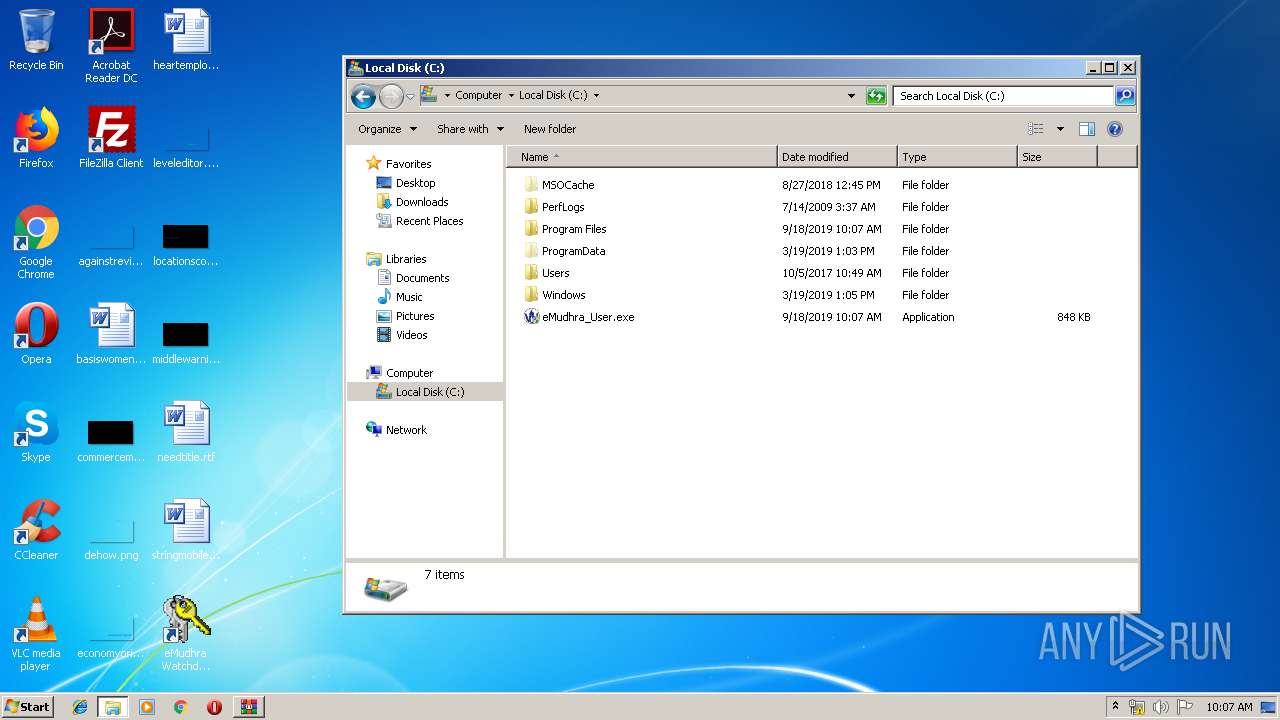
Application was dropped or rewritten from another process
- eMudhra_User.exe (PID: 2708)
- eMudhra_User.exe (PID: 3108)
- eMMonitor34.exe (PID: 3464)
- eMCertMND34.exe (PID: 3864)
- eMudhraPKCSUtil.exe (PID: 3136)
- eMAdminTool.exe (PID: 3112)
Loads dropped or rewritten executable
- eMudhra_User.exe (PID: 3108)
- eMAdminTool.exe (PID: 3112)
- eMMonitor34.exe (PID: 3464)
- eMCertMND34.exe (PID: 3864)
Changes the autorun value in the registry
- eMudhra_User.exe (PID: 3108)
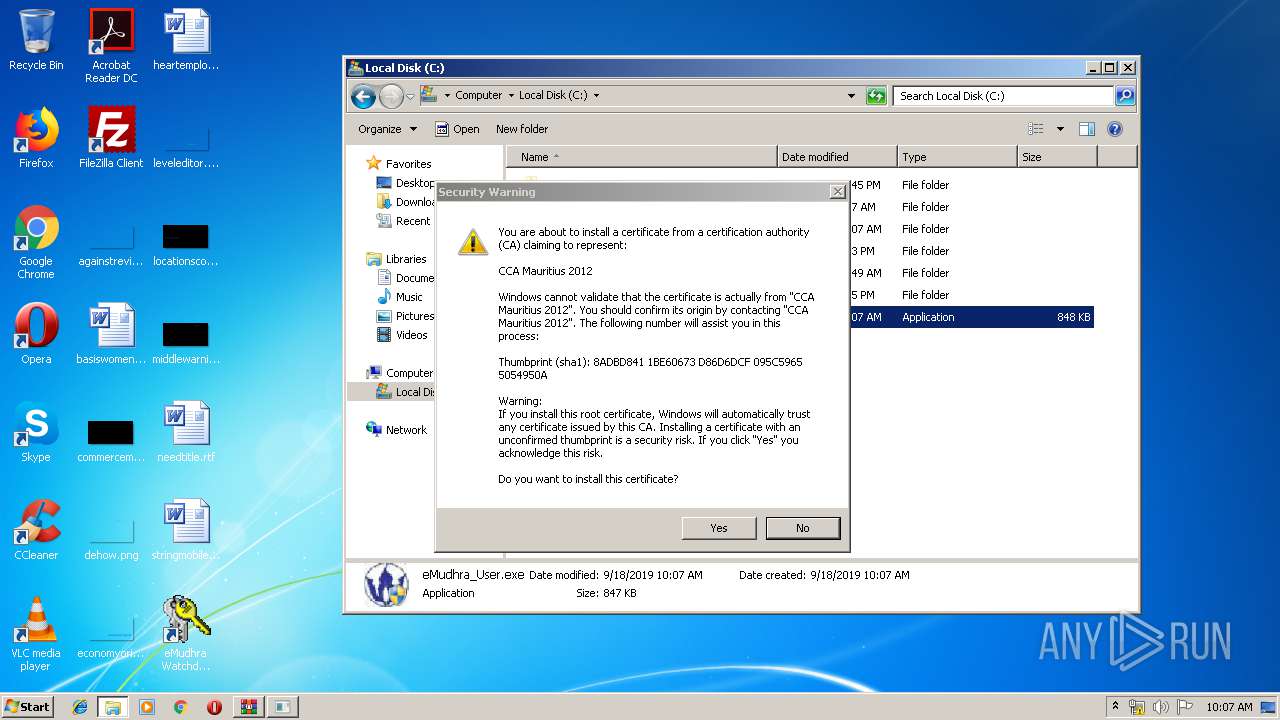
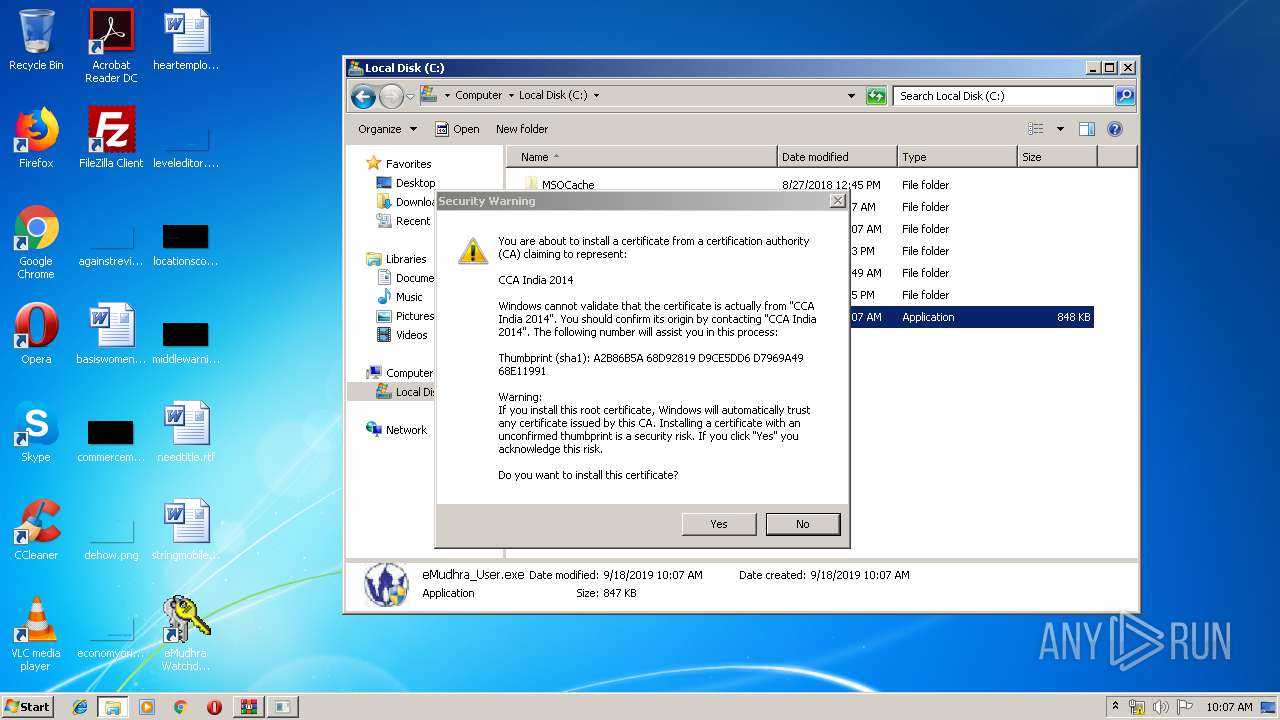
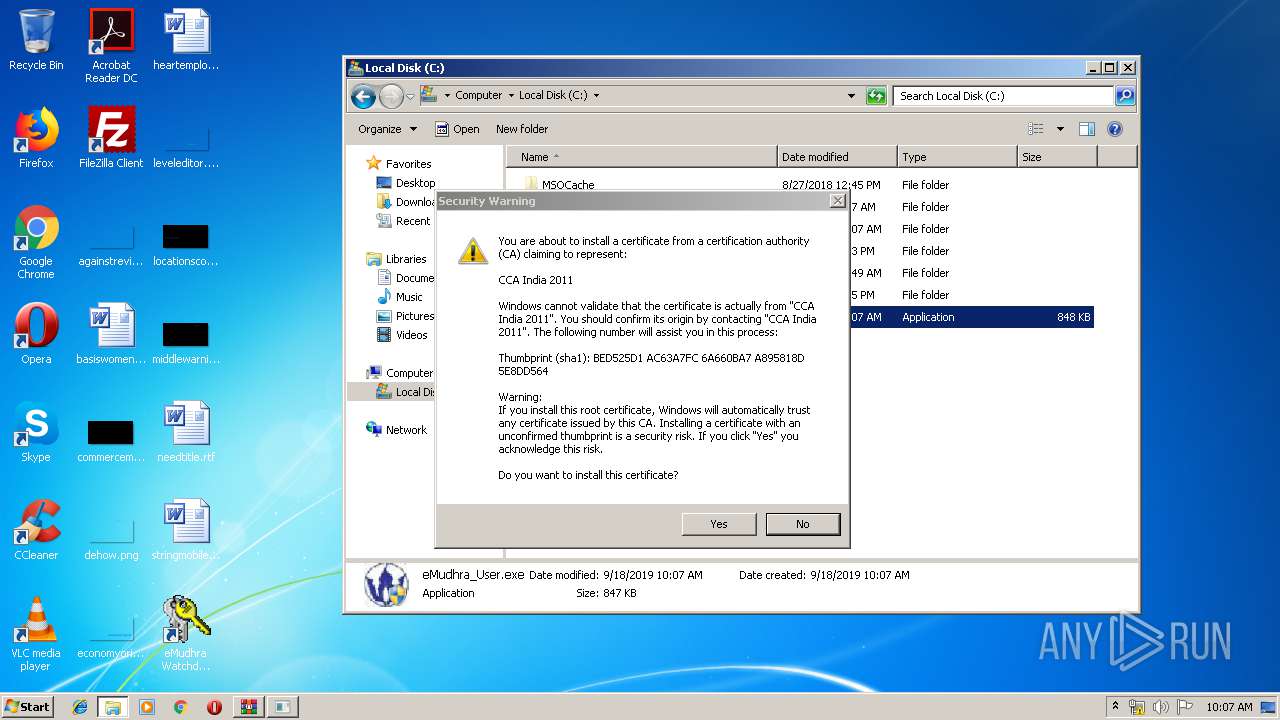
Changes settings of System certificates
- eMCertMND34.exe (PID: 3864)
SUSPICIOUS
Executed via COM
- DllHost.exe (PID: 2476)
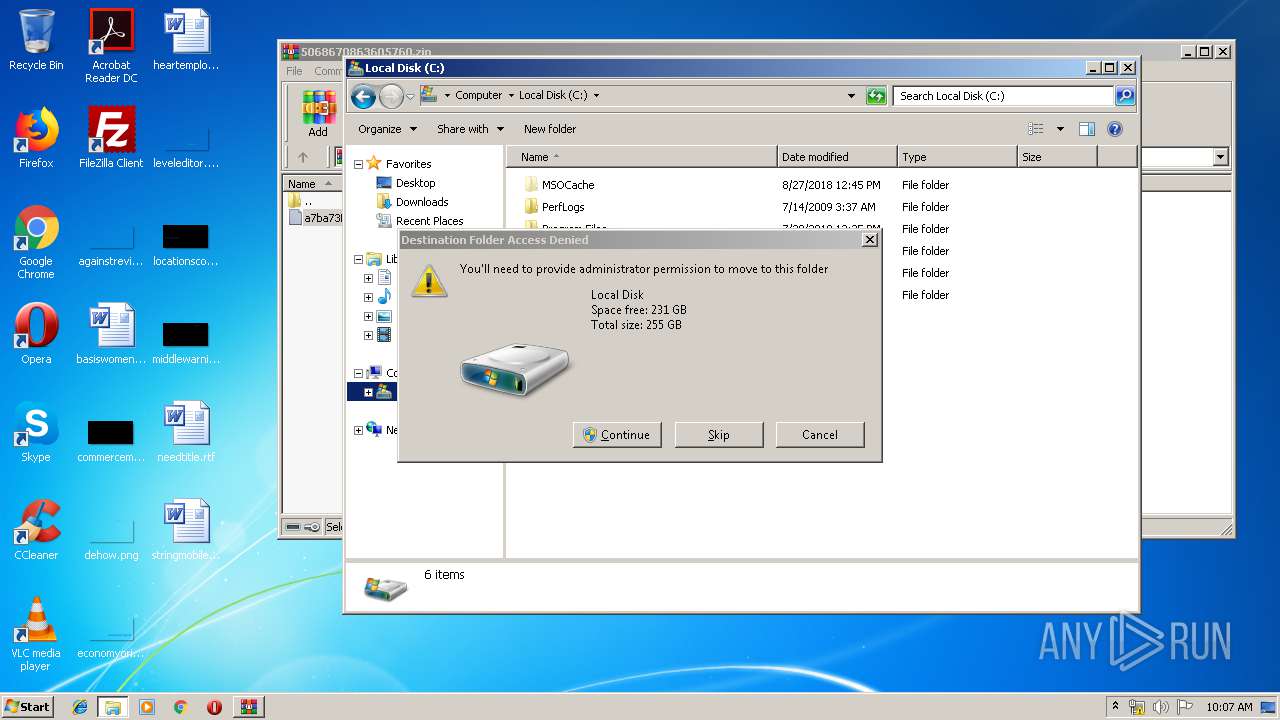
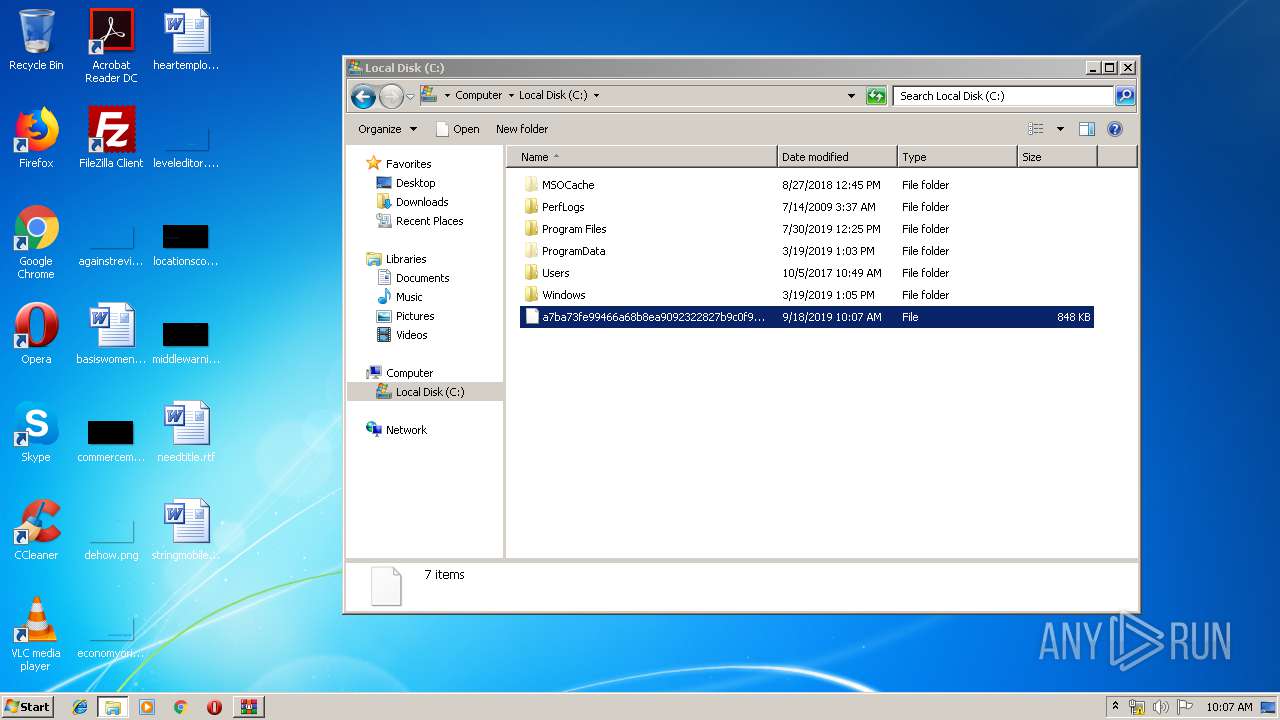
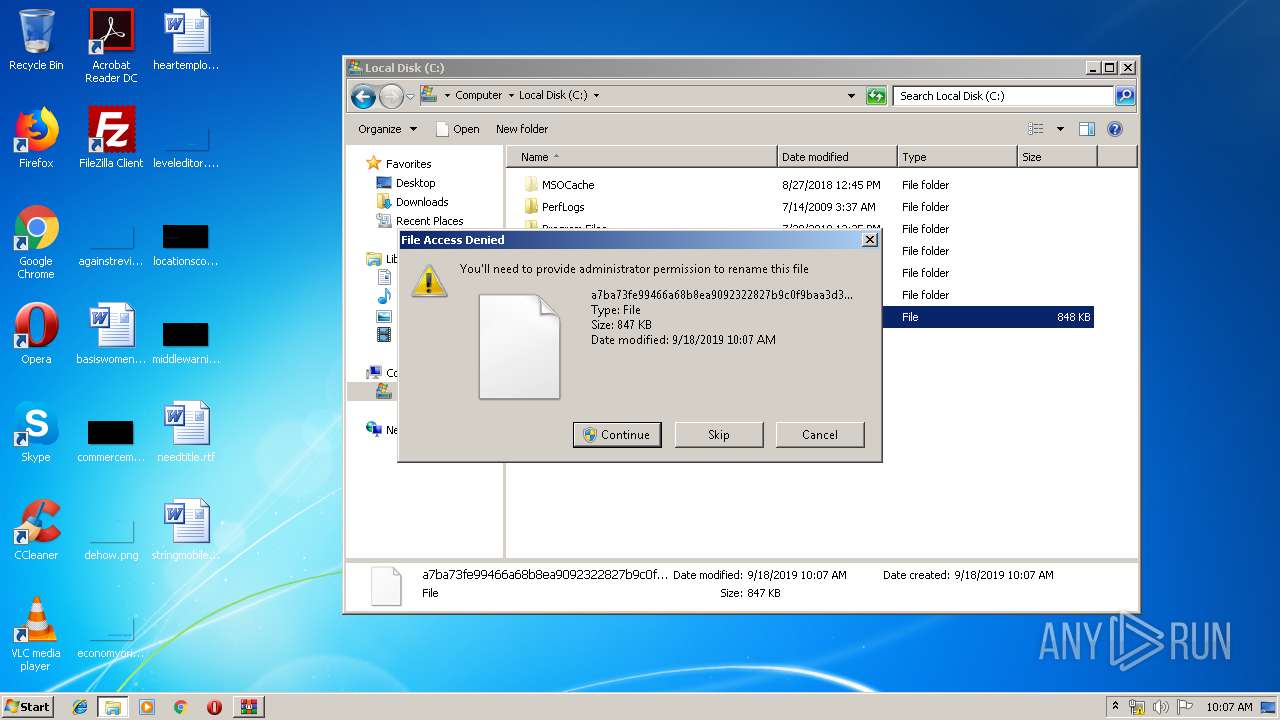
Executable content was dropped or overwritten
- DllHost.exe (PID: 2476)
- WinRAR.exe (PID: 3560)
- eMudhra_User.exe (PID: 3108)
Creates files in the Windows directory
- eMudhra_User.exe (PID: 3108)
Creates files in the program directory
- eMudhra_User.exe (PID: 3108)
Creates a software uninstall entry
- eMudhra_User.exe (PID: 3108)
Executed as Windows Service
- eMMonitor34.exe (PID: 3464)
Loads DLL from Mozilla Firefox
- eMudhraPKCSUtil.exe (PID: 3136)
INFO
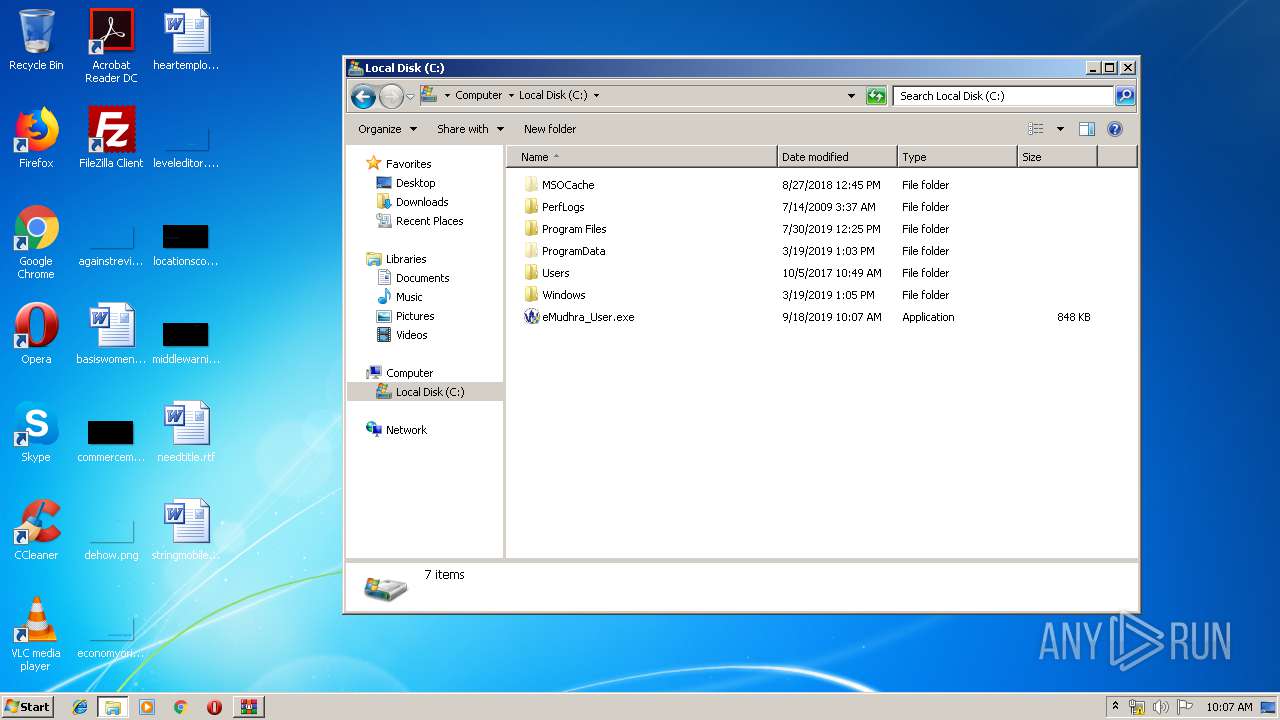
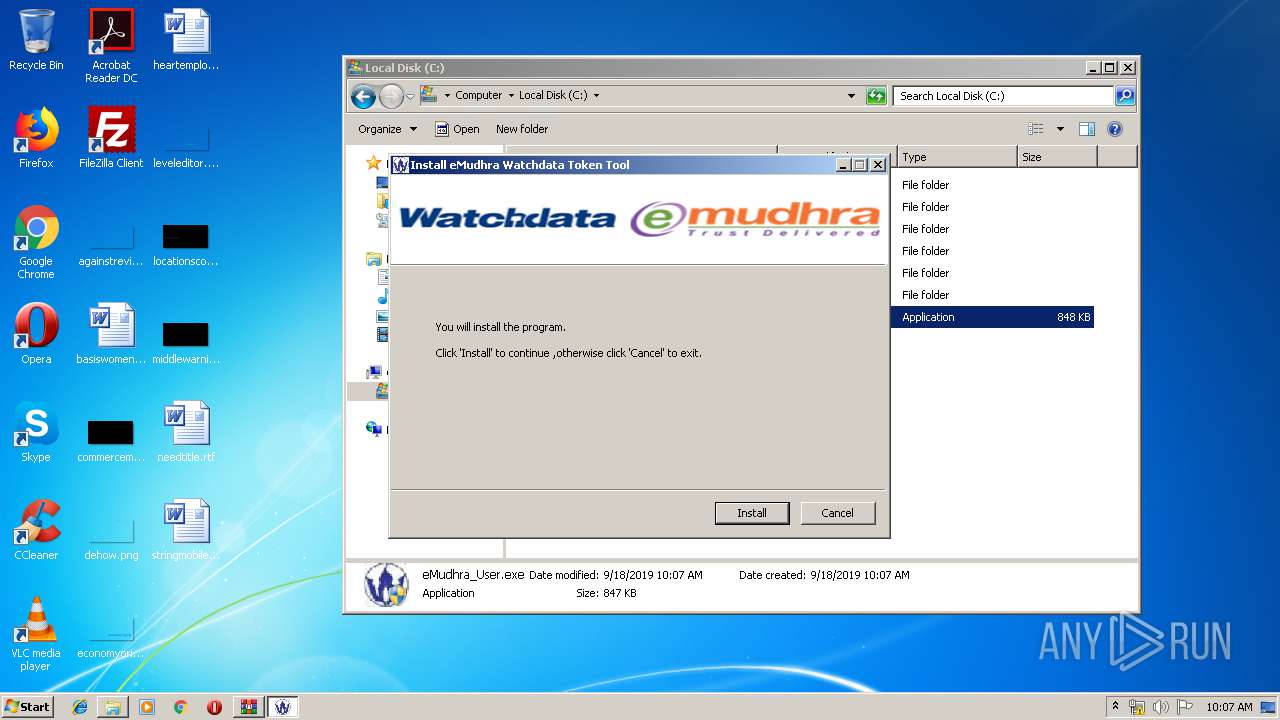
Manual execution by user
- eMudhra_User.exe (PID: 3108)
- eMudhra_User.exe (PID: 2708)
- eMAdminTool.exe (PID: 3112)
Reads settings of System Certificates
- eMCertMND34.exe (PID: 3864)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
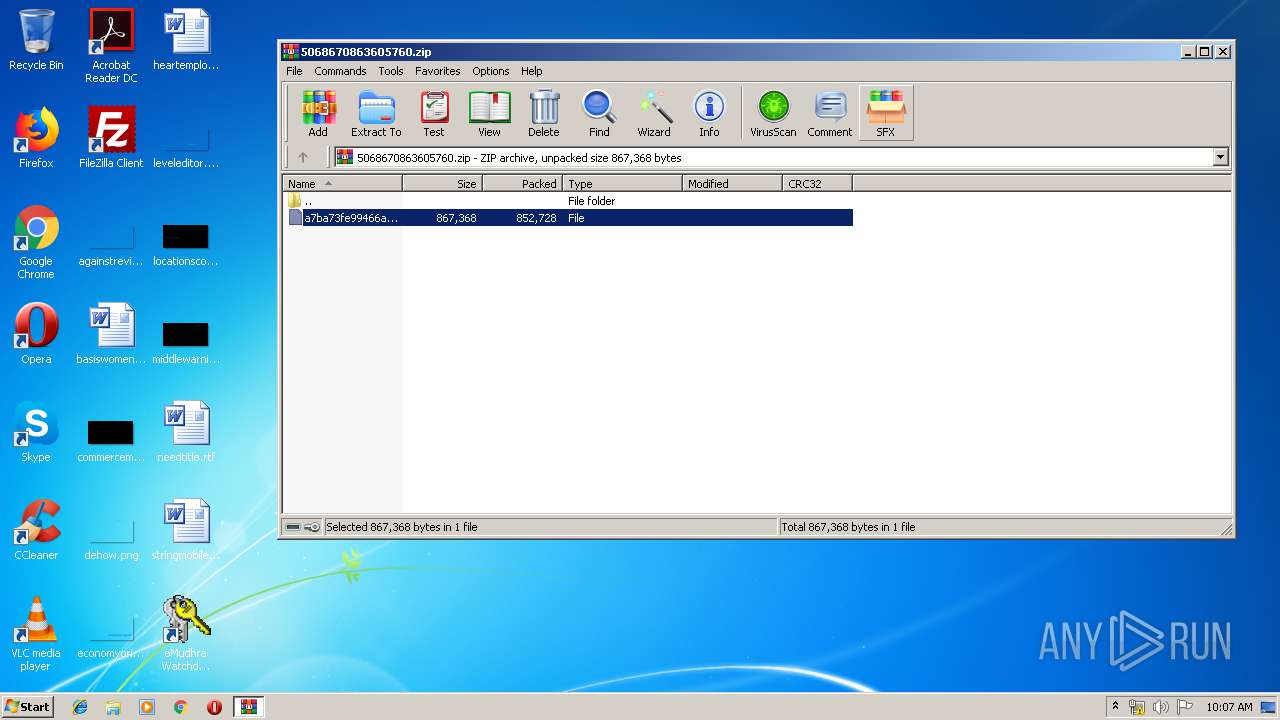
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | 0x0009 |
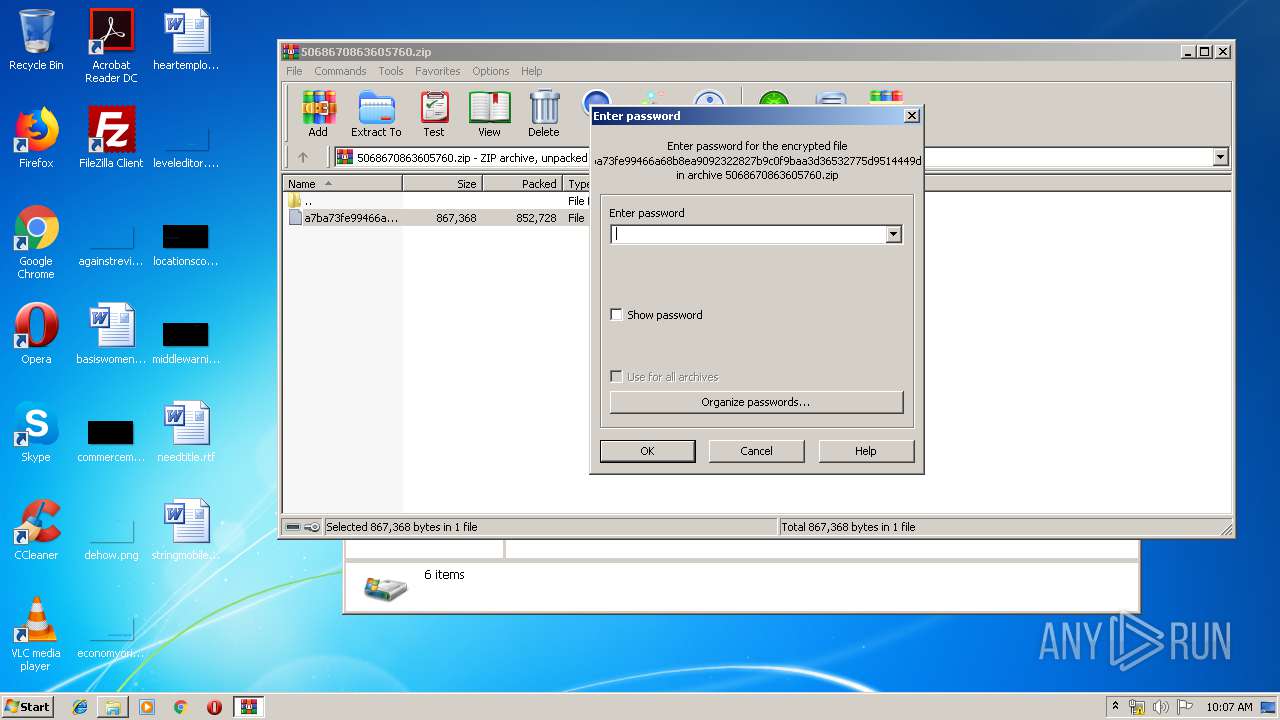
| ZipCompression: | Unknown (99) |
| ZipModifyDate: | 1980:00:00 00:00:00 |
| ZipCRC: | 0x00000000 |
| ZipCompressedSize: | 852728 |
| ZipUncompressedSize: | 867368 |
| ZipFileName: | a7ba73fe99466a68b8ea9092322827b9c0f9baa3d36532775d9514449d4daffc |
Total processes
48
Monitored processes
8
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2476 | C:\Windows\system32\DllHost.exe /Processid:{3AD05575-8857-4850-9277-11B85BDB8E09} | C:\Windows\system32\DllHost.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2708 | "C:\eMudhra_User.exe" | C:\eMudhra_User.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 3108 | "C:\eMudhra_User.exe" | C:\eMudhra_User.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
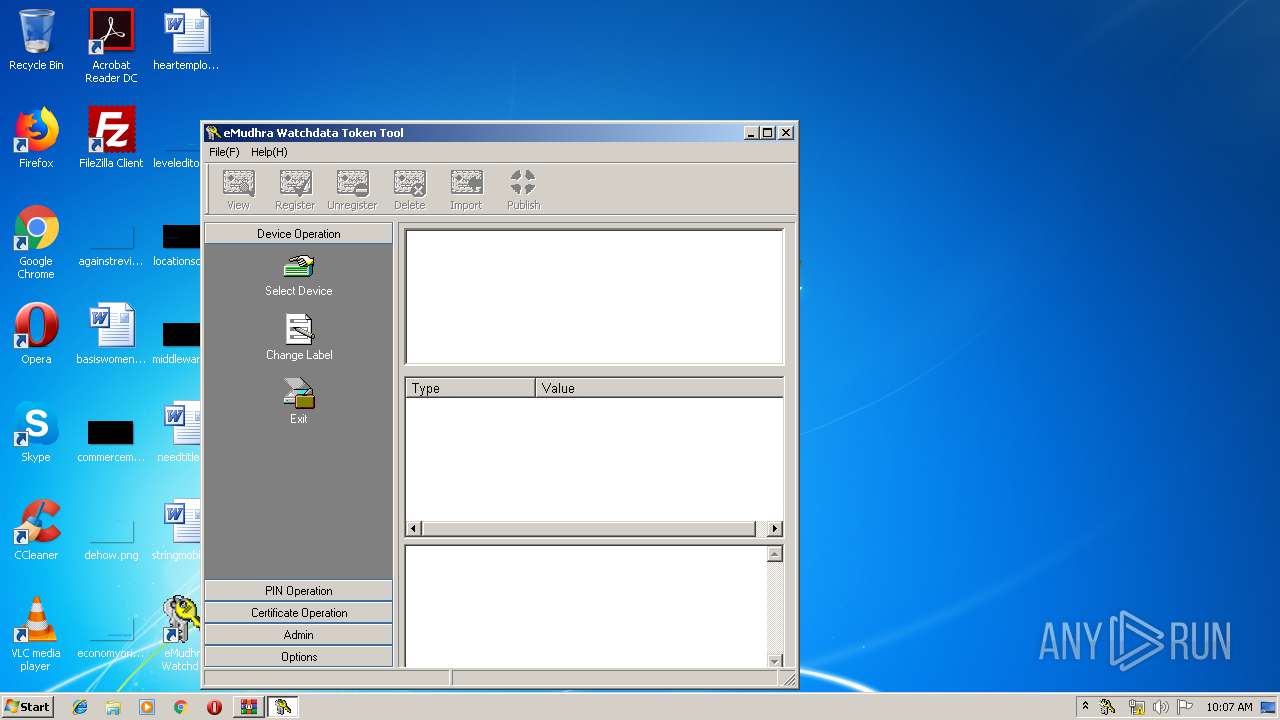
| 3112 | "C:\Program Files\eMudhra\eMudhra USB Token\eMAdminTool.exe" | C:\Program Files\eMudhra\eMudhra USB Token\eMAdminTool.exe | — | explorer.exe | |||||||||||
User: admin Company: Watchdata Technologies Pte. Ltd. Integrity Level: MEDIUM Description: eMudhra Watchdata Token Tool Exit code: 0 Version: 3, 4, 0, 0 Modules
| |||||||||||||||
| 3136 | "C:\Program Files\eMudhra\eMudhra USB Token\eMudhraPKCSUtil.exe" -install | C:\Program Files\eMudhra\eMudhra USB Token\eMudhraPKCSUtil.exe | — | eMCertMND34.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 1 Modules
| |||||||||||||||
| 3464 | "C:\Windows\system32\eMudhra\eMudhra CSP V1.0\eMMonitor34.exe" | C:\Windows\system32\eMudhra\eMudhra CSP V1.0\eMMonitor34.exe | — | services.exe | |||||||||||
User: SYSTEM Company: eMudhra Integrity Level: SYSTEM Description: eMudhra Service 3.4 Exit code: 0 Version: 3, 4, 0, 0 Modules
| |||||||||||||||
| 3560 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Downloads\5068670863605760.zip" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 3864 | "C:\Windows\system32\eMudhra\eMudhra CSP V1.0\eMCertMND34.exe" | C:\Windows\system32\eMudhra\eMudhra CSP V1.0\eMCertMND34.exe | — | eMudhra_User.exe | |||||||||||
User: admin Company: eMudhra Integrity Level: HIGH Description: eMudhra Daemon3.2 Exit code: 0 Version: 3, 2, 0, 0 Modules
| |||||||||||||||
Total events
723
Read events
667
Write events
55
Delete events
1
Modification events
| (PID) Process: | (3560) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (3560) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (3560) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\72\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3560) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Downloads\5068670863605760.zip | |||
| (PID) Process: | (3560) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3560) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3560) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (3560) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (3560) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
| (PID) Process: | (3108) eMudhra_User.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | eMudhracertm_nd34 |
Value: C:\Windows\System32\eMudhra\eMudhra CSP V1.0\eMCertMND34.exe | |||
Executable files
27
Suspicious files
2
Text files
7
Unknown types
4
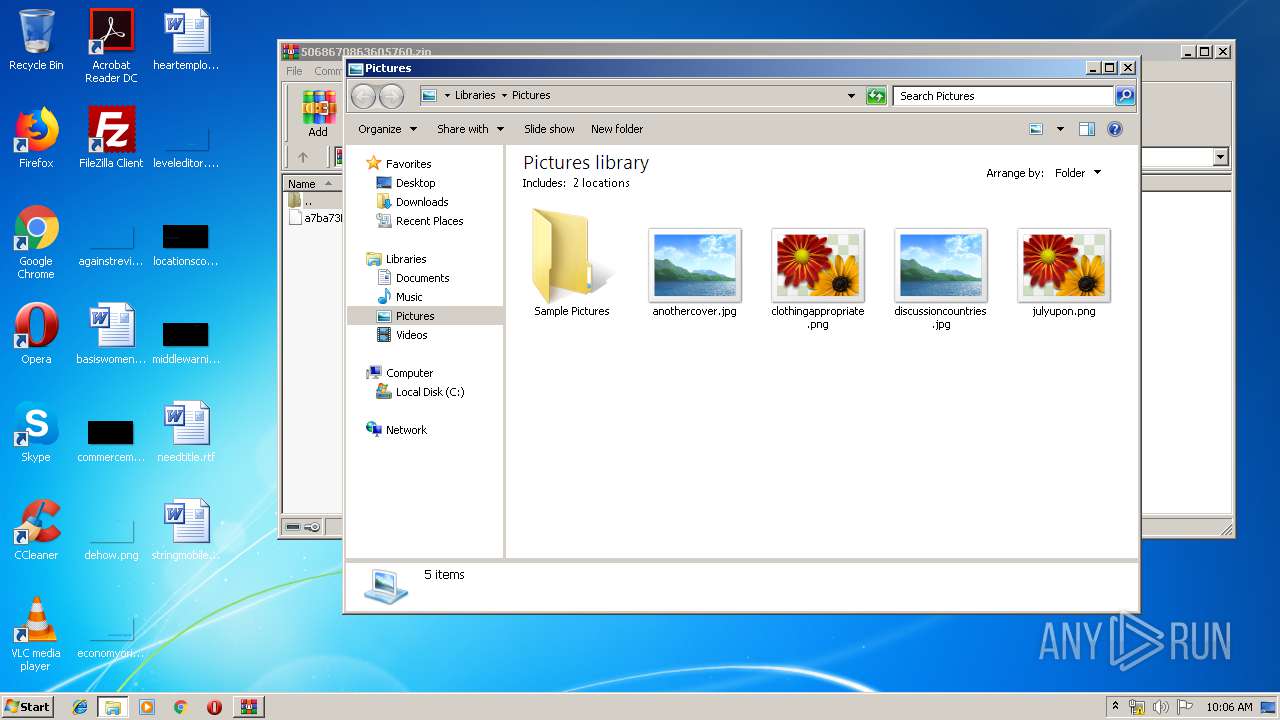
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3560 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb3560.12685\a7ba73fe99466a68b8ea9092322827b9c0f9baa3d36532775d9514449d4daffc | executable | |
MD5:— | SHA256:— | |||
| 3108 | eMudhra_User.exe | C:\Windows\system32\eMudhra\eMudhra CSP V1.0\TokenMgr.dll | executable | |
MD5:— | SHA256:— | |||
| 2476 | DllHost.exe | C:\eMudhra_User.exe | executable | |
MD5:— | SHA256:— | |||
| 3108 | eMudhra_User.exe | C:\Windows\system32\eMudhraNSIS.dll | executable | |
MD5:— | SHA256:— | |||
| 3108 | eMudhra_User.exe | C:\Windows\system32\eMudhra\eMudhra CSP V1.0\Protect.sig | binary | |
MD5:— | SHA256:— | |||
| 3108 | eMudhra_User.exe | C:\Windows\system32\eMudhra\eMudhra CSP V1.0\UIResE3.dll | executable | |
MD5:— | SHA256:— | |||
| 3108 | eMudhra_User.exe | C:\Windows\system32\eMudhra\eMudhra CSP V1.0\WDAlg.dll | executable | |
MD5:— | SHA256:— | |||
| 2476 | DllHost.exe | C:\a7ba73fe99466a68b8ea9092322827b9c0f9baa3d36532775d9514449d4daffc | executable | |
MD5:— | SHA256:— | |||
| 3108 | eMudhra_User.exe | C:\Users\admin\AppData\Local\Temp\nsz2647.tmp\modern-header.bmp | image | |
MD5:— | SHA256:— | |||
| 3108 | eMudhra_User.exe | C:\Users\admin\AppData\Local\Temp\nsz2647.tmp\UserInfo.dll | executable | |
MD5:D16E06C5DE8FB8213A0464568ED9852F | SHA256:728472BA312AE8AF7F30D758AB473E0772477A68FCD1D2D547DAFE6D8800D531 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report