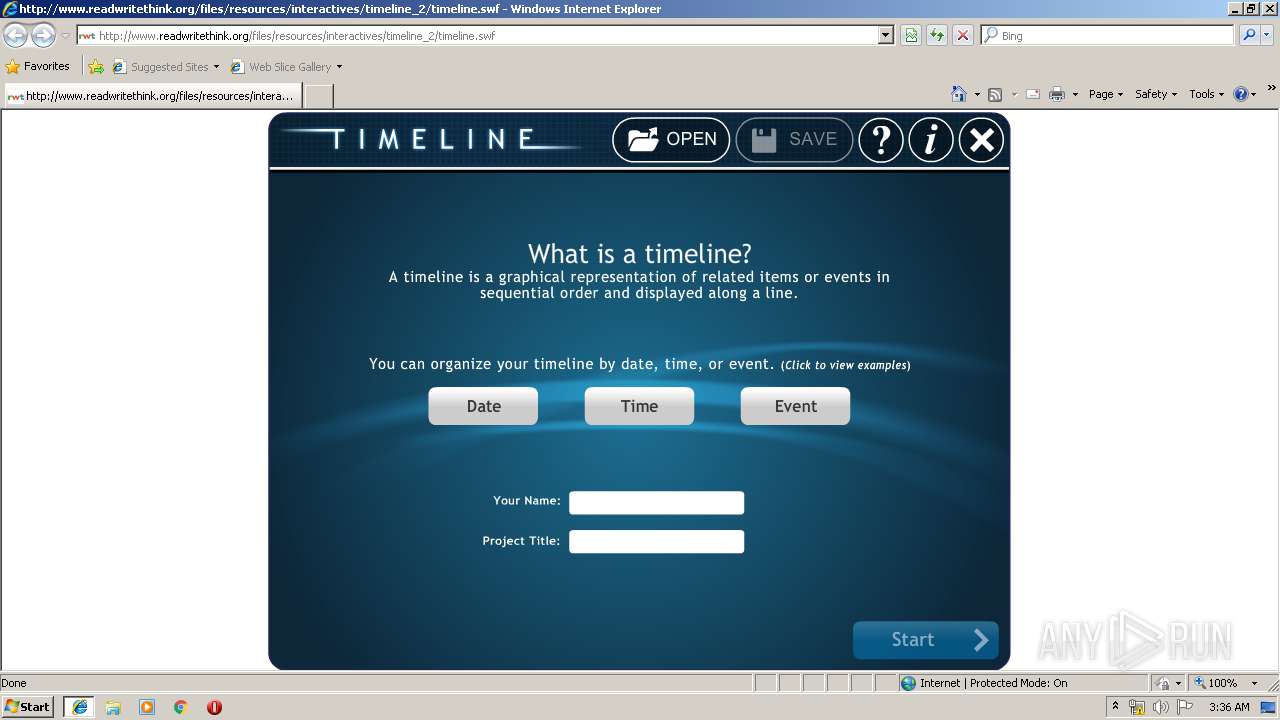
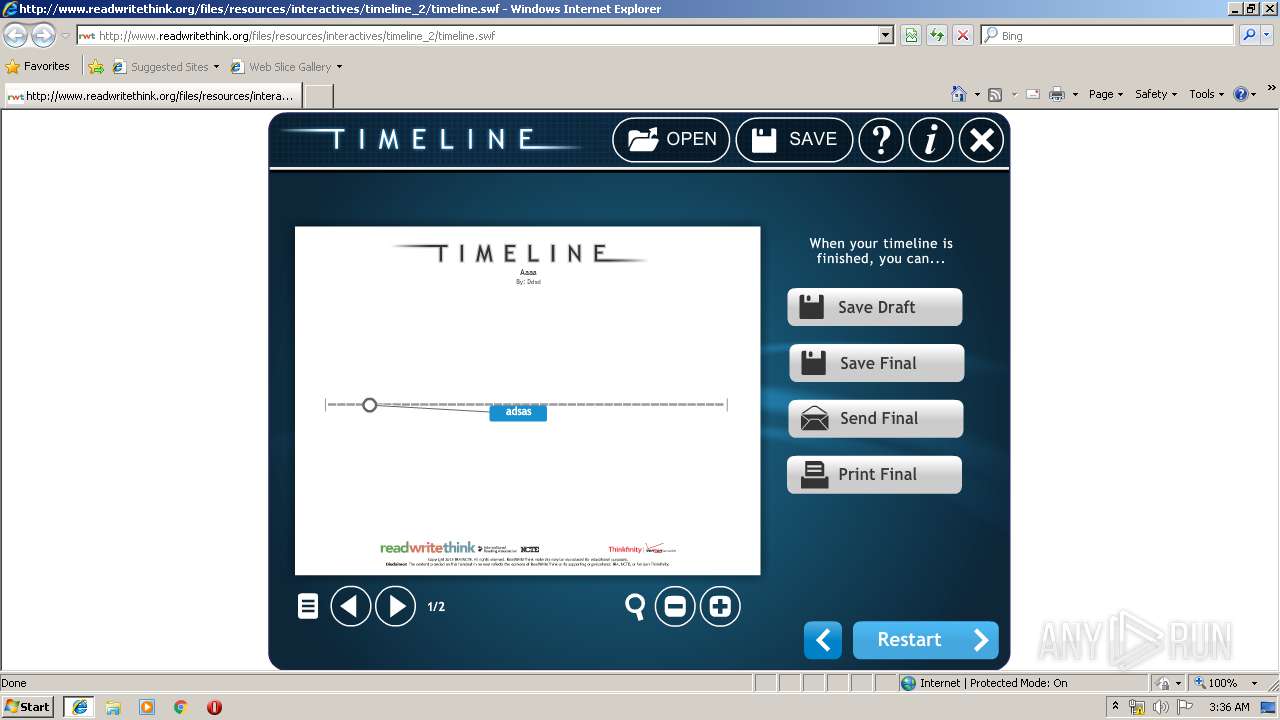
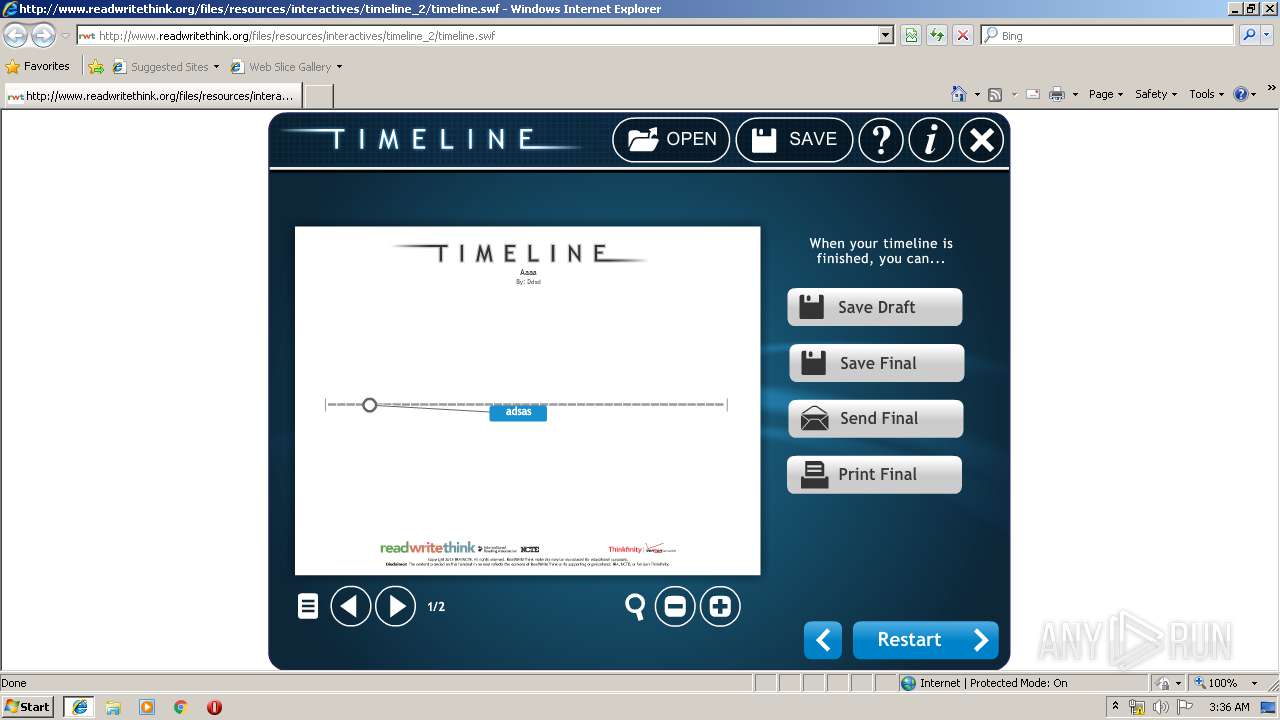
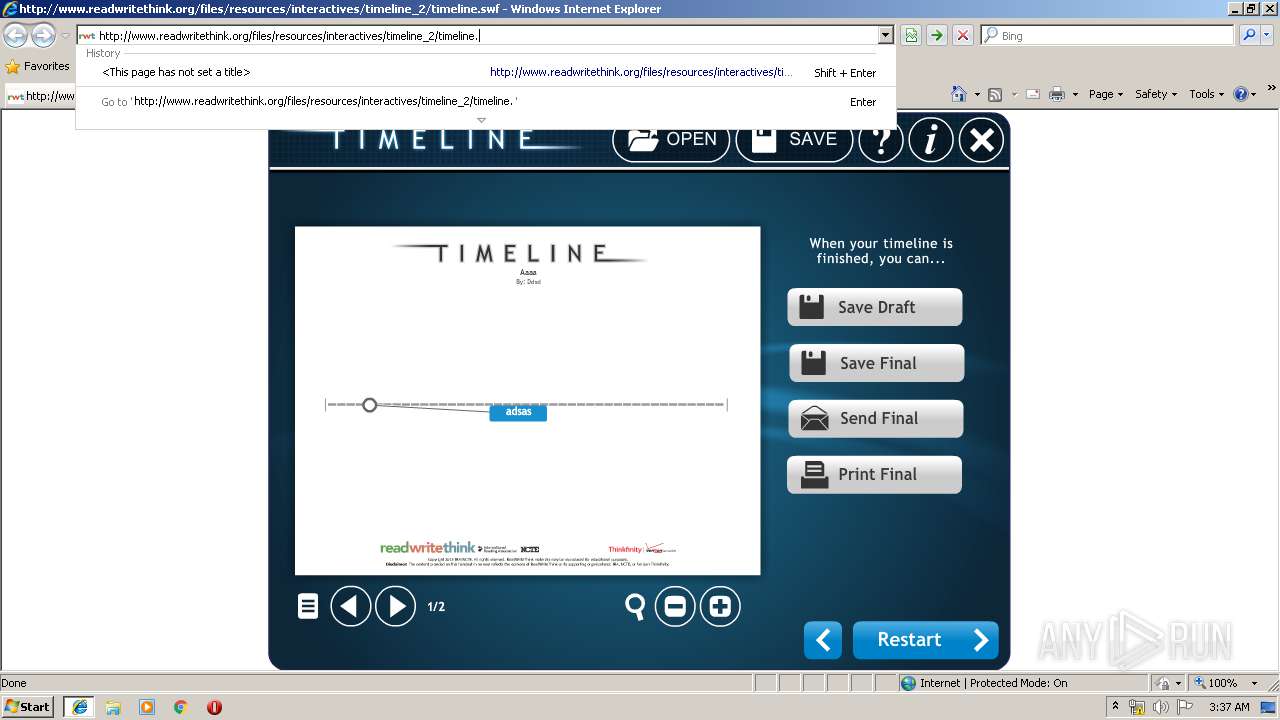
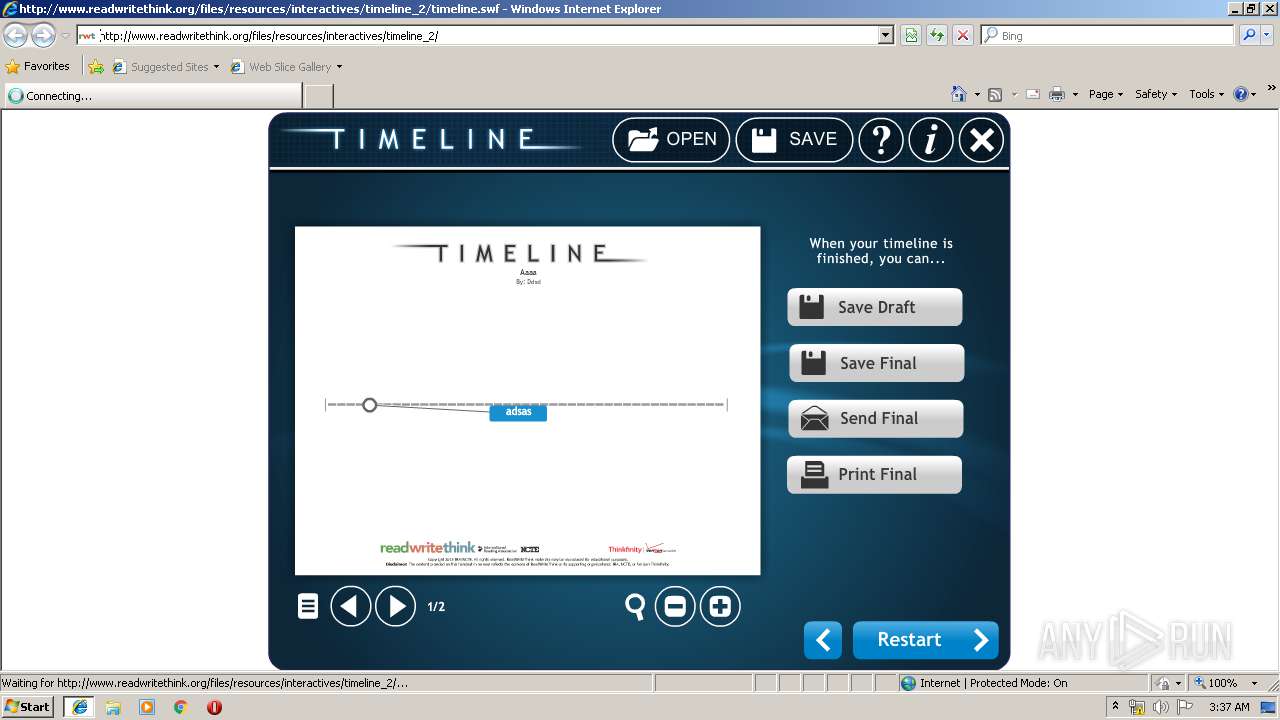
| URL: | http://www.readwritethink.org/files/resources/interactives/timeline_2/timeline.swf |
| Full analysis: | https://app.any.run/tasks/e2438ea6-fc7d-4b18-b036-73f2a0c64a5d |
| Verdict: | No threats detected |
| Analysis date: | April 09, 2019, 02:35:45 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 9E399A2CAD86C30957692B50108BD6E7 |
| SHA1: | 1F5C2DF0BC9DF35F9616EFCEA10B23459949B406 |
| SHA256: | 5CEE0B4743CADB6BCC637703C17E4595AA425FA3AA5A1257A09700F1500E9B3B |
| SSDEEP: | 3:N1KJS4QoFmNKxMONXWu5S/IKmOw:Cc4QzUxMHu5GI7Ow |
MALICIOUS
No malicious indicators.SUSPICIOUS
Reads Internet Cache Settings
- FlashUtil32_26_0_0_131_ActiveX.exe (PID: 1412)
INFO
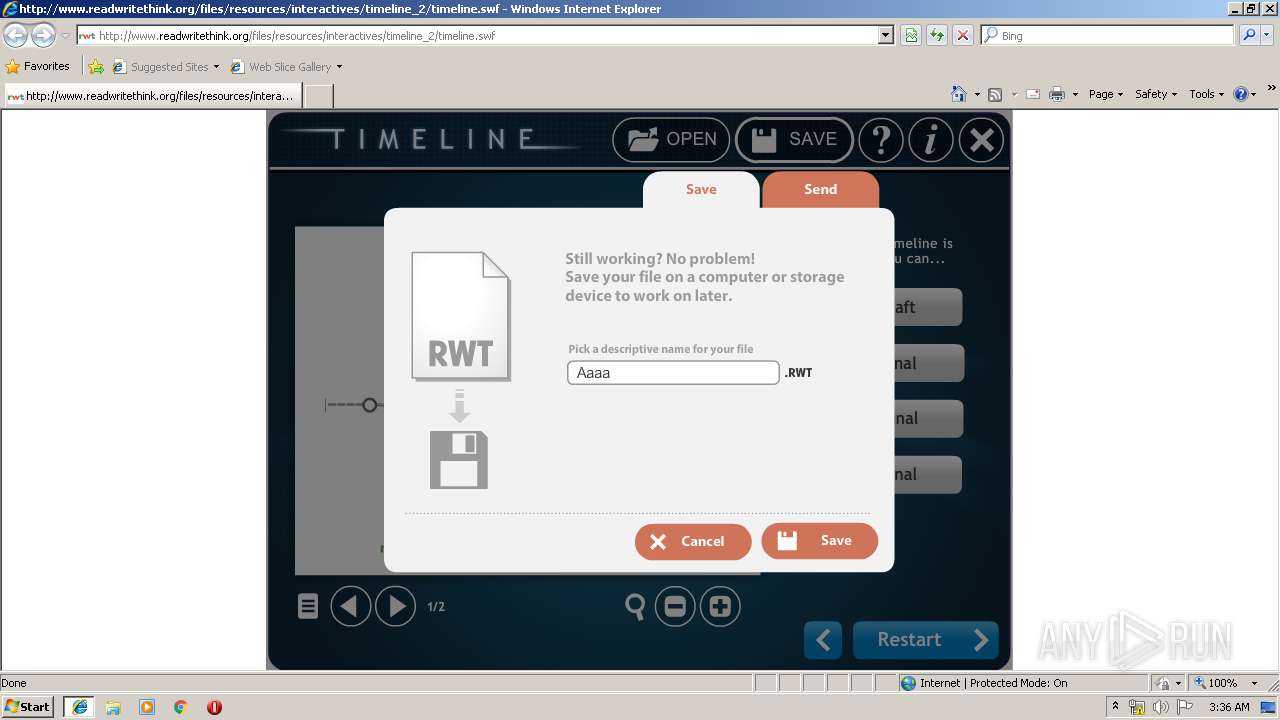
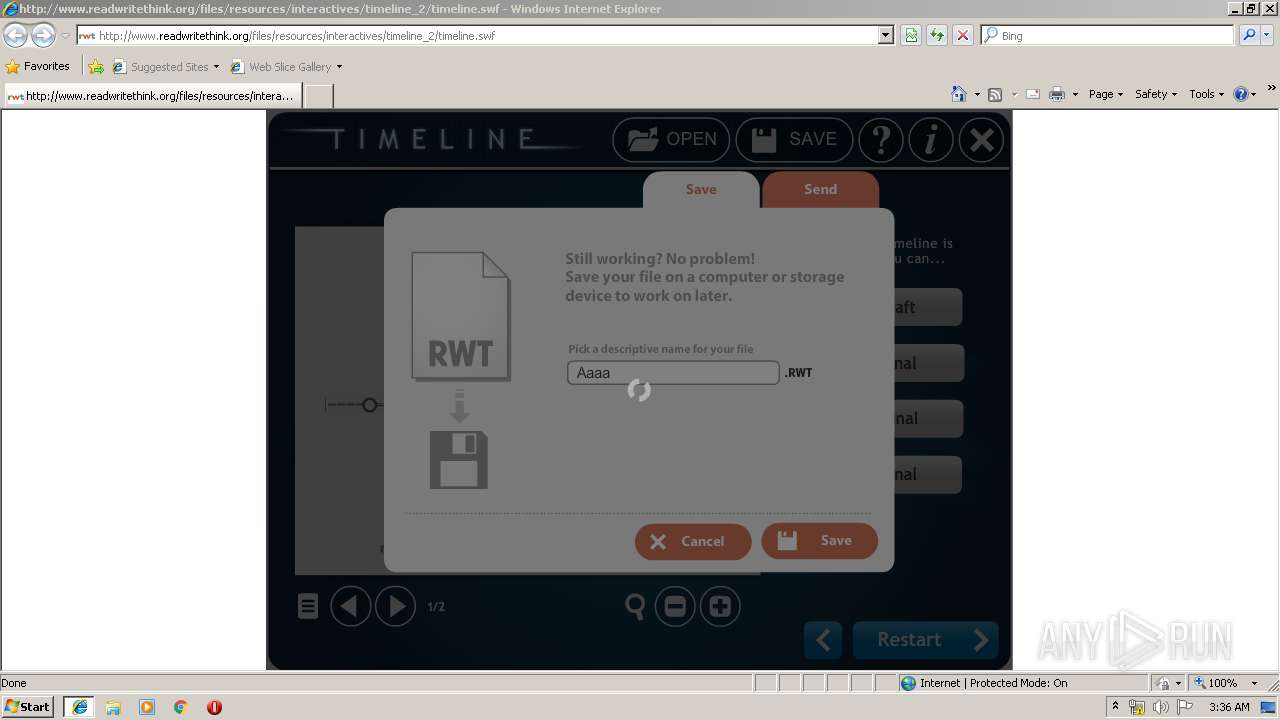
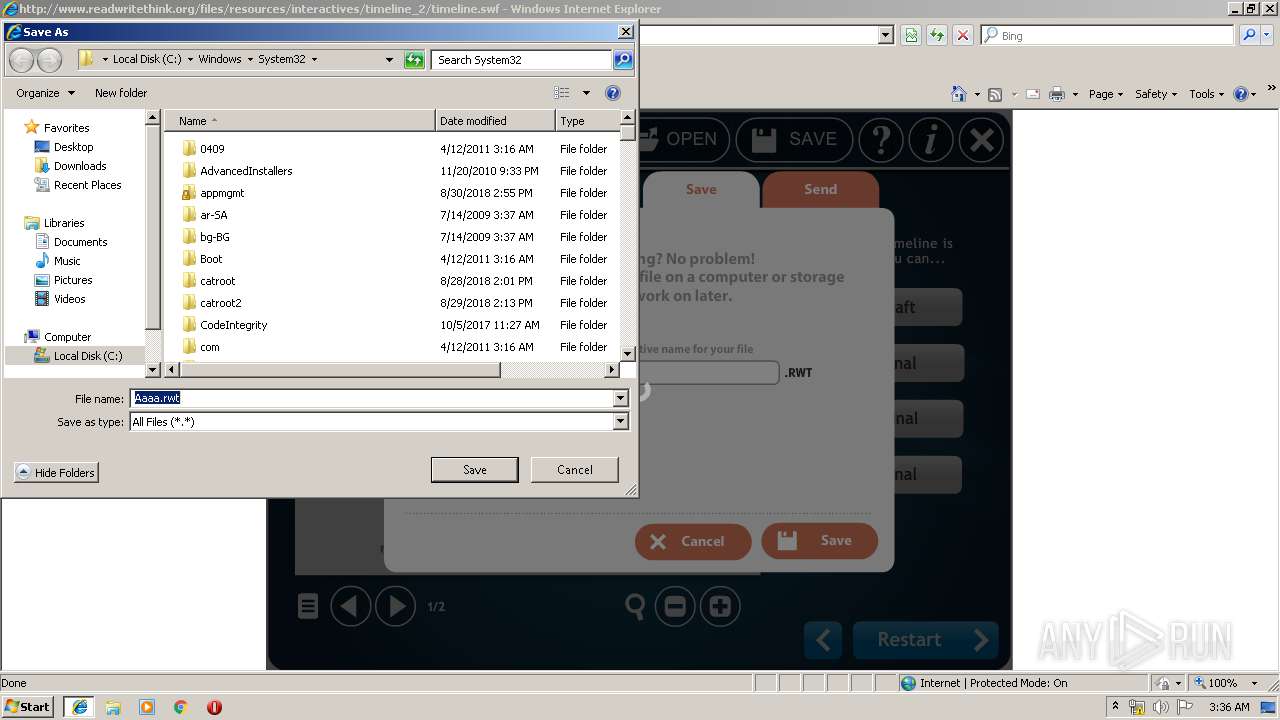
Creates files in the user directory
- iexplore.exe (PID: 1856)
- FlashUtil32_26_0_0_131_ActiveX.exe (PID: 1412)
Changes internet zones settings
- iexplore.exe (PID: 2292)
Reads Internet Cache Settings
- iexplore.exe (PID: 1856)
- iexplore.exe (PID: 2292)
Application launched itself
- iexplore.exe (PID: 2292)
Reads internet explorer settings
- iexplore.exe (PID: 1856)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
37
Monitored processes
3
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1412 | C:\Windows\system32\Macromed\Flash\FlashUtil32_26_0_0_131_ActiveX.exe -Embedding | C:\Windows\system32\Macromed\Flash\FlashUtil32_26_0_0_131_ActiveX.exe | — | svchost.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: MEDIUM Description: Adobe® Flash® Player Installer/Uninstaller 26.0 r0 Exit code: 0 Version: 26,0,0,131 Modules
| |||||||||||||||
| 1856 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2292 CREDAT:71937 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2292 | "C:\Program Files\Internet Explorer\iexplore.exe" http://www.readwritethink.org/files/resources/interactives/timeline_2/timeline.swf | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
1 117
Read events
939
Write events
175
Delete events
3
Modification events
| (PID) Process: | (2292) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2292) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2292) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2292) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Zones |
| Operation: | write | Name: | SecuritySafe |
Value: 1 | |||
| (PID) Process: | (2292) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (2292) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 4600000071000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2292) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Recovery\Active |
| Operation: | write | Name: | {3991BC43-5A70-11E9-A09E-5254004A04AF} |
Value: 0 | |||
| (PID) Process: | (2292) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Type |
Value: 4 | |||
| (PID) Process: | (2292) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Count |
Value: 1 | |||
| (PID) Process: | (2292) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Time |
Value: E3070400020009000200240007007B01 | |||
Executable files
0
Suspicious files
1
Text files
13
Unknown types
28
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2292 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\H6QNMHE9\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 2292 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 1412 | FlashUtil32_26_0_0_131_ActiveX.exe | C:\Users\admin\AppData\Roaming\Macromedia\Flash Player\macromedia.com\support\flashplayer\sys\settings.sxx:Zone.Identifier | — | |
MD5:— | SHA256:— | |||
| 1412 | FlashUtil32_26_0_0_131_ActiveX.exe | C:\Users\admin\AppData\Roaming\Macromedia\Flash Player\macromedia.com\support\flashplayer\sys\settings.sxx | — | |
MD5:— | SHA256:— | |||
| 1412 | FlashUtil32_26_0_0_131_ActiveX.exe | C:\Users\admin\AppData\Roaming\Macromedia\Flash Player\macromedia.com\support\flashplayer\sys\#www.readwritethink.org\settings.sxx:Zone.Identifier | — | |
MD5:— | SHA256:— | |||
| 1412 | FlashUtil32_26_0_0_131_ActiveX.exe | C:\Users\admin\AppData\Roaming\Macromedia\Flash Player\macromedia.com\support\flashplayer\sys\#www.readwritethink.org\settings.sxx | — | |
MD5:— | SHA256:— | |||
| 1412 | FlashUtil32_26_0_0_131_ActiveX.exe | C:\Users\admin\AppData\Roaming\Macromedia\Flash Player\#SharedObjects\T3YJFD83\www.readwritethink.org\files\resources\interactives\timeline_2\timeline.swf\timeline.sxx:Zone.Identifier | — | |
MD5:— | SHA256:— | |||
| 1412 | FlashUtil32_26_0_0_131_ActiveX.exe | C:\Users\admin\AppData\Roaming\Macromedia\Flash Player\#SharedObjects\T3YJFD83\www.readwritethink.org\files\resources\interactives\timeline_2\timeline.swf\timeline.sxx | — | |
MD5:— | SHA256:— | |||
| 1856 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\index.dat | dat | |
MD5:012DF53E841E605905BF9955CB74ABF6 | SHA256:DF99628EDD716EE10C3A4538AD3669C97CA28237D45C43C9F30279EACE09A33E | |||
| 1856 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\History\Low\History.IE5\index.dat | dat | |
MD5:F9C064E008EDDCFFE6A0D212D98913B7 | SHA256:EF9ED0171601274367575CFE7A491DBBF9CD7F200275A0E4A5CF689979C33D76 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
9
TCP/UDP connections
6
DNS requests
3
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1856 | iexplore.exe | GET | 200 | 204.232.153.97:80 | http://www.readwritethink.org/files/resources/interactives/timeline_2/timeline.swf | US | swf | 763 Kb | malicious |
2292 | iexplore.exe | GET | 200 | 204.232.153.97:80 | http://www.readwritethink.org/favicon.ico | US | image | 1.37 Kb | malicious |
1856 | iexplore.exe | GET | 200 | 172.217.17.142:80 | http://www.google-analytics.com/__utm.gif?utmwv=4.3as&utmn=1393535642&utmhn=www.readwritethink.org&utmcs=UTF-8&utmsr=1280x720&utmsc=24-bit&utmul=en&utmje=0&utmfl=15.0%20r0&utmhid=61248934&utmr=-&utmp=/timeline/web/install&utmac=UA-7976532-1&utmcn=1&utmcc=__utma%3D41624993.359658901194700860.1554777371.1554777371.1554777371.1%3B%2B__utmz%3D41624993.1554777371.1.1.utmcsr%3D(direct)%7Cutmccn%3D(direct)%7Cutmcmd%3D(none)%3B | US | image | 35 b | whitelisted |
2292 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
1856 | iexplore.exe | GET | 200 | 172.217.17.142:80 | http://www.google-analytics.com/__utm.gif?utmwv=4.3as&utmn=445077360&utmhn=www.readwritethink.org&utmcs=UTF-8&utmsr=1280x720&utmsc=24-bit&utmul=en&utmje=0&utmfl=15.0%20r0&utmhid=1496068803&utmr=-&utmp=/timeline/web/launch&utmac=UA-7976532-1&utmcn=1&utmcc=__utma%3D41624993.359658901194700860.1554777371.1554777371.1554777371.1%3B%2B__utmz%3D41624993.1554777371.1.1.utmcsr%3D(direct)%7Cutmccn%3D(direct)%7Cutmcmd%3D(none)%3B | US | image | 35 b | whitelisted |
1856 | iexplore.exe | GET | 200 | 172.217.17.142:80 | http://www.google-analytics.com/__utm.gif?utmwv=4.3as&utmn=909146042&utmhn=www.readwritethink.org&utmcs=UTF-8&utmsr=1280x720&utmsc=24-bit&utmul=en&utmje=0&utmfl=15.0%20r0&utmhid=926694669&utmr=-&utmp=/timeline/web/new_project&utmac=UA-7976532-1&utmcn=1&utmcc=__utma%3D41624993.359658901194700860.1554777371.1554777371.1554777371.1%3B%2B__utmz%3D41624993.1554777371.1.1.utmcsr%3D(direct)%7Cutmccn%3D(direct)%7Cutmcmd%3D(none)%3B | US | image | 35 b | whitelisted |
1856 | iexplore.exe | GET | 200 | 172.217.17.142:80 | http://www.google-analytics.com/__utm.gif?utmwv=4.3as&utmn=1172422275&utmhn=www.readwritethink.org&utmcs=UTF-8&utmsr=1280x720&utmsc=24-bit&utmul=en&utmje=0&utmfl=15.0%20r0&utmhid=1060069998&utmr=-&utmp=/timeline/web/new_project&utmac=UA-7976532-1&utmcn=1&utmcc=__utma%3D41624993.359658901194700860.1554777371.1554777371.1554777371.1%3B%2B__utmz%3D41624993.1554777371.1.1.utmcsr%3D(direct)%7Cutmccn%3D(direct)%7Cutmcmd%3D(none)%3B | US | image | 35 b | whitelisted |
1856 | iexplore.exe | GET | 200 | 172.217.17.142:80 | http://www.google-analytics.com/__utm.gif?utmwv=4.3as&utmn=1971667699&utmhn=www.readwritethink.org&utmcs=UTF-8&utmsr=1280x720&utmsc=24-bit&utmul=en&utmje=0&utmfl=15.0%20r0&utmhid=2020471369&utmr=-&utmp=/timeline/web/session&utmac=UA-7976532-1&utmcn=1&utmcc=__utma%3D41624993.359658901194700860.1554777371.1554777371.1554777371.1%3B%2B__utmz%3D41624993.1554777371.1.1.utmcsr%3D(direct)%7Cutmccn%3D(direct)%7Cutmcmd%3D(none)%3B | US | image | 35 b | whitelisted |
1856 | iexplore.exe | GET | — | 204.232.153.97:80 | http://www.readwritethink.org/files/resources/interactives/timeline_2/ | US | — | — | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1856 | iexplore.exe | 204.232.153.97:80 | www.readwritethink.org | Rackspace Ltd. | US | suspicious |
2292 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
2292 | iexplore.exe | 204.232.153.97:80 | www.readwritethink.org | Rackspace Ltd. | US | suspicious |
1856 | iexplore.exe | 172.217.17.142:80 | www.google-analytics.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.readwritethink.org |
| malicious |
www.bing.com |
| whitelisted |
www.google-analytics.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1856 | iexplore.exe | Potential Corporate Privacy Violation | ET POLICY Outdated Flash Version M1 |