| download: | prepaid-expense-tracking-excel.html |
| Full analysis: | https://app.any.run/tasks/eda41778-f068-450c-b726-17595148b9c3 |
| Verdict: | Malicious activity |
| Analysis date: | March 30, 2020, 20:59:51 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | text/html |
| File info: | HTML document, ASCII text, with very long lines, with no line terminators |
| MD5: | 9ADB65AD386E185365688ED147610E18 |
| SHA1: | 8F4A568D8950907EC9B30B92067FA7CE8EDADB24 |
| SHA256: | 5CED403013961BAD560983D51C9B4AFA563EE995F2CB39B7867C3605499AAC93 |
| SSDEEP: | 12:MIuno/KHxVAC59mRCf4IjFCz5eZu+YQKCGD4Kzb0PIm:M/o/WHAiuU7CYZunR5/bMR |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
Application launched itself
- iexplore.exe (PID: 2952)
Reads internet explorer settings
- iexplore.exe (PID: 3492)
- iexplore.exe (PID: 3524)
- iexplore.exe (PID: 1440)
Reads Internet Cache Settings
- iexplore.exe (PID: 2952)
- iexplore.exe (PID: 1440)
Reads settings of System Certificates
- iexplore.exe (PID: 3492)
- iexplore.exe (PID: 3524)
- iexplore.exe (PID: 2952)
- iexplore.exe (PID: 1440)
Changes internet zones settings
- iexplore.exe (PID: 2952)
Creates files in the user directory
- iexplore.exe (PID: 2952)
- iexplore.exe (PID: 1440)
Changes settings of System certificates
- iexplore.exe (PID: 3524)
- iexplore.exe (PID: 3492)
- iexplore.exe (PID: 2952)
Adds / modifies Windows certificates
- iexplore.exe (PID: 3492)
- iexplore.exe (PID: 2952)
- iexplore.exe (PID: 3524)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .html | | | HyperText Markup Language (100) |
|---|
Total processes
39
Monitored processes
4
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1440 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2952 CREDAT:464129 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2952 | "C:\Program Files\Internet Explorer\iexplore.exe" C:\Users\admin\AppData\Local\Temp\prepaid-expense-tracking-excel.html | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3492 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2952 CREDAT:4207618 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3524 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2952 CREDAT:144385 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
15 740
Read events
1 648
Write events
9 472
Delete events
4 620
Modification events
| (PID) Process: | (2952) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: 1126844930 | |||
| (PID) Process: | (2952) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30803670 | |||
| (PID) Process: | (2952) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (2952) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2952) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2952) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2952) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (2952) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 46000000A1000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2952) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2952) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
Executable files
0
Suspicious files
134
Text files
238
Unknown types
65
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1440 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Cab7C5C.tmp | — | |
MD5:— | SHA256:— | |||
| 1440 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Tar7C5D.tmp | — | |
MD5:— | SHA256:— | |||
| 2952 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 1440 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\caf[1].js | text | |
MD5:— | SHA256:— | |||
| 1440 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\5IWPIAR9\99C_code[1].png | image | |
MD5:— | SHA256:— | |||
| 1440 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\84AFE219AEC53B0C9251F5E19EF019BD_2C9D5E6D83DF507CBE6C15521D5D3562 | der | |
MD5:— | SHA256:— | |||
| 1440 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\YTOWV792\feature-illu-dot-com-domain[1].png | image | |
MD5:— | SHA256:— | |||
| 1440 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\icon-afternic-is-this-your-domain-44px[1].png | image | |
MD5:— | SHA256:— | |||
| 1440 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\new_logo_GDTrans[1].png | image | |
MD5:— | SHA256:— | |||
| 1440 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\MNLX2XUF.txt | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
81
TCP/UDP connections
227
DNS requests
73
Threats
18
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
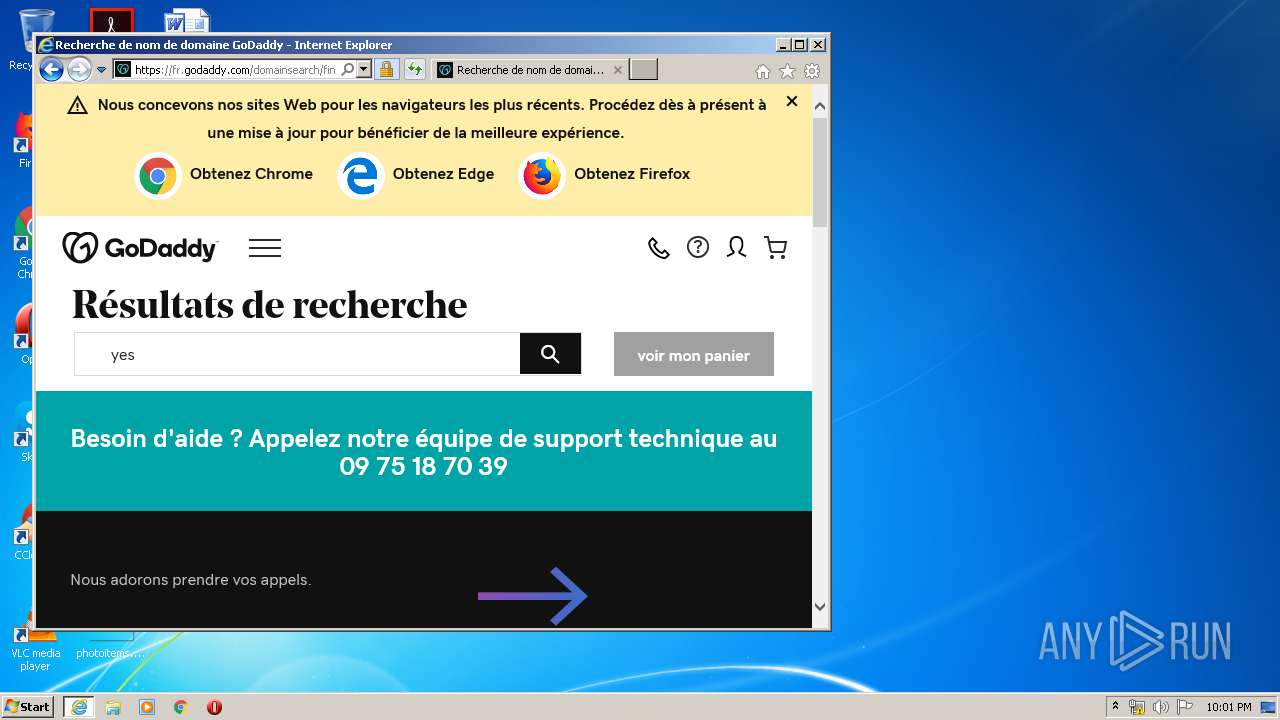
3524 | iexplore.exe | GET | 200 | 104.109.73.120:80 | http://parked-content.godaddy.com/park/pJW6qzS2MTulozSkM3IlraMyMJWyYaOvrt== | NL | html | 267 b | whitelisted |
1440 | iexplore.exe | GET | 200 | 2.16.186.98:80 | http://ak2.imgaft.com/script/jquery-1.3.1.min.js | unknown | text | 23.7 Kb | shared |
1440 | iexplore.exe | GET | 200 | 192.124.249.36:80 | http://ocsp.godaddy.com//MEIwQDA%2BMDwwOjAJBgUrDgMCGgUABBQdI2%2BOBkuXH93foRUj4a7lAr4rGwQUOpqFBxBnKLbv9r0FQW4gwZTaD94CAQc%3D | US | der | 1.69 Kb | whitelisted |
1440 | iexplore.exe | GET | 200 | 104.109.73.120:80 | http://parked-content.godaddy.com/images/99C_code.png | NL | image | 7.42 Kb | whitelisted |
1440 | iexplore.exe | GET | 200 | 192.124.249.41:80 | http://ocsp.godaddy.com//MEIwQDA%2BMDwwOjAJBgUrDgMCGgUABBQdI2%2BOBkuXH93foRUj4a7lAr4rGwQUOpqFBxBnKLbv9r0FQW4gwZTaD94CAQc%3D | US | der | 1.69 Kb | whitelisted |
1440 | iexplore.exe | GET | 200 | 184.168.221.46:80 | http://dominiqueandthemirror.com/?reqp=1&reqr= | US | html | 16.0 Kb | malicious |
3492 | iexplore.exe | GET | 200 | 104.109.73.120:80 | http://parked-content.godaddy.com/park/pJW6qzS2MTulozSkM3IlraMyMJWyYaOvrt== | NL | html | 267 b | whitelisted |
1440 | iexplore.exe | GET | 200 | 216.58.210.4:80 | http://www.google.com/adsense/domains/caf.js | US | text | 56.0 Kb | malicious |
1440 | iexplore.exe | GET | 200 | 192.124.249.23:80 | http://ocsp.starfieldtech.com//MEIwQDA%2BMDwwOjAJBgUrDgMCGgUABBQUwPiEZQ6%2FsVZNPaFToNfxx8ZwqAQUfAwyH6fZMH%2FEfWijYqihzqsHWycCAQc%3D | US | der | 1.74 Kb | whitelisted |
1440 | iexplore.exe | GET | 502 | 184.168.221.46:80 | http://dominiqueandthemirror.com/?reqp=1&reqr= | US | text | 294 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3492 | iexplore.exe | 104.109.73.120:80 | — | Akamai International B.V. | NL | whitelisted |
— | — | 104.109.73.120:80 | — | Akamai International B.V. | NL | whitelisted |
1440 | iexplore.exe | 216.58.210.4:80 | www.google.com | Google Inc. | US | whitelisted |
1440 | iexplore.exe | 184.168.221.46:80 | dominiqueandthemirror.com | GoDaddy.com, LLC | US | malicious |
1440 | iexplore.exe | 23.8.15.19:443 | www.godaddy.com | Akamai International B.V. | NL | suspicious |
1440 | iexplore.exe | 192.124.249.41:80 | ocsp.godaddy.com | Sucuri | US | suspicious |
1440 | iexplore.exe | 192.124.249.36:80 | ocsp.godaddy.com | Sucuri | US | suspicious |
1440 | iexplore.exe | 216.58.210.4:443 | www.google.com | Google Inc. | US | whitelisted |
2952 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
1440 | iexplore.exe | 104.111.235.54:443 | img1.wsimg.com | Akamai International B.V. | NL | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
parked-content.godaddy.com |
| whitelisted |
dominiqueandthemirror.com |
| malicious |
www.google.com |
| malicious |
www.godaddy.com |
| whitelisted |
ak2.imgaft.com |
| shared |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.godaddy.com |
| whitelisted |
img1.wsimg.com |
| whitelisted |
ocsp.starfieldtech.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1440 | iexplore.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
1440 | iexplore.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
1440 | iexplore.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
1440 | iexplore.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
1440 | iexplore.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
1440 | iexplore.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
1440 | iexplore.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
1440 | iexplore.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
1440 | iexplore.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
1440 | iexplore.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |