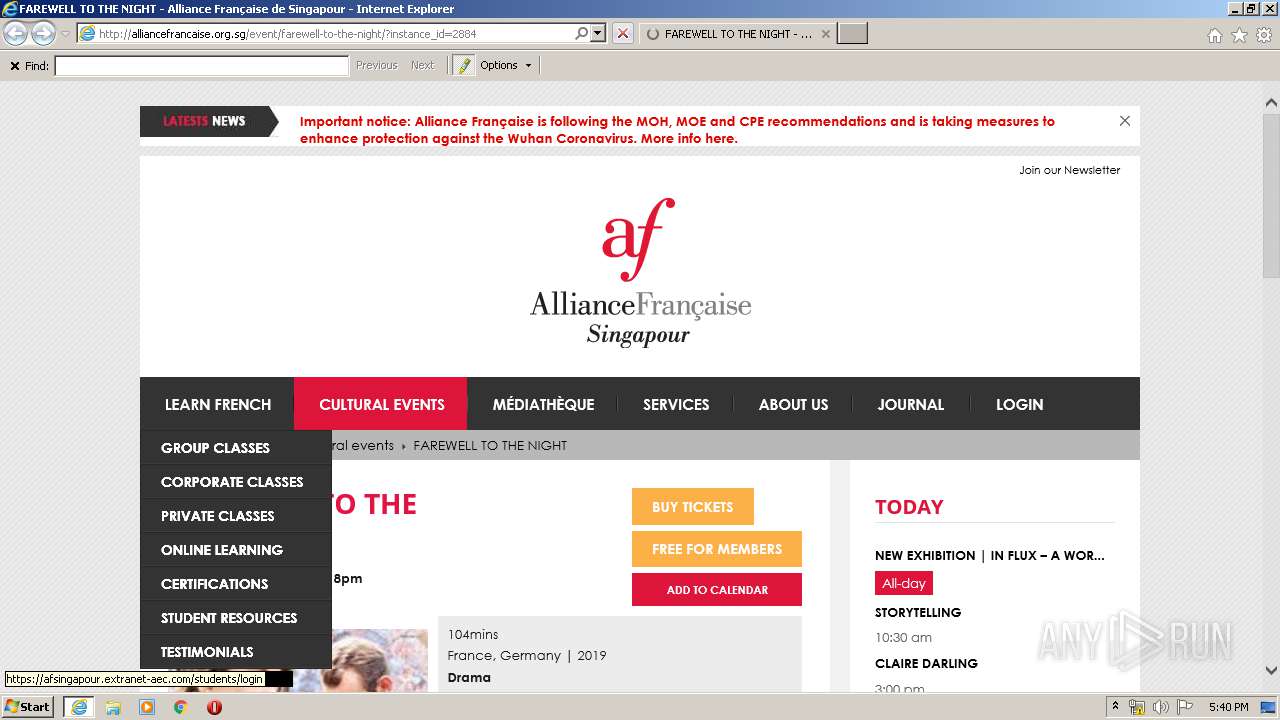
| URL: | http://alliancefrancaise.org.sg/event/farewell-to-the-night/?instance_id=2884 |
| Full analysis: | https://app.any.run/tasks/9e69ff78-e78c-4440-a239-a7e304e2a129 |
| Verdict: | Malicious activity |
| Analysis date: | February 21, 2020, 17:37:44 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 46DC43C439130D5585F1272036FDD1D6 |
| SHA1: | B360C431BB8CDA90D9BB159E7AD66FD4F2FB3061 |
| SHA256: | 5CE91A1CDF171D5E6F6D7D12F6A3D8681C9E10571E358DBCB7E9718AEE573605 |
| SSDEEP: | 3:N1KfsELX5wDQS7Kh23KCLn:CkETy0+L |
MALICIOUS
Connects to CnC server
- iexplore.exe (PID: 3600)
SUSPICIOUS
No suspicious indicators.INFO
Reads Internet Cache Settings
- iexplore.exe (PID: 2108)
- iexplore.exe (PID: 3600)
Changes internet zones settings
- iexplore.exe (PID: 2108)
Application launched itself
- iexplore.exe (PID: 2108)
Dropped object may contain Bitcoin addresses
- iexplore.exe (PID: 3600)
Reads settings of System Certificates
- iexplore.exe (PID: 3600)
- iexplore.exe (PID: 2108)
Creates files in the user directory
- iexplore.exe (PID: 2108)
- iexplore.exe (PID: 3600)
Reads internet explorer settings
- iexplore.exe (PID: 3600)
Adds / modifies Windows certificates
- iexplore.exe (PID: 2108)
Changes settings of System certificates
- iexplore.exe (PID: 2108)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
41
Monitored processes
2
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2108 | "C:\Program Files\Internet Explorer\iexplore.exe" "http://alliancefrancaise.org.sg/event/farewell-to-the-night/?instance_id=2884" | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3600 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2108 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
6 192
Read events
445
Write events
3 880
Delete events
1 867
Modification events
| (PID) Process: | (3600) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\LowCache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (3600) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\LowCache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (3600) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\LowCache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2108) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: 3131657138 | |||
| (PID) Process: | (2108) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30795997 | |||
| (PID) Process: | (2108) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (2108) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2108) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2108) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2108) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
Executable files
0
Suspicious files
62
Text files
215
Unknown types
40
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3600 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\style[1].css | text | |
MD5:— | SHA256:— | |||
| 3600 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\farewell-to-the-night[1].htm | html | |
MD5:— | SHA256:— | |||
| 3600 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\sb-instagram[1].css | text | |
MD5:— | SHA256:— | |||
| 3600 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\YTOWV792\overrides[1].css | text | |
MD5:— | SHA256:— | |||
| 2108 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 3600 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\YTOWV792\style[1].css | text | |
MD5:— | SHA256:— | |||
| 3600 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\css[1].css | text | |
MD5:— | SHA256:— | |||
| 3600 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\font-awesome.min[1].css | text | |
MD5:FEDA974A77EA5783B8BE673F142B7C88 | SHA256:0FB1BBCA73646E8E2B93C82E8D8B219647B13D4B440C48E338290B9A685B8DE1 | |||
| 3600 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\5IWPIAR9\20c1f9347f59cf976e[1].js | text | |
MD5:— | SHA256:— | |||
| 3600 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\plugin[1].css | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
178
TCP/UDP connections
148
DNS requests
40
Threats
8
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3600 | iexplore.exe | GET | 200 | 64.58.126.236:80 | http://datapro.website/optout/set/lat?jsonp=__mtz_cb_368567277&key=20c1f9347f59cf976e&cv=1574223961&t=1574223960843 | US | — | — | malicious |
3600 | iexplore.exe | GET | 200 | 64.58.126.236:80 | http://datapro.website/optout/set/lt?jsonp=__mtz_cb_286668838&key=20c1f9347f59cf976e&cv=432168&t=1574223957907 | US | — | — | malicious |
3600 | iexplore.exe | GET | 200 | 64.58.126.236:80 | http://datapro.website/optout/set/lat?jsonp=__mtz_cb_132637301&key=20c1f9347f59cf976e&cv=1574223958&t=1574223957907 | US | — | — | malicious |
3600 | iexplore.exe | GET | 200 | 101.100.211.41:80 | http://alliancefrancaise.org.sg/wp-content/plugins/all-in-one-event-calendar/cache/274060ef_ai1ec_parsed_css.css | SG | text | 204 Kb | malicious |
3600 | iexplore.exe | GET | 200 | 101.100.211.41:80 | http://alliancefrancaise.org.sg/?wpss-routing=custom-css | SG | compressed | 4.76 Kb | malicious |
3600 | iexplore.exe | GET | 200 | 101.100.211.41:80 | http://alliancefrancaise.org.sg/wp-content/plugins/gplus-comments/assets/styles/plugin.css | SG | text | 1.20 Kb | malicious |
3600 | iexplore.exe | GET | 200 | 101.100.211.41:80 | http://alliancefrancaise.org.sg/wp-content/plugins/mailchimp//css/flick/flick.css | SG | text | 4.76 Kb | malicious |
3600 | iexplore.exe | GET | 200 | 101.100.211.41:80 | http://alliancefrancaise.org.sg/wp-content/plugins/youtube-embed/css/main.min.css | SG | text | 154 b | malicious |
3600 | iexplore.exe | GET | 200 | 172.217.22.10:80 | http://ajax.googleapis.com/ajax/libs/jqueryui/1.9.2/jquery-ui.min.js | US | text | 61.1 Kb | whitelisted |
3600 | iexplore.exe | GET | 200 | 101.100.211.41:80 | http://alliancefrancaise.org.sg/wp-content/cache/min/1/mailchimpSF_main_css.css | SG | text | 373 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3600 | iexplore.exe | 172.217.22.42:80 | fonts.googleapis.com | Google Inc. | US | whitelisted |
3600 | iexplore.exe | 101.100.211.41:80 | alliancefrancaise.org.sg | Vodien Internet Solutions Pte Ltd | SG | malicious |
3600 | iexplore.exe | 209.197.3.15:80 | netdna.bootstrapcdn.com | Highwinds Network Group, Inc. | US | whitelisted |
3600 | iexplore.exe | 172.217.22.10:80 | ajax.googleapis.com | Google Inc. | US | whitelisted |
3600 | iexplore.exe | 104.20.19.70:80 | www.powr.io | Cloudflare Inc | US | shared |
2108 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
3600 | iexplore.exe | 104.20.19.70:443 | www.powr.io | Cloudflare Inc | US | shared |
3600 | iexplore.exe | 151.139.128.14:80 | ocsp.trust-provider.com | Highwinds Network Group, Inc. | US | suspicious |
3600 | iexplore.exe | 172.217.18.168:443 | ssl.google-analytics.com | Google Inc. | US | whitelisted |
3600 | iexplore.exe | 216.58.207.46:80 | www.google-analytics.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
alliancefrancaise.org.sg |
| malicious |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
netdna.bootstrapcdn.com |
| whitelisted |
ajax.googleapis.com |
| whitelisted |
plankjock.com |
| malicious |
datapro.website |
| malicious |
www.powr.io |
| shared |
ocsp.trust-provider.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3600 | iexplore.exe | A Network Trojan was detected | ET MALWARE LNKR landing page (possible compromised site) M3 |
3600 | iexplore.exe | A Network Trojan was detected | ET MALWARE LNKR landing page (possible compromised site) M4 |
3600 | iexplore.exe | A Network Trojan was detected | ET MALWARE LNKR CnC Activity M1 |
3600 | iexplore.exe | A Network Trojan was detected | ET MALWARE LNKR CnC Activity M3 |
3600 | iexplore.exe | A Network Trojan was detected | ET MALWARE LNKR landing page (possible compromised site) M3 |
3600 | iexplore.exe | A Network Trojan was detected | ET MALWARE LNKR landing page (possible compromised site) M4 |
3600 | iexplore.exe | A Network Trojan was detected | ET MALWARE LNKR CnC Activity M1 |
3600 | iexplore.exe | A Network Trojan was detected | ET MALWARE LNKR CnC Activity M3 |