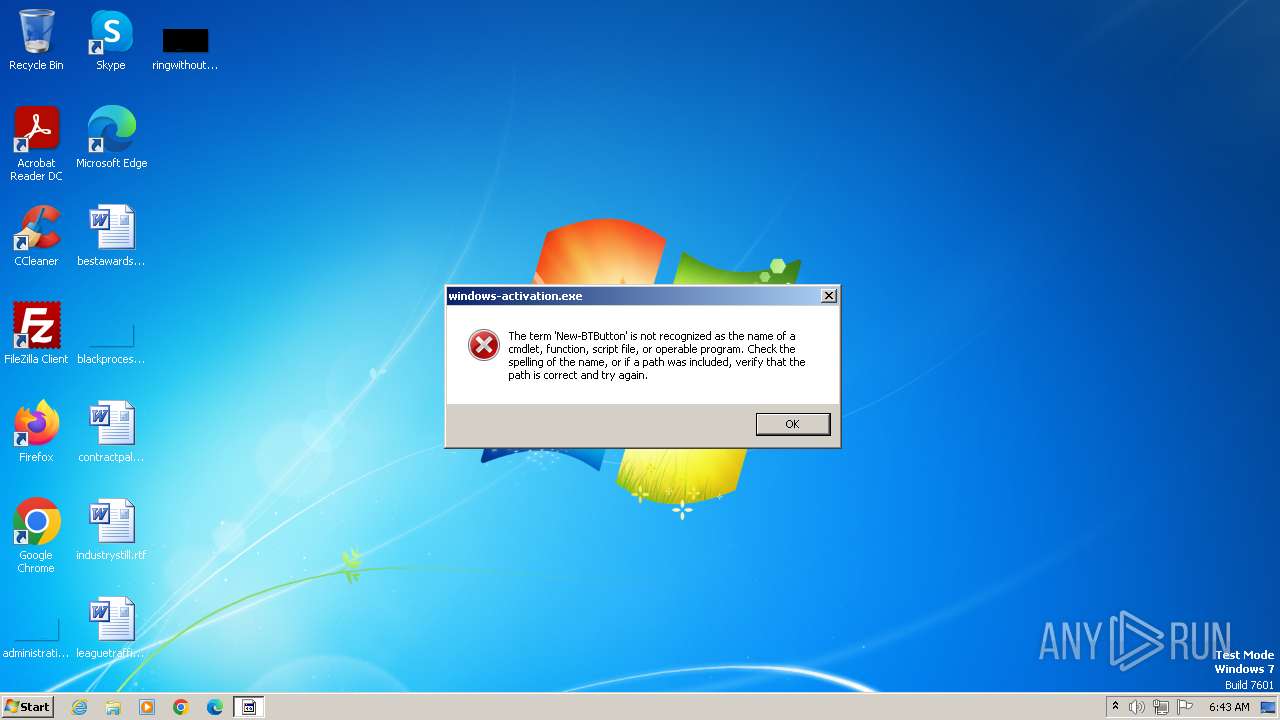
| File name: | windows-activation.exe |
| Full analysis: | https://app.any.run/tasks/cf74d635-4c6c-48bd-9ded-24f14527672e |
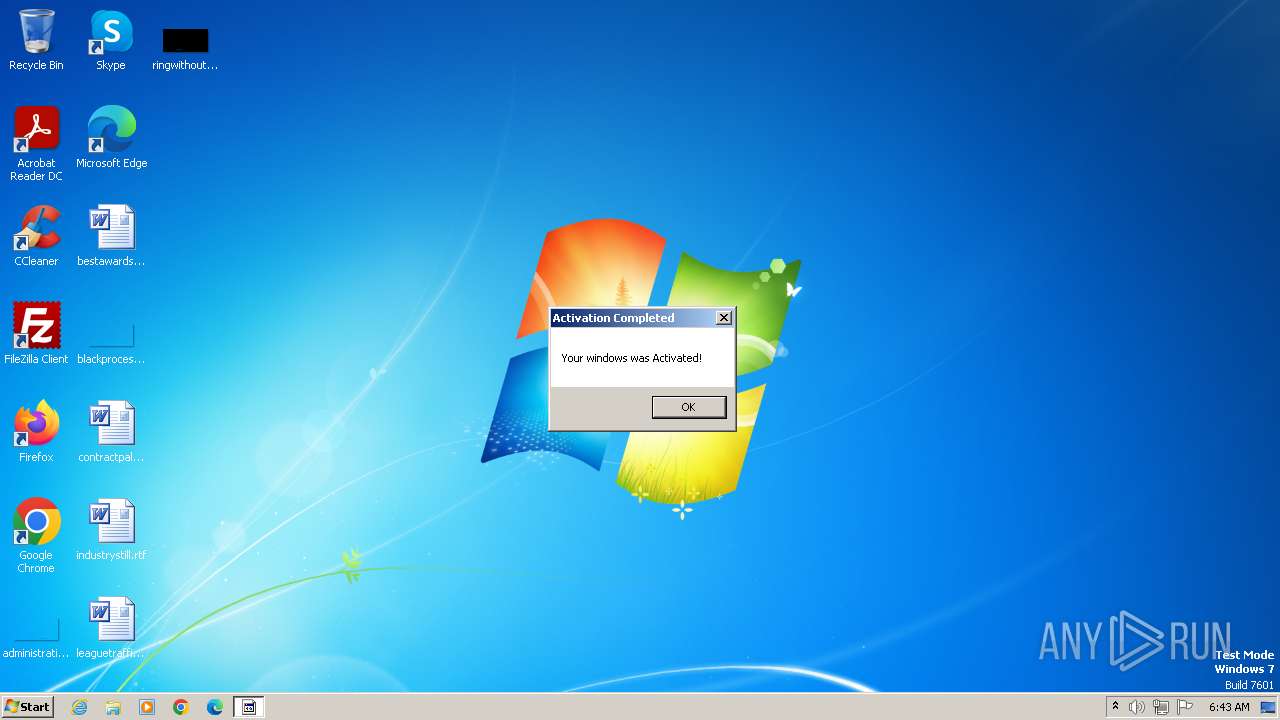
| Verdict: | Malicious activity |
| Analysis date: | May 17, 2024, 05:42:28 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows |
| MD5: | 04923B22F4F342A06A485B6B50869FB7 |
| SHA1: | E9AF5CE18039D6630970ED4FD9A17E56F8A3844C |
| SHA256: | 5CDF578561F1CE44491D6ABC000E8CA89B82561D1F8E2E716BF75E11C5D07CAE |
| SSDEEP: | 768:bmqVcVrESRzLsskjpjQhnCXbOfq10koCseQ:pSVrEKzAsAJbOgoC0 |
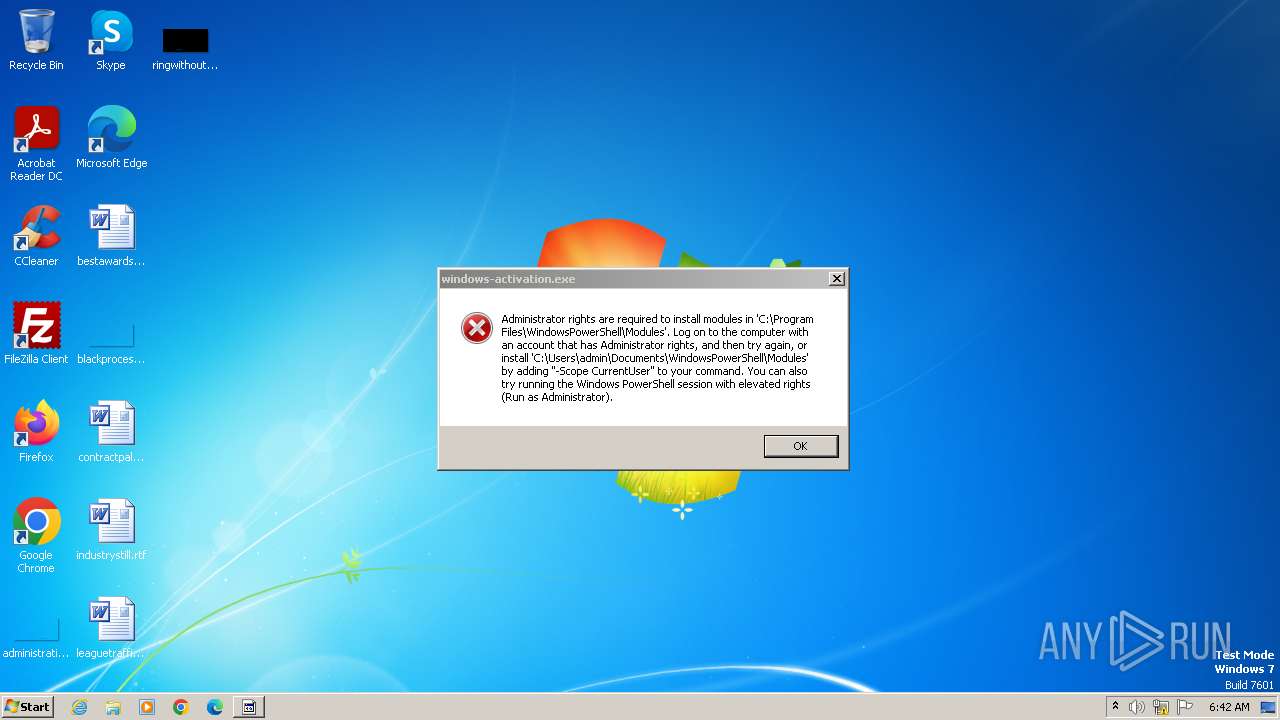
MALICIOUS
Drops the executable file immediately after the start
- windows-activation.exe (PID: 3976)
- csc.exe (PID: 1292)
Starts Visual C# compiler
- windows-activation.exe (PID: 3976)
SUSPICIOUS
Reads security settings of Internet Explorer
- windows-activation.exe (PID: 3976)
Gets or sets the security protocol (POWERSHELL)
- windows-activation.exe (PID: 3976)
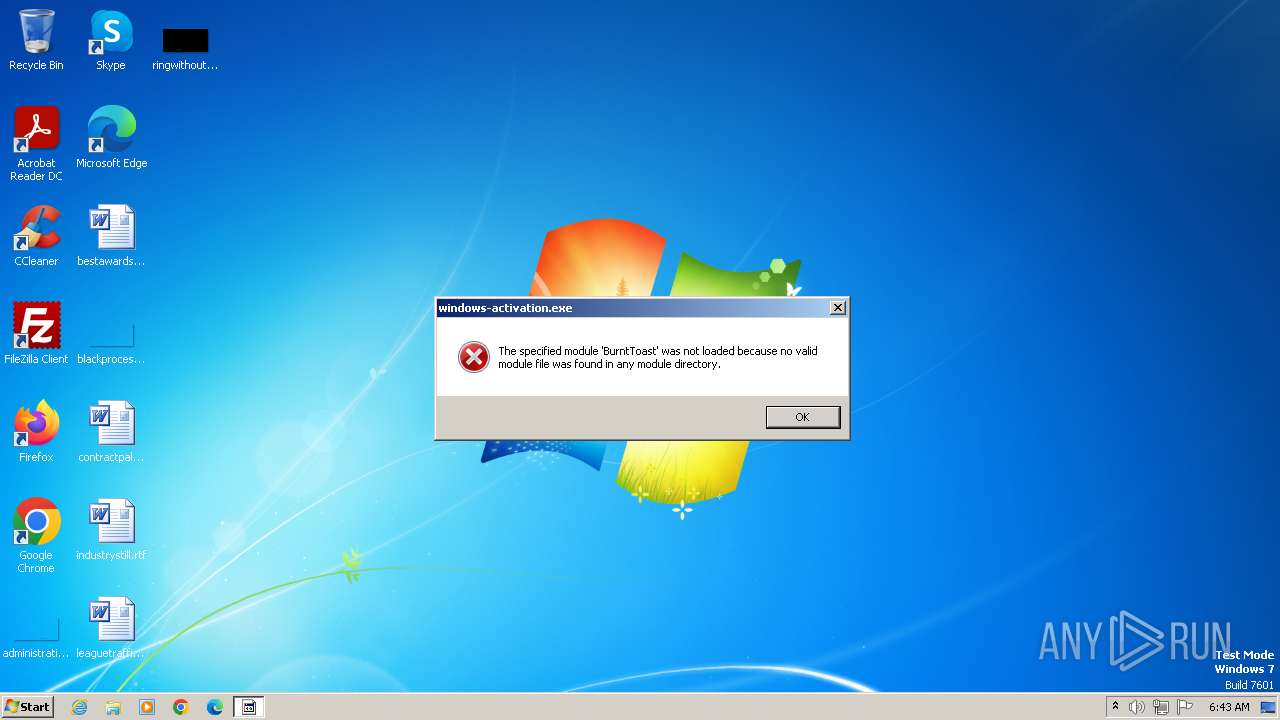
Uses RUNDLL32.EXE to load library
- windows-activation.exe (PID: 3976)
Reads the Internet Settings
- windows-activation.exe (PID: 3976)
- sipnotify.exe (PID: 1060)
Uses .NET C# to load dll
- windows-activation.exe (PID: 3976)
Gets path to any of the special folders (POWERSHELL)
- windows-activation.exe (PID: 3976)
Checks Windows Trust Settings
- windows-activation.exe (PID: 3976)
Executable content was dropped or overwritten
- csc.exe (PID: 1292)
The process executes via Task Scheduler
- sipnotify.exe (PID: 1060)
Executes as Windows Service
- EOSNotify.exe (PID: 304)
Reads settings of System Certificates
- sipnotify.exe (PID: 1060)
- windows-activation.exe (PID: 3976)
INFO
Checks supported languages
- windows-activation.exe (PID: 3976)
- csc.exe (PID: 1292)
- cvtres.exe (PID: 2316)
- wmpnscfg.exe (PID: 2008)
Reads the computer name
- windows-activation.exe (PID: 3976)
- wmpnscfg.exe (PID: 2008)
Reads Environment values
- windows-activation.exe (PID: 3976)
Reads the machine GUID from the registry
- windows-activation.exe (PID: 3976)
- csc.exe (PID: 1292)
- cvtres.exe (PID: 2316)
Create files in a temporary directory
- windows-activation.exe (PID: 3976)
- csc.exe (PID: 1292)
- cvtres.exe (PID: 2316)
Reads the software policy settings
- windows-activation.exe (PID: 3976)
- sipnotify.exe (PID: 1060)
Reads security settings of Internet Explorer
- sipnotify.exe (PID: 1060)
Manual execution by a user
- wmpnscfg.exe (PID: 2008)
Disables trace logs
- windows-activation.exe (PID: 3976)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (55.8) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (21) |
| .scr | | | Windows screen saver (9.9) |
| .dll | | | Win32 Dynamic Link Library (generic) (5) |
| .exe | | | Win32 Executable (generic) (3.4) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2024:02:02 10:49:47+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 11 |
| CodeSize: | 34816 |
| InitializedDataSize: | 2048 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xa75e |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 0.0.0.0 |
| ProductVersionNumber: | 0.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| FileDescription: | |
| FileVersion: | 0.0.0.0 |
| InternalName: | file.exe |
| LegalCopyright: | |
| OriginalFileName: | file.exe |
| ProductVersion: | 0.0.0.0 |
| AssemblyVersion: | 0.0.0.0 |
Total processes
41
Monitored processes
7
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 304 | C:\Windows\system32\EOSNotify.exe | C:\Windows\System32\EOSNotify.exe | — | services.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: EOS Notification Exit code: 0 Version: 6.1.7601.24544 (win7sp1_ldr_escrow.191230-1647) Modules
| |||||||||||||||
| 1060 | C:\Windows\system32\sipnotify.exe -LogonOrUnlock | C:\Windows\System32\sipnotify.exe | taskeng.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: sipnotify Exit code: 0 Version: 6.1.7602.20480 (win7sp1_ldr_escrow.191010-1716) Modules
| |||||||||||||||
| 1292 | "C:\Windows\Microsoft.NET\Framework\v4.0.30319\csc.exe" /noconfig /fullpaths @"C:\Users\admin\AppData\Local\Temp\tkpxi5ju.cmdline" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\csc.exe | windows-activation.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Visual C# Command Line Compiler Exit code: 0 Version: 4.8.3761.0 built by: NET48REL1 Modules
| |||||||||||||||
| 2008 | "C:\Program Files\Windows Media Player\wmpnscfg.exe" | C:\Program Files\Windows Media Player\wmpnscfg.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Media Player Network Sharing Service Configuration Application Exit code: 0 Version: 12.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2316 | C:\Windows\Microsoft.NET\Framework\v4.0.30319\cvtres.exe /NOLOGO /READONLY /MACHINE:IX86 "/OUT:C:\Users\admin\AppData\Local\Temp\RES44EA.tmp" "c:\Users\admin\AppData\Local\Temp\CSC82B42FA7C574564966593C4E981DEC0.TMP" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\cvtres.exe | — | csc.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft® Resource File To COFF Object Conversion Utility Exit code: 0 Version: 14.10.25028.0 built by: VCTOOLSD15RTM Modules
| |||||||||||||||
| 3976 | "C:\Users\admin\AppData\Local\Temp\windows-activation.exe" | C:\Users\admin\AppData\Local\Temp\windows-activation.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: Version: 0.0.0.0 Modules
| |||||||||||||||
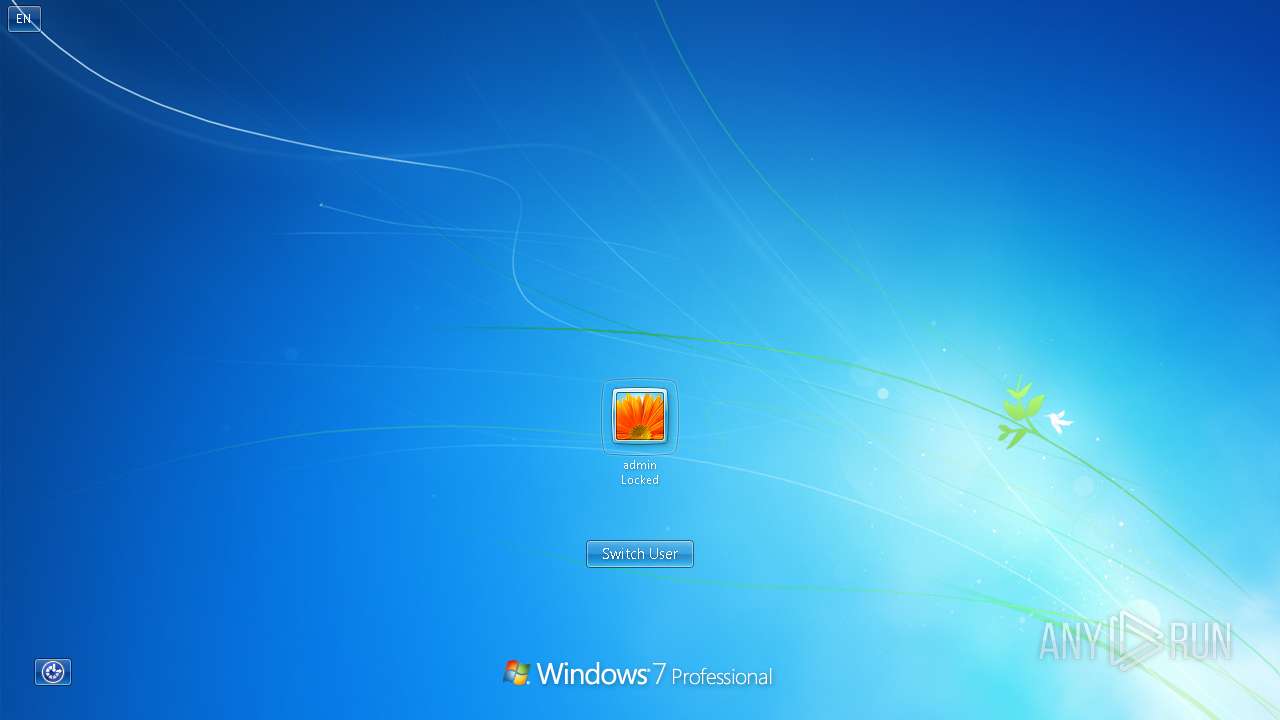
| 4048 | "C:\Windows\system32\rundll32.exe" user32.dll,LockWorkStation | C:\Windows\System32\rundll32.exe | — | windows-activation.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
10 337
Read events
10 270
Write events
55
Delete events
12
Modification events
| (PID) Process: | (3976) windows-activation.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (3976) windows-activation.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (3976) windows-activation.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (3976) windows-activation.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (1060) sipnotify.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\182\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (1060) sipnotify.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\EnterpriseCertificates\Root\Certificates |
| Operation: | delete value | Name: | 9F6134C5FA75E4FDDE631B232BE961D6D4B97DB6 |
Value: | |||
| (PID) Process: | (1060) sipnotify.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\EnterpriseCertificates\Root\Certificates\9F6134C5FA75E4FDDE631B232BE961D6D4B97DB6 |
| Operation: | write | Name: | Blob |
Value: 0F00000001000000200000009065F32AFC2CFEA7F452D2D6BE94D20C877EFC1C05433D9935696193FDCC05D80300000001000000140000009F6134C5FA75E4FDDE631B232BE961D6D4B97DB6200000000100000047030000308203433082022BA00302010202147327B7C17D5AE708EF73F1F45A79D78B4E99A29F300D06092A864886F70D01010B05003031310B3009060355040613025553310F300D06035504080C06426F73746F6E3111300F060355040A0C084469676943657274301E170D3233303932393130353030335A170D3339303530383130353030335A3031310B3009060355040613025553310F300D06035504080C06426F73746F6E3111300F060355040A0C08446967694365727430820122300D06092A864886F70D01010105000382010F003082010A0282010100D91B7A55548F44F3E97C493153B75B055695736B184640D7335A2E6218083B5A1BEE2695209350E57A3EB76FBC604CB3B250DF3D9D0C560D1FBDFE30108D233A3C555100BE1A3F8E543C0B253E06E91B6D5F9CB3A093009BC8B4D3A0EB19DB59E56DA7E3D637847970D6C2AEB4A1FCF3896A7C080FE68759BAA62E6AAA8B7C7CBDA176DDC72F8D259A16D3469E31F19D2959904611D730D7D26FCFED789A0C49698FDFABF3F6727D08C61A073BB11E85C96486D49B0E0D38364C008A5EB964F8813C5DF004F9E76D2F8DB90702D800032674959BF0DF823785419101CEA928A10ACBAE7E48FE19202F3CB7BCF416476D17CB64C5570FCED443BD75D9F2C632FF0203010001A3533051301D0603551D0E041604145D6CA352CEFC713CBBC5E21F663C3639FD19D4D7301F0603551D230418301680145D6CA352CEFC713CBBC5E21F663C3639FD19D4D7300F0603551D130101FF040530030101FF300D06092A864886F70D01010B05000382010100AF2218E4CA18144728FCC76EA14958061522FD4A018BED1A4BFCC5CCE70BC6AE9DF7D3795C9A010D53628E2B6E7C10D6B07E53546235A5EE480E5A434E312154BF1E39AAC27D2C18D4F41CBBECFE4538CEF93EF62C17D187A7F720F4A9478410D09620C9F8B293B5786A5440BC0743B7B7753CF66FBA498B7E083BC267597238DC031B9BB131F997D9B8164AAED0D6E328420E53E1969DA6CD035078179677A7177BB2BF9C87CF592910CD380E8501B92040A39469C782BA383BEAE498C060FCC7C429BC10B7B6B7A0659C9BE03DC13DB46C638CF5E3B22A303726906DC8DD91C64501EBFC282A3A497EC430CACC066EE4BF9C5C8F2F2A05D0C1921A9E3E85E3 | |||
| (PID) Process: | (1060) sipnotify.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\EnterpriseCertificates\Root\Certificates\9F6134C5FA75E4FDDE631B232BE961D6D4B97DB6 |
| Operation: | delete value | Name: | File |
Value: | |||
| (PID) Process: | (1060) sipnotify.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\EnterpriseCertificates\Root\Certificates\9F6134C5FA75E4FDDE631B232BE961D6D4B97DB6 |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (1060) sipnotify.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\EnterpriseCertificates\Root\Certificates\9F6134C5FA75E4FDDE631B232BE961D6D4B97DB6 |
| Operation: | write | Name: | Blob |
Value: 1400000001000000140000005D6CA352CEFC713CBBC5E21F663C3639FD19D4D70300000001000000140000009F6134C5FA75E4FDDE631B232BE961D6D4B97DB6200000000100000047030000308203433082022BA00302010202147327B7C17D5AE708EF73F1F45A79D78B4E99A29F300D06092A864886F70D01010B05003031310B3009060355040613025553310F300D06035504080C06426F73746F6E3111300F060355040A0C084469676943657274301E170D3233303932393130353030335A170D3339303530383130353030335A3031310B3009060355040613025553310F300D06035504080C06426F73746F6E3111300F060355040A0C08446967694365727430820122300D06092A864886F70D01010105000382010F003082010A0282010100D91B7A55548F44F3E97C493153B75B055695736B184640D7335A2E6218083B5A1BEE2695209350E57A3EB76FBC604CB3B250DF3D9D0C560D1FBDFE30108D233A3C555100BE1A3F8E543C0B253E06E91B6D5F9CB3A093009BC8B4D3A0EB19DB59E56DA7E3D637847970D6C2AEB4A1FCF3896A7C080FE68759BAA62E6AAA8B7C7CBDA176DDC72F8D259A16D3469E31F19D2959904611D730D7D26FCFED789A0C49698FDFABF3F6727D08C61A073BB11E85C96486D49B0E0D38364C008A5EB964F8813C5DF004F9E76D2F8DB90702D800032674959BF0DF823785419101CEA928A10ACBAE7E48FE19202F3CB7BCF416476D17CB64C5570FCED443BD75D9F2C632FF0203010001A3533051301D0603551D0E041604145D6CA352CEFC713CBBC5E21F663C3639FD19D4D7301F0603551D230418301680145D6CA352CEFC713CBBC5E21F663C3639FD19D4D7300F0603551D130101FF040530030101FF300D06092A864886F70D01010B05000382010100AF2218E4CA18144728FCC76EA14958061522FD4A018BED1A4BFCC5CCE70BC6AE9DF7D3795C9A010D53628E2B6E7C10D6B07E53546235A5EE480E5A434E312154BF1E39AAC27D2C18D4F41CBBECFE4538CEF93EF62C17D187A7F720F4A9478410D09620C9F8B293B5786A5440BC0743B7B7753CF66FBA498B7E083BC267597238DC031B9BB131F997D9B8164AAED0D6E328420E53E1969DA6CD035078179677A7177BB2BF9C87CF592910CD380E8501B92040A39469C782BA383BEAE498C060FCC7C429BC10B7B6B7A0659C9BE03DC13DB46C638CF5E3B22A303726906DC8DD91C64501EBFC282A3A497EC430CACC066EE4BF9C5C8F2F2A05D0C1921A9E3E85E3 | |||
Executable files
1
Suspicious files
6
Text files
9
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3976 | windows-activation.exe | C:\Users\admin\AppData\Local\Temp\tkpxi5ju.0.cs | text | |
MD5:A29444398AC9A819C5D208948B81A14C | SHA256:F447865E0C75B6C39BECAB9B9527FCC583DEF24C18A66CC815A9419F375DDC11 | |||
| 3976 | windows-activation.exe | C:\Users\admin\AppData\Local\Temp\j2kicj0e.li1.ps1 | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:— | |||
| 1060 | sipnotify.exe | C:\Users\admin\AppData\Local\microsoft\windows\SipNotify\eoscontent\metadata.json | binary | |
MD5:E8A970BA6CE386EED9A5E724F26212A6 | SHA256:7E06107D585D8FC7870998F3856DCC3E35800AA97E4406AAB83BC8444B6CBDE3 | |||
| 1292 | csc.exe | C:\Users\admin\AppData\Local\Temp\tkpxi5ju.dll | executable | |
MD5:2F4EDDE85EA57864BA90BDC847D51A78 | SHA256:490D20D7291F82AE7F3D5953BB1CD25C08D07821F0E91D99FBE563DB29002D39 | |||
| 1292 | csc.exe | C:\Users\admin\AppData\Local\Temp\tkpxi5ju.out | text | |
MD5:6355380EA8BDDE3E141484F2AAE169D1 | SHA256:D1A7F1572B923C8158986834846F9CD332971E0F2F9797606D0E6E49853DB16B | |||
| 1060 | sipnotify.exe | C:\Users\admin\AppData\Local\microsoft\windows\SipNotify\eoscontent\en-us.html | html | |
MD5:9752942B57692148B9F614CF4C119A36 | SHA256:E31B834DD53FA6815F396FC09C726636ABF98F3367F0CF1590EF5EB3801C75D1 | |||
| 1060 | sipnotify.exe | C:\Users\admin\AppData\Local\microsoft\windows\SipNotify\eoscontent\script.js | text | |
MD5:A2682382967C351F7ED21762F9E5DE9E | SHA256:36B1D26F1EC69685648C0528C2FCE95A3C2DBECF828CDFA4A8B4239A15B644A2 | |||
| 3976 | windows-activation.exe | C:\Users\admin\AppData\Local\Temp\i2ccy0s0.14t.psm1 | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:— | |||
| 2316 | cvtres.exe | C:\Users\admin\AppData\Local\Temp\RES44EA.tmp | binary | |
MD5:67DD354FB77B709772AF8E13FB359C57 | SHA256:8E9ADCF0950788AFEB9E1DFFADED80B272350246DFB247FE54C0047B69236640 | |||
| 1292 | csc.exe | C:\Users\admin\AppData\Local\Temp\CSC82B42FA7C574564966593C4E981DEC0.TMP | res | |
MD5:35B15135A80C2488F7046DCD0652F317 | SHA256:F3E8FD4D6CBEE15D700DF127789616BD2DF17A72F2F5B25321FABFFDE47916EB | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
6
DNS requests
2
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1060 | sipnotify.exe | HEAD | 200 | 23.197.138.118:80 | http://query.prod.cms.rt.microsoft.com/cms/api/am/binary/RE2JgkA?v=133604017657210000 | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 224.0.0.252:5355 | — | — | — | unknown |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1088 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
1060 | sipnotify.exe | 23.197.138.118:80 | query.prod.cms.rt.microsoft.com | Akamai International B.V. | US | unknown |
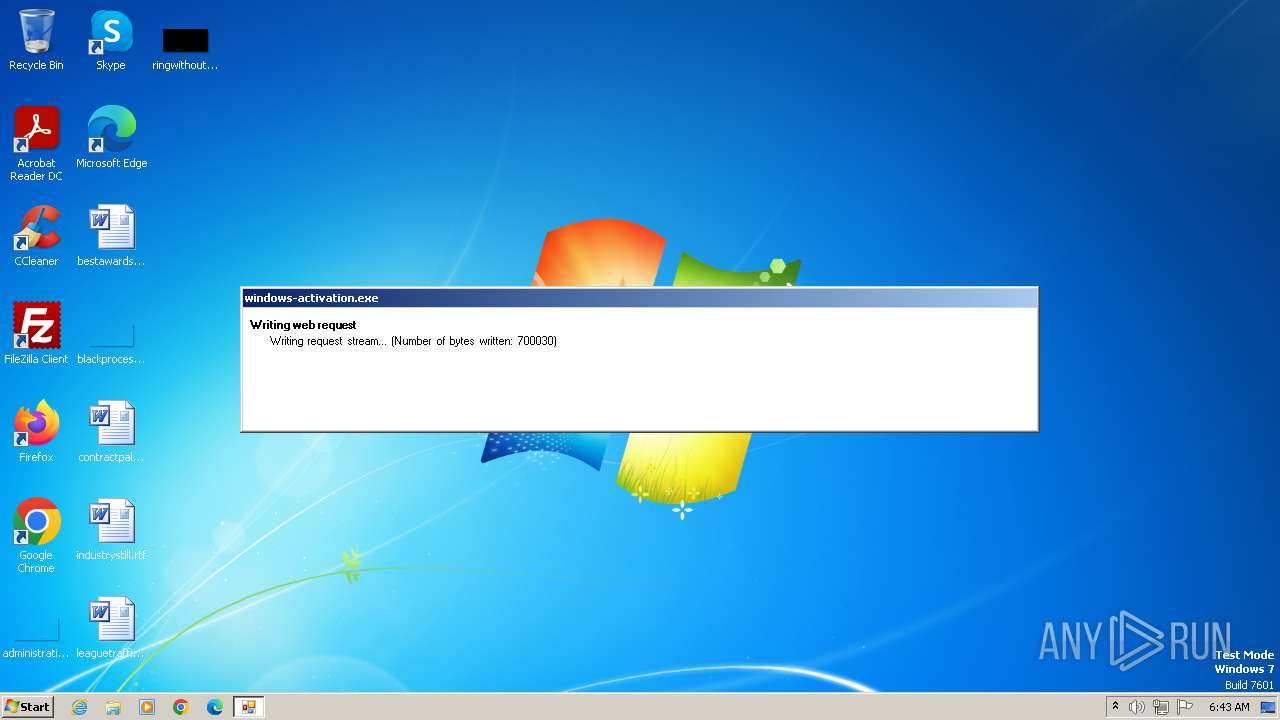
3976 | windows-activation.exe | 162.19.58.157:443 | i.ibb.co | OVH SAS | FR | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
query.prod.cms.rt.microsoft.com |
| whitelisted |
i.ibb.co |
| shared |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3976 | windows-activation.exe | Not Suspicious Traffic | INFO [ANY.RUN] Image hosting service ImgBB |