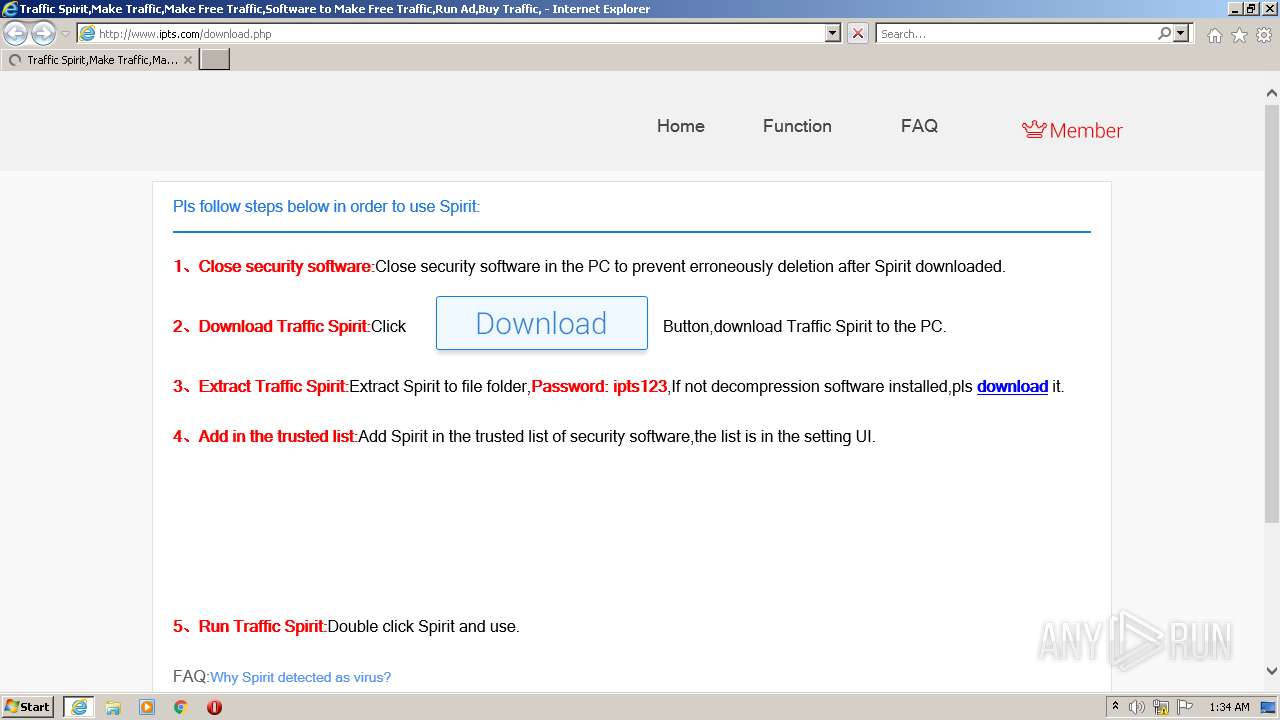
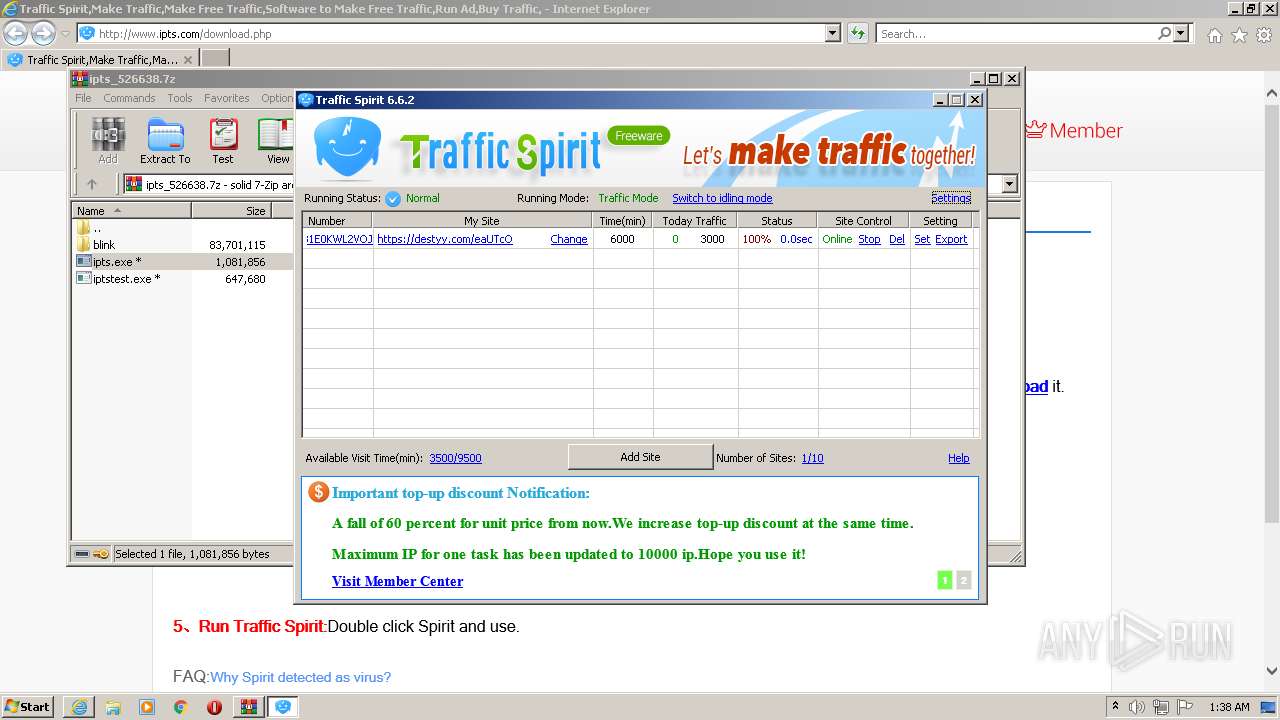
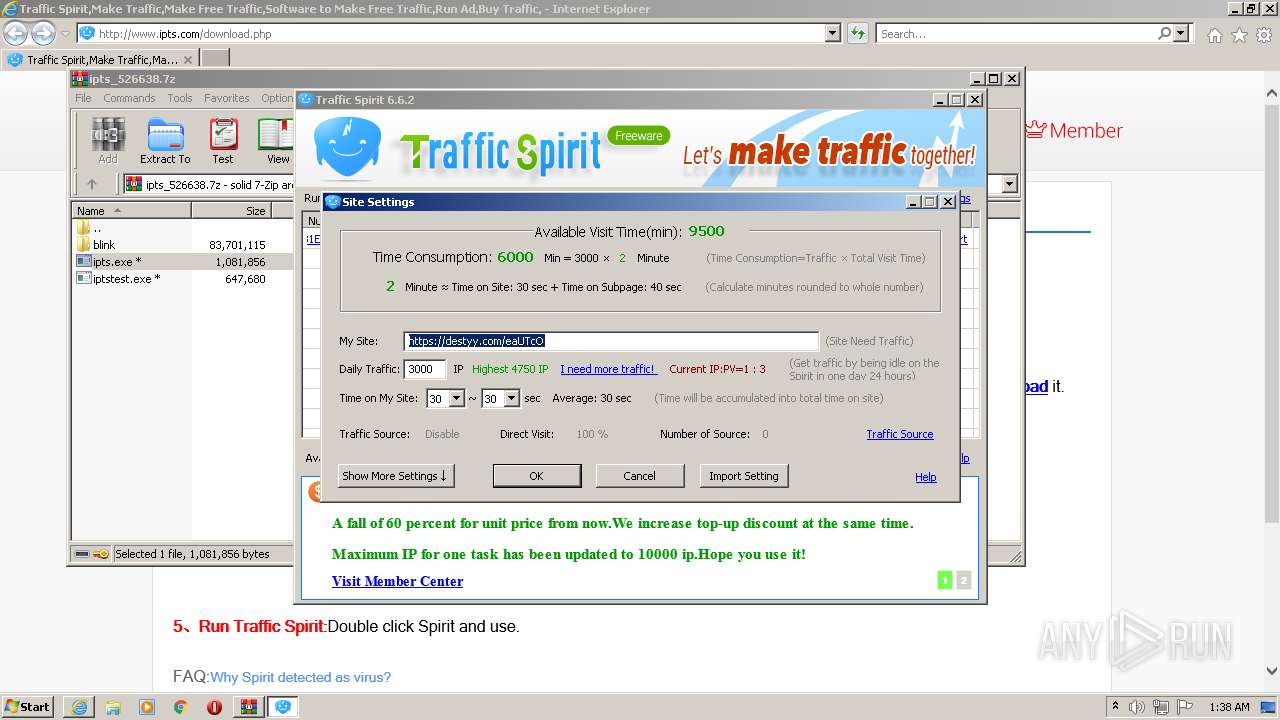
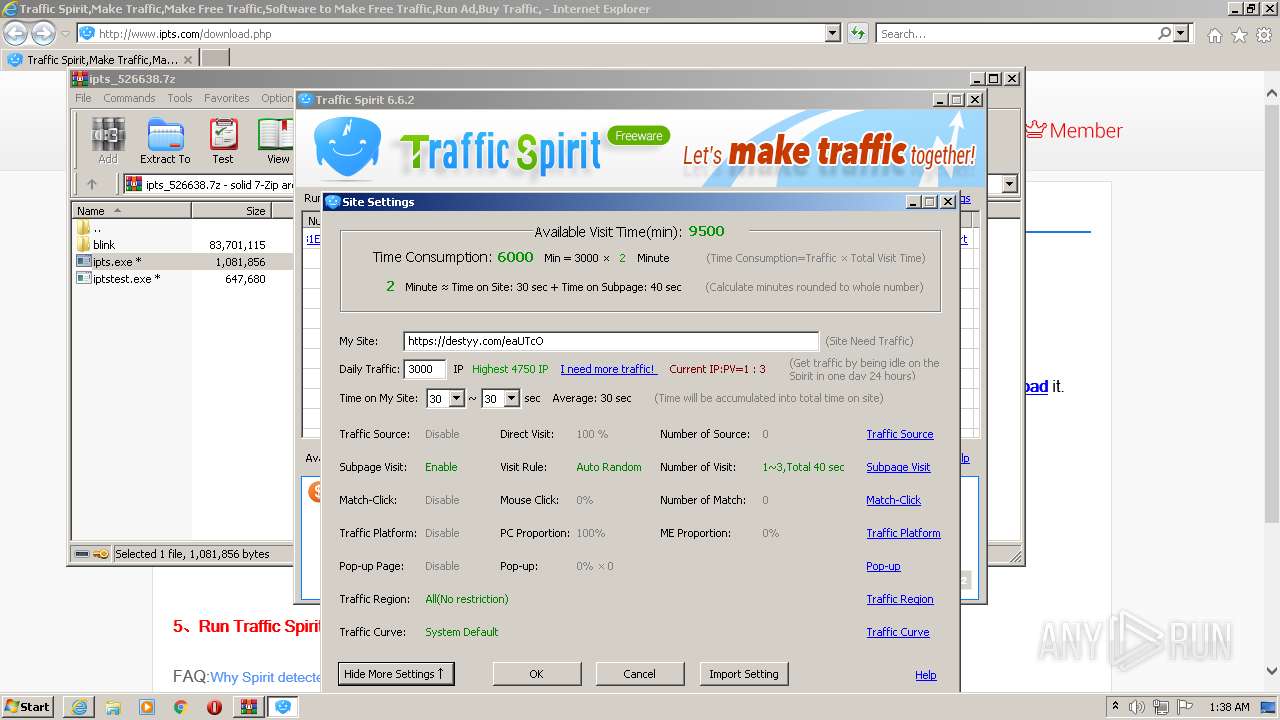
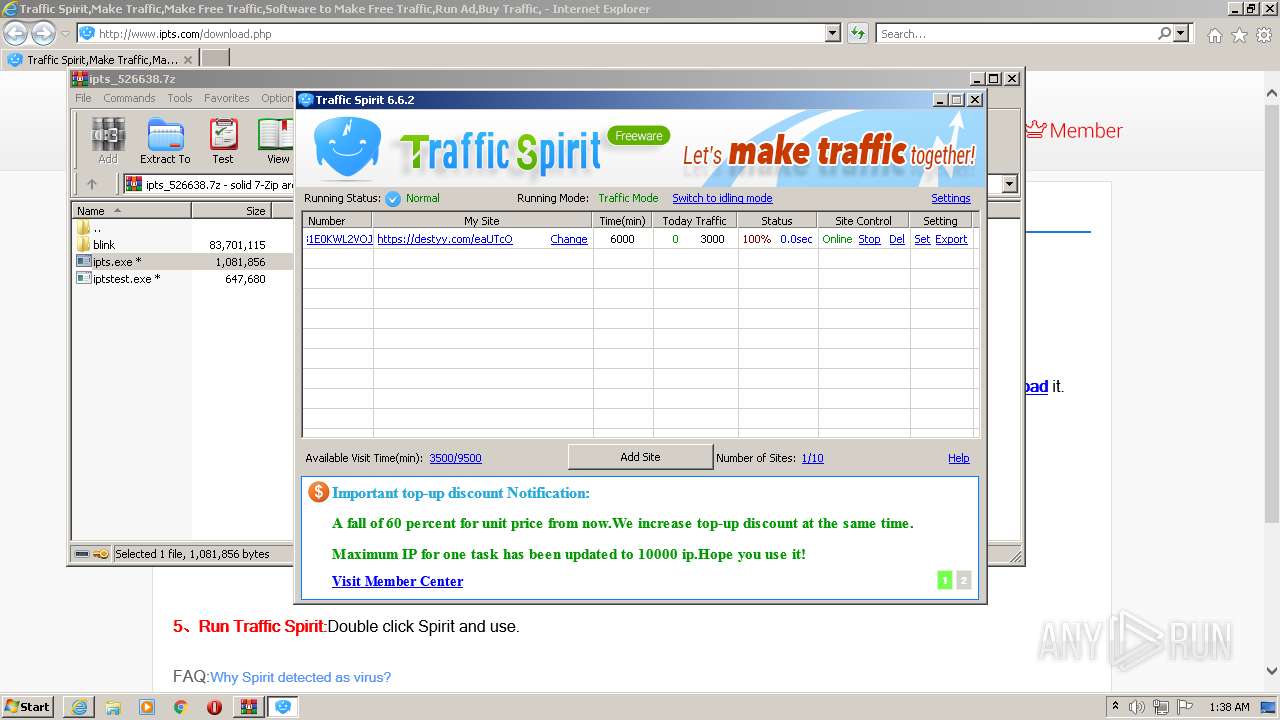
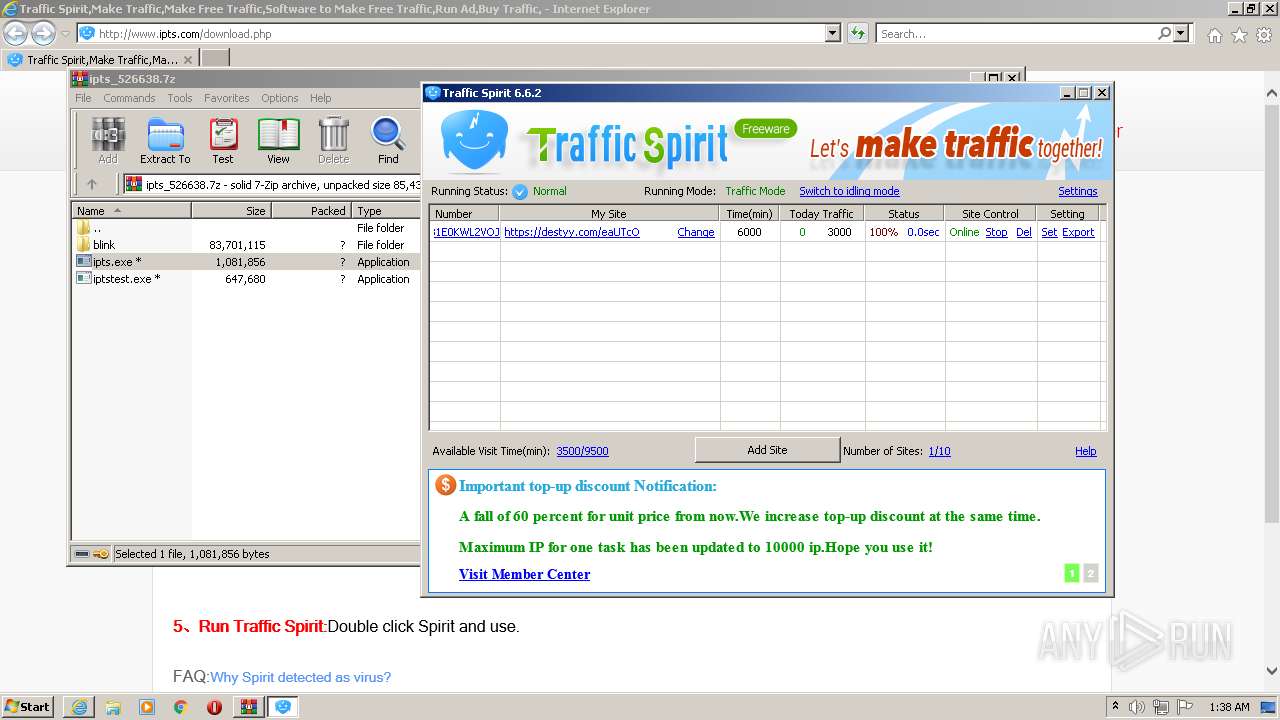
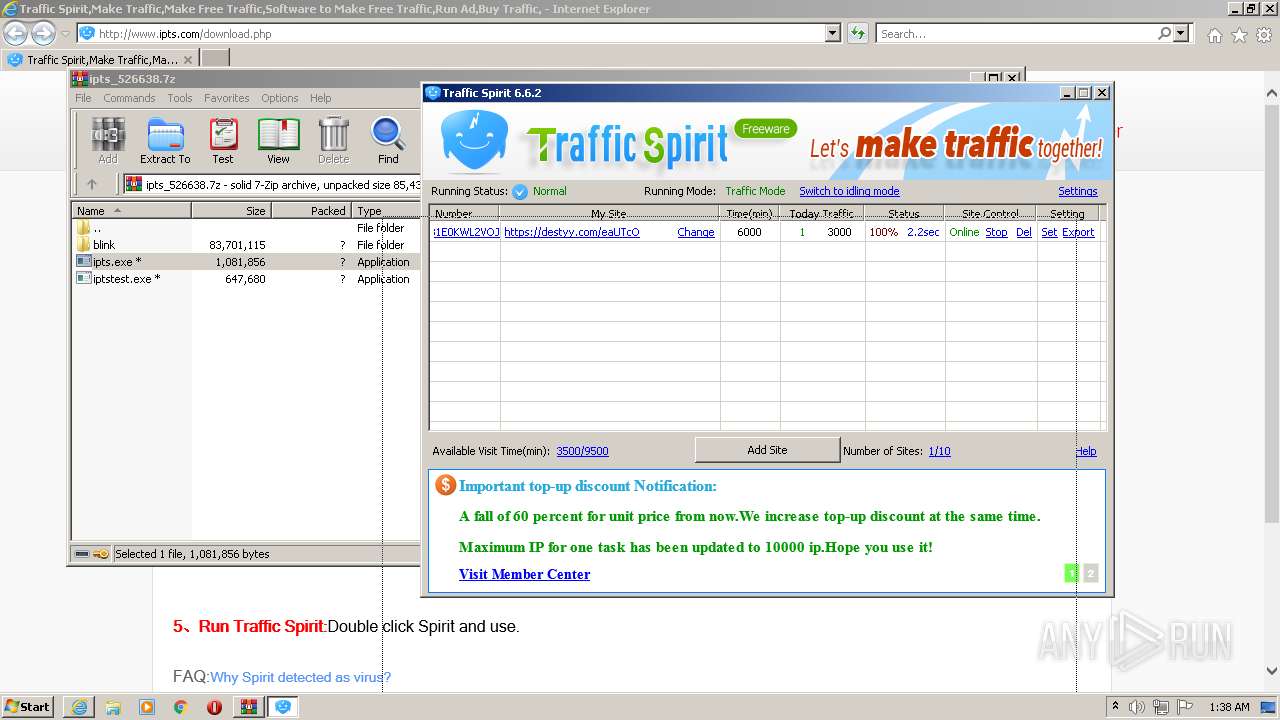
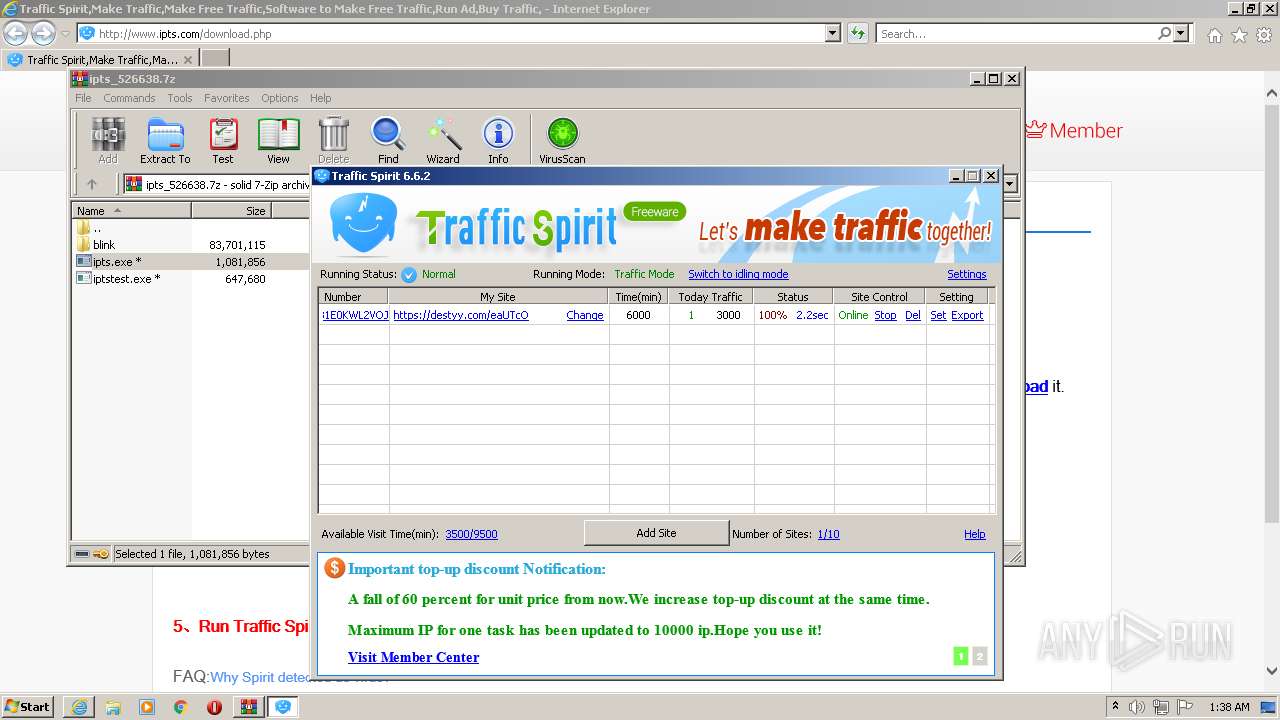
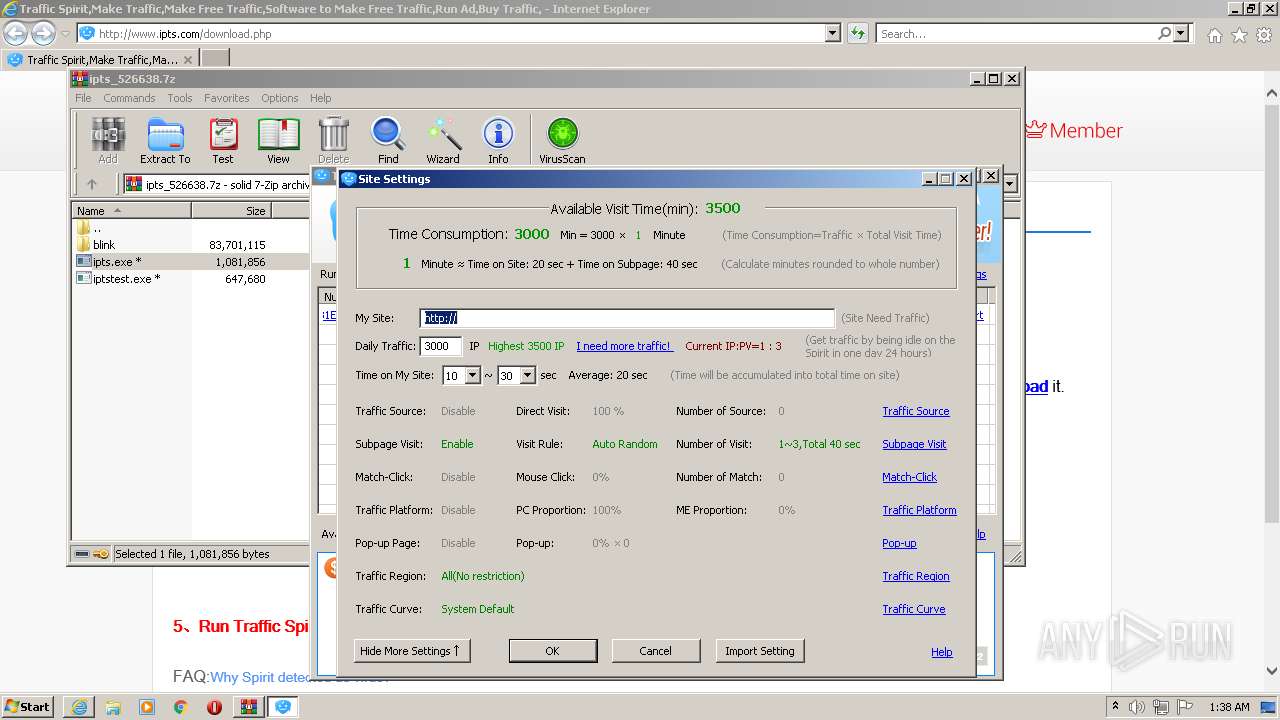
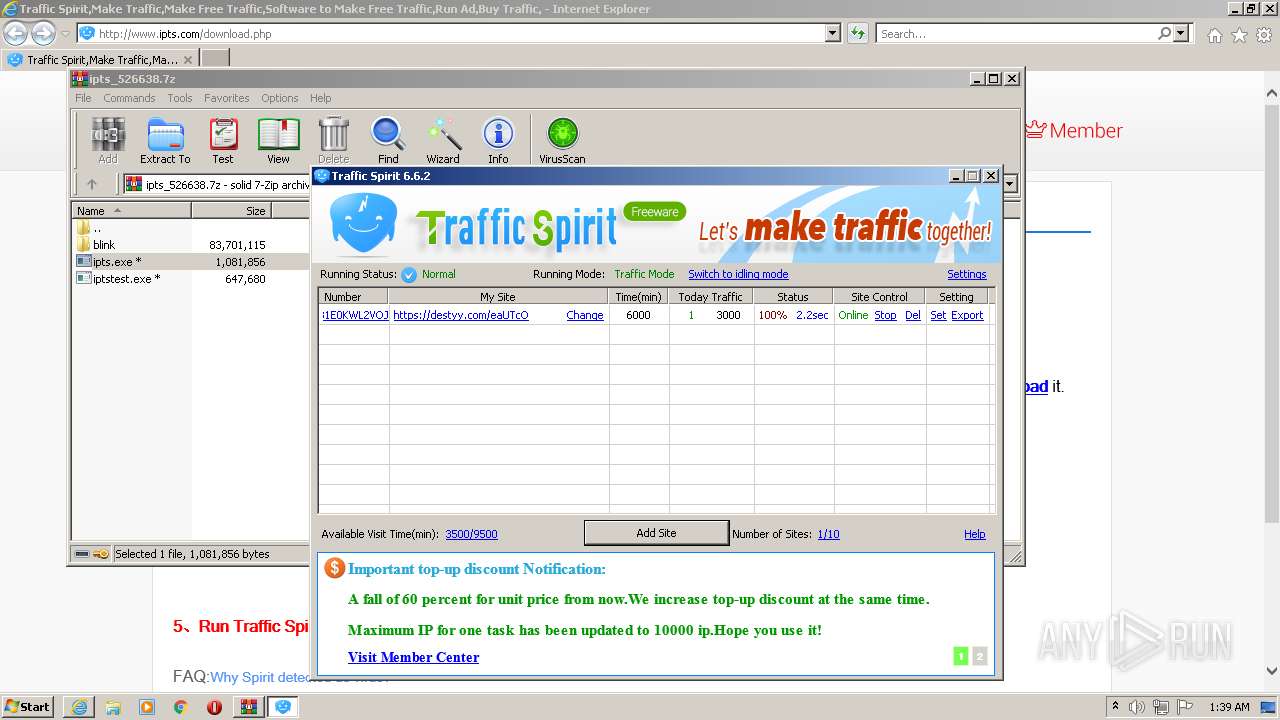
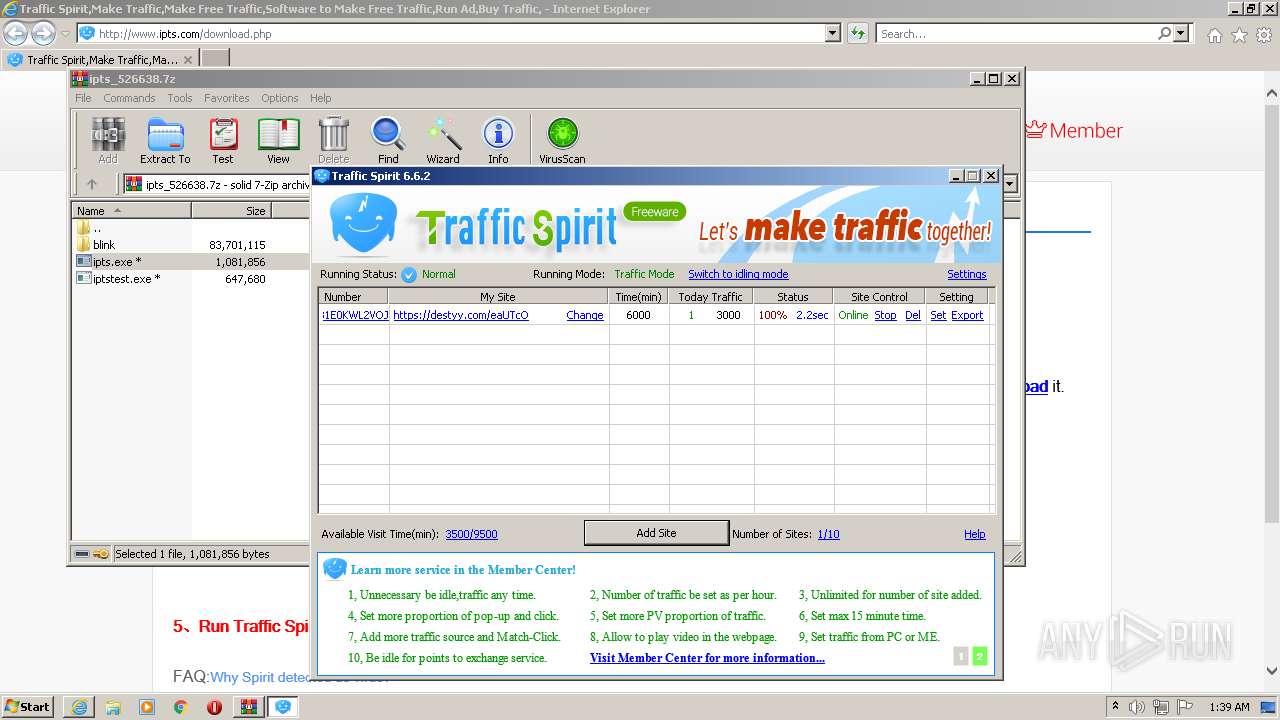
| URL: | http://www.ipts.com/download.php |
| Full analysis: | https://app.any.run/tasks/1e3ae52b-09e4-4249-93bc-d4308f6c2b78 |
| Verdict: | Malicious activity |
| Analysis date: | February 13, 2022, 01:34:47 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 0AC36F368FE6991E15DC2CCA640C56F7 |
| SHA1: | FE2B79CF6FA2DCF3FAECF288A398BB0725D4ED74 |
| SHA256: | 5CA83E8492D7E4C381A639D133544E658061501147C98F76B44D690AD713074C |
| SSDEEP: | 3:N1KJS4rLdIKBKKV:Cc4rLdMKV |
MALICIOUS
Application was dropped or rewritten from another process
- ipts.exe (PID: 3728)
- ipts.exe (PID: 2252)
- ipts.exe (PID: 2044)
- ipts.exe (PID: 2868)
- ipts.exe (PID: 3720)
- ipts.exe (PID: 2672)
- ipts.exe (PID: 1852)
- ipts.exe (PID: 3244)
- ipts.exe (PID: 1872)
- ipts.exe (PID: 2876)
- ipts.exe (PID: 3744)
- ipts.exe (PID: 3780)
Changes the autorun value in the registry
- ipts.exe (PID: 2252)
Loads dropped or rewritten executable
- ipts.exe (PID: 3728)
- ipts.exe (PID: 2044)
- ipts.exe (PID: 2868)
- ipts.exe (PID: 3720)
- ipts.exe (PID: 1852)
- ipts.exe (PID: 2672)
- ipts.exe (PID: 1872)
- ipts.exe (PID: 3244)
- ipts.exe (PID: 2876)
- ipts.exe (PID: 3780)
- ipts.exe (PID: 3744)
SUSPICIOUS
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 400)
- iexplore.exe (PID: 3584)
- ipts.exe (PID: 2252)
Reads the computer name
- WinRAR.exe (PID: 3040)
- ipts.exe (PID: 2252)
- ipts.exe (PID: 3728)
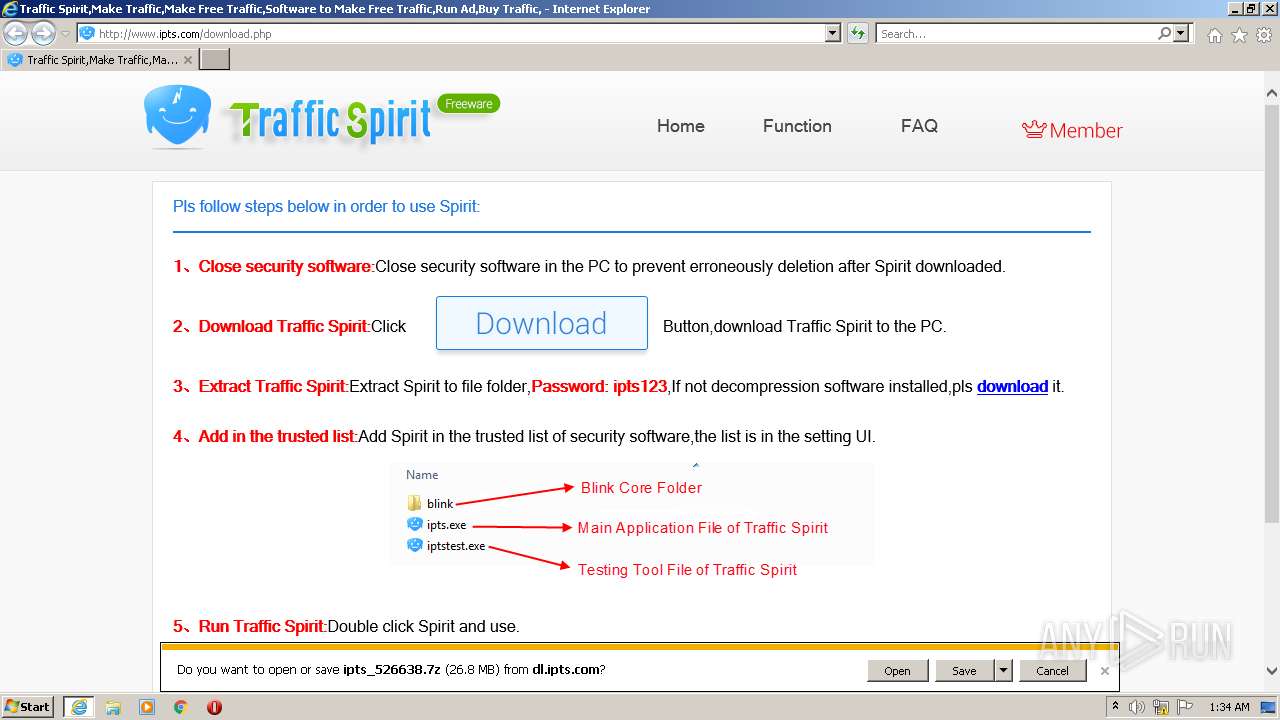
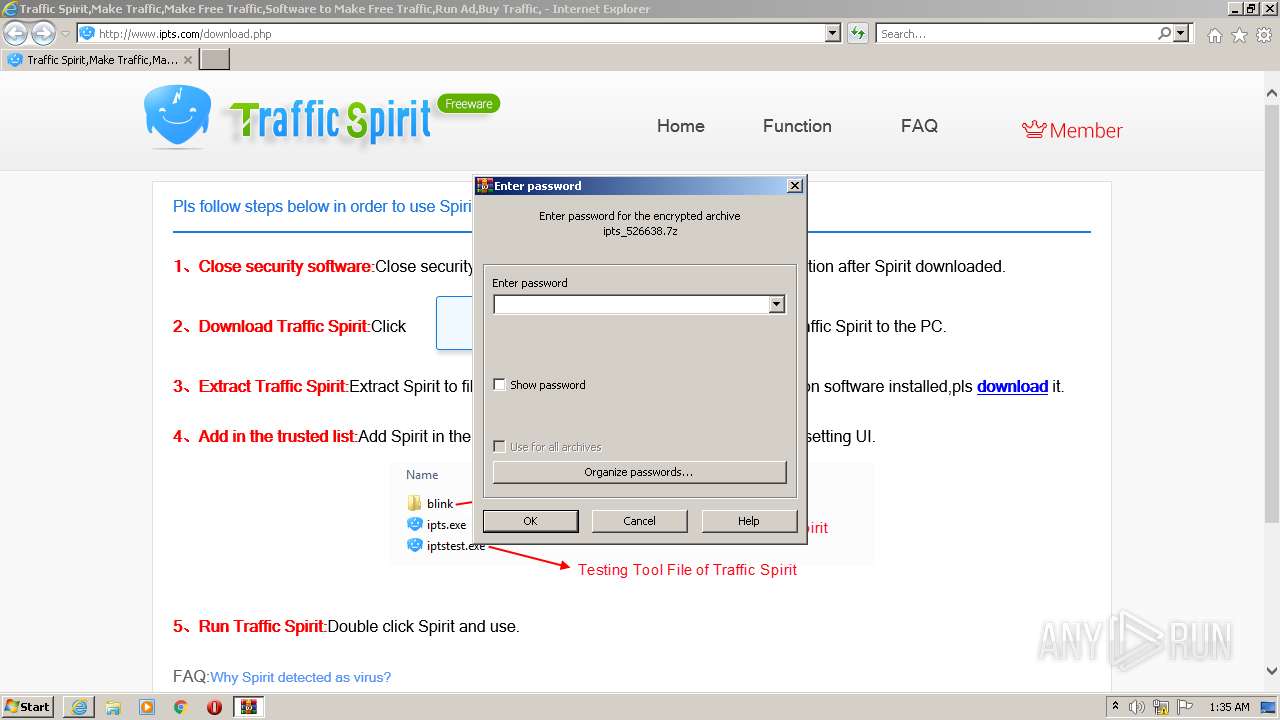
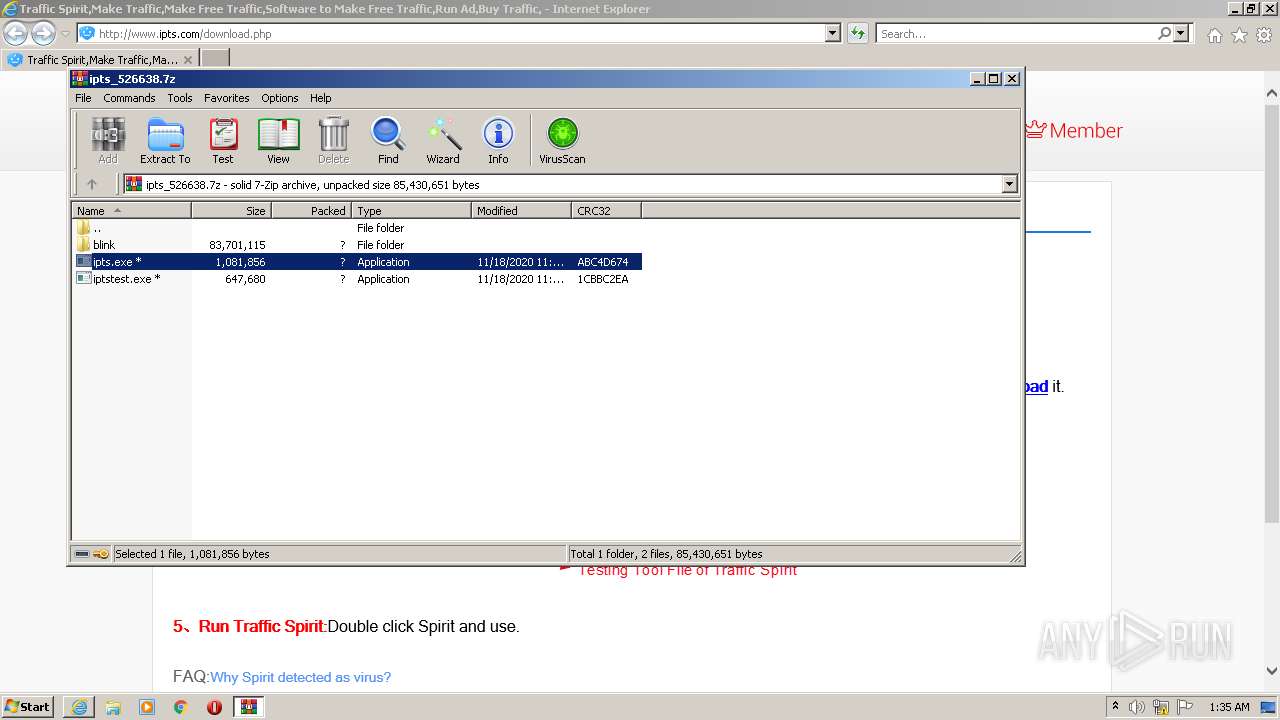
Executable content was dropped or overwritten
- WinRAR.exe (PID: 3040)
Checks supported languages
- WinRAR.exe (PID: 3040)
- ipts.exe (PID: 2252)
- ipts.exe (PID: 3728)
- ipts.exe (PID: 2044)
- ipts.exe (PID: 2868)
- ipts.exe (PID: 3720)
- ipts.exe (PID: 1852)
- ipts.exe (PID: 2672)
- ipts.exe (PID: 3244)
- ipts.exe (PID: 1872)
- ipts.exe (PID: 2876)
- ipts.exe (PID: 3744)
- ipts.exe (PID: 3780)
Reads internet explorer settings
- ipts.exe (PID: 2252)
Drops a file that was compiled in debug mode
- WinRAR.exe (PID: 3040)
Reads CPU info
- ipts.exe (PID: 2252)
Application launched itself
- ipts.exe (PID: 2252)
- ipts.exe (PID: 3728)
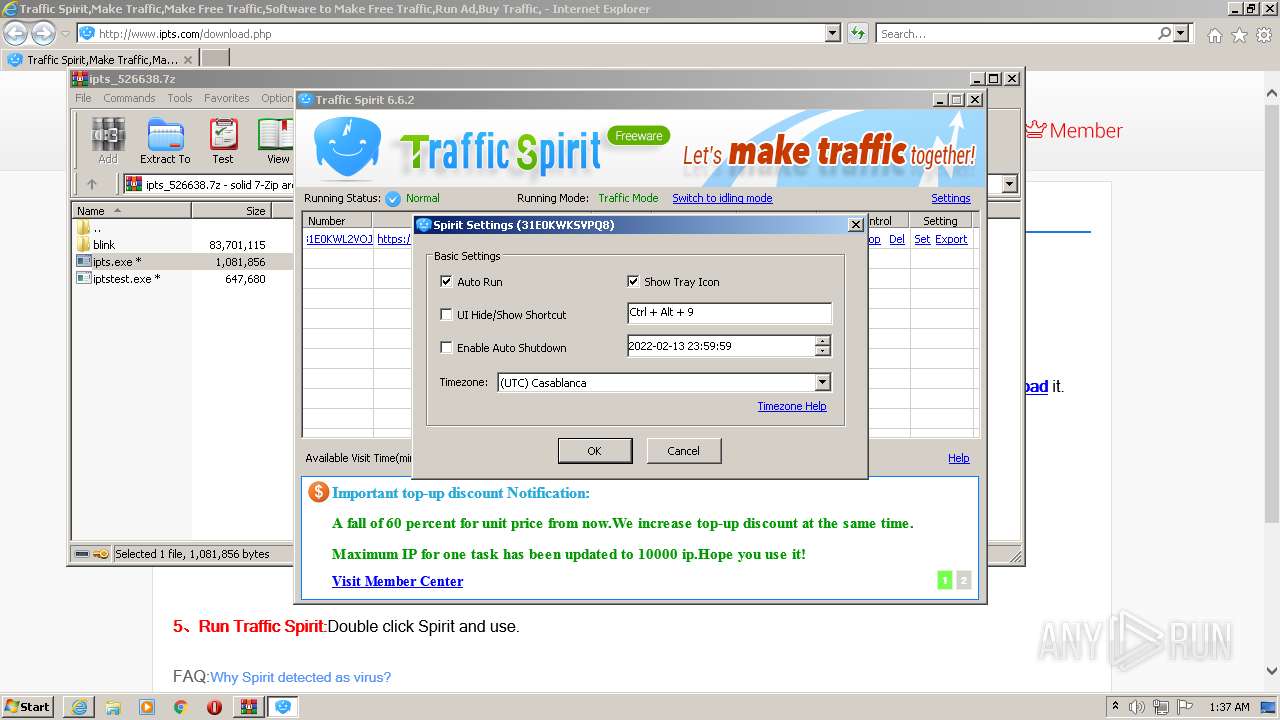
Reads the time zone
- ipts.exe (PID: 2044)
- ipts.exe (PID: 2868)
- ipts.exe (PID: 3720)
- ipts.exe (PID: 1852)
- ipts.exe (PID: 2672)
- ipts.exe (PID: 3244)
- ipts.exe (PID: 1872)
- ipts.exe (PID: 2876)
- ipts.exe (PID: 3744)
- ipts.exe (PID: 3780)
Creates files in the user directory
- ipts.exe (PID: 2252)
INFO
Application launched itself
- iexplore.exe (PID: 3584)
Changes internet zones settings
- iexplore.exe (PID: 3584)
Reads the computer name
- iexplore.exe (PID: 3584)
- iexplore.exe (PID: 400)
Creates files in the user directory
- iexplore.exe (PID: 400)
- iexplore.exe (PID: 3584)
Reads settings of System Certificates
- iexplore.exe (PID: 3584)
- ipts.exe (PID: 3728)
Checks supported languages
- iexplore.exe (PID: 3584)
- iexplore.exe (PID: 400)
Modifies the phishing filter of IE
- iexplore.exe (PID: 3584)
Dropped object may contain Bitcoin addresses
- WinRAR.exe (PID: 3040)
- ipts.exe (PID: 3728)
Reads internet explorer settings
- iexplore.exe (PID: 400)
Checks Windows Trust Settings
- iexplore.exe (PID: 3584)
Changes settings of System certificates
- iexplore.exe (PID: 3584)
Adds / modifies Windows certificates
- iexplore.exe (PID: 3584)
Reads the hosts file
- ipts.exe (PID: 3728)
Dropped object may contain TOR URL's
- ipts.exe (PID: 3728)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
51
Monitored processes
15
Malicious processes
13
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process |
|---|---|---|---|---|
| 400 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3584 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | |
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) | ||||
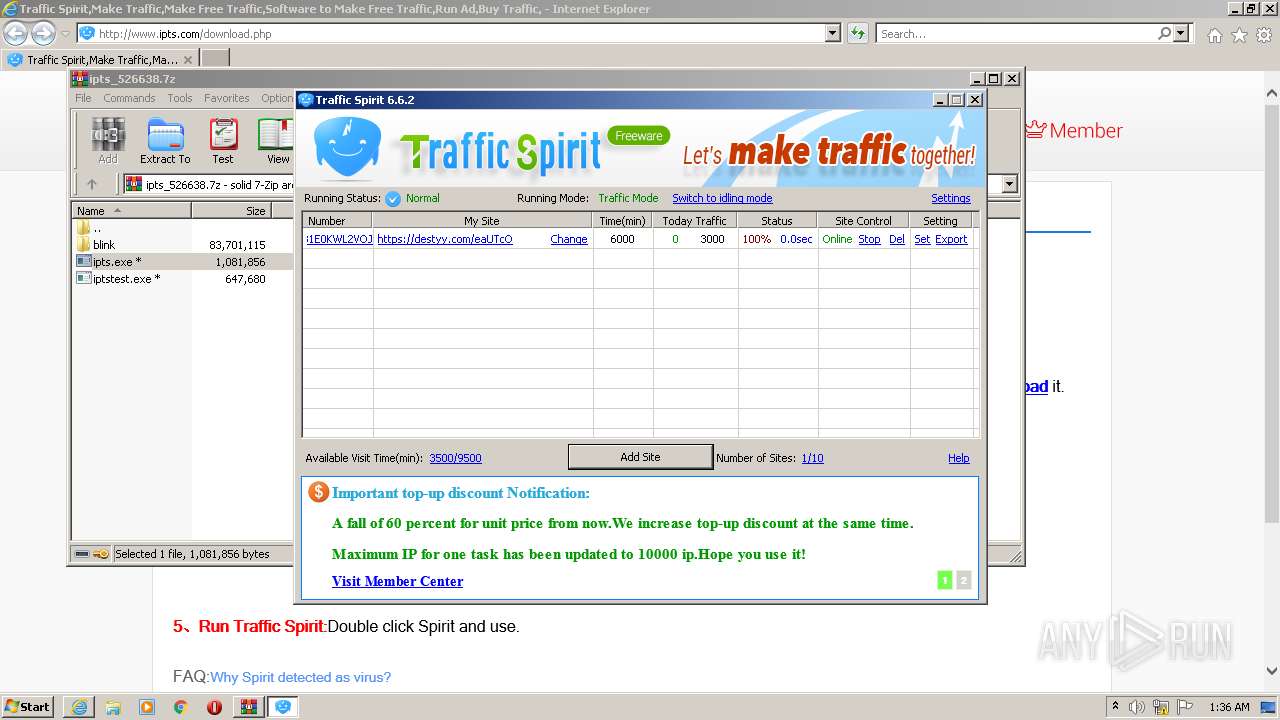
| 1852 | "C:\Users\admin\AppData\Local\Temp\Rar$EXb3040.31085\ipts.exe" --type=renderer --touch-events=enabled --lang=en-US --runtask --device-scale-factor=1 --num-raster-threads=2 --content-image-texture-target=3553,3553,3553,3553,3553,3553,3553,3553,3553,3553,3553,3553,3553,3553 --video-image-texture-target=3553 --disable-accelerated-video-decode --disable-webrtc-hw-encoding --disable-gpu-compositing --channel="3728.3.103994529\946345517" /prefetch:1 | C:\Users\admin\AppData\Local\Temp\Rar$EXb3040.31085\ipts.exe | — | ipts.exe |
User: admin Company: Spiritsoft Integrity Level: LOW Description: Traffic Spirit Exit code: 0 Version: 2020.11.19.37 | ||||
| 1872 | "C:\Users\admin\AppData\Local\Temp\Rar$EXb3040.31085\ipts.exe" --type=renderer --touch-events=enabled --lang=en-US --runtask --device-scale-factor=1 --num-raster-threads=2 --content-image-texture-target=3553,3553,3553,3553,3553,3553,3553,3553,3553,3553,3553,3553,3553,3553 --video-image-texture-target=3553 --disable-accelerated-video-decode --disable-webrtc-hw-encoding --disable-gpu-compositing --channel="3728.6.1727048394\291101808" /prefetch:1 | C:\Users\admin\AppData\Local\Temp\Rar$EXb3040.31085\ipts.exe | — | ipts.exe |
User: admin Company: Spiritsoft Integrity Level: LOW Description: Traffic Spirit Exit code: 0 Version: 2020.11.19.37 | ||||
| 2044 | "C:\Users\admin\AppData\Local\Temp\Rar$EXb3040.31085\ipts.exe" --type=renderer --touch-events=enabled --lang=en-US --runtask --device-scale-factor=1 --num-raster-threads=2 --content-image-texture-target=3553,3553,3553,3553,3553,3553,3553,3553,3553,3553,3553,3553,3553,3553 --video-image-texture-target=3553 --disable-accelerated-video-decode --disable-webrtc-hw-encoding --disable-gpu-compositing --channel="3728.0.1514406197\65167212" /prefetch:1 | C:\Users\admin\AppData\Local\Temp\Rar$EXb3040.31085\ipts.exe | — | ipts.exe |
User: admin Company: Spiritsoft Integrity Level: LOW Description: Traffic Spirit Exit code: 0 Version: 2020.11.19.37 | ||||
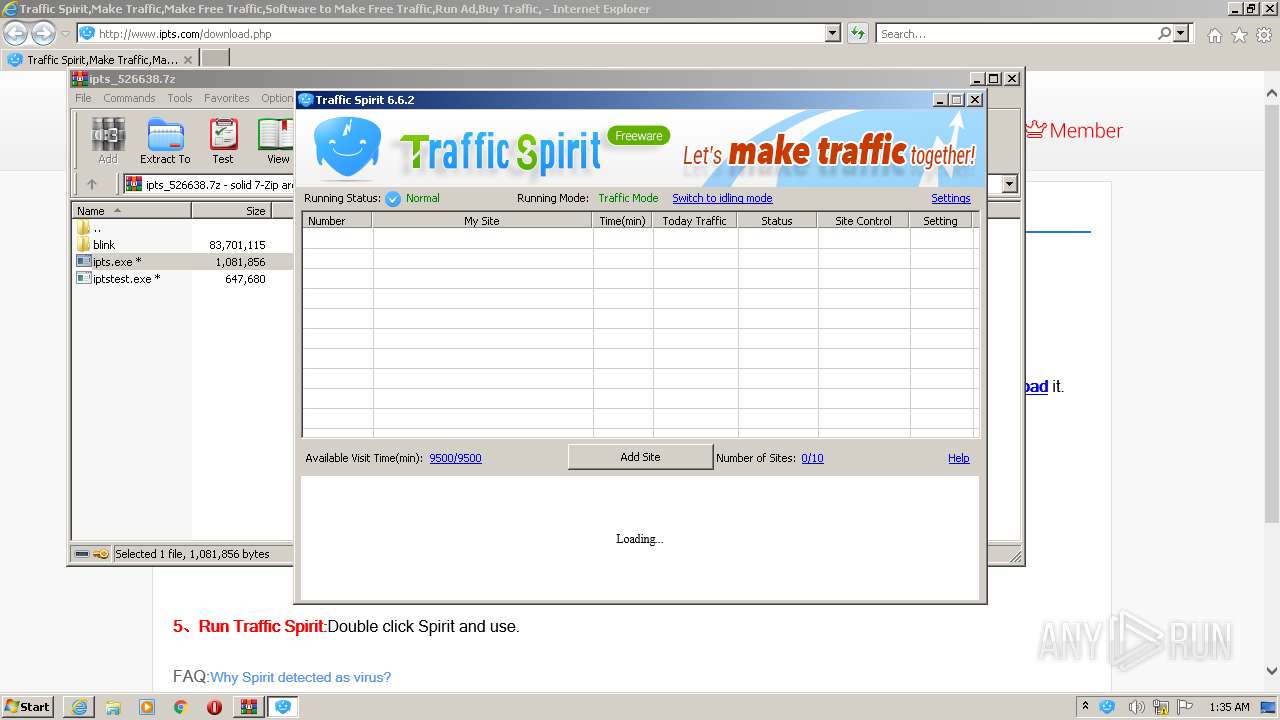
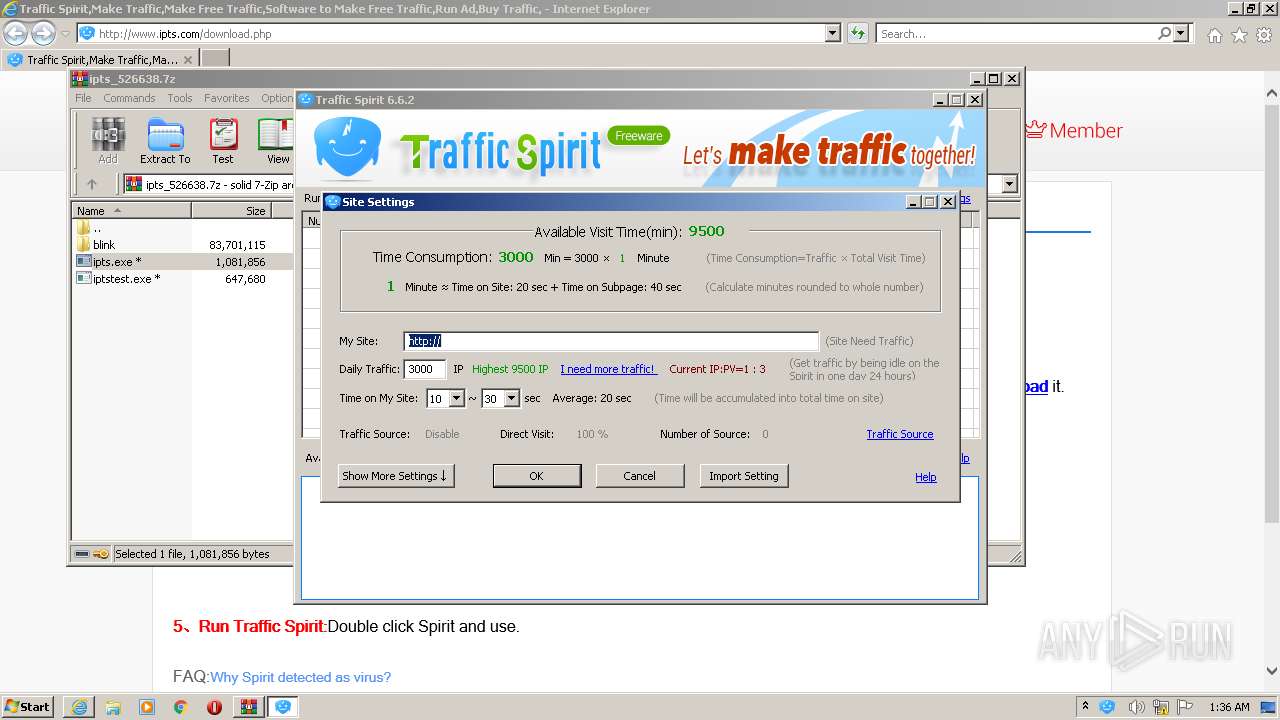
| 2252 | "C:\Users\admin\AppData\Local\Temp\Rar$EXb3040.31085\ipts.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXb3040.31085\ipts.exe | WinRAR.exe | |
User: admin Company: Spiritsoft Integrity Level: MEDIUM Description: Traffic Spirit Exit code: 0 Version: 2020.11.19.37 | ||||
| 2672 | "C:\Users\admin\AppData\Local\Temp\Rar$EXb3040.31085\ipts.exe" --type=renderer --touch-events=enabled --lang=en-US --runtask --device-scale-factor=1 --num-raster-threads=2 --content-image-texture-target=3553,3553,3553,3553,3553,3553,3553,3553,3553,3553,3553,3553,3553,3553 --video-image-texture-target=3553 --disable-accelerated-video-decode --disable-webrtc-hw-encoding --disable-gpu-compositing --channel="3728.4.698460545\1668329351" /prefetch:1 | C:\Users\admin\AppData\Local\Temp\Rar$EXb3040.31085\ipts.exe | — | ipts.exe |
User: admin Company: Spiritsoft Integrity Level: LOW Description: Traffic Spirit Exit code: 0 Version: 2020.11.19.37 | ||||
| 2868 | "C:\Users\admin\AppData\Local\Temp\Rar$EXb3040.31085\ipts.exe" --type=renderer --touch-events=enabled --lang=en-US --runtask --device-scale-factor=1 --num-raster-threads=2 --content-image-texture-target=3553,3553,3553,3553,3553,3553,3553,3553,3553,3553,3553,3553,3553,3553 --video-image-texture-target=3553 --disable-accelerated-video-decode --disable-webrtc-hw-encoding --disable-gpu-compositing --channel="3728.1.1634625990\1328211383" /prefetch:1 | C:\Users\admin\AppData\Local\Temp\Rar$EXb3040.31085\ipts.exe | — | ipts.exe |
User: admin Company: Spiritsoft Integrity Level: LOW Description: Traffic Spirit Exit code: 0 Version: 2020.11.19.37 | ||||
| 2876 | "C:\Users\admin\AppData\Local\Temp\Rar$EXb3040.31085\ipts.exe" --type=renderer --touch-events=enabled --lang=en-US --runtask --device-scale-factor=1 --num-raster-threads=2 --content-image-texture-target=3553,3553,3553,3553,3553,3553,3553,3553,3553,3553,3553,3553,3553,3553 --video-image-texture-target=3553 --disable-accelerated-video-decode --disable-webrtc-hw-encoding --disable-gpu-compositing --channel="3728.7.417592850\2147205685" /prefetch:1 | C:\Users\admin\AppData\Local\Temp\Rar$EXb3040.31085\ipts.exe | — | ipts.exe |
User: admin Company: Spiritsoft Integrity Level: LOW Description: Traffic Spirit Exit code: 0 Version: 2020.11.19.37 | ||||
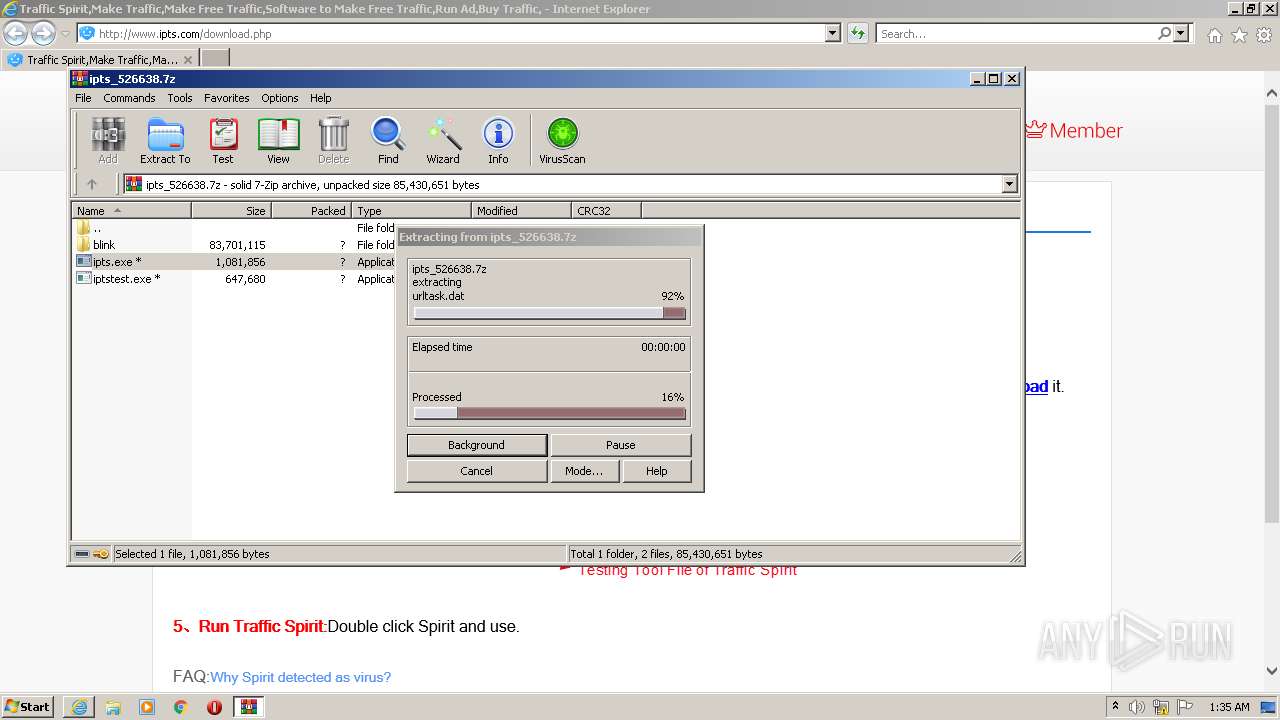
| 3040 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\6Z2BCOUL\ipts_526638.7z" | C:\Program Files\WinRAR\WinRAR.exe | iexplore.exe | |
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 | ||||
| 3244 | "C:\Users\admin\AppData\Local\Temp\Rar$EXb3040.31085\ipts.exe" --type=renderer --touch-events=enabled --lang=en-US --runtask --device-scale-factor=1 --num-raster-threads=2 --content-image-texture-target=3553,3553,3553,3553,3553,3553,3553,3553,3553,3553,3553,3553,3553,3553 --video-image-texture-target=3553 --disable-accelerated-video-decode --disable-webrtc-hw-encoding --disable-gpu-compositing --channel="3728.5.1868800075\2020489646" /prefetch:1 | C:\Users\admin\AppData\Local\Temp\Rar$EXb3040.31085\ipts.exe | — | ipts.exe |
User: admin Company: Spiritsoft Integrity Level: LOW Description: Traffic Spirit Exit code: 0 Version: 2020.11.19.37 | ||||
Total events
0
Read events
0
Write events
0
Delete events
0
Modification events
Executable files
7
Suspicious files
426
Text files
438
Unknown types
50
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 400 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\download[1].htm | html | |
MD5:— | SHA256:— | |||
| 400 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\EQ0CRMC4.txt | text | |
MD5:— | SHA256:— | |||
| 400 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\5IWPIAR9\z_stat[1].js | text | |
MD5:— | SHA256:— | |||
| 400 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\K3T2O9N1.txt | text | |
MD5:— | SHA256:— | |||
| 400 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\core[1].js | html | |
MD5:— | SHA256:— | |||
| 400 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\2BIJHGFC.txt | text | |
MD5:— | SHA256:— | |||
| 3584 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\imagestore\f7ruq93\imagestore.dat | binary | |
MD5:— | SHA256:— | |||
| 400 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\file[1].png | image | |
MD5:— | SHA256:— | |||
| 400 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\S6N2RMUG.txt | text | |
MD5:— | SHA256:— | |||
| 3584 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
868
TCP/UDP connections
1 576
DNS requests
432
Threats
467
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
400 | iexplore.exe | GET | — | 47.88.10.215:80 | http://www.ipts.com/images/xz_hover.png | JP | — | — | malicious |
400 | iexplore.exe | GET | — | 47.88.10.215:80 | http://www.ipts.com/images/xz_down.png | JP | — | — | malicious |
400 | iexplore.exe | GET | 200 | 47.88.10.215:80 | http://www.ipts.com/images/file.png | JP | image | 9.87 Kb | malicious |
400 | iexplore.exe | GET | 200 | 58.215.157.250:80 | http://s4.cnzz.com/z_stat.php?id=1255129158 | CN | text | 3.95 Kb | whitelisted |
400 | iexplore.exe | GET | 200 | 47.88.10.215:80 | http://www.ipts.com/download.php | JP | html | 2.63 Kb | malicious |
3584 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8Ull8gIGmZT9XHrHiJQeI%3D | US | der | 1.47 Kb | whitelisted |
400 | iexplore.exe | GET | 200 | 154.94.7.127:80 | http://dl.ipts.com/v5/ipts_526638.7z | US | compressed | 26.8 Mb | unknown |
400 | iexplore.exe | GET | 200 | 47.88.10.215:80 | http://www.ipts.com/style/style.css | JP | text | 521 b | malicious |
400 | iexplore.exe | GET | 200 | 47.88.10.215:80 | http://www.ipts.com/images/top_bg.png | JP | image | 166 b | malicious |
400 | iexplore.exe | GET | 200 | 47.88.10.215:80 | http://www.ipts.com/images/vipuser.png | JP | image | 2.29 Kb | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
400 | iexplore.exe | 58.215.157.250:80 | s4.cnzz.com | AS Number for CHINANET jiangsu province backbone | CN | unknown |
400 | iexplore.exe | 203.119.146.29:80 | z11.cnzz.com | — | CN | unknown |
400 | iexplore.exe | 47.246.136.160:80 | cnzz.mmstat.com | — | US | unknown |
3584 | iexplore.exe | 47.88.10.215:80 | www.ipts.com | Alibaba (China) Technology Co., Ltd. | JP | suspicious |
400 | iexplore.exe | 59.82.14.134:80 | pcookie.cnzz.com | — | CN | unknown |
3584 | iexplore.exe | 204.79.197.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
3584 | iexplore.exe | 23.32.238.178:80 | ctldl.windowsupdate.com | XO Communications | US | suspicious |
3584 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3584 | iexplore.exe | 152.199.19.161:443 | iecvlist.microsoft.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
400 | iexplore.exe | 154.94.7.127:80 | dl.ipts.com | MULTACOM CORPORATION | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.ipts.com |
| malicious |
s4.cnzz.com |
| whitelisted |
z11.cnzz.com |
| whitelisted |
c.cnzz.com |
| whitelisted |
cnzz.mmstat.com |
| whitelisted |
pcookie.cnzz.com |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3728 | ipts.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |
3728 | ipts.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |
3728 | ipts.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |
3728 | ipts.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |
3728 | ipts.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |
3728 | ipts.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |
3728 | ipts.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |
3728 | ipts.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |
3728 | ipts.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |
3728 | ipts.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |