| File name: | SecuriteInfo.com.Win32.Malware-gen.24050.20684.msi |
| Full analysis: | https://app.any.run/tasks/eff35045-9fdf-462d-b032-5afbf006d03d |
| Verdict: | Malicious activity |
| Analysis date: | May 16, 2025, 15:32:12 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Indicators: | |
| MD5: | E84DB67F8F30CD4BA03A0C9E6952628B |
| SHA1: | C24C01CC464DB661EC5F5910411B7049793FC1E6 |
| SHA256: | 5CA4552216DDC3B276E3CF2684CC5041B31931181A54D5CB62113BF6AABA1575 |
| SSDEEP: | 98304:t7KltuUF/1KdhUj+Rt2URMTUOyV59Avpj31mvrBvSSRkYhYYzjOMrdBg5HJKxqi3:tu3aAt6twV7WIps |
MALICIOUS
Executing a file with an untrusted certificate
- SF32.exe (PID: 5552)
- SF32.exe (PID: 1040)
- SF32.exe (PID: 6540)
Known privilege escalation attack
- dllhost.exe (PID: 896)
SUSPICIOUS
Executes as Windows Service
- VSSVC.exe (PID: 1132)
Executable content was dropped or overwritten
- SF32.exe (PID: 5552)
- SF32.exe (PID: 6540)
Starts itself from another location
- SF32.exe (PID: 5552)
Starts CMD.EXE for commands execution
- SF32.exe (PID: 1040)
- SF32.exe (PID: 6540)
Connects to unusual port
- svchost.exe (PID: 1244)
INFO
Reads the computer name
- msiexec.exe (PID: 5608)
Executable content was dropped or overwritten
- msiexec.exe (PID: 5608)
Manages system restore points
- SrTasks.exe (PID: 736)
The sample compiled with english language support
- msiexec.exe (PID: 5608)
- SF32.exe (PID: 5552)
- SF32.exe (PID: 6540)
Checks supported languages
- msiexec.exe (PID: 5608)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
148
Monitored processes
16
Malicious processes
3
Suspicious processes
2
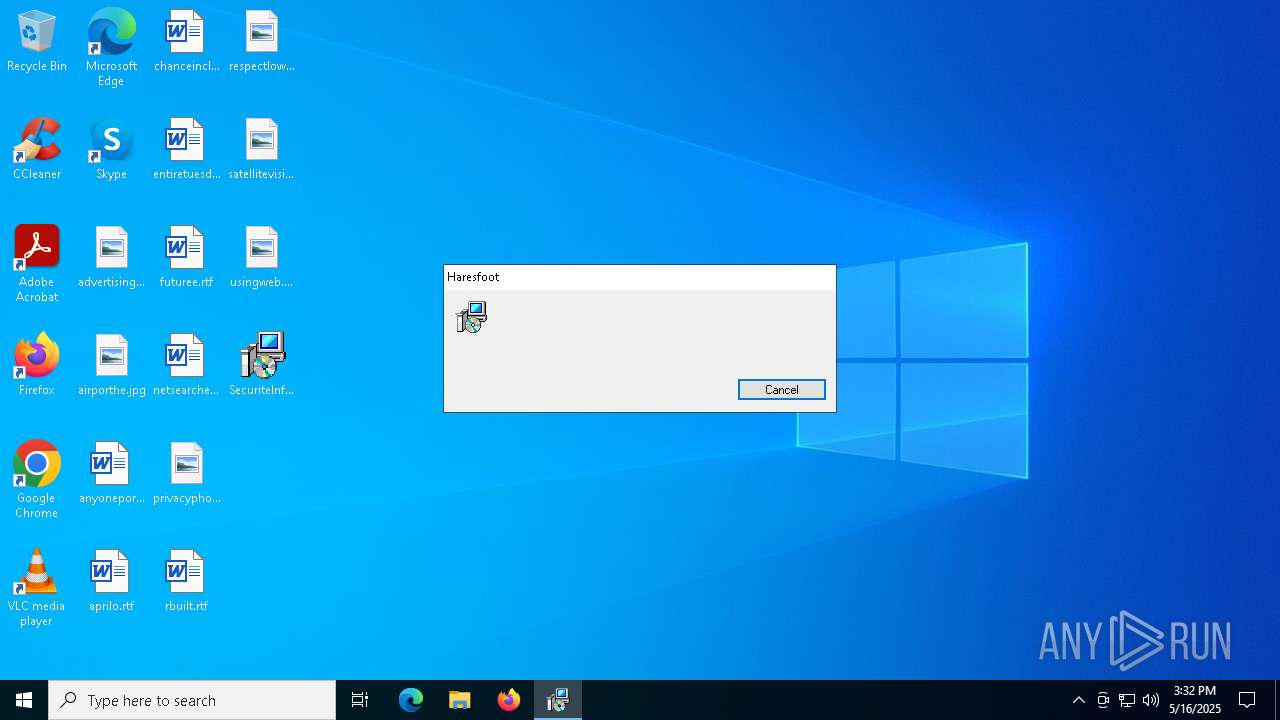
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 208 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | SrTasks.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 736 | C:\WINDOWS\system32\srtasks.exe ExecuteScopeRestorePoint /WaitForRestorePoint:11 | C:\Windows\System32\SrTasks.exe | — | msiexec.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Windows System Protection background tasks. Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 896 | C:\WINDOWS\SysWOW64\DllHost.exe /Processid:{3E5FC7F9-9A51-4367-9063-A120244FBEC7} | C:\Windows\SysWOW64\dllhost.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: COM Surrogate Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1040 | C:\ProgramData\psh_ultra\SF32.exe | C:\ProgramData\psh_ultra\SF32.exe | — | SF32.exe | |||||||||||
User: admin Company: wisecleaner.com Integrity Level: MEDIUM Description: WiseTurbo Exit code: 0 Version: 4.2.1.50 Modules
| |||||||||||||||
| 1132 | C:\WINDOWS\system32\vssvc.exe | C:\Windows\System32\VSSVC.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Volume Shadow Copy Service Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1244 | "C:\Windows\System32\svchost.exe" | C:\Windows\SysWOW64\svchost.exe | dllhost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Host Process for Windows Services Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1300 | C:\WINDOWS\SysWOW64\cmd.exe | C:\Windows\SysWOW64\cmd.exe | — | SF32.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2084 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5212 | C:\ProgramData\AdaptiveDisp.exe | C:\ProgramData\AdaptiveDisp.exe | — | SF32.exe | |||||||||||
User: admin Company: Tonec Inc. Integrity Level: HIGH Description: Internet Download Manager module Exit code: 0 Version: 6, 35, 9, 1 Modules
| |||||||||||||||
| 5552 | "C:\Users\admin\AppData\Local\Diphtheria\SF32.exe" | C:\Users\admin\AppData\Local\Diphtheria\SF32.exe | msiexec.exe | ||||||||||||
User: admin Company: wisecleaner.com Integrity Level: MEDIUM Description: WiseTurbo Exit code: 0 Version: 4.2.1.50 Modules
| |||||||||||||||
Total events
7 092
Read events
6 828
Write events
246
Delete events
18
Modification events
| (PID) Process: | (5608) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SystemRestore |
| Operation: | write | Name: | SrCreateRp (Enter) |
Value: 4800000000000000DB8652B977C6DB01E8150000380A0000D50700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (5608) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGetSnapshots (Enter) |
Value: 48000000000000005FD754B977C6DB01E8150000380A0000D20700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (5608) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGetSnapshots (Leave) |
Value: 4800000000000000C31BCCB977C6DB01E8150000380A0000D20700000100000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (5608) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppEnumGroups (Enter) |
Value: 4800000000000000C31BCCB977C6DB01E8150000380A0000D10700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (5608) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppEnumGroups (Leave) |
Value: 480000000000000001D4D0B977C6DB01E8150000380A0000D10700000100000000000000010000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (5608) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppCreate (Enter) |
Value: 4800000000000000F39BD5B977C6DB01E8150000380A0000D00700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (5608) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\SPP |
| Operation: | write | Name: | LastIndex |
Value: 11 | |||
| (PID) Process: | (5608) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGatherWriterMetadata (Enter) |
Value: 4800000000000000241A5BBA77C6DB01E8150000380A0000D30700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (5608) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\VssapiPublisher |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4800000000000000D1E25FBA77C6DB01E815000060160000E803000001000000000000000000000005E509A4EE26ED408758E8B64921891400000000000000000000000000000000 | |||
| (PID) Process: | (1132) VSSVC.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\ASR Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 480000000000000066DB6BBA77C6DB016C04000064180000E80300000100000001000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
Executable files
5
Suspicious files
25
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5608 | msiexec.exe | C:\System Volume Information\SPP\metadata-2 | — | |
MD5:— | SHA256:— | |||
| 5608 | msiexec.exe | C:\Windows\Installer\112855.msi | — | |
MD5:— | SHA256:— | |||
| 5608 | msiexec.exe | C:\Windows\Installer\112857.msi | — | |
MD5:— | SHA256:— | |||
| 5608 | msiexec.exe | C:\System Volume Information\SPP\OnlineMetadataCache\{a409e505-26ee-40ed-8758-e8b649218914}_OnDiskSnapshotProp | binary | |
MD5:0201BBBE6E5DF0B7A65698FB6F124586 | SHA256:8DD2F871A5927E97EE6102AB101F605186C5E6AD7069C9A66C1EB309F2B1BF79 | |||
| 5608 | msiexec.exe | C:\Windows\Temp\~DF50A5253ADA6A64FF.TMP | binary | |
MD5:C11EE0D15FB68CB9C5EE7965BDE66339 | SHA256:581E8DE46662920B337565C8ABE414A4F189802A25C0E6B068BFDCBC7C550D57 | |||
| 5608 | msiexec.exe | C:\Users\admin\AppData\Local\Diphtheria\SF32.exe | executable | |
MD5:1F166F5C76EB155D44DD1BF160F37A6A | SHA256:2D13424B09BA004135A26CCD60B64CDD6917D80CE43070CBC114569EAE608588 | |||
| 5608 | msiexec.exe | C:\Windows\Installer\MSI2B14.tmp | binary | |
MD5:16209E4292BC9BDF4C43CF7A4B4F58AE | SHA256:4900606951152F919325146087B751C7A574A95AE7A43AB42FD2249E7CD92D92 | |||
| 5608 | msiexec.exe | C:\Users\admin\AppData\Local\Diphtheria\alcove.flac | binary | |
MD5:09AF3A8CC16E697FF2271838BC47991D | SHA256:C90717F7CBFAE38F23AA8D366676AB95AF23771815789D24DB03A0F0D7271788 | |||
| 5608 | msiexec.exe | C:\Windows\Installer\inprogressinstallinfo.ipi | binary | |
MD5:C11EE0D15FB68CB9C5EE7965BDE66339 | SHA256:581E8DE46662920B337565C8ABE414A4F189802A25C0E6B068BFDCBC7C550D57 | |||
| 5608 | msiexec.exe | C:\Windows\Temp\~DFEA3CDB5B7F67BE9D.TMP | binary | |
MD5:BF619EAC0CDF3F68D496EA9344137E8B | SHA256:076A27C79E5ACE2A3D47F9DD2E83E4FF6EA8872B3C2218F66C92B89B55F36560 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
10
TCP/UDP connections
69
DNS requests
18
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2104 | svchost.exe | GET | 200 | 69.192.161.161:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
2104 | svchost.exe | GET | 200 | 23.216.77.28:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
4996 | RUXIMICS.exe | GET | 304 | 69.192.161.161:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
4172 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20Update%20Signing%20CA%202.1.crl | unknown | — | — | whitelisted |
4172 | SIHClient.exe | GET | 200 | 23.216.77.22:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut_2010-06-23.crl | unknown | — | — | whitelisted |
4172 | SIHClient.exe | GET | 200 | 23.216.77.22:80 | http://crl.microsoft.com/pki/crl/products/MicTimStaPCA_2010-07-01.crl | unknown | — | — | whitelisted |
4172 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20Update%20Signing%20CA%202.2.crl | unknown | — | — | whitelisted |
4172 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Signing%20CA%202.2.crl | unknown | — | — | whitelisted |
4172 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
4172 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Signing%20CA%202.1.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4996 | RUXIMICS.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2104 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 172.211.123.248:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
2104 | svchost.exe | 23.216.77.28:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
2104 | svchost.exe | 69.192.161.161:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4996 | RUXIMICS.exe | 69.192.161.161:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
6544 | svchost.exe | 20.190.159.2:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
activation-v2.sls.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1244 | svchost.exe | Misc Attack | ET DROP Spamhaus DROP Listed Traffic Inbound group 19 |