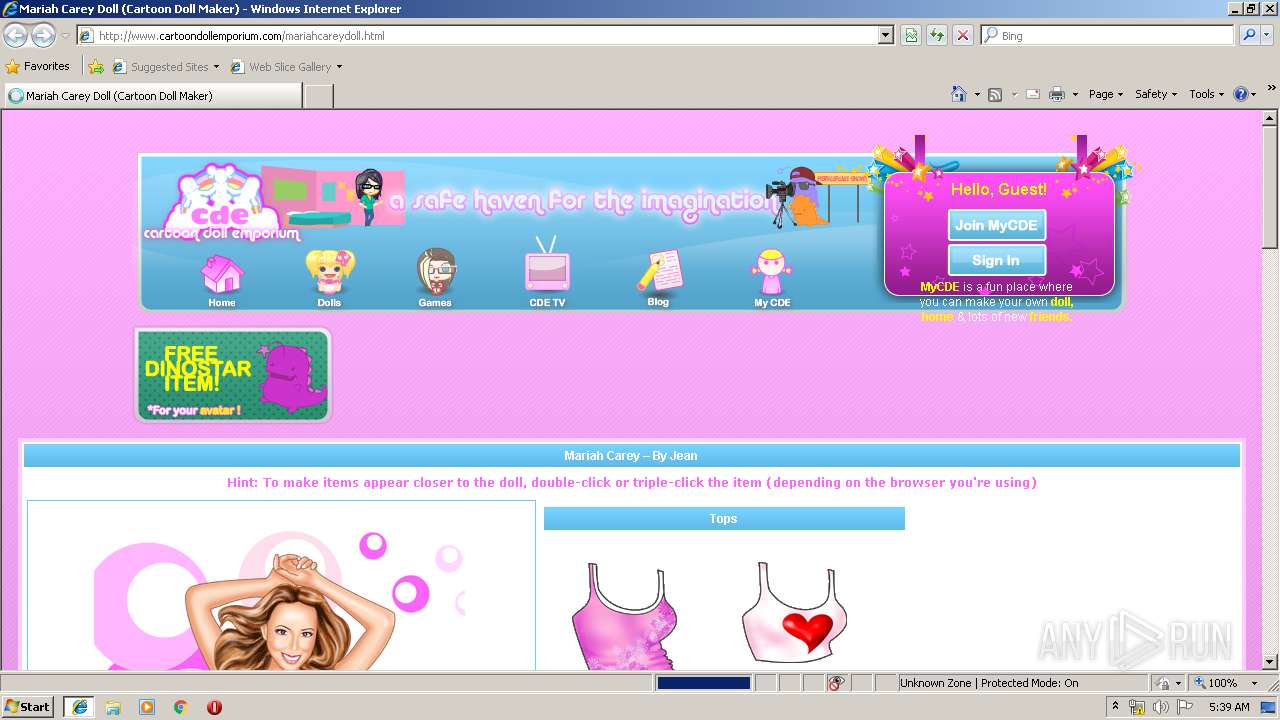
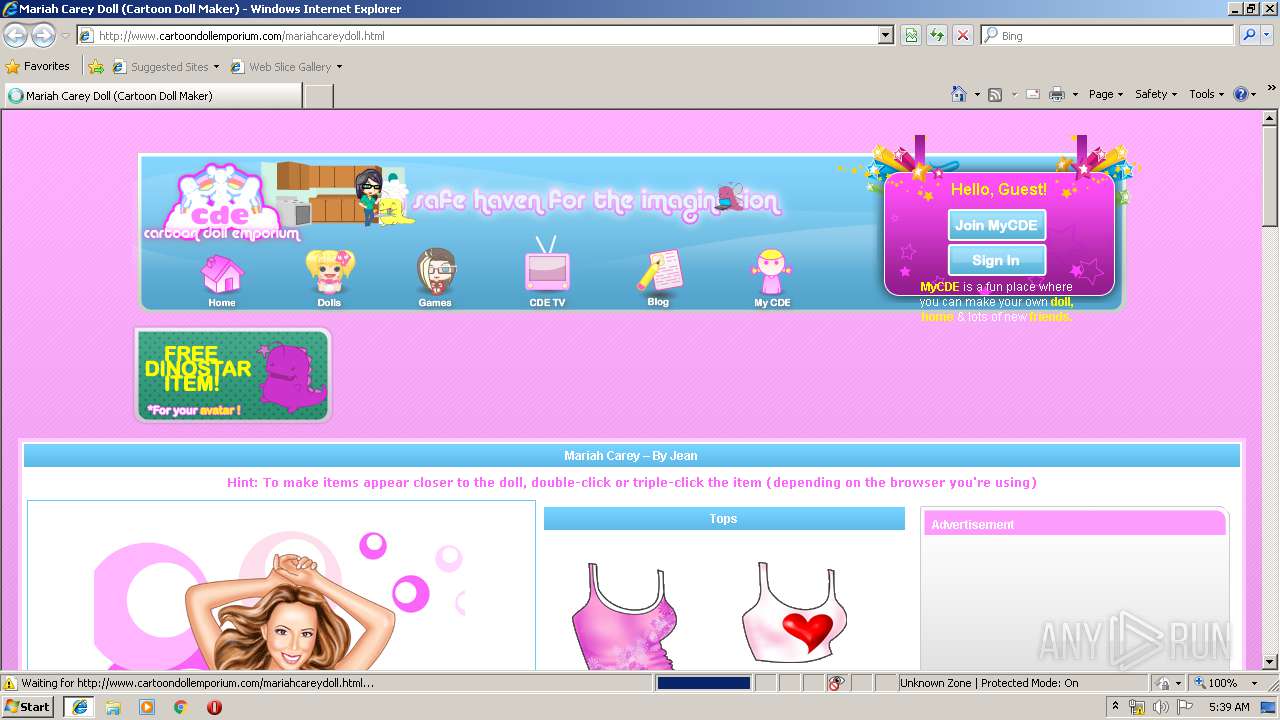
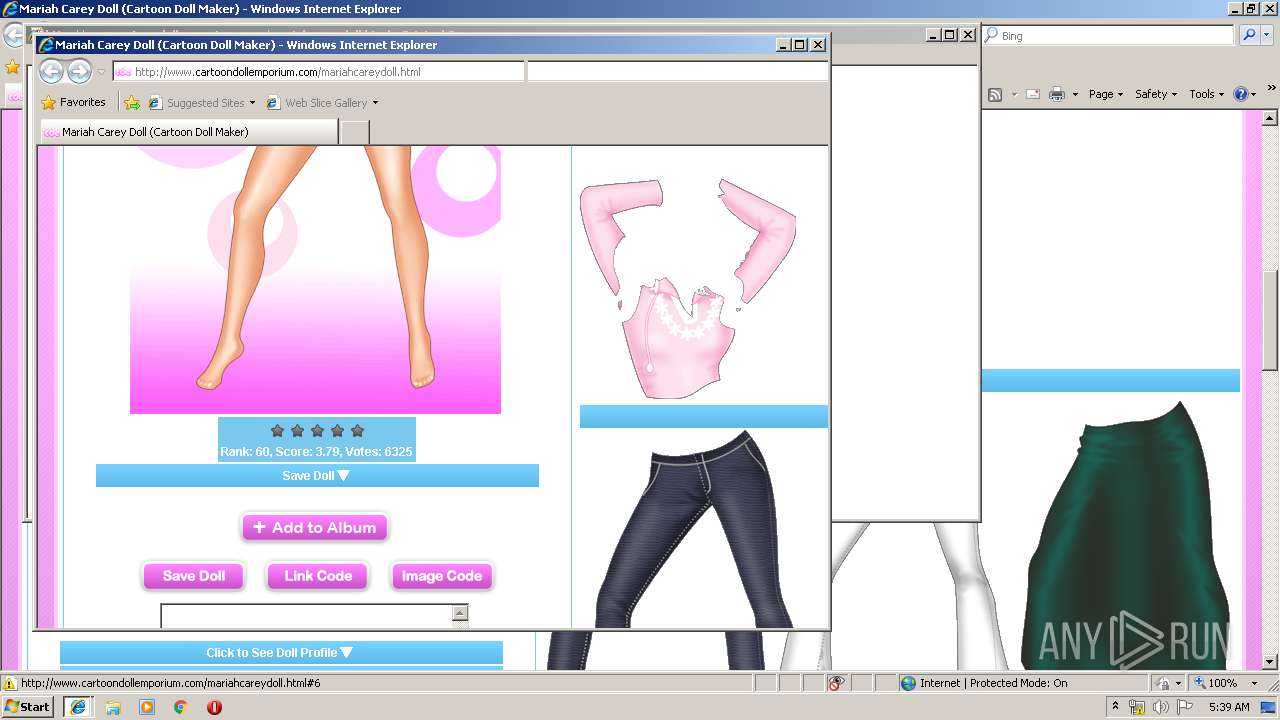
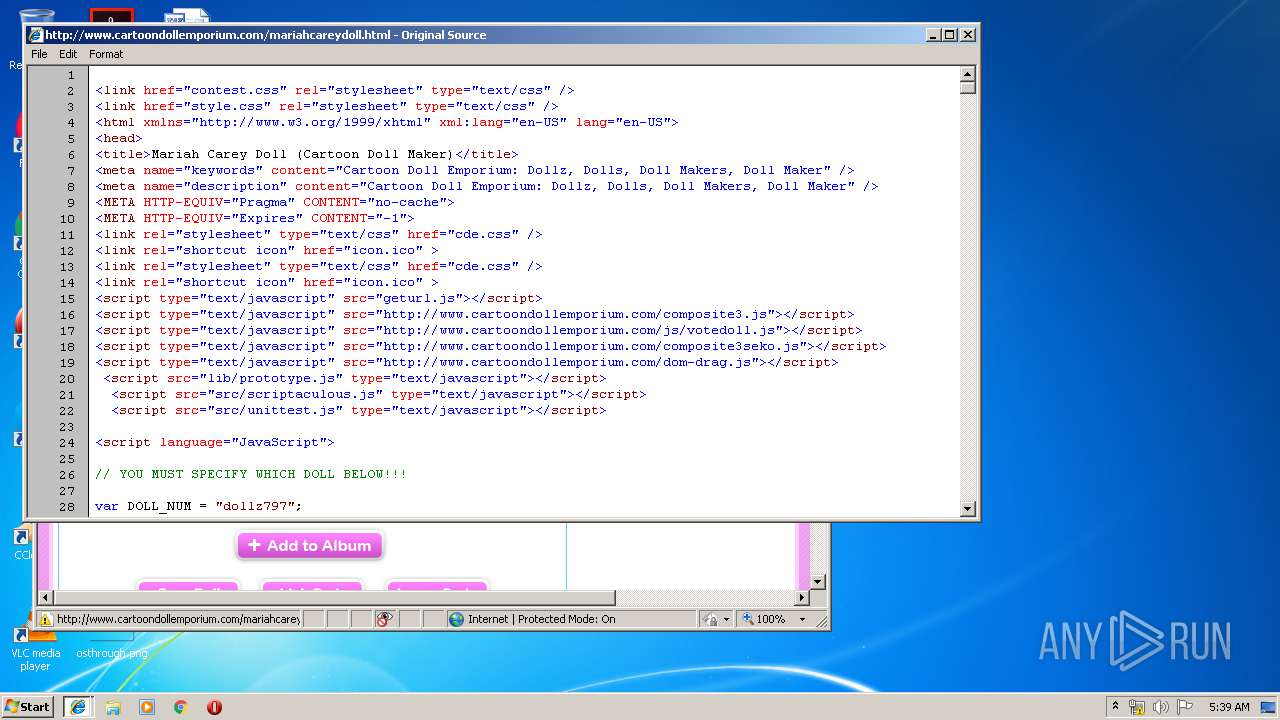
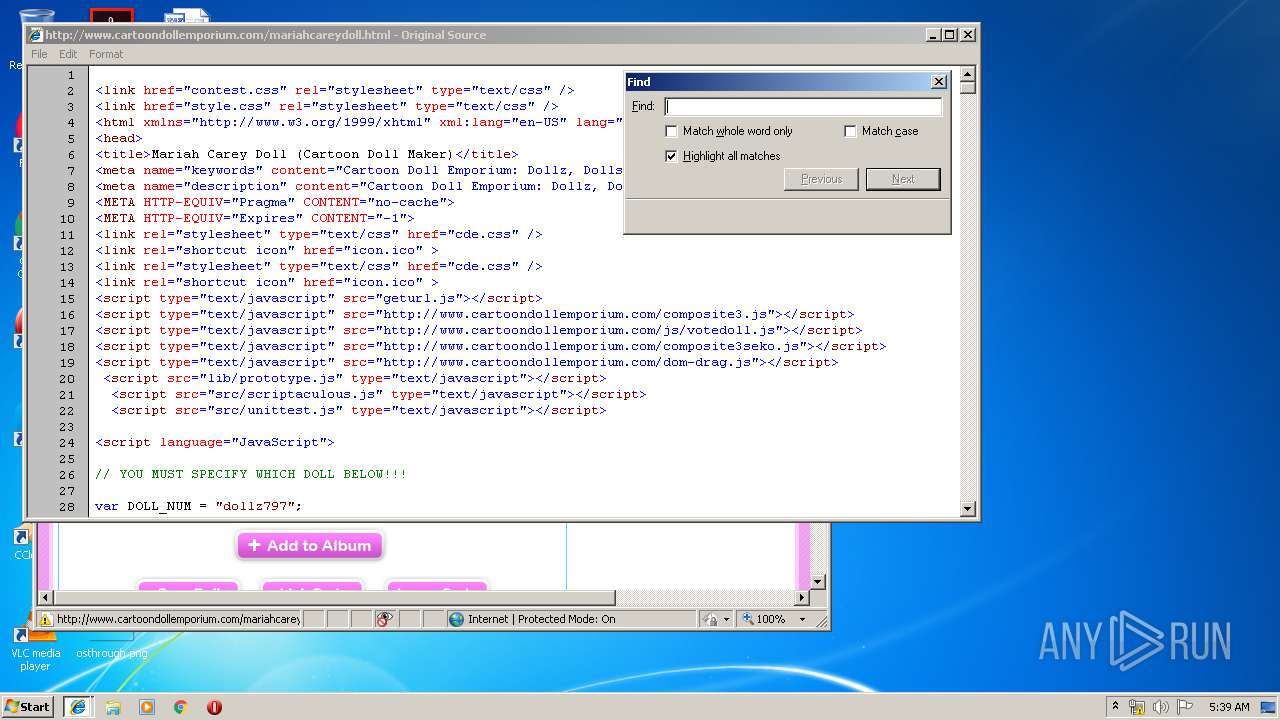
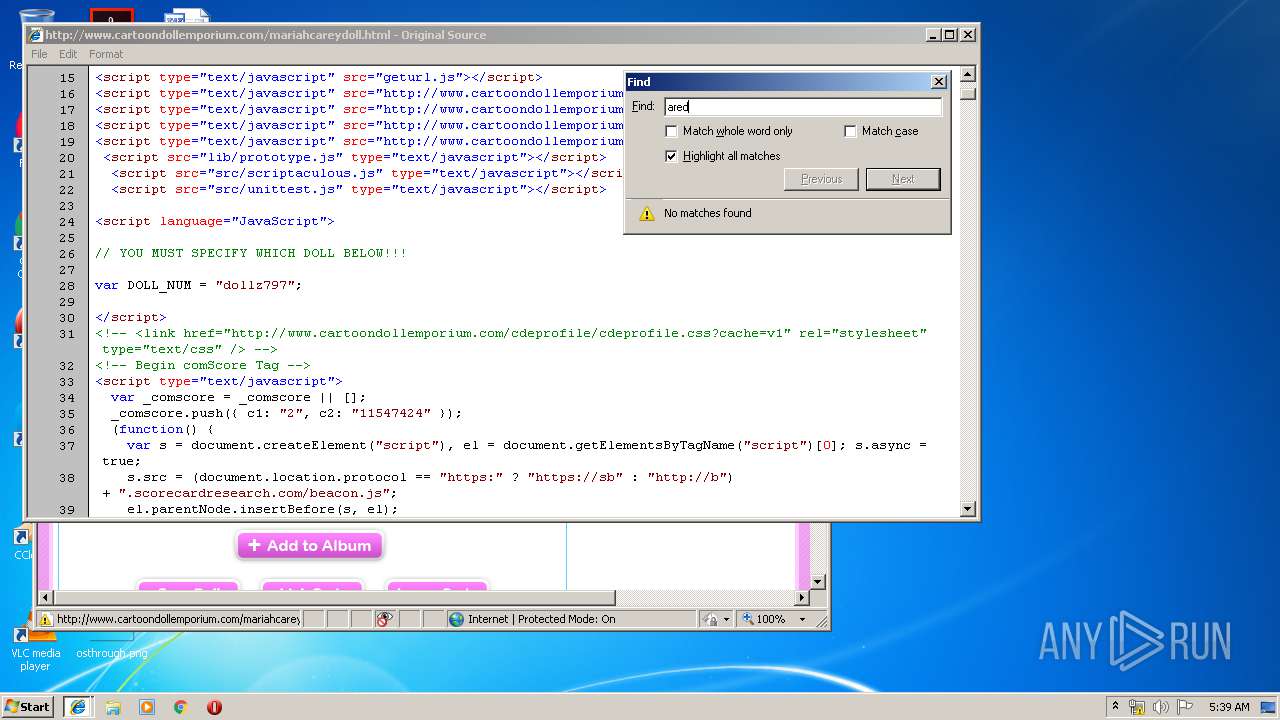
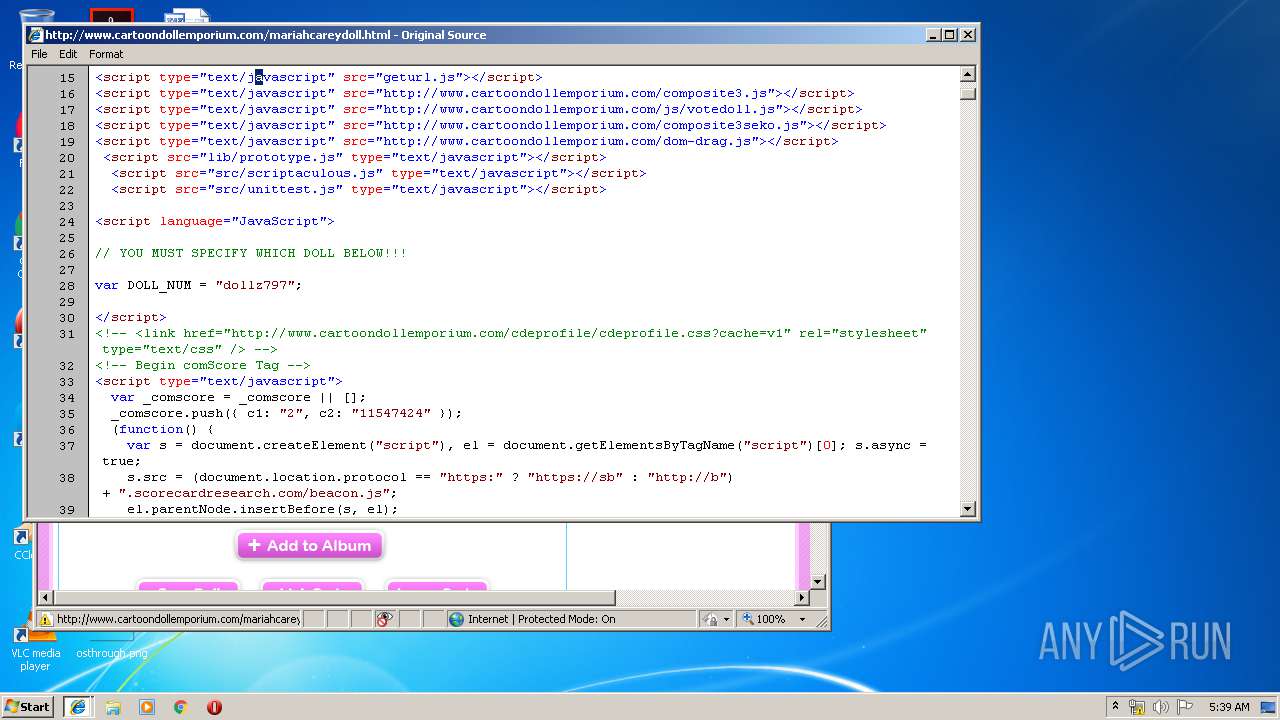
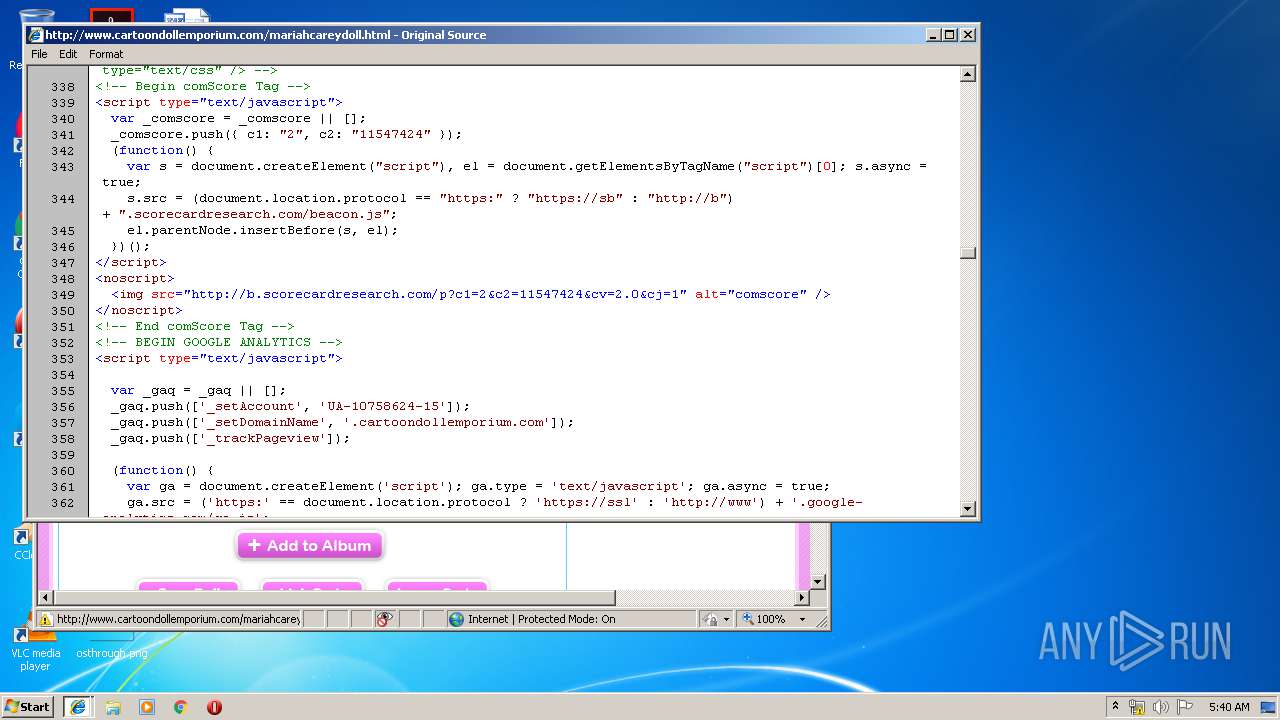
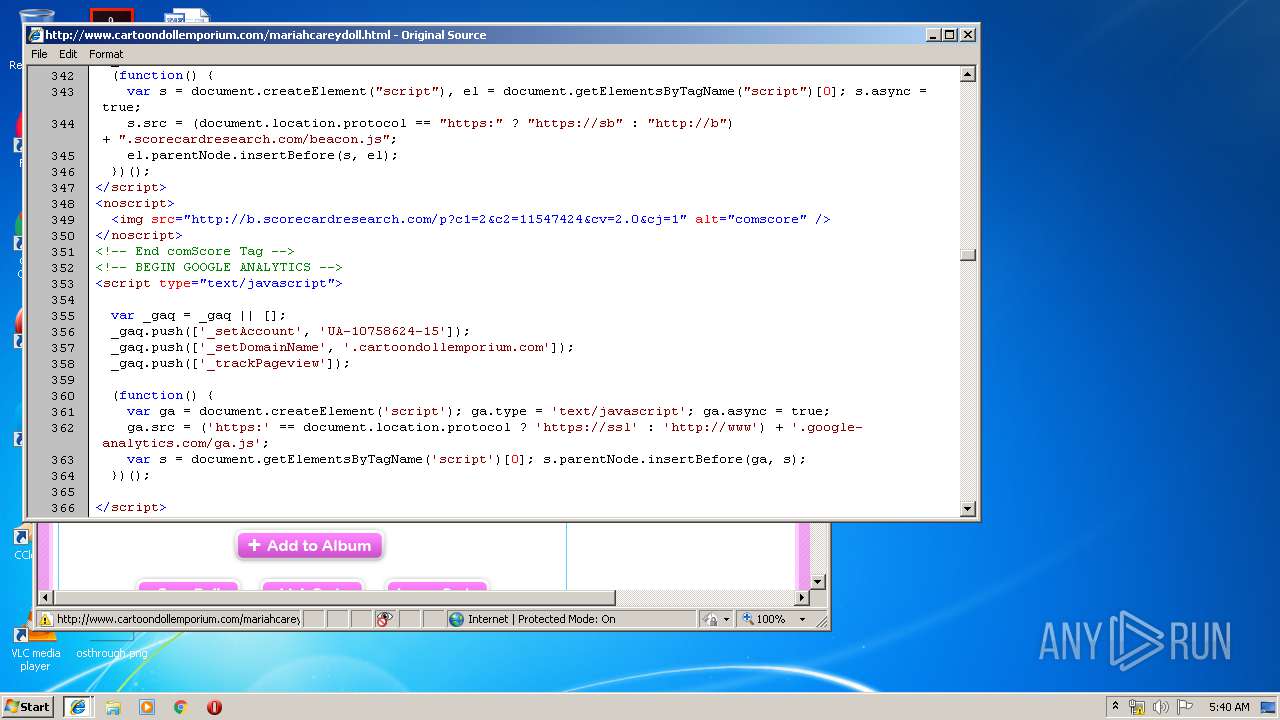
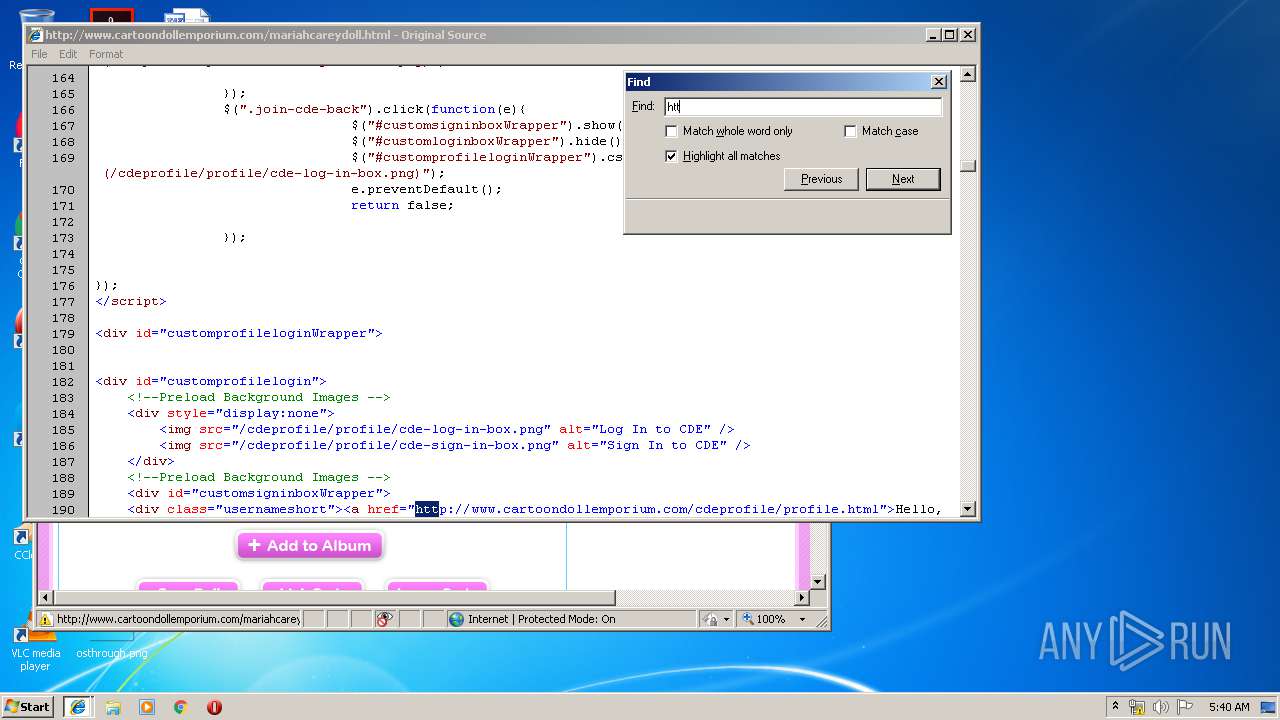
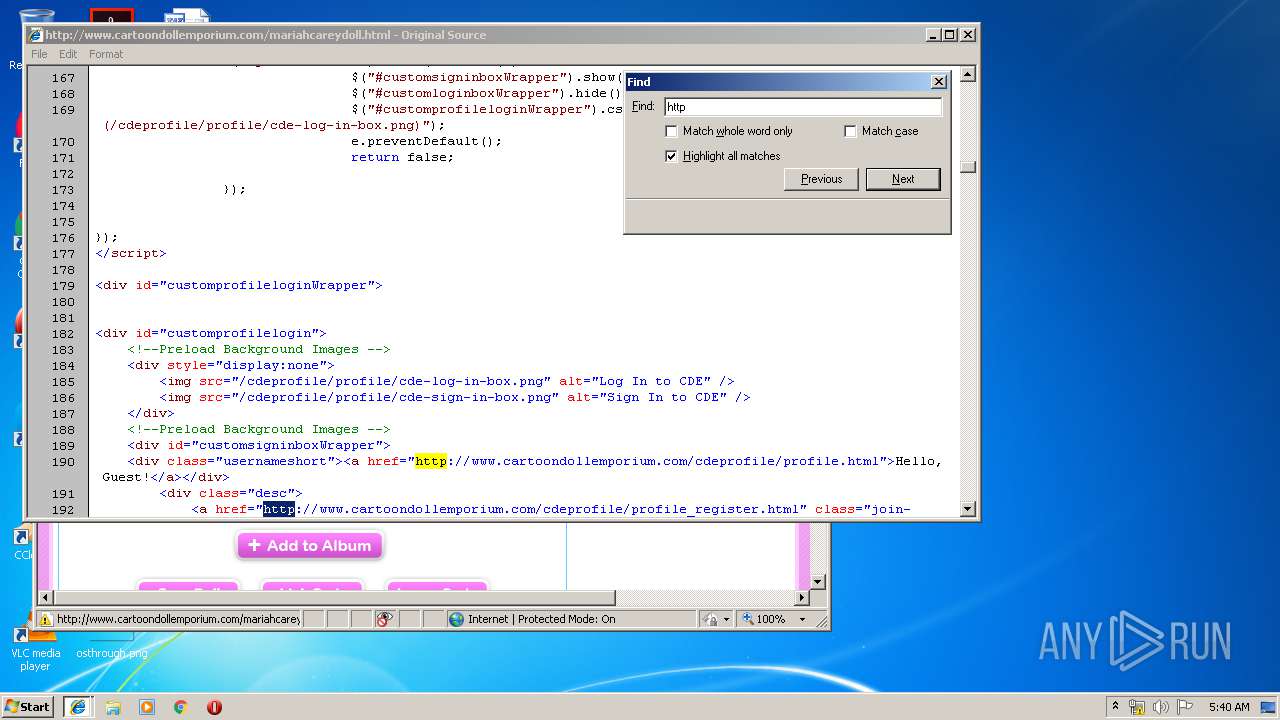
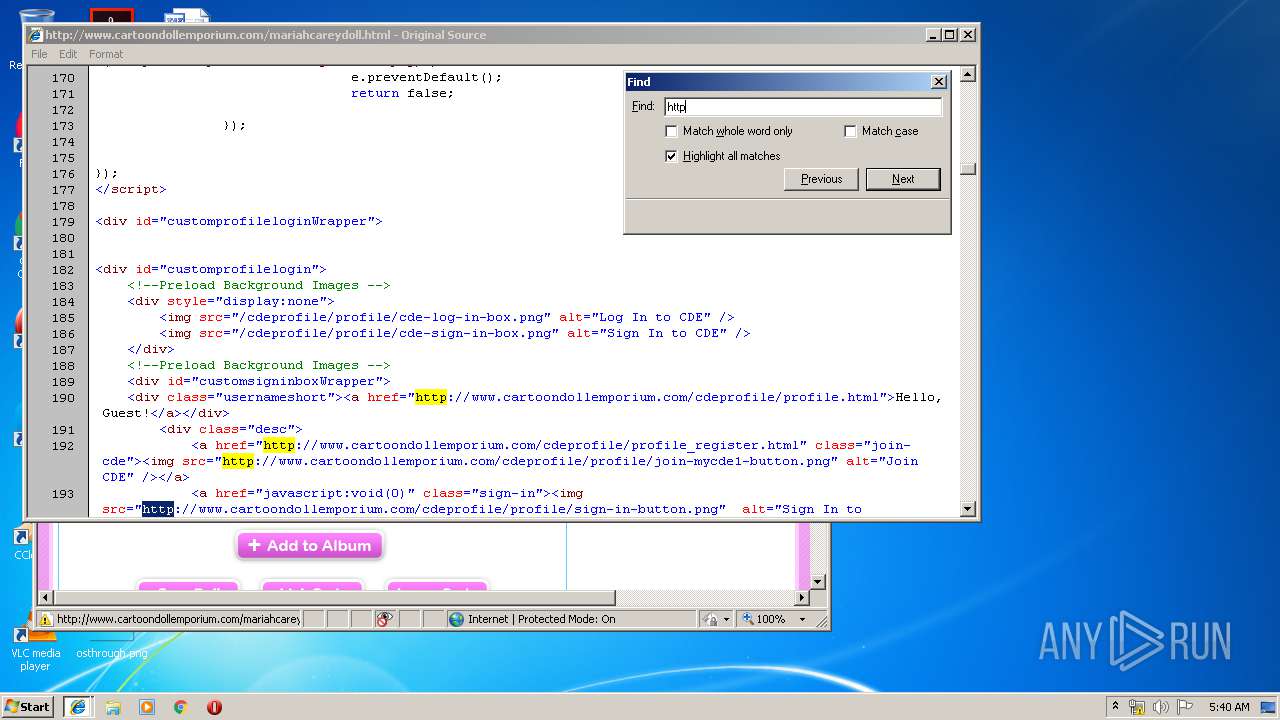
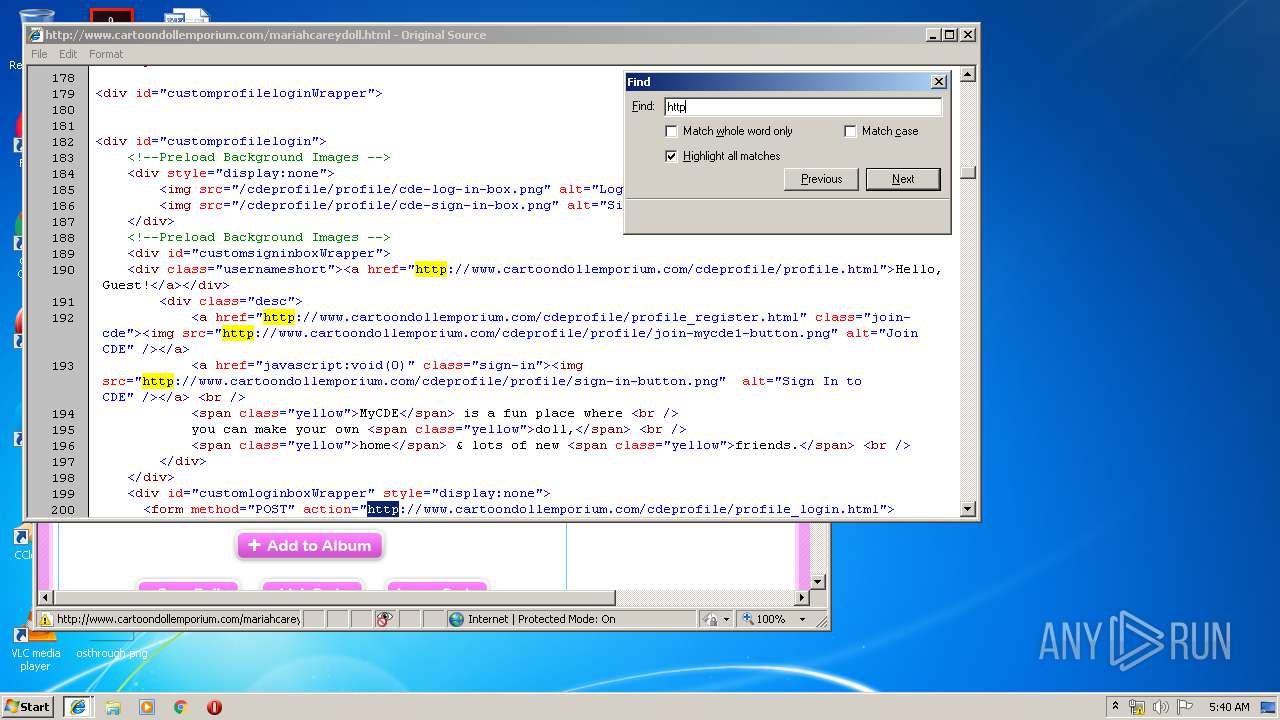
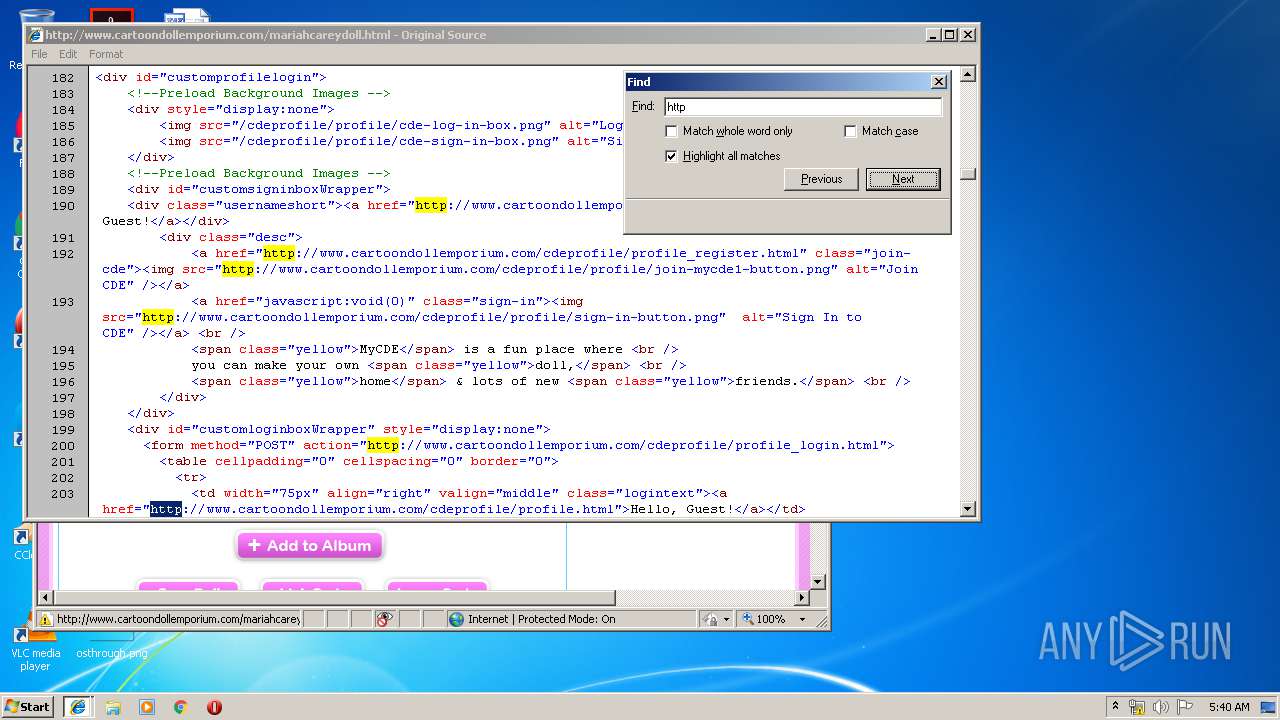
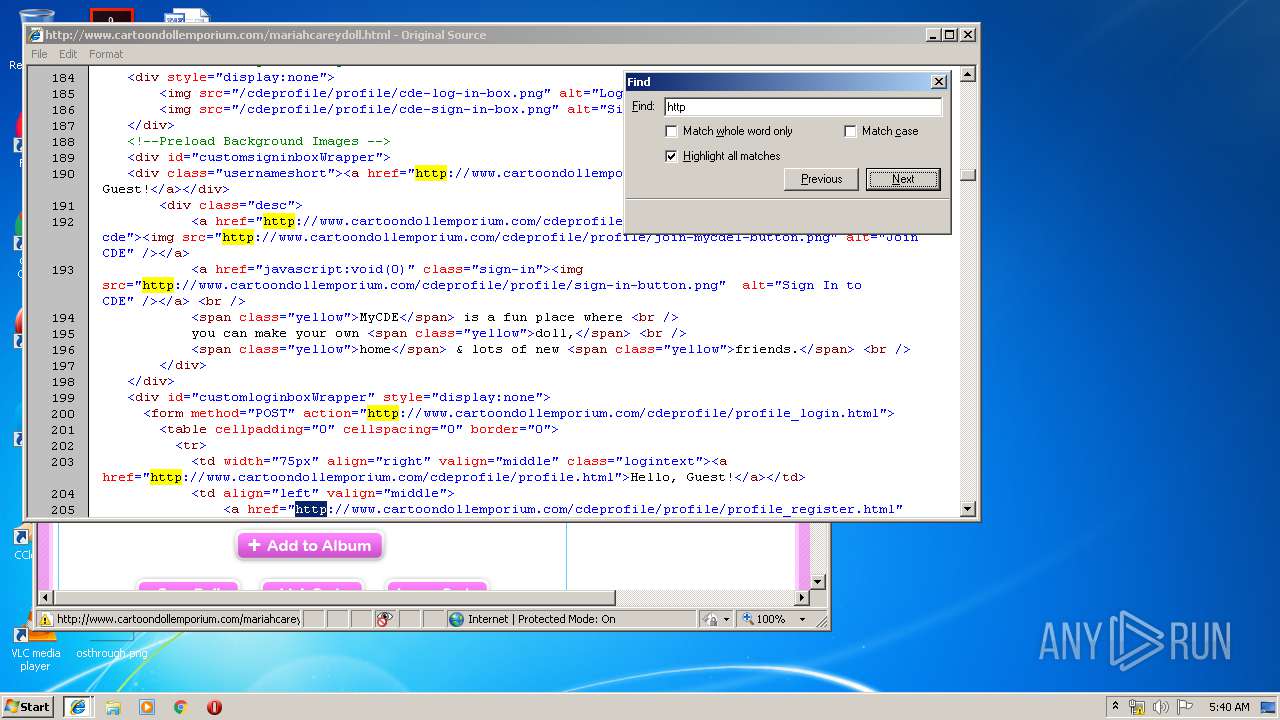
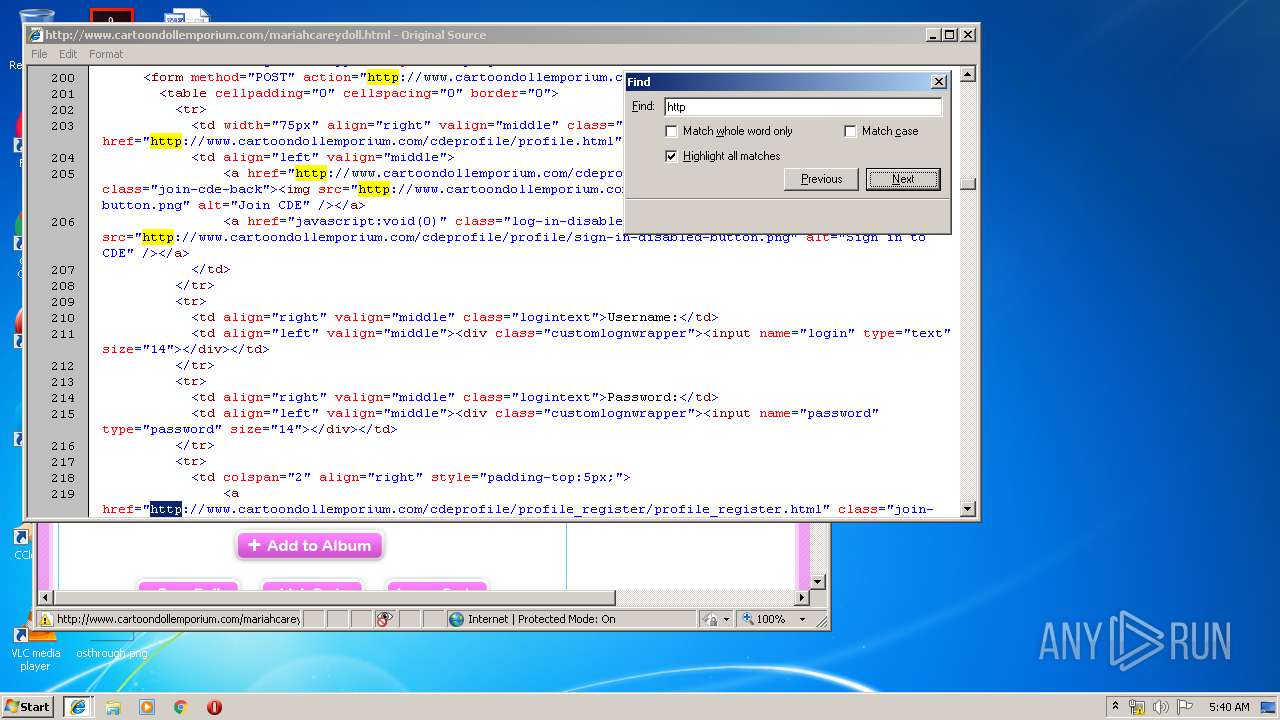
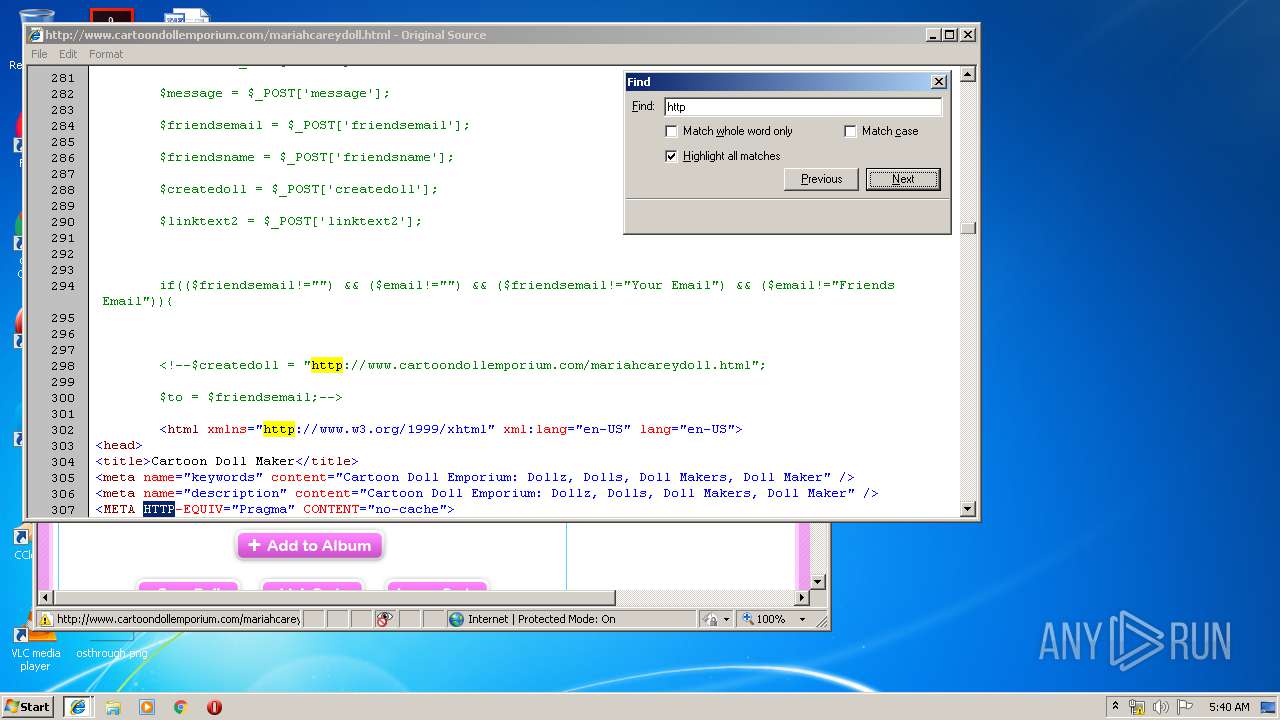
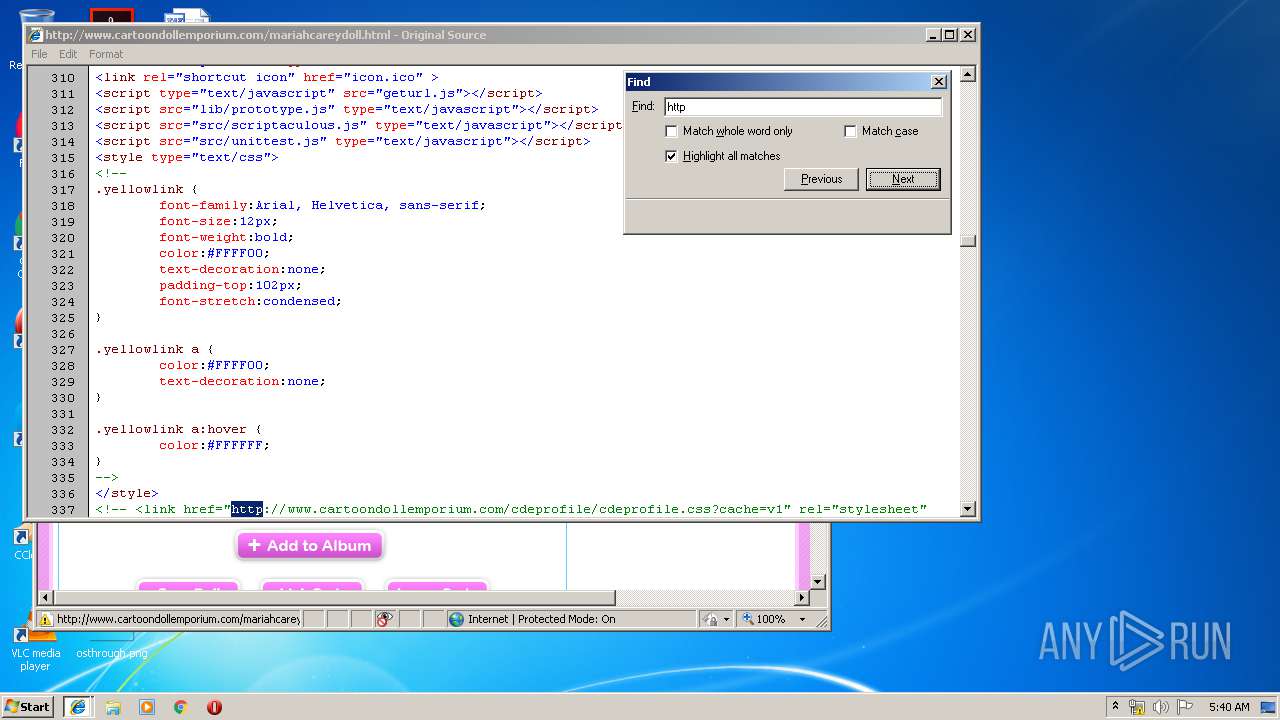
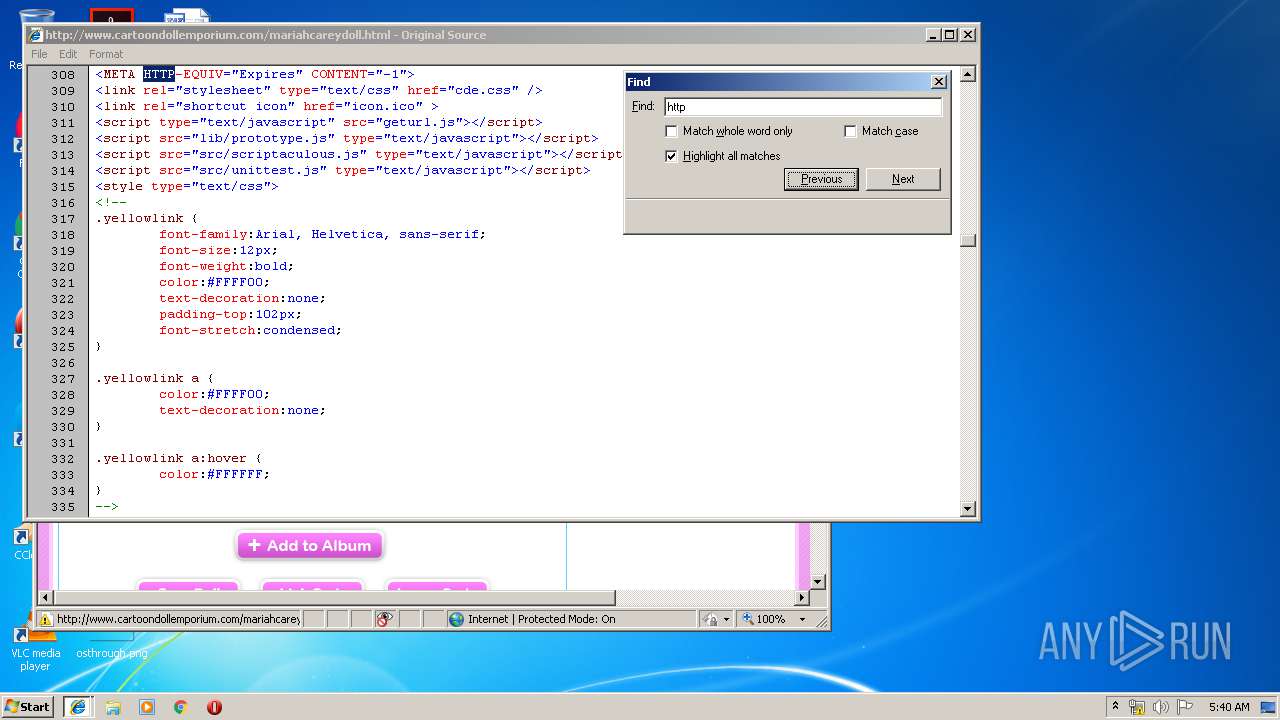
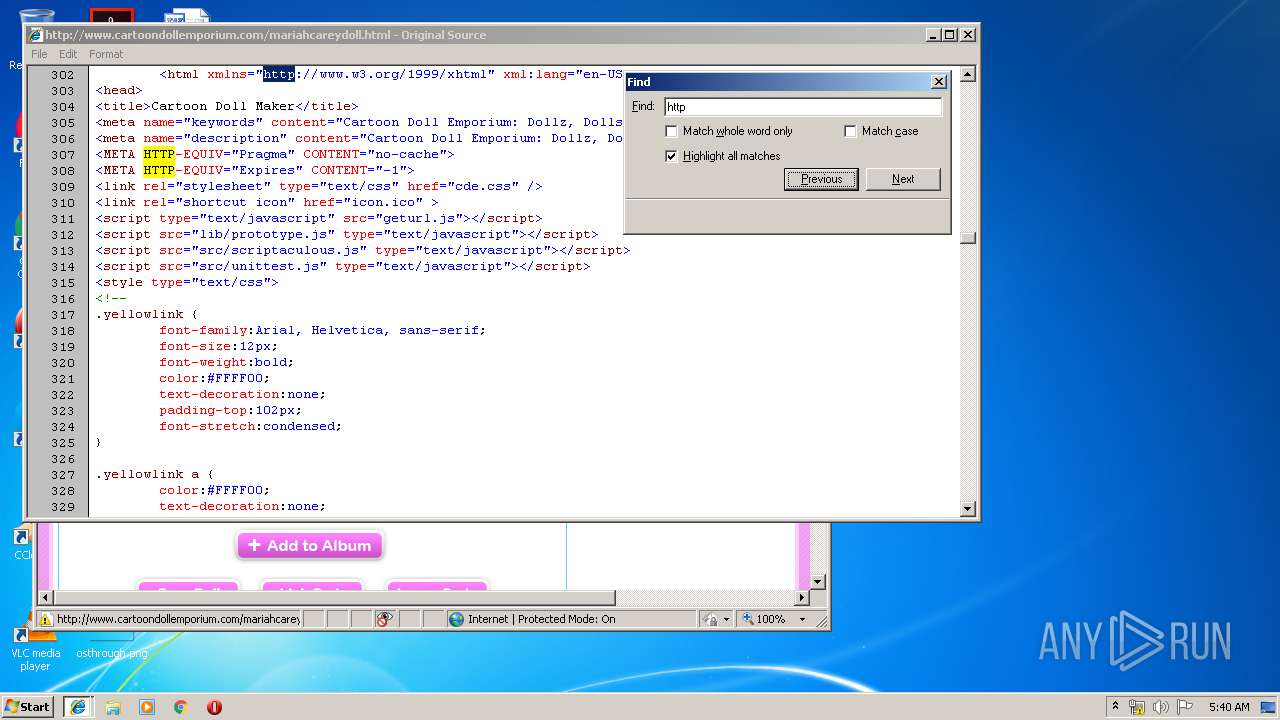
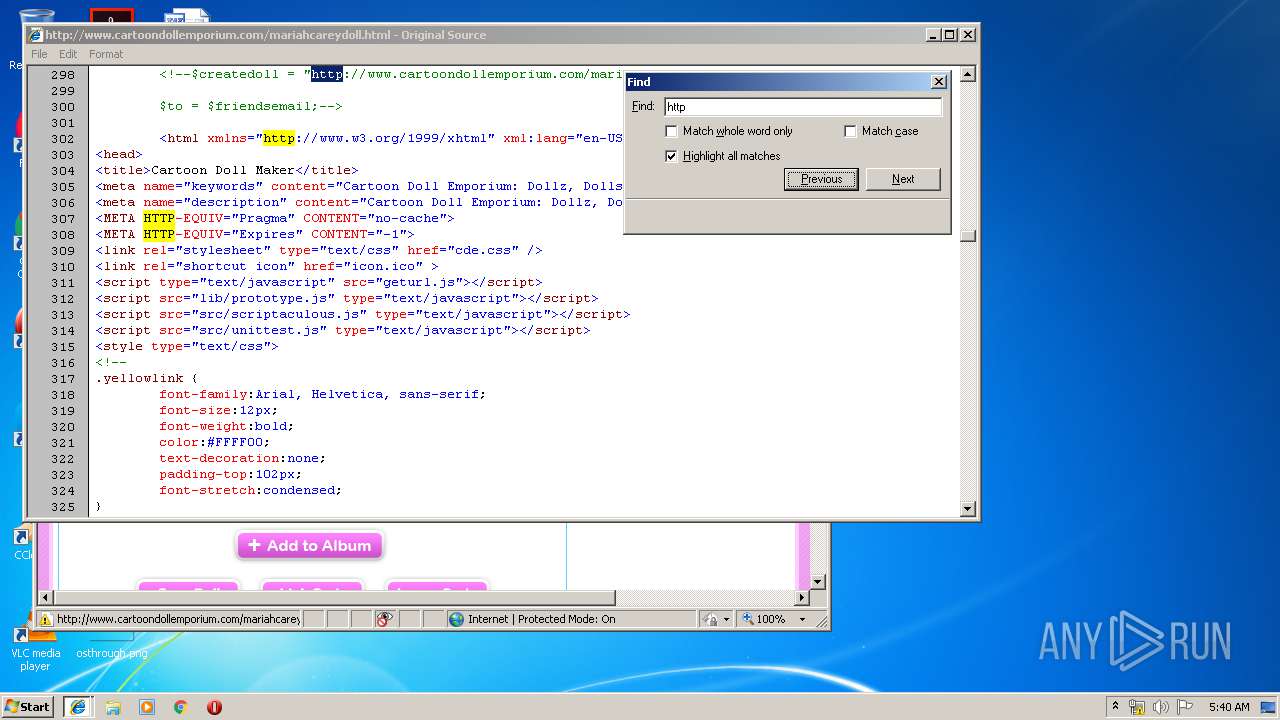
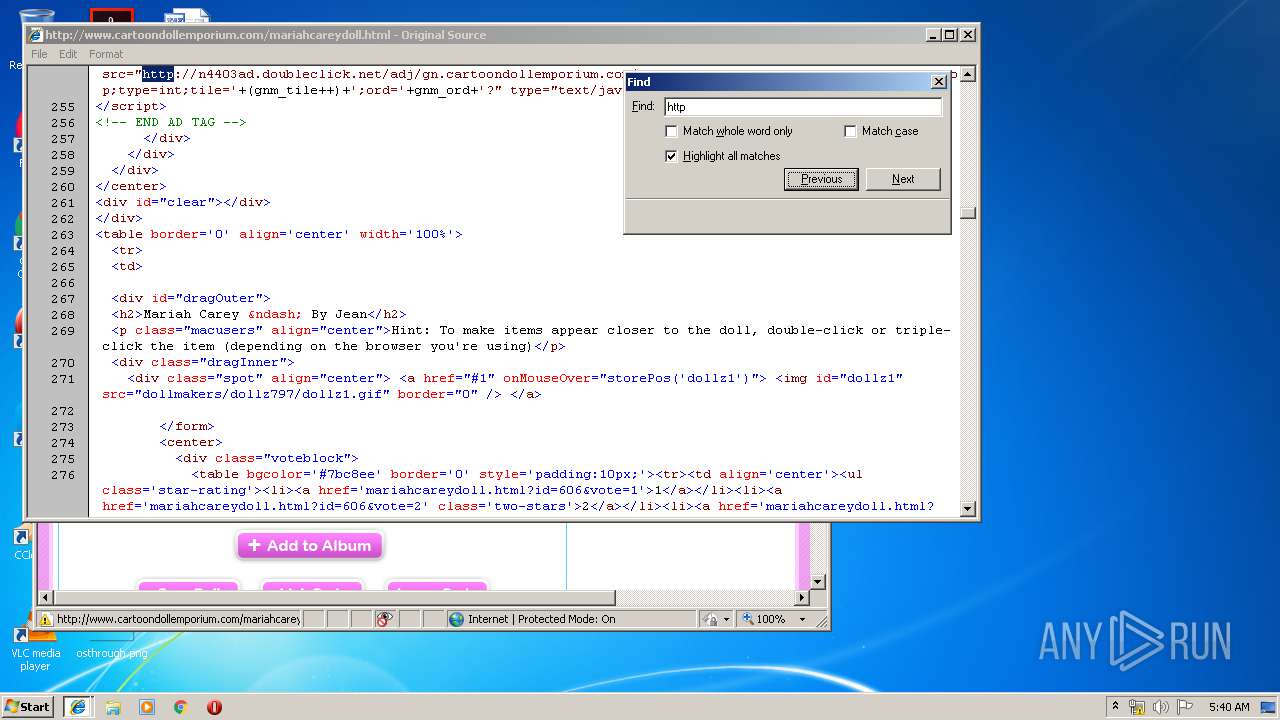
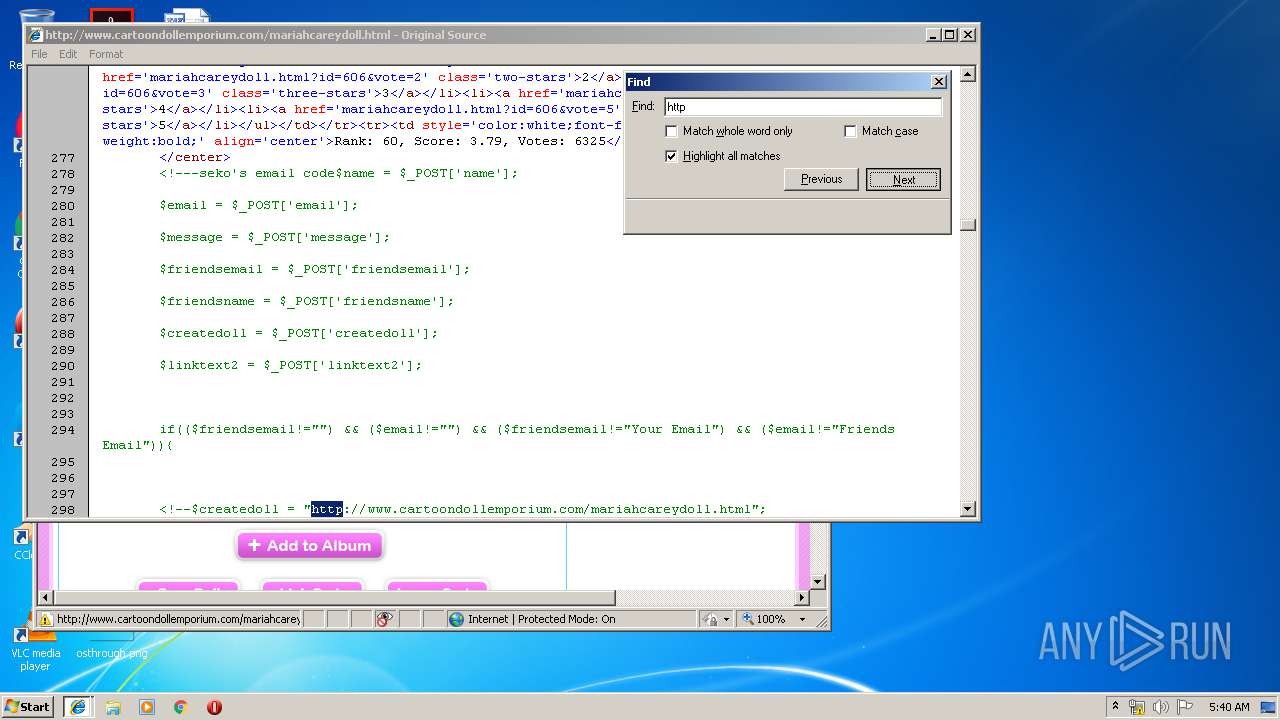
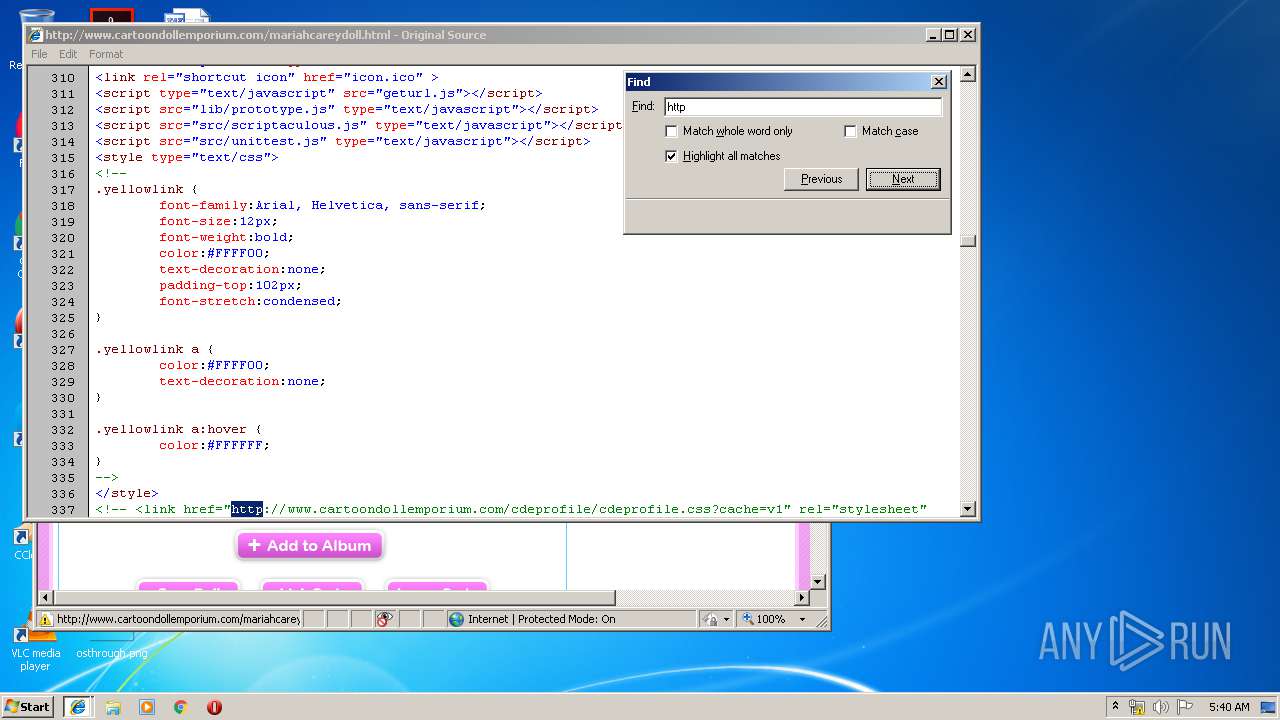
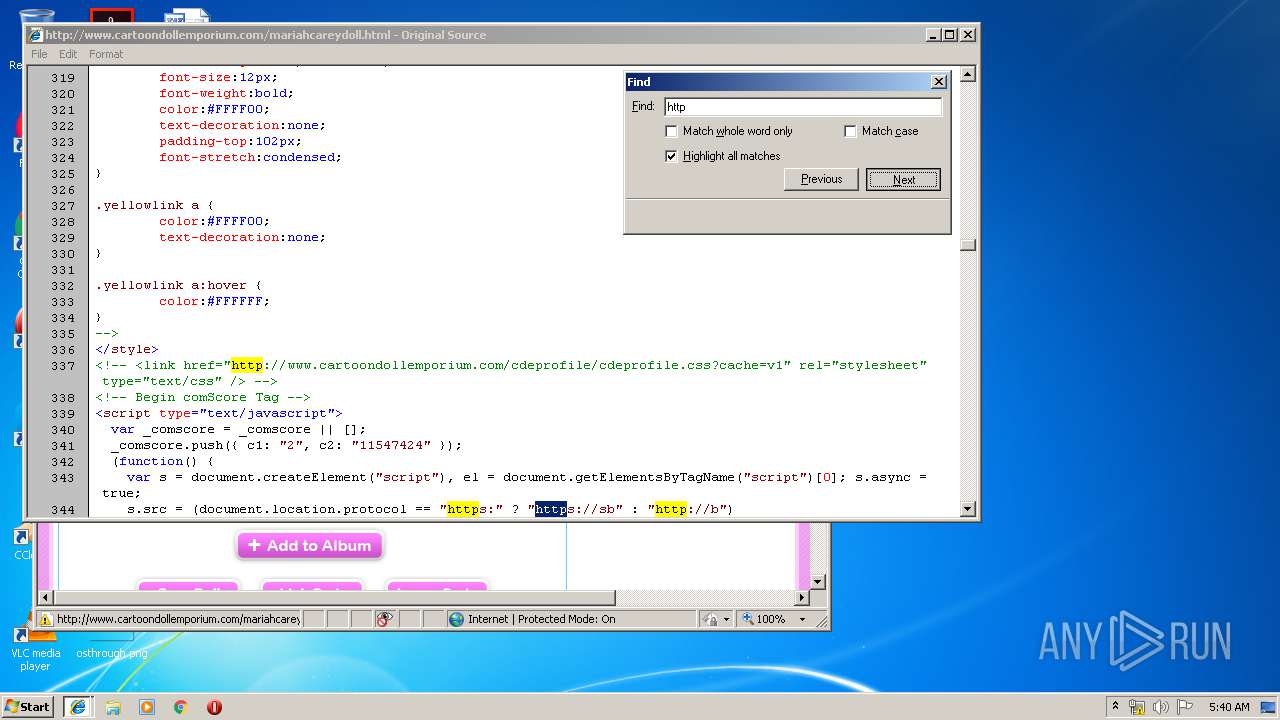
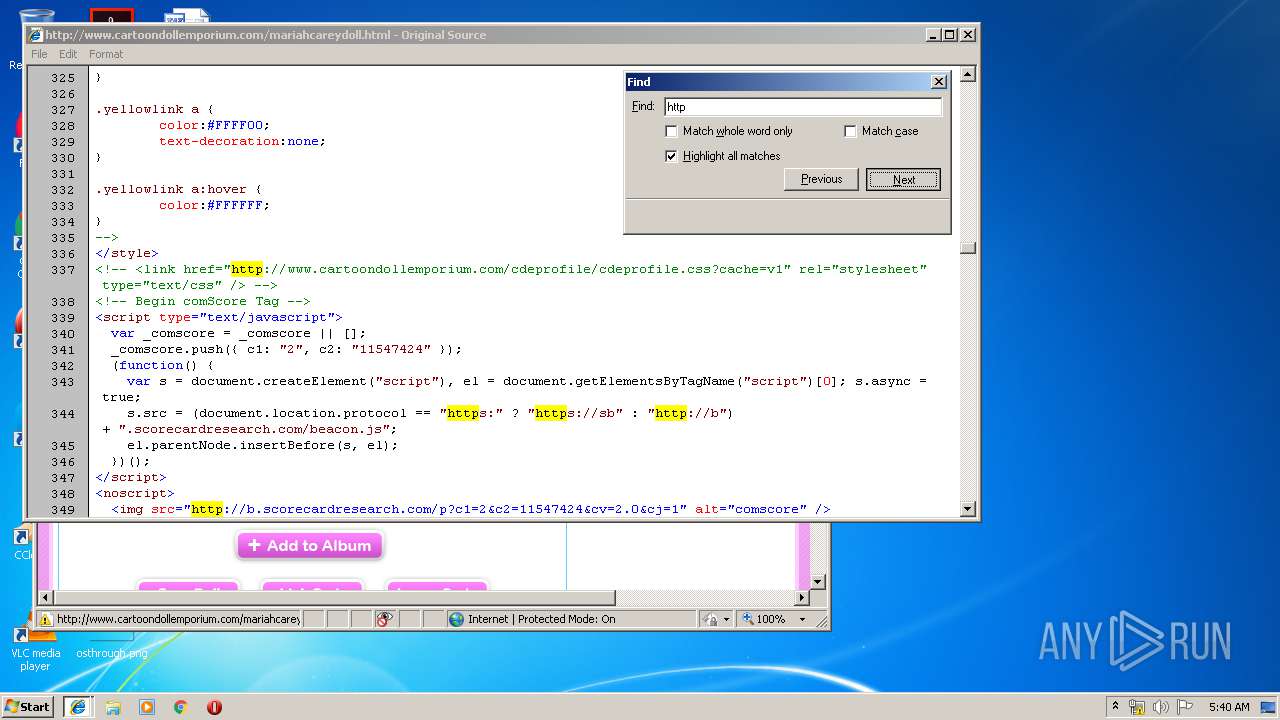
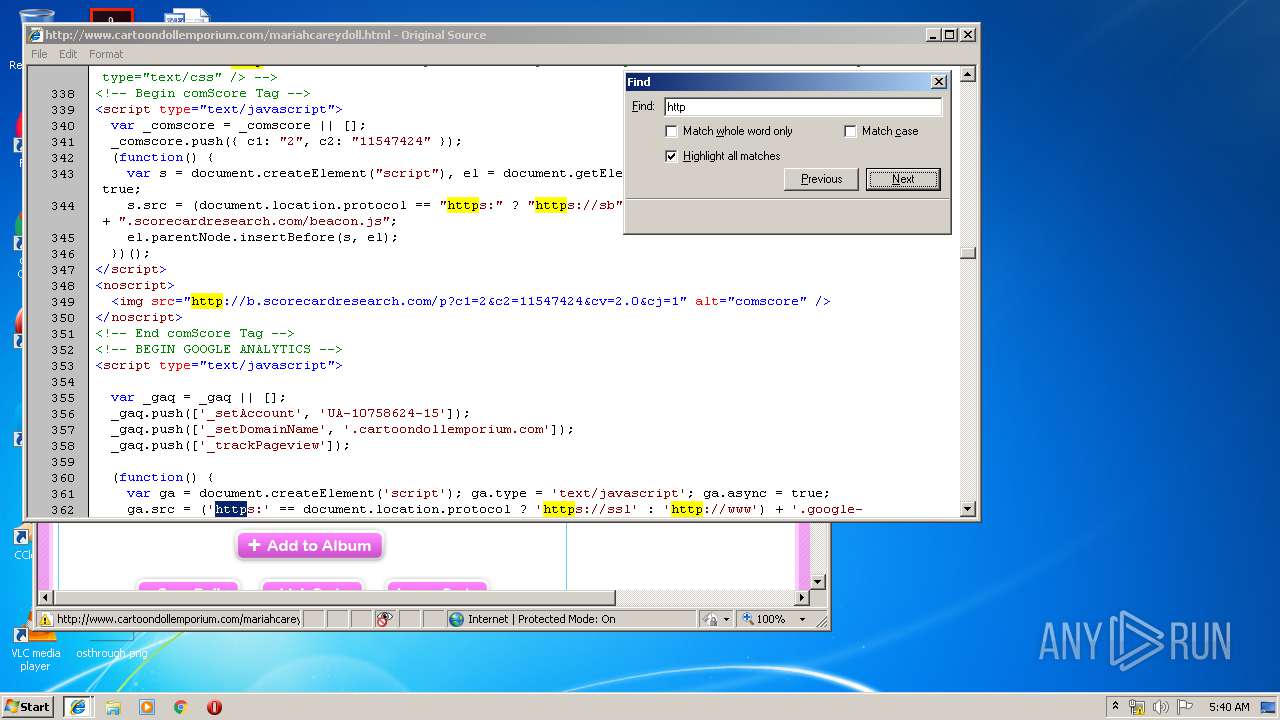
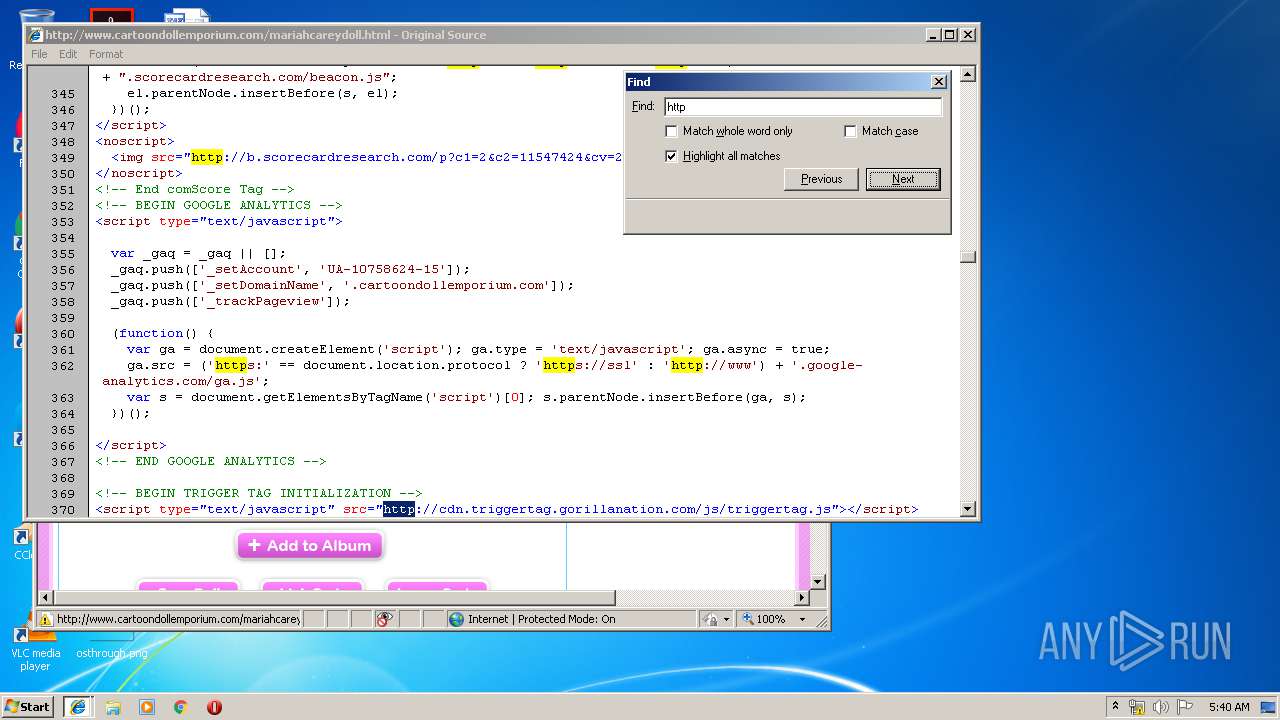
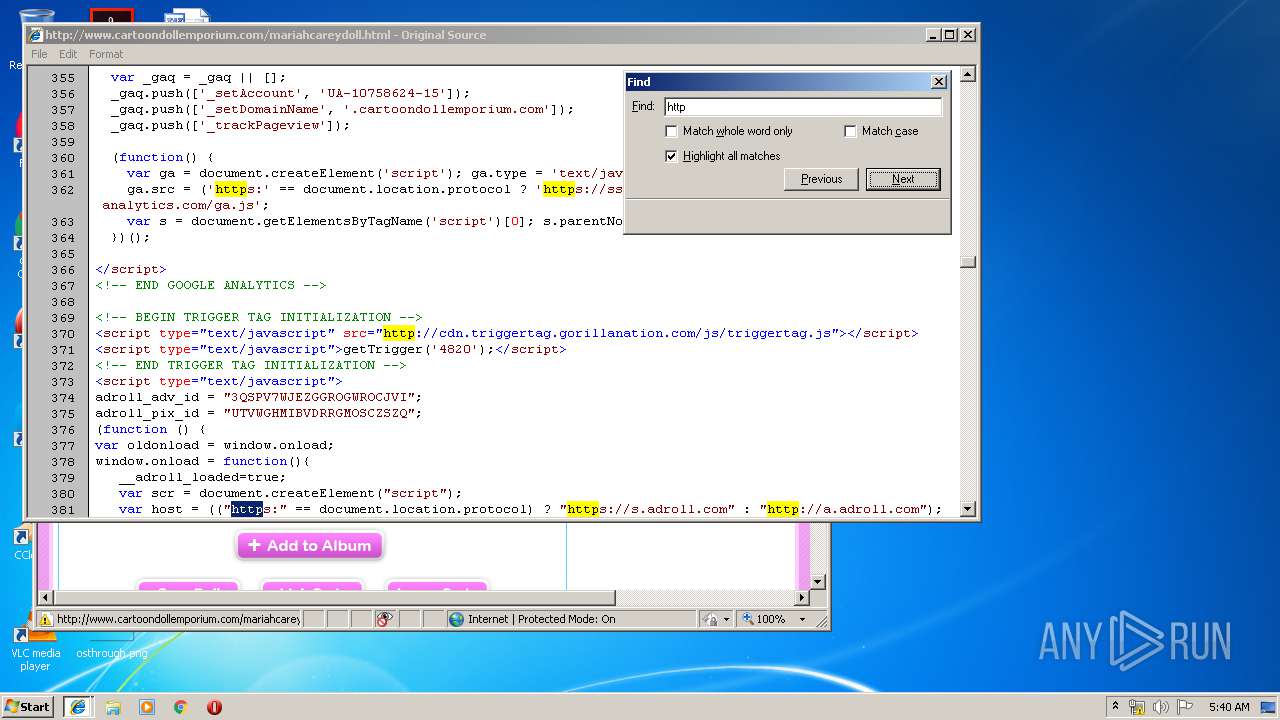
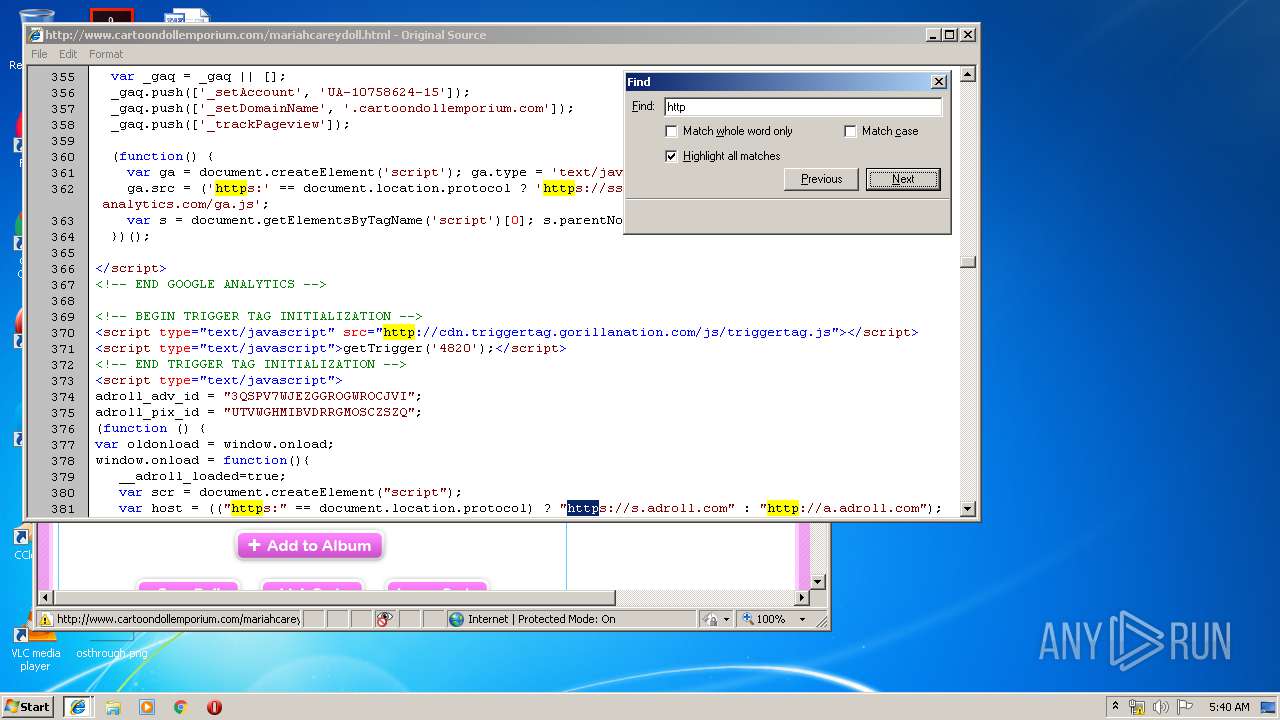
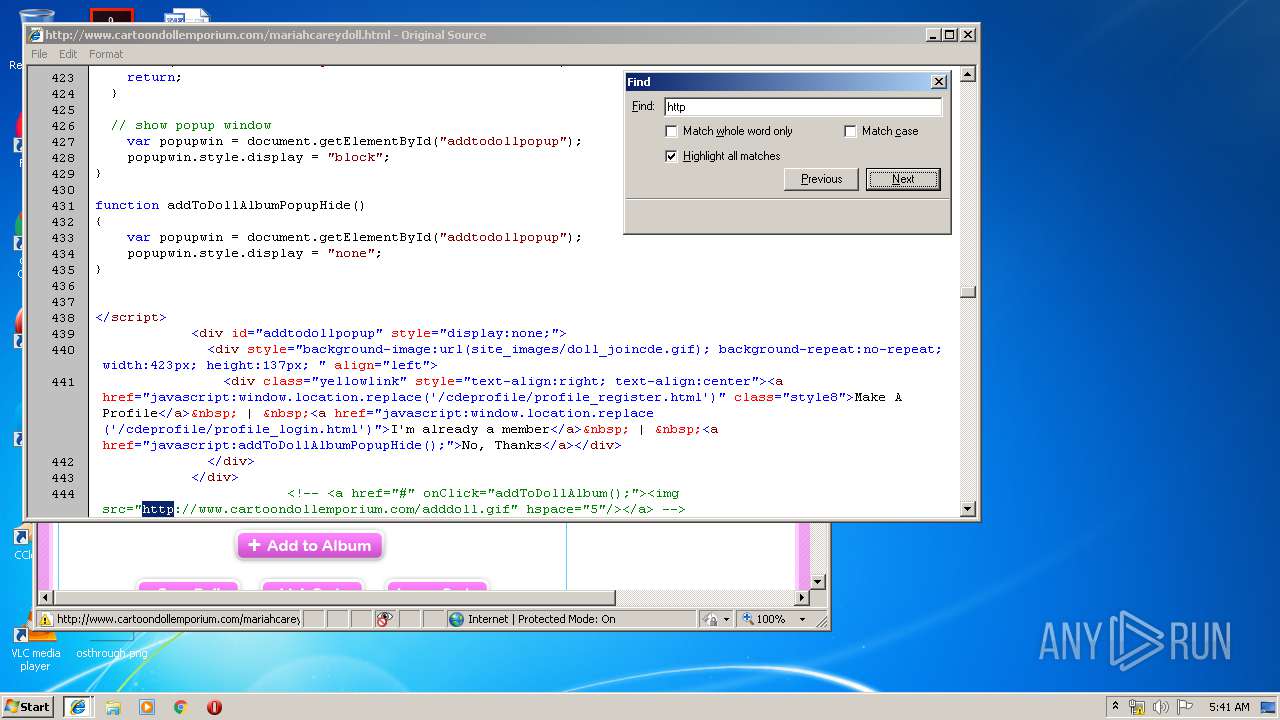
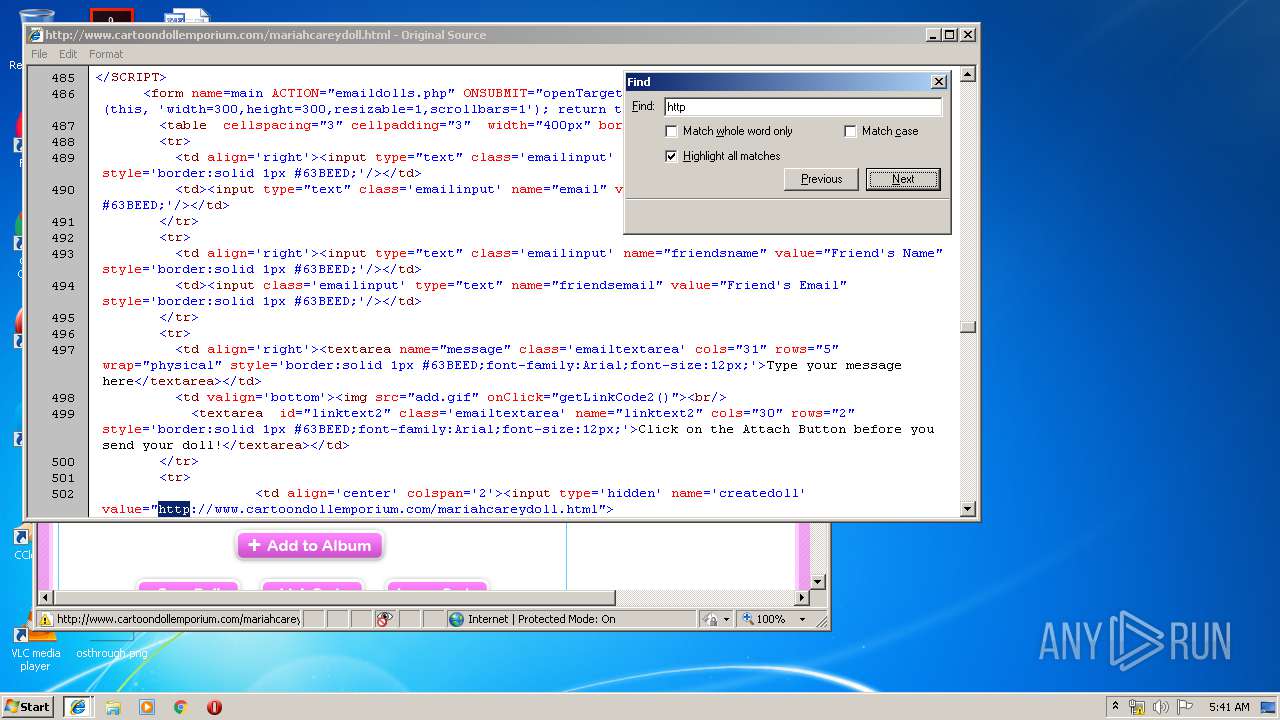
| URL: | http://www.cartoondollemporium.com/mariahcareydoll.html |
| Full analysis: | https://app.any.run/tasks/8440d0bb-8682-4db4-b80d-51df23f51e42 |
| Verdict: | Malicious activity |
| Analysis date: | July 25, 2019, 04:38:12 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 9A65417B94BBC673D55A2EA3FD4DBE24 |
| SHA1: | 5787DE0B9765E1BD3A95188032D6B2D87905E991 |
| SHA256: | 5C92567433138BDFFA42480B695FA1EB7126EA48306E9B0F3FA15EFB5F324A74 |
| SSDEEP: | 3:N1KJS4bRtY/iPEaJP0:Cc4VPECP0 |
MALICIOUS
No malicious indicators.SUSPICIOUS
Executed via COM
- FlashUtil32_26_0_0_131_ActiveX.exe (PID: 3304)
INFO
Changes internet zones settings
- iexplore.exe (PID: 3892)
Application launched itself
- iexplore.exe (PID: 3892)
Creates files in the user directory
- iexplore.exe (PID: 2052)
- FlashUtil32_26_0_0_131_ActiveX.exe (PID: 3304)
Reads settings of System Certificates
- iexplore.exe (PID: 2052)
Reads internet explorer settings
- iexplore.exe (PID: 2052)
Reads Internet Cache Settings
- iexplore.exe (PID: 2052)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
39
Monitored processes
3
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2052 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3892 CREDAT:71937 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3304 | C:\Windows\system32\Macromed\Flash\FlashUtil32_26_0_0_131_ActiveX.exe -Embedding | C:\Windows\system32\Macromed\Flash\FlashUtil32_26_0_0_131_ActiveX.exe | — | svchost.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: MEDIUM Description: Adobe® Flash® Player Installer/Uninstaller 26.0 r0 Exit code: 0 Version: 26,0,0,131 Modules
| |||||||||||||||
| 3892 | "C:\Program Files\Internet Explorer\iexplore.exe" "http://www.cartoondollemporium.com/mariahcareydoll.html" | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
487
Read events
398
Write events
87
Delete events
2
Modification events
| (PID) Process: | (3892) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (3892) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3892) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3892) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Zones |
| Operation: | write | Name: | SecuritySafe |
Value: 1 | |||
| (PID) Process: | (3892) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (3892) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 4600000077000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3892) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Recovery\Active |
| Operation: | write | Name: | {111D1CA1-AE96-11E9-A9B1-5254004A04AF} |
Value: 0 | |||
| (PID) Process: | (3892) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Type |
Value: 4 | |||
| (PID) Process: | (3892) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Count |
Value: 1 | |||
| (PID) Process: | (3892) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Time |
Value: E3070700040019000400260026008500 | |||
Executable files
0
Suspicious files
5
Text files
114
Unknown types
31
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3892 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\JGRR2OYX\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 3892 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 2052 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\History\Low\History.IE5\index.dat | dat | |
MD5:1CC3B1D0E19495DEBB64FACE11EBC0EF | SHA256:203F9B4F37F5F0C4F348A159FF0F7F749C1F8BA67EBB2FA0FCF39ECAA8118C34 | |||
| 2052 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\index.dat | dat | |
MD5:3A6FA10A37A406E011B6FE65915F3564 | SHA256:9353E3D000471B5B6C658E828E04457CF0D8179D5A6BE52284673CA10AEF0D87 | |||
| 2052 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\I82PY3OI\mariahcareydoll[1].html | html | |
MD5:588B7FCEB52B94C894FE0AA7FFEAE625 | SHA256:EE2A43D9F4409BA834756A1ACBFFF17C30CE75BB501928659A066B3F89BF3585 | |||
| 2052 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\I82PY3OI\geturl[1].js | text | |
MD5:F215ADEDC318DCB935E952938010CCCC | SHA256:718B9E903A157FF76FAE3C9EFCDCCDEF52DFCAEB2666438ED30A333D32A9F2E6 | |||
| 2052 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\B6111W9P\triggertag[1].js | text | |
MD5:26716490EE3019F3B4D0021C99531778 | SHA256:A24C20A1468ACDB637AC8A89D5E90BEE8FFA99F90407FF7392BDA3D0490D906B | |||
| 2052 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\I82PY3OI\style[1].css | text | |
MD5:86C84C6A82C4ED1D1572995979D1A191 | SHA256:64F71F955251AB8DFD5CA03514A146A412924456EC7FBAF582928CE929F0C100 | |||
| 2052 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\I82PY3OI\votedoll[1].js | text | |
MD5:8281C5C9C88CF89204533ADE4B881AD1 | SHA256:0FD3A4A0A90D4CDCAB50A40378119823567933FCBC83970EA2EDEF6918CD2645 | |||
| 2052 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\desktop.ini | ini | |
MD5:4A3DEB274BB5F0212C2419D3D8D08612 | SHA256:2842973D15A14323E08598BE1DFB87E54BF88A76BE8C7BC94C56B079446EDF38 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
94
TCP/UDP connections
24
DNS requests
17
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2052 | iexplore.exe | GET | 200 | 173.192.50.116:80 | http://www.cartoondollemporium.com/cde.css | US | text | 15.4 Kb | suspicious |
2052 | iexplore.exe | GET | 200 | 173.192.50.116:80 | http://www.cartoondollemporium.com/images2/star.gif | US | image | 562 b | suspicious |
2052 | iexplore.exe | GET | 200 | 173.192.50.116:80 | http://www.cartoondollemporium.com/images2/star2.gif | US | image | 360 b | suspicious |
2052 | iexplore.exe | GET | 200 | 173.192.50.116:80 | http://www.cartoondollemporium.com/mariahcareydoll.html | US | html | 9.01 Kb | suspicious |
2052 | iexplore.exe | GET | 200 | 173.192.50.116:80 | http://www.cartoondollemporium.com/geturl.js | US | text | 356 b | suspicious |
2052 | iexplore.exe | GET | 200 | 173.192.50.116:80 | http://www.cartoondollemporium.com/js/votedoll.js | US | text | 389 b | suspicious |
2052 | iexplore.exe | GET | 200 | 173.192.50.116:80 | http://www.cartoondollemporium.com/composite3seko.js | US | binary | 20 b | suspicious |
2052 | iexplore.exe | GET | 200 | 104.16.166.11:80 | http://cdn.triggertag.gorillanation.com/js/triggertag.js | US | text | 959 b | whitelisted |
2052 | iexplore.exe | GET | 200 | 173.192.50.116:80 | http://www.cartoondollemporium.com/lib/prototype.js | US | text | 21.5 Kb | suspicious |
3892 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2052 | iexplore.exe | 172.217.18.170:80 | ajax.googleapis.com | Google Inc. | US | whitelisted |
2052 | iexplore.exe | 173.192.50.116:80 | www.cartoondollemporium.com | SoftLayer Technologies Inc. | US | suspicious |
2052 | iexplore.exe | 172.217.22.78:80 | www.google-analytics.com | Google Inc. | US | whitelisted |
3892 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
2052 | iexplore.exe | 104.16.166.11:80 | cdn.triggertag.gorillanation.com | Cloudflare Inc | US | shared |
2052 | iexplore.exe | 2.16.186.80:80 | b.scorecardresearch.com | Akamai International B.V. | — | whitelisted |
2052 | iexplore.exe | 104.27.129.251:80 | cdn.assets.craveonline.com | Cloudflare Inc | US | shared |
2052 | iexplore.exe | 204.11.109.78:80 | tags.expo9.exponential.com | Exponential Interactive, Inc. | US | unknown |
2052 | iexplore.exe | 204.11.109.65:80 | a.tribalfusion.com | Exponential Interactive, Inc. | US | unknown |
2052 | iexplore.exe | 172.217.22.102:80 | n4403ad.doubleclick.net | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.cartoondollemporium.com |
| suspicious |
ajax.googleapis.com |
| whitelisted |
cdn.triggertag.gorillanation.com |
| whitelisted |
www.bing.com |
| whitelisted |
b.scorecardresearch.com |
| whitelisted |
www.google-analytics.com |
| whitelisted |
geo.gorillanation.com |
| unknown |
cdn.assets.craveonline.com |
| whitelisted |
n4403ad.doubleclick.net |
| suspicious |
tags.expo9.exponential.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2052 | iexplore.exe | Potential Corporate Privacy Violation | ET POLICY Outdated Flash Version M1 |