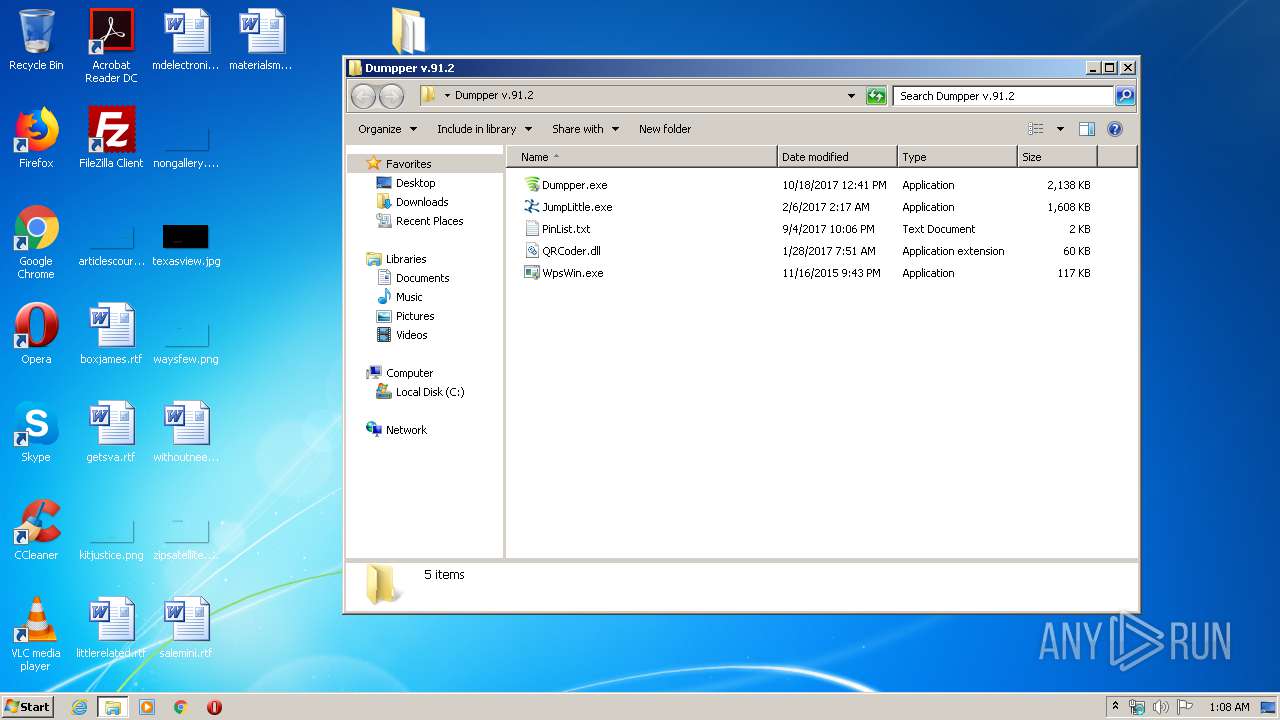
| File name: | Dumpper v.91.2.zip |
| Full analysis: | https://app.any.run/tasks/63a70baa-3c88-4919-bbce-c2f4ace10941 |
| Verdict: | Malicious activity |
| Analysis date: | April 13, 2020, 00:07:59 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
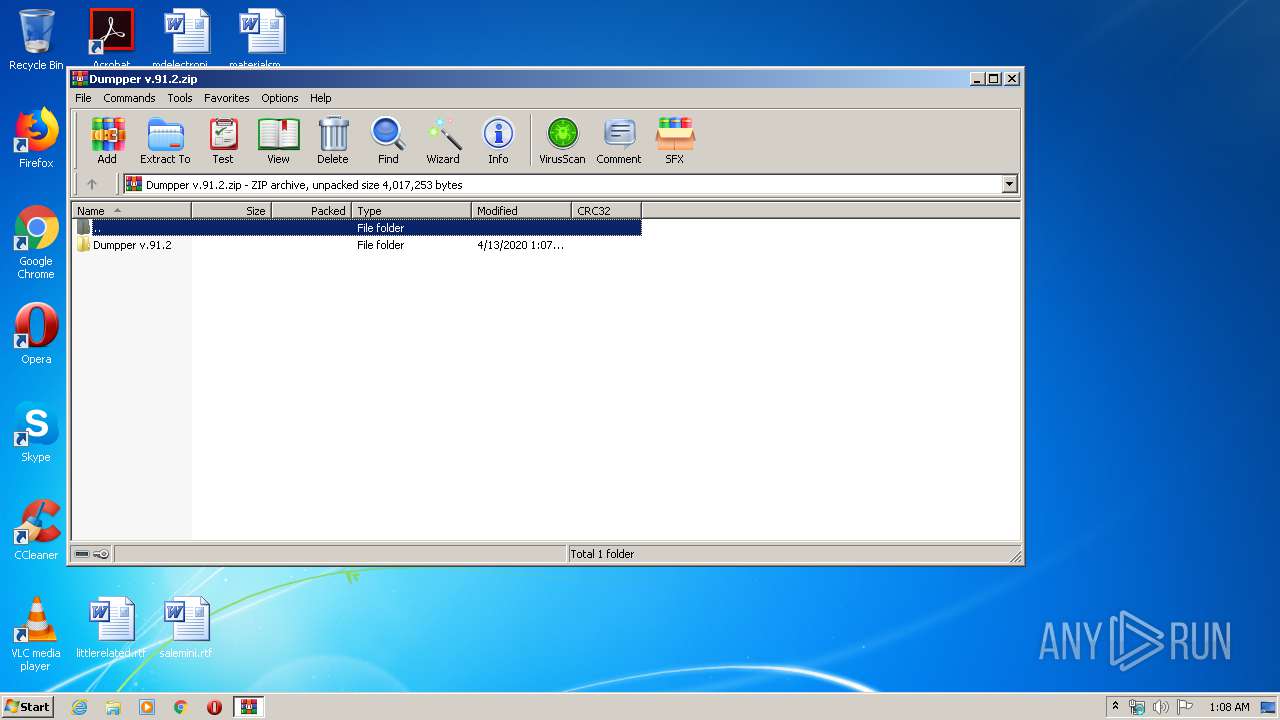
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | 4BD576863F10262FF13C8B06DD175783 |
| SHA1: | 4D44FBBB972DEF898029F377CB6B35B2F6B38F77 |
| SHA256: | 5C762517052975F7173CD165CE9C5C265821AE8EDD02DE0BBE9A60F9D142ED1F |
| SSDEEP: | 49152:575k0lh8uE4AEF+PxNugVH2W8gi/4WQn2Mf:51bJEM+pNuXaM4tn2a |
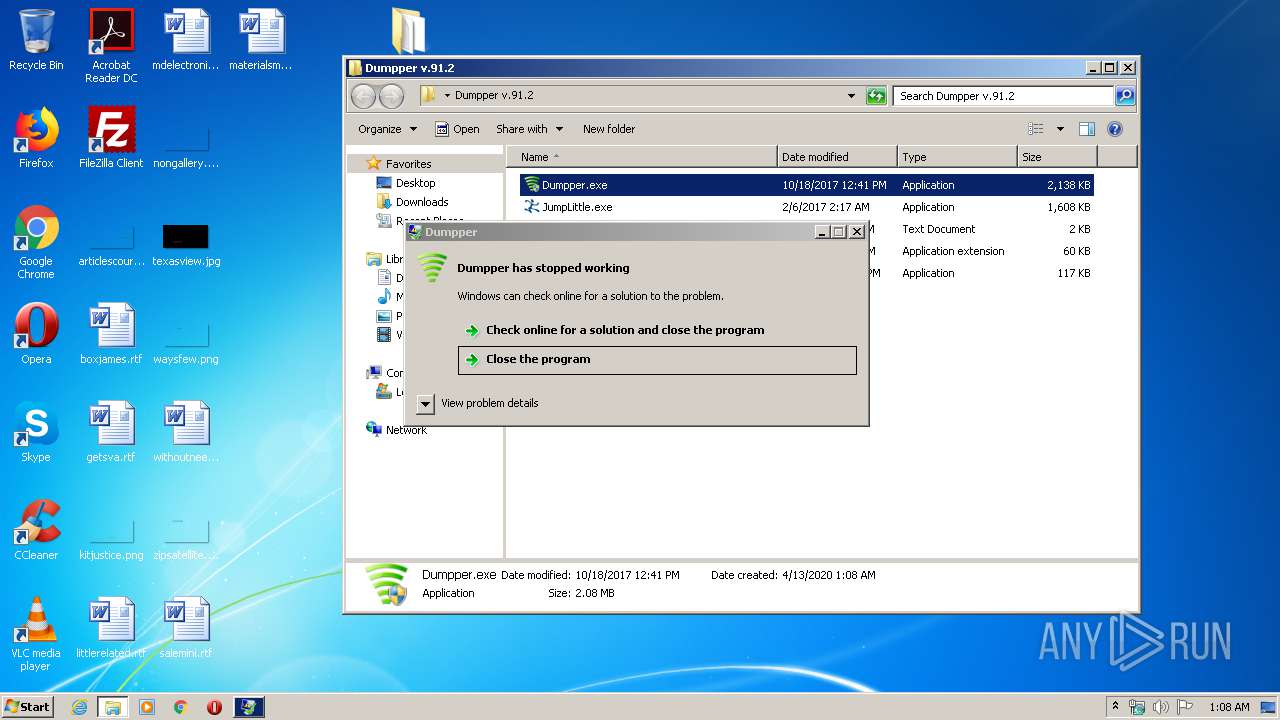
MALICIOUS
Loads dropped or rewritten executable
- SearchProtocolHost.exe (PID: 744)
- explorer.exe (PID: 372)
Application was dropped or rewritten from another process
- WpsWin.exe (PID: 3092)
- WpsWin.exe (PID: 1008)
- JumpLittle.exe (PID: 3528)
- Dumpper.exe (PID: 2900)
- Dumpper.exe (PID: 440)
- Dumpper.exe (PID: 1228)
SUSPICIOUS
Executable content was dropped or overwritten
- WinRAR.exe (PID: 3552)
INFO
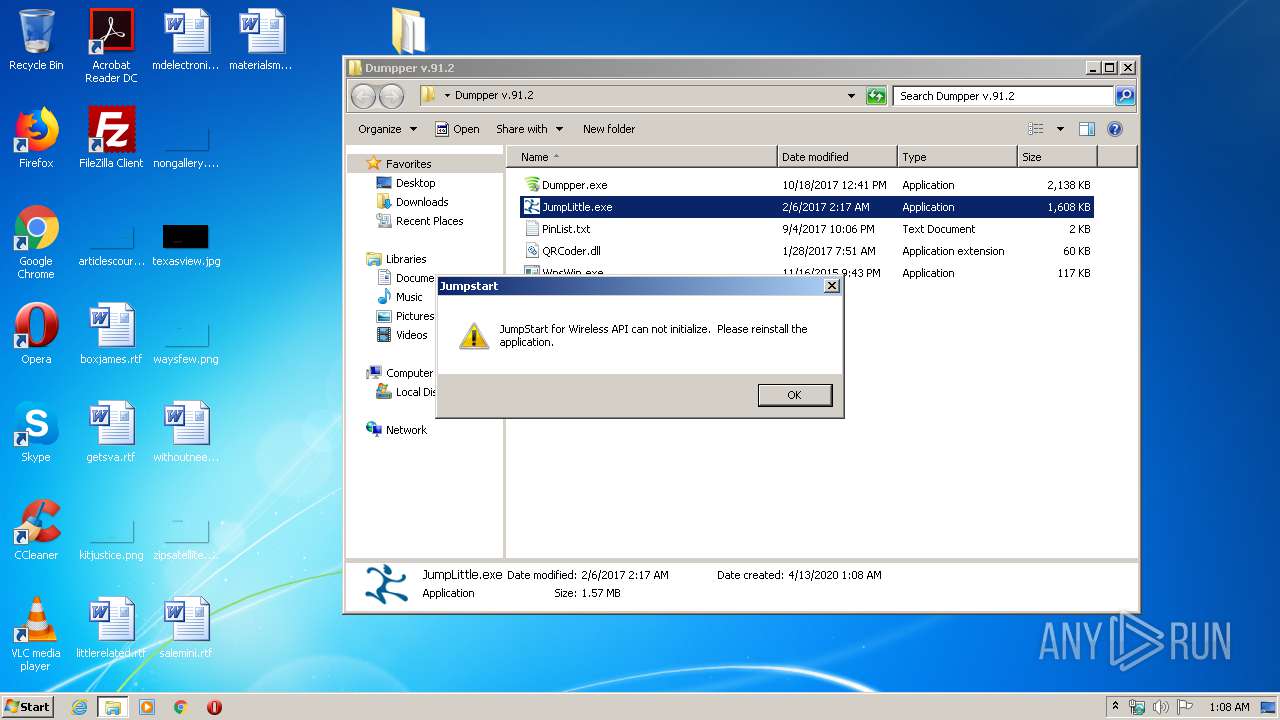
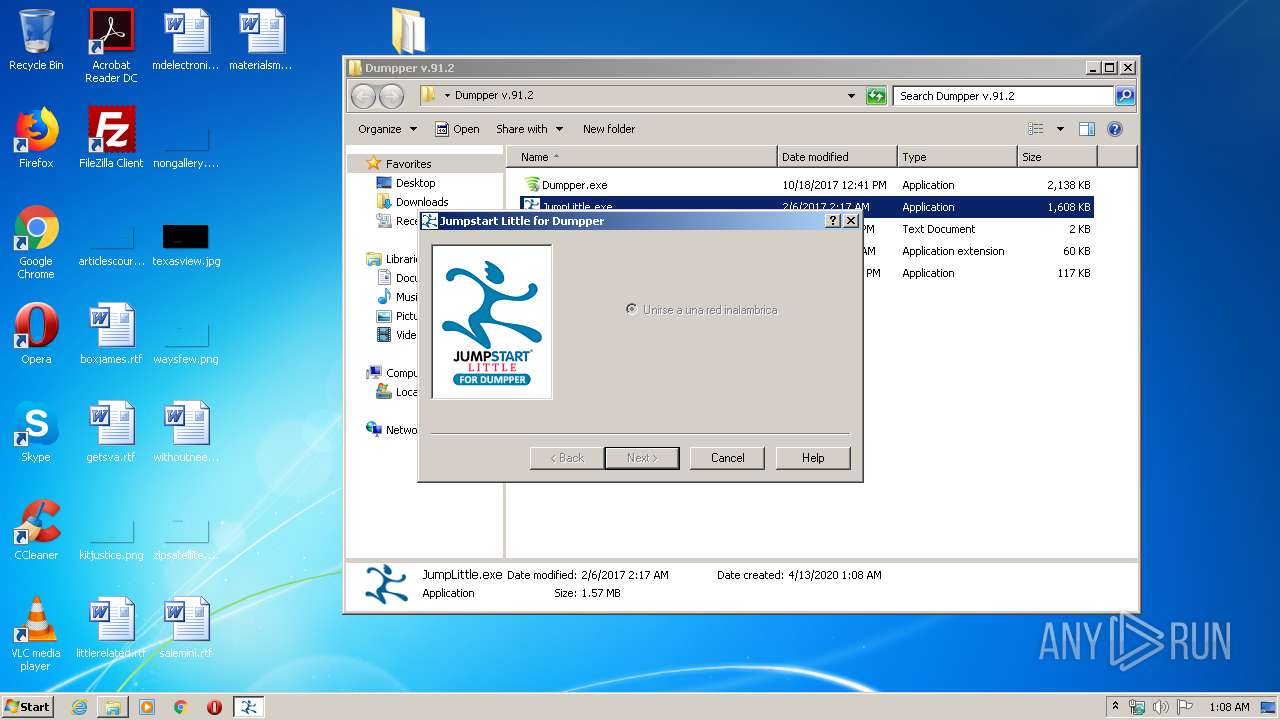
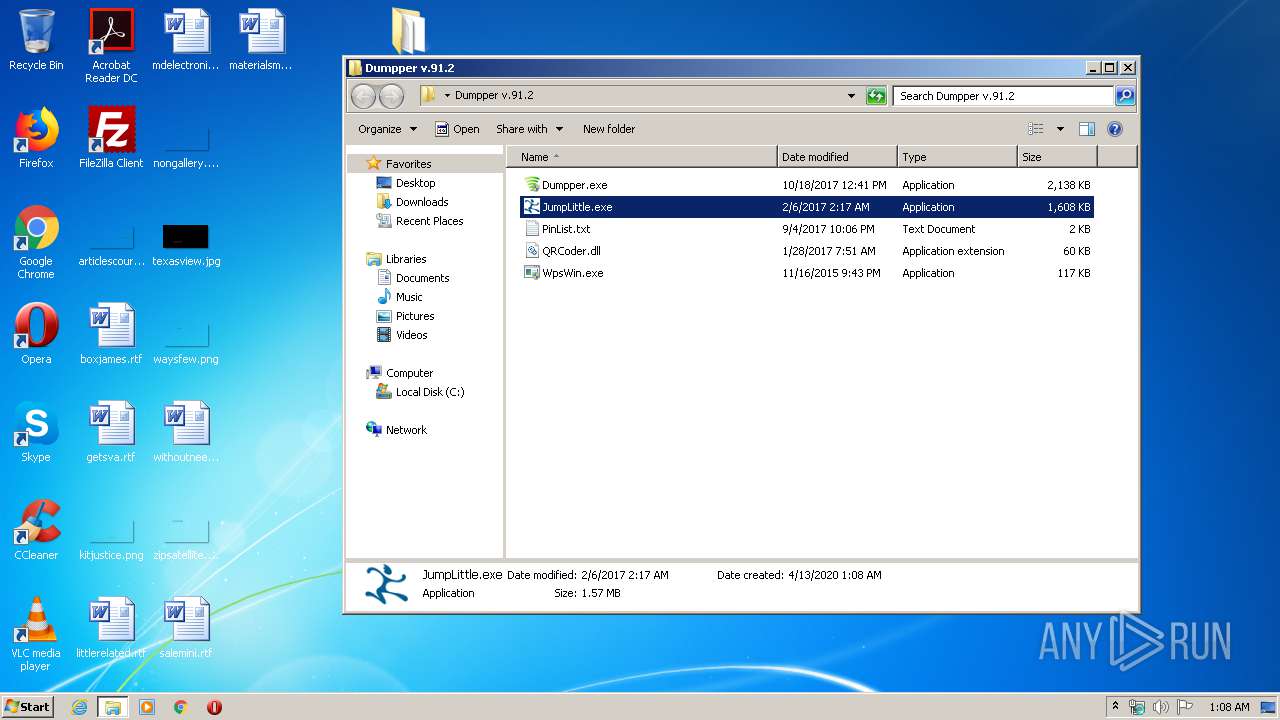
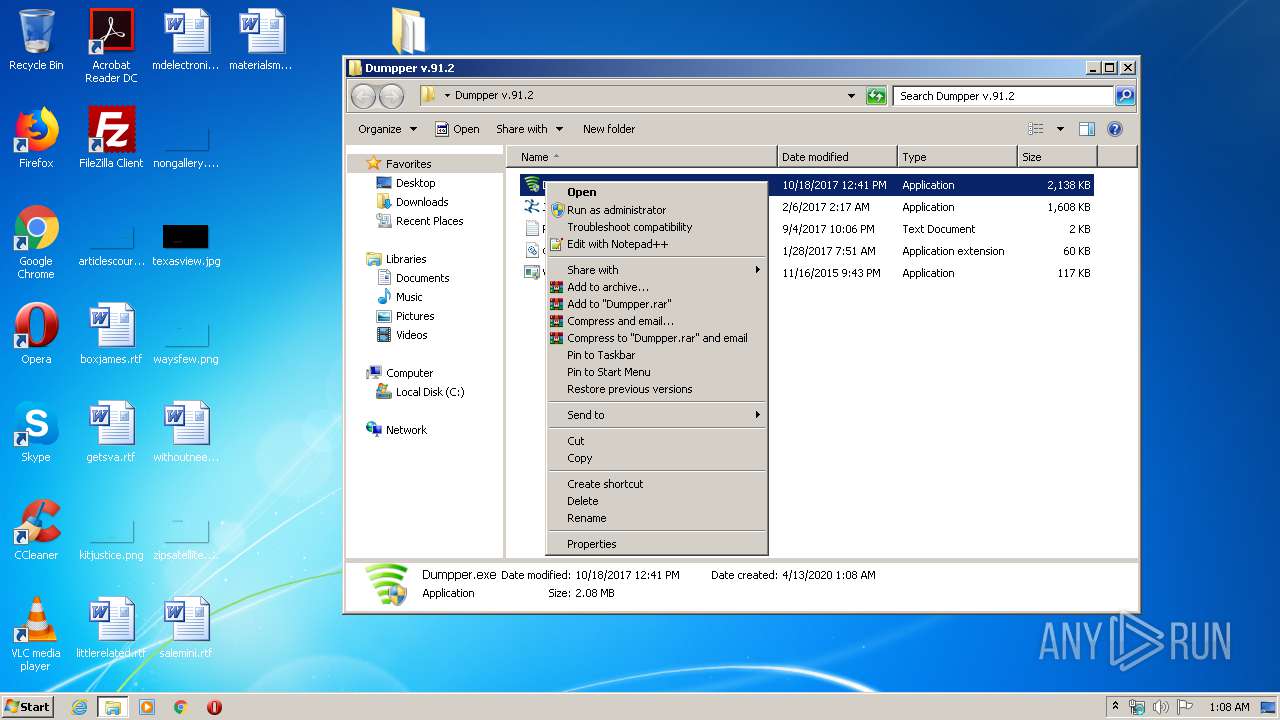
Manual execution by user
- JumpLittle.exe (PID: 3528)
- WpsWin.exe (PID: 1008)
- WpsWin.exe (PID: 3092)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | None |
| ZipModifyDate: | 2020:04:13 03:07:01 |
| ZipCRC: | 0x00000000 |
| ZipCompressedSize: | - |
| ZipUncompressedSize: | - |
| ZipFileName: | Dumpper v.91.2/ |
Total processes
57
Monitored processes
9
Malicious processes
5
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 372 | C:\Windows\Explorer.EXE | C:\Windows\explorer.exe | — | — | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
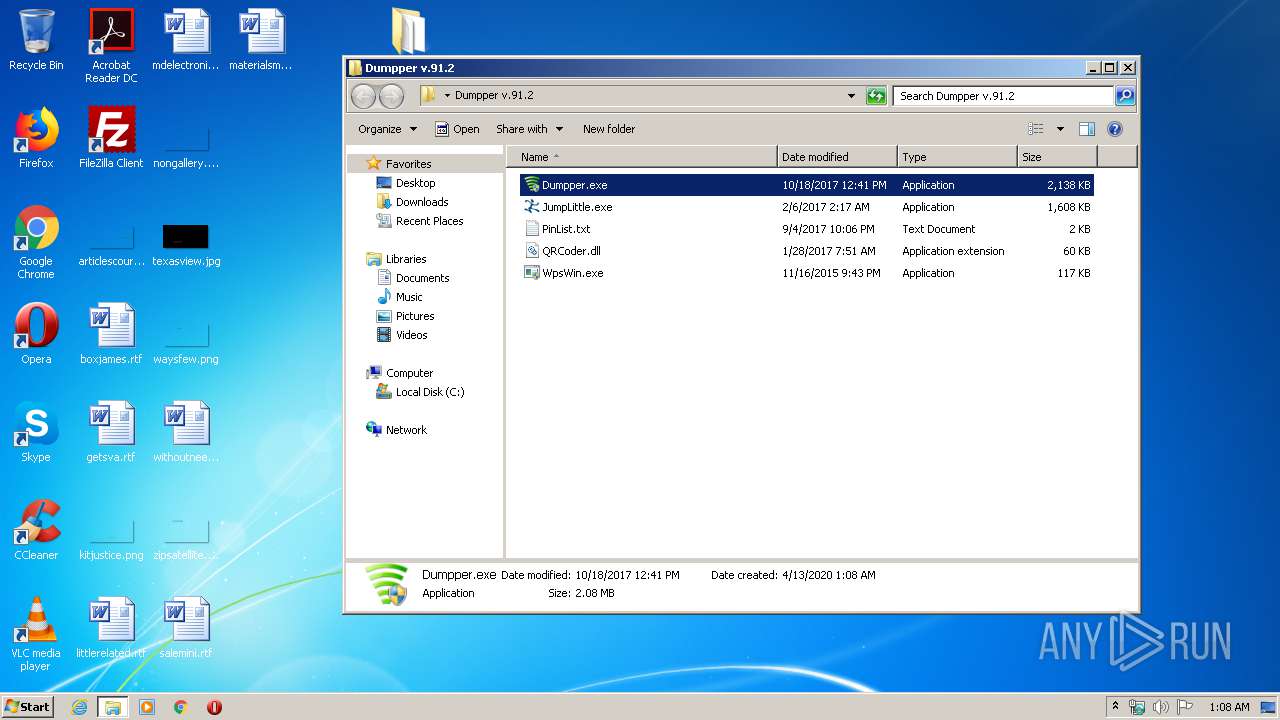
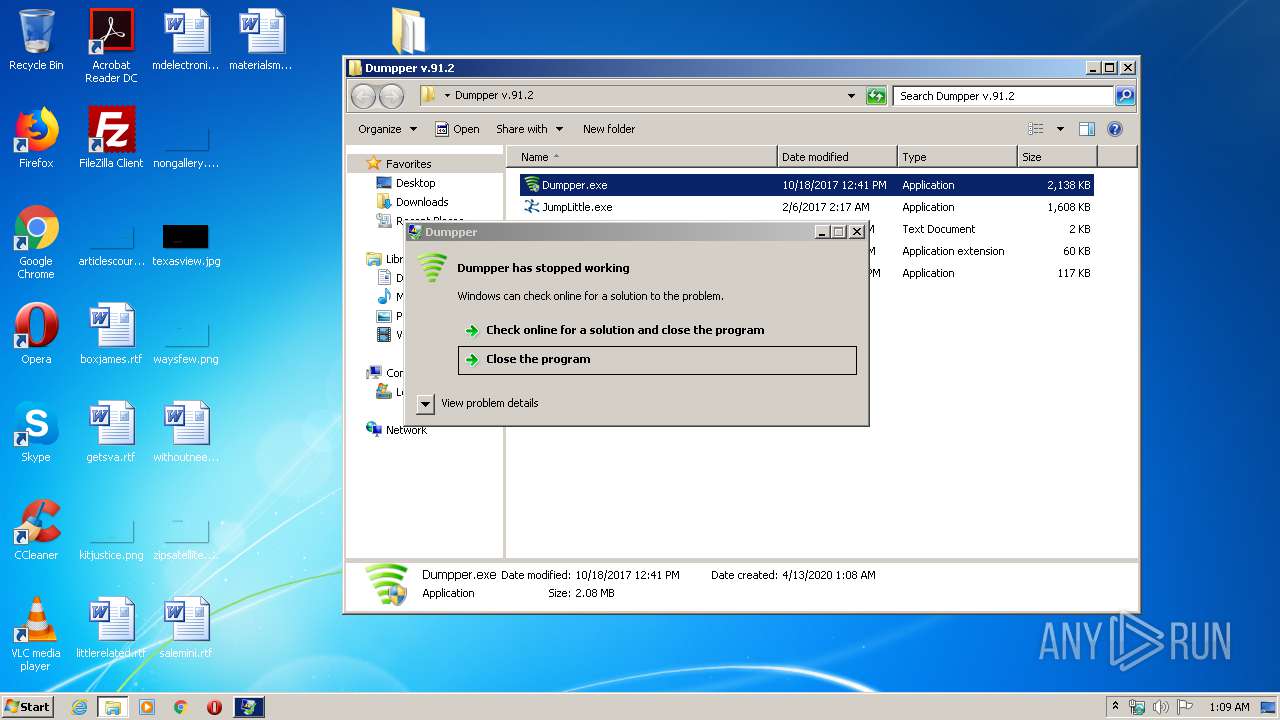
| 440 | "C:\Users\admin\Desktop\Dumpper v.91.2\Dumpper.exe" | C:\Users\admin\Desktop\Dumpper v.91.2\Dumpper.exe | explorer.exe | ||||||||||||
User: admin Company: SkyTech Integrity Level: HIGH Description: Dumpper Exit code: 3762504530 Version: 1.0.0.0 Modules
| |||||||||||||||
| 744 | "C:\Windows\system32\SearchProtocolHost.exe" Global\UsGthrFltPipeMssGthrPipe5_ Global\UsGthrCtrlFltPipeMssGthrPipe5 1 -2147483646 "Software\Microsoft\Windows Search" "Mozilla/4.0 (compatible; MSIE 6.0; Windows NT; MS Search 4.0 Robot)" "C:\ProgramData\Microsoft\Search\Data\Temp\usgthrsvc" "DownLevelDaemon" | C:\Windows\System32\SearchProtocolHost.exe | — | SearchIndexer.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft Windows Search Protocol Host Exit code: 0 Version: 7.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1008 | "C:\Users\admin\Desktop\Dumpper v.91.2\WpsWin.exe" | C:\Users\admin\Desktop\Dumpper v.91.2\WpsWin.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 1228 | "C:\Users\admin\Desktop\Dumpper v.91.2\Dumpper.exe" | C:\Users\admin\Desktop\Dumpper v.91.2\Dumpper.exe | explorer.exe | ||||||||||||
User: admin Company: SkyTech Integrity Level: HIGH Description: Dumpper Exit code: 3762504530 Version: 1.0.0.0 Modules
| |||||||||||||||
| 2900 | "C:\Users\admin\Desktop\Dumpper v.91.2\Dumpper.exe" | C:\Users\admin\Desktop\Dumpper v.91.2\Dumpper.exe | — | explorer.exe | |||||||||||
User: admin Company: SkyTech Integrity Level: MEDIUM Description: Dumpper Exit code: 3221226540 Version: 1.0.0.0 Modules
| |||||||||||||||
| 3092 | "C:\Users\admin\Desktop\Dumpper v.91.2\WpsWin.exe" | C:\Users\admin\Desktop\Dumpper v.91.2\WpsWin.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 3528 | "C:\Users\admin\Desktop\Dumpper v.91.2\JumpLittle.exe" | C:\Users\admin\Desktop\Dumpper v.91.2\JumpLittle.exe | — | explorer.exe | |||||||||||
User: admin Company: Atheros Communications, Inc. Integrity Level: MEDIUM Description: Jumpstart for Wireless Exit code: 0 Version: 2.1.0.18 Modules
| |||||||||||||||
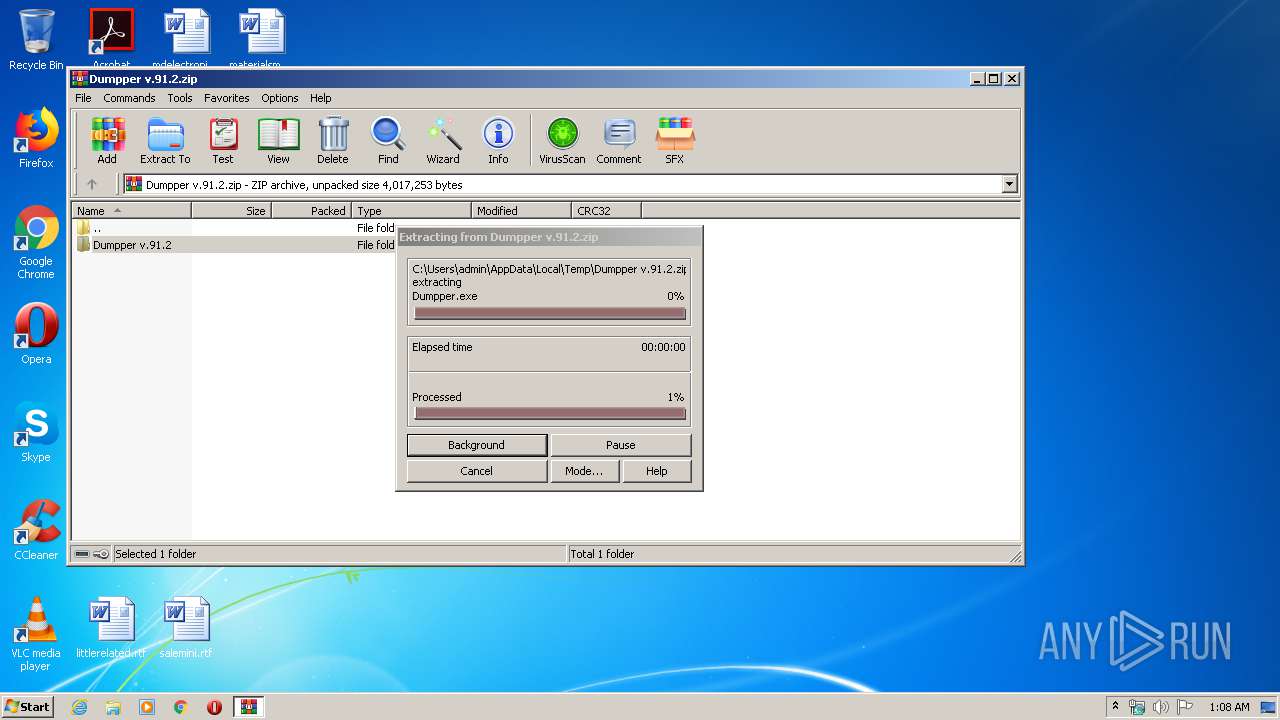
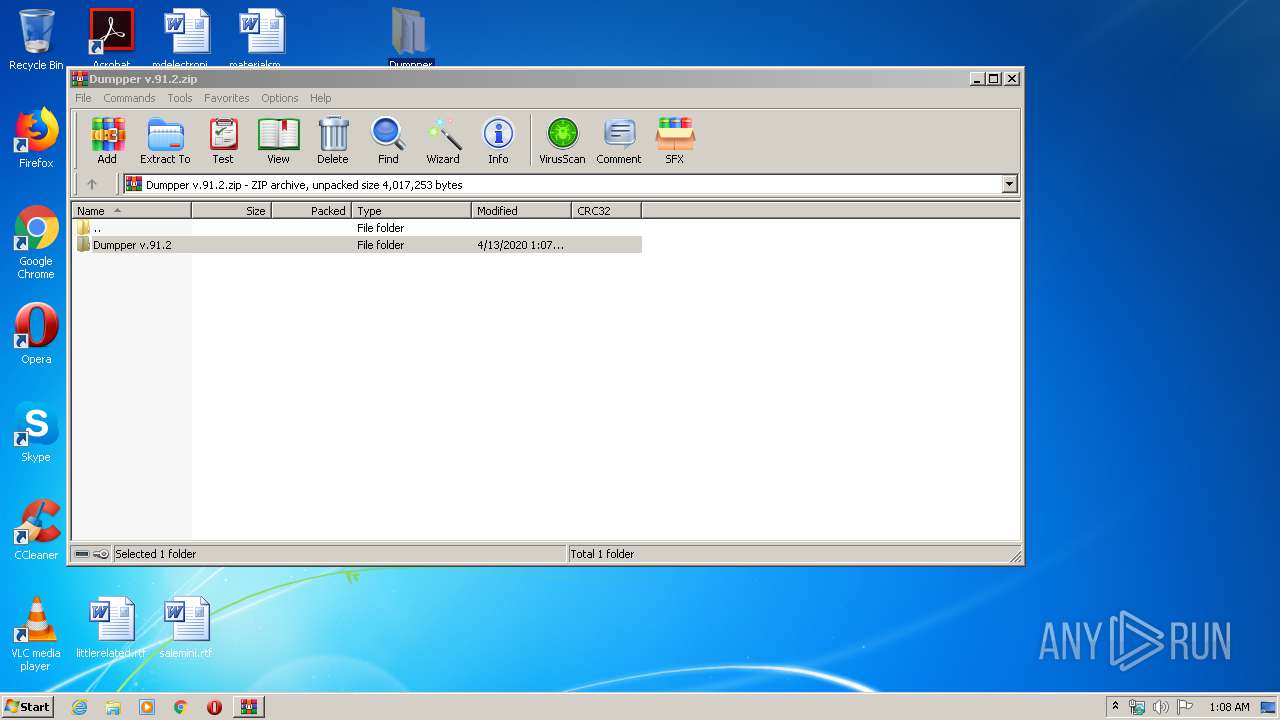
| 3552 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\Dumpper v.91.2.zip" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
Total events
1 984
Read events
1 872
Write events
112
Delete events
0
Modification events
| (PID) Process: | (372) explorer.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3552) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (3552) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (3552) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3552) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\Dumpper v.91.2.zip | |||
| (PID) Process: | (3552) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3552) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3552) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (3552) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (372) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.zip\OpenWithList |
| Operation: | write | Name: | a |
Value: WinRAR.exe | |||
Executable files
4
Suspicious files
0
Text files
1
Unknown types
0
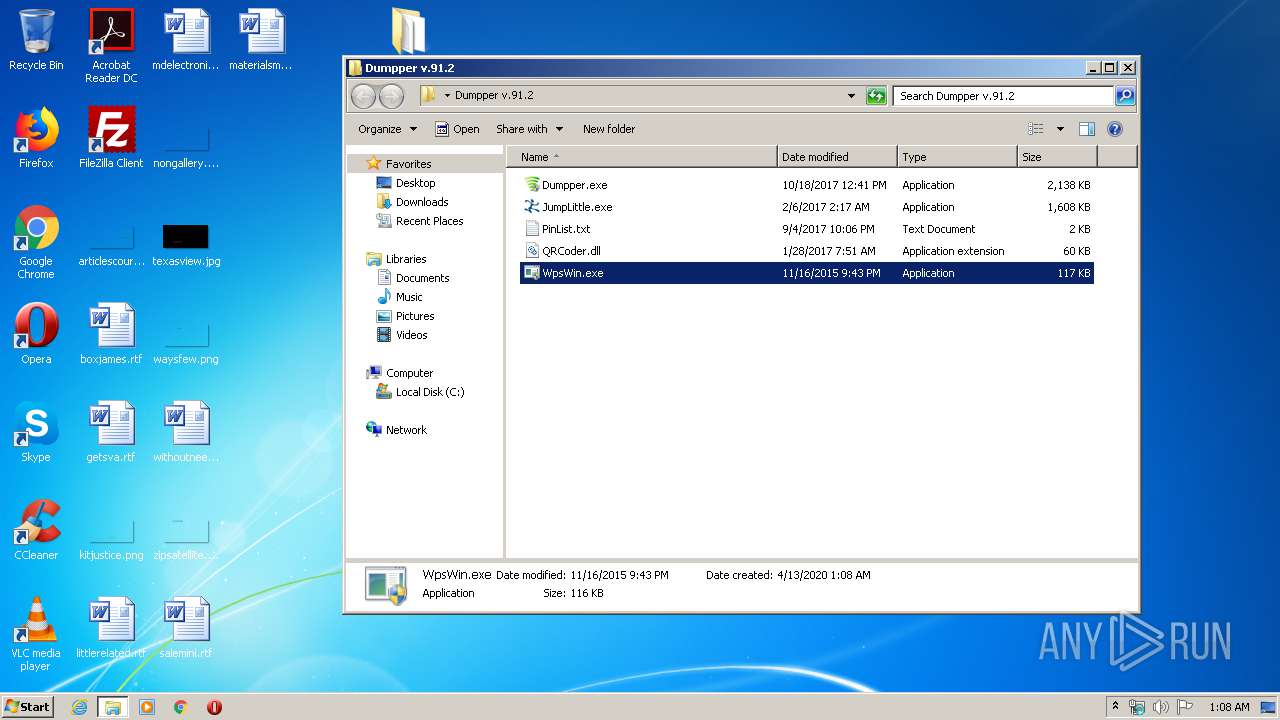
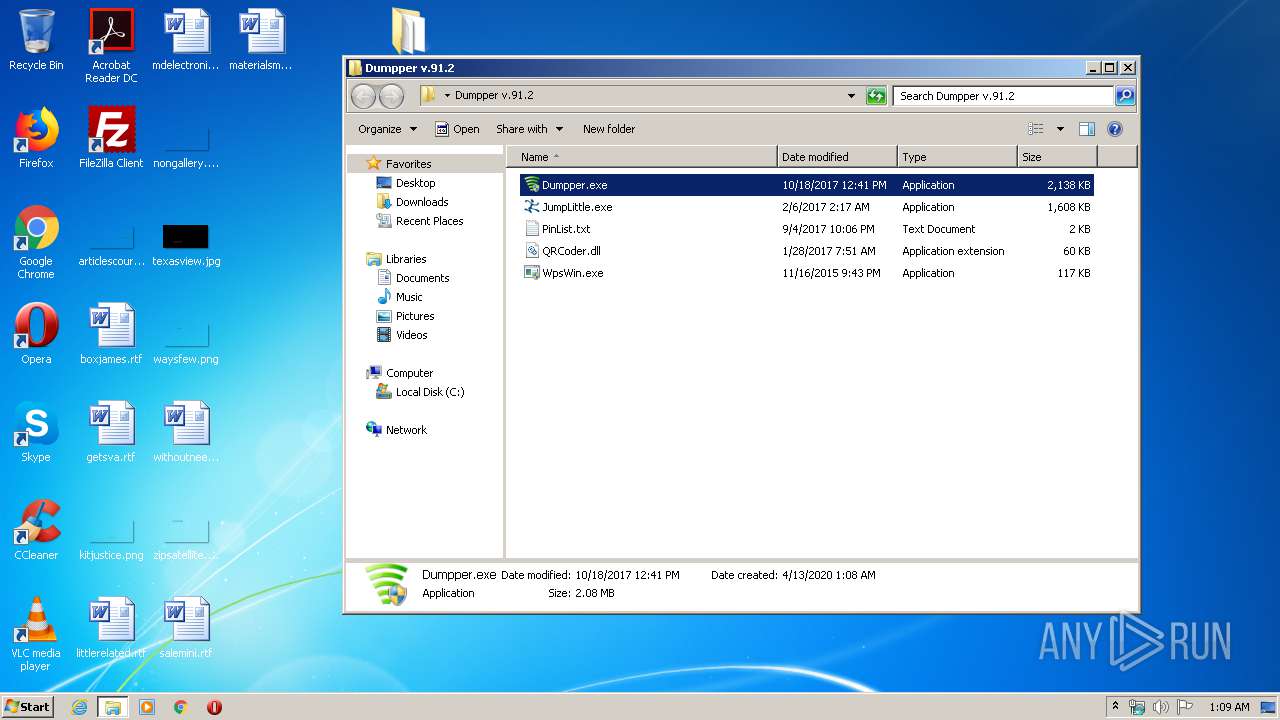
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 372 | explorer.exe | C:\Users\admin\Desktop\Dumpper v.91.2 | — | |
MD5:— | SHA256:— | |||
| 3552 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3552.33310\Dumpper v.91.2\PinList.txt | text | |
MD5:DE26AD8D80DB7D2DAA87823C21292D4E | SHA256:92764E46DC115DB3D7DE64A053B1AB98DF03CAB9EF7F0C049CD745B618E924BF | |||
| 3552 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3552.33310\Dumpper v.91.2\Dumpper.exe | executable | |
MD5:9B8EB74FFE2C1C4EDC4AEEDCBA2B9612 | SHA256:01F5AFA3C3A9AA9D4AE51E3EEE5850A084AE516D2DCB84A0579C4B07FEE37F83 | |||
| 3552 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3552.33310\Dumpper v.91.2\QRCoder.dll | executable | |
MD5:2D3DD942212A37AA55D5CBEC32BBCD76 | SHA256:D0A13DB264406B02A4529BC017FE72FD91DDA5D639DA3C3C66E28EE2B489C066 | |||
| 3552 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3552.33310\Dumpper v.91.2\WpsWin.exe | executable | |
MD5:D474EAEB9542D2BE2AC1853936BB774B | SHA256:93229A919E830257DC87BFD9EC11E5E1DDFBF18425484E4450DB7329E6D0C1D8 | |||
| 3552 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3552.33310\Dumpper v.91.2\JumpLittle.exe | executable | |
MD5:1E0FE724AC8EEE75461AA814C480705D | SHA256:177023C40080306164E32221C019B31DD91DF3F94DCE19A2416A74AE9061917F | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report