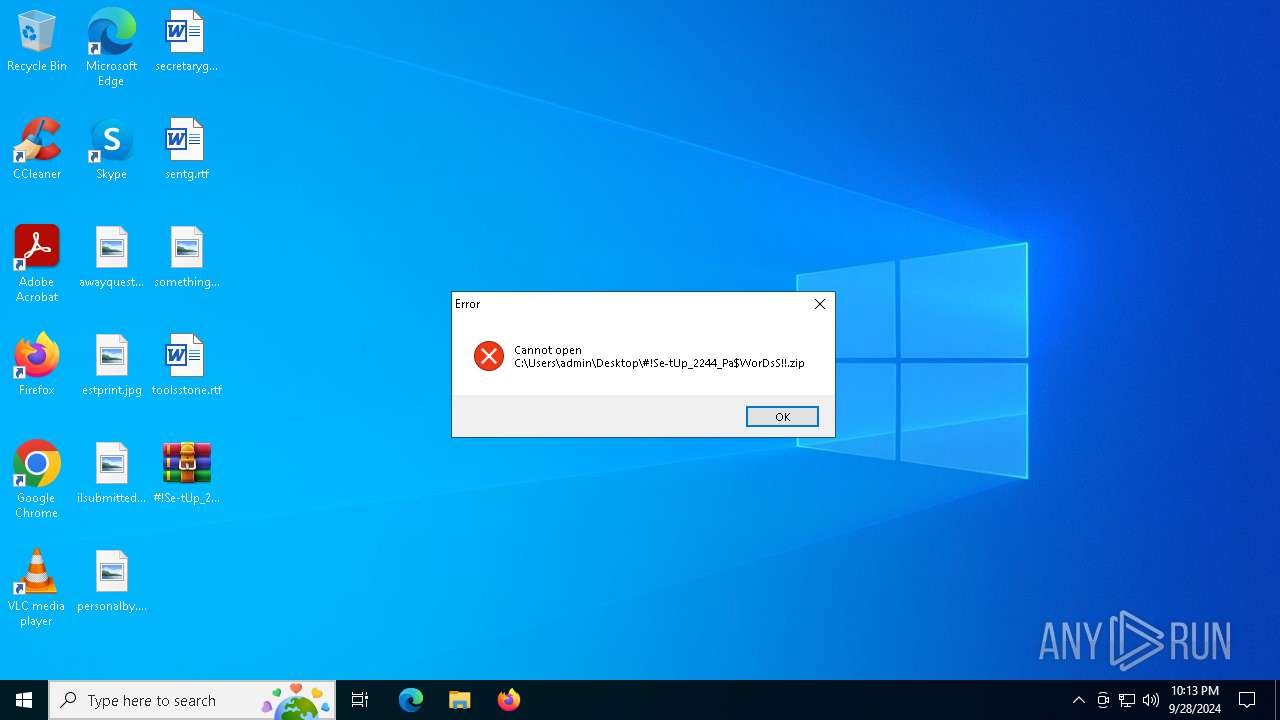
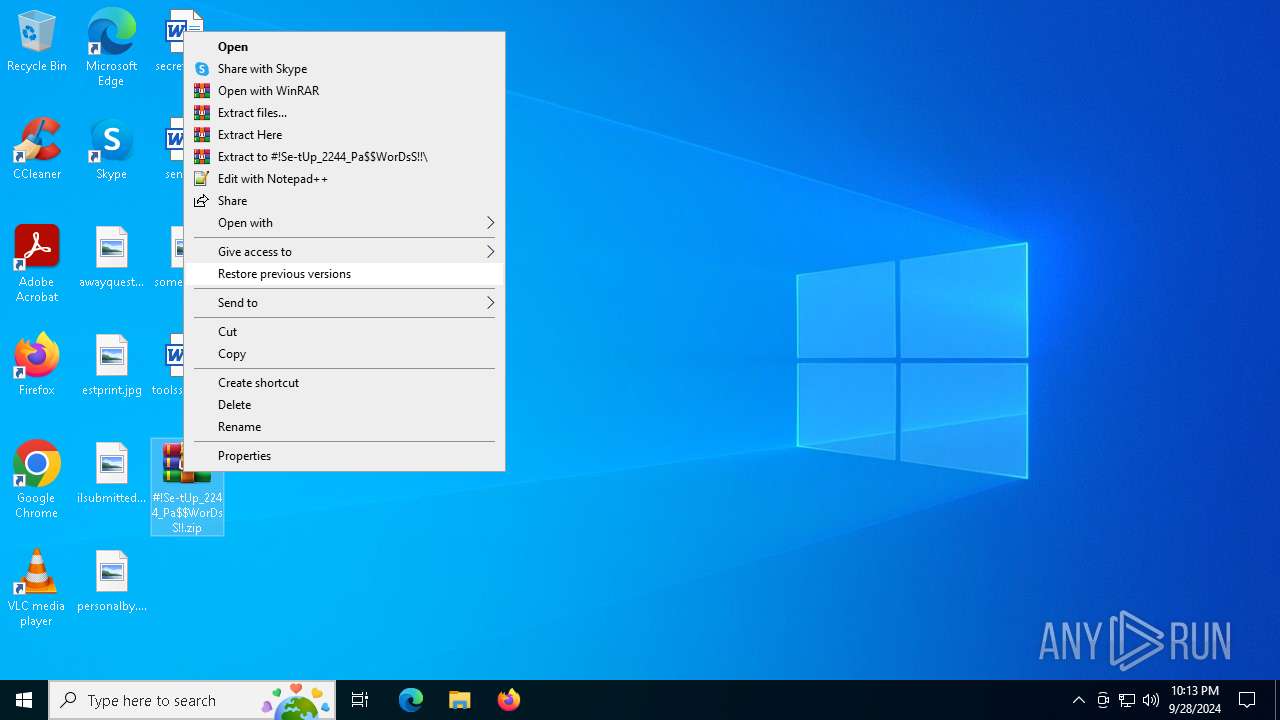
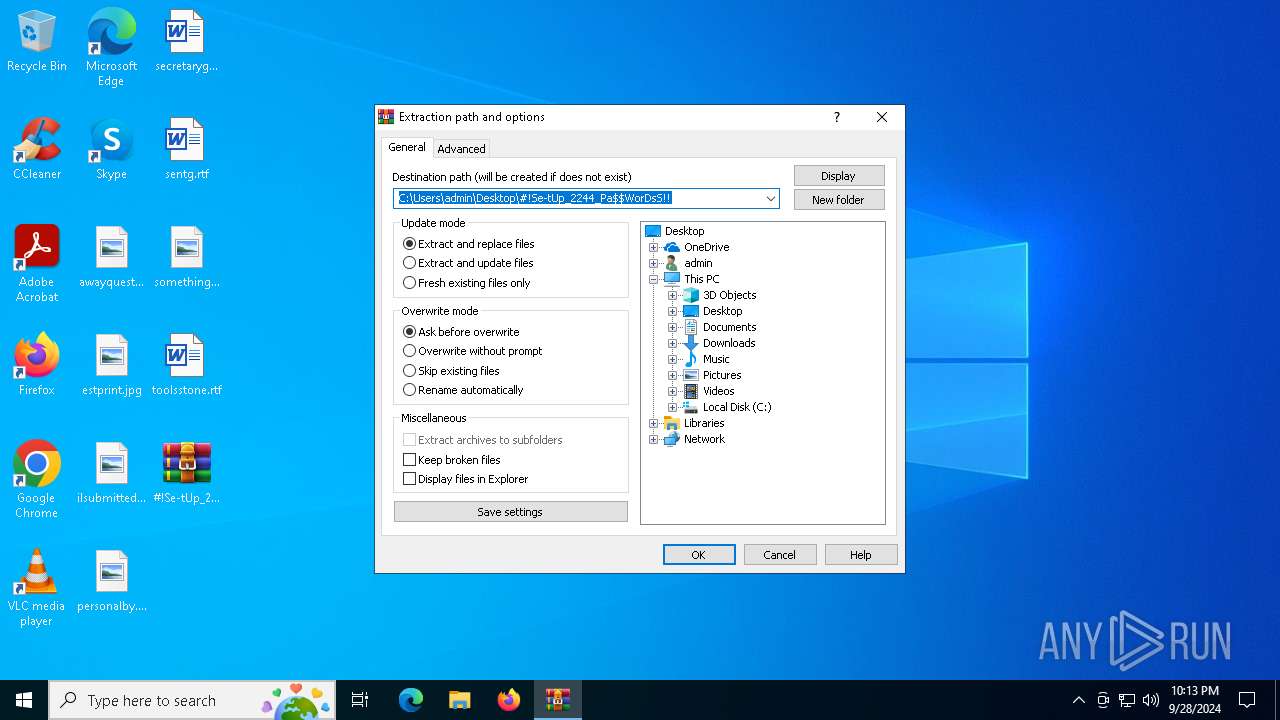
| File name: | #!Se-tUp_2244_Pa$WorDsS!!.zip |
| Full analysis: | https://app.any.run/tasks/d1c8e5b0-75cd-4d65-bc8d-1511154739ab |
| Verdict: | Malicious activity |
| Analysis date: | September 28, 2024, 22:13:12 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract, compression method=deflate |
| MD5: | ABBDEB9F888A5596668053A4B0C0065A |
| SHA1: | 5B4F41A9F230B0A5B0E18AF7BECD60417B2B41D9 |
| SHA256: | 5C5F84C9EEEC9EACBD491613708FBD3966A0B54FE96779FE3A90E5F2C5E4BAD3 |
| SSDEEP: | 98304:4bKfMgcEHoGwZH89qqFjU/KQ8Z2OVt5pGeevMF9Q1tGoYfS2TS1fcAvMj6JPFtPF:fsVuDpjplCiC |
MALICIOUS
Changes powershell execution policy (Bypass)
- SearchIndexer.exe (PID: 1636)
Bypass execution policy to execute commands
- powershell.exe (PID: 4780)
SUSPICIOUS
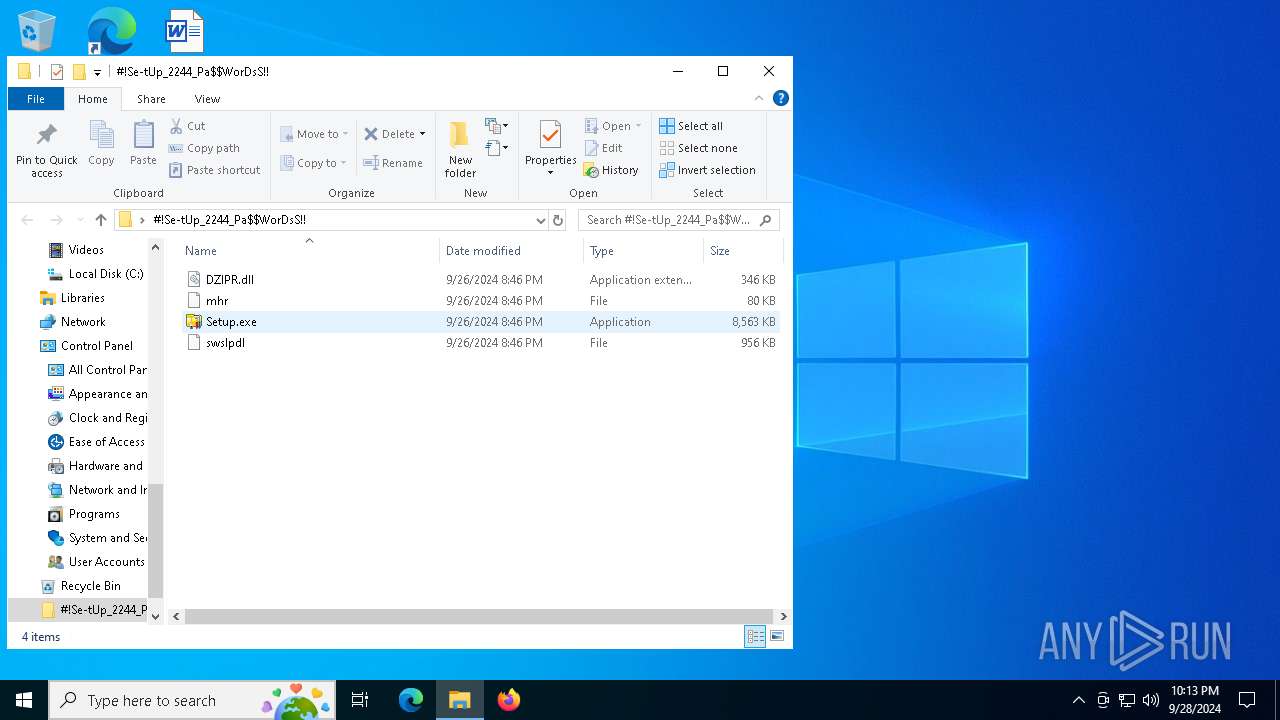
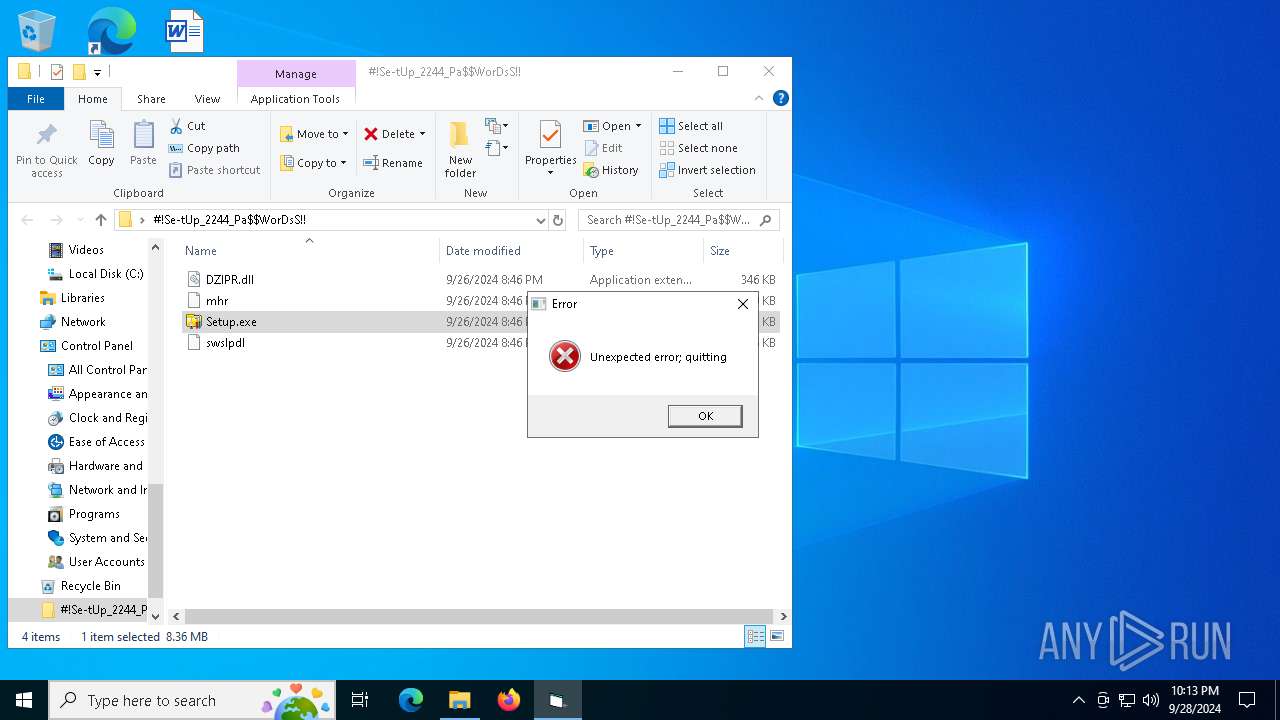
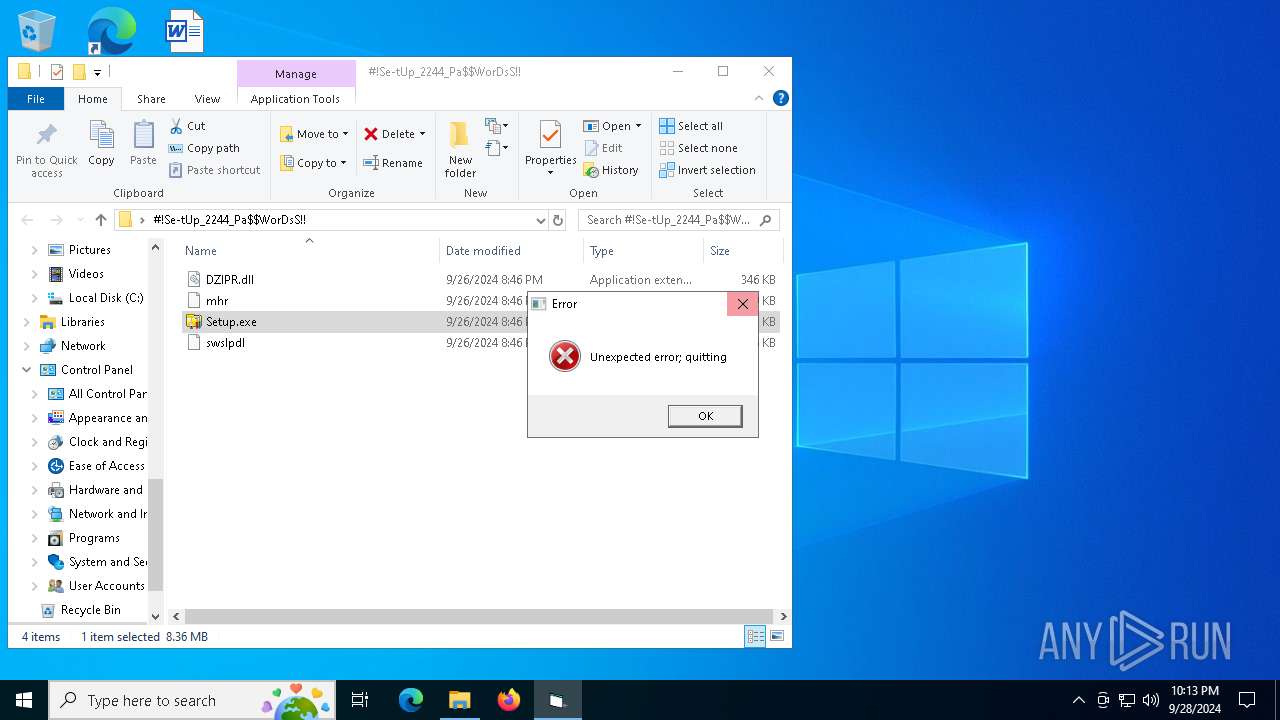
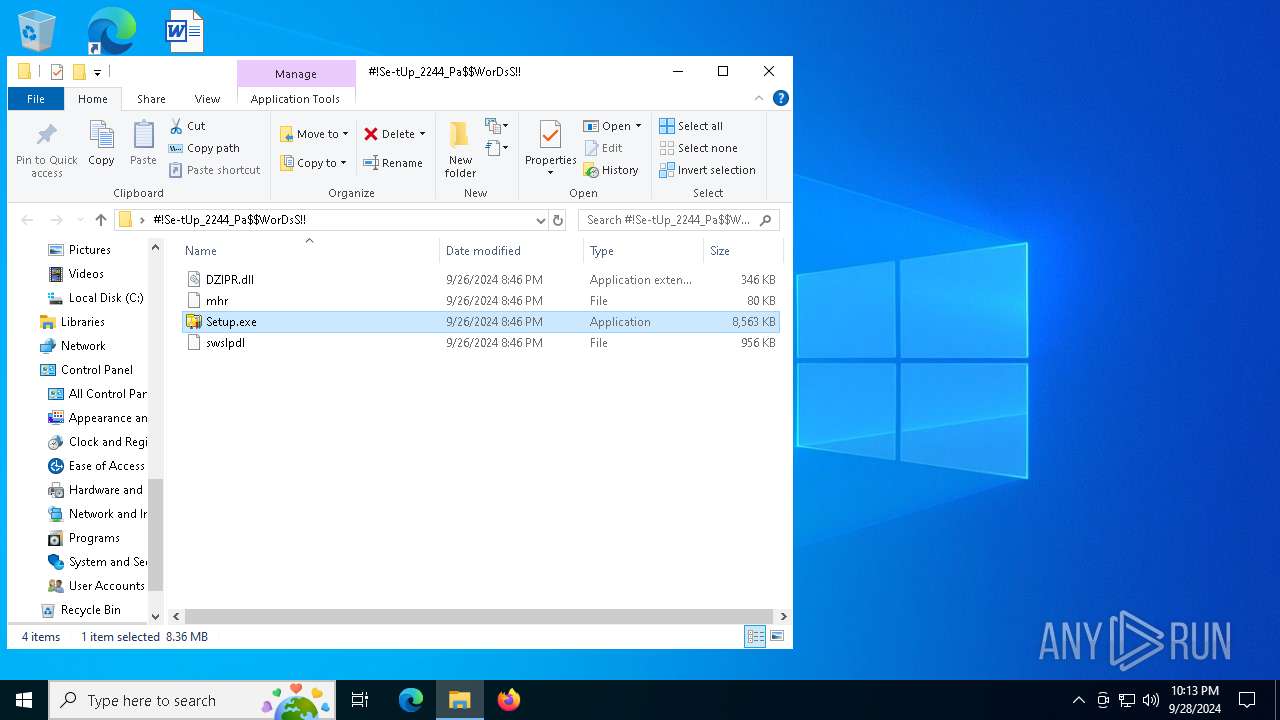
Executable content was dropped or overwritten
- Setup.exe (PID: 5880)
Starts application with an unusual extension
- Setup.exe (PID: 5880)
The process executes Powershell scripts
- SearchIndexer.exe (PID: 1636)
Starts POWERSHELL.EXE for commands execution
- SearchIndexer.exe (PID: 1636)
INFO
Executable content was dropped or overwritten
- WinRAR.exe (PID: 7016)
Manual execution by a user
- WinRAR.exe (PID: 7016)
- Setup.exe (PID: 5880)
The process uses the downloaded file
- WinRAR.exe (PID: 7016)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2024:09:26 22:46:50 |
| ZipCRC: | 0x930007c2 |
| ZipCompressedSize: | 932152 |
| ZipUncompressedSize: | 978542 |
| ZipFileName: | swslpdl |
Total processes
141
Monitored processes
12
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 304 | C:\WINDOWS\SysWOW64\more.com | C:\Windows\SysWOW64\more.com | — | Setup.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: More Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 376 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\Desktop\#!Se-tUp_2244_Pa$WorDsS!!.zip | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 1 Version: 5.91.0 Modules
| |||||||||||||||
| 1636 | C:\WINDOWS\SysWOW64\SearchIndexer.exe | C:\Windows\SysWOW64\SearchIndexer.exe | more.com | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Windows Search Indexer Exit code: 0 Version: 7.0.19041.3758 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4168 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | more.com | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4780 | powershell -exec bypass -f "C:\Users\admin\AppData\Local\Temp\PESD6OWWPQF7Y9GZSFL88BZQD.ps1" | C:\Windows\SysWOW64\WindowsPowerShell\v1.0\powershell.exe | — | SearchIndexer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5060 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5300 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5656 | "C:\WINDOWS\System32\SLUI.exe" RuleId=3482d82e-ca2c-4e1f-8864-da0267b484b2;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=4de7cb65-cdf1-4de9-8ae8-e3cce27b9f2c;NotificationInterval=1440;Trigger=TimerEvent | C:\Windows\System32\slui.exe | SppExtComObj.Exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5676 | C:\Users\admin\Soho\RODGLSEYZFWSFMIJCZDKVM\StrCmp.exe | C:\Users\admin\Soho\RODGLSEYZFWSFMIJCZDKVM\StrCmp.exe | — | Setup.exe | |||||||||||
User: admin Company: aaa Integrity Level: MEDIUM Exit code: 0 Version: 1.00 Modules
| |||||||||||||||
| 5880 | "C:\Users\admin\Desktop\#!Se-tUp_2244_Pa$WorDsS!!\Setup.exe" | C:\Users\admin\Desktop\#!Se-tUp_2244_Pa$WorDsS!!\Setup.exe | explorer.exe | ||||||||||||
User: admin Company: DataNumen, Inc. Integrity Level: MEDIUM Exit code: 1 Version: 4.0.0.0 Modules
| |||||||||||||||
Total events
11 203
Read events
11 175
Write events
15
Delete events
13
Modification events
| (PID) Process: | (376) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (376) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (376) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (376) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (376) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\General\Toolbar\Layout |
| Operation: | write | Name: | Band76_0 |
Value: 4C000000730100000402000000000000F0F0F00000000000000000000000000000000000000000009803140000000000000000003B000000B402000000000000000000000000000001000000 | |||
| (PID) Process: | (376) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\General\Toolbar\Layout |
| Operation: | write | Name: | Band76_1 |
Value: 4C000000730100000500000000000000F0F0F0000000000000000000000000000000000000000000460315000000000000000000180000002A00000000000000000000000000000002000000 | |||
| (PID) Process: | (376) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\General\Toolbar\Layout |
| Operation: | write | Name: | Band76_2 |
Value: 4C000000730100000400000000000000F0F0F0000000000000000000000000000000000000000000700215000000000000000000180000006400000000000000000000000000000003000000 | |||
| (PID) Process: | (7016) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | delete value | Name: | 15 |
Value: | |||
| (PID) Process: | (7016) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | delete value | Name: | 14 |
Value: | |||
| (PID) Process: | (7016) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | delete value | Name: | 13 |
Value: | |||
Executable files
4
Suspicious files
6
Text files
7
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 304 | more.com | C:\Users\admin\AppData\Local\Temp\ialabcsektcfwr | — | |
MD5:— | SHA256:— | |||
| 5880 | Setup.exe | C:\Users\admin\Soho\mhr | binary | |
MD5:5902B494BB3B4FB3DFFAB3B2EA6DA8E5 | SHA256:EDC8DC9B1F50D58DBBABA0A80F2017BA1D5D1CAF376383053D38F5837E71E6C1 | |||
| 4780 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_bvagzcip.uok.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 5880 | Setup.exe | C:\Users\admin\Soho\RODGLSEYZFWSFMIJCZDKVM\StrCmp.exe | executable | |
MD5:916D7425A559AAA77F640710A65F9182 | SHA256:118DE01FB498E81EAB4ADE980A621AF43B52265A9FCBAE5DEDC492CDF8889F35 | |||
| 5880 | Setup.exe | C:\Users\admin\Soho\swslpdl | binary | |
MD5:769FED553DC3E9B74D32C894671B050E | SHA256:5DDA61C9D63E7A9BE646E0A7CD378127F3397007245EAF6CC783F90C010EFDD3 | |||
| 7016 | WinRAR.exe | C:\Users\admin\Desktop\#!Se-tUp_2244_Pa$WorDsS!!\Setup.exe | executable | |
MD5:EC9CE1D67F98072281015C7726FBA245 | SHA256:9AB4145D5525AE741B80F4E66F505ABBA59ADCBE01868DFEF84FBE4450634CC1 | |||
| 7016 | WinRAR.exe | C:\Users\admin\Desktop\#!Se-tUp_2244_Pa$WorDsS!!\DZIPR.dll | executable | |
MD5:C75E7F820B6E71FBA9EF5DA72BF511B0 | SHA256:A0AE4D9174B539EDE280CC596FC88C14E475B44D5FB477444AB123456EAB047F | |||
| 5880 | Setup.exe | C:\Users\admin\Soho\DZIPR.dll | executable | |
MD5:C75E7F820B6E71FBA9EF5DA72BF511B0 | SHA256:A0AE4D9174B539EDE280CC596FC88C14E475B44D5FB477444AB123456EAB047F | |||
| 4780 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_xaukeivt.aeu.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 1636 | SearchIndexer.exe | C:\Users\admin\AppData\Local\Temp\PESD6OWWPQF7Y9GZSFL88BZQD.ps1 | text | |
MD5:FD8EDC156E282155F7D2FBA4663530A3 | SHA256:F6D16DB3E818DC771911891F60A40C967676690F90F7EA03F7A2C6172966C881 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
52
DNS requests
22
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6716 | svchost.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
3860 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
240 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
5240 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
5240 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1932 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
2120 | MoUsoCoreWorker.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6716 | svchost.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
3888 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1932 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
240 | svchost.exe | 20.190.160.17:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
240 | svchost.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
arc.msn.com |
| whitelisted |
fd.api.iris.microsoft.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2256 | svchost.exe | Misc activity | ET INFO Pastebin Service Domain in DNS Lookup (rentry .co) |
1636 | SearchIndexer.exe | Misc activity | ET INFO Observed Pastebin Service Domain (rentry .co in TLS SNI) |