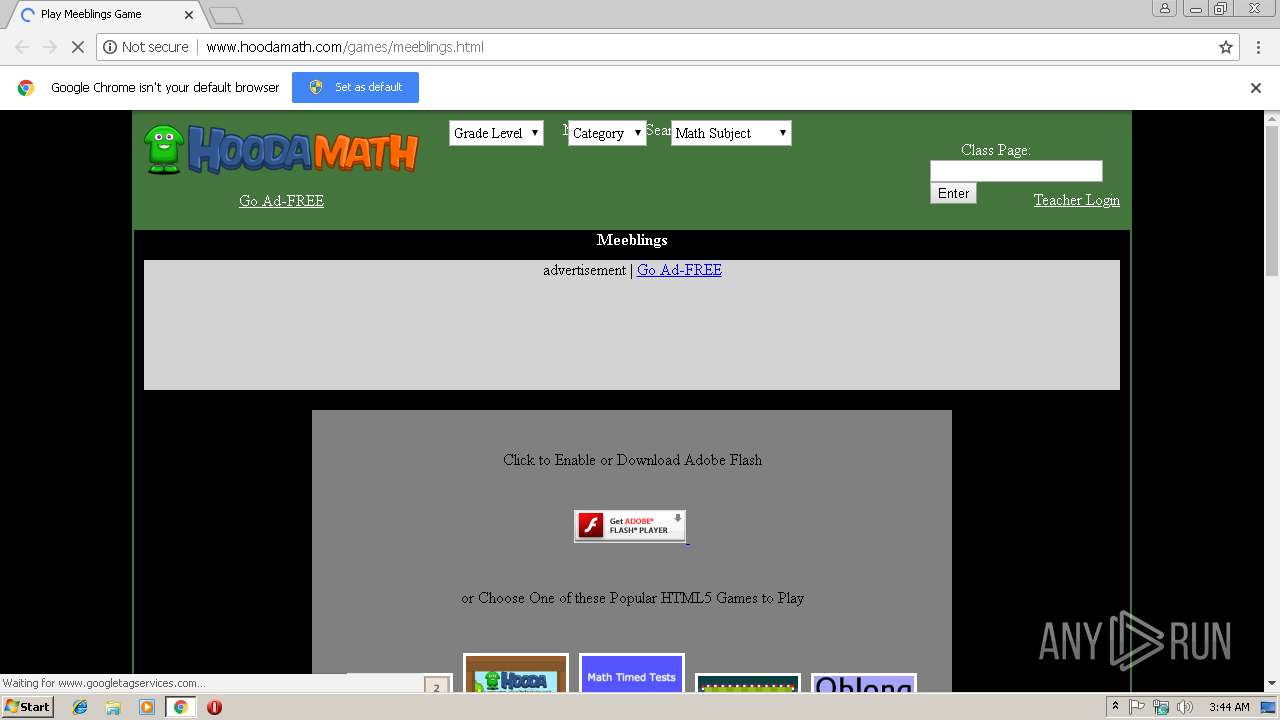
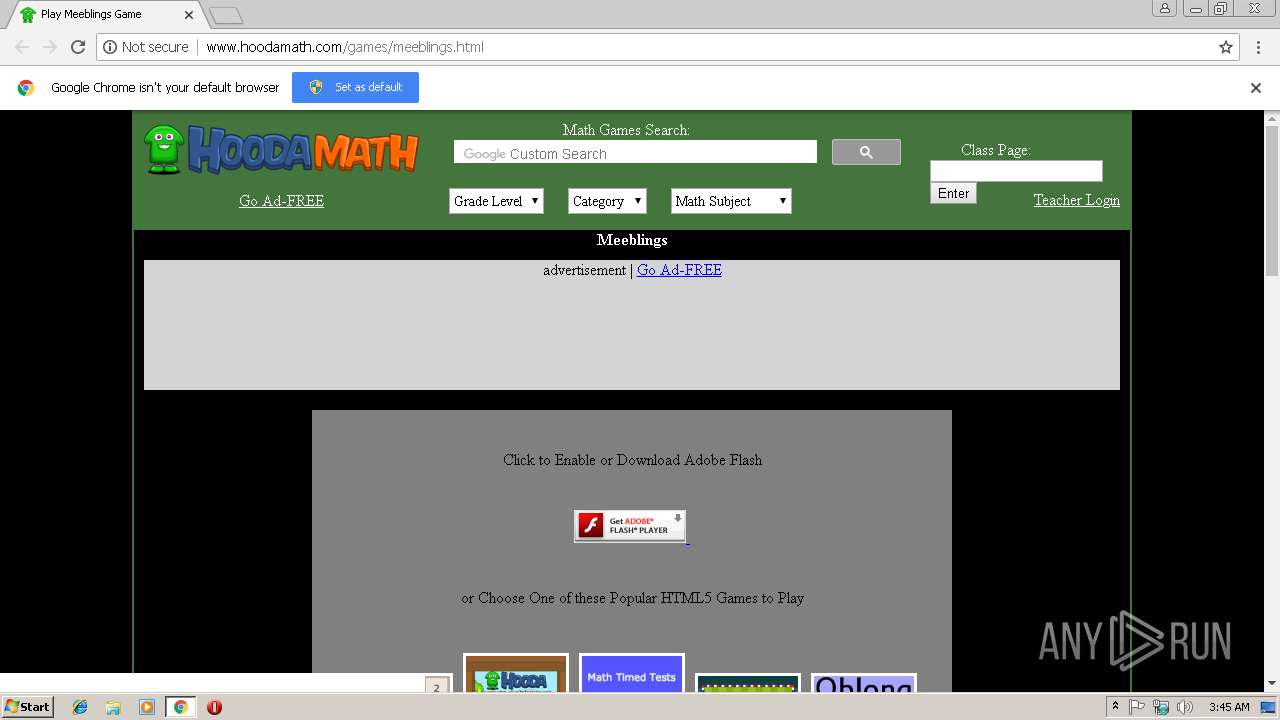
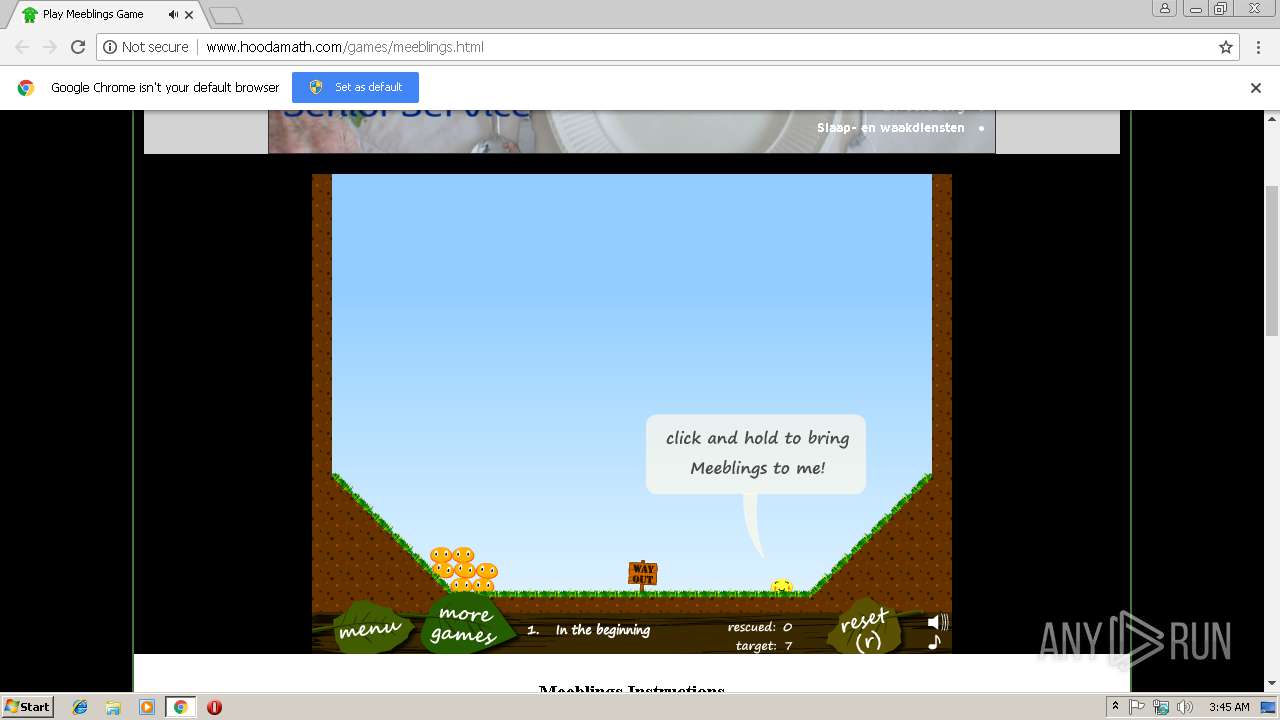
| URL: | http://www.hoodamath.com/games/meeblings.html |
| Full analysis: | https://app.any.run/tasks/fed1d559-c390-4d39-ab23-b5288b306759 |
| Verdict: | Malicious activity |
| Analysis date: | February 04, 2019, 03:44:41 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | C62E3B1E35C04B8879D56D4501E36EC2 |
| SHA1: | B5D1FD43F10B4F9783CA2FE64EC914B2C338E3E5 |
| SHA256: | 5C59C872CEB25CFCD6E3EFD4B504E267125E3E7EAF0D3FA88E2E6B751B6F5C50 |
| SSDEEP: | 3:N1KJS4nSdIKHIzK97CWwJ:Cc4nA3v8 |
MALICIOUS
Connects to CnC server
- chrome.exe (PID: 2996)
SUSPICIOUS
No suspicious indicators.INFO
Application launched itself
- chrome.exe (PID: 2996)
Reads settings of System Certificates
- chrome.exe (PID: 2996)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
40
Monitored processes
10
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1424 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=844,3031516371800422712,2667241742975915268,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAACAAwBAAQAAAAAAAAAAAGAAEAAAAAAAAAAAAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAKAAAAEAAAAAAAAAAAAAAACwAAABAAAAAAAAAAAQAAAAoAAAAQAAAAAAAAAAEAAAALAAAA --service-request-channel-token=11BFF5CE3237868FC9DA1CE0606B0AEB --mojo-platform-channel-handle=948 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2576 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=844,3031516371800422712,2667241742975915268,131072 --enable-features=PasswordImport --service-pipe-token=9A0EAD4AFD8AFA7516EDF6E549A9802B --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=9A0EAD4AFD8AFA7516EDF6E549A9802B --renderer-client-id=4 --mojo-platform-channel-handle=1896 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2740 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=844,3031516371800422712,2667241742975915268,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=25421683833339DCAF8622C9E165AED0 --mojo-platform-channel-handle=2284 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2756 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=844,3031516371800422712,2667241742975915268,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=3BE049E1DF63DAB6EB47D85141C58B88 --mojo-platform-channel-handle=4000 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2960 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=3000 --on-initialized-event-handle=304 --parent-handle=308 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2992 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=ppapi --field-trial-handle=844,3031516371800422712,2667241742975915268,131072 --enable-features=PasswordImport --ppapi-flash-args --lang=en-US --device-scale-factor=1 --ppapi-antialiased-text-enabled=0 --ppapi-subpixel-rendering-setting=0 --service-request-channel-token=7E7C8F05353B37C66E6F008550038557 --mojo-platform-channel-handle=3872 --ignored=" --type=renderer " /prefetch:3 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2996 | "C:\Program Files\Google\Chrome\Application\chrome.exe" http://www.hoodamath.com/games/meeblings.html | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 3208 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=844,3031516371800422712,2667241742975915268,131072 --enable-features=PasswordImport --service-pipe-token=D98078C2AB2F37394DB98912B6D15B63 --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=D98078C2AB2F37394DB98912B6D15B63 --renderer-client-id=3 --mojo-platform-channel-handle=2140 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 3736 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=68.0.3440.106 --initial-client-data=0x78,0x7c,0x80,0x74,0x84,0x701500b0,0x701500c0,0x701500cc | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 3888 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=844,3031516371800422712,2667241742975915268,131072 --enable-features=PasswordImport --disable-gpu-sandbox --gpu-preferences=KAAAAAAAAACAAwBAAQAAAAAAAAAAAGAAEAAAAAAAAAAAAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAKAAAAEAAAAAAAAAAAAAAACwAAABAAAAAAAAAAAQAAAAoAAAAQAAAAAAAAAAEAAAALAAAA --service-request-channel-token=C90F5E660EBA0075C160C9BA42927F7B --mojo-platform-channel-handle=3732 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
Total events
533
Read events
489
Write events
41
Delete events
3
Modification events
| (PID) Process: | (2996) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2996) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2960) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2996-13193725497510750 |
Value: 259 | |||
| (PID) Process: | (2996) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2996) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2996) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2996) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3516-13180984670829101 |
Value: 0 | |||
| (PID) Process: | (2996) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (2996) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 2996-13193725497510750 |
Value: 259 | |||
| (PID) Process: | (2996) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid |
Value: | |||
Executable files
0
Suspicious files
27
Text files
88
Unknown types
39
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2996 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\80236e9a-ce30-46e4-9a6e-a6fa699d771b.tmp | — | |
MD5:— | SHA256:— | |||
| 2996 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Download Service\EntryDB\000016.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2996 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000016.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2996 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\c682f19b-a845-484b-9dbe-196f7869b4ea.tmp | — | |
MD5:— | SHA256:— | |||
| 2996 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Last Version | text | |
MD5:— | SHA256:— | |||
| 2996 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RF20e7e3.TMP | text | |
MD5:— | SHA256:— | |||
| 2996 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2996 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF20e7e3.TMP | text | |
MD5:— | SHA256:— | |||
| 2996 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Download Service\EntryDB\LOG.old~RF20e7d4.TMP | text | |
MD5:8CA4BA2B95D7089861A48ED69FDE6561 | SHA256:AA64C14D0C68B62BBAB62A6D6FA4662FF89E1FBC7B337C926AC213C191D6406C | |||
| 2996 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Service Worker\Database\LOG.old | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
91
TCP/UDP connections
57
DNS requests
35
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2996 | chrome.exe | GET | 200 | 54.230.202.46:80 | http://jpg.hoodamath.com/newlogo_951x173.png | US | image | 58.3 Kb | suspicious |
2996 | chrome.exe | GET | 200 | 54.230.202.94:80 | http://www.hoodamath.com/games/meeblings.html | US | html | 33.3 Kb | malicious |
2996 | chrome.exe | GET | 301 | 92.123.235.227:80 | http://www.adobe.com/images/shared/download_buttons/get_flash_player.gif | unknown | html | 281 b | whitelisted |
2996 | chrome.exe | GET | 302 | 216.58.208.36:80 | http://www.google.com/cse/cse.js?cx=002931417018926584874:4kvydnq3lno | US | html | 267 b | malicious |
2996 | chrome.exe | GET | 200 | 54.230.202.46:80 | http://jpg.hoodamath.com/large/takeitdown_300x225.jpg | US | image | 16.4 Kb | suspicious |
2996 | chrome.exe | GET | 200 | 54.230.202.46:80 | http://jpg.hoodamath.com/large/spillthesand_300x225.jpg | US | image | 7.91 Kb | suspicious |
2996 | chrome.exe | GET | 200 | 54.230.202.46:80 | http://jpg.hoodamath.com/large/gravitystacker_300x225.jpg | US | image | 11.7 Kb | suspicious |
2996 | chrome.exe | GET | 200 | 54.230.202.46:80 | http://jpg.hoodamath.com/large/cargobridgearmorgamesedition_300x225.jpg | US | image | 15.4 Kb | suspicious |
2996 | chrome.exe | GET | 200 | 54.230.202.46:80 | http://jpg.hoodamath.com/large/savethepenguin_300x225.jpg | US | image | 13.9 Kb | suspicious |
2996 | chrome.exe | GET | 200 | 54.230.202.46:80 | http://jpg.hoodamath.com/large/colorfill_300x225.jpg | US | image | 15.7 Kb | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2996 | chrome.exe | 92.123.235.227:443 | www.adobe.com | Akamai International B.V. | — | whitelisted |
2996 | chrome.exe | 172.217.18.3:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2996 | chrome.exe | 216.58.208.35:443 | www.gstatic.com | Google Inc. | US | whitelisted |
2996 | chrome.exe | 172.217.18.98:443 | www.googletagservices.com | Google Inc. | US | whitelisted |
2996 | chrome.exe | 54.230.202.94:80 | www.hoodamath.com | Amazon.com, Inc. | US | unknown |
2996 | chrome.exe | 216.58.206.2:443 | adservice.google.com | Google Inc. | US | whitelisted |
2996 | chrome.exe | 216.58.205.238:443 | cse.google.com | Google Inc. | US | whitelisted |
2996 | chrome.exe | 54.230.202.46:80 | jpg.hoodamath.com | Amazon.com, Inc. | US | unknown |
2996 | chrome.exe | 172.217.22.14:80 | www.google-analytics.com | Google Inc. | US | whitelisted |
2996 | chrome.exe | 216.58.208.33:80 | tpc.googlesyndication.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
www.hoodamath.com |
| malicious |
www.gstatic.com |
| whitelisted |
accounts.google.com |
| shared |
www.googletagservices.com |
| whitelisted |
www.adobe.com |
| whitelisted |
jpg.hoodamath.com |
| suspicious |
www.google.com |
| malicious |
class.hoodamath.com |
| unknown |
cse.google.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
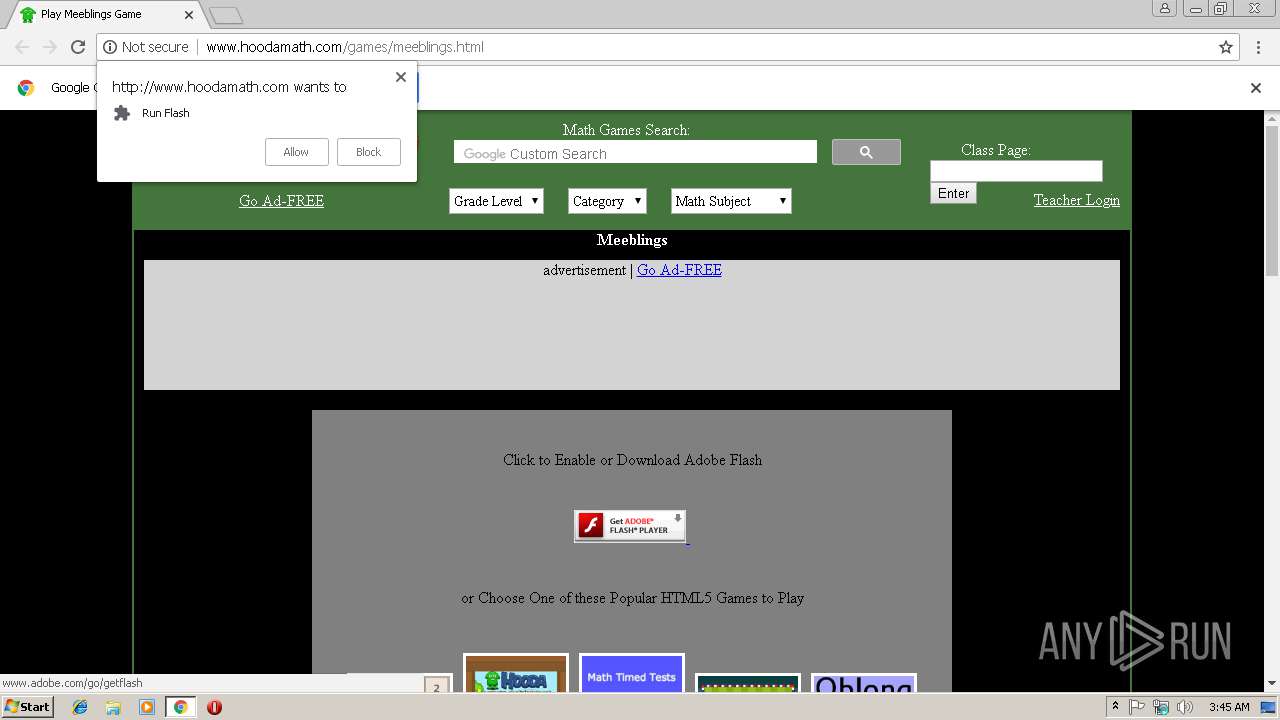
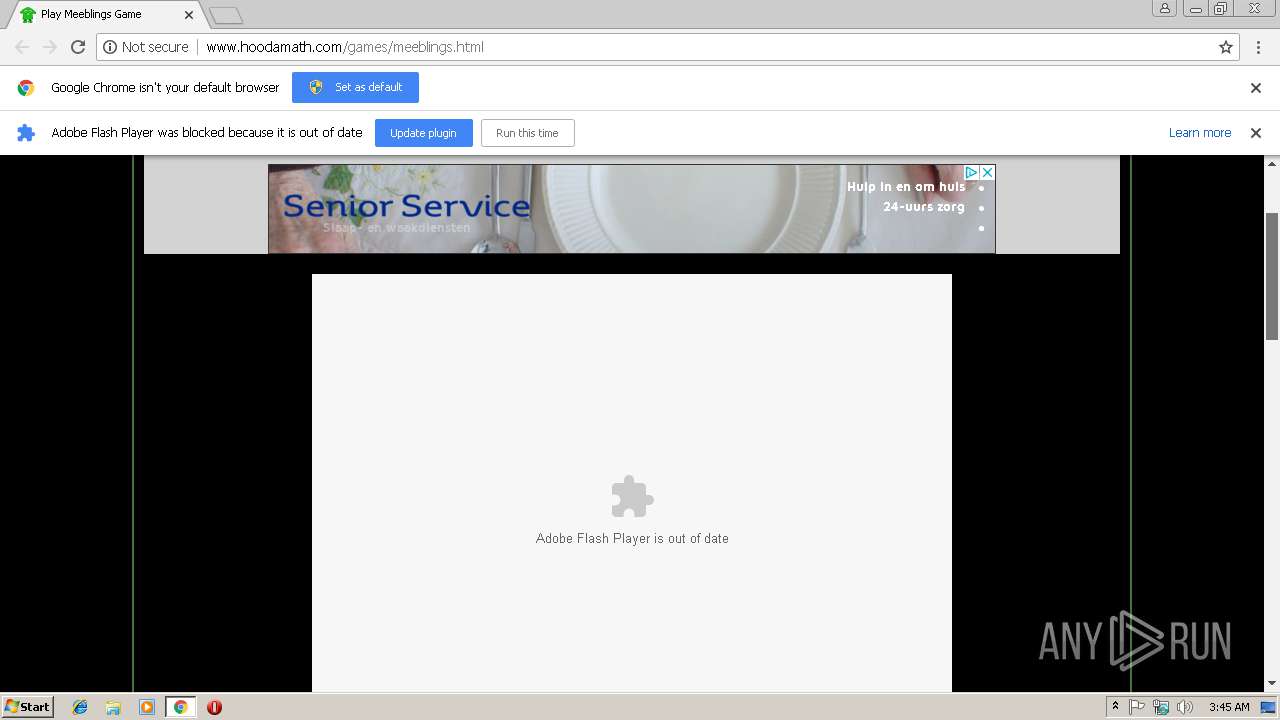
2996 | chrome.exe | Potential Corporate Privacy Violation | ET POLICY Outdated Flash Version M2 |
2996 | chrome.exe | Potential Corporate Privacy Violation | POLICY [PTsecurity] MochiBot SWF Check-in |