| File name: | rpm-8-9-3-3150-mpkinst.exe |
| Full analysis: | https://app.any.run/tasks/9ef35a8a-d69c-4113-b3df-287689730984 |
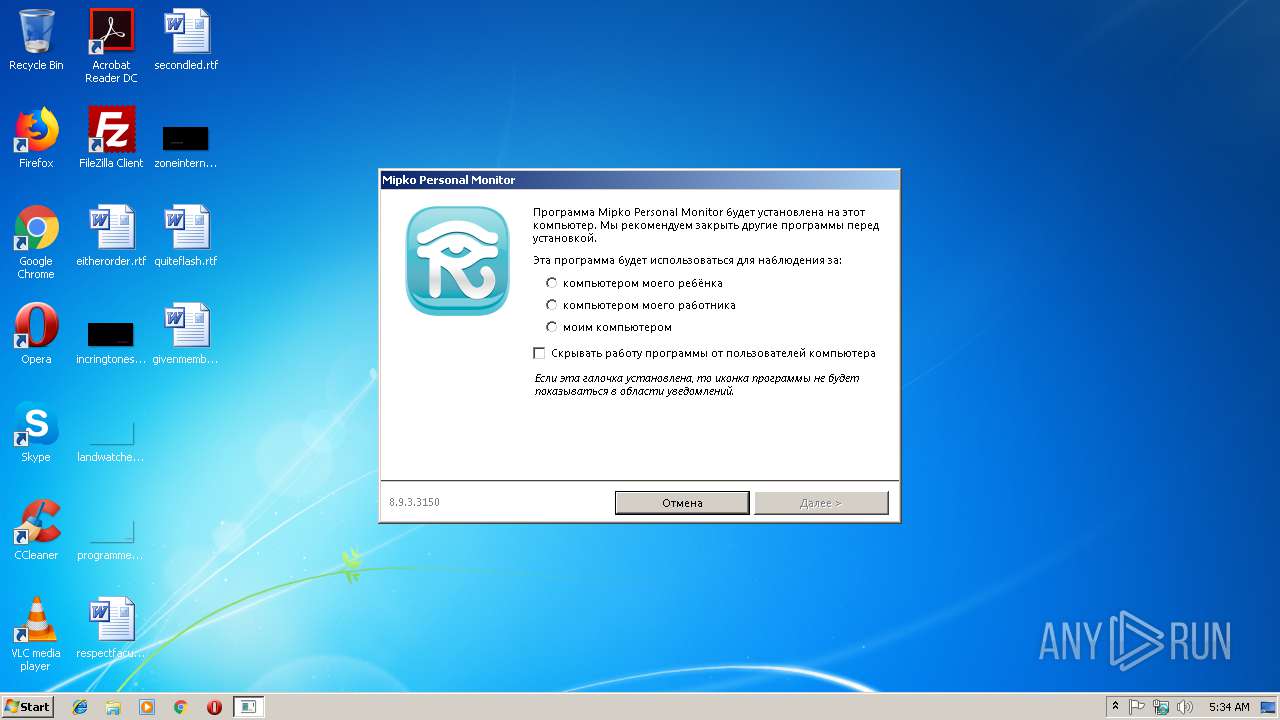
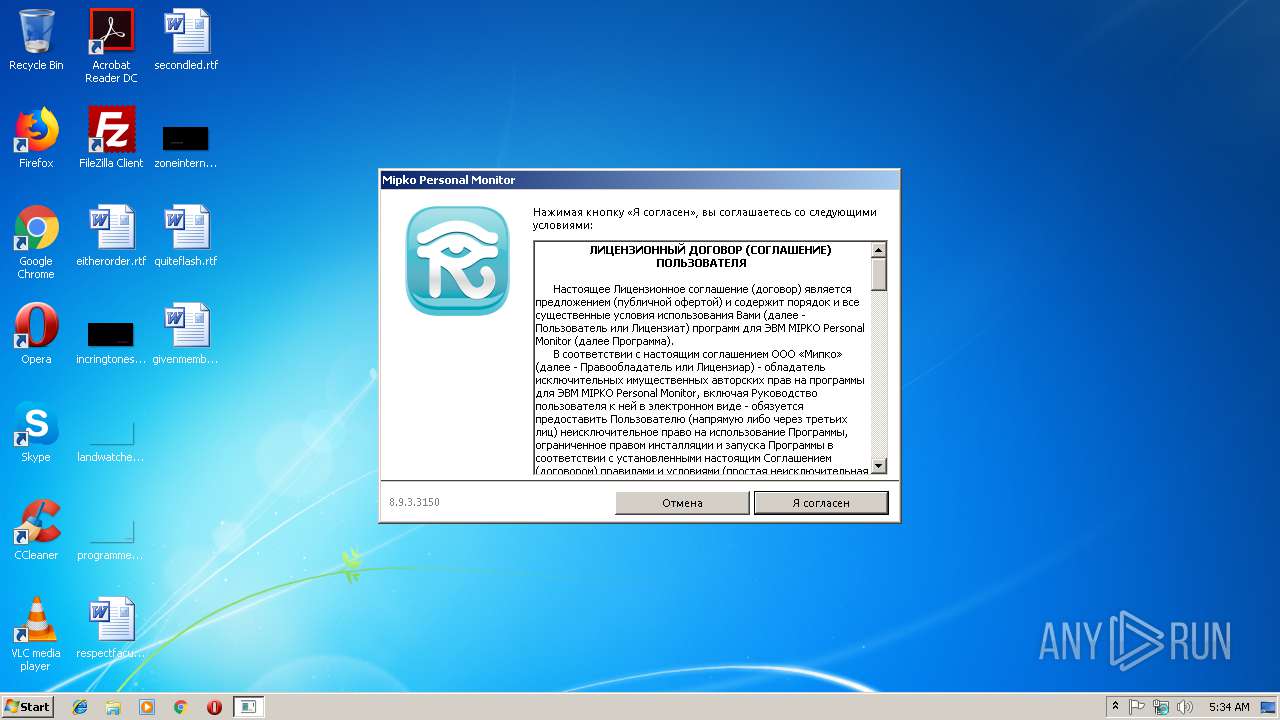
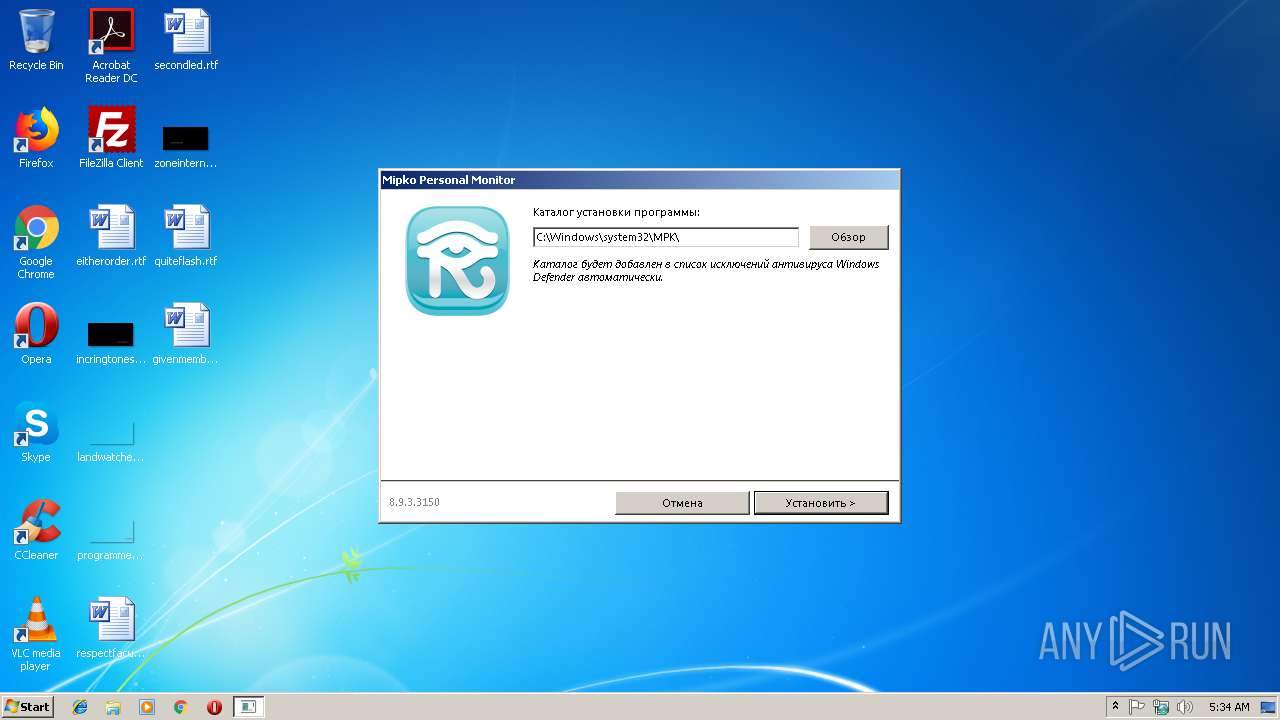
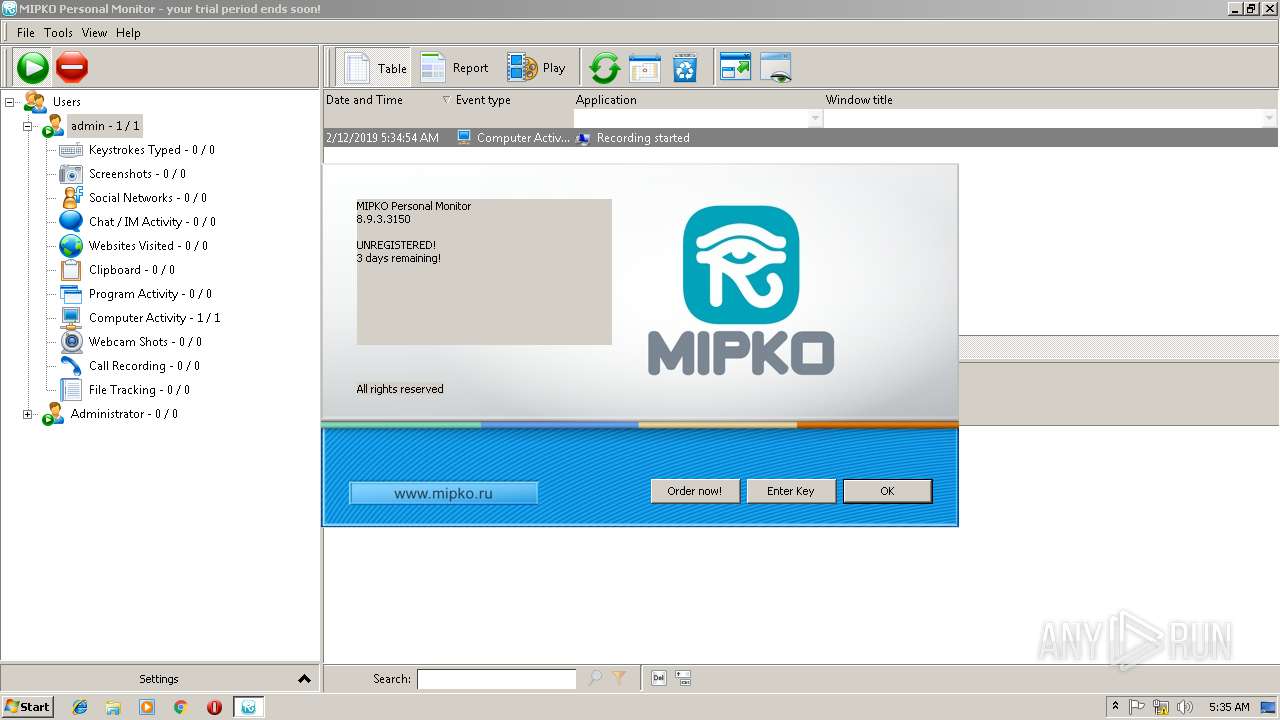
| Verdict: | Malicious activity |
| Analysis date: | February 12, 2019, 05:34:01 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 51FF378C929330D52FC0A0C50393F65E |
| SHA1: | 7A1C3B3D6FF9AB9D572B99272B6E5241CDC5C340 |
| SHA256: | 5C53572648231B25913B9AC2B686CD8DE1B1FA47E050B52211452F2E6F0F44A2 |
| SSDEEP: | 196608:PExh/SNz9CFQnzNVFztPHwWYy40fmF7xAxgXrfyZeMLZp5BYOLVJUqDPkIogwQEL:PExh/SV4qhx+0dg7KZemZfB/7XEnAK |
MALICIOUS
Application was dropped or rewritten from another process
- 2A87C370-29AE-4A49-82CB-2421F7DBC3EC.exe (PID: 2356)
- mpk.exe (PID: 2244)
- mpkview.exe (PID: 2408)
- lsynchost.exe (PID: 2336)
- lsynchost.exe (PID: 3212)
- lsynchost.exe (PID: 4068)
- lsynchost.exe (PID: 2956)
- MPKInst.exe (PID: 3496)
- MPK.exe (PID: 2816)
Changes the login/logoff helper path in the registry
- 2A87C370-29AE-4A49-82CB-2421F7DBC3EC.tmp (PID: 3084)
Loads dropped or rewritten executable
- MPK.exe (PID: 2816)
- explorer.exe (PID: 116)
- mpkview.exe (PID: 2408)
SUSPICIOUS
Executable content was dropped or overwritten
- rpm-8-9-3-3150-mpkinst.exe (PID: 2344)
- 2A87C370-29AE-4A49-82CB-2421F7DBC3EC.exe (PID: 2356)
- 2A87C370-29AE-4A49-82CB-2421F7DBC3EC.tmp (PID: 3084)
Removes files from Windows directory
- rpm-8-9-3-3150-mpkinst.exe (PID: 2344)
- mpkview.exe (PID: 2408)
Reads Windows owner or organization settings
- 2A87C370-29AE-4A49-82CB-2421F7DBC3EC.tmp (PID: 3084)
Creates files in the Windows directory
- rpm-8-9-3-3150-mpkinst.exe (PID: 2344)
- MPK.exe (PID: 2816)
- 2A87C370-29AE-4A49-82CB-2421F7DBC3EC.tmp (PID: 3084)
Starts CMD.EXE for commands execution
- 2A87C370-29AE-4A49-82CB-2421F7DBC3EC.tmp (PID: 3084)
Reads the Windows organization settings
- 2A87C370-29AE-4A49-82CB-2421F7DBC3EC.tmp (PID: 3084)
Uses NETSH.EXE for network configuration
- cmd.exe (PID: 3724)
- cmd.exe (PID: 2292)
Creates files in the program directory
- mpk.exe (PID: 2244)
- MPK.exe (PID: 2816)
- mpkview.exe (PID: 2408)
Creates COM task schedule object
- mpkview.exe (PID: 2408)
INFO
Loads dropped or rewritten executable
- 2A87C370-29AE-4A49-82CB-2421F7DBC3EC.tmp (PID: 3084)
Application was dropped or rewritten from another process
- 2A87C370-29AE-4A49-82CB-2421F7DBC3EC.tmp (PID: 3084)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Inno Setup installer (53.5) |
|---|---|---|
| .exe | | | InstallShield setup (21) |
| .exe | | | Win32 EXE PECompact compressed (generic) (20.2) |
| .exe | | | Win32 Executable (generic) (2.1) |
| .exe | | | Win16/32 Executable Delphi generic (1) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2019:01:17 16:15:55+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 2121728 |
| InitializedDataSize: | 12486144 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x2078bc |
| OSVersion: | 5 |
| ImageVersion: | - |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
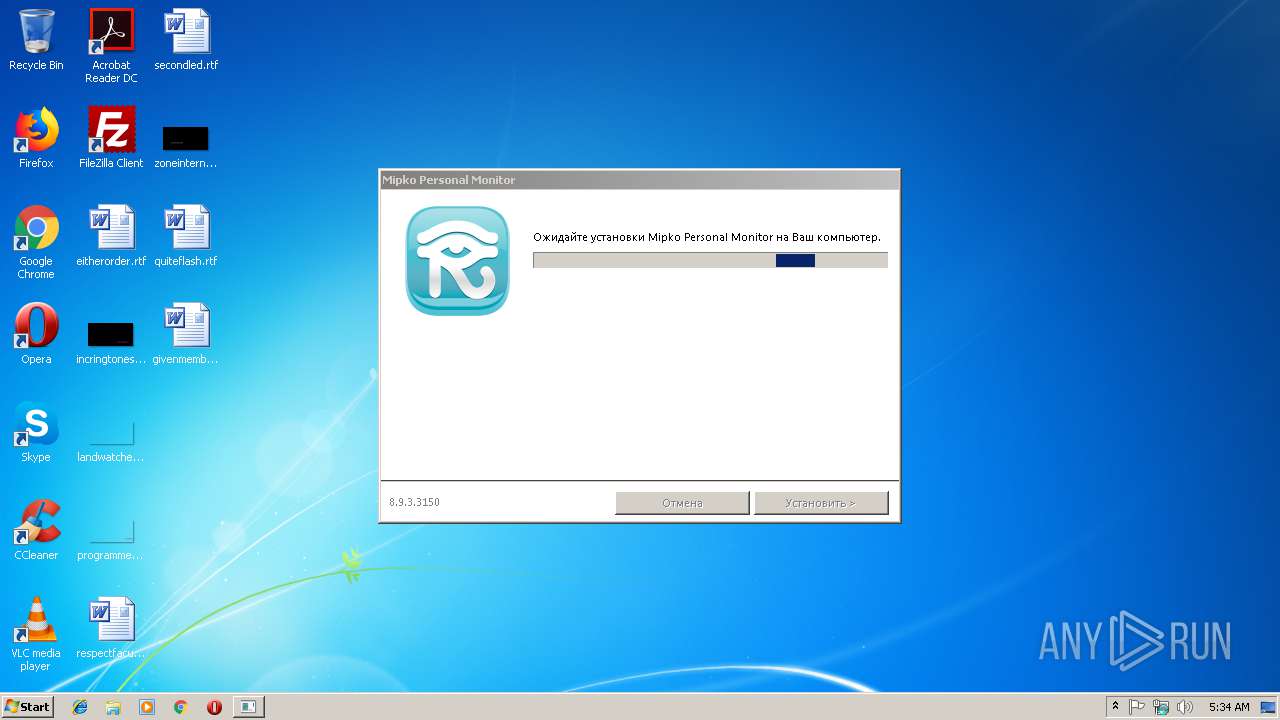
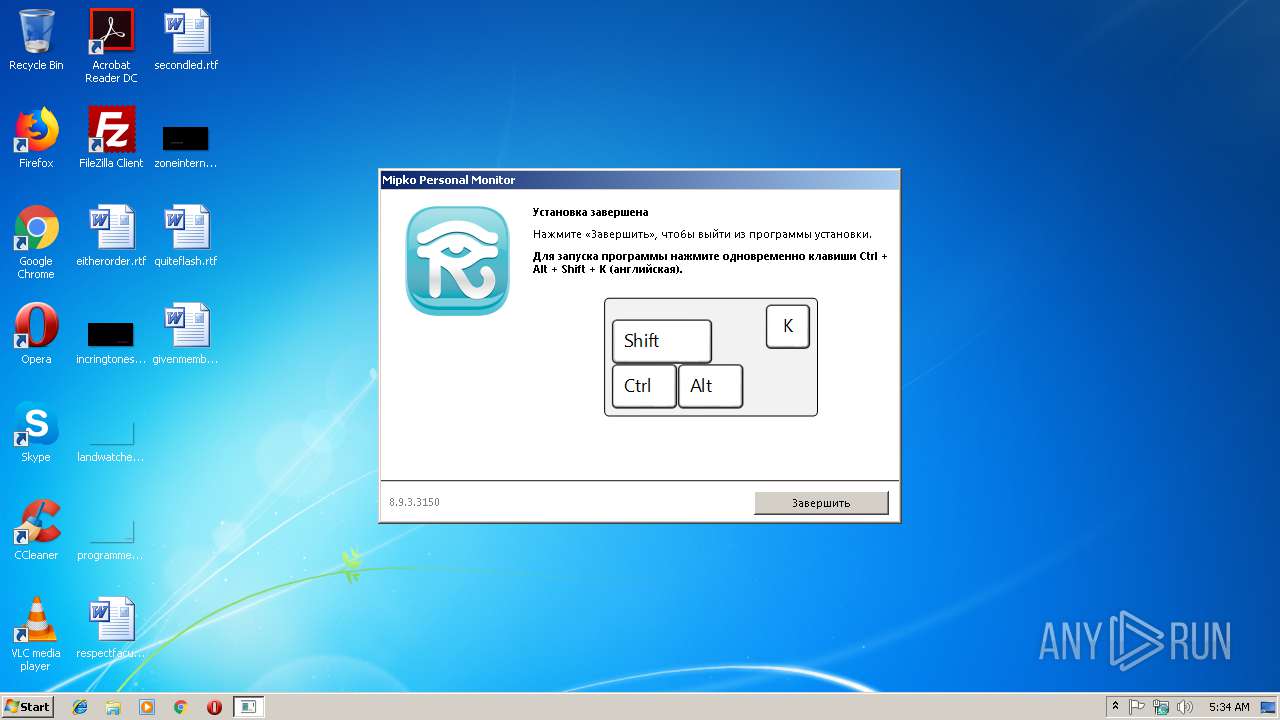
| FileVersionNumber: | 8.9.3.3150 |
| ProductVersionNumber: | 8.9.3.3150 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | ASCII |
| FileVersion: | 8.9.3.3150 |
| ProductVersion: | 8.9.3.3150 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 17-Jan-2019 15:15:55 |
| Detected languages: |
|
| FileVersion: | 8.9.3.3150 |
| ProductVersion: | 8.9.3.3150 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0050 |
| Pages in file: | 0x0002 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x000F |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x001A |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 11 |
| Time date stamp: | 17-Jan-2019 15:15:55 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00204550 | 0x00204600 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.27443 |
.itext | 0x00206000 | 0x00001910 | 0x00001A00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.17378 |
.data | 0x00208000 | 0x0000D610 | 0x0000D800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 5.55699 |
.bss | 0x00216000 | 0x000871FC | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.idata | 0x0029E000 | 0x00003F16 | 0x00004000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 5.28098 |
.didata | 0x002A2000 | 0x0000085E | 0x00000A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.66117 |
.edata | 0x002A3000 | 0x0000004C | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 0.801191 |
.tls | 0x002A4000 | 0x00000048 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rdata | 0x002A5000 | 0x00000018 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 0.210826 |
.reloc | 0x002A6000 | 0x0002B928 | 0x0002BA00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.6407 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 3.77332 | 1101 | UNKNOWN | Russian - Russia | RT_MANIFEST |
2 | 2.80231 | 308 | UNKNOWN | English - United States | RT_CURSOR |
3 | 3.00046 | 308 | UNKNOWN | English - United States | RT_CURSOR |
4 | 2.56318 | 308 | UNKNOWN | English - United States | RT_CURSOR |
5 | 2.6949 | 308 | UNKNOWN | English - United States | RT_CURSOR |
6 | 2.62527 | 308 | UNKNOWN | English - United States | RT_CURSOR |
7 | 2.91604 | 308 | UNKNOWN | English - United States | RT_CURSOR |
100 | 3.37477 | 17806 | UNKNOWN | Russian - Russia | RT_RCDATA |
200 | 7.99824 | 10939080 | UNKNOWN | Russian - Russia | RT_RCDATA |
300 | 6.34887 | 1038783 | UNKNOWN | Russian - Russia | RT_RCDATA |
Imports
advapi32.dll |
comctl32.dll |
gdi32.dll |
kernel32.dll |
kernel32.dll (delay-loaded) |
msimg32.dll |
msvcrt.dll |
ole32.dll |
oleaut32.dll |
shell32.dll |
Exports
Title | Ordinal | Address |
|---|---|---|
0x | 1 | 0x00168854 |
Total processes
51
Monitored processes
17
Malicious processes
7
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 116 | C:\Windows\Explorer.EXE | C:\Windows\explorer.exe | — | — | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1200 | netsh advfirewall firewall add rule name="TCP\IP" dir=in action=allow program="C:\Windows\system32\MPK\mpkview.exe" enable=yes | C:\Windows\system32\netsh.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Network Command Shell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1316 | netsh advfirewall firewall add rule name="TCP\IP" dir=in action=allow program="C:\Windows\system32\MPK\mpk.exe" enable=yes | C:\Windows\system32\netsh.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Network Command Shell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2244 | C:\Windows\system32\MPK\mpk.exe | C:\Windows\system32\MPK\mpk.exe | — | rpm-8-9-3-3150-mpkinst.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Version: 8.9.3.3150 Modules
| |||||||||||||||
| 2292 | "C:\Windows\system32\cmd.exe" /c netsh advfirewall firewall add rule name="TCP\IP" dir=in action=allow program="C:\Windows\system32\MPK\mpk.exe" enable=yes | C:\Windows\system32\cmd.exe | — | 2A87C370-29AE-4A49-82CB-2421F7DBC3EC.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2336 | c:\windows\system32\mpk\\lsynchost.exe /install /silent | c:\windows\system32\mpk\lsynchost.exe | — | MPKInst.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Version: 8.9.3.3150 Modules
| |||||||||||||||
| 2344 | "C:\Users\admin\AppData\Local\Temp\rpm-8-9-3-3150-mpkinst.exe" | C:\Users\admin\AppData\Local\Temp\rpm-8-9-3-3150-mpkinst.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Version: 8.9.3.3150 Modules
| |||||||||||||||
| 2356 | C:\Windows\system32\MPK\2A87C370-29AE-4A49-82CB-2421F7DBC3EC.exe /SDI=0 /AF="C:\Windows\system32\MPK\" /LOG="C:\Windows\system32\MPK\log.txt" /VERYSILENT /SUPPRESSMSGBOXES /NORESTART /RESTARTEXITCODE=100 /PASSWORD=9f42040a-7b35-4f3f-a546-91c708a2b843 /PM | C:\Windows\system32\MPK\2A87C370-29AE-4A49-82CB-2421F7DBC3EC.exe | rpm-8-9-3-3150-mpkinst.exe | ||||||||||||
User: admin Company: MIPKO Integrity Level: HIGH Description: Personal Monitor Setup Exit code: 0 Version: 8.9.3.3150 Modules
| |||||||||||||||
| 2408 | C:\Windows\system32\MPK\mpkview.exe | C:\Windows\system32\MPK\mpkview.exe | rpm-8-9-3-3150-mpkinst.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Version: 8.9.3.3150 Modules
| |||||||||||||||
| 2816 | "c:\windows\system32\mpk\MPK.exe" | c:\windows\system32\mpk\MPK.exe | lsynchost.exe | ||||||||||||
User: SYSTEM Integrity Level: SYSTEM Exit code: 0 Version: 8.9.3.3150 Modules
| |||||||||||||||
Total events
529
Read events
381
Write events
148
Delete events
0
Modification events
| (PID) Process: | (116) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\UserAssist\{CEBFF5CD-ACE2-4F4F-9178-9926F41749EA}\Count |
| Operation: | write | Name: | P:\Hfref\nqzva\NccQngn\Ybpny\Grzc\ecz-8-9-3-3150-zcxvafg.rkr |
Value: 00000000000000000000000000000000000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BFFFFFFFFF000000000000000000000000 | |||
| (PID) Process: | (116) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\UserAssist\{CEBFF5CD-ACE2-4F4F-9178-9926F41749EA}\Count |
| Operation: | write | Name: | HRZR_PGYFRFFVBA |
Value: 000000002E0000003D000000FA3A1500090000000B000000DCC402007B00370043003500410034003000450046002D0041003000460042002D0034004200460043002D0038003700340041002D004300300046003200450030004200390046004100380045007D005C00410064006F00620065005C004100630072006F0062006100740020005200650061006400650072002000440043005C005200650061006400650072005C004100630072006F0052006400330032002E0065007800650000000000D09866060000000034E82802C05D5A740200000002000000000C00940F000000E8E82802010000000400000001000000010000006B001001D098660605000000D098660602020000E20101AE2B51EA0088E7280239B58D76E20101AE24E82802130000000400000030000000120000001D000000130000001D0000000E00000012000000020000003200000014000000E387EE7A38E82802F3AE5B7400574100E20101AE010000000000000011000000F0443500E8443500A14A52740000000020E800001F51EA7AD0E728028291917520E828028CD800006B51EA7AE4E72802B69C917590D8D4035C0000000401000084F2280244F228026B4E317411000000F0443500E8443500A8EAD403FA4F31740000000074E80000AB5EEA7A24E828028291917574E8280228E8280227959175000000008CD8D40350E82802CD9491758CD8D403FCE8280200D4D403E19491750000000000D4D403FCE8280258E82802000000000E0000005DEC04007B00440036003500320033003100420030002D0042003200460031002D0034003800350037002D0041003400430045002D004100380045003700430036004500410037004400320037007D005C007400610073006B006D00670072002E0065007800650000003702000008023CE23702350100C082BAD075B048D4750200000001000000A048D4750100000068E23702C5B8D075A848D47501000000C81008000000000090E237026BB9D07500000000350100C001000000B0E23702973CB8779C3CB877F58CF77501000000350100C00000000088E23702FFFFFFFFF8E23702EDE0B47745727800FEFFFFFFC0E237020D6BD075A0E737028CE8370200000000F8E23702973CB8779C3CB877BD8CF775000000008CE83702A0E73702D0E237020100000070E73702EDE0B47745727800FEFFFFFF08E337020D6BD0757E0000008CE8370280E73702F36BD075E186D0752794C6128CE8370210000000570104003E0040008CE83702A0E73702000000000000000000000000000008025CE537020000080254E33702350100C000000000D8E637023200000018000000000000000000000088E3370211000000B8450B00B0450B0032000000D8E63702F0E300009B1EC112A0E3370282919576F0E33702A4E3370227959576000000006C155002CCE33702CD9495766C15500278E43702E0105002E194957600000000E010500278E43702D4E33702090000000B000000DCC402007B00370043003500410034003000450046002D0041003000460042002D0034004200460043002D0038003700340041002D004300300046003200450030004200390046004100380045007D005C00410064006F00620065005C004100630072006F0062006100740020005200650061006400650072002000440043005C005200650061006400650072005C004100630072006F0052006400330032002E0065007800650000000000D09866060000000034E82802C05D5A740200000002000000000C00940F000000E8E82802010000000400000001000000010000006B001001D098660605000000D098660602020000E20101AE2B51EA0088E7280239B58D76E20101AE24E82802130000000400000030000000120000001D000000130000001D0000000E00000012000000020000003200000014000000E387EE7A38E82802F3AE5B7400574100E20101AE010000000000000011000000F0443500E8443500A14A52740000000020E800001F51EA7AD0E728028291917520E828028CD800006B51EA7AE4E72802B69C917590D8D4035C0000000401000084F2280244F228026B4E317411000000F0443500E8443500A8EAD403FA4F31740000000074E80000AB5EEA7A24E828028291917574E8280228E8280227959175000000008CD8D40350E82802CD9491758CD8D403FCE8280200D4D403E19491750000000000D4D403FCE8280258E82802 | |||
| (PID) Process: | (116) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\UserAssist\{CEBFF5CD-ACE2-4F4F-9178-9926F41749EA}\Count |
| Operation: | write | Name: | P:\Hfref\nqzva\NccQngn\Ybpny\Grzc\ecz-8-9-3-3150-zcxvafg.rkr |
Value: 00000000000000000100000000000000000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BFFFFFFFFF000000000000000000000000 | |||
| (PID) Process: | (116) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\UserAssist\{CEBFF5CD-ACE2-4F4F-9178-9926F41749EA}\Count |
| Operation: | write | Name: | HRZR_PGYFRFFVBA |
Value: 000000002E0000003E000000FA3A1500090000000B000000DCC402007B00370043003500410034003000450046002D0041003000460042002D0034004200460043002D0038003700340041002D004300300046003200450030004200390046004100380045007D005C00410064006F00620065005C004100630072006F0062006100740020005200650061006400650072002000440043005C005200650061006400650072005C004100630072006F0052006400330032002E0065007800650000000000D09866060000000034E82802C05D5A740200000002000000000C00940F000000E8E82802010000000400000001000000010000006B001001D098660605000000D098660602020000E20101AE2B51EA0088E7280239B58D76E20101AE24E82802130000000400000030000000120000001D000000130000001D0000000E00000012000000020000003200000014000000E387EE7A38E82802F3AE5B7400574100E20101AE010000000000000011000000F0443500E8443500A14A52740000000020E800001F51EA7AD0E728028291917520E828028CD800006B51EA7AE4E72802B69C917590D8D4035C0000000401000084F2280244F228026B4E317411000000F0443500E8443500A8EAD403FA4F31740000000074E80000AB5EEA7A24E828028291917574E8280228E8280227959175000000008CD8D40350E82802CD9491758CD8D403FCE8280200D4D403E19491750000000000D4D403FCE8280258E82802000000000E0000005DEC04007B00440036003500320033003100420030002D0042003200460031002D0034003800350037002D0041003400430045002D004100380045003700430036004500410037004400320037007D005C007400610073006B006D00670072002E0065007800650000003702000008023CE23702350100C082BAD075B048D4750200000001000000A048D4750100000068E23702C5B8D075A848D47501000000C81008000000000090E237026BB9D07500000000350100C001000000B0E23702973CB8779C3CB877F58CF77501000000350100C00000000088E23702FFFFFFFFF8E23702EDE0B47745727800FEFFFFFFC0E237020D6BD075A0E737028CE8370200000000F8E23702973CB8779C3CB877BD8CF775000000008CE83702A0E73702D0E237020100000070E73702EDE0B47745727800FEFFFFFF08E337020D6BD0757E0000008CE8370280E73702F36BD075E186D0752794C6128CE8370210000000570104003E0040008CE83702A0E73702000000000000000000000000000008025CE537020000080254E33702350100C000000000D8E637023200000018000000000000000000000088E3370211000000B8450B00B0450B0032000000D8E63702F0E300009B1EC112A0E3370282919576F0E33702A4E3370227959576000000006C155002CCE33702CD9495766C15500278E43702E0105002E194957600000000E010500278E43702D4E33702090000000B000000DCC402007B00370043003500410034003000450046002D0041003000460042002D0034004200460043002D0038003700340041002D004300300046003200450030004200390046004100380045007D005C00410064006F00620065005C004100630072006F0062006100740020005200650061006400650072002000440043005C005200650061006400650072005C004100630072006F0052006400330032002E0065007800650000000000D09866060000000034E82802C05D5A740200000002000000000C00940F000000E8E82802010000000400000001000000010000006B001001D098660605000000D098660602020000E20101AE2B51EA0088E7280239B58D76E20101AE24E82802130000000400000030000000120000001D000000130000001D0000000E00000012000000020000003200000014000000E387EE7A38E82802F3AE5B7400574100E20101AE010000000000000011000000F0443500E8443500A14A52740000000020E800001F51EA7AD0E728028291917520E828028CD800006B51EA7AE4E72802B69C917590D8D4035C0000000401000084F2280244F228026B4E317411000000F0443500E8443500A8EAD403FA4F31740000000074E80000AB5EEA7A24E828028291917574E8280228E8280227959175000000008CD8D40350E82802CD9491758CD8D403FCE8280200D4D403E19491750000000000D4D403FCE8280258E82802 | |||
| (PID) Process: | (2344) rpm-8-9-3-3150-mpkinst.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows Defender\Exclusions\Paths |
| Operation: | write | Name: | C:\Windows\system32\MPK\ |
Value: 0 | |||
| (PID) Process: | (116) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\UserAssist\{CEBFF5CD-ACE2-4F4F-9178-9926F41749EA}\Count |
| Operation: | write | Name: | P:\Hfref\nqzva\NccQngn\Ybpny\Grzc\ecz-8-9-3-3150-zcxvafg.rkr |
Value: 00000000000000000100000074190000000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BFFFFFFFFF000000000000000000000000 | |||
| (PID) Process: | (116) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\UserAssist\{CEBFF5CD-ACE2-4F4F-9178-9926F41749EA}\Count |
| Operation: | write | Name: | HRZR_PGYFRFFVBA |
Value: 000000002E0000003E0000006E541500090000000B000000DCC402007B00370043003500410034003000450046002D0041003000460042002D0034004200460043002D0038003700340041002D004300300046003200450030004200390046004100380045007D005C00410064006F00620065005C004100630072006F0062006100740020005200650061006400650072002000440043005C005200650061006400650072005C004100630072006F0052006400330032002E0065007800650000000000D09866060000000034E82802C05D5A740200000002000000000C00940F000000E8E82802010000000400000001000000010000006B001001D098660605000000D098660602020000E20101AE2B51EA0088E7280239B58D76E20101AE24E82802130000000400000030000000120000001D000000130000001D0000000E00000012000000020000003200000014000000E387EE7A38E82802F3AE5B7400574100E20101AE010000000000000011000000F0443500E8443500A14A52740000000020E800001F51EA7AD0E728028291917520E828028CD800006B51EA7AE4E72802B69C917590D8D4035C0000000401000084F2280244F228026B4E317411000000F0443500E8443500A8EAD403FA4F31740000000074E80000AB5EEA7A24E828028291917574E8280228E8280227959175000000008CD8D40350E82802CD9491758CD8D403FCE8280200D4D403E19491750000000000D4D403FCE8280258E82802000000000E0000005DEC04007B00440036003500320033003100420030002D0042003200460031002D0034003800350037002D0041003400430045002D004100380045003700430036004500410037004400320037007D005C007400610073006B006D00670072002E0065007800650000003702000008023CE23702350100C082BAD075B048D4750200000001000000A048D4750100000068E23702C5B8D075A848D47501000000C81008000000000090E237026BB9D07500000000350100C001000000B0E23702973CB8779C3CB877F58CF77501000000350100C00000000088E23702FFFFFFFFF8E23702EDE0B47745727800FEFFFFFFC0E237020D6BD075A0E737028CE8370200000000F8E23702973CB8779C3CB877BD8CF775000000008CE83702A0E73702D0E237020100000070E73702EDE0B47745727800FEFFFFFF08E337020D6BD0757E0000008CE8370280E73702F36BD075E186D0752794C6128CE8370210000000570104003E0040008CE83702A0E73702000000000000000000000000000008025CE537020000080254E33702350100C000000000D8E637023200000018000000000000000000000088E3370211000000B8450B00B0450B0032000000D8E63702F0E300009B1EC112A0E3370282919576F0E33702A4E3370227959576000000006C155002CCE33702CD9495766C15500278E43702E0105002E194957600000000E010500278E43702D4E33702090000000B000000DCC402007B00370043003500410034003000450046002D0041003000460042002D0034004200460043002D0038003700340041002D004300300046003200450030004200390046004100380045007D005C00410064006F00620065005C004100630072006F0062006100740020005200650061006400650072002000440043005C005200650061006400650072005C004100630072006F0052006400330032002E0065007800650000000000D09866060000000034E82802C05D5A740200000002000000000C00940F000000E8E82802010000000400000001000000010000006B001001D098660605000000D098660602020000E20101AE2B51EA0088E7280239B58D76E20101AE24E82802130000000400000030000000120000001D000000130000001D0000000E00000012000000020000003200000014000000E387EE7A38E82802F3AE5B7400574100E20101AE010000000000000011000000F0443500E8443500A14A52740000000020E800001F51EA7AD0E728028291917520E828028CD800006B51EA7AE4E72802B69C917590D8D4035C0000000401000084F2280244F228026B4E317411000000F0443500E8443500A8EAD403FA4F31740000000074E80000AB5EEA7A24E828028291917574E8280228E8280227959175000000008CD8D40350E82802CD9491758CD8D403FCE8280200D4D403E19491750000000000D4D403FCE8280258E82802 | |||
| (PID) Process: | (3084) 2A87C370-29AE-4A49-82CB-2421F7DBC3EC.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Winlogon |
| Operation: | write | Name: | Userinit |
Value: c:\windows\system32\userinit.exe, | |||
| (PID) Process: | (3084) 2A87C370-29AE-4A49-82CB-2421F7DBC3EC.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Winlogon |
| Operation: | write | Name: | DefaultDataInformation |
Value: 0x01292105 | |||
| (PID) Process: | (3084) 2A87C370-29AE-4A49-82CB-2421F7DBC3EC.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
Executable files
22
Suspicious files
6
Text files
116
Unknown types
5
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3084 | 2A87C370-29AE-4A49-82CB-2421F7DBC3EC.tmp | C:\Windows\system32\MPK\is-VNHRE.tmp | — | |
MD5:— | SHA256:— | |||
| 3084 | 2A87C370-29AE-4A49-82CB-2421F7DBC3EC.tmp | C:\Windows\system32\MPK\is-0I60J.tmp | — | |
MD5:— | SHA256:— | |||
| 3084 | 2A87C370-29AE-4A49-82CB-2421F7DBC3EC.tmp | C:\Windows\system32\MPK\is-9GI0J.tmp | — | |
MD5:— | SHA256:— | |||
| 3084 | 2A87C370-29AE-4A49-82CB-2421F7DBC3EC.tmp | C:\Windows\system32\MPK\is-VKPVV.tmp | — | |
MD5:— | SHA256:— | |||
| 3084 | 2A87C370-29AE-4A49-82CB-2421F7DBC3EC.tmp | C:\Windows\system32\MPK\is-SF5P1.tmp | — | |
MD5:— | SHA256:— | |||
| 3084 | 2A87C370-29AE-4A49-82CB-2421F7DBC3EC.tmp | C:\Windows\system32\MPK\is-NGS3K.tmp | — | |
MD5:— | SHA256:— | |||
| 3084 | 2A87C370-29AE-4A49-82CB-2421F7DBC3EC.tmp | C:\Windows\system32\MPK\is-I3SQQ.tmp | — | |
MD5:— | SHA256:— | |||
| 3084 | 2A87C370-29AE-4A49-82CB-2421F7DBC3EC.tmp | C:\Windows\system32\MPK\is-F1TQ1.tmp | — | |
MD5:— | SHA256:— | |||
| 3084 | 2A87C370-29AE-4A49-82CB-2421F7DBC3EC.tmp | C:\Windows\system32\MPK\is-K5TE9.tmp | — | |
MD5:— | SHA256:— | |||
| 3084 | 2A87C370-29AE-4A49-82CB-2421F7DBC3EC.tmp | C:\Windows\system32\MPK\is-AV9CS.tmp | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
DNS requests
Threats
Process | Message |
|---|---|
MPK.exe | c:\windows\system32\mpk\SQLite3.dll |
MPK.exe | c:\windows\system32\mpk\SQLite3.dll |
MPK.exe | freeing sqlite dll |
MPK.exe | loading sqlite lib |
MPK.exe | c:\windows\system32\mpk\SQLite3.dll |
MPK.exe | loading sqlite lib |
MPK.exe | c:\windows\system32\mpk\SQLite3.dll |
MPK.exe | freeing sqlite dll |
MPK.exe | loading sqlite lib |
MPK.exe | c:\windows\system32\mpk\SQLite3.dll |