| File name: | 5c5123168c4542d01c78d5514b7fe95a672d7aa0f42e300640e84c7f04cf0c9d |
| Full analysis: | https://app.any.run/tasks/19a47493-d24a-48f5-a04b-08647c28785b |
| Verdict: | Malicious activity |
| Threats: | Stealers are a group of malicious software that are intended for gaining unauthorized access to users’ information and transferring it to the attacker. The stealer malware category includes various types of programs that focus on their particular kind of data, including files, passwords, and cryptocurrency. Stealers are capable of spying on their targets by recording their keystrokes and taking screenshots. This type of malware is primarily distributed as part of phishing campaigns. |
| Analysis date: | March 25, 2025, 05:22:31 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 9 sections |
| MD5: | 48BB04C3784C8F1867D40E74E366D90C |
| SHA1: | 70CFD21D59D21D1C5501D42C01D5C56EE61CD07F |
| SHA256: | 5C5123168C4542D01C78D5514B7FE95A672D7AA0F42E300640E84C7F04CF0C9D |
| SSDEEP: | 49152:BKFBRduX/LsgdyPOE3XSN9SQhWupZzg0Sh66I668JRWNilSaHDzYt/uF10rC8gx1:YRuXTsEqOEHkWGzgB4ARosNH3YhuF106 |
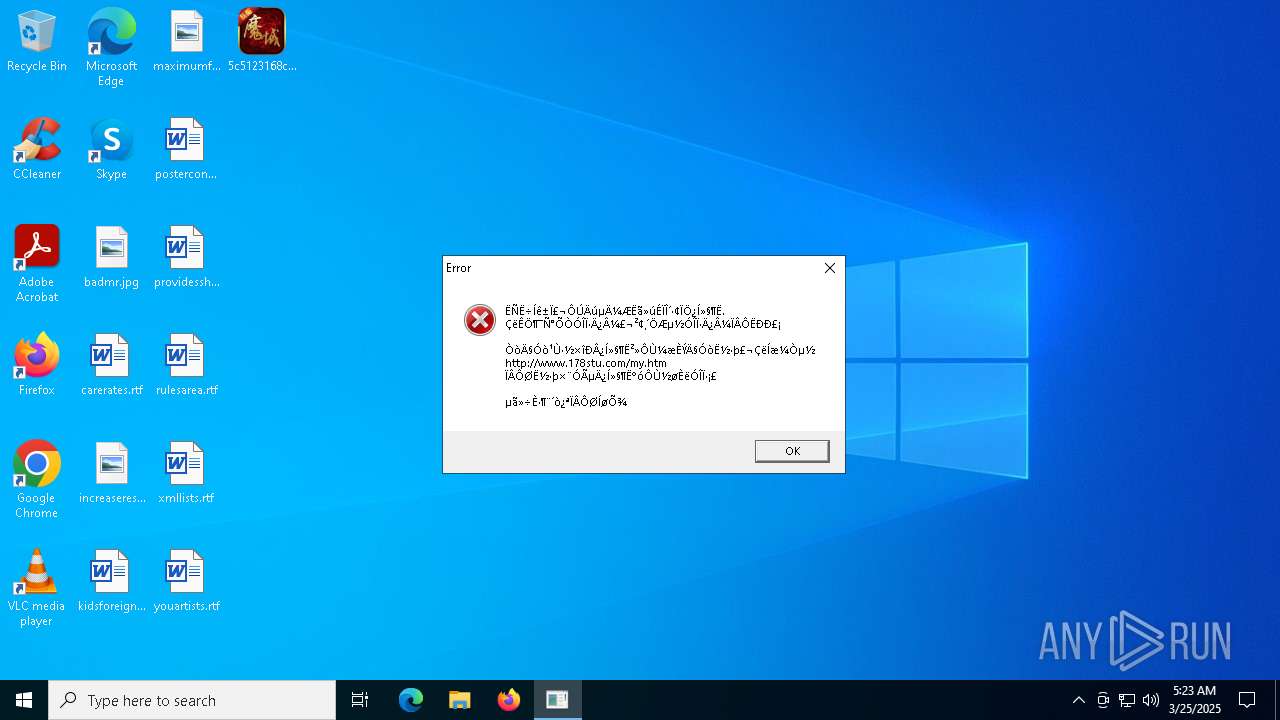
MALICIOUS
XORed URL has been found (YARA)
- 5c5123168c4542d01c78d5514b7fe95a672d7aa0f42e300640e84c7f04cf0c9d.exe (PID: 6744)
Connects to the CnC server
- 5c5123168c4542d01c78d5514b7fe95a672d7aa0f42e300640e84c7f04cf0c9d.exe (PID: 6744)
Actions looks like stealing of personal data
- 5c5123168c4542d01c78d5514b7fe95a672d7aa0f42e300640e84c7f04cf0c9d.exe (PID: 6744)
SUSPICIOUS
Application launched itself
- 5c5123168c4542d01c78d5514b7fe95a672d7aa0f42e300640e84c7f04cf0c9d.exe (PID: 2692)
Reads security settings of Internet Explorer
- 5c5123168c4542d01c78d5514b7fe95a672d7aa0f42e300640e84c7f04cf0c9d.exe (PID: 2692)
- 5c5123168c4542d01c78d5514b7fe95a672d7aa0f42e300640e84c7f04cf0c9d.exe (PID: 6744)
Connects to unusual port
- 5c5123168c4542d01c78d5514b7fe95a672d7aa0f42e300640e84c7f04cf0c9d.exe (PID: 2692)
- 5c5123168c4542d01c78d5514b7fe95a672d7aa0f42e300640e84c7f04cf0c9d.exe (PID: 6744)
There is functionality for taking screenshot (YARA)
- 5c5123168c4542d01c78d5514b7fe95a672d7aa0f42e300640e84c7f04cf0c9d.exe (PID: 6744)
There is functionality for communication over UDP network (YARA)
- 5c5123168c4542d01c78d5514b7fe95a672d7aa0f42e300640e84c7f04cf0c9d.exe (PID: 6744)
Potential Corporate Privacy Violation
- 5c5123168c4542d01c78d5514b7fe95a672d7aa0f42e300640e84c7f04cf0c9d.exe (PID: 6744)
Contacting a server suspected of hosting an CnC
- 5c5123168c4542d01c78d5514b7fe95a672d7aa0f42e300640e84c7f04cf0c9d.exe (PID: 6744)
INFO
The sample compiled with chinese language support
- 5c5123168c4542d01c78d5514b7fe95a672d7aa0f42e300640e84c7f04cf0c9d.exe (PID: 2692)
Reads the computer name
- 5c5123168c4542d01c78d5514b7fe95a672d7aa0f42e300640e84c7f04cf0c9d.exe (PID: 2692)
- 5c5123168c4542d01c78d5514b7fe95a672d7aa0f42e300640e84c7f04cf0c9d.exe (PID: 6744)
- identity_helper.exe (PID: 4728)
Checks supported languages
- 5c5123168c4542d01c78d5514b7fe95a672d7aa0f42e300640e84c7f04cf0c9d.exe (PID: 2692)
- 5c5123168c4542d01c78d5514b7fe95a672d7aa0f42e300640e84c7f04cf0c9d.exe (PID: 6744)
- identity_helper.exe (PID: 4728)
Process checks computer location settings
- 5c5123168c4542d01c78d5514b7fe95a672d7aa0f42e300640e84c7f04cf0c9d.exe (PID: 2692)
Checks proxy server information
- 5c5123168c4542d01c78d5514b7fe95a672d7aa0f42e300640e84c7f04cf0c9d.exe (PID: 6744)
- slui.exe (PID: 5528)
Aspack has been detected
- 5c5123168c4542d01c78d5514b7fe95a672d7aa0f42e300640e84c7f04cf0c9d.exe (PID: 6744)
Compiled with Borland Delphi (YARA)
- 5c5123168c4542d01c78d5514b7fe95a672d7aa0f42e300640e84c7f04cf0c9d.exe (PID: 6744)
Manual execution by a user
- msedge.exe (PID: 6424)
Reads Environment values
- identity_helper.exe (PID: 4728)
Reads the software policy settings
- slui.exe (PID: 5528)
Application launched itself
- msedge.exe (PID: 960)
- msedge.exe (PID: 6424)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
xor-url
(PID) Process(6744) 5c5123168c4542d01c78d5514b7fe95a672d7aa0f42e300640e84c7f04cf0c9d.exe
Decrypted-URLs (2)http://info.178stu.com/hst2_new.txt
http://www.178stu.com/hst2_new.txt
TRiD
| .exe | | | Win32 Executable (generic) (42.6) |
|---|---|---|
| .exe | | | Win16/32 Executable Delphi generic (19.5) |
| .exe | | | Generic Win/DOS Executable (18.9) |
| .exe | | | DOS Executable Generic (18.9) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2021:12:11 12:45:48+00:00 |
| ImageFileCharacteristics: | Executable, No line numbers, No symbols, Bytes reversed lo, 32-bit, Bytes reversed hi |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 546816 |
| InitializedDataSize: | 1371648 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x86c70 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.0 |
| ProductVersionNumber: | 1.0.0.0 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Chinese (Simplified) |
| CharacterSet: | Windows, Chinese (Simplified) |
| CompanyName: | 潇湘网络 |
| FileDescription: | 商业程序 |
| InternalName: | LoginTools.exe |
| LegalCopyright: | 版权所有 (C) 2022 |
| OriginalFileName: | LoginTools.exe |
| ProductName: | 商业程序 |
| ProductVersion: | 1, 0, 0, 0 |
| FileVersion: | 1,0,0,0 |
Total processes
160
Monitored processes
35
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 632 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data" /prefetch:4 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Crashpad" --annotation=IsOfficialBuild=1 --annotation=channel= --annotation=chromium-version=122.0.6261.70 "--annotation=exe=C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --annotation=plat=Win64 "--annotation=prod=Microsoft Edge" --annotation=ver=122.0.2365.59 --initial-client-data=0x310,0x314,0x318,0x308,0x320,0x7ffc898a5fd8,0x7ffc898a5fe4,0x7ffc898a5ff0 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 736 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=entity_extraction_service.mojom.Extractor --lang=en-US --service-sandbox-type=entity_extraction --onnx-enabled-for-ee --no-appcompat-clear --mojo-platform-channel-handle=5344 --field-trial-handle=2364,i,7488303095380290569,7864606430093343844,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 776 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --no-appcompat-clear --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=6 --mojo-platform-channel-handle=3412 --field-trial-handle=2364,i,7488303095380290569,7864606430093343844,262144 --variations-seed-version /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 812 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=asset_store.mojom.AssetStoreService --lang=en-US --service-sandbox-type=asset_store_service --no-appcompat-clear --mojo-platform-channel-handle=5288 --field-trial-handle=2364,i,7488303095380290569,7864606430093343844,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
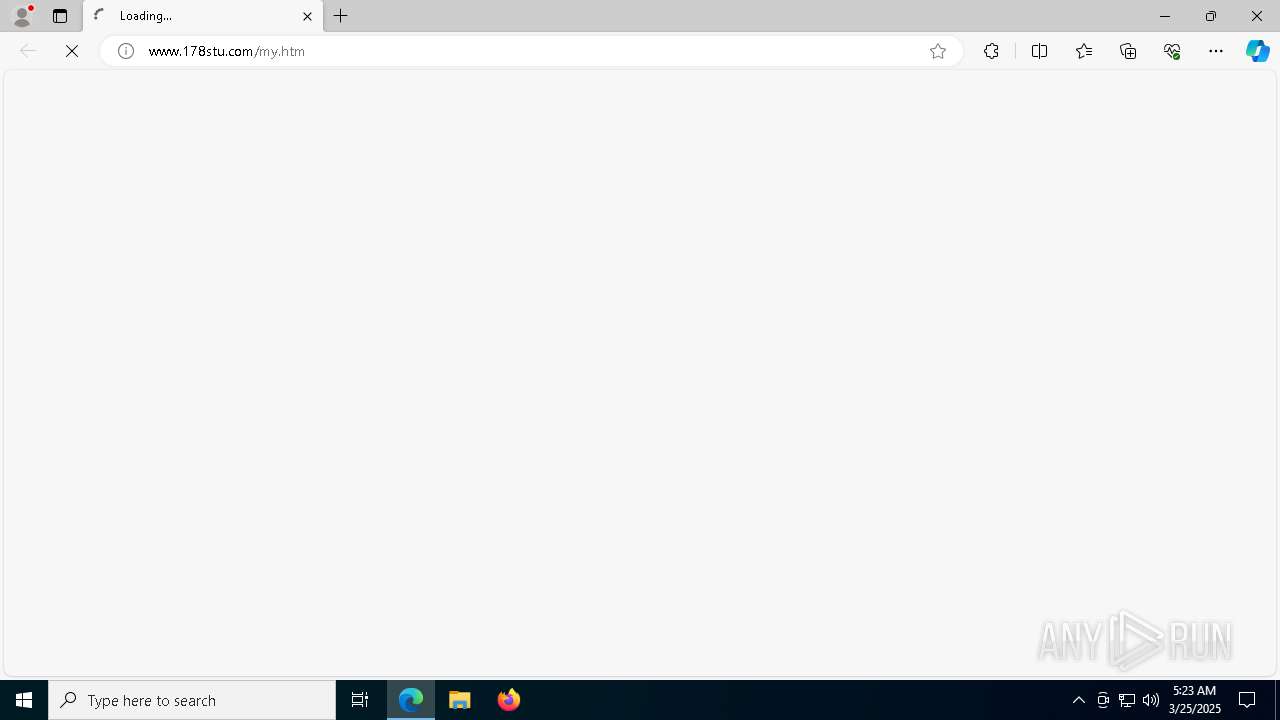
| 960 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --single-argument http://www.178stu.com/my.htm | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | 5c5123168c4542d01c78d5514b7fe95a672d7aa0f42e300640e84c7f04cf0c9d.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Edge Exit code: 1 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1388 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5932 --field-trial-handle=2364,i,7488303095380290569,7864606430093343844,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1388 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=5844 --field-trial-handle=2364,i,7488303095380290569,7864606430093343844,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 2196 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2268 | "C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe" --type=utility --utility-sub-type=winrt_app_id.mojom.WinrtAppIdService --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=5160 --field-trial-handle=2364,i,7488303095380290569,7864606430093343844,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: PWA Identity Proxy Host Exit code: 3221226029 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 2344 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data" /prefetch:4 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Crashpad" --annotation=IsOfficialBuild=1 --annotation=channel= --annotation=chromium-version=122.0.6261.70 "--annotation=exe=C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --annotation=plat=Win64 "--annotation=prod=Microsoft Edge" --annotation=ver=122.0.2365.59 --initial-client-data=0x298,0x29c,0x2a0,0x290,0x2ac,0x7ffc898a5fd8,0x7ffc898a5fe4,0x7ffc898a5ff0 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
Total events
9 636
Read events
9 612
Write events
24
Delete events
0
Modification events
| (PID) Process: | (6744) 5c5123168c4542d01c78d5514b7fe95a672d7aa0f42e300640e84c7f04cf0c9d.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (6744) 5c5123168c4542d01c78d5514b7fe95a672d7aa0f42e300640e84c7f04cf0c9d.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (6744) 5c5123168c4542d01c78d5514b7fe95a672d7aa0f42e300640e84c7f04cf0c9d.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (960) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (960) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (960) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (960) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (960) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 9FFDE335BA8F2F00 | |||
| (PID) Process: | (6424) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (6424) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
Executable files
5
Suspicious files
71
Text files
29
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6424 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF11ec8f.TMP | — | |
MD5:— | SHA256:— | |||
| 6424 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6424 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF11ec8f.TMP | — | |
MD5:— | SHA256:— | |||
| 6424 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6424 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF11ec8f.TMP | — | |
MD5:— | SHA256:— | |||
| 6424 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6424 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF11ecbe.TMP | — | |
MD5:— | SHA256:— | |||
| 6424 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6424 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF11ecbe.TMP | — | |
MD5:— | SHA256:— | |||
| 6424 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
38
TCP/UDP connections
58
DNS requests
43
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2104 | svchost.exe | GET | 200 | 2.20.245.133:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6744 | 5c5123168c4542d01c78d5514b7fe95a672d7aa0f42e300640e84c7f04cf0c9d.exe | GET | — | 103.133.93.52:80 | http://info.178stu.com/hst2_new.txt | unknown | — | — | malicious |
6744 | 5c5123168c4542d01c78d5514b7fe95a672d7aa0f42e300640e84c7f04cf0c9d.exe | GET | — | 103.133.93.52:80 | http://www.178stu.com/hst2_new.txt | unknown | — | — | malicious |
— | — | GET | 401 | 13.107.6.158:443 | https://business.bing.com/api/v1/user/token/microsoftgraph?&clienttype=edge-omnibox | unknown | — | — | unknown |
4000 | msedge.exe | GET | — | 103.133.93.52:80 | http://www.178stu.com/my.htm | unknown | — | — | malicious |
— | — | GET | 304 | 150.171.27.11:443 | https://edge.microsoft.com/abusiveadblocking/api/v1/blocklist | unknown | — | — | unknown |
— | — | GET | 200 | 13.107.246.45:443 | https://edgeassetservice.azureedge.net/assets/domains_config_gz/3.0.7/asset?assetgroup=EntityExtractionDomainsConfig | unknown | — | — | unknown |
4000 | msedge.exe | GET | — | 103.133.93.52:80 | http://www.178stu.com/my.htm | unknown | — | — | malicious |
4000 | msedge.exe | GET | — | 103.133.93.52:80 | http://www.178stu.com/my.htm | unknown | — | — | malicious |
— | — | GET | 302 | 2.23.181.156:443 | https://go.microsoft.com/fwlink/?linkid=2133855&bucket=15 | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
2104 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2692 | 5c5123168c4542d01c78d5514b7fe95a672d7aa0f42e300640e84c7f04cf0c9d.exe | 1.15.12.73:4567 | — | Shenzhen Tencent Computer Systems Company Limited | CN | unknown |
6744 | 5c5123168c4542d01c78d5514b7fe95a672d7aa0f42e300640e84c7f04cf0c9d.exe | 1.15.12.73:4567 | — | Shenzhen Tencent Computer Systems Company Limited | CN | unknown |
2104 | svchost.exe | 2.20.245.133:80 | crl.microsoft.com | Akamai International B.V. | SE | whitelisted |
6744 | 5c5123168c4542d01c78d5514b7fe95a672d7aa0f42e300640e84c7f04cf0c9d.exe | 103.133.93.52:80 | info.178stu.com | SUPERCLOUDS LIMITED | HK | malicious |
2104 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4880 | slui.exe | 20.83.72.98:443 | activation-v2.sls.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
info.178stu.com |
| malicious |
crl.microsoft.com |
| whitelisted |
www.178stu.com |
| malicious |
activation-v2.sls.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
business.bing.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
6744 | 5c5123168c4542d01c78d5514b7fe95a672d7aa0f42e300640e84c7f04cf0c9d.exe | Potential Corporate Privacy Violation | ET INFO Unsupported/Fake Windows NT Version 5.0 |
6744 | 5c5123168c4542d01c78d5514b7fe95a672d7aa0f42e300640e84c7f04cf0c9d.exe | Potential Corporate Privacy Violation | ET INFO Unsupported/Fake Windows NT Version 5.0 |
2 ETPRO signatures available at the full report