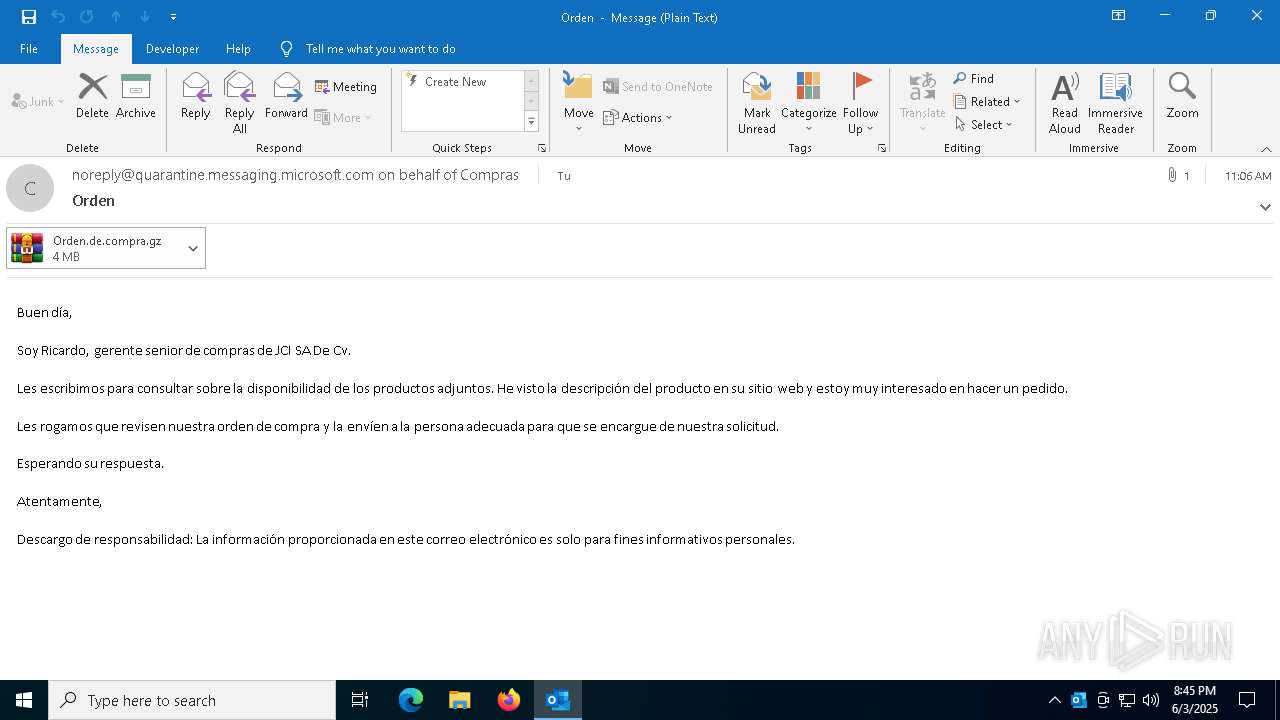
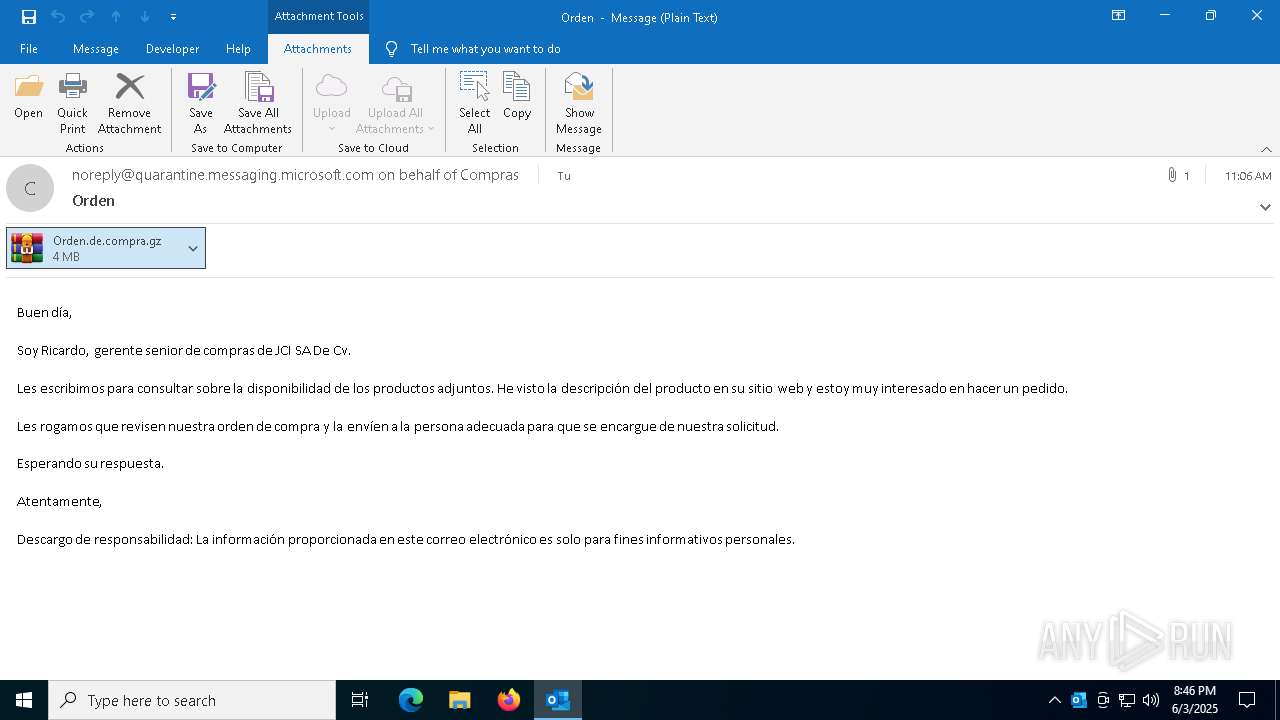
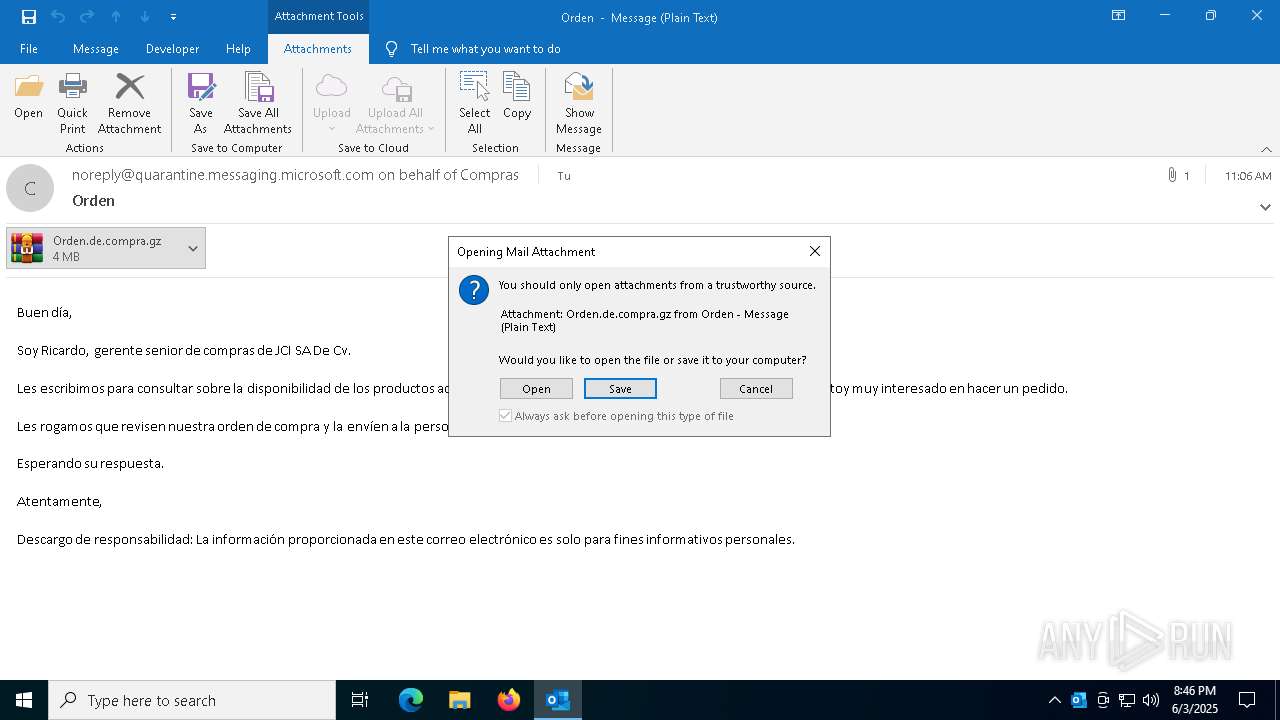
| File name: | Orden.eml |
| Full analysis: | https://app.any.run/tasks/d68be928-2c62-4cd1-987e-3baef1dafae4 |
| Verdict: | Malicious activity |
| Analysis date: | June 03, 2025, 20:45:37 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | message/rfc822 |
| File info: | RFC 822 mail, ASCII text, with very long lines (358), with CRLF line terminators |
| MD5: | 11E26C106B9BEB879AEA99868F2B56F9 |
| SHA1: | D1FB88431C4D648BD1B78F4562110A60331A4D76 |
| SHA256: | 5C4387F6ECF8A2EF31E55713F4CB90F7AFA114B5DCFC7DD7BB82E7FB088392AD |
| SSDEEP: | 49152:xbAh6KAQIA5pojf3LGpp/n5EQPN6Rgp/kHBShcJ86vn0fP1tz1q/GJBnGn7cKqQF:7 |
MALICIOUS
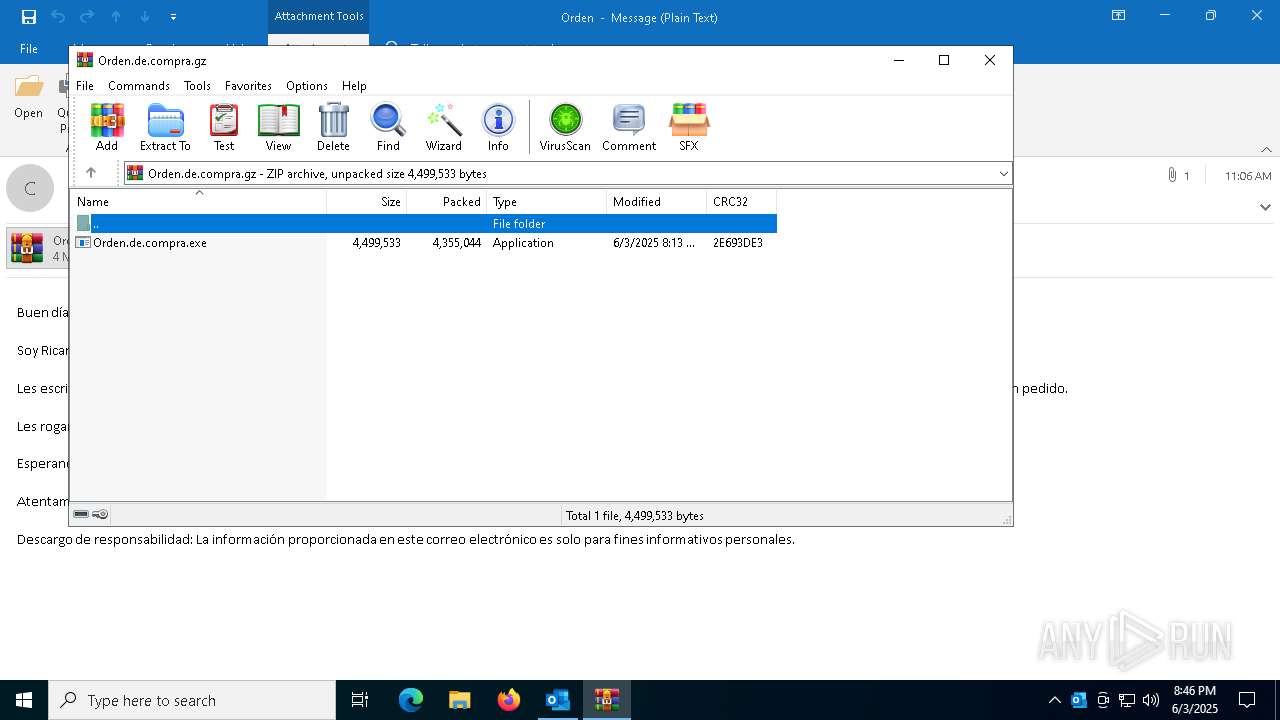
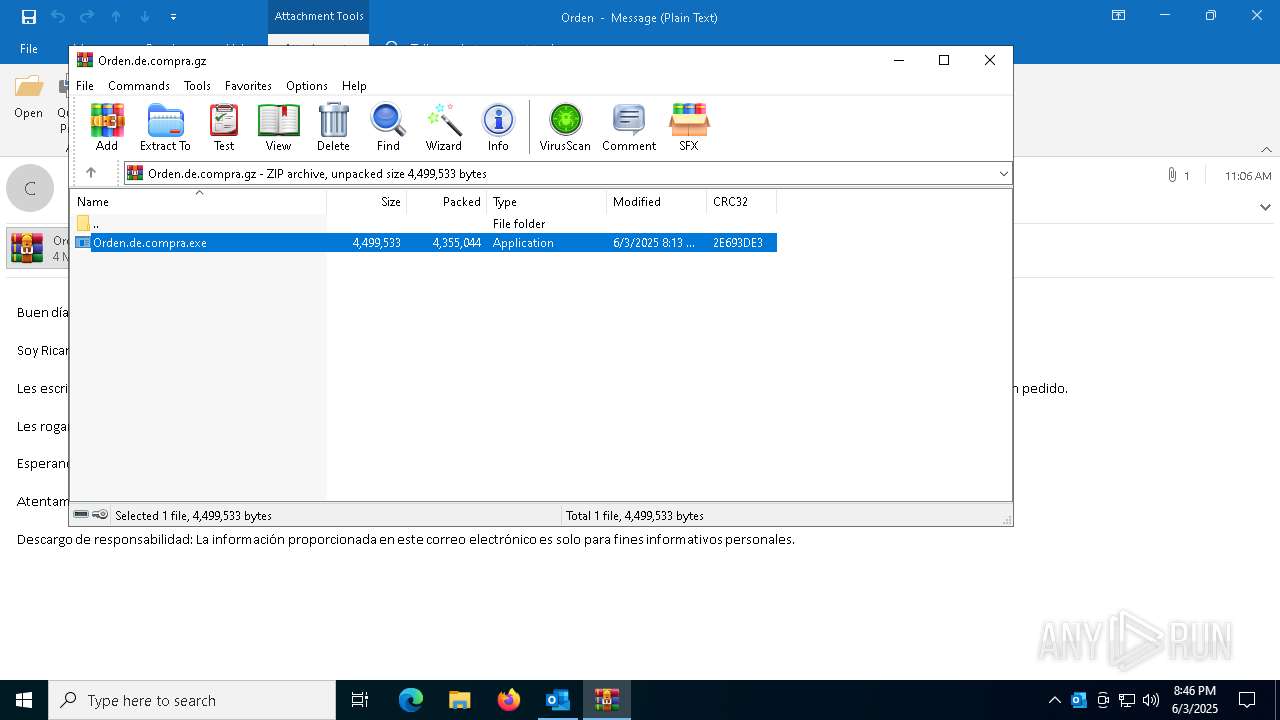
Generic archive extractor
- OUTLOOK.EXE (PID: 7048)
Changes the autorun value in the registry
- asefkjzbf.exe (PID: 7328)
- Client.exe (PID: 456)
SUSPICIOUS
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 8168)
- Orden.de.compra.exe (PID: 5736)
- asefkjzbf.sfx.exe (PID: 4224)
Executable content was dropped or overwritten
- Orden.de.compra.exe (PID: 5736)
- asefkjzbf.sfx.exe (PID: 4224)
- asefkjzbf.exe (PID: 7328)
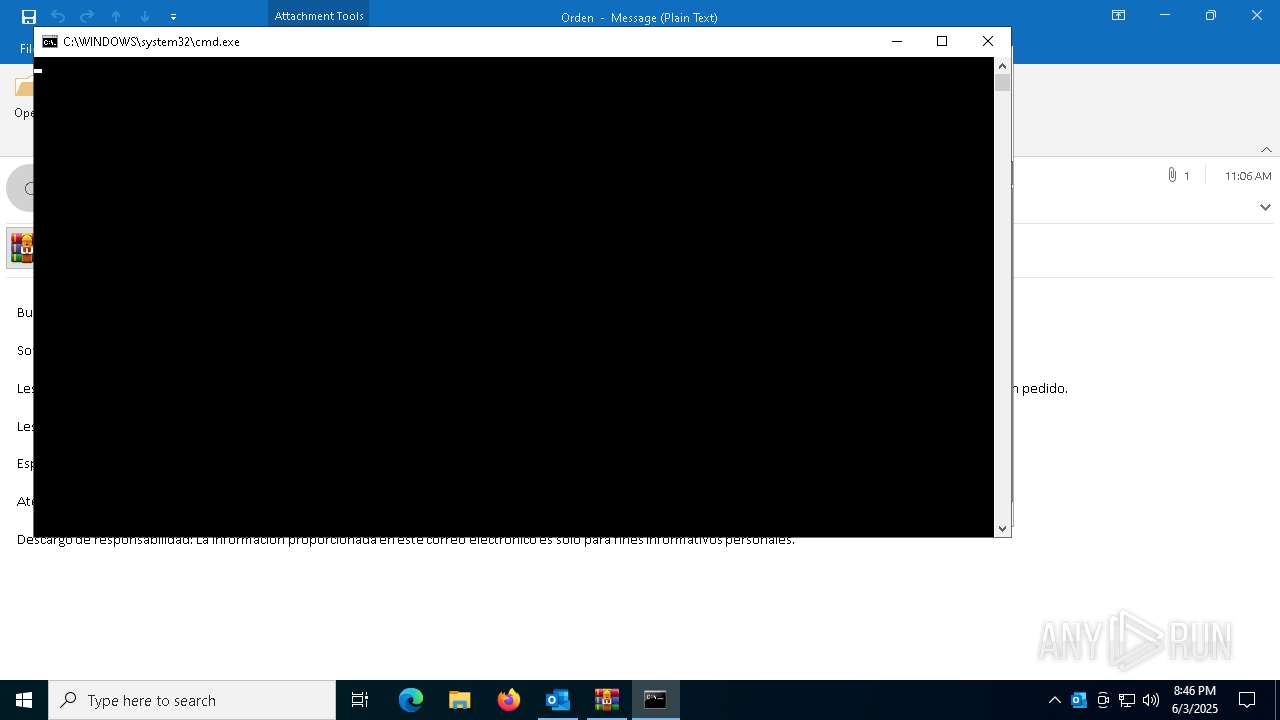
Starts CMD.EXE for commands execution
- Orden.de.compra.exe (PID: 5736)
The executable file from the user directory is run by the CMD process
- asefkjzbf.sfx.exe (PID: 4224)
Executing commands from a ".bat" file
- Orden.de.compra.exe (PID: 5736)
Starts itself from another location
- asefkjzbf.exe (PID: 7328)
Application launched itself
- Client.exe (PID: 3132)
- asefkjzbf.exe (PID: 5416)
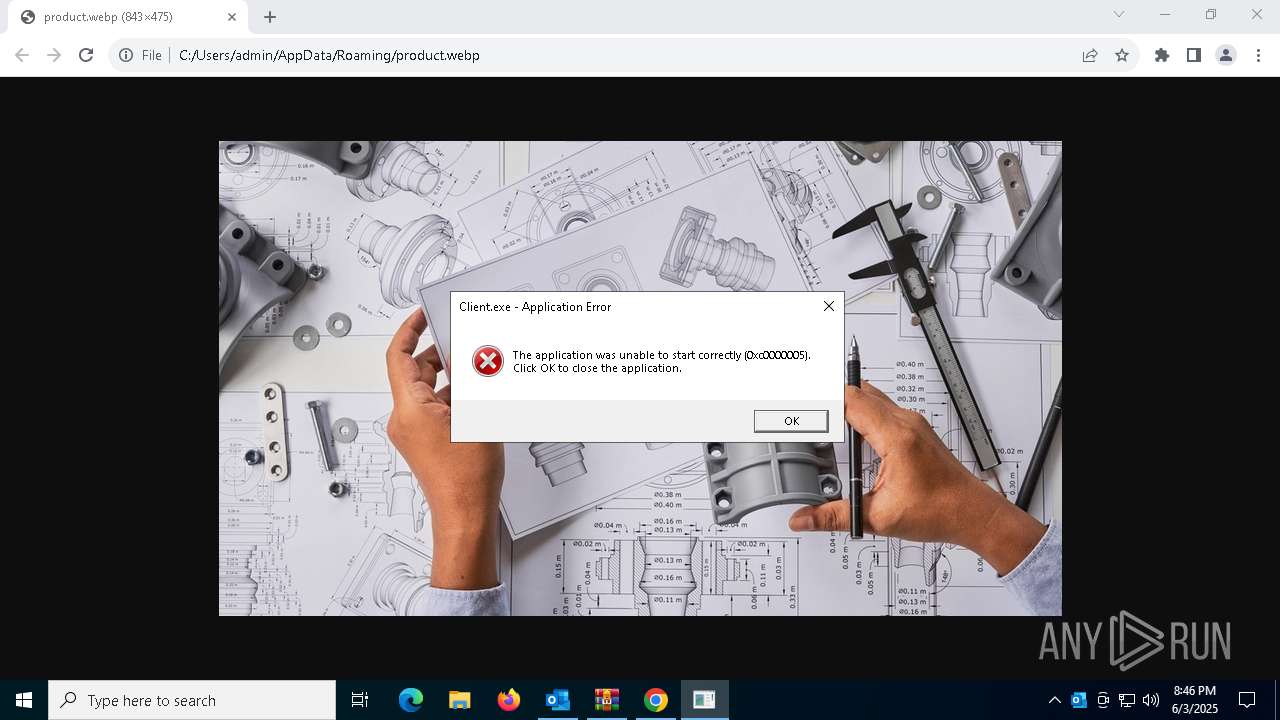
Executes application which crashes
- Client.exe (PID: 2384)
Connects to unusual port
- Client.exe (PID: 456)
INFO
Executable content was dropped or overwritten
- WinRAR.exe (PID: 8168)
Creates files or folders in the user directory
- Orden.de.compra.exe (PID: 5736)
- asefkjzbf.sfx.exe (PID: 4224)
- asefkjzbf.exe (PID: 7328)
Checks supported languages
- Orden.de.compra.exe (PID: 5736)
- asefkjzbf.sfx.exe (PID: 4224)
- asefkjzbf.exe (PID: 5416)
- Client.exe (PID: 3132)
- asefkjzbf.exe (PID: 3896)
- asefkjzbf.exe (PID: 7328)
- Client.exe (PID: 456)
Reads the computer name
- Orden.de.compra.exe (PID: 5736)
- asefkjzbf.sfx.exe (PID: 4224)
- asefkjzbf.exe (PID: 5416)
- asefkjzbf.exe (PID: 7328)
- asefkjzbf.exe (PID: 3896)
- Client.exe (PID: 3132)
- Client.exe (PID: 456)
Process checks computer location settings
- Orden.de.compra.exe (PID: 5736)
- asefkjzbf.sfx.exe (PID: 4224)
Application launched itself
- chrome.exe (PID: 7724)
Reads the machine GUID from the registry
- asefkjzbf.exe (PID: 5416)
- asefkjzbf.exe (PID: 3896)
- asefkjzbf.exe (PID: 7328)
- Client.exe (PID: 3132)
- Client.exe (PID: 456)
Launching a file from a Registry key
- asefkjzbf.exe (PID: 7328)
- Client.exe (PID: 456)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .eml | | | E-Mail message (Var. 5) (100) |
|---|
Total processes
169
Monitored processes
39
Malicious processes
1
Suspicious processes
5
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 456 | C:\Users\admin\AppData\Roaming\SubDir\Client.exe | C:\Users\admin\AppData\Roaming\SubDir\Client.exe | Client.exe | ||||||||||||
User: admin Company: Microsoft, Corporation Integrity Level: MEDIUM Description: License Authenticator Version: 6.8.8.8 Modules
| |||||||||||||||
| 668 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=storage.mojom.StorageService --lang=en-US --service-sandbox-type=service --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=2264 --field-trial-handle=1808,i,1850209526633834312,5852551538275275048,262144 --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Version: 122.0.6261.70 Modules
| |||||||||||||||
| 780 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=5680 --field-trial-handle=1808,i,1850209526633834312,5852551538275275048,262144 --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 1164 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1168 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=quarantine.mojom.Quarantine --lang=en-US --service-sandbox-type=none --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=5824 --field-trial-handle=1808,i,1850209526633834312,5852551538275275048,262144 --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 1328 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=quarantine.mojom.Quarantine --lang=en-US --service-sandbox-type=none --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=5748 --field-trial-handle=1808,i,1850209526633834312,5852551538275275048,262144 --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 2124 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=quarantine.mojom.Quarantine --lang=en-US --service-sandbox-type=none --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=5892 --field-trial-handle=1808,i,1850209526633834312,5852551538275275048,262144 --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 2384 | C:\Users\admin\AppData\Roaming\SubDir\Client.exe | C:\Users\admin\AppData\Roaming\SubDir\Client.exe | Client.exe | ||||||||||||
User: admin Company: Microsoft, Corporation Integrity Level: MEDIUM Description: License Authenticator Version: 6.8.8.8 Modules
| |||||||||||||||
| 3132 | "C:\Users\admin\AppData\Roaming\SubDir\Client.exe" | C:\Users\admin\AppData\Roaming\SubDir\Client.exe | — | asefkjzbf.exe | |||||||||||
User: admin Company: Microsoft, Corporation Integrity Level: MEDIUM Description: License Authenticator Exit code: 0 Version: 6.8.8.8 Modules
| |||||||||||||||
| 3896 | C:\Users\admin\AppData\Roaming\asefkjzbf.exe | C:\Users\admin\AppData\Roaming\asefkjzbf.exe | — | asefkjzbf.exe | |||||||||||
User: admin Company: Microsoft, Corporation Integrity Level: MEDIUM Description: License Authenticator Exit code: 2 Version: 6.8.8.8 Modules
| |||||||||||||||
Total events
25 872
Read events
24 734
Write events
1 016
Delete events
122
Modification events
| (PID) Process: | (7048) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\Common\ClientTelemetry\Sampling |
| Operation: | write | Name: | 6 |
Value: 01941A000000001000B24E9A3E06000000000000000600000000000000 | |||
| (PID) Process: | (7048) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\Common\CrashPersistence\OUTLOOK\7048 |
| Operation: | write | Name: | 0 |
Value: 0B0E100E874602EB078B42AD50EFC66DAF6A902300469CB9EFE28799F5ED016A04102400449A7D64B29D01008500A907556E6B6E6F776EC906022222CA0DC2190000C91003783634C5118837D2120B6F00750074006C006F006F006B002E00650078006500C51620C517808004C91808323231322D44656300 | |||
| (PID) Process: | (7048) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Outlook\Diagnostics |
| Operation: | delete value | Name: | BootCommand |
Value: | |||
| (PID) Process: | (7048) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Outlook\Diagnostics |
| Operation: | delete value | Name: | BootFailureCount |
Value: | |||
| (PID) Process: | (7048) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Outlook\Diagnostics\BootDiagnosticsDataPreviousSession |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (7048) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Outlook\Diagnostics\BootDiagnosticsDataPreviousSession |
| Operation: | write | Name: | CantBootResolution |
Value: BootSuccess | |||
| (PID) Process: | (7048) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Outlook\Diagnostics\BootDiagnosticsDataPreviousSession |
| Operation: | write | Name: | ProfileBeingOpened |
Value: Outlook | |||
| (PID) Process: | (7048) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Outlook\Diagnostics\BootDiagnosticsDataPreviousSession |
| Operation: | write | Name: | SessionId |
Value: C3D8E96E-C1AF-4750-8D52-F4E28119C131 | |||
| (PID) Process: | (7048) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Outlook\Diagnostics\BootDiagnosticsDataPreviousSession |
| Operation: | write | Name: | BootDiagnosticsLogFile |
Value: C:\Users\admin\AppData\Local\Temp\Outlook Logging\OUTLOOK_16_0_16026_20146-20240718T1116060318-1644.etl | |||
| (PID) Process: | (7048) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Outlook\Diagnostics |
| Operation: | delete value | Name: | ProfileBeingOpened |
Value: | |||
Executable files
4
Suspicious files
63
Text files
16
Unknown types
5
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7048 | OUTLOOK.EXE | C:\Users\admin\Documents\Outlook Files\Outlook1.pst | — | |
MD5:— | SHA256:— | |||
| 7048 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\olkF98.tmp | — | |
MD5:— | SHA256:— | |||
| 7724 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF126912.TMP | — | |
MD5:— | SHA256:— | |||
| 7724 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7724 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old~RF126922.TMP | — | |
MD5:— | SHA256:— | |||
| 7724 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7724 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF126932.TMP | — | |
MD5:— | SHA256:— | |||
| 7724 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7724 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Service Worker\Database\LOG.old~RF126941.TMP | — | |
MD5:— | SHA256:— | |||
| 7724 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Service Worker\Database\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
53
DNS requests
30
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4020 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 2.16.168.124:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
4020 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
7048 | OUTLOOK.EXE | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEA77flR%2B3w%2FxBpruV2lte6A%3D | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
7552 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
3896 | RUXIMICS.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5496 | MoUsoCoreWorker.exe | 2.16.168.124:80 | crl.microsoft.com | Akamai International B.V. | RU | whitelisted |
5496 | MoUsoCoreWorker.exe | 2.23.246.101:80 | www.microsoft.com | Ooredoo Q.S.C. | QA | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
7048 | OUTLOOK.EXE | 52.123.129.14:443 | ecs.office.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7048 | OUTLOOK.EXE | 2.16.168.206:443 | omex.cdn.office.net | Akamai International B.V. | RU | whitelisted |
7048 | OUTLOOK.EXE | 52.111.236.4:443 | messaging.lifecycle.office.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
ecs.office.com |
| whitelisted |
omex.cdn.office.net |
| whitelisted |
messaging.lifecycle.office.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2196 | svchost.exe | Misc activity | INFO [ANY.RUN] Dynamic DNS Service (ydns .eu) |
456 | Client.exe | Misc Attack | ET DROP Spamhaus DROP Listed Traffic Inbound group 43 |
2196 | svchost.exe | Misc activity | INFO [ANY.RUN] Dynamic DNS Service (ydns .eu) |