| File name: | gpedit.exe |
| Full analysis: | https://app.any.run/tasks/de14089c-85ee-4388-8660-2b79b11e93f5 |
| Verdict: | Malicious activity |
| Analysis date: | June 06, 2024, 17:12:26 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 43D3FF349AD31E0AD76201755445CB1E |
| SHA1: | 7B3B15C369203CF892FB0B023201C5627E23973A |
| SHA256: | 5C402FD8244E177338A2A8F0C7B8DF055D5A06EBD7A5225EDB3D3CDAF1D1C749 |
| SSDEEP: | 49152:2lrceNxKawdLEqGu/r/hrmYLDs6kIDN5nxsBt0cqHyVsTbx9qOUDkkJ28Sv01xcP:gnNx8tGcrcIInIDNdxotJc8sTbx9qOU+ |
MALICIOUS
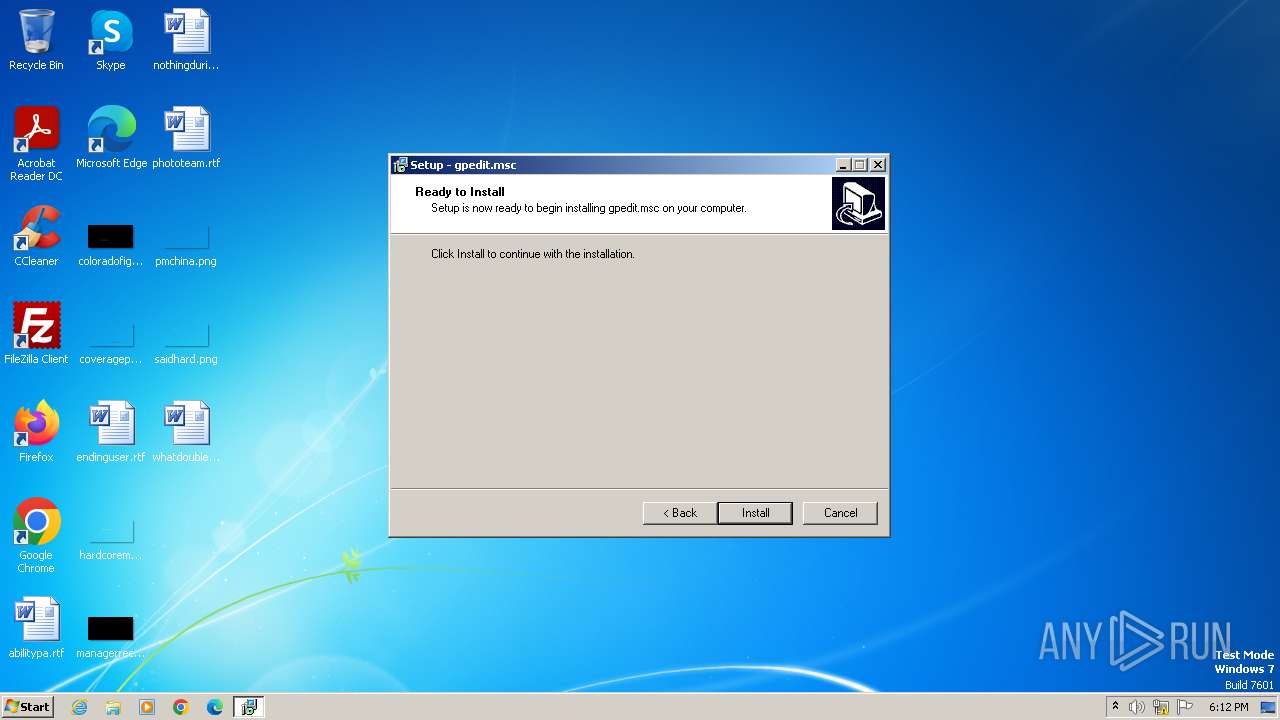
Drops the executable file immediately after the start
- gpedit.exe (PID: 3980)
- gpedit.exe (PID: 2104)
- gpedit.tmp (PID: 2108)
- cmd.exe (PID: 2028)
Creates a writable file in the system directory
- cmd.exe (PID: 2028)
Registers / Runs the DLL via REGSVR32.EXE
- cmd.exe (PID: 2028)
SUSPICIOUS
Executable content was dropped or overwritten
- gpedit.exe (PID: 3980)
- gpedit.exe (PID: 2104)
- gpedit.tmp (PID: 2108)
- cmd.exe (PID: 2028)
Process drops legitimate windows executable
- gpedit.tmp (PID: 2108)
- cmd.exe (PID: 2028)
Reads the Windows owner or organization settings
- gpedit.tmp (PID: 2108)
Reads the Internet Settings
- installer.exe (PID: 1064)
Reads security settings of Internet Explorer
- installer.exe (PID: 1064)
Takes ownership (TAKEOWN.EXE)
- cmd.exe (PID: 2028)
Executing commands from a ".bat" file
- installer.exe (PID: 1064)
Starts CMD.EXE for commands execution
- installer.exe (PID: 1064)
Uses ICACLS.EXE to modify access control lists
- cmd.exe (PID: 2028)
The process creates files with name similar to system file names
- cmd.exe (PID: 2028)
Creates/Modifies COM task schedule object
- regsvr32.exe (PID: 2008)
- regsvr32.exe (PID: 768)
INFO
Create files in a temporary directory
- gpedit.exe (PID: 3980)
- gpedit.exe (PID: 2104)
- gpedit.tmp (PID: 2108)
Checks supported languages
- gpedit.tmp (PID: 3996)
- gpedit.exe (PID: 3980)
- gpedit.exe (PID: 2104)
- gpedit.tmp (PID: 2108)
- installer.exe (PID: 1064)
Reads the computer name
- gpedit.tmp (PID: 3996)
- gpedit.tmp (PID: 2108)
- installer.exe (PID: 1064)
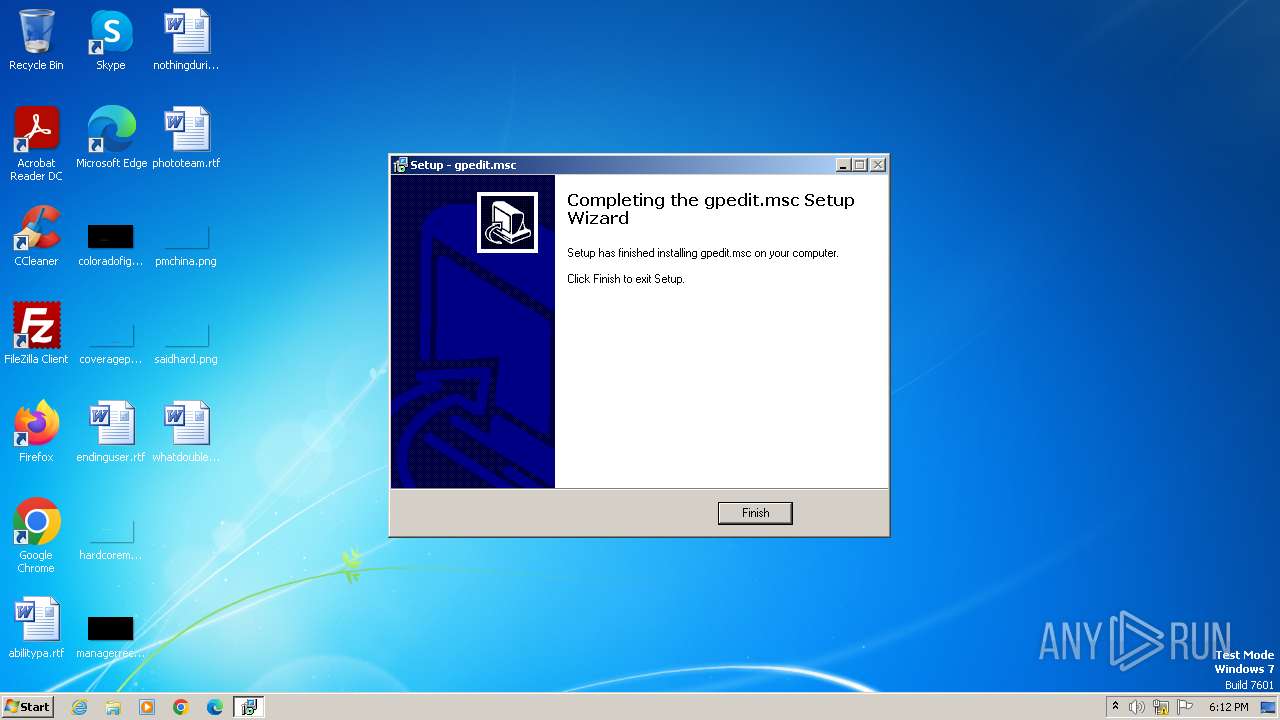
Creates a software uninstall entry
- gpedit.tmp (PID: 2108)
Reads Environment values
- installer.exe (PID: 1064)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Inno Setup installer (77.7) |
|---|---|---|
| .exe | | | Win32 Executable Delphi generic (10) |
| .dll | | | Win32 Dynamic Link Library (generic) (4.6) |
| .exe | | | Win32 Executable (generic) (3.1) |
| .exe | | | Win16/32 Executable Delphi generic (1.4) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 1992:06:19 22:22:17+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, Bytes reversed lo, 32-bit, Bytes reversed hi |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 37888 |
| InitializedDataSize: | 17920 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x9b24 |
| OSVersion: | 1 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 0.0.0.0 |
| ProductVersionNumber: | 0.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
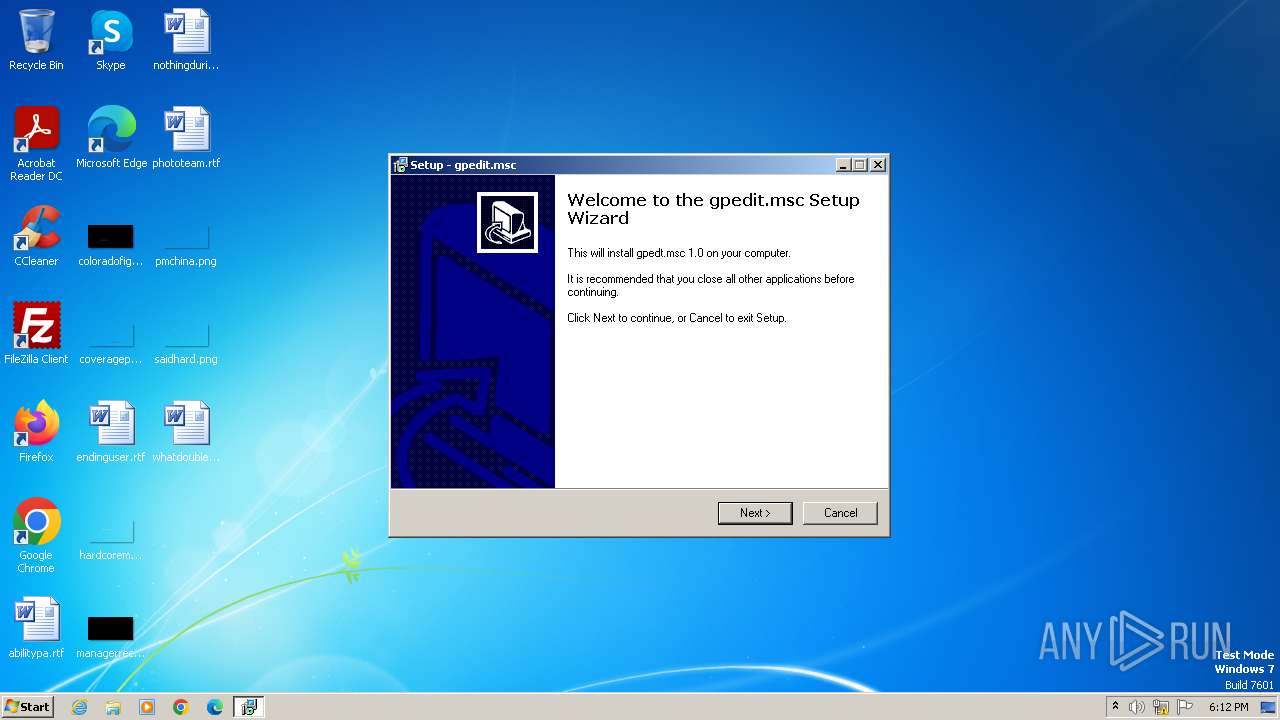
| Comments: | This installation was built with Inno Setup. |
| CompanyName: | Richard |
| FileDescription: | gpedit.msc Setup |
| FileVersion: | |
| LegalCopyright: | |
| ProductName: | gpedit.msc |
| ProductVersion: |
Total processes
58
Monitored processes
23
Malicious processes
6
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 304 | icacls C:\Windows\System32\gptext.dll /grant:r admin:f | C:\Windows\System32\icacls.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 316 | takeown /f C:\Windows\System32\appmgr.dll | C:\Windows\System32\takeown.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Takes ownership of a file Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 692 | takeown /f C:\Windows\System32\GPBAK\* | C:\Windows\System32\takeown.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Takes ownership of a file Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 768 | regsvr32 /s C:\Windows\System32\gpedit.dll | C:\Windows\System32\regsvr32.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft(C) Register Server Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1056 | icacls C:\Windows\System32\appmgr.dll /grant:r admin:f | C:\Windows\System32\icacls.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1064 | "C:\Windows\Temp\gpedit\installer.exe" | C:\Windows\Temp\gpedit\installer.exe | — | gpedit.tmp | |||||||||||
User: admin Integrity Level: HIGH Description: Installer Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 1132 | regsvr32 /s C:\Windows\System32\fdeploy.dll | C:\Windows\System32\regsvr32.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft(C) Register Server Exit code: 3 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1184 | takeown /f C:\Windows\System32\gpedit.dll | C:\Windows\System32\takeown.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Takes ownership of a file Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1236 | icacls C:\Windows\System32\fdeploy.dll /grant:r admin:f | C:\Windows\System32\icacls.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1604 | icacls C:\Windows\System32\GPBAK\* /grant:r admin:f | C:\Windows\System32\icacls.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
6 704
Read events
6 584
Write events
120
Delete events
0
Modification events
| (PID) Process: | (2108) gpedit.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\{10B9C608-BF7C-4CCF-A658-C01D969DCA21}_is1 |
| Operation: | write | Name: | Inno Setup: Setup Version |
Value: 5.3.7 (a) | |||
| (PID) Process: | (2108) gpedit.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\{10B9C608-BF7C-4CCF-A658-C01D969DCA21}_is1 |
| Operation: | write | Name: | Inno Setup: App Path |
Value: | |||
| (PID) Process: | (2108) gpedit.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\{10B9C608-BF7C-4CCF-A658-C01D969DCA21}_is1 |
| Operation: | write | Name: | Inno Setup: Icon Group |
Value: (Default) | |||
| (PID) Process: | (2108) gpedit.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\{10B9C608-BF7C-4CCF-A658-C01D969DCA21}_is1 |
| Operation: | write | Name: | Inno Setup: User |
Value: admin | |||
| (PID) Process: | (2108) gpedit.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\{10B9C608-BF7C-4CCF-A658-C01D969DCA21}_is1 |
| Operation: | write | Name: | DisplayName |
Value: gpedt.msc 1.0 | |||
| (PID) Process: | (2108) gpedit.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\{10B9C608-BF7C-4CCF-A658-C01D969DCA21}_is1 |
| Operation: | write | Name: | UninstallString |
Value: "C:\Windows\unins000.exe" | |||
| (PID) Process: | (2108) gpedit.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\{10B9C608-BF7C-4CCF-A658-C01D969DCA21}_is1 |
| Operation: | write | Name: | QuietUninstallString |
Value: "C:\Windows\unins000.exe" /SILENT | |||
| (PID) Process: | (2108) gpedit.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\{10B9C608-BF7C-4CCF-A658-C01D969DCA21}_is1 |
| Operation: | write | Name: | Publisher |
Value: Richard | |||
| (PID) Process: | (2108) gpedit.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\{10B9C608-BF7C-4CCF-A658-C01D969DCA21}_is1 |
| Operation: | write | Name: | URLInfoAbout |
Value: http://www.vistax64.com/member.php?u=151549 | |||
| (PID) Process: | (2108) gpedit.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\{10B9C608-BF7C-4CCF-A658-C01D969DCA21}_is1 |
| Operation: | write | Name: | HelpLink |
Value: http://www.vistax64.com/member.php?u=151549 | |||
Executable files
30
Suspicious files
1
Text files
22
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2108 | gpedit.tmp | C:\Windows\Temp\gpedit\appmgr.dll | executable | |
MD5:76422D781C0FBBB368F8559DC12A39B1 | SHA256:2613B7E843D0AD5959A74D2B2601F5E981E8E1FDC39A44DA175AB076C08839A3 | |||
| 2108 | gpedit.tmp | C:\Windows\Temp\gpedit\is-KTI9P.tmp | executable | |
MD5:CBA0BE94E3985F6DB7701E259C73B43B | SHA256:A1F26B60132F7DB711140B4F170BD3A9C92053BF178BEF6D5809E12C483BF7FC | |||
| 2108 | gpedit.tmp | C:\Windows\Temp\gpedit\fdeploy.dll | executable | |
MD5:5E12974F81FAE8F695E2B4EA05418AF3 | SHA256:5F6331AF5E4159A48A5F2DA6C9B52C970564F58FC5A889CBCB90F9EDCA011D90 | |||
| 2108 | gpedit.tmp | C:\Windows\Temp\gpedit\is-GRVSQ.tmp | executable | |
MD5:5E12974F81FAE8F695E2B4EA05418AF3 | SHA256:5F6331AF5E4159A48A5F2DA6C9B52C970564F58FC5A889CBCB90F9EDCA011D90 | |||
| 2108 | gpedit.tmp | C:\Windows\Temp\gpedit\gpedit.dll | executable | |
MD5:65F8DA8424AD27A365F61CCC8621FED2 | SHA256:92BEBA4934D0263FD21827CC96E02689DA9ABAED571FE88836B3469F70D4A28E | |||
| 2108 | gpedit.tmp | C:\Windows\Temp\gpedit\is-F0PKA.tmp | executable | |
MD5:65F8DA8424AD27A365F61CCC8621FED2 | SHA256:92BEBA4934D0263FD21827CC96E02689DA9ABAED571FE88836B3469F70D4A28E | |||
| 2104 | gpedit.exe | C:\Users\admin\AppData\Local\Temp\is-JP8MR.tmp\gpedit.tmp | executable | |
MD5:E60A74A65005E4C4F61CBE9C09D368DF | SHA256:78F6692D50D07BD78A97294D196F9AE7D1FC48B058375E5D7BB766970FAAB758 | |||
| 3980 | gpedit.exe | C:\Users\admin\AppData\Local\Temp\is-593B2.tmp\gpedit.tmp | executable | |
MD5:E60A74A65005E4C4F61CBE9C09D368DF | SHA256:78F6692D50D07BD78A97294D196F9AE7D1FC48B058375E5D7BB766970FAAB758 | |||
| 2108 | gpedit.tmp | C:\Windows\Temp\gpedit\is-MEOQL.tmp | executable | |
MD5:D8849F77C0B66226335A59D26CB4EDC6 | SHA256:4990031453204C57E36E850252A39B05D6ECDAB9E71A8136FB4900F17E59C9CA | |||
| 2108 | gpedit.tmp | C:\Windows\Temp\gpedit\conf.adm | text | |
MD5:6C2422F9265D2EAD5CFB47540BD46C71 | SHA256:3C21ED1D9EE8DE426D9DD329499CE4EB9CC24122AEA61694FCFE9115C0EA2EA7 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
4
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1088 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |