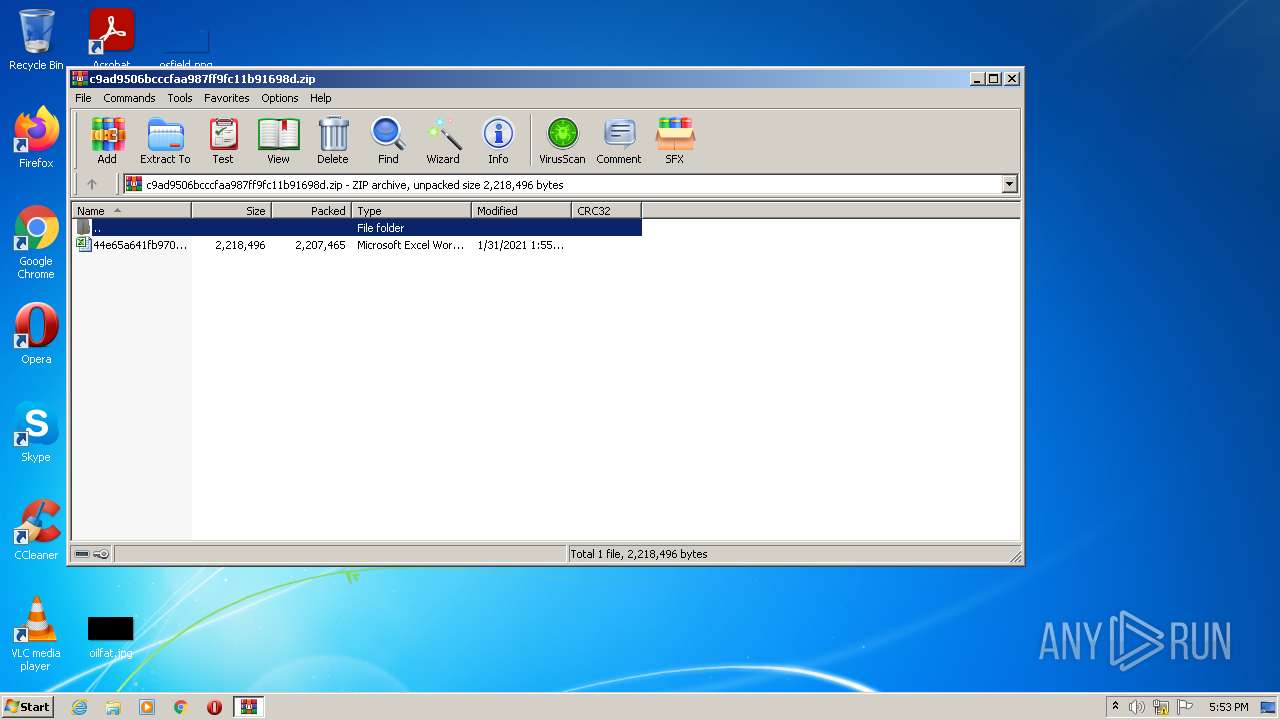
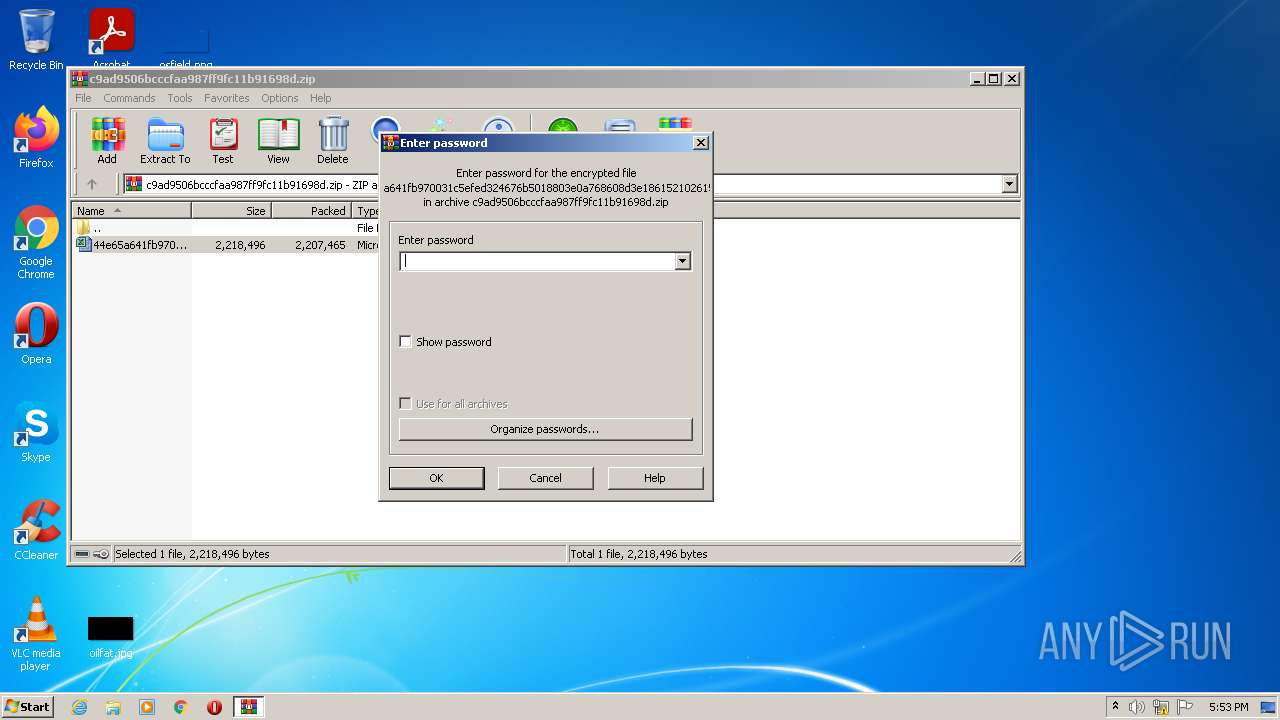
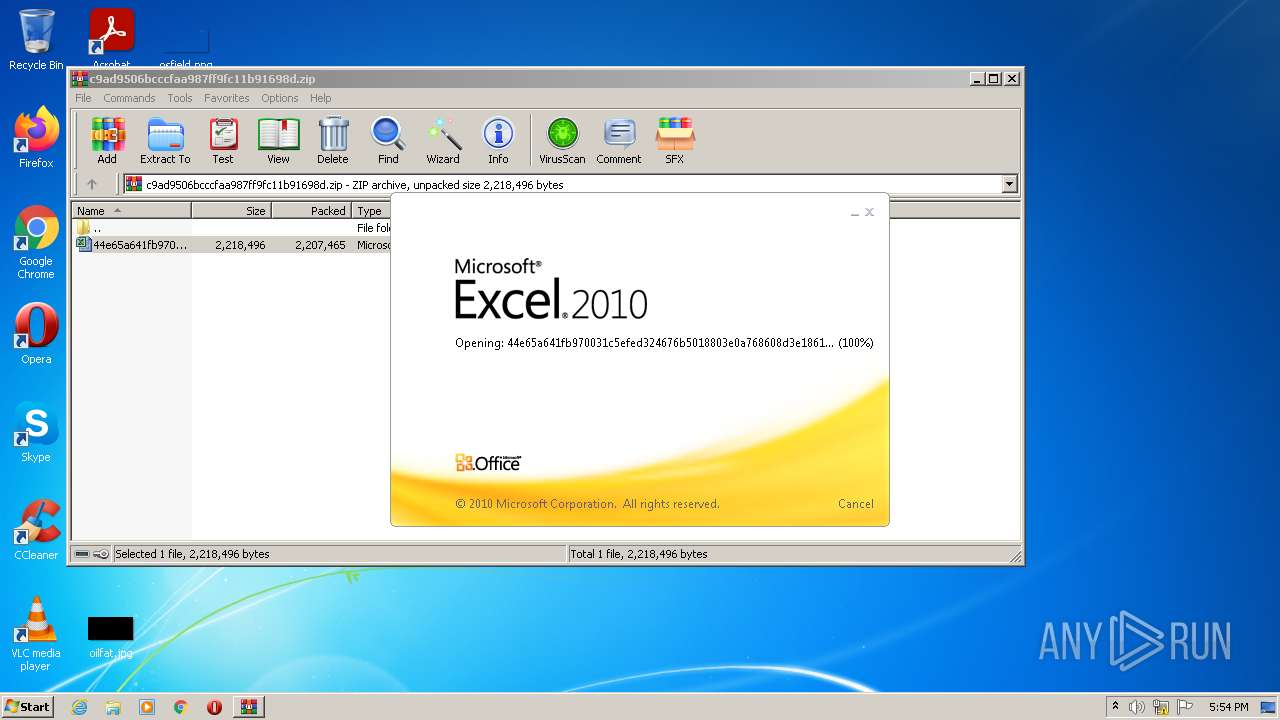
| File name: | c9ad9506bcccfaa987ff9fc11b91698d.zip |
| Full analysis: | https://app.any.run/tasks/8706199d-d3c6-445e-a272-2b439aca3321 |
| Verdict: | Malicious activity |
| Analysis date: | December 05, 2022, 17:53:25 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v5.1 to extract |
| MD5: | 6FDF4A6DDD6F564589DD060BDC4DA2C3 |
| SHA1: | 68B34A47861C76B9544ADDCC2F8217EF249F4773 |
| SHA256: | 5C34C14865F4A98F6CC623710E445F479175AEAFAFCB55614B139FB61CFF9DE7 |
| SSDEEP: | 49152:K1Sbs3khfrYYv4IVKmJ5ucb8K/U0gmY9XzPJeR2tgUbUuBwdip3HvD3DF/:YSbRfr2IVKmJ5ucfLMTJvgU4ldip3fx |
MALICIOUS
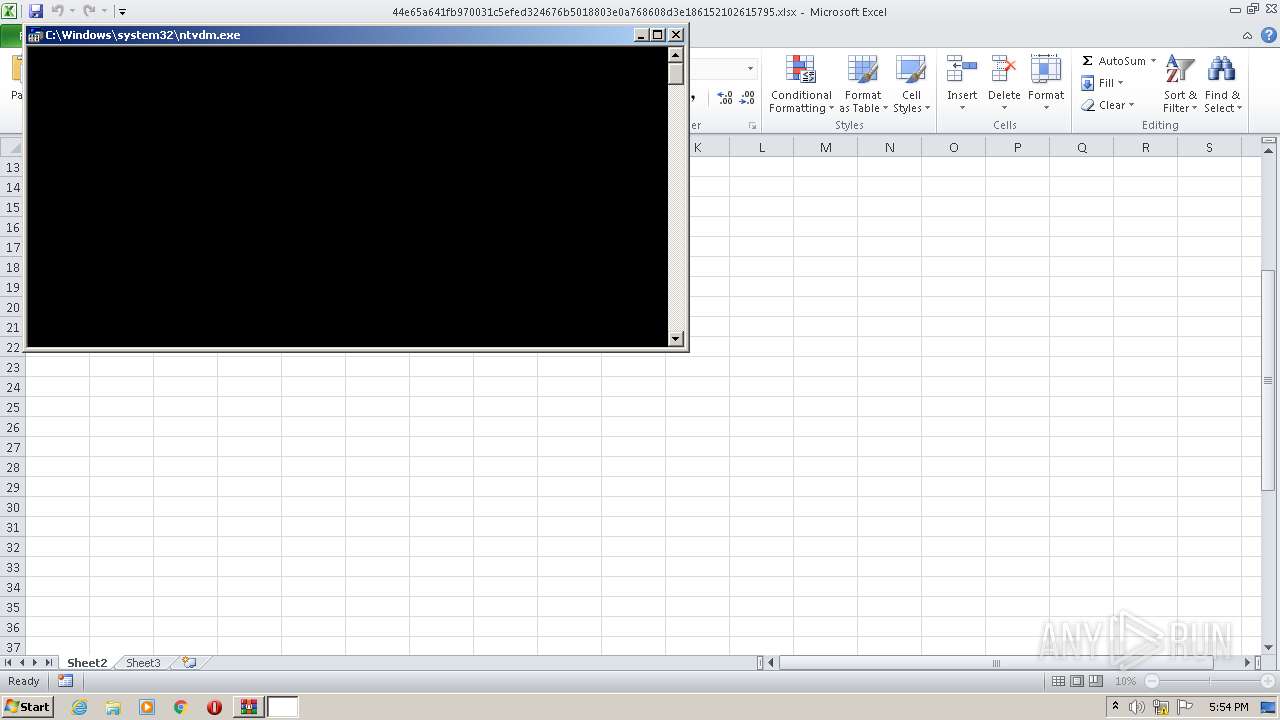
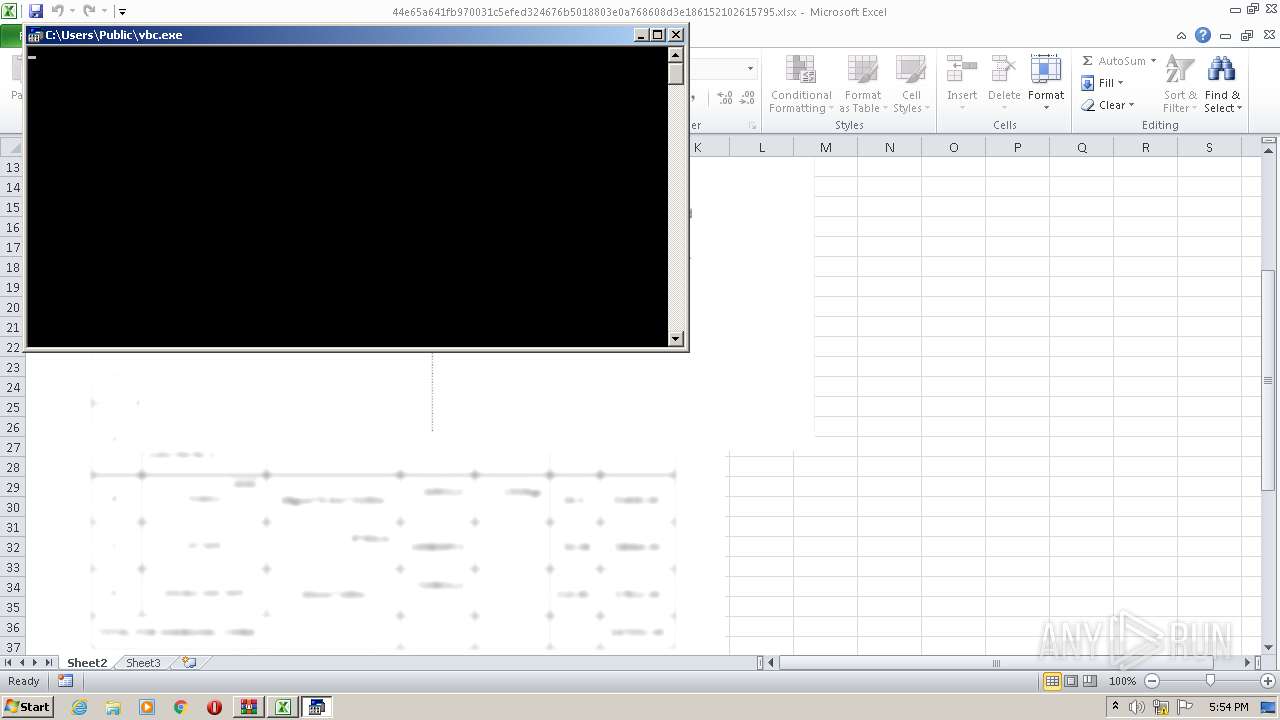
Equation Editor starts application (CVE-2017-11882)
- EQNEDT32.EXE (PID: 2268)
Suspicious connection from the Equation Editor
- EQNEDT32.EXE (PID: 2268)
SUSPICIOUS
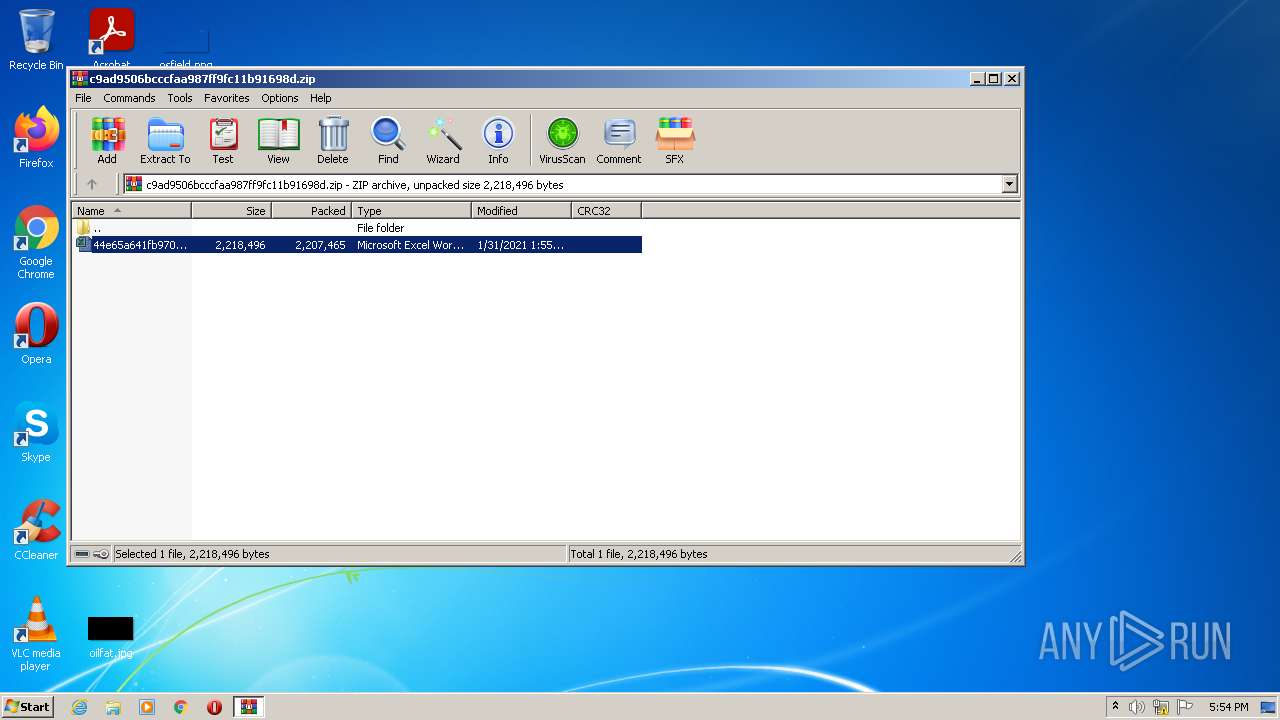
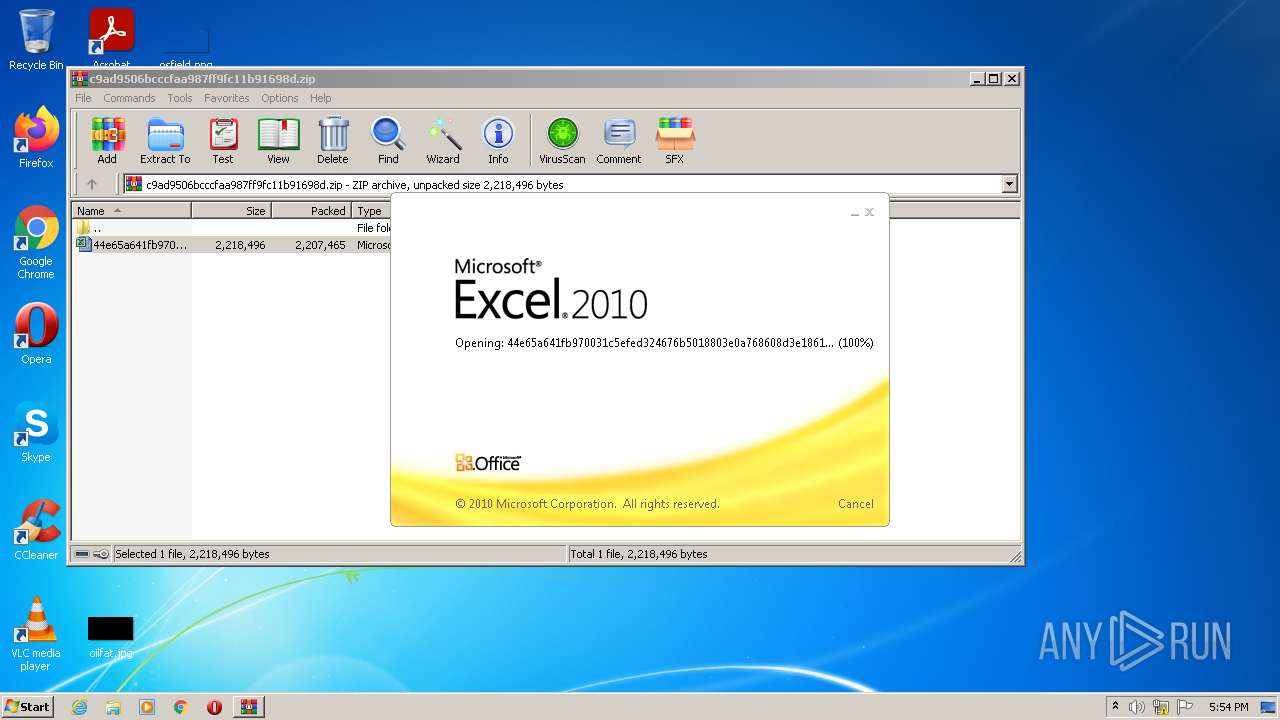
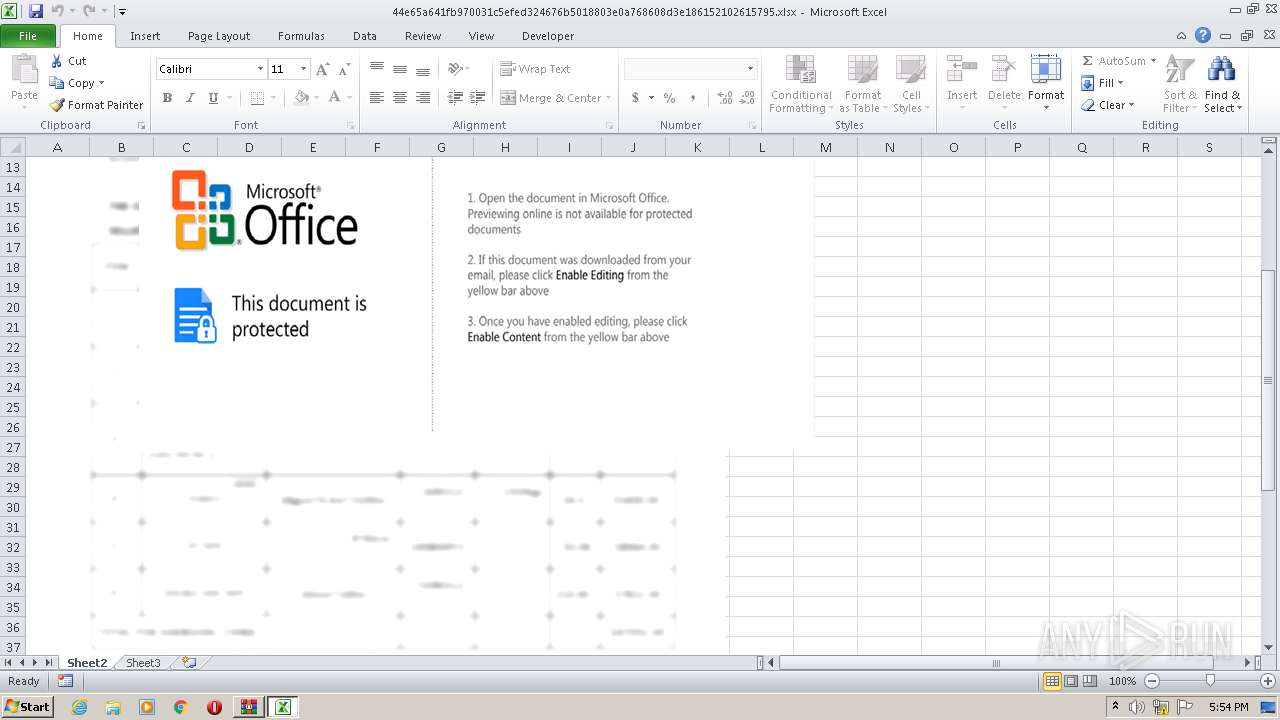
Starts Microsoft Office Application
- WinRAR.exe (PID: 1860)
Reads the Internet Settings
- EQNEDT32.EXE (PID: 2268)
Process requests binary or script from the Internet
- EQNEDT32.EXE (PID: 2268)
INFO
Reads Microsoft Office registry keys
- WinRAR.exe (PID: 1860)
Dropped object may contain Bitcoin addresses
- EXCEL.EXE (PID: 3744)
Checks supported languages
- EQNEDT32.EXE (PID: 2268)
Reads the computer name
- EQNEDT32.EXE (PID: 2268)
Checks proxy server information
- EQNEDT32.EXE (PID: 2268)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
Total processes
39
Monitored processes
4
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1860 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\c9ad9506bcccfaa987ff9fc11b91698d.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 2268 | "C:\Program Files\Common Files\Microsoft Shared\EQUATION\EQNEDT32.EXE" -Embedding | C:\Program Files\Common Files\Microsoft Shared\EQUATION\EQNEDT32.EXE | svchost.exe | ||||||||||||
User: admin Company: Design Science, Inc. Integrity Level: MEDIUM Description: Microsoft Equation Editor Exit code: 0 Version: 00110900 Modules
| |||||||||||||||
| 2940 | "C:\Windows\system32\ntvdm.exe" -i1 | C:\Windows\system32\ntvdm.exe | — | EQNEDT32.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: NTVDM.EXE Exit code: 3221225477 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3744 | "C:\Program Files\Microsoft Office\Office14\EXCEL.EXE" /dde | C:\Program Files\Microsoft Office\Office14\EXCEL.EXE | — | WinRAR.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Excel Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
Total events
2 934
Read events
2 840
Write events
83
Delete events
11
Modification events
| (PID) Process: | (1860) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (1860) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (1860) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\16C\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
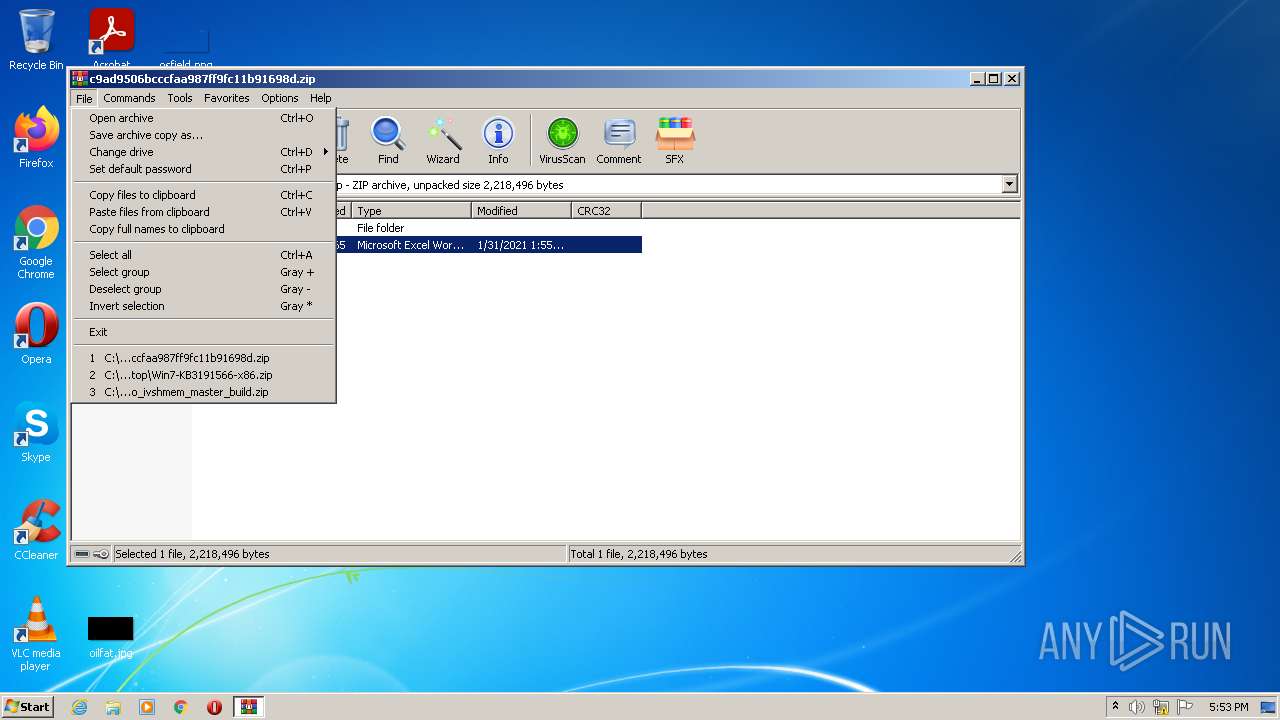
| (PID) Process: | (1860) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\virtio_ivshmem_master_build.zip | |||
| (PID) Process: | (1860) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\Win7-KB3191566-x86.zip | |||
| (PID) Process: | (1860) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\c9ad9506bcccfaa987ff9fc11b91698d.zip | |||
| (PID) Process: | (1860) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (1860) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (1860) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (1860) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
Executable files
0
Suspicious files
1
Text files
5
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3744 | EXCEL.EXE | C:\Users\admin\AppData\Local\Temp\CVR653F.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 1860 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DIb1860.32176\44e65a641fb970031c5efed324676b5018803e0a768608d3e186152102615795.xlsx | binary | |
MD5:C9AD9506BCCCFAA987FF9FC11B91698D | SHA256:44E65A641FB970031C5EFED324676B5018803E0A768608D3E186152102615795 | |||
| 2940 | ntvdm.exe | C:\Users\admin\AppData\Local\Temp\scs75F9.tmp | text | |
MD5:4C361DEA398F7AEEF49953BDC0AB4A9B | SHA256:06D61C23E6CA59B9DDAD1796ECCC42C032CD8F6F424AF6CFEE5D085D36FF7DFD | |||
| 3744 | EXCEL.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\8CF15C0D.emf | emf | |
MD5:0FA392C202F7506D4532E08F3D1419D0 | SHA256:B7B48D3DE9EF45C190AF926E384385003DE89848FC2A38A11001B8040589A5C1 | |||
| 2268 | EQNEDT32.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\PO2HN1X2\network[1].htm | html | |
MD5:06A1AC2F557B27281AFC326894F9B593 | SHA256:F61B4BAB3131CD843C7044D4B3FF89F3929EF038275DF1B0FA4B498DBCC9642E | |||
| 2268 | EQNEDT32.EXE | C:\Users\Public\vbc.exe | html | |
MD5:E2BDAD32EE840A09F97430DAFB4F882C | SHA256:3B97ADAD5CC1D0CBB9DDF29E19782F61903BFCB706A9EAAEB8F4805D7E001B7B | |||
| 2940 | ntvdm.exe | C:\Users\admin\AppData\Local\Temp\scs75F8.tmp | text | |
MD5:8CF6DDB5AA59B49F34B967CD46F013B6 | SHA256:EE06792197C3E025B84860A72460EAF628C66637685F8C52C5A08A9CC35D376C | |||
| 2268 | EQNEDT32.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\B6QGX7LP\ILF05I8K.htm | html | |
MD5:E2BDAD32EE840A09F97430DAFB4F882C | SHA256:3B97ADAD5CC1D0CBB9DDF29E19782F61903BFCB706A9EAAEB8F4805D7E001B7B | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
2
DNS requests
3
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2268 | EQNEDT32.EXE | GET | 302 | 70.38.21.229:80 | http://andaluciabeach.net/image/network.exe | CA | html | 214 b | suspicious |
2268 | EQNEDT32.EXE | GET | 200 | 70.38.21.229:80 | http://www.andaluciabeach.net/ | CA | html | 216 b | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2268 | EQNEDT32.EXE | 70.38.21.229:80 | andaluciabeach.net | IWEB-AS | CA | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
andaluciabeach.net |
| suspicious |
www.andaluciabeach.net |
| suspicious |