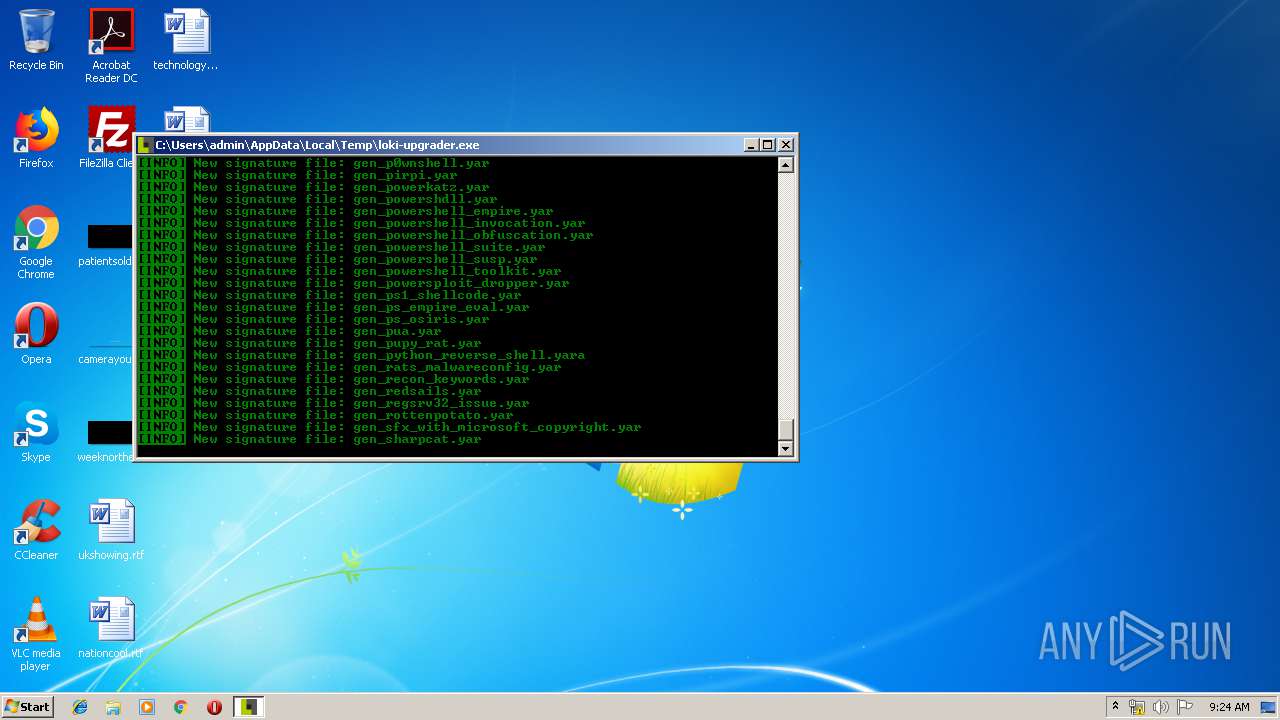
| File name: | loki-upgrader.exe |
| Full analysis: | https://app.any.run/tasks/a400f238-3743-4f16-8987-015f02e483e9 |
| Verdict: | No threats detected |
| Analysis date: | April 25, 2019, 08:23:35 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (console) Intel 80386, for MS Windows |
| MD5: | D267E21A68508A58D09D19250AF4B56E |
| SHA1: | 3EE09E5BDB3E1FFAF8FBA9B727239105B582129E |
| SHA256: | 5C2F5E09959DD47108BF5B77DAEF3D1DA6966DF777A88D755B44D0BF0B442EAC |
| SSDEEP: | 196608:Z1wMlVBuYCZHV8efWYBhOkWz8xZo9EmoApbpSzZTfubZB:9FuYCKefWDkWAxTxzZf |
MALICIOUS
Loads dropped or rewritten executable
- loki-upgrader.exe (PID: 2736)
SUSPICIOUS
Executable content was dropped or overwritten
- loki-upgrader.exe (PID: 916)
- loki-upgrader.exe (PID: 2736)
Loads Python modules
- loki-upgrader.exe (PID: 2736)
INFO
Dropped object may contain TOR URL's
- loki-upgrader.exe (PID: 2736)
Dropped object may contain Bitcoin addresses
- loki-upgrader.exe (PID: 2736)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (67.4) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (14.2) |
| .exe | | | Win32 Executable (generic) (9.7) |
| .exe | | | Generic Win/DOS Executable (4.3) |
| .exe | | | DOS Executable Generic (4.3) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2013:03:23 23:26:54+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 9 |
| CodeSize: | 105472 |
| InitializedDataSize: | 137216 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xb2f7 |
| OSVersion: | 5 |
| ImageVersion: | - |
| SubsystemVersion: | 5 |
| Subsystem: | Windows command line |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_CUI |
| Compilation Date: | 23-Mar-2013 22:26:54 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000D8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 4 |
| Time date stamp: | 23-Mar-2013 22:26:54 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00019AB6 | 0x00019C00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.70545 |
.rdata | 0x0001B000 | 0x000061A4 | 0x00006200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.66867 |
.data | 0x00022000 | 0x0000A684 | 0x00001800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 2.97778 |
.rsrc | 0x0002D000 | 0x00019CBC | 0x00019E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 3.04836 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
0 | 2.60989 | 76 | Latin 1 / Western European | UNKNOWN | RT_GROUP_ICON |
1 | 3.00358 | 1128 | Latin 1 / Western European | UNKNOWN | RT_ICON |
2 | 2.52655 | 4264 | Latin 1 / Western European | UNKNOWN | RT_ICON |
3 | 3.25633 | 9640 | Latin 1 / Western European | UNKNOWN | RT_ICON |
4 | 2.50351 | 16936 | Latin 1 / Western European | UNKNOWN | RT_ICON |
5 | 2.49709 | 67624 | Latin 1 / Western European | UNKNOWN | RT_ICON |
6 | 5.43869 | 4264 | Latin 1 / Western European | UNKNOWN | RT_ICON |
7 | 5.89356 | 1128 | Latin 1 / Western European | UNKNOWN | RT_ICON |
101 | 2.71858 | 104 | Latin 1 / Western European | UNKNOWN | RT_GROUP_ICON |
Imports
KERNEL32.dll |
WS2_32.dll |
Total processes
33
Monitored processes
2
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
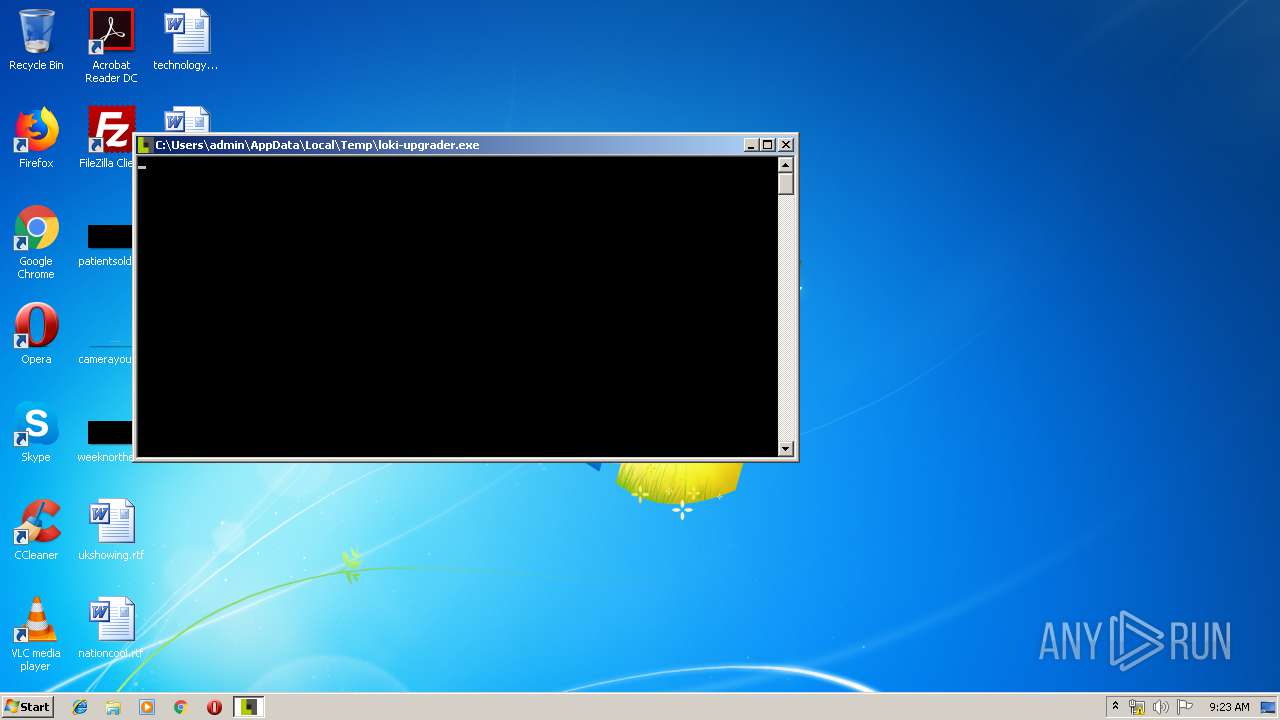
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 916 | "C:\Users\admin\AppData\Local\Temp\loki-upgrader.exe" | C:\Users\admin\AppData\Local\Temp\loki-upgrader.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2736 | "C:\Users\admin\AppData\Local\Temp\loki-upgrader.exe" | C:\Users\admin\AppData\Local\Temp\loki-upgrader.exe | loki-upgrader.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
Total events
13
Read events
13
Write events
0
Delete events
0
Modification events
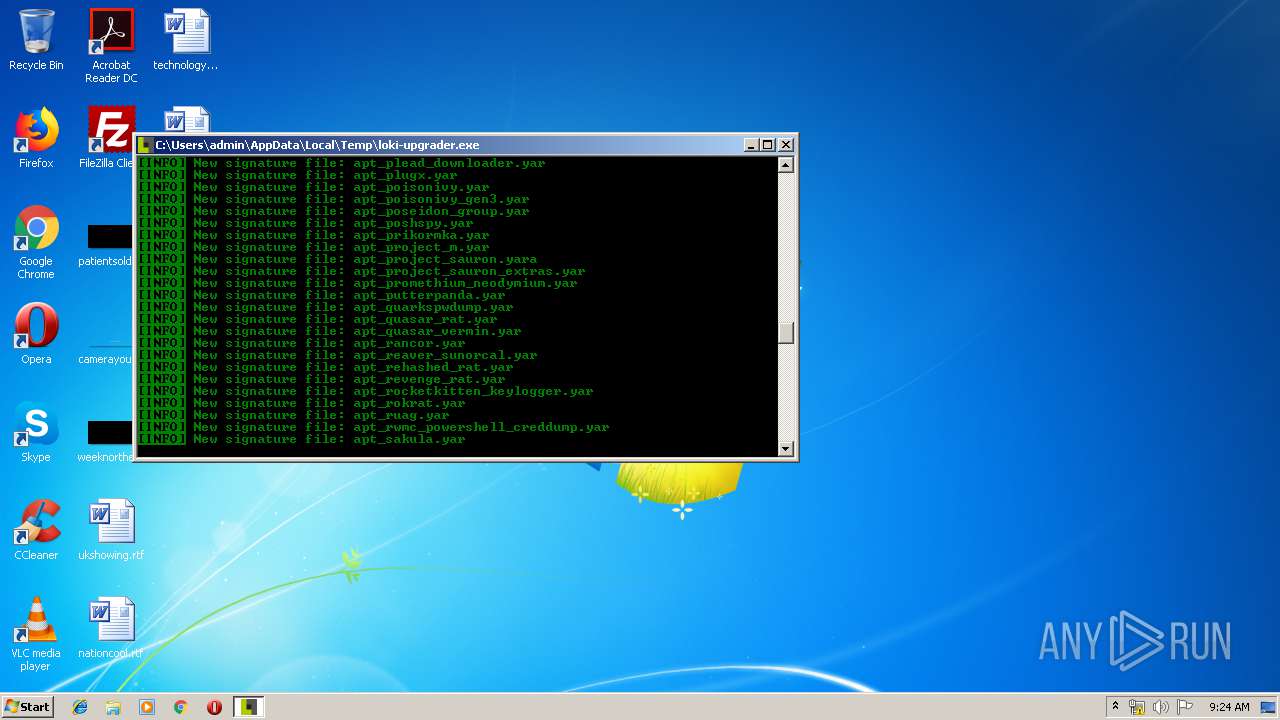
Executable files
32
Suspicious files
1
Text files
572
Unknown types
6
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 916 | loki-upgrader.exe | C:\Users\admin\AppData\Local\Temp\_MEI9162\Microsoft.VC90.CRT.manifest | xml | |
MD5:4F9ED5EFA4F7B75BCFE0F36C36EE5CB6 | SHA256:FF718390133B400EE679177B2902BBB918DB148BBB4ABABA03D0A1DF325B3303 | |||
| 916 | loki-upgrader.exe | C:\Users\admin\AppData\Local\Temp\_MEI9162\pylzma.pyd | executable | |
MD5:1F7A05819BC589BD25C03776E3171F53 | SHA256:573EA919AEED7B9551EA0CB6FCD11C4A785DBB116DA1FCB15A32687C80D4BE0E | |||
| 916 | loki-upgrader.exe | C:\Users\admin\AppData\Local\Temp\_MEI9162\psutil._psutil_windows.pyd | executable | |
MD5:3D3B3863AA2D68FCE7BC0338999B2B38 | SHA256:C23F62A88ED54B865898E1A8FF70D7273B62A50FB0EC8B4D7B3446C58A991668 | |||
| 916 | loki-upgrader.exe | C:\Users\admin\AppData\Local\Temp\_MEI9162\_win32sysloader.pyd | executable | |
MD5:0DDC179AAEFD31BE60FE5611CE372CF4 | SHA256:6842DF5C73F1D7DE30C6FC8F811143EC530312BD7A389294763ACE96A8F97835 | |||
| 916 | loki-upgrader.exe | C:\Users\admin\AppData\Local\Temp\_MEI9162\win32pipe.pyd | executable | |
MD5:FC95A6441AB4B4E4B37B5CFE34A7CC9F | SHA256:20B8C5D1BD57DB9ABC8713DBFAFD1A4928DA4CC7F22D3E7C1BBC47370053FF51 | |||
| 916 | loki-upgrader.exe | C:\Users\admin\AppData\Local\Temp\_MEI9162\msvcm90.dll | executable | |
MD5:4A8BC195ABDC93F0DB5DAB7F5093C52F | SHA256:B371AF3CE6CB5D0B411919A188D5274DF74D5EE49F6DD7B1CCB5A31466121A18 | |||
| 916 | loki-upgrader.exe | C:\Users\admin\AppData\Local\Temp\_MEI9162\python27.dll | executable | |
MD5:E8E4FE4D10DA850A499F230FF7DB3078 | SHA256:43CF527AD207D0F1AD5A20FF92B35EB8170DF92B6E8DAF93580A6A5ED361B3A9 | |||
| 916 | loki-upgrader.exe | C:\Users\admin\AppData\Local\Temp\_MEI9162\win32trace.pyd | executable | |
MD5:E0CD1272B8830EE160898EAC103A4FF9 | SHA256:D0AF5A2952F38FC8543F48762C37A85F7D5F8128EFE522341F4939CA018E31C2 | |||
| 916 | loki-upgrader.exe | C:\Users\admin\AppData\Local\Temp\_MEI9162\pyexpat.pyd | executable | |
MD5:9E3F01175CCBD6F276ACD03DB37C124B | SHA256:769D702EB01C8852BF7DA864C3F3E16FD99B8AB9CB25E0E6430EF75C8AF581C2 | |||
| 916 | loki-upgrader.exe | C:\Users\admin\AppData\Local\Temp\_MEI9162\select.pyd | executable | |
MD5:0A734BBCDE69D7A780F5991558588DD0 | SHA256:5BB016F690F9B49AF124BB62AFABC348D20C423D98A3499EB006FB9E55CF04AE | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
5
DNS requests
4
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
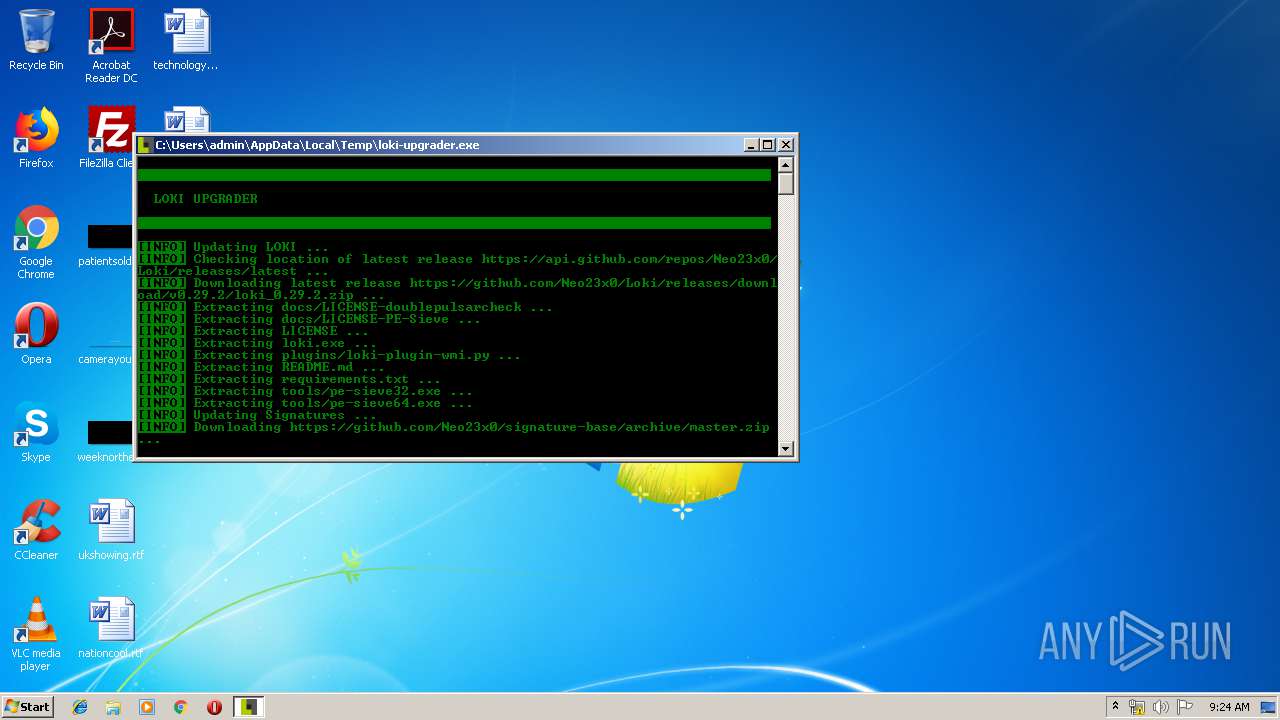
2736 | loki-upgrader.exe | 140.82.118.3:443 | github.com | — | US | malicious |
2736 | loki-upgrader.exe | 192.30.253.121:443 | codeload.github.com | GitHub, Inc. | US | shared |
2736 | loki-upgrader.exe | 192.30.253.117:443 | api.github.com | GitHub, Inc. | US | shared |
2736 | loki-upgrader.exe | 52.216.96.139:443 | github-production-release-asset-2e65be.s3.amazonaws.com | Amazon.com, Inc. | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
api.github.com |
| whitelisted |
github.com |
| malicious |
github-production-release-asset-2e65be.s3.amazonaws.com |
| shared |
codeload.github.com |
| whitelisted |