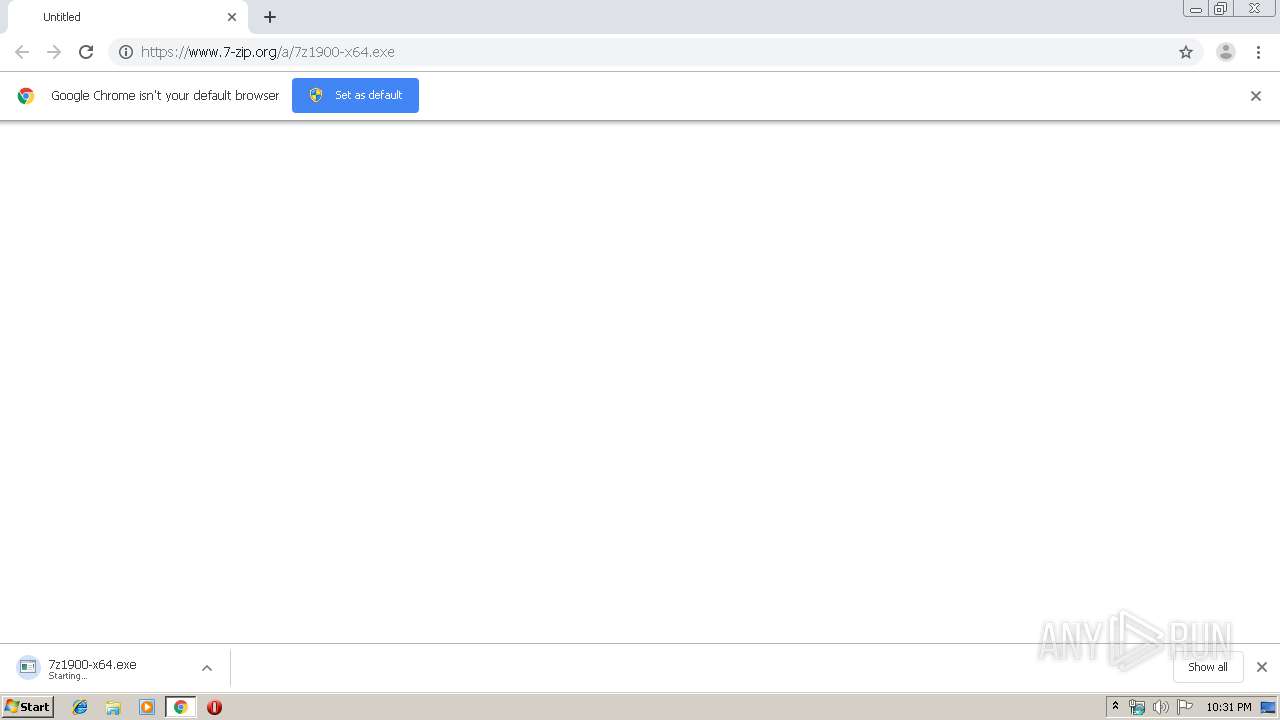
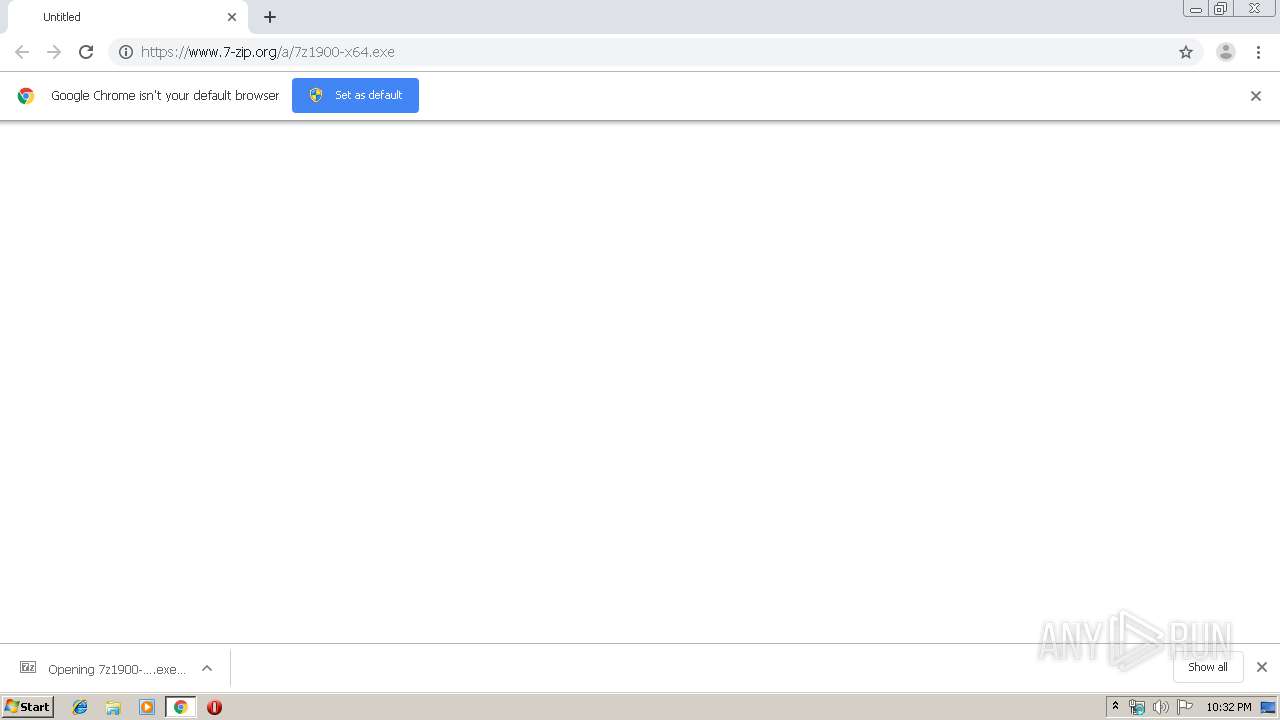
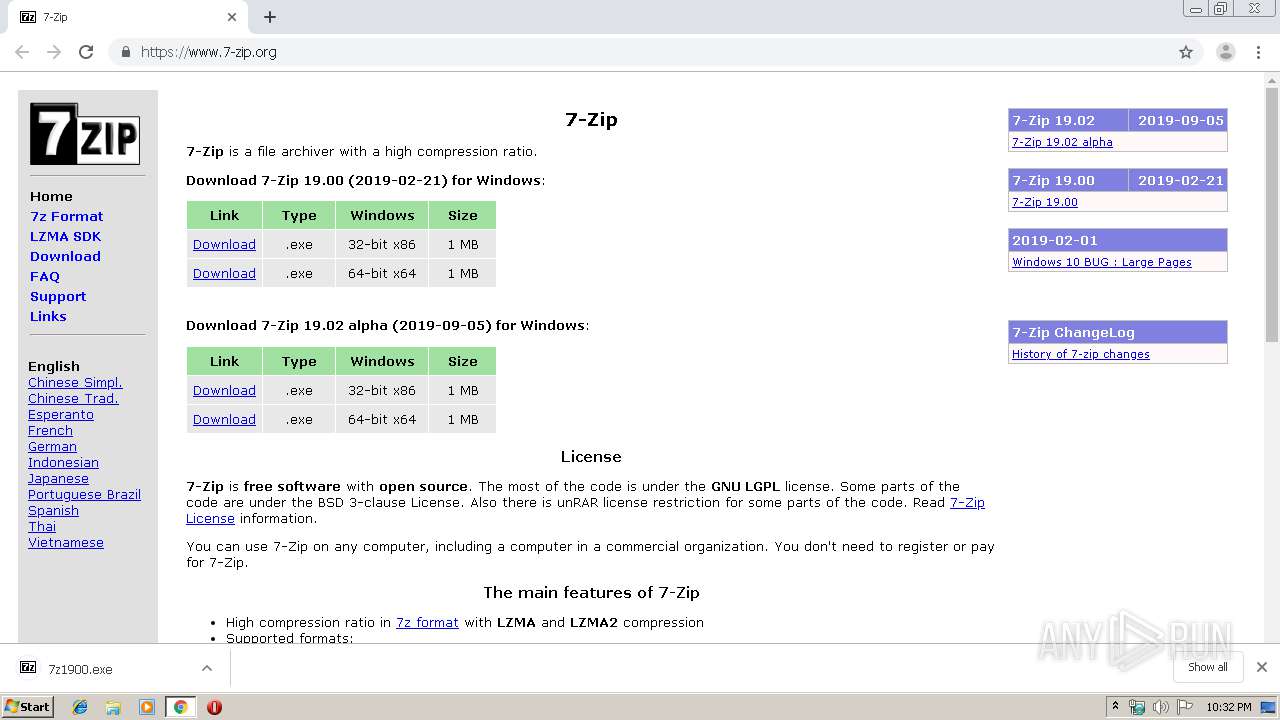
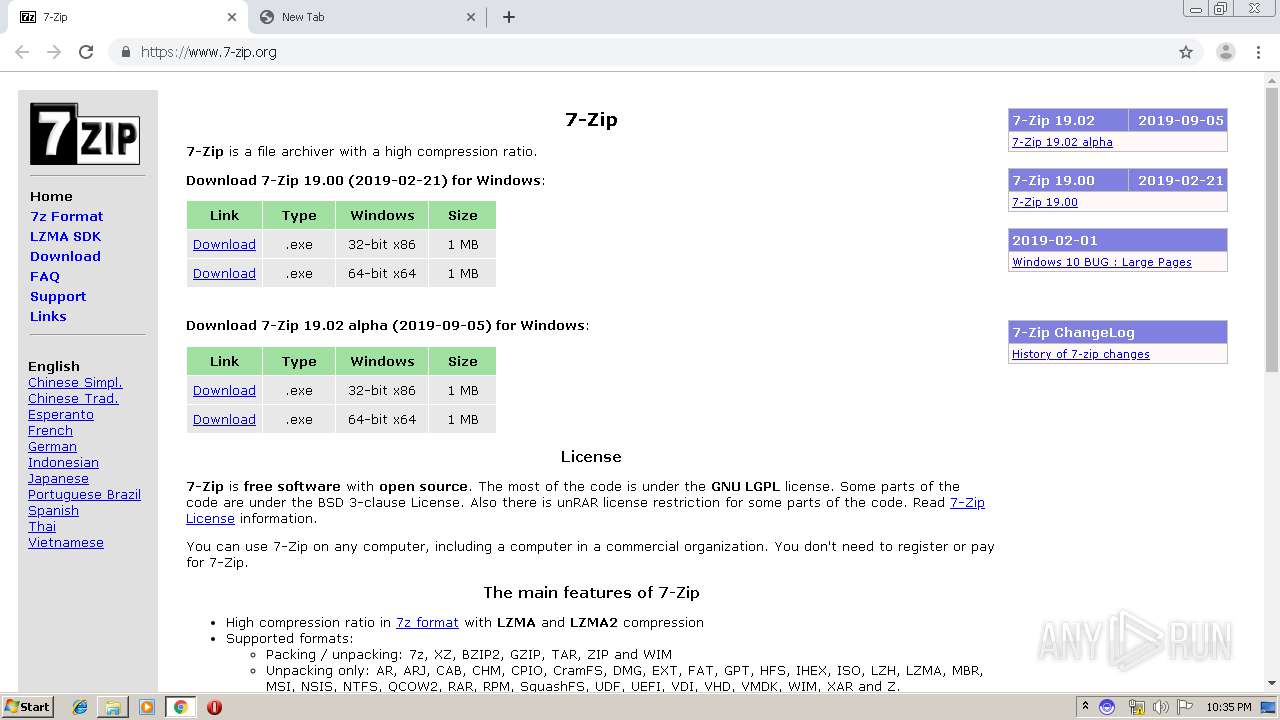
| URL: | https://www.7-zip.org/a/7z1900-x64.exe |
| Full analysis: | https://app.any.run/tasks/cf7ab748-7792-4740-8d6a-d657384c56c5 |
| Verdict: | Malicious activity |
| Analysis date: | December 05, 2019, 22:31:39 |
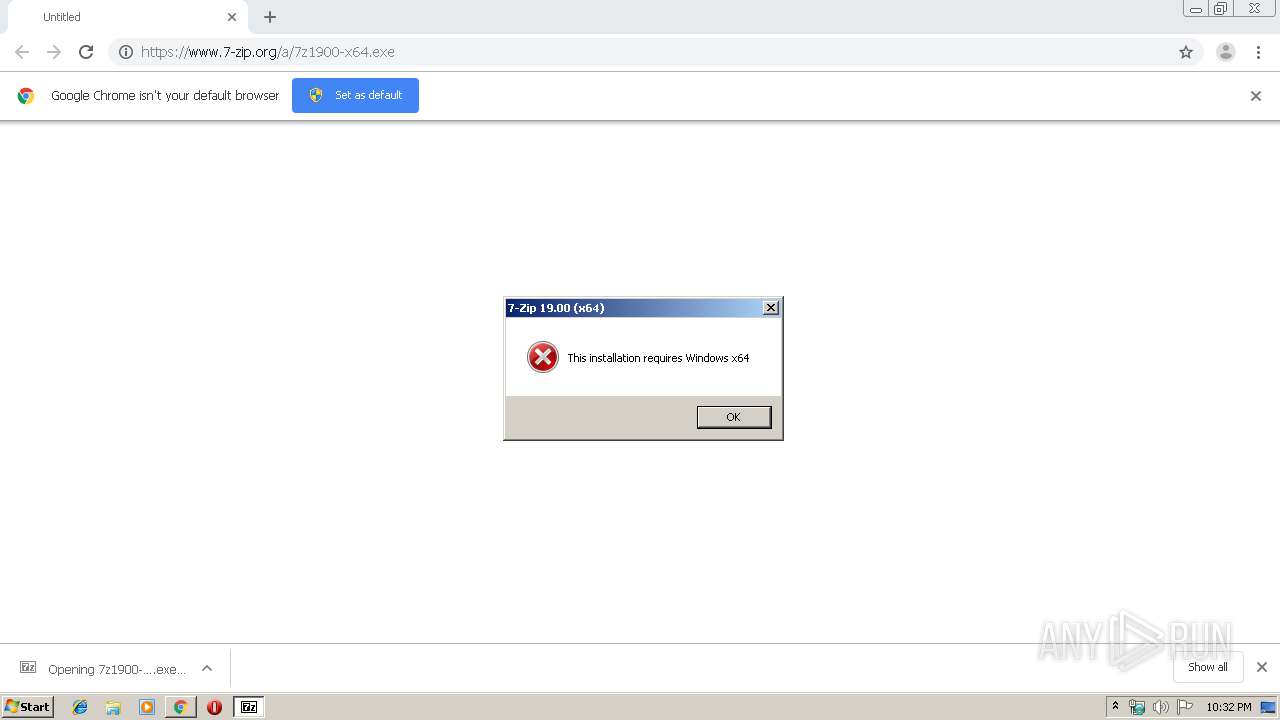
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 31F3473D652424800FCA7BA616D2BEA5 |
| SHA1: | 57A349F8728CBDD60475D351C4079FC455367024 |
| SHA256: | 5C2D499F5EF0A08EA576F752AFD0C895F84AE52A294AAEEE3FAD917B10471A16 |
| SSDEEP: | 3:N8DSLohI0A:2OLo5A |
MALICIOUS
Application was dropped or rewritten from another process
- 7z1900.exe (PID: 1812)
- 7z1900.exe (PID: 2408)
- 7z1900-x64.exe (PID: 1768)
- 7zG.exe (PID: 1600)
- 7z.exe (PID: 272)
- 7z1900-x64.exe (PID: 3860)
- Update.exe (PID: 3944)
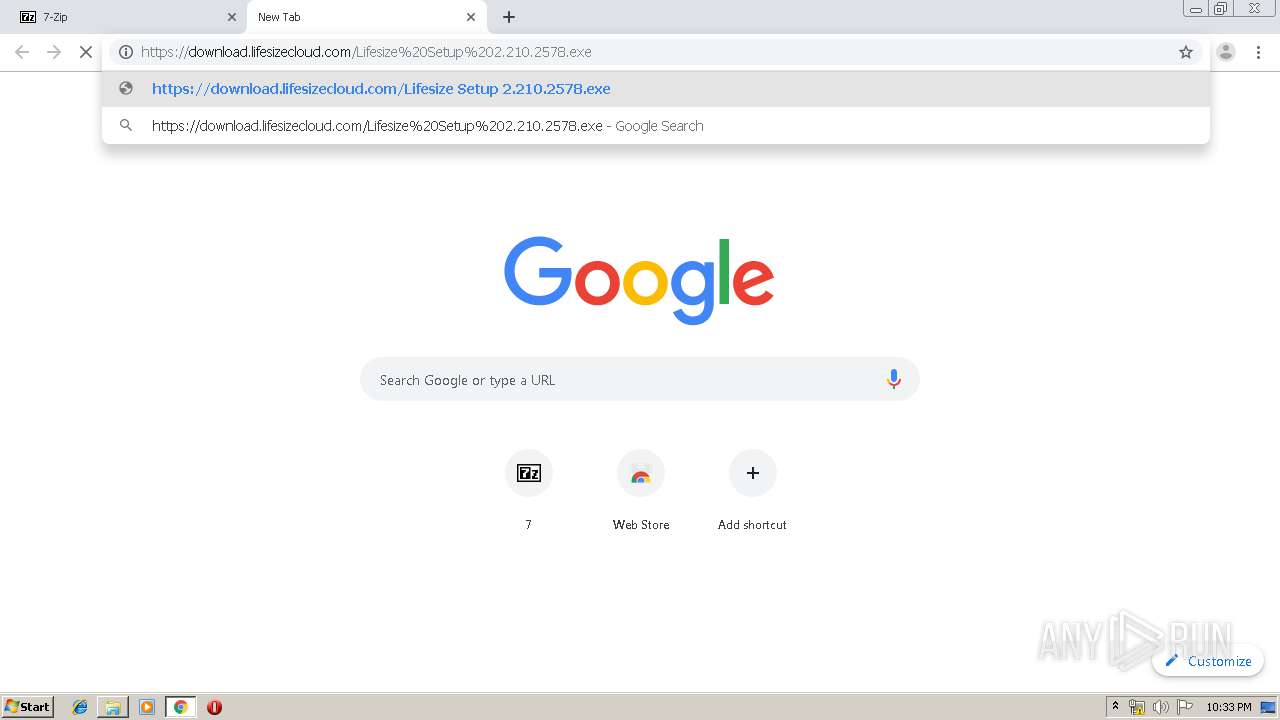
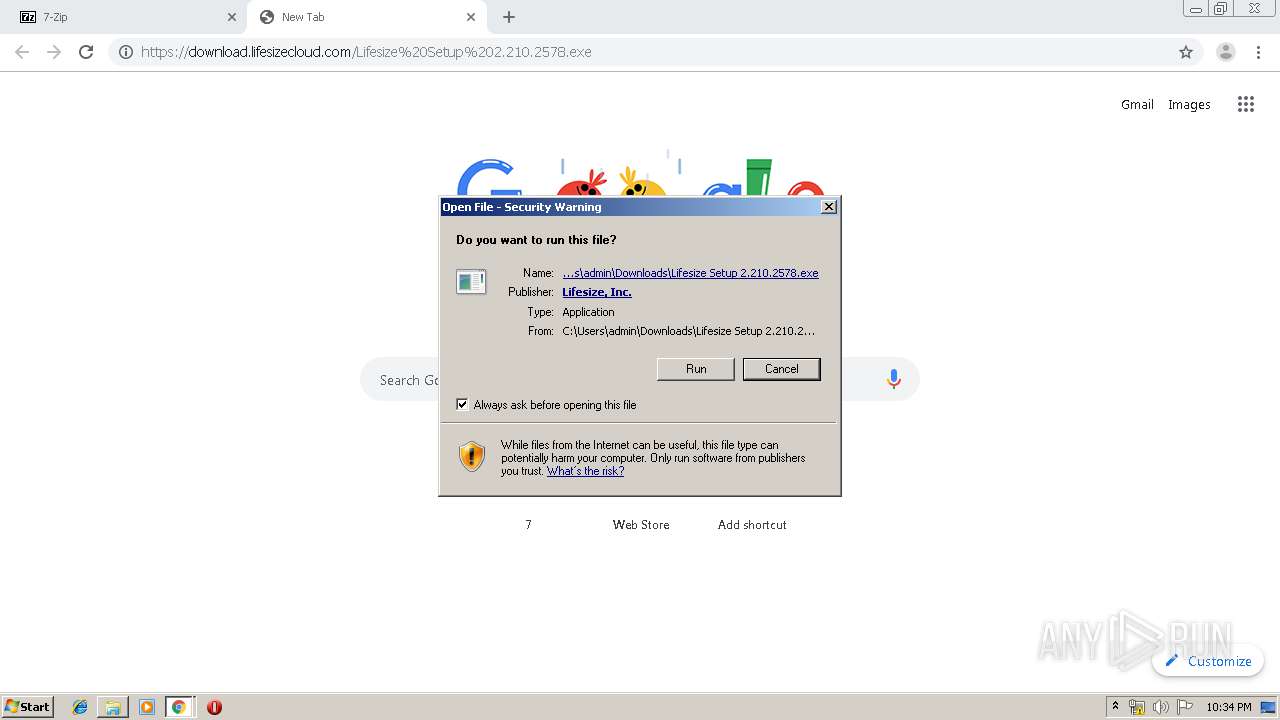
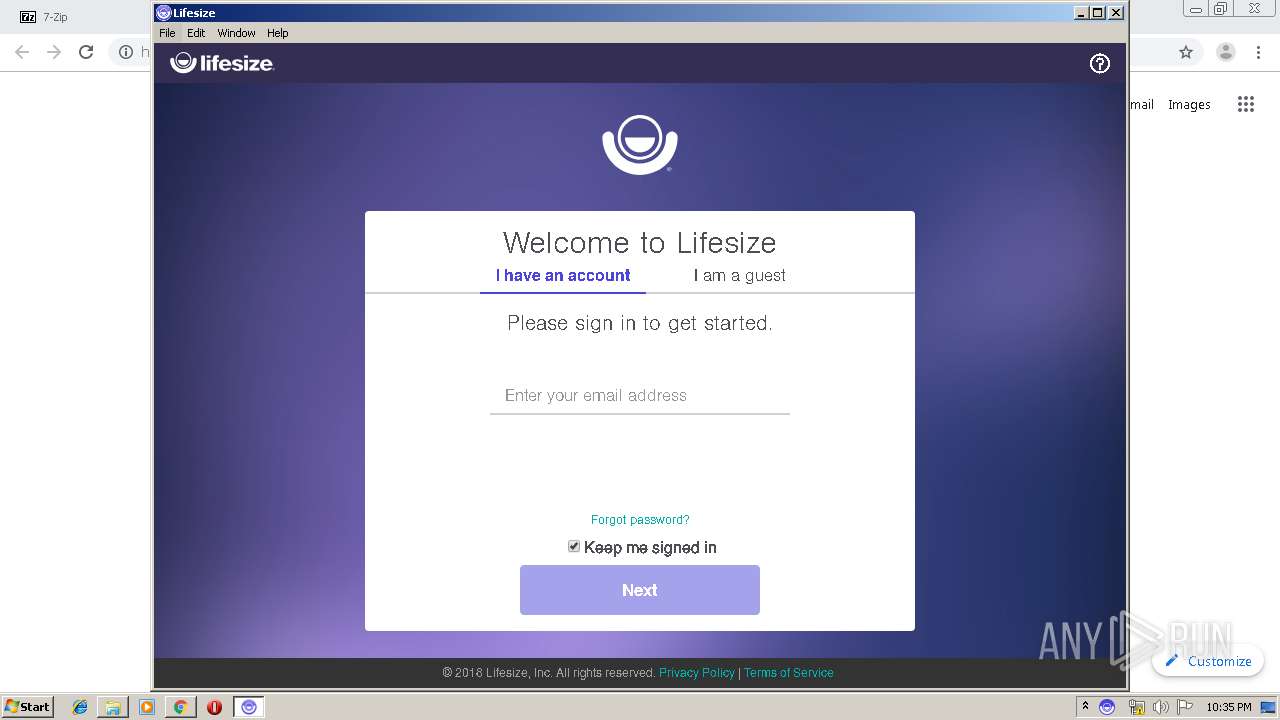
- Lifesize Setup 2.210.2578.exe (PID: 2676)
- 7zFM.exe (PID: 1596)
- update.exe (PID: 3052)
- Lifesize App Service.exe (PID: 3932)
- Lifesize App Service.exe (PID: 3860)
- Update.exe (PID: 2748)
Loads dropped or rewritten executable
- chrome.exe (PID: 2092)
- svchost.exe (PID: 864)
- Lifesize.exe (PID: 2688)
- Lifesize.exe (PID: 1528)
- Lifesize.exe (PID: 3312)
- Lifesize.exe (PID: 2364)
- Lifesize.exe (PID: 3172)
- Lifesize.exe (PID: 3504)
- Lifesize.exe (PID: 3448)
- Lifesize.exe (PID: 3088)
- Lifesize.exe (PID: 2996)
Changes the autorun value in the registry
- Lifesize.exe (PID: 2688)
- reg.exe (PID: 3100)
SUSPICIOUS
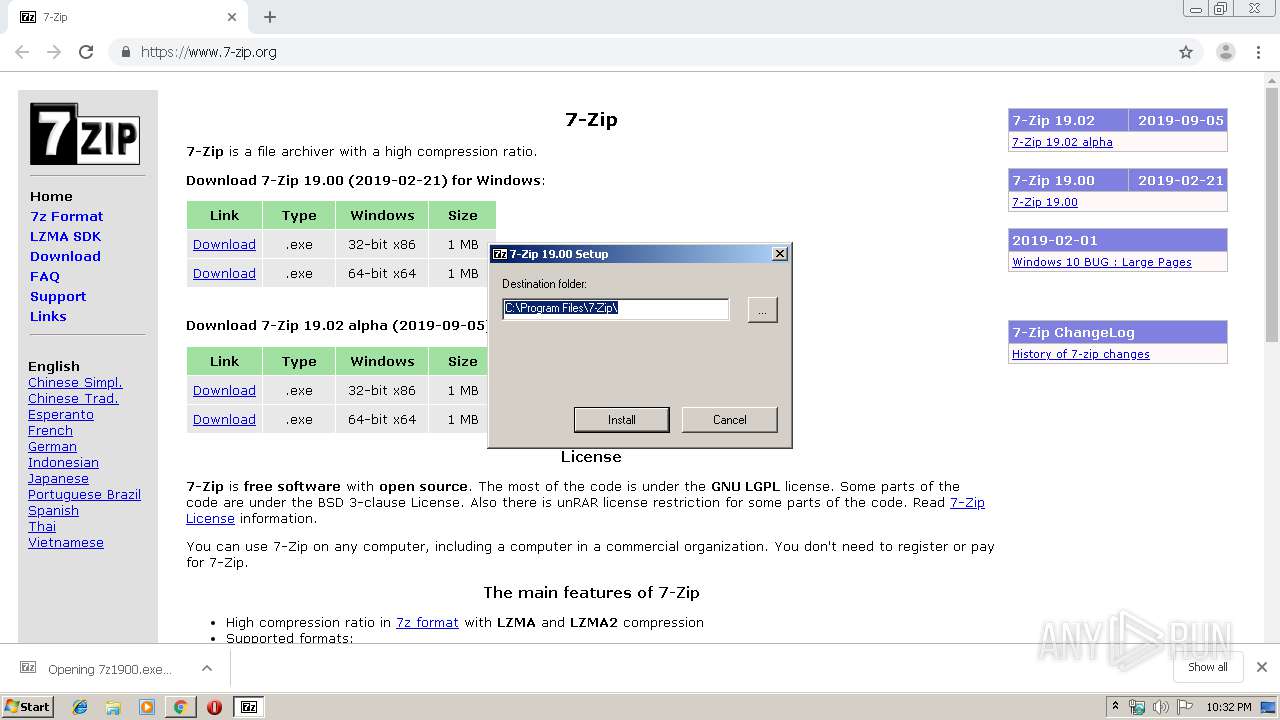
Creates a software uninstall entry
- 7z1900.exe (PID: 1812)
- Update.exe (PID: 3944)
Executable content was dropped or overwritten
- 7z1900.exe (PID: 1812)
- chrome.exe (PID: 2520)
- chrome.exe (PID: 3792)
- Update.exe (PID: 3944)
- Lifesize Setup 2.210.2578.exe (PID: 2676)
- Lifesize.exe (PID: 3504)
Creates COM task schedule object
- 7z1900.exe (PID: 1812)
Modifies files in Chrome extension folder
- chrome.exe (PID: 2520)
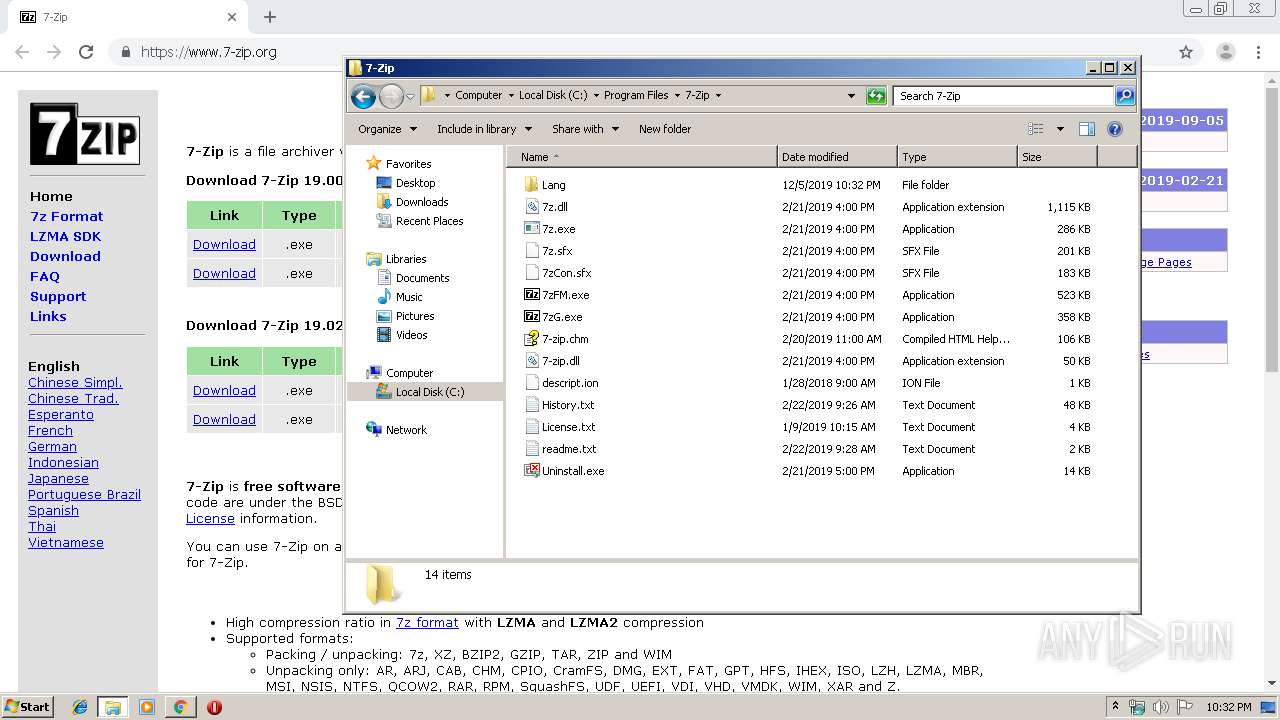
Creates files in the program directory
- 7z1900.exe (PID: 1812)
Creates files in the user directory
- Lifesize.exe (PID: 2688)
- update.exe (PID: 3052)
- Lifesize.exe (PID: 2996)
- Lifesize.exe (PID: 3088)
Uses REG.EXE to modify Windows registry
- Lifesize.exe (PID: 2688)
- Lifesize.exe (PID: 2996)
Modifies the open verb of a shell class
- Lifesize.exe (PID: 2688)
Reads CPU info
- Lifesize.exe (PID: 2688)
- Lifesize.exe (PID: 2996)
Application launched itself
- Lifesize.exe (PID: 2688)
- Lifesize.exe (PID: 2996)
Reads Environment values
- Update.exe (PID: 3944)
INFO
Application launched itself
- chrome.exe (PID: 2520)
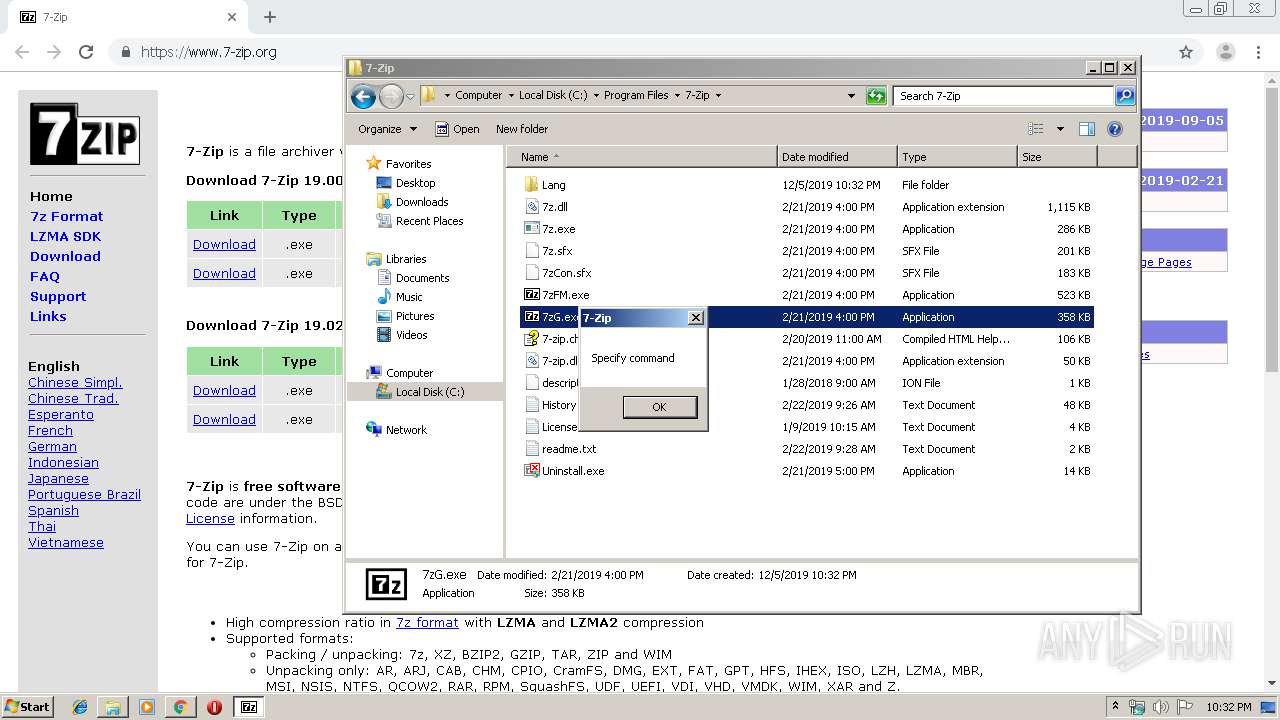
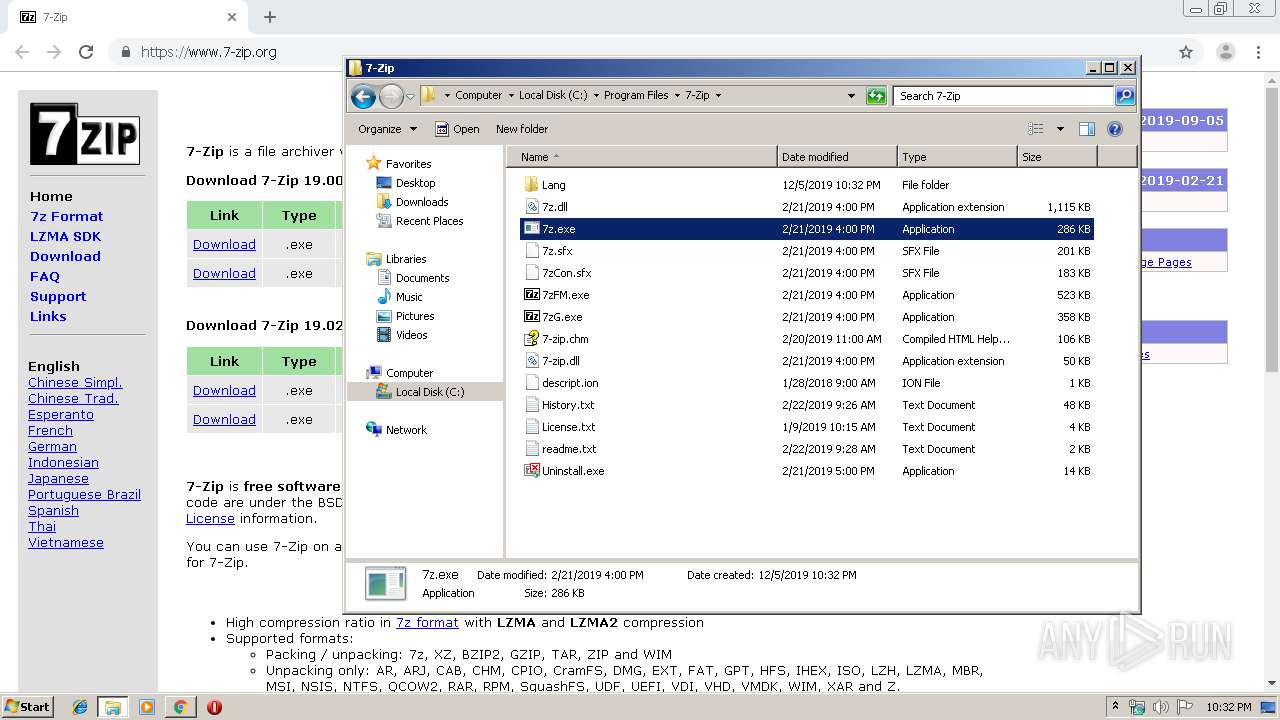
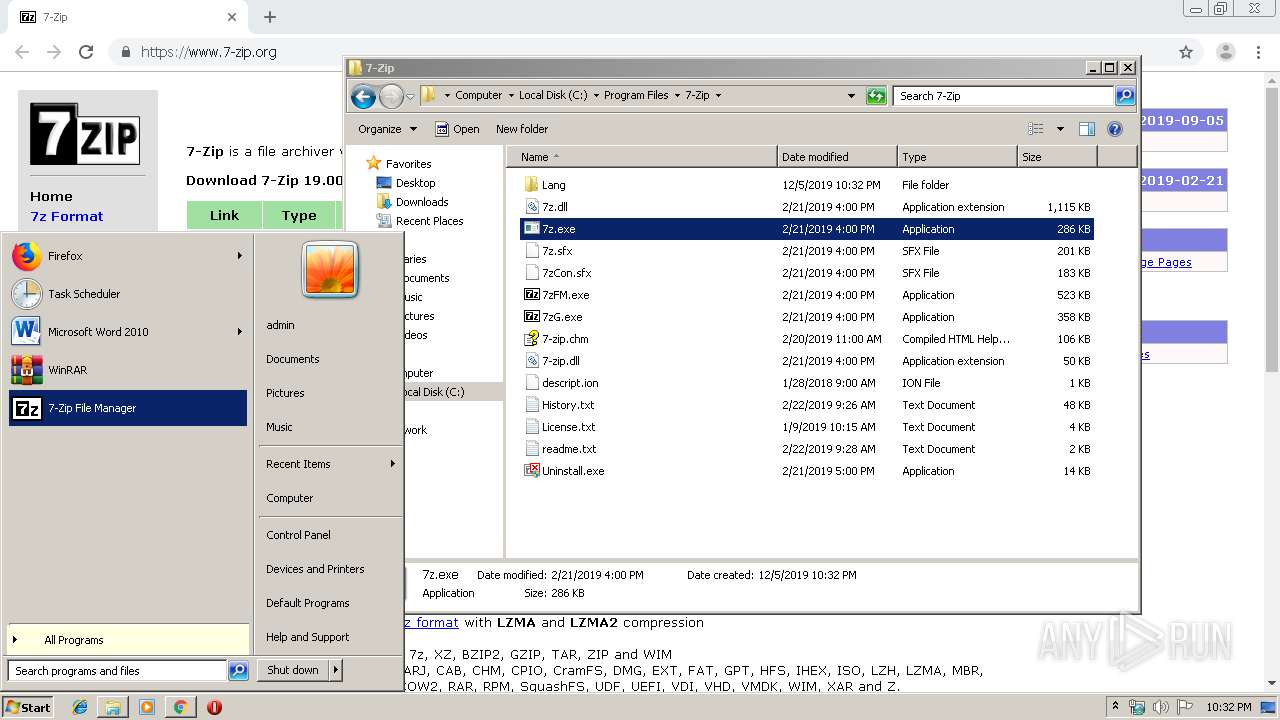
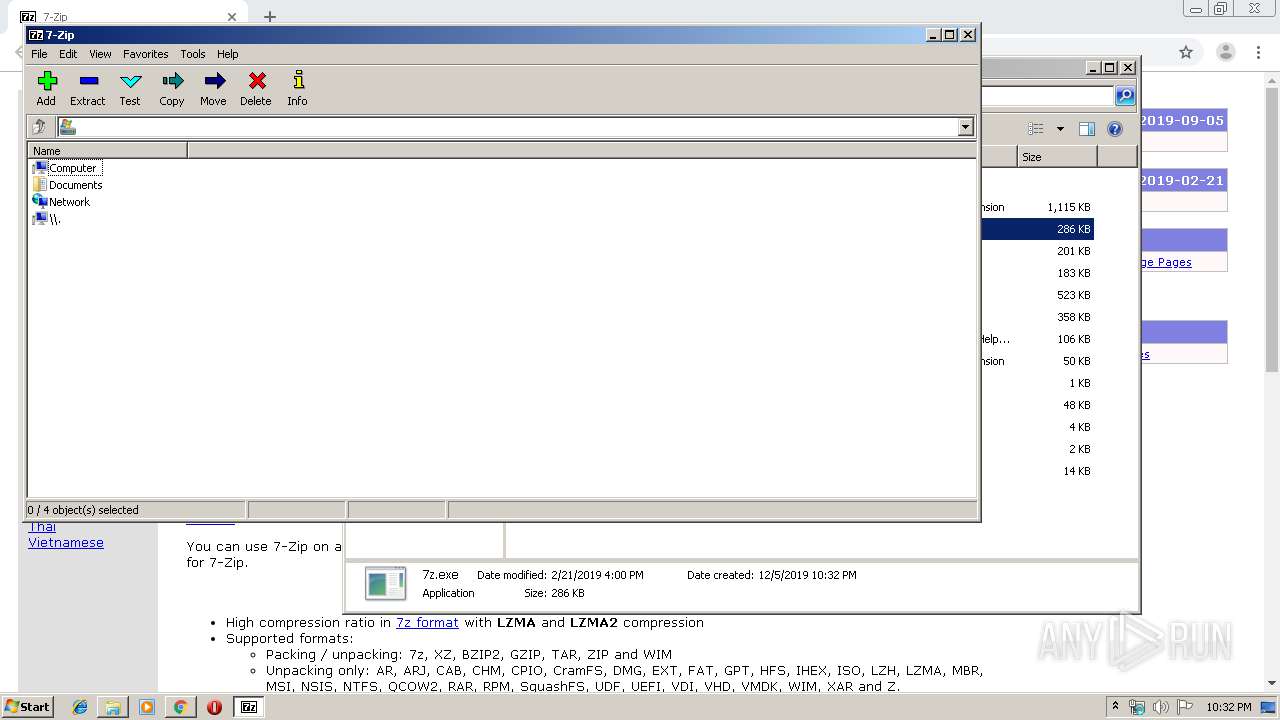
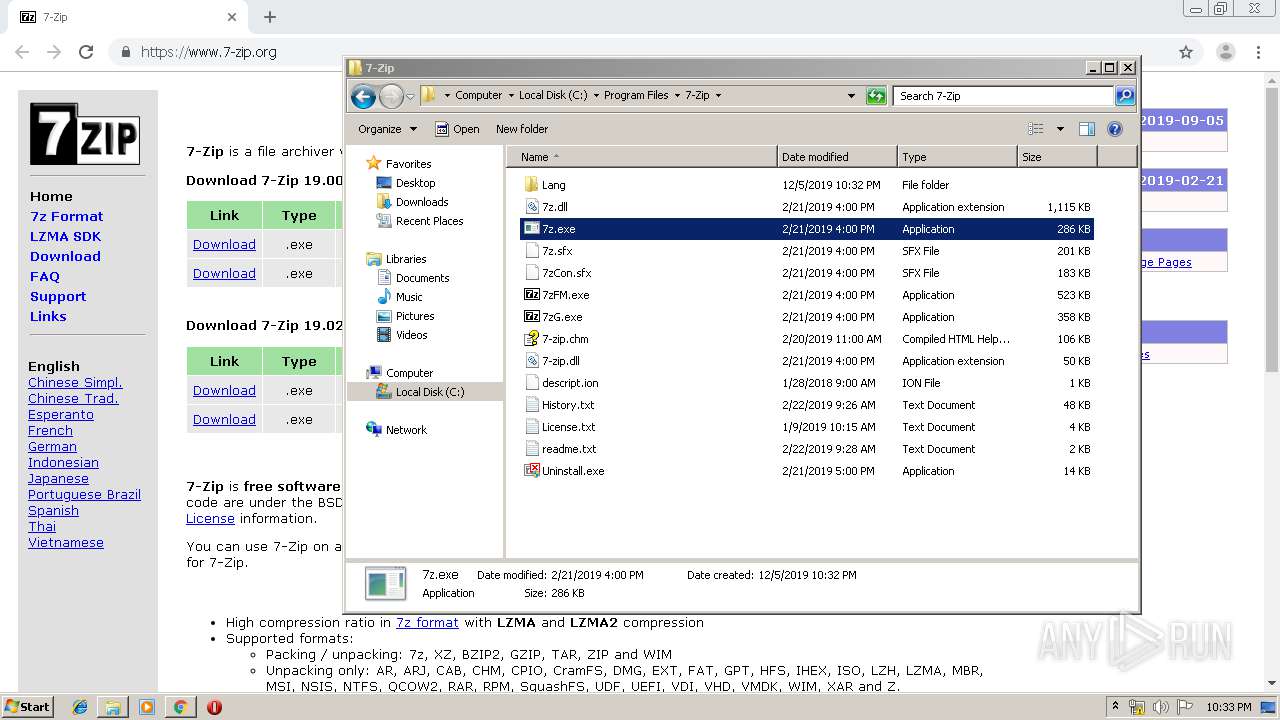
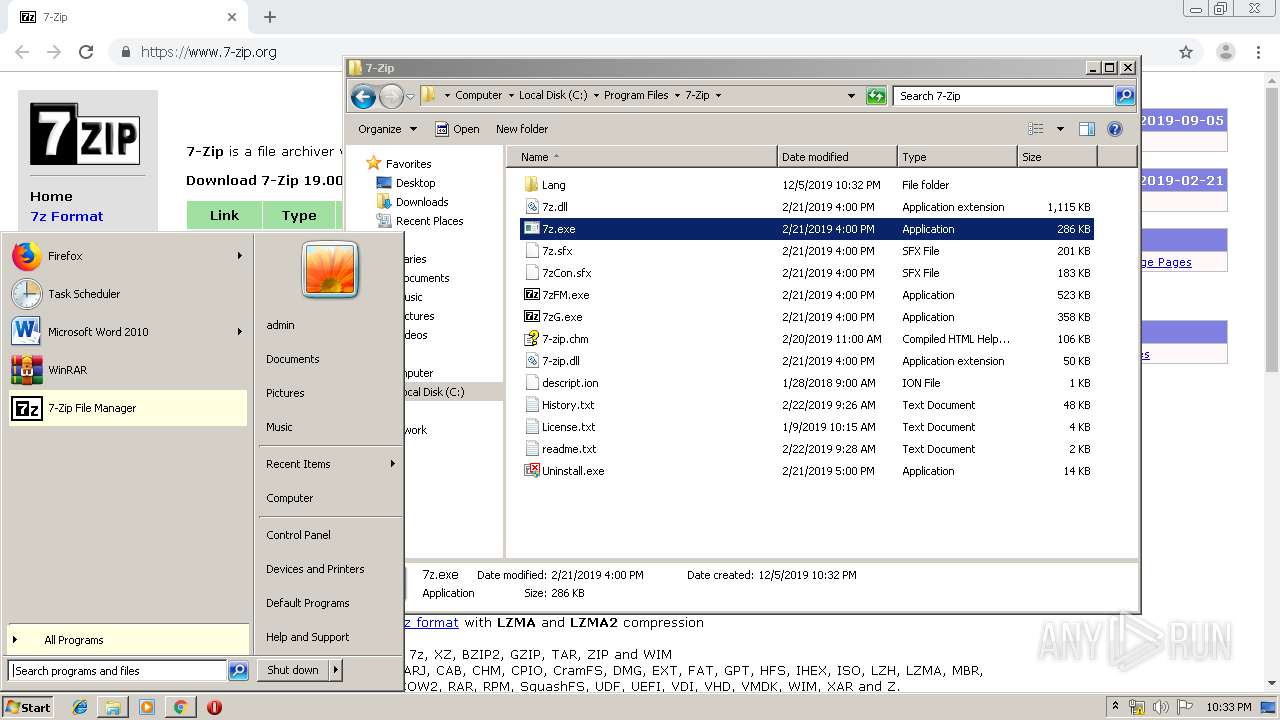
Manual execution by user
- explorer.exe (PID: 3704)
- 7zG.exe (PID: 1600)
- 7z.exe (PID: 272)
- 7zFM.exe (PID: 1596)
Reads the hosts file
- chrome.exe (PID: 2520)
- Lifesize.exe (PID: 2688)
- chrome.exe (PID: 3792)
- Lifesize.exe (PID: 2996)
Reads Internet Cache Settings
- chrome.exe (PID: 2520)
Reads settings of System Certificates
- chrome.exe (PID: 2520)
- chrome.exe (PID: 3792)
- Update.exe (PID: 3944)
Changes settings of System certificates
- chrome.exe (PID: 2520)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
106
Monitored processes
60
Malicious processes
10
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
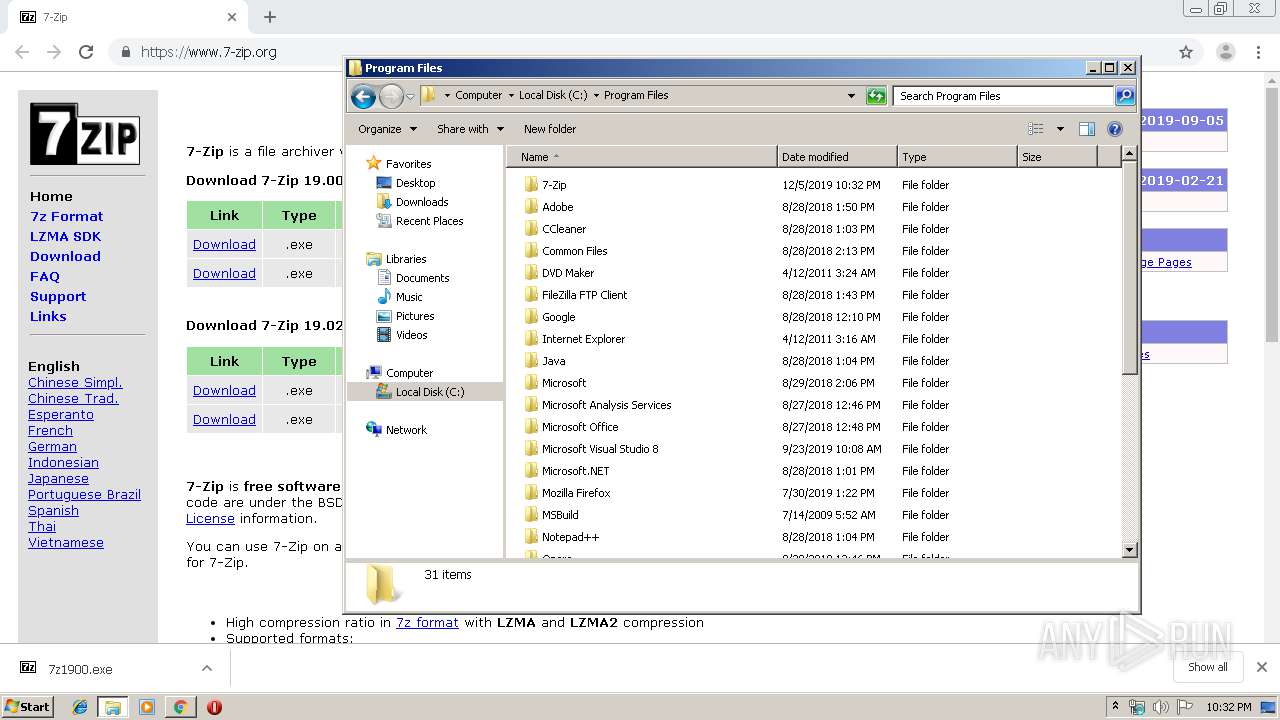
| 272 | "C:\Program Files\7-Zip\7z.exe" | C:\Program Files\7-Zip\7z.exe | — | explorer.exe | |||||||||||
User: admin Company: Igor Pavlov Integrity Level: MEDIUM Description: 7-Zip Console Exit code: 0 Version: 19.00 Modules
| |||||||||||||||
| 584 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1036,1236811904945844624,4354228354654112906,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=17909857131654634722 --renderer-client-id=25 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=904 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 620 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1036,1236811904945844624,4354228354654112906,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=12807222360266909524 --mojo-platform-channel-handle=4132 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 864 | C:\Windows\system32\svchost.exe -k netsvcs | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1024 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1036,1236811904945844624,4354228354654112906,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=3494315224765404763 --mojo-platform-channel-handle=3972 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1244 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1036,1236811904945844624,4354228354654112906,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=17774211867238655335 --renderer-client-id=30 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4852 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1528 | "C:\Users\admin\AppData\Local\lifesize_app\app-2.210.2578\Lifesize.exe" --type=gpu-process --disable-features=SpareRendererForSitePerProcess --gpu-preferences=KAAAAAAAAACAAwAAAQAAAAAAAAAAAGAAAAAAAAEAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=3330630627931318 --mojo-platform-channel-handle=1236 --ignored=" --type=renderer " /prefetch:2 | C:\Users\admin\AppData\Local\lifesize_app\app-2.210.2578\Lifesize.exe | — | Lifesize.exe | |||||||||||
User: admin Company: Lifesize Integrity Level: LOW Description: Lifesize Exit code: 0 Version: 2.210.2578.2578 Modules
| |||||||||||||||
| 1596 | "C:\Program Files\7-Zip\7zFM.exe" | C:\Program Files\7-Zip\7zFM.exe | — | explorer.exe | |||||||||||
User: admin Company: Igor Pavlov Integrity Level: MEDIUM Description: 7-Zip File Manager Exit code: 0 Version: 19.00 Modules
| |||||||||||||||
| 1600 | "C:\Program Files\7-Zip\7zG.exe" | C:\Program Files\7-Zip\7zG.exe | — | explorer.exe | |||||||||||
User: admin Company: Igor Pavlov Integrity Level: MEDIUM Description: 7-Zip GUI Exit code: 0 Version: 19.00 Modules
| |||||||||||||||
| 1728 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1036,1236811904945844624,4354228354654112906,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=16797442049059586932 --mojo-platform-channel-handle=488 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
2 284
Read events
2 062
Write events
217
Delete events
5
Modification events
| (PID) Process: | (2520) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2520) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2520) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2520) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2388) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2520-13220058715524375 |
Value: 259 | |||
| (PID) Process: | (2520) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2520) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2520) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2520) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 1512-13197841398593750 |
Value: 0 | |||
| (PID) Process: | (2520) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
34
Suspicious files
61
Text files
524
Unknown types
82
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2520 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\85663d89-e2b5-402c-972e-68bb5a5cdd90.tmp | — | |
MD5:— | SHA256:— | |||
| 2520 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000020.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2520 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF39aa92.TMP | text | |
MD5:— | SHA256:— | |||
| 2520 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old~RF39aae0.TMP | text | |
MD5:— | SHA256:— | |||
| 2520 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF39aaa2.TMP | text | |
MD5:— | SHA256:— | |||
| 2520 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2520 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2520 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\EventDB\LOG.old~RF39ab00.TMP | text | |
MD5:— | SHA256:— | |||
| 2520 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 864 | svchost.exe | C:\Windows\appcompat\programs\RecentFileCache.bcf | txt | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
44
DNS requests
32
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3792 | chrome.exe | GET | 302 | 172.217.16.206:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx | US | html | 511 b | whitelisted |
3792 | chrome.exe | GET | 302 | 172.217.16.206:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 516 b | whitelisted |
3792 | chrome.exe | GET | 200 | 173.194.160.200:80 | http://r2---sn-hpa7zn76.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mip=185.183.105.212&mm=28&mn=sn-hpa7zn76&ms=nvh&mt=1575585079&mv=m&mvi=1&pl=24&shardbypass=yes | US | crx | 862 Kb | whitelisted |
3792 | chrome.exe | GET | 200 | 67.27.157.126:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 57.4 Kb | whitelisted |
3792 | chrome.exe | GET | 200 | 143.204.208.222:80 | http://x.ss2.us/x.cer | US | der | 1.27 Kb | whitelisted |
2520 | chrome.exe | GET | 200 | 91.199.212.52:80 | http://crt.comodoca.com/COMODORSAAddTrustCA.crt | GB | der | 1.37 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3792 | chrome.exe | 159.65.89.65:443 | www.7-zip.org | — | US | suspicious |
3792 | chrome.exe | 172.217.22.36:443 | www.google.com | Google Inc. | US | whitelisted |
3792 | chrome.exe | 172.217.22.3:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
3792 | chrome.exe | 216.58.207.77:443 | accounts.google.com | Google Inc. | US | whitelisted |
3792 | chrome.exe | 172.217.18.14:443 | clients2.google.com | Google Inc. | US | whitelisted |
3792 | chrome.exe | 216.58.206.3:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
3792 | chrome.exe | 172.217.16.206:80 | redirector.gvt1.com | Google Inc. | US | whitelisted |
3792 | chrome.exe | 173.194.182.136:80 | r3---sn-hpa7znsz.gvt1.com | Google Inc. | US | whitelisted |
3792 | chrome.exe | 172.217.22.99:443 | www.google.it | Google Inc. | US | whitelisted |
3792 | chrome.exe | 216.58.207.74:443 | safebrowsing.googleapis.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
www.7-zip.org |
| whitelisted |
accounts.google.com |
| shared |
www.google.com |
| malicious |
ssl.gstatic.com |
| whitelisted |
clients2.google.com |
| whitelisted |
redirector.gvt1.com |
| whitelisted |
r3---sn-hpa7znsz.gvt1.com |
| whitelisted |
clients2.googleusercontent.com |
| whitelisted |
r2---sn-hpa7zn76.gvt1.com |
| whitelisted |