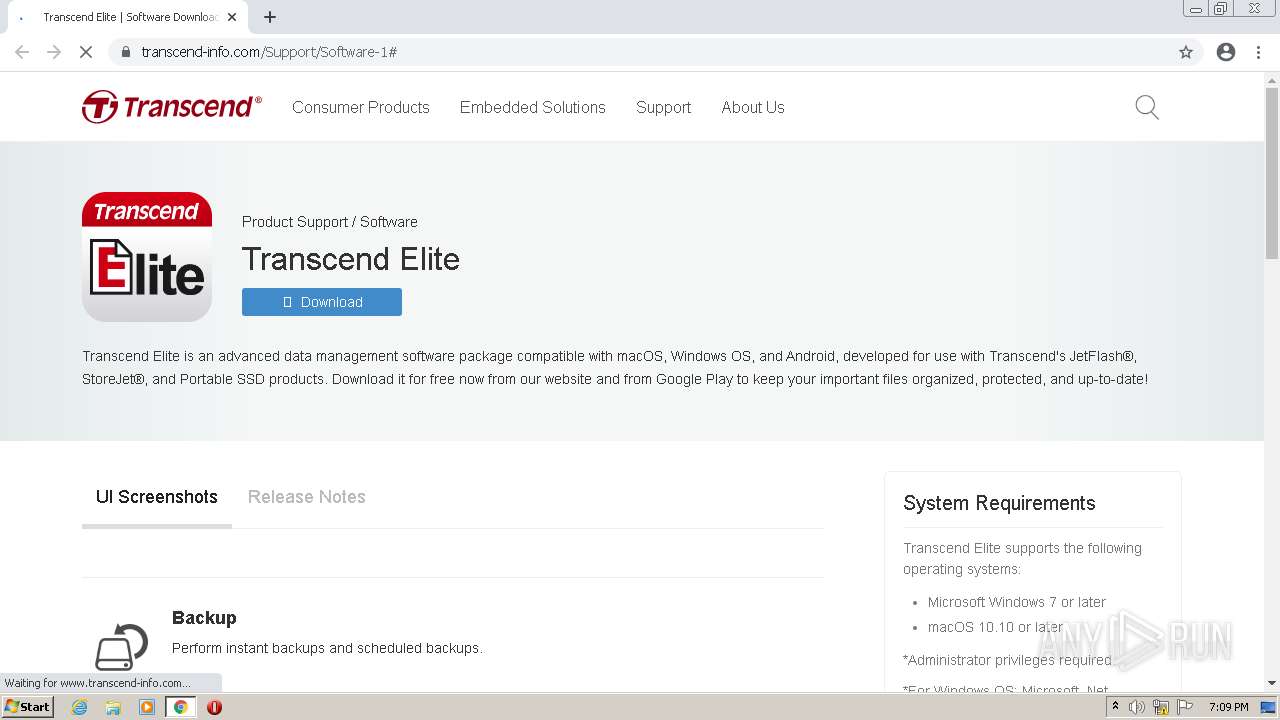
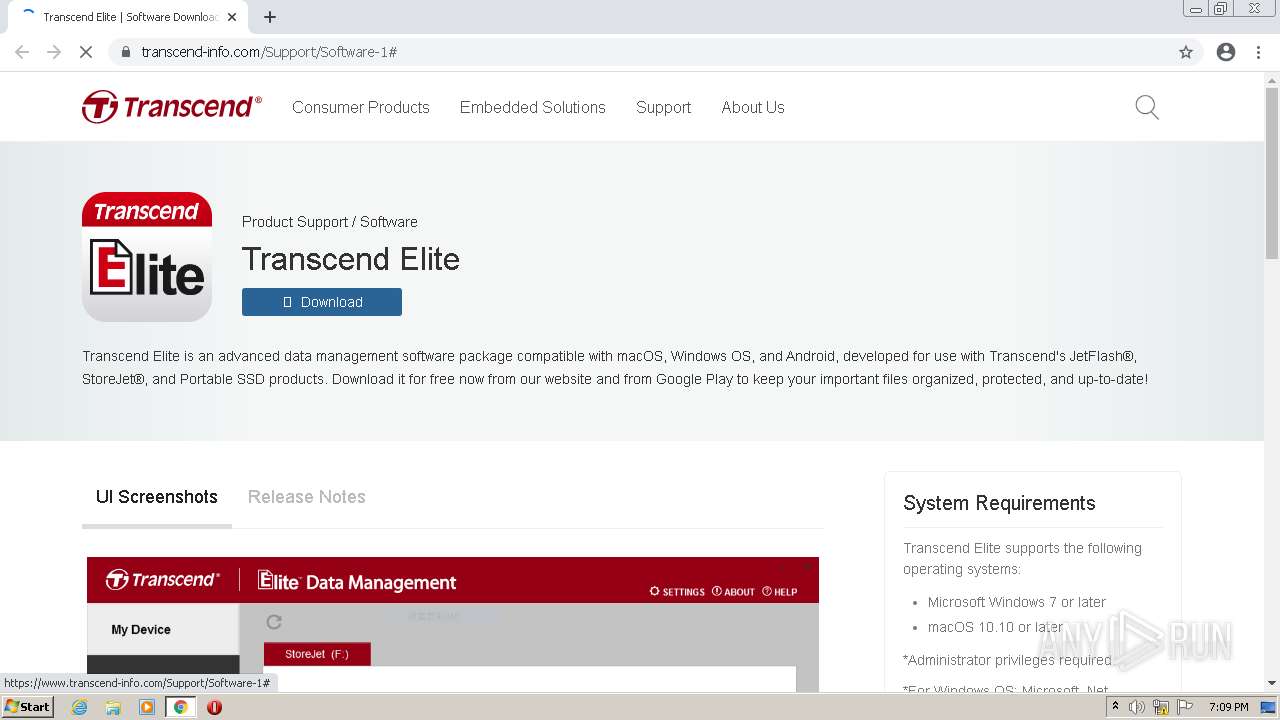
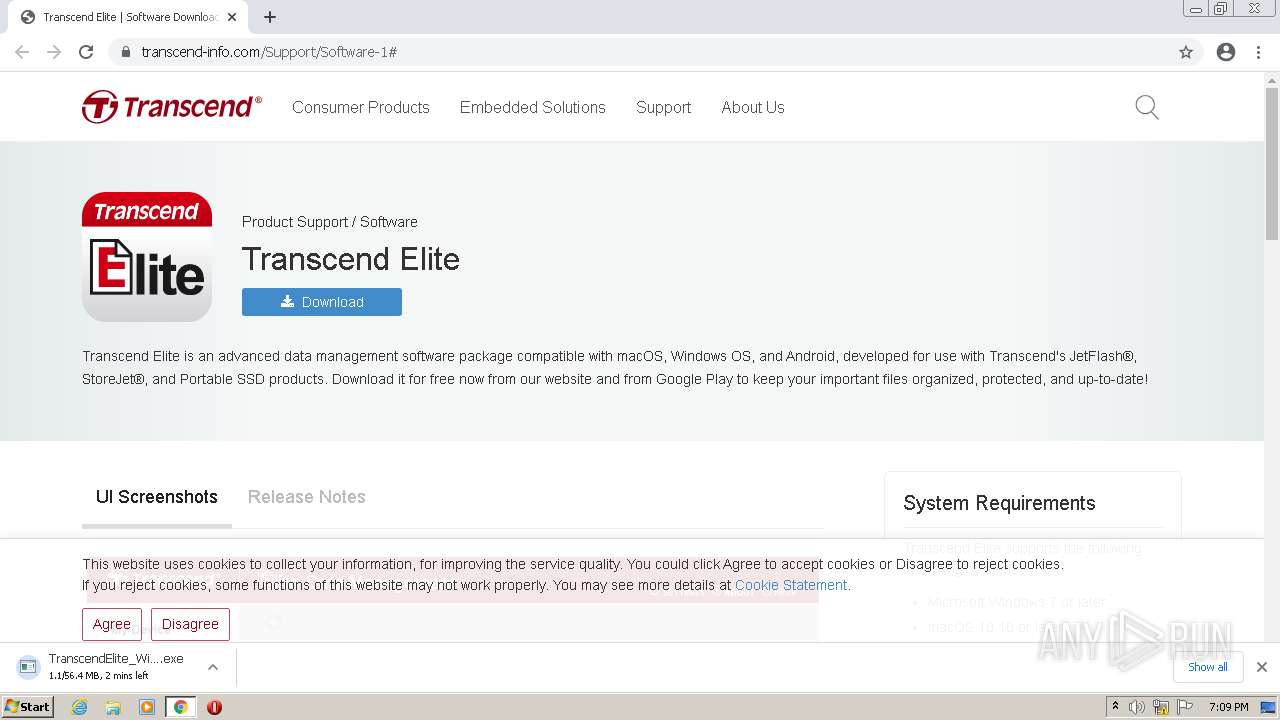
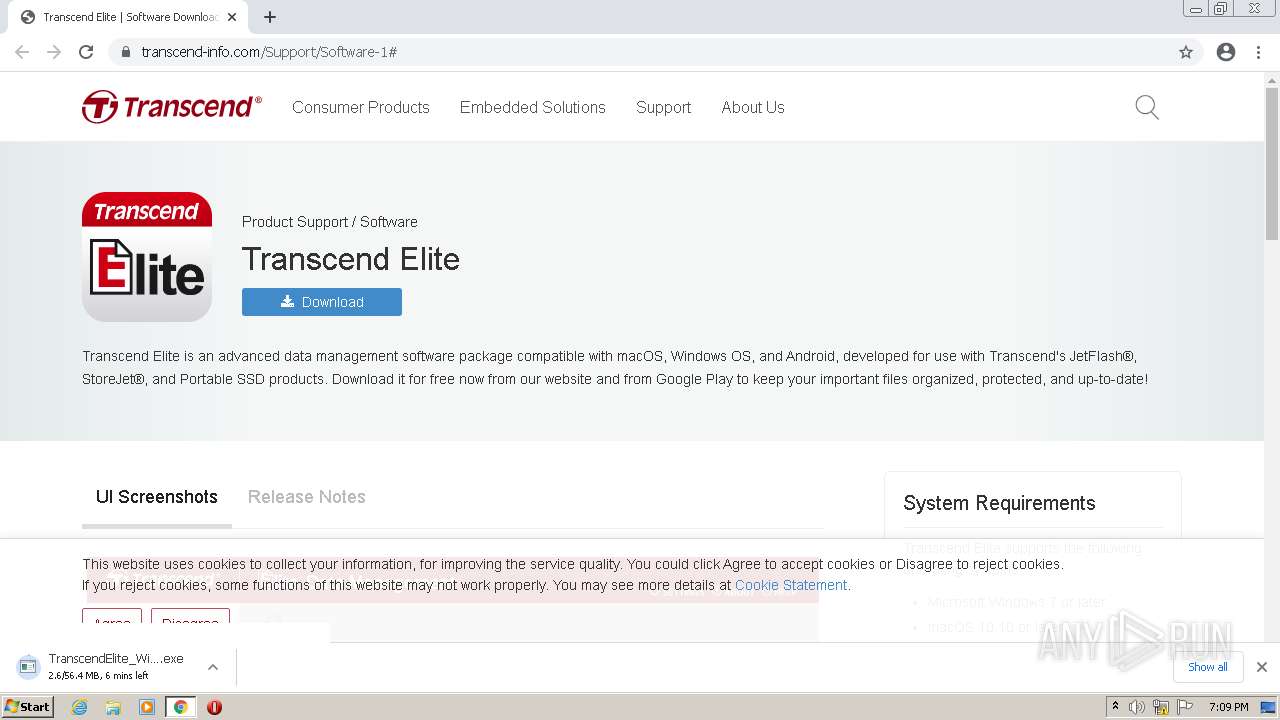
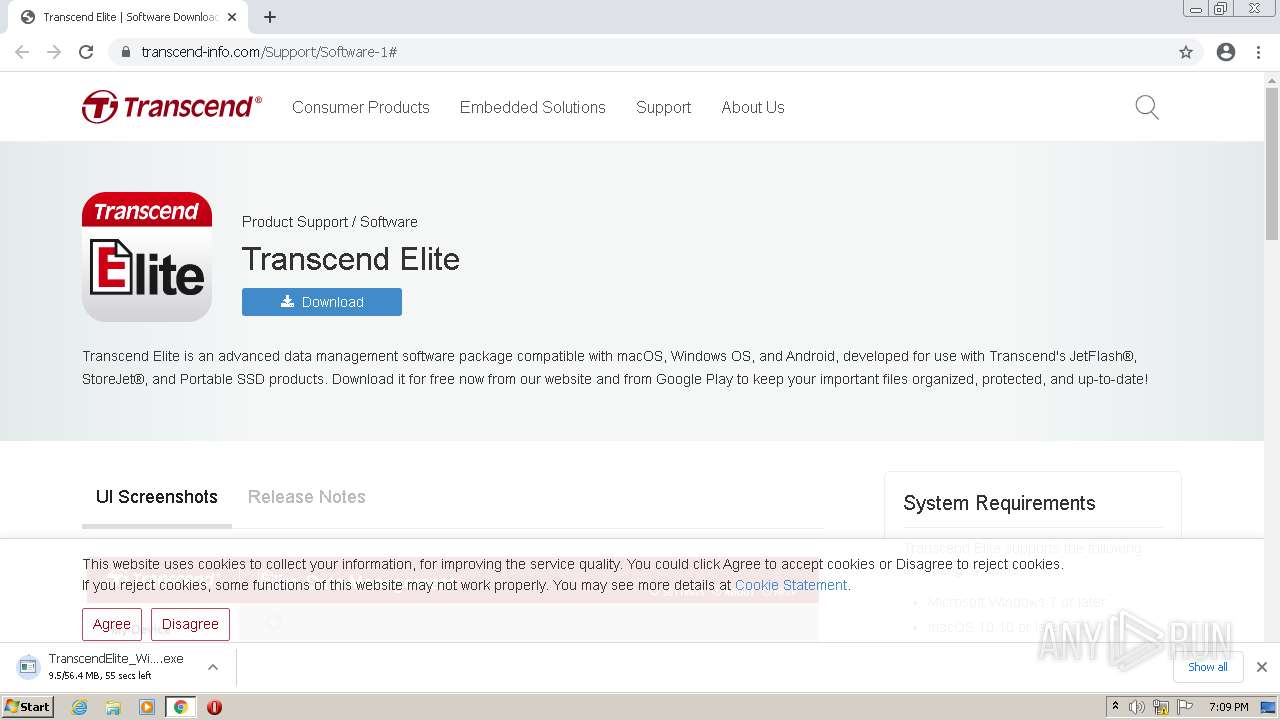
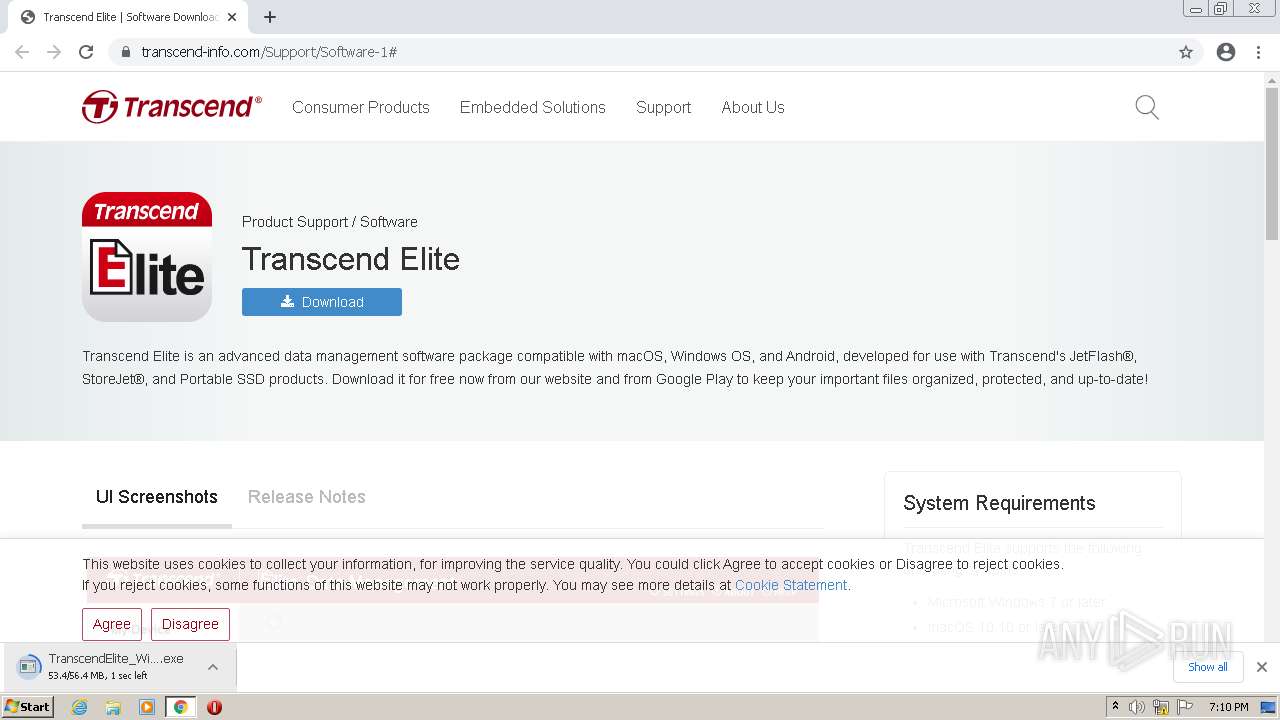
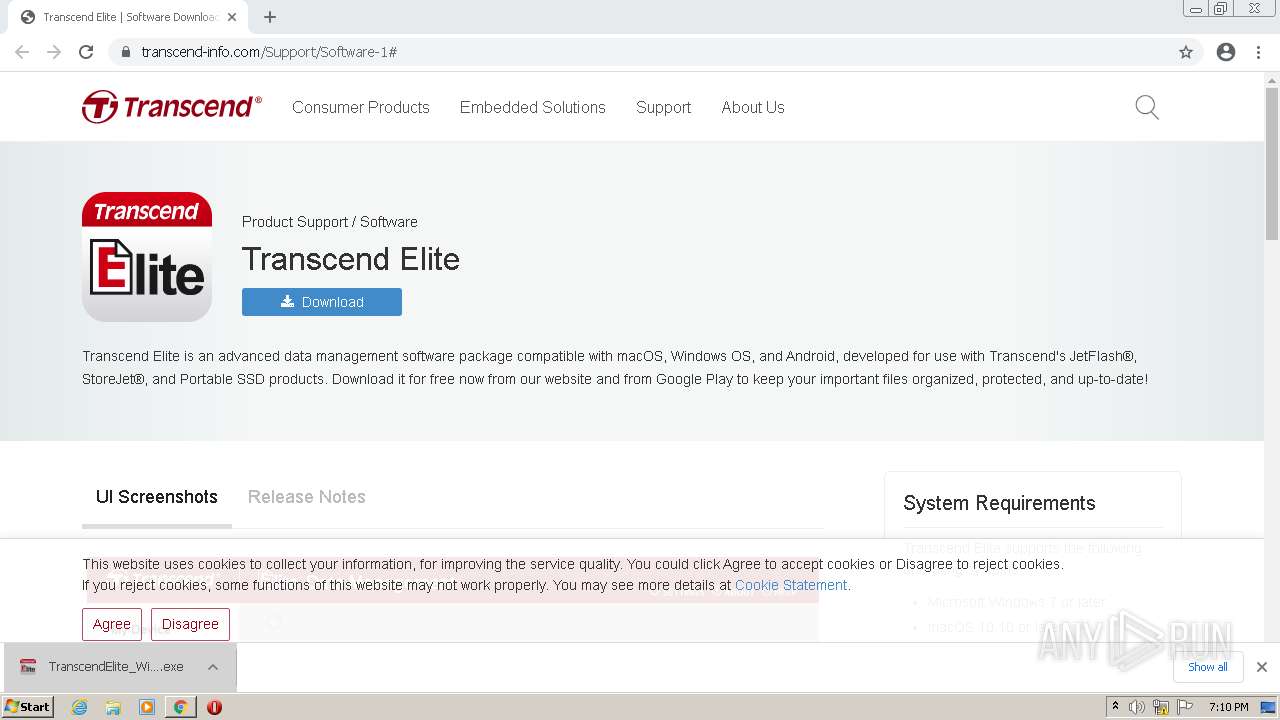
| URL: | https://www.transcend-info.com/Support/Software-1# |
| Full analysis: | https://app.any.run/tasks/5e0bec80-15c8-4888-a89d-aa60f2a1ce6c |
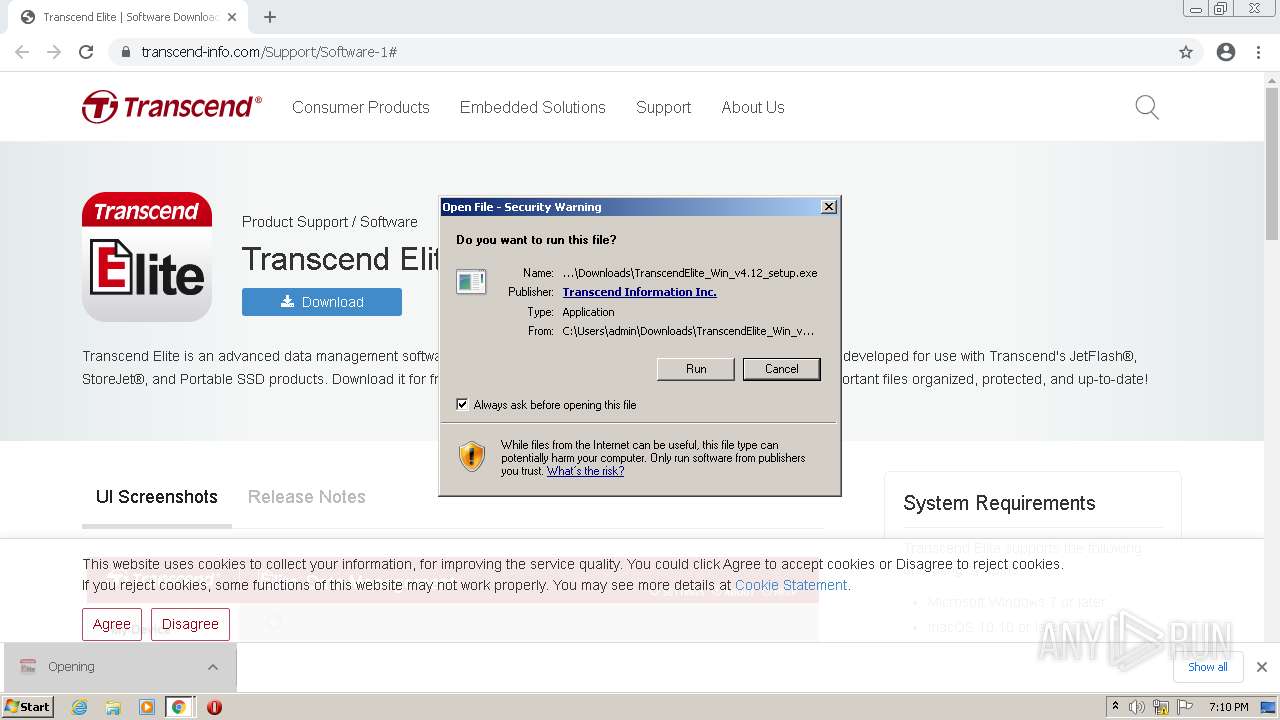
| Verdict: | Malicious activity |
| Analysis date: | May 20, 2022, 18:09:22 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 3218319DF696C586200E0FF642EF707A |
| SHA1: | 45B92AD7415838D55FBF7CD0D074405B0F1AB029 |
| SHA256: | 5C2D243975A0D298D8EA59F9643EC8D97D0AB644BD39B3E4BB94CDF8AA35E16E |
| SSDEEP: | 3:N8DSLIsDGX28mGn:2OLnDGHmG |
MALICIOUS
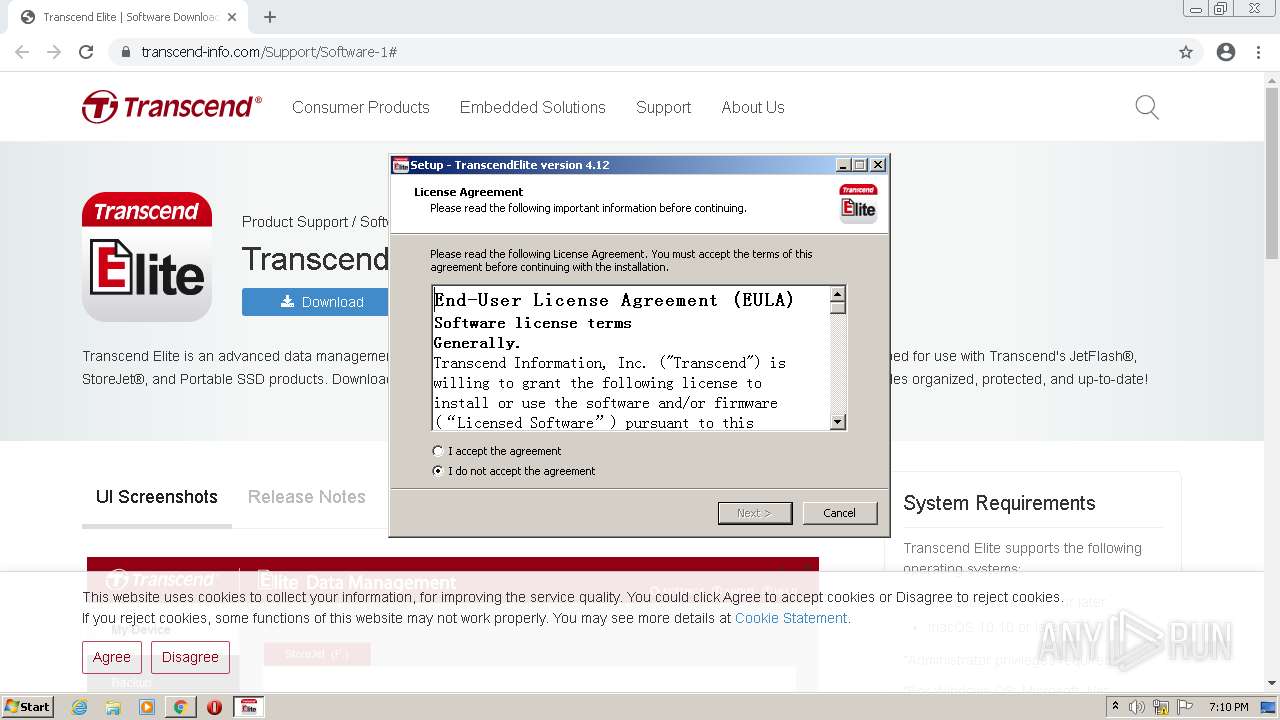
Drops executable file immediately after starts
- chrome.exe (PID: 2976)
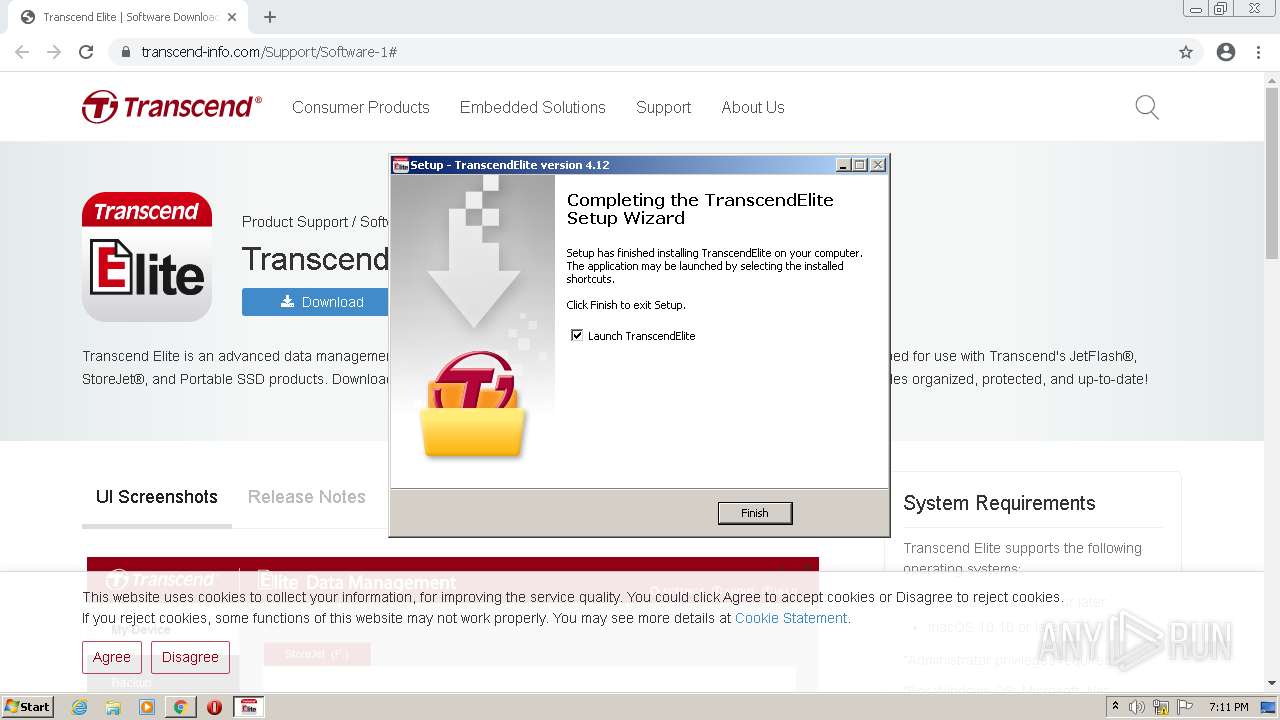
- TranscendElite_Win_v4.12_setup.exe (PID: 2700)
- TranscendElite_Win_v4.12_setup.exe (PID: 3412)
- TranscendElite_Win_v4.12_setup.tmp (PID: 2528)
- chrome.exe (PID: 2492)
Application was dropped or rewritten from another process
- TranscendElite_Win_v4.12_setup.exe (PID: 2700)
- TranscendElite_Win_v4.12_setup.exe (PID: 3412)
- OTBservice.exe (PID: 2004)
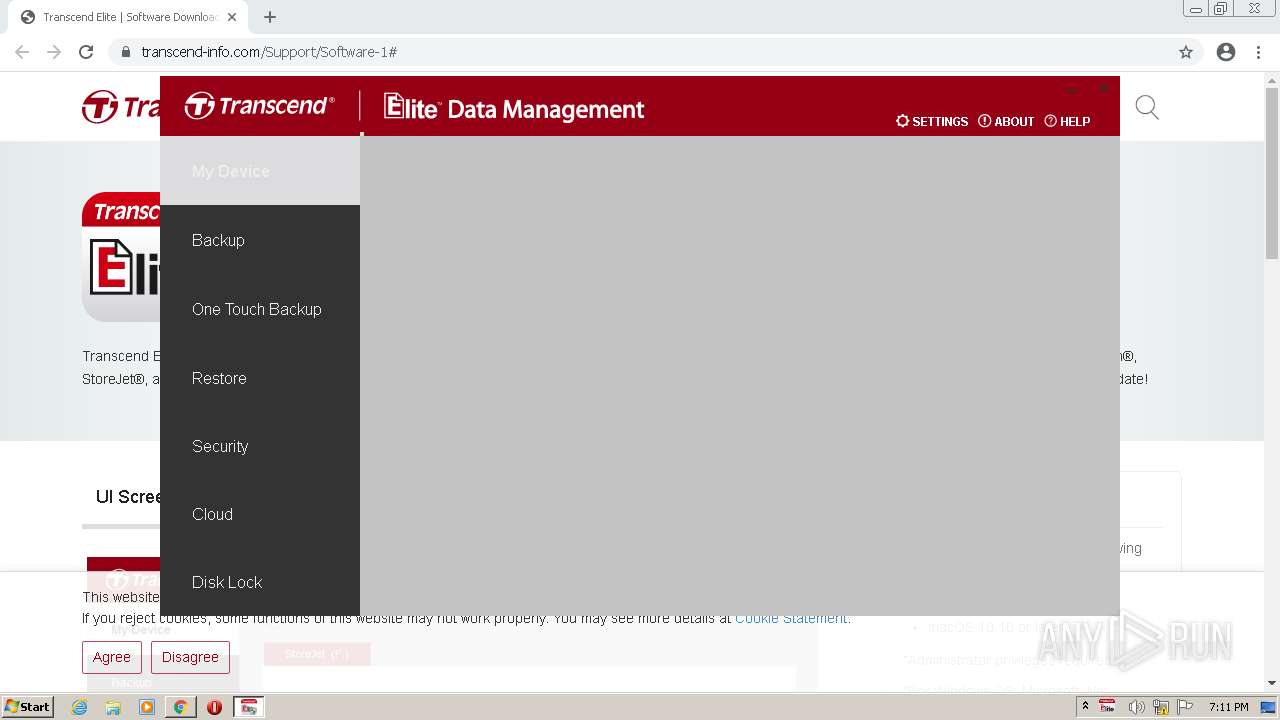
- TranscendElite.exe (PID: 1320)
- CefSharp.BrowserSubprocess.exe (PID: 3728)
Starts NET.EXE for service management
- TranscendElite_Win_v4.12_setup.tmp (PID: 2528)
Loads dropped or rewritten executable
- TranscendElite.exe (PID: 1320)
- CefSharp.BrowserSubprocess.exe (PID: 3728)
Changes settings of System certificates
- TranscendElite.exe (PID: 1320)
SUSPICIOUS
Modifies files in Chrome extension folder
- chrome.exe (PID: 2976)
Executable content was dropped or overwritten
- chrome.exe (PID: 2976)
- TranscendElite_Win_v4.12_setup.exe (PID: 2700)
- TranscendElite_Win_v4.12_setup.exe (PID: 3412)
- TranscendElite_Win_v4.12_setup.tmp (PID: 2528)
- chrome.exe (PID: 2492)
Drops a file with a compile date too recent
- chrome.exe (PID: 2976)
- TranscendElite_Win_v4.12_setup.exe (PID: 2700)
- TranscendElite_Win_v4.12_setup.exe (PID: 3412)
- TranscendElite_Win_v4.12_setup.tmp (PID: 2528)
- chrome.exe (PID: 2492)
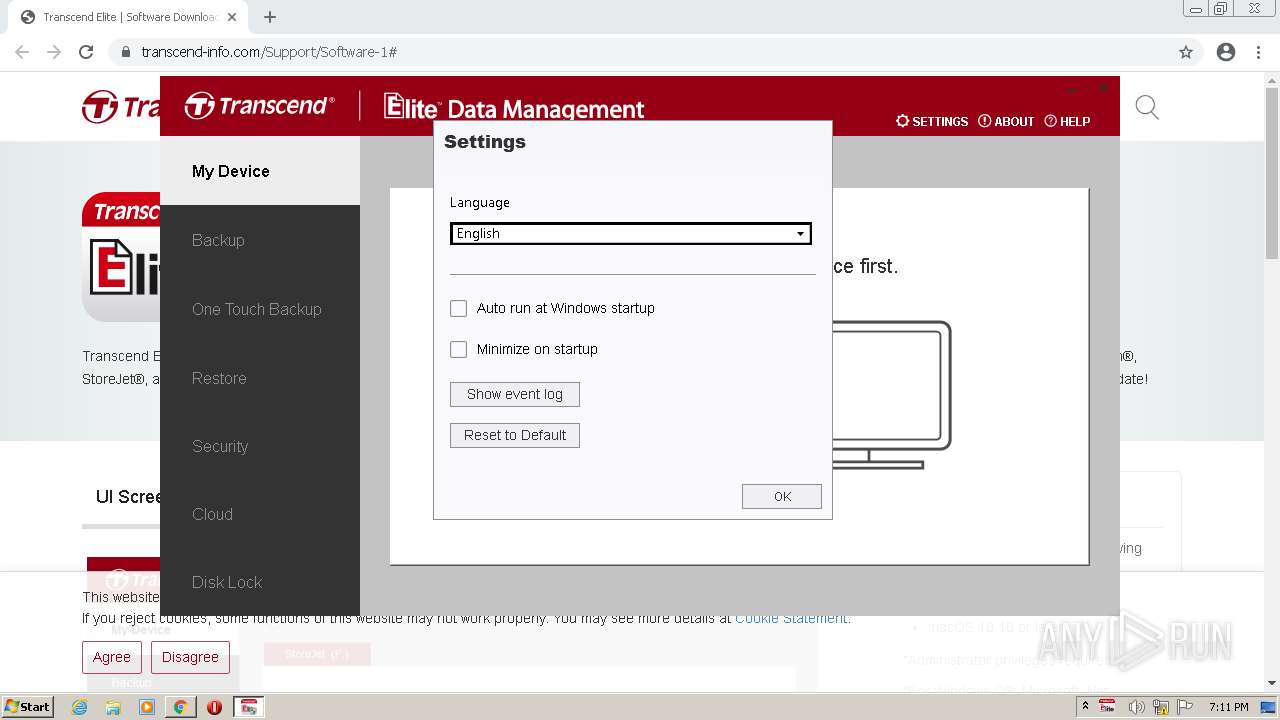
Checks supported languages
- TranscendElite_Win_v4.12_setup.exe (PID: 2700)
- TranscendElite_Win_v4.12_setup.tmp (PID: 4024)
- TranscendElite_Win_v4.12_setup.exe (PID: 3412)
- TranscendElite_Win_v4.12_setup.tmp (PID: 2528)
- InstallUtil.exe (PID: 3288)
- TranscendElite.exe (PID: 1320)
- OTBservice.exe (PID: 2004)
- CefSharp.BrowserSubprocess.exe (PID: 3728)
Reads the computer name
- TranscendElite_Win_v4.12_setup.tmp (PID: 4024)
- TranscendElite_Win_v4.12_setup.tmp (PID: 2528)
- InstallUtil.exe (PID: 3288)
- TranscendElite.exe (PID: 1320)
- CefSharp.BrowserSubprocess.exe (PID: 3728)
- OTBservice.exe (PID: 2004)
Reads the Windows organization settings
- TranscendElite_Win_v4.12_setup.tmp (PID: 2528)
Reads Windows owner or organization settings
- TranscendElite_Win_v4.12_setup.tmp (PID: 2528)
Uses TASKKILL.EXE to kill process
- TranscendElite_Win_v4.12_setup.tmp (PID: 2528)
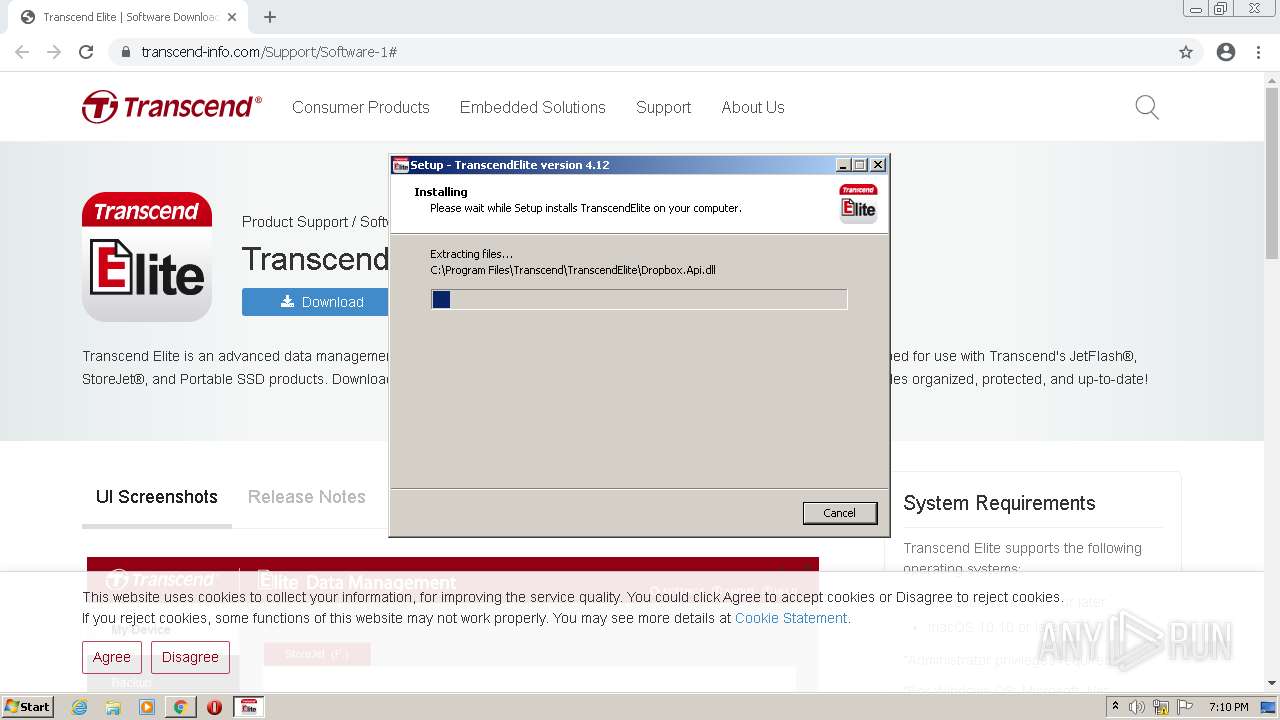
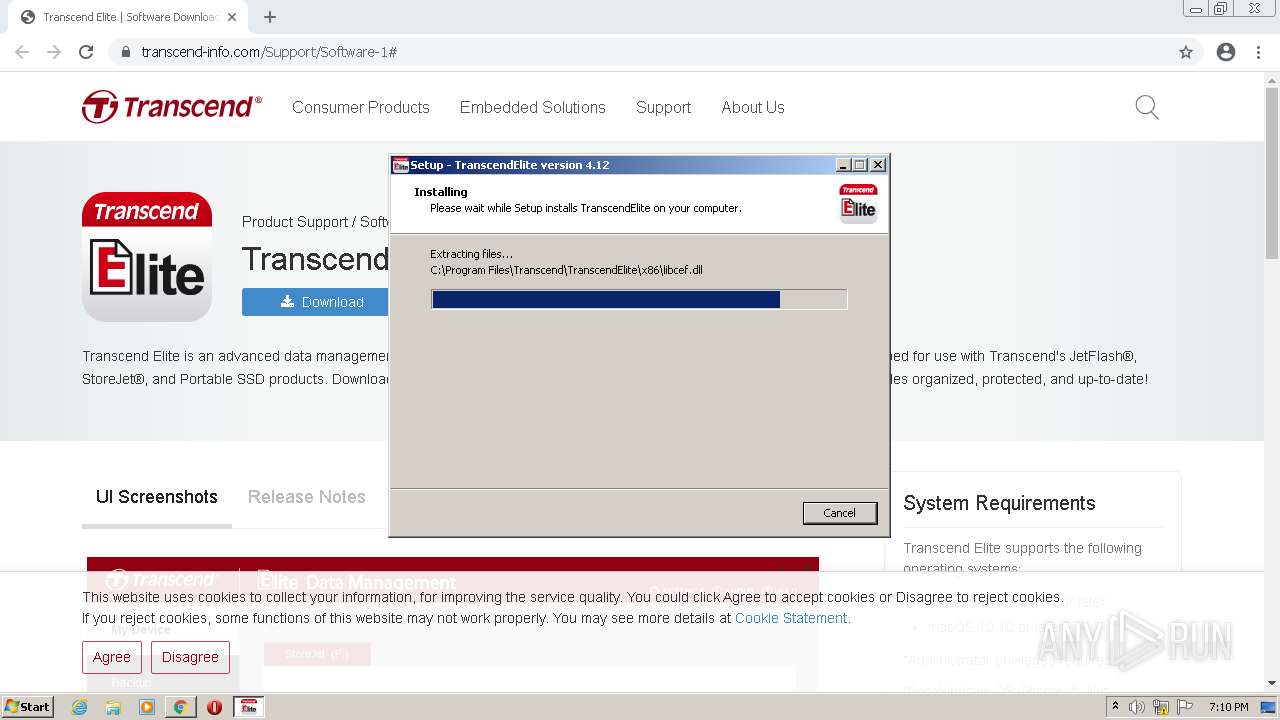
Creates a directory in Program Files
- TranscendElite_Win_v4.12_setup.tmp (PID: 2528)
Creates files in the Windows directory
- InstallUtil.exe (PID: 3288)
Creates files in the program directory
- InstallUtil.exe (PID: 3288)
- TranscendElite.exe (PID: 1320)
Executed as Windows Service
- OTBservice.exe (PID: 2004)
Adds / modifies Windows certificates
- TranscendElite.exe (PID: 1320)
Reads Environment values
- TranscendElite.exe (PID: 1320)
Starts Internet Explorer
- TranscendElite.exe (PID: 1320)
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 2268)
INFO
Checks supported languages
- chrome.exe (PID: 2976)
- chrome.exe (PID: 3272)
- chrome.exe (PID: 2180)
- chrome.exe (PID: 1848)
- chrome.exe (PID: 3612)
- chrome.exe (PID: 1024)
- chrome.exe (PID: 2560)
- chrome.exe (PID: 2960)
- chrome.exe (PID: 3052)
- chrome.exe (PID: 2364)
- chrome.exe (PID: 2036)
- chrome.exe (PID: 1280)
- chrome.exe (PID: 2440)
- chrome.exe (PID: 3144)
- chrome.exe (PID: 2984)
- chrome.exe (PID: 1532)
- chrome.exe (PID: 764)
- taskkill.exe (PID: 3452)
- net.exe (PID: 2280)
- net1.exe (PID: 2464)
- WISPTIS.EXE (PID: 2188)
- chrome.exe (PID: 660)
- iexplore.exe (PID: 3704)
- chrome.exe (PID: 2880)
- iexplore.exe (PID: 2268)
- chrome.exe (PID: 2716)
- chrome.exe (PID: 3932)
- chrome.exe (PID: 616)
- chrome.exe (PID: 2492)
- chrome.exe (PID: 4040)
- chrome.exe (PID: 2084)
Reads the hosts file
- chrome.exe (PID: 660)
- chrome.exe (PID: 2976)
- TranscendElite.exe (PID: 1320)
Application launched itself
- chrome.exe (PID: 2976)
- iexplore.exe (PID: 3704)
Reads the computer name
- chrome.exe (PID: 2976)
- chrome.exe (PID: 3612)
- chrome.exe (PID: 1848)
- chrome.exe (PID: 660)
- chrome.exe (PID: 2364)
- chrome.exe (PID: 2036)
- chrome.exe (PID: 1280)
- chrome.exe (PID: 2440)
- chrome.exe (PID: 2984)
- chrome.exe (PID: 764)
- taskkill.exe (PID: 3452)
- net1.exe (PID: 2464)
- WISPTIS.EXE (PID: 2188)
- iexplore.exe (PID: 3704)
- iexplore.exe (PID: 2268)
Reads settings of System Certificates
- chrome.exe (PID: 660)
- chrome.exe (PID: 2976)
- TranscendElite.exe (PID: 1320)
- iexplore.exe (PID: 2268)
- iexplore.exe (PID: 3704)
Checks Windows Trust Settings
- chrome.exe (PID: 2976)
- TranscendElite.exe (PID: 1320)
- iexplore.exe (PID: 2268)
- iexplore.exe (PID: 3704)
Reads the date of Windows installation
- chrome.exe (PID: 2440)
Application was dropped or rewritten from another process
- TranscendElite_Win_v4.12_setup.tmp (PID: 4024)
- TranscendElite_Win_v4.12_setup.tmp (PID: 2528)
Loads dropped or rewritten executable
- TranscendElite_Win_v4.12_setup.tmp (PID: 2528)
Creates a software uninstall entry
- TranscendElite_Win_v4.12_setup.tmp (PID: 2528)
Creates files in the program directory
- TranscendElite_Win_v4.12_setup.tmp (PID: 2528)
Dropped object may contain Bitcoin addresses
- TranscendElite_Win_v4.12_setup.tmp (PID: 2528)
Changes internet zones settings
- iexplore.exe (PID: 3704)
Adds / modifies Windows certificates
- iexplore.exe (PID: 2268)
Changes settings of System certificates
- iexplore.exe (PID: 2268)
Reads internet explorer settings
- iexplore.exe (PID: 2268)
Creates files in the user directory
- iexplore.exe (PID: 3704)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
86
Monitored processes
40
Malicious processes
8
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 616 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --field-trial-handle=1032,970760062285986978,3067390077234626027,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=1612 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 660 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --field-trial-handle=1032,970760062285986978,3067390077234626027,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --mojo-platform-channel-handle=1328 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 764 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=quarantine.mojom.Quarantine --field-trial-handle=1032,970760062285986978,3067390077234626027,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=2852 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1024 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1032,970760062285986978,3067390077234626027,131072 --enable-features=PasswordImport --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1860 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1280 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --field-trial-handle=1032,970760062285986978,3067390077234626027,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=1640 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
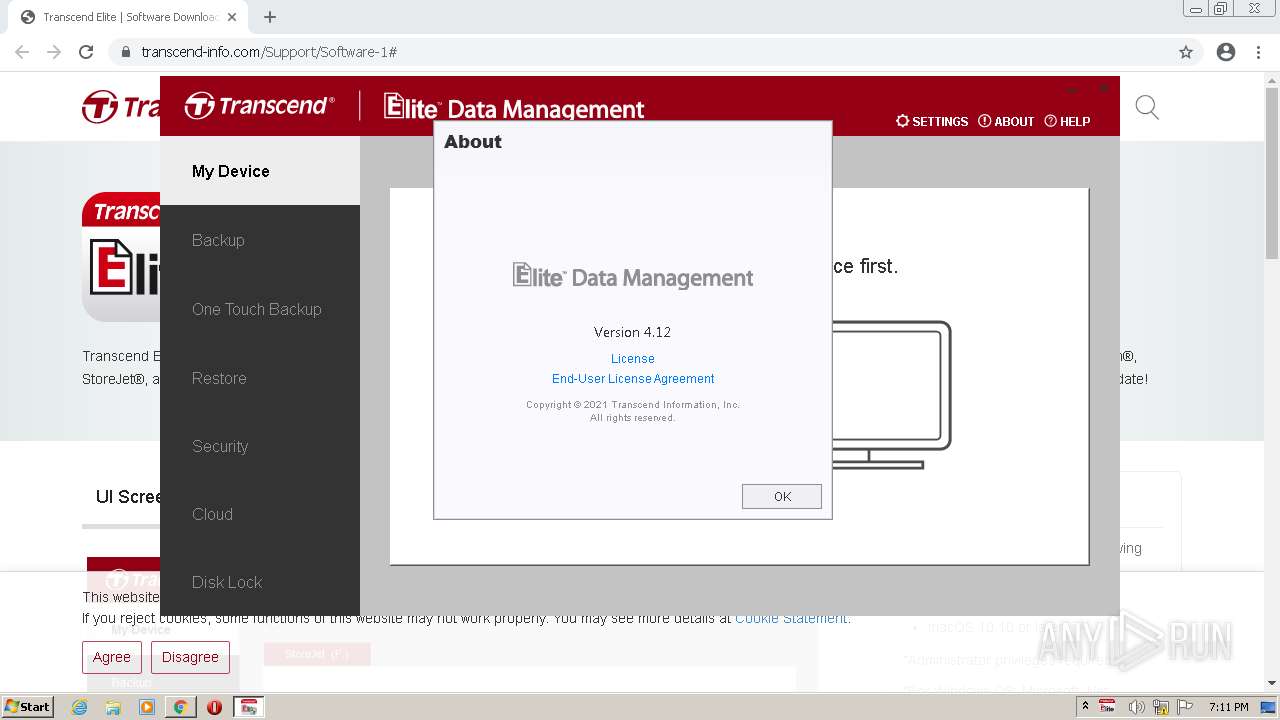
| 1320 | "C:\Program Files\Transcend\TranscendElite\TranscendElite.exe" | C:\Program Files\Transcend\TranscendElite\TranscendElite.exe | TranscendElite_Win_v4.12_setup.tmp | ||||||||||||
User: admin Company: Transcend Information, Inc. Integrity Level: HIGH Description: TranscendElite Exit code: 0 Version: 4.12 Modules
| |||||||||||||||
| 1532 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilReadIcon --field-trial-handle=1032,970760062285986978,3067390077234626027,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=icon_reader --mojo-platform-channel-handle=2772 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1848 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1032,970760062285986978,3067390077234626027,131072 --enable-features=PasswordImport --gpu-preferences=MAAAAAAAAADgACAwAAAAAAAAAAAAAAAAAABgAAAAAAAQAAAAAAAAAAAAAAAAAAAAKAAAAAQAAAAgAAAAAAAAACgAAAAAAAAAMAAAAAAAAAA4AAAAAAAAABAAAAAAAAAAAAAAAAUAAAAQAAAAAAAAAAAAAAAGAAAAEAAAAAAAAAABAAAABQAAABAAAAAAAAAAAQAAAAYAAAA= --use-gl=swiftshader-webgl --mojo-platform-channel-handle=1088 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 2004 | "C:\Program Files\Transcend\TranscendElite\OTBservice.exe" | C:\Program Files\Transcend\TranscendElite\OTBservice.exe | services.exe | ||||||||||||
User: SYSTEM Integrity Level: SYSTEM Description: OTBservice Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 2036 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --field-trial-handle=1032,970760062285986978,3067390077234626027,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=3164 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
Total events
42 546
Read events
42 094
Write events
441
Delete events
11
Modification events
| (PID) Process: | (2976) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2976) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2976) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2976) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2976) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2976) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2976) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2976) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (2976) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid |
Value: | |||
| (PID) Process: | (2976) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid_installdate |
Value: 0 | |||
Executable files
167
Suspicious files
69
Text files
189
Unknown types
136
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2976 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-6287D956-BA0.pma | — | |
MD5:— | SHA256:— | |||
| 2976 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Preferences | text | |
MD5:— | SHA256:— | |||
| 2976 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\bb78a5ad-8f36-4851-b811-50d836a3c74c.tmp | text | |
MD5:— | SHA256:— | |||
| 2976 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RFfd400.TMP | text | |
MD5:64AD8ED3E666540337BA541C549F72F7 | SHA256:BECBDB08B5B37D203A85F2E974407334053BB1D2270F0B3C9A4DB963896F2206 | |||
| 2976 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Local Storage\leveldb\LOG.old | text | |
MD5:7721CDA9F5B73CE8A135471EB53B4E0E | SHA256:DD730C576766A46FFC84E682123248ECE1FF1887EC0ACAB22A5CE93A450F4500 | |||
| 2976 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RFfd400.TMP | text | |
MD5:936EB7280DA791E6DD28EF3A9B46D39C | SHA256:CBAF2AFD831B32F6D1C12337EE5D2F090D6AE1F4DCB40B08BEF49BF52AD9721F | |||
| 2976 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Last Version | text | |
MD5:00046F773EFDD3C8F8F6D0F87A2B93DC | SHA256:593EDE11D17AF7F016828068BCA2E93CF240417563FB06DC8A579110AEF81731 | |||
| 2976 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Platform Notifications\LOG.old~RFfd596.TMP | text | |
MD5:109A25C32EE1132ECD6D9F3ED9ADF01A | SHA256:DA6028DB9485C65E683643658326F02B1D0A1566DE14914EF28E5248EB94F0DD | |||
| 2976 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Extension State\LOG.old~RFfdbc0.TMP | text | |
MD5:D097F8EB2230B3F32C41C5D75790508C | SHA256:ADDF87D20CD455CFB4AACB6B76719629C0277A4CF70B496343047BB73ABBAEF5 | |||
| 2976 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\6a88fce2-cda1-4d58-afb0-a8e9a66702ae.tmp | binary | |
MD5:5058F1AF8388633F609CADB75A75DC9D | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
35
TCP/UDP connections
70
DNS requests
33
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | — | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adktovjj3t3n7jwiiegl5h6y3v5q_1.3.36.121/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.121_win_bxugoraqoudfswxg22hsatfdbi.crx3 | US | — | — | whitelisted |
— | — | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adktovjj3t3n7jwiiegl5h6y3v5q_1.3.36.121/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.121_win_bxugoraqoudfswxg22hsatfdbi.crx3 | US | — | — | whitelisted |
2268 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEAo3h2ReX7SMIk79G%2B0UDDw%3D | US | der | 1.47 Kb | whitelisted |
2976 | chrome.exe | GET | 200 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?97777d2712ae290e | US | compressed | 60.0 Kb | whitelisted |
— | — | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adktovjj3t3n7jwiiegl5h6y3v5q_1.3.36.121/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.121_win_bxugoraqoudfswxg22hsatfdbi.crx3 | US | binary | 7.54 Kb | whitelisted |
— | — | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adktovjj3t3n7jwiiegl5h6y3v5q_1.3.36.121/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.121_win_bxugoraqoudfswxg22hsatfdbi.crx3 | US | binary | 5.64 Kb | whitelisted |
— | — | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adktovjj3t3n7jwiiegl5h6y3v5q_1.3.36.121/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.121_win_bxugoraqoudfswxg22hsatfdbi.crx3 | US | binary | 11.3 Kb | whitelisted |
— | — | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adktovjj3t3n7jwiiegl5h6y3v5q_1.3.36.121/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.121_win_bxugoraqoudfswxg22hsatfdbi.crx3 | US | binary | 32.9 Kb | whitelisted |
3704 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAqvpsXKY8RRQeo74ffHUxc%3D | US | der | 471 b | whitelisted |
— | — | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adktovjj3t3n7jwiiegl5h6y3v5q_1.3.36.121/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.121_win_bxugoraqoudfswxg22hsatfdbi.crx3 | US | binary | 15.6 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
660 | chrome.exe | 142.250.186.78:443 | clients2.google.com | Google Inc. | US | whitelisted |
660 | chrome.exe | 220.128.205.242:443 | www.transcend-info.com | Data Communication Business Group | TW | suspicious |
660 | chrome.exe | 142.250.186.109:443 | accounts.google.com | Google Inc. | US | whitelisted |
— | — | 142.250.186.109:443 | accounts.google.com | Google Inc. | US | whitelisted |
660 | chrome.exe | 172.217.23.97:443 | clients2.googleusercontent.com | Google Inc. | US | whitelisted |
— | — | 172.217.23.97:443 | clients2.googleusercontent.com | Google Inc. | US | whitelisted |
660 | chrome.exe | 168.95.245.1:443 | cdn.transcend-info.com | Data Communication Business Group | TW | suspicious |
660 | chrome.exe | 142.250.186.42:443 | content-autofill.googleapis.com | Google Inc. | US | whitelisted |
660 | chrome.exe | 142.250.186.67:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
660 | chrome.exe | 142.250.186.110:443 | sb-ssl.google.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clients2.google.com |
| whitelisted |
www.transcend-info.com |
| suspicious |
accounts.google.com |
| shared |
clients2.googleusercontent.com |
| whitelisted |
cdn.transcend-info.com |
| suspicious |
content-autofill.googleapis.com |
| whitelisted |
ssl.gstatic.com |
| whitelisted |
sb-ssl.google.com |
| whitelisted |
secure.globalsign.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
Threats
Process | Message |
|---|---|
OTBservice.exe |
MSG::CAsmtUSBDev::EnumerateHostController:1030: EnumerateHostController: HCD DriverKey Name is {36fc9e60-c465-11cf-8056-444553540000}\0000 |
OTBservice.exe |
MSG::CAsmtUSBDev::EnumerateHostController:1031: EnumerateHostController: HCD Device Desc is Intel(R) ICH9 Family USB Universal Host Controller - 2934 |
OTBservice.exe |
MSG::CAsmtUSBDev::EnumerateHostController:1032: EnumerateHostController: HARDWARE ID is PCI\VEN_8086&DEV_2934&SUBSYS_11001AF4&REV_03 |
OTBservice.exe |
MSG::CAsmtUSBDev::GetRootHubName:973: this->strRootHubName[\\.\USB#ROOT_HUB#4&c55b0f1&0#{f18a0e88-c30c-11d0-8815-00a0c906bed8}] |
OTBservice.exe |
MSG::CAsmtUSBDev::EnumerateHostController:1041: EnumerateHostController: Root hub name is \\.\USB#ROOT_HUB#4&c55b0f1&0#{f18a0e88-c30c-11d0-8815-00a0c906bed8} |
OTBservice.exe |
MSG::CAsmtUSBDev::GetPortData:1141: In GetPortData with fHandle = 368, ulPortCount = 2, iHubDepth = 0 |
OTBservice.exe |
MSG::CAsmtUSBDev::GetPortData:1202: GetPortData: DriverKeyName = {745a17a0-74d3-11d0-b6fe-00a0c90f57da}\0000 , Desc = USB Input Device , |
OTBservice.exe |
MSG::CAsmtUSBDev::GetDeviceDescriptor:1603: GetDeviceDescriptor:
Device Descriptor
bLength 12
bDescriptorType 01
bcdUSB 0100
bDeviceClass 00
bDeviceSubClass 00
bDeviceProtocol 00
bMaxEP0Size 08
wVendorID 0627 [27]
wProductID 0001 [01]
wDeviceID 0000 [00]
Tmp 01
iManufacturer QEMU
Tmp 03
iProduct QEMU USB Tablet
Tmp 0a
iSerialNumber 42
bNumConfigurations 01 |
OTBservice.exe |
MSG::CAsmtUSBDev::ucGetPhysicalAddressFromSN:5917: : SPDRP_CLASSGUID {36fc9e60-c465-11cf-8056-444553540000} |
OTBservice.exe |
MSG::CAsmtUSBDev::ucGetPhysicalAddressFromSN:5921: : SPDRP_ADDRESS 0 4 |