| File name: | SpySheriff.exe |
| Full analysis: | https://app.any.run/tasks/86ee148b-5dda-4132-9069-ba0e5fe8d976 |
| Verdict: | Malicious activity |
| Analysis date: | June 23, 2025, 16:24:37 |
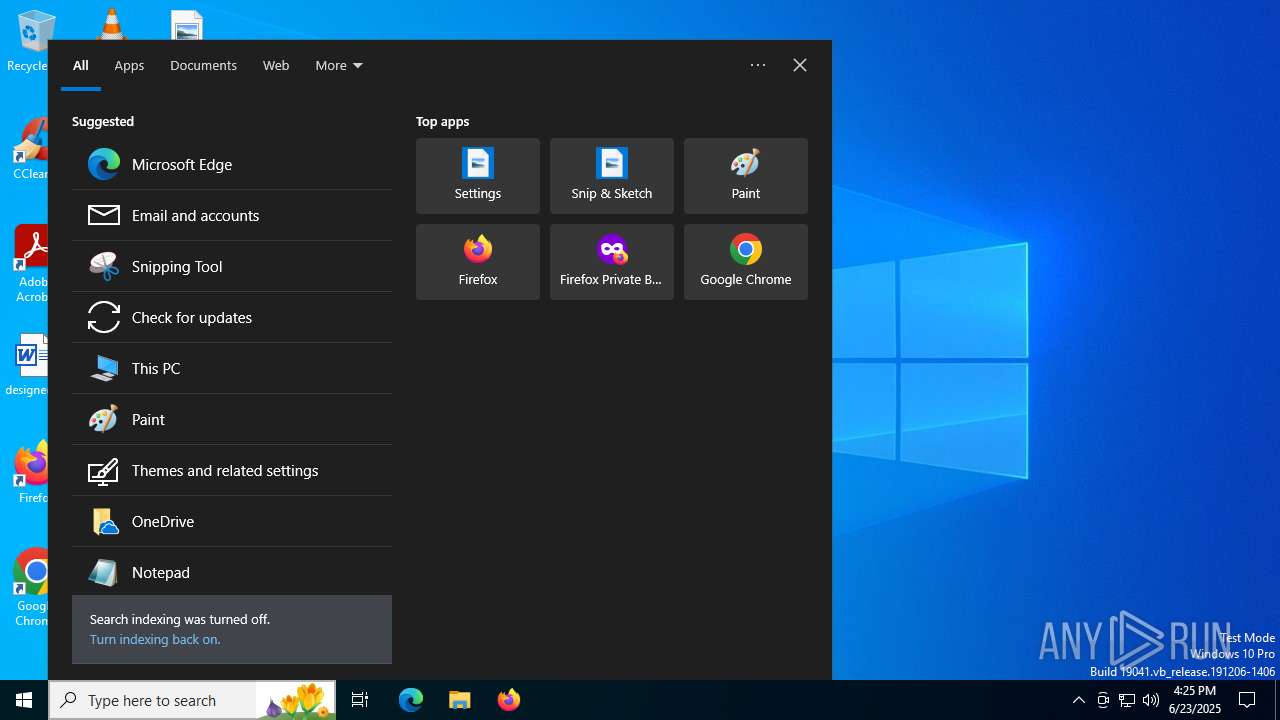
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 5 sections |
| MD5: | C899F93E8B753FEDD068EF3FE2EDB0FD |
| SHA1: | 144B1F18D0E307D14937C21CA1D7CBFC91828A10 |
| SHA256: | 5C2A85FB56DE2E0A1A1D260EF2177E0209477586C8A6740494BBAF40A9785F47 |
| SSDEEP: | 12288:eBMDMf+ztV53y2k9I68iXDycz+rYIYsVRSHsDrL:eS4S53h68eIZjDP |
MALICIOUS
Changes the autorun value in the registry
- SpySheriff.exe (PID: 1520)
Scans artifacts that could help determine the target
- SpySheriff.exe (PID: 1520)
SUSPICIOUS
Creates file in the systems drive root
- SpySheriff.exe (PID: 1520)
Reads Internet Explorer settings
- SpySheriff.exe (PID: 1520)
Reads security settings of Internet Explorer
- SpySheriff.exe (PID: 1520)
The process executes via Task Scheduler
- updater.exe (PID: 1324)
Application launched itself
- updater.exe (PID: 1324)
Checks for Java to be installed
- SpySheriff.exe (PID: 1520)
PSEXEC has been detected
- SpySheriff.exe (PID: 1520)
Checks for the .NET to be installed
- SpySheriff.exe (PID: 1520)
Reads Microsoft Outlook installation path
- SpySheriff.exe (PID: 1520)
Reads the history of recent RDP connections
- SpySheriff.exe (PID: 1520)
The process checks if it is being run in the virtual environment
- SpySheriff.exe (PID: 1520)
Check the default browser
- SpySheriff.exe (PID: 1520)
Searches for installed software
- SpySheriff.exe (PID: 1520)
INFO
Launching a file from a Registry key
- SpySheriff.exe (PID: 1520)
Checks supported languages
- SpySheriff.exe (PID: 1520)
- updater.exe (PID: 3884)
- updater.exe (PID: 1324)
Reads the computer name
- SpySheriff.exe (PID: 1520)
- updater.exe (PID: 1324)
Reads mouse settings
- SpySheriff.exe (PID: 1520)
Process checks computer location settings
- SpySheriff.exe (PID: 1520)
Reads Microsoft Office registry keys
- SpySheriff.exe (PID: 1520)
Checks proxy server information
- SpySheriff.exe (PID: 1520)
- slui.exe (PID: 5424)
Process checks whether UAC notifications are on
- SpySheriff.exe (PID: 1520)
- updater.exe (PID: 1324)
Reads the software policy settings
- SpySheriff.exe (PID: 1520)
- slui.exe (PID: 5424)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable (generic) (52.9) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (23.5) |
| .exe | | | DOS Executable Generic (23.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2006:02:24 11:33:55+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 698368 |
| InitializedDataSize: | 420290560 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1000 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Total processes
142
Monitored processes
4
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1324 | "C:\Program Files (x86)\Google\GoogleUpdater\134.0.6985.0\updater.exe" --wake --system | C:\Program Files (x86)\Google\GoogleUpdater\134.0.6985.0\updater.exe | — | svchost.exe | |||||||||||
User: SYSTEM Company: Google LLC Integrity Level: SYSTEM Description: Google Updater Exit code: 0 Version: 134.0.6985.0 Modules
| |||||||||||||||
| 1520 | "C:\Users\admin\AppData\Local\Temp\SpySheriff.exe" | C:\Users\admin\AppData\Local\Temp\SpySheriff.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Modules
| |||||||||||||||
| 3884 | "C:\Program Files (x86)\Google\GoogleUpdater\134.0.6985.0\updater.exe" --crash-handler --system "--database=C:\Program Files (x86)\Google\GoogleUpdater\134.0.6985.0\Crashpad" --url=https://clients2.google.com/cr/report --annotation=prod=Update4 --annotation=ver=134.0.6985.0 "--attachment=C:\Program Files (x86)\Google\GoogleUpdater\updater.log" --initial-client-data=0x298,0x29c,0x2a0,0x274,0x2a4,0x111c460,0x111c46c,0x111c478 | C:\Program Files (x86)\Google\GoogleUpdater\134.0.6985.0\updater.exe | — | updater.exe | |||||||||||
User: SYSTEM Company: Google LLC Integrity Level: SYSTEM Description: Google Updater Exit code: 0 Version: 134.0.6985.0 Modules
| |||||||||||||||
| 5424 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
163 559
Read events
163 535
Write events
24
Delete events
0
Modification events
| (PID) Process: | (1520) SpySheriff.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\SpySheriff |
| Operation: | write | Name: | ScanOnStartup |
Value: 1 | |||
| (PID) Process: | (1520) SpySheriff.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\SpySheriff |
| Operation: | write | Name: | PlaySounds |
Value: 1 | |||
| (PID) Process: | (1520) SpySheriff.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\SpySheriff |
| Operation: | write | Name: | ScheduledScan |
Value: 0 | |||
| (PID) Process: | (1520) SpySheriff.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\SpySheriff |
| Operation: | write | Name: | ScheduledScanHour |
Value: 0 | |||
| (PID) Process: | (1520) SpySheriff.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\SpySheriff |
| Operation: | write | Name: | ScheduledScanMin |
Value: 0 | |||
| (PID) Process: | (1520) SpySheriff.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\SpySheriff |
| Operation: | write | Name: | SecurityLevel |
Value: 2 | |||
| (PID) Process: | (1520) SpySheriff.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\SpySheriff |
| Operation: | write | Name: | Uninstall |
Value: C:\Users\admin\AppData\Local\Temp | |||
| (PID) Process: | (1520) SpySheriff.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\SpySheriff\IE Security |
| Operation: | write | Name: | BlockIframeTags |
Value: 0 | |||
| (PID) Process: | (1520) SpySheriff.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\SpySheriff\IE Security |
| Operation: | write | Name: | BlockJavascripts |
Value: 0 | |||
| (PID) Process: | (1520) SpySheriff.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\SpySheriff\IE Security |
| Operation: | write | Name: | BlockLocations |
Value: 0 | |||
Executable files
0
Suspicious files
0
Text files
1
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3884 | updater.exe | C:\Program Files (x86)\Google\GoogleUpdater\updater.log | text | |
MD5:795986107FEA58B324C602045CBD3294 | SHA256:0A8844B64197005D9B4F348910AE9FBD76B3FF99E0622CA758D37F91566DA21F | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
36
DNS requests
20
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5328 | SearchApp.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 184.24.77.39:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6796 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
6796 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
5080 | svchost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
2940 | svchost.exe | GET | 200 | 23.209.209.135:80 | http://x1.c.lencr.org/ | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
5944 | MoUsoCoreWorker.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1268 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
3924 | RUXIMICS.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1268 | svchost.exe | 184.24.77.39:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
1268 | svchost.exe | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
5328 | SearchApp.exe | 2.16.241.218:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
5328 | SearchApp.exe | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
5328 | SearchApp.exe | 2.16.241.207:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
th.bing.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |