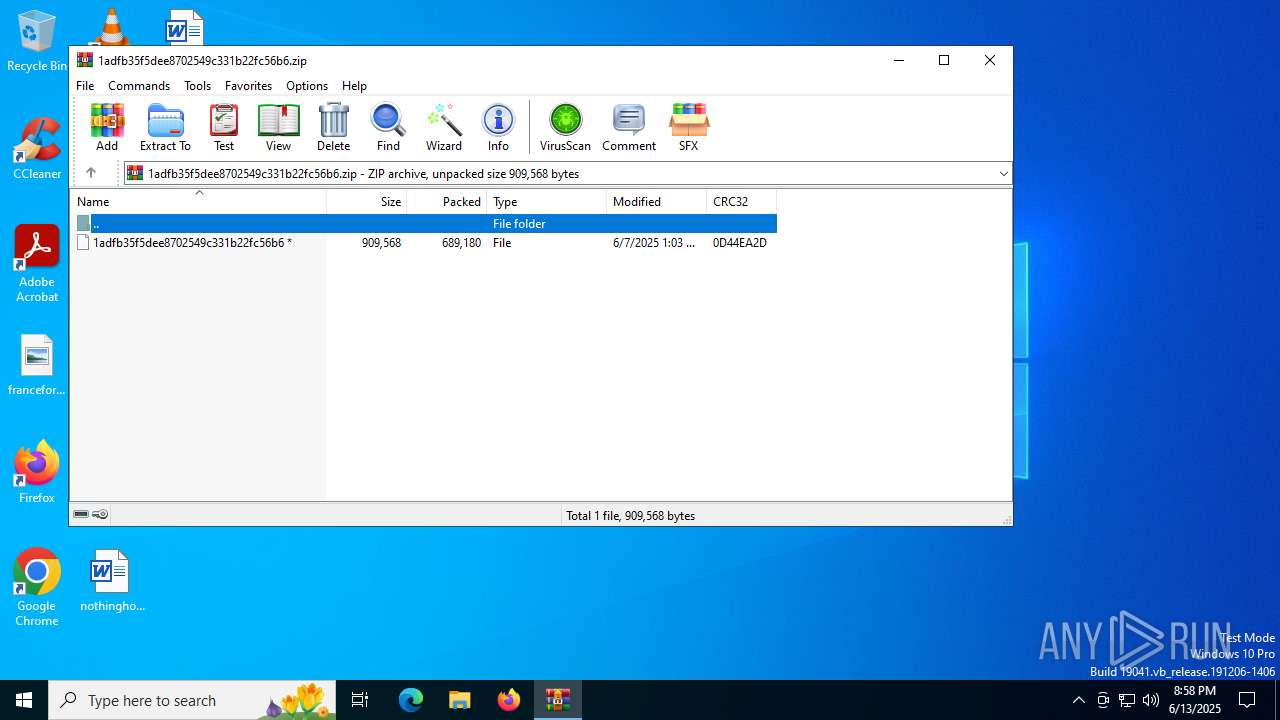
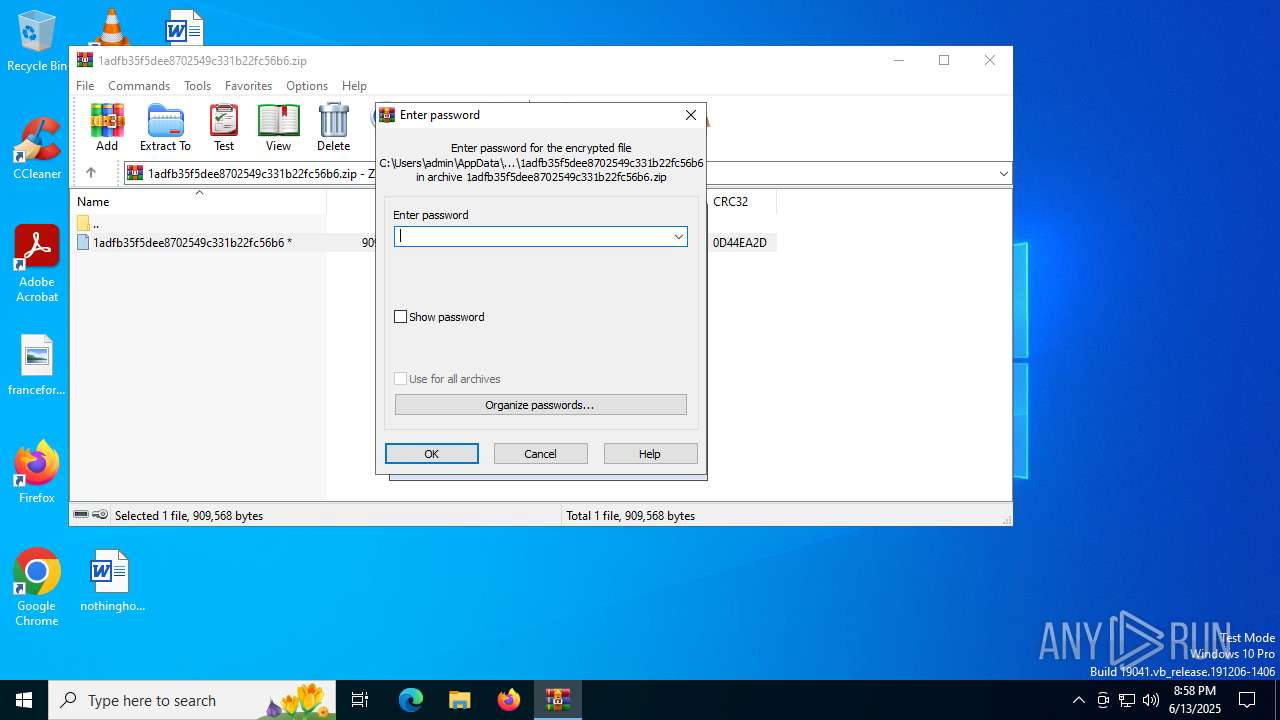
| File name: | 1adfb35f5dee8702549c331b22fc56b6.zip |
| Full analysis: | https://app.any.run/tasks/9dcf2203-848b-4589-bd87-f0660e869821 |
| Verdict: | Malicious activity |
| Analysis date: | June 13, 2025, 20:57:58 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract, compression method=deflate |
| MD5: | 3F95AB5EAA58F58D67F2F45C7EF722A4 |
| SHA1: | 9DC2E3FF1EBC8090421F8B6DA8D3D707E4DDB1DE |
| SHA256: | 5C21F7F8634EBEF842C2C1BA9AB41BF2BE6BB1A207AEF13B0C2BD78B34107E03 |
| SSDEEP: | 24576:uUmdefgbHvaRu/jBm08v7ZII/R/68ayyutWUWKK5bv4LOPLEjgLw:nmdefgbHvaRu/jB2v7ZII/R/68ay7tWM |
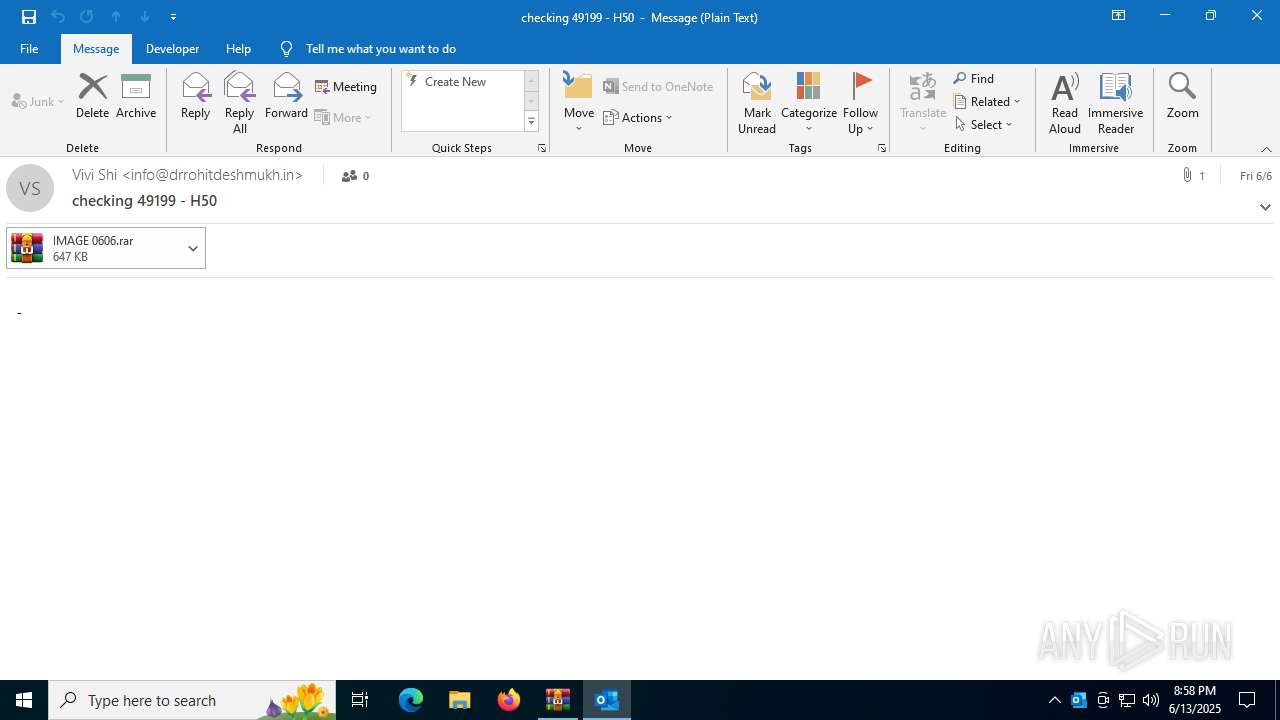
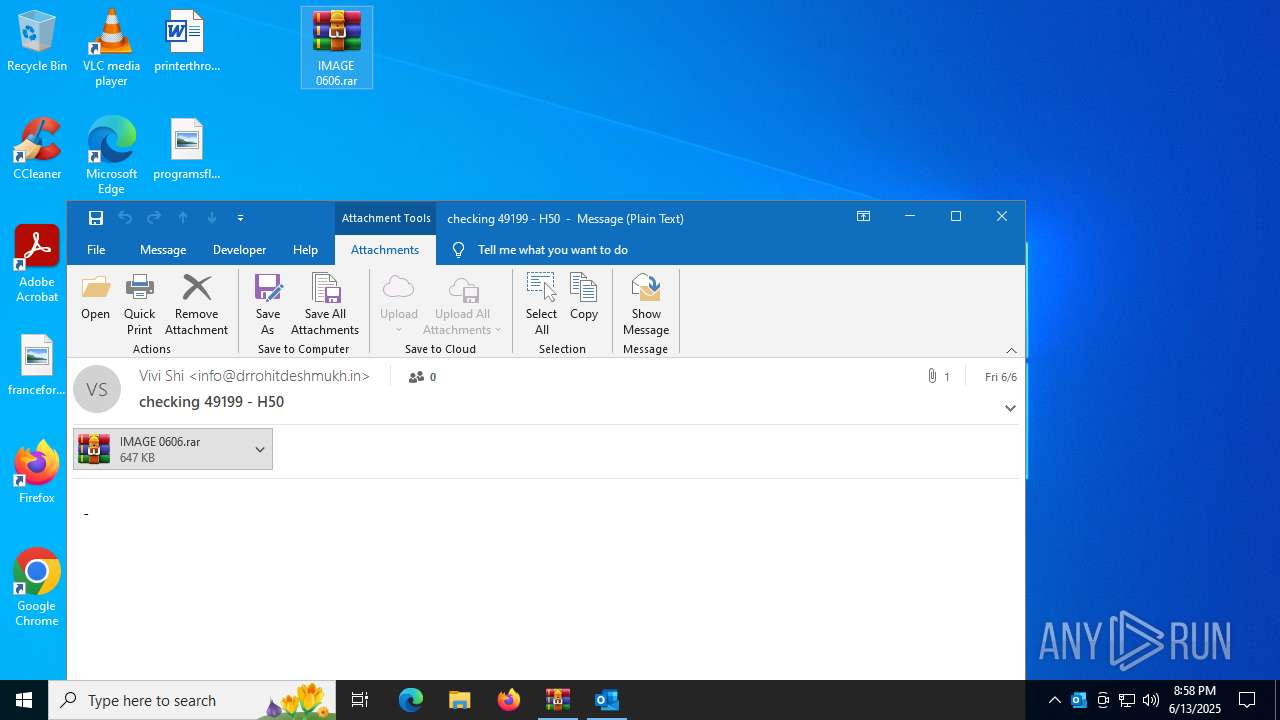
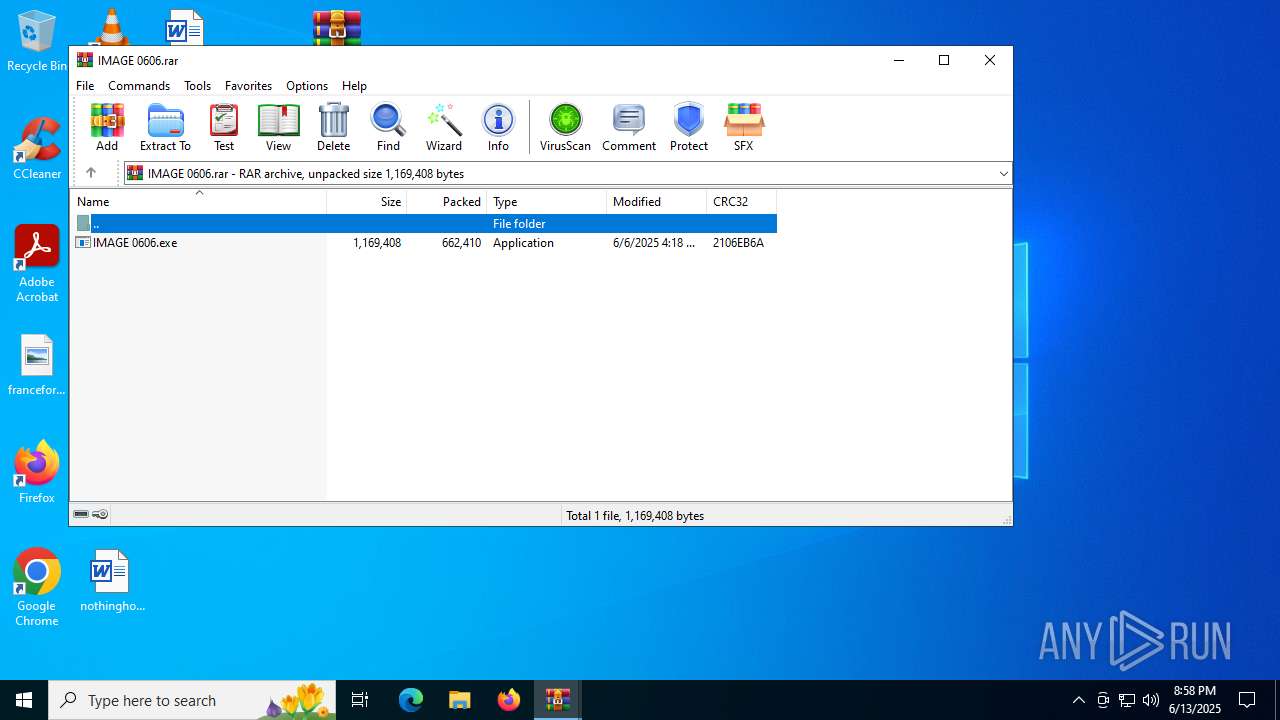
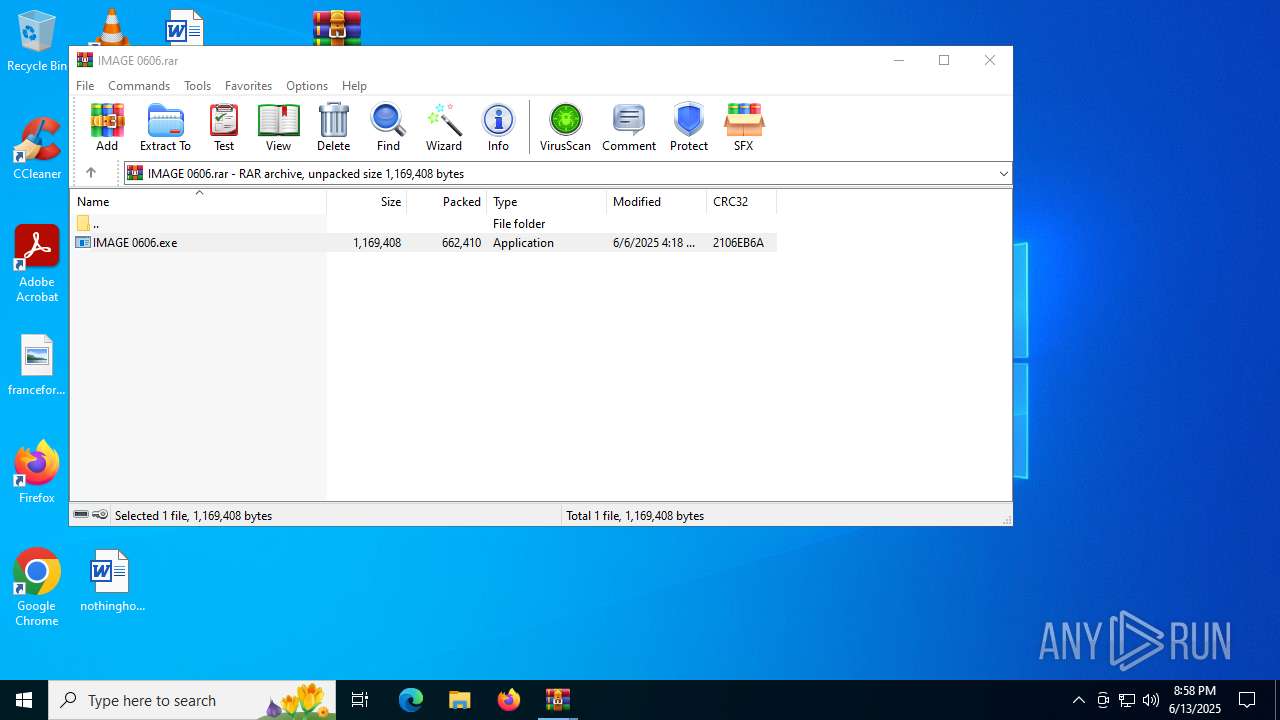
MALICIOUS
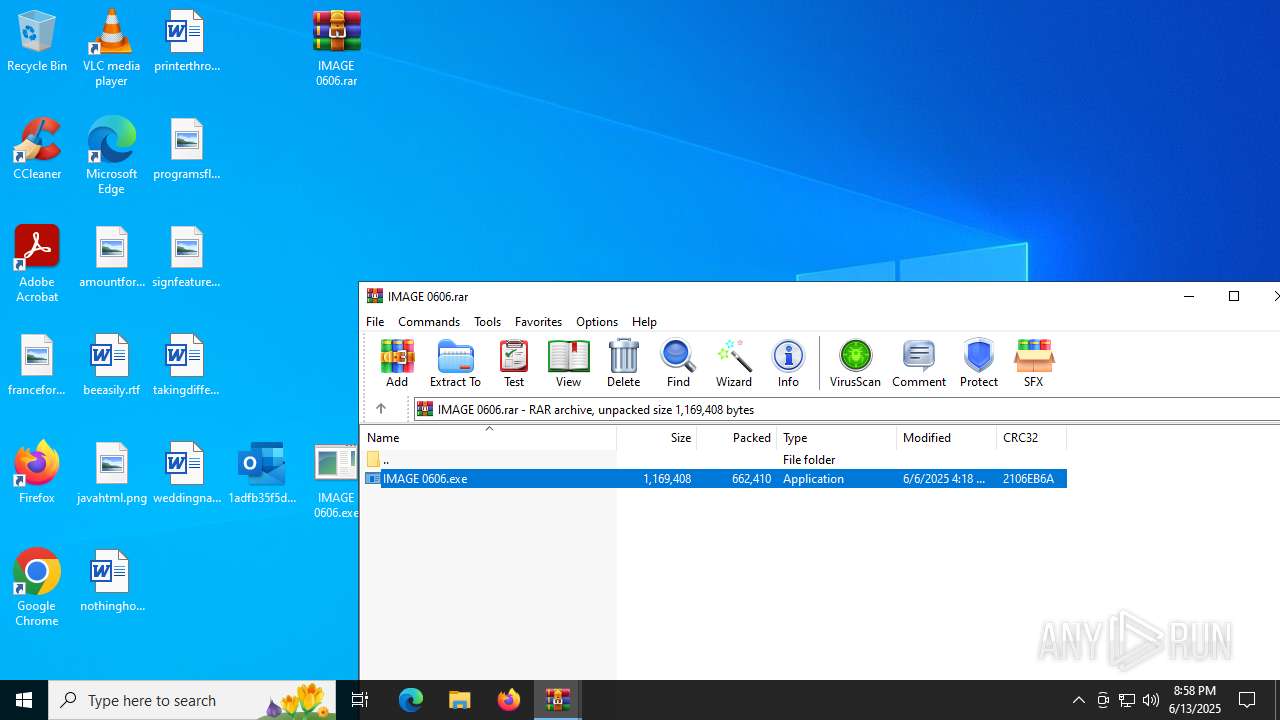
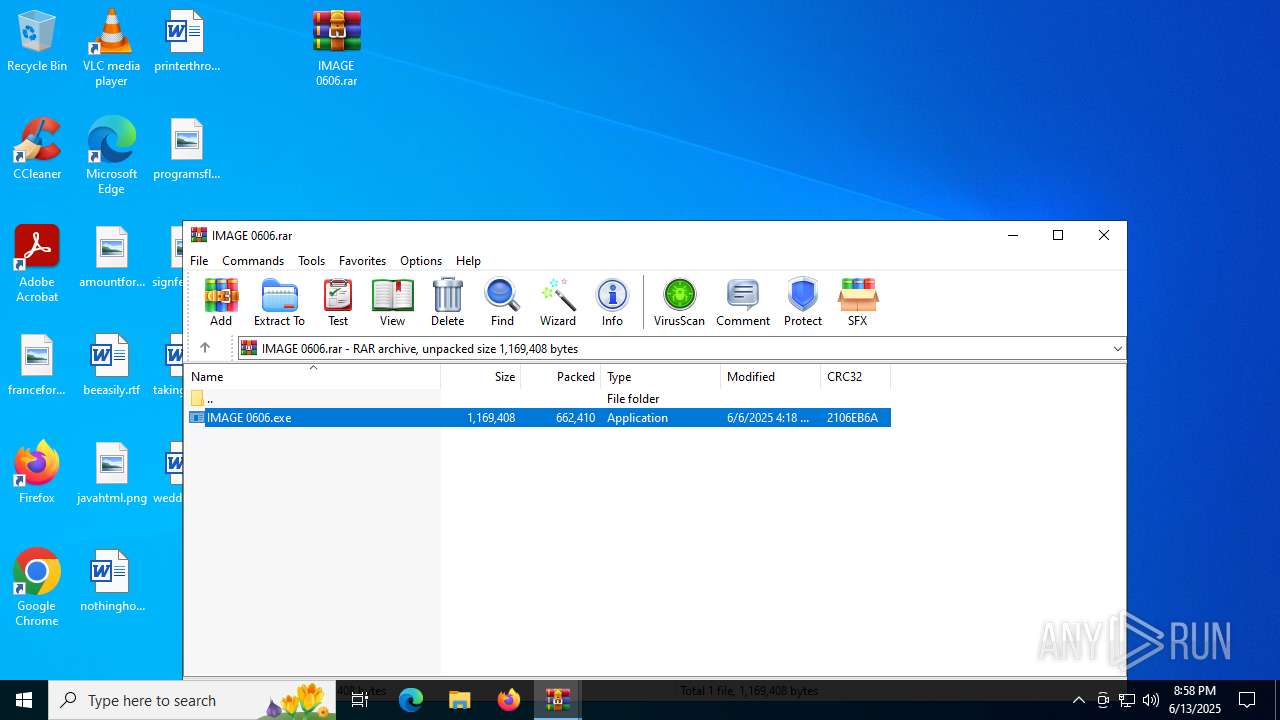
Generic archive extractor
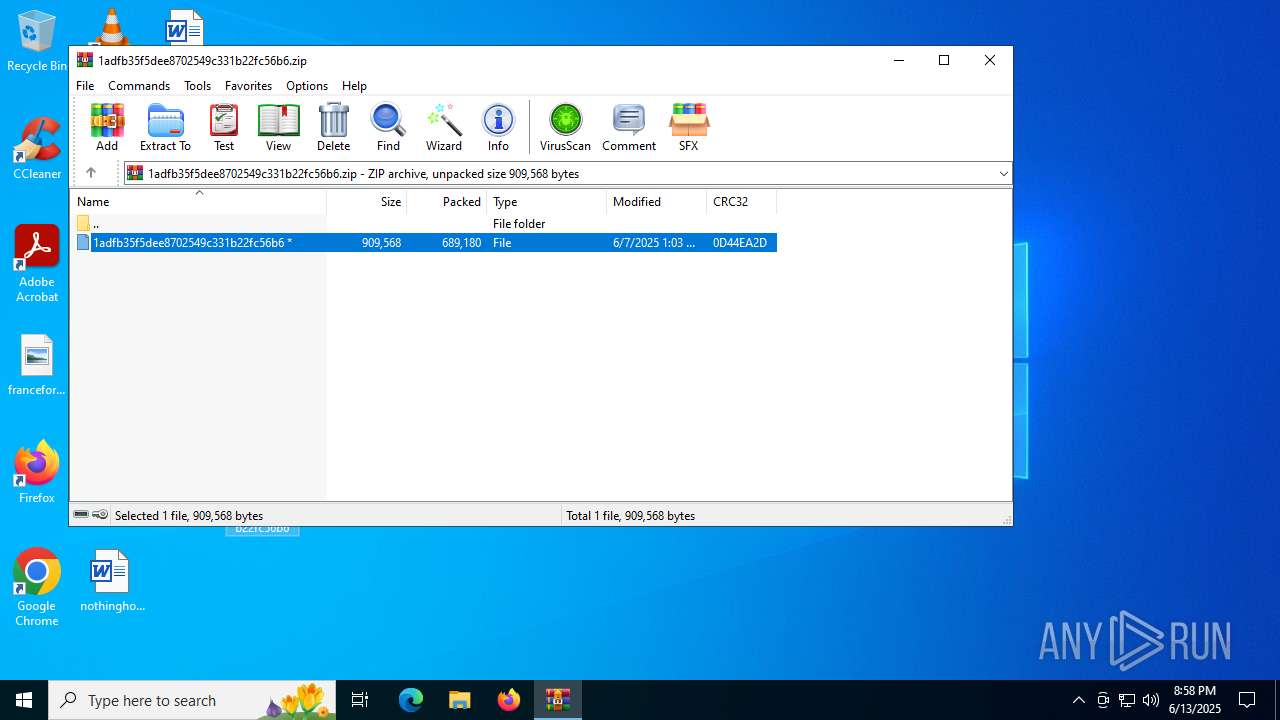
- WinRAR.exe (PID: 2116)
SUSPICIOUS
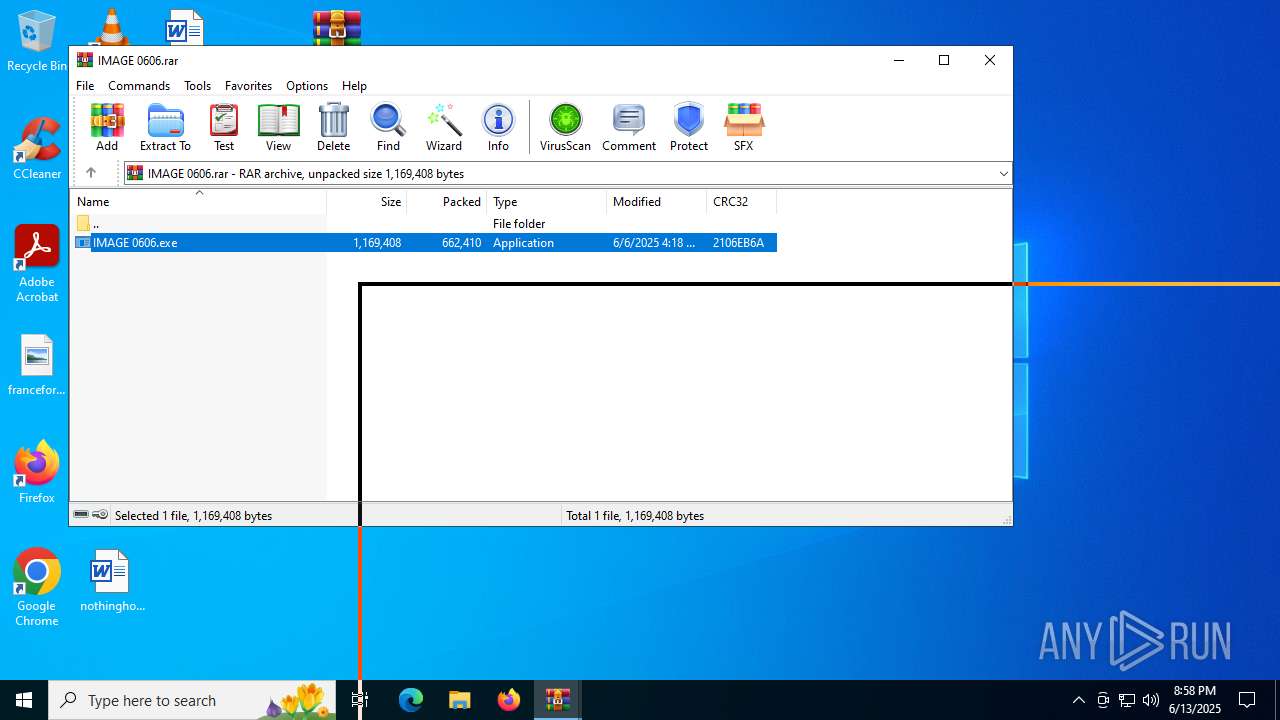
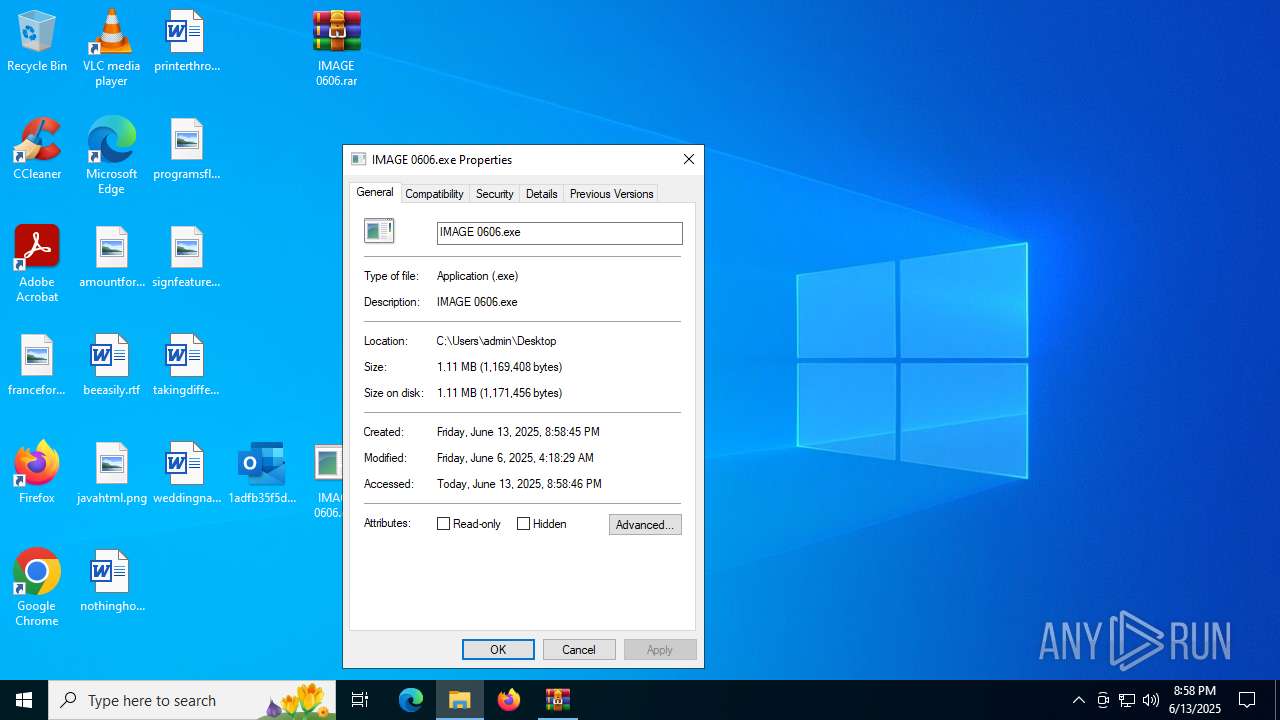
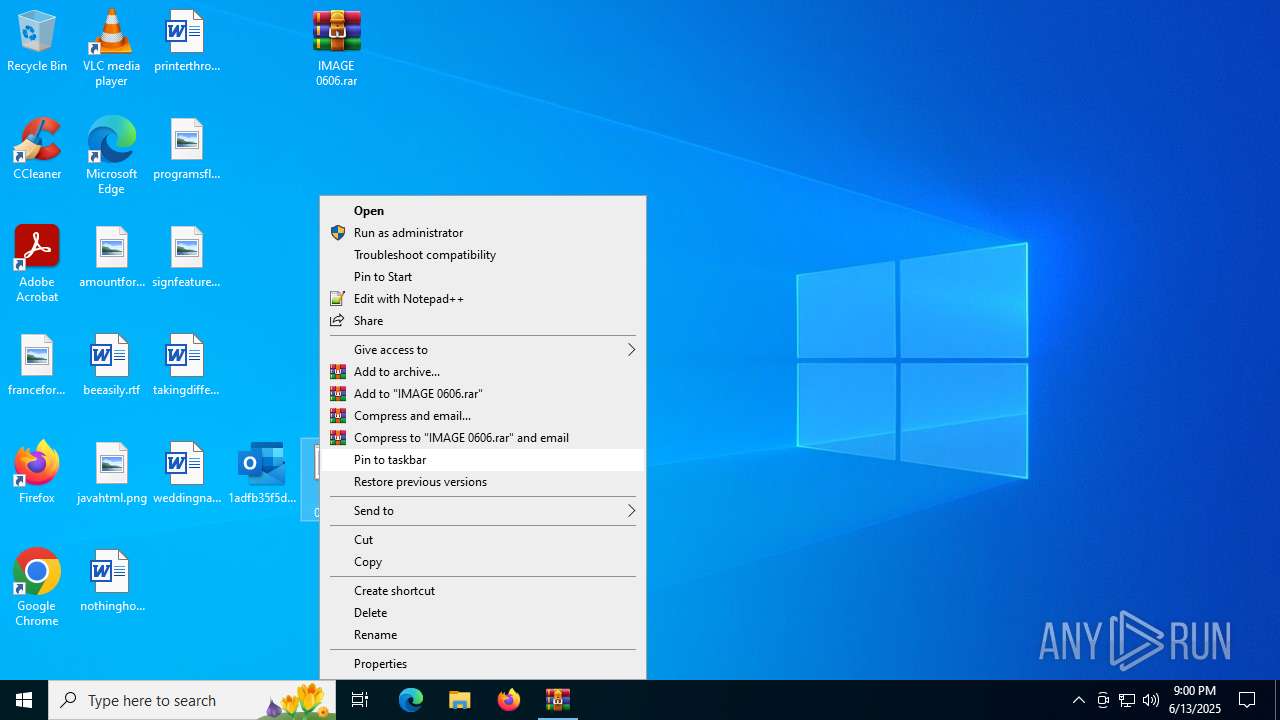
Executes application which crashes
- IMAGE 0606.exe (PID: 2876)
INFO
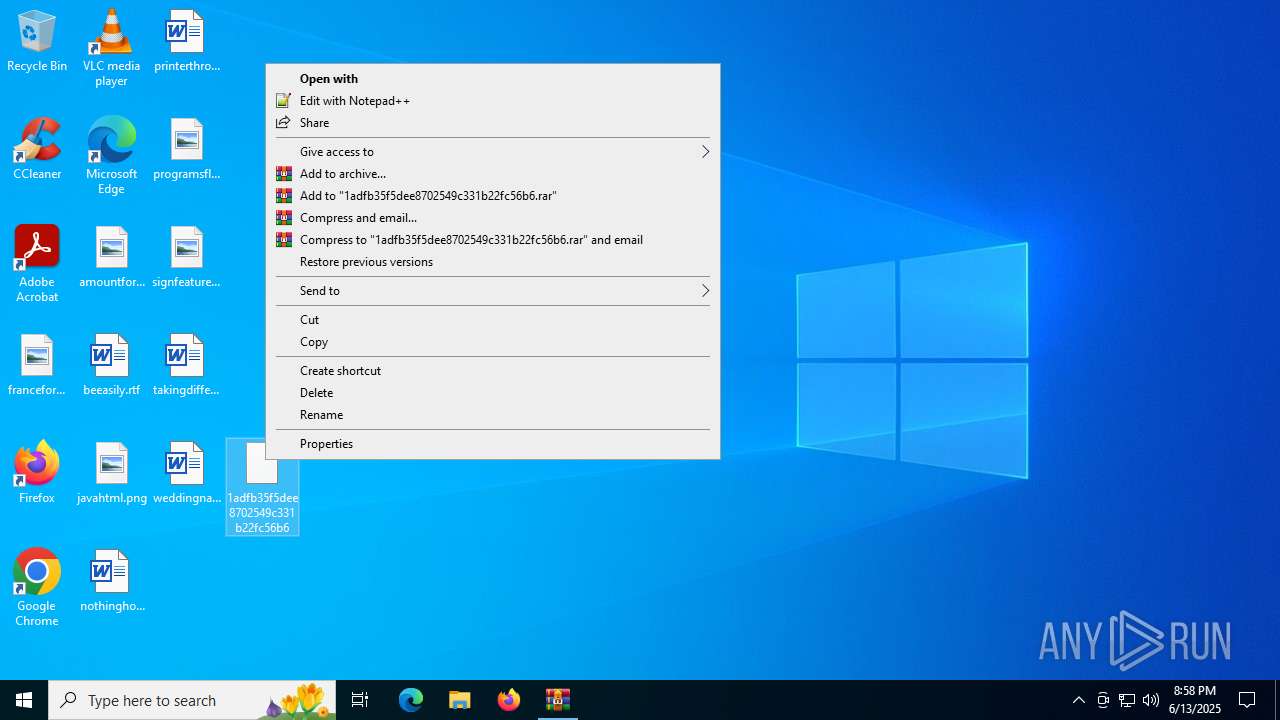
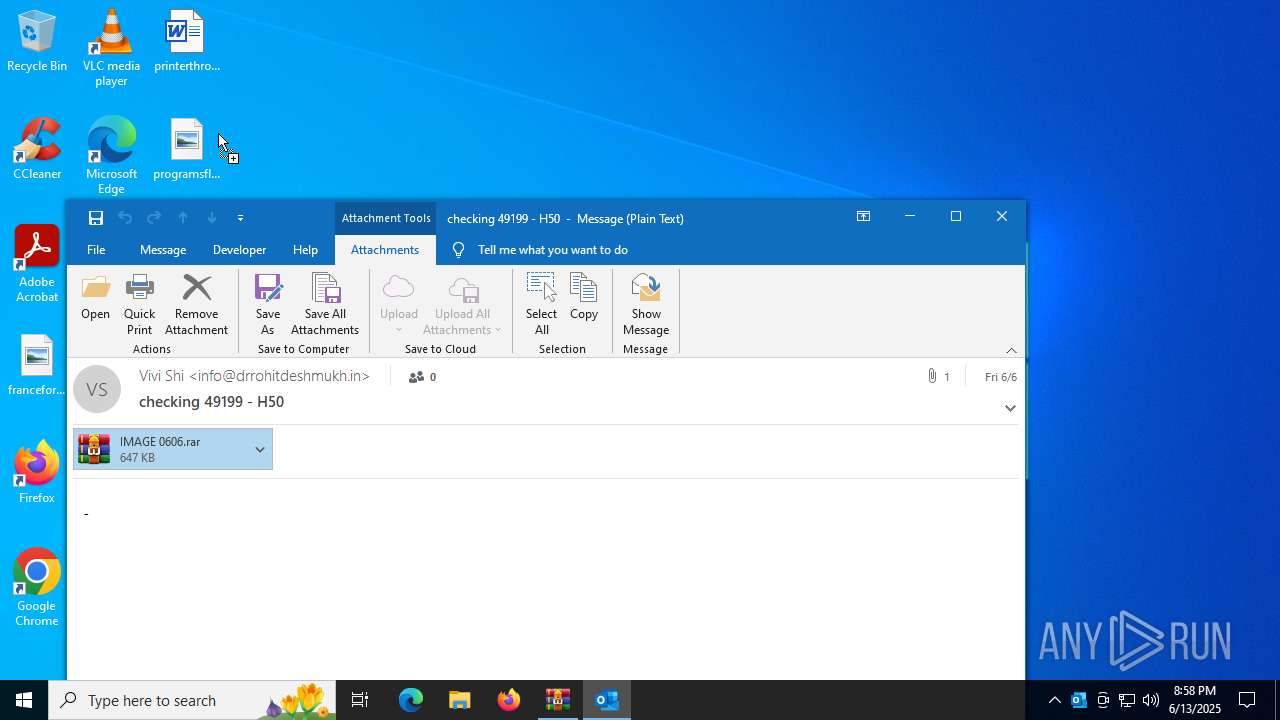
Executable content was dropped or overwritten
- WinRAR.exe (PID: 2520)
The sample compiled with english language support
- OUTLOOK.EXE (PID: 1204)
- WinRAR.exe (PID: 2520)
- WinRAR.exe (PID: 2116)
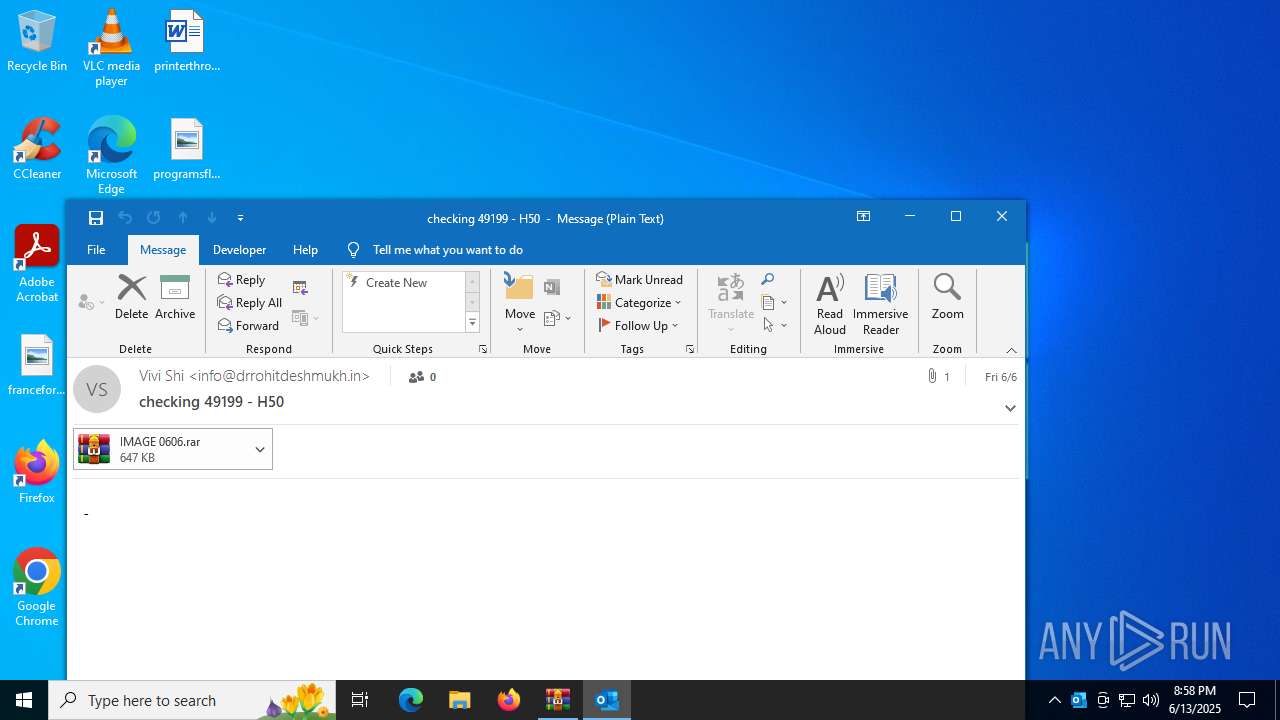
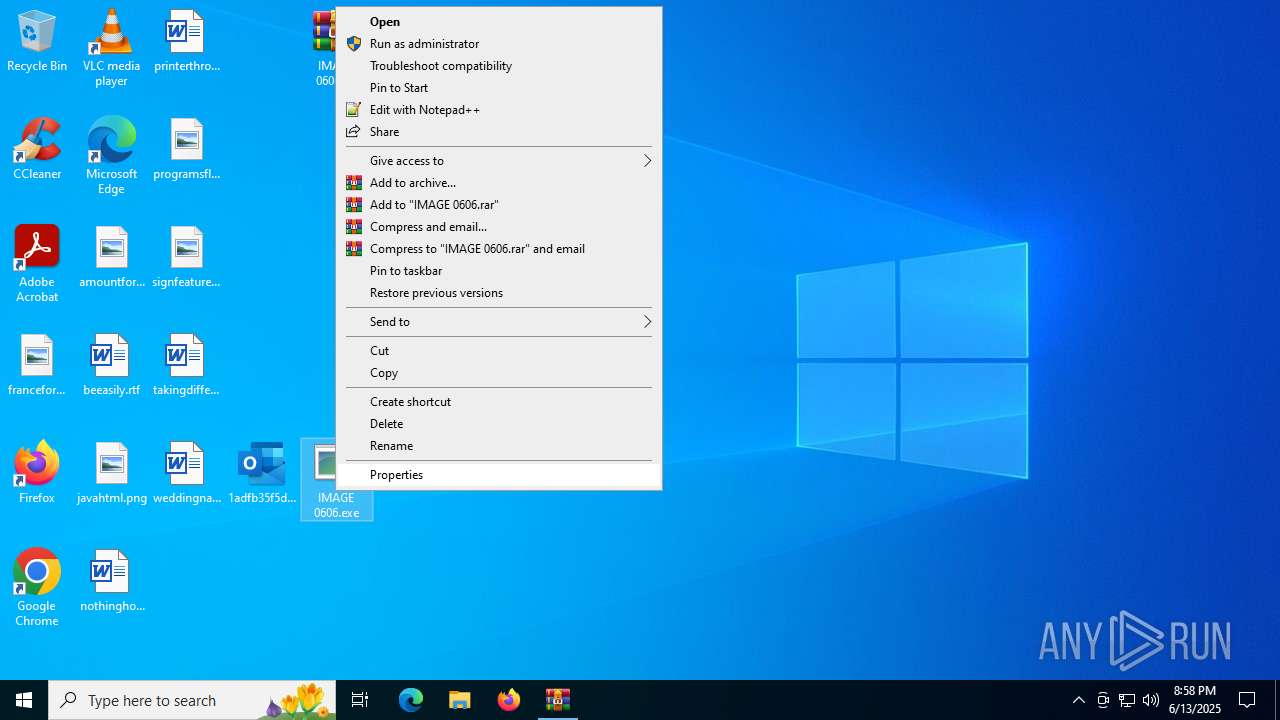
Manual execution by a user
- WinRAR.exe (PID: 2520)
- OUTLOOK.EXE (PID: 1204)
- IMAGE 0606.exe (PID: 2876)
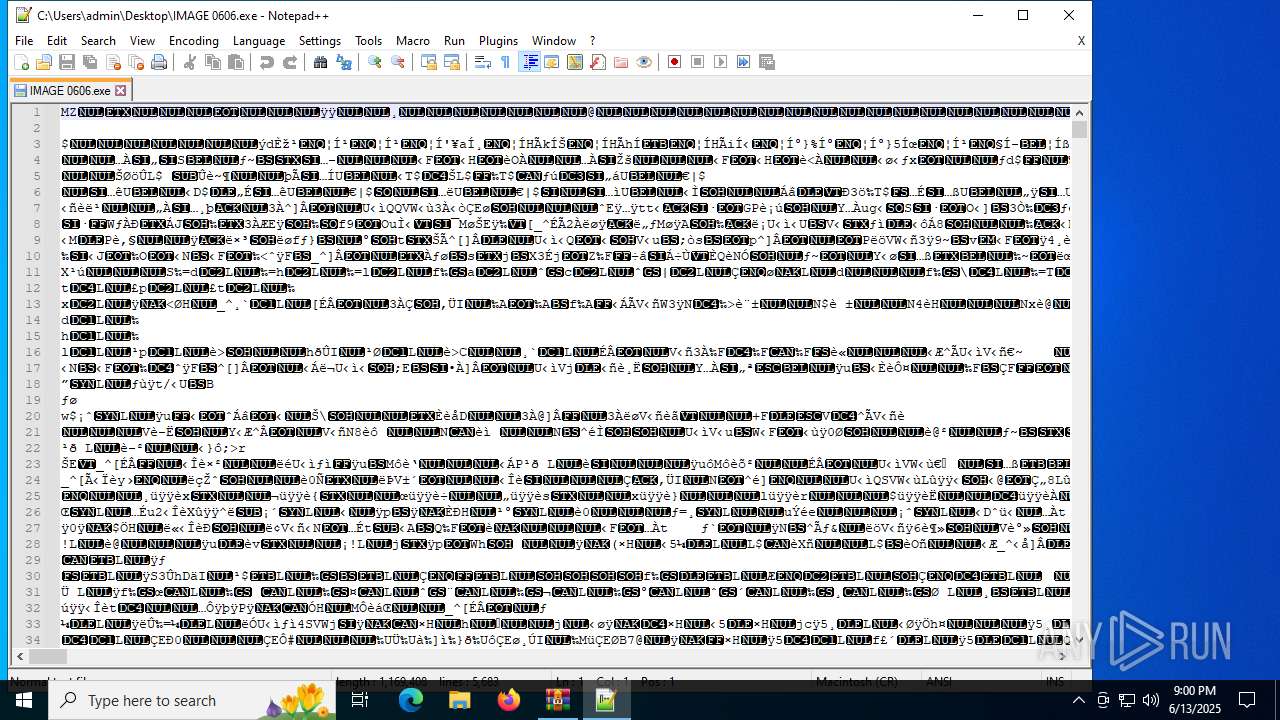
- notepad++.exe (PID: 6876)
Reads mouse settings
- IMAGE 0606.exe (PID: 2876)
Checks supported languages
- IMAGE 0606.exe (PID: 2876)
Create files in a temporary directory
- IMAGE 0606.exe (PID: 2876)
Checks proxy server information
- WerFault.exe (PID: 2620)
- slui.exe (PID: 5372)
Creates files or folders in the user directory
- WerFault.exe (PID: 2620)
Reads the software policy settings
- WerFault.exe (PID: 2620)
- slui.exe (PID: 5372)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 788 |
|---|---|
| ZipBitFlag: | 0x0001 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2025:06:07 01:03:44 |
| ZipCRC: | 0x0d44ea2d |
| ZipCompressedSize: | 689180 |
| ZipUncompressedSize: | 909568 |
| ZipFileName: | 1adfb35f5dee8702549c331b22fc56b6 |
Total processes
150
Monitored processes
9
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1204 | "C:\Program Files\Microsoft Office\Root\Office16\OUTLOOK.EXE" /eml "C:\Users\admin\Desktop\1adfb35f5dee8702549c331b22fc56b6.eml" | C:\Program Files\Microsoft Office\root\Office16\OUTLOOK.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Outlook Exit code: 0 Version: 16.0.16026.20146 Modules
| |||||||||||||||
| 2116 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\AppData\Local\Temp\1adfb35f5dee8702549c331b22fc56b6.zip | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Version: 5.91.0 Modules
| |||||||||||||||
| 2520 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Desktop\IMAGE 0606.rar" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 2620 | C:\WINDOWS\SysWOW64\WerFault.exe -u -p 2876 -s 704 | C:\Windows\SysWOW64\WerFault.exe | IMAGE 0606.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Problem Reporting Exit code: 0 Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
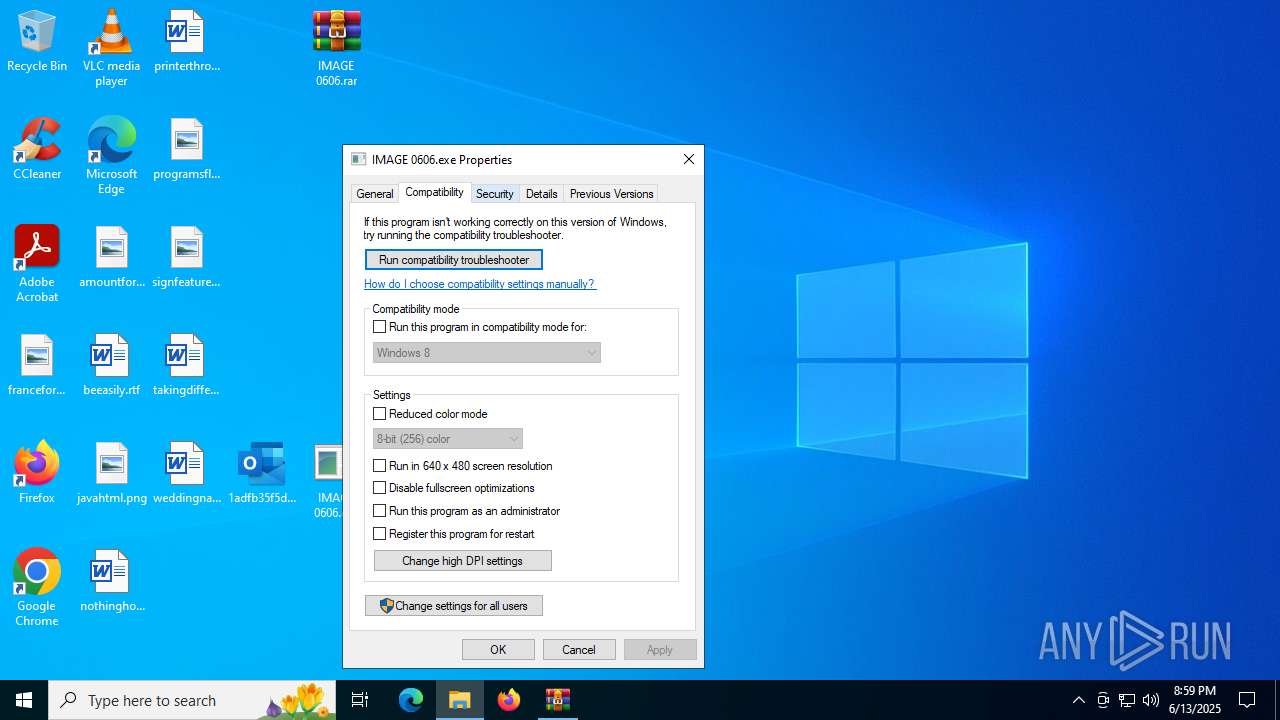
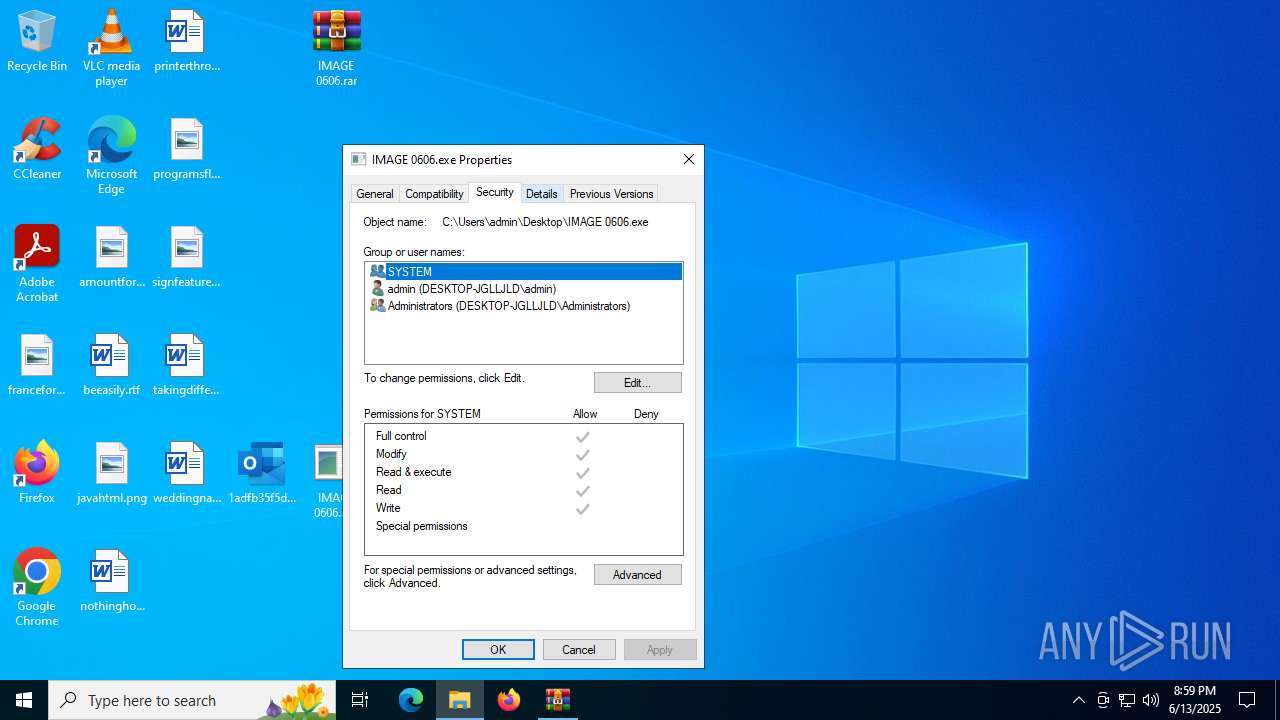
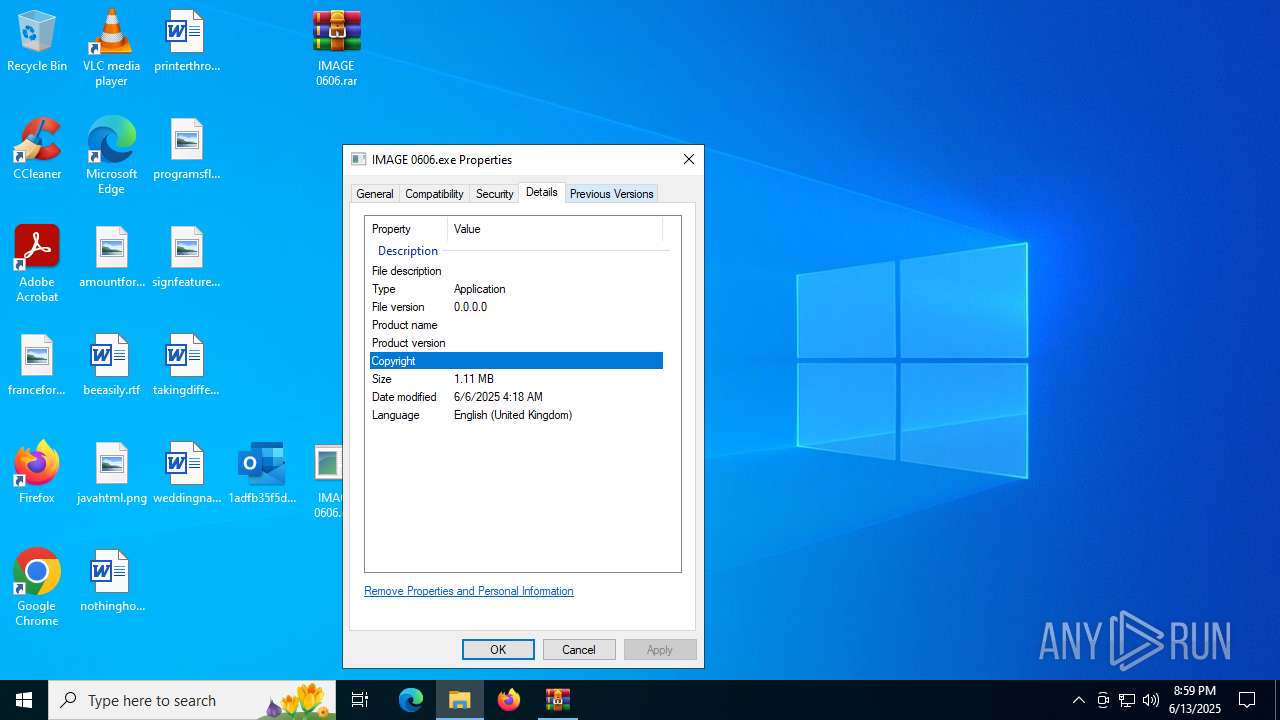
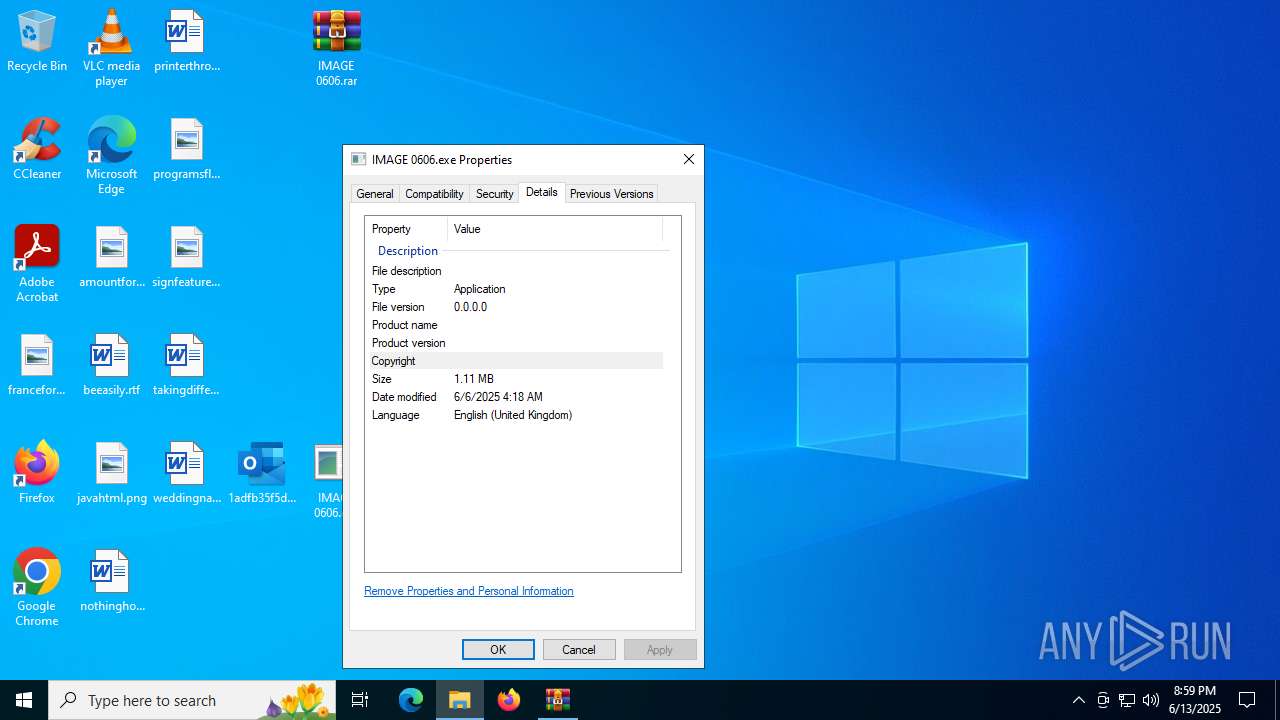
| 2876 | "C:\Users\admin\Desktop\IMAGE 0606.exe" | C:\Users\admin\Desktop\IMAGE 0606.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221225477 Modules
| |||||||||||||||
| 5372 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5960 | "C:\Users\admin\Desktop\IMAGE 0606.exe" | C:\Windows\SysWOW64\svchost.exe | — | IMAGE 0606.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) | |||||||||||||||
| 6876 | "C:\Program Files\Notepad++\notepad++.exe" "C:\Users\admin\Desktop\IMAGE 0606.exe" | C:\Program Files\Notepad++\notepad++.exe | explorer.exe | ||||||||||||
User: admin Company: Don HO don.h@free.fr Integrity Level: MEDIUM Description: Notepad++ : a free (GNU) source code editor Exit code: 0 Version: 7.91 Modules
| |||||||||||||||
| 6936 | "C:\Program Files\Microsoft Office\root\VFS\ProgramFilesCommonX64\Microsoft Shared\OFFICE16\ai.exe" "FCAE46A2-09BF-470B-B3BC-948486C3FF52" "C51864C5-AF09-482F-9071-F584D8234F18" "1204" | C:\Program Files\Microsoft Office\root\VFS\ProgramFilesCommonX64\Microsoft Shared\OFFICE16\ai.exe | — | OUTLOOK.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Artificial Intelligence (AI) Host for the Microsoft® Windows® Operating System and Platform x64. Exit code: 0 Version: 0.12.2.0 Modules
| |||||||||||||||
Total events
20 995
Read events
19 797
Write events
1 065
Delete events
133
Modification events
| (PID) Process: | (2116) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (2116) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (2116) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (2116) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\1adfb35f5dee8702549c331b22fc56b6.zip | |||
| (PID) Process: | (2116) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2116) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2116) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2116) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2116) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2116) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
Executable files
1
Suspicious files
23
Text files
14
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1204 | OUTLOOK.EXE | C:\Users\admin\Documents\Outlook Files\Outlook1.pst | — | |
MD5:— | SHA256:— | |||
| 2116 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb2116.9548\1adfb35f5dee8702549c331b22fc56b6 | binary | |
MD5:1ADFB35F5DEE8702549C331B22FC56B6 | SHA256:0B51F0698F9ACEBDA34CB8CEB7B2F501E8D48EF8469B2C3B7B35EAD42E4752DB | |||
| 1204 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\TokenBroker\Cache\56a61aeb75d8f5be186c26607f4bb213abe7c5ec.tbres | binary | |
MD5:9711FEA863CA84F0FD630046011AC7A7 | SHA256:DB663136E78BF8641028B43E29E30065E8DE06E8DCA4754B62C213E944AFE88F | |||
| 1204 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\TokenBroker\Cache\089d66ba04a8cec4bdc5267f42f39cf84278bb67.tbres | binary | |
MD5:7A09DE46A9EDE0AD6917C9AC123BC3BB | SHA256:BBB4D8F1538DFE10E5DE4BEEF912AE2492F6D36B7C15E27C5F8D81D8E532F8BC | |||
| 1204 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\Content.Outlook\LXO94S8L\IMAGE 0606.rar | compressed | |
MD5:8631D98E66D54FB3E9B5BFA44BFF539B | SHA256:D2AE31B0066721A9FAAFB2088A3E38D5F1F233DF14537837EBF1E83019BACD71 | |||
| 1204 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\~DF4E3216099FBD5C8F.TMP | binary | |
MD5:8E25FA50277CC16E296E9464B6927642 | SHA256:1C941A727607667F46FF604F366E2A5CA9EA2DFEBA6F2B3E55FDE617010A8F7D | |||
| 1204 | OUTLOOK.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Outlook\Outlook.srs | binary | |
MD5:1CECBECC9016598C406FF99CB0889A79 | SHA256:38156B8FAC83C9BFA75EB807E9DEF777E6283A002344F3AD9155B42F02DAE212 | |||
| 1204 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\~DF610C9C1676CD6C5E.TMP | binary | |
MD5:F08C1B4C3A3ACD33E0C4711B992D47FF | SHA256:4F041CB7C5D1109ADA3DBFCAD414062A0F13207735ADEEB0252E26850779883B | |||
| 1204 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Office\16.0\AddInClassifierCache\OfficeSharedEntitiesUpdated.bin | text | |
MD5:78D01285376A0E791D8ADDB978E56DDE | SHA256:1D2C06D1D228C9A6F542E8DD9746AE5C55877DDC1D693FD70D6319264D126102 | |||
| 1204 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Outlook\RoamCache\Stream_TableViewPreviewPrefs_2_BA989BBD315F2B4CA7054A8FE065A766.dat | xml | |
MD5:0E092DB99AEE99FDFF9B5B222C732CFD | SHA256:D1614AD99ADED9F6F5C1BE7FE7FFA5124BD04A526580DA3818EA8A954E852AA6 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
10
TCP/UDP connections
37
DNS requests
27
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1268 | svchost.exe | GET | 200 | 23.48.23.139:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
1204 | OUTLOOK.EXE | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
6348 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
6348 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
4544 | svchost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
2620 | WerFault.exe | GET | 200 | 2.16.168.124:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
1204 | OUTLOOK.EXE | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEA77flR%2B3w%2FxBpruV2lte6A%3D | unknown | — | — | whitelisted |
2620 | WerFault.exe | GET | 200 | 23.219.150.101:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
2940 | svchost.exe | GET | 200 | 23.209.209.135:80 | http://x1.c.lencr.org/ | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5944 | MoUsoCoreWorker.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
1268 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6172 | RUXIMICS.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1268 | svchost.exe | 23.48.23.139:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
1268 | svchost.exe | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
5944 | MoUsoCoreWorker.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1204 | OUTLOOK.EXE | 52.109.28.46:443 | officeclient.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | GB | whitelisted |
1204 | OUTLOOK.EXE | 52.123.128.14:443 | ecs.office.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
officeclient.microsoft.com |
| whitelisted |
ecs.office.com |
| whitelisted |
roaming.officeapps.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
omex.cdn.office.net |
| whitelisted |
messaging.lifecycle.office.com |
| whitelisted |
Threats
Process | Message |
|---|---|
notepad++.exe | VerifyLibrary: certificate revocation checking is disabled
|
notepad++.exe | VerifyLibrary: C:\Program Files\Notepad++\SciLexer.dll
|
notepad++.exe | ED255D9151912E40DF048A56288E969A8D0DAFA3
|
notepad++.exe | VerifyLibrary: error while getting certificate informations
|
notepad++.exe | VerifyLibrary: C:\Program Files\Notepad++\updater\gup.exe
|
notepad++.exe | VerifyLibrary: certificate revocation checking is disabled
|