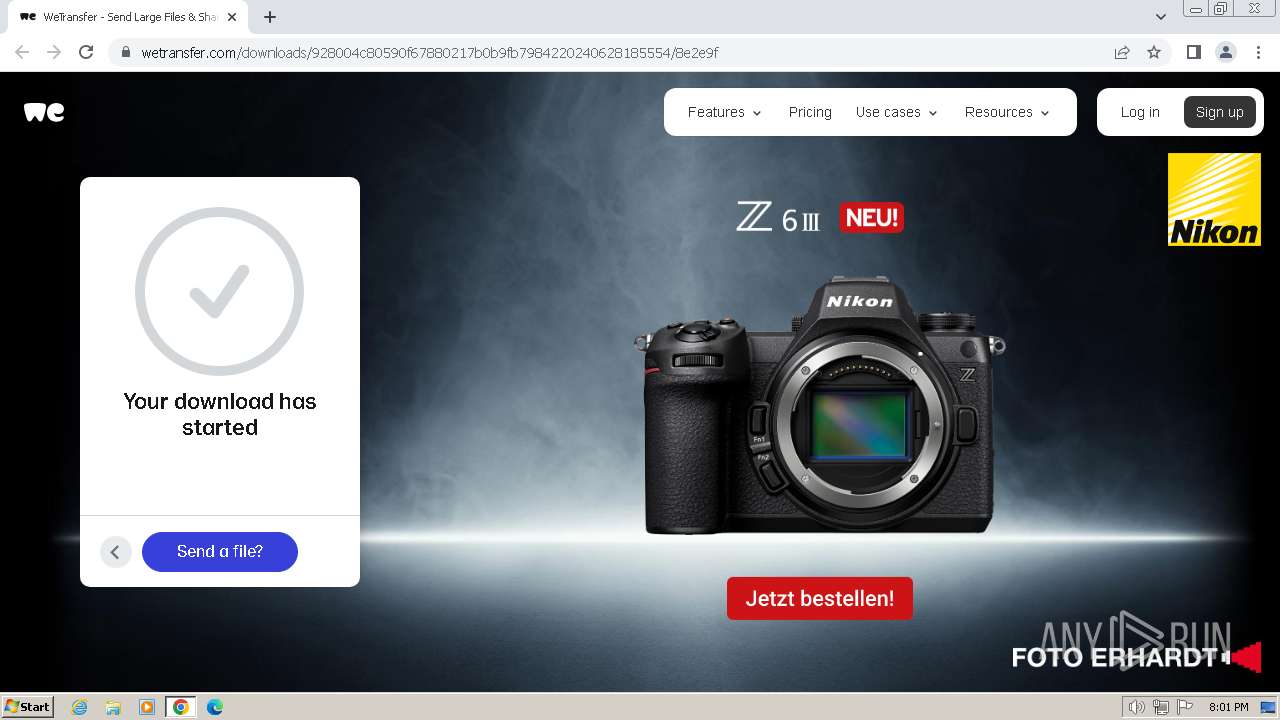
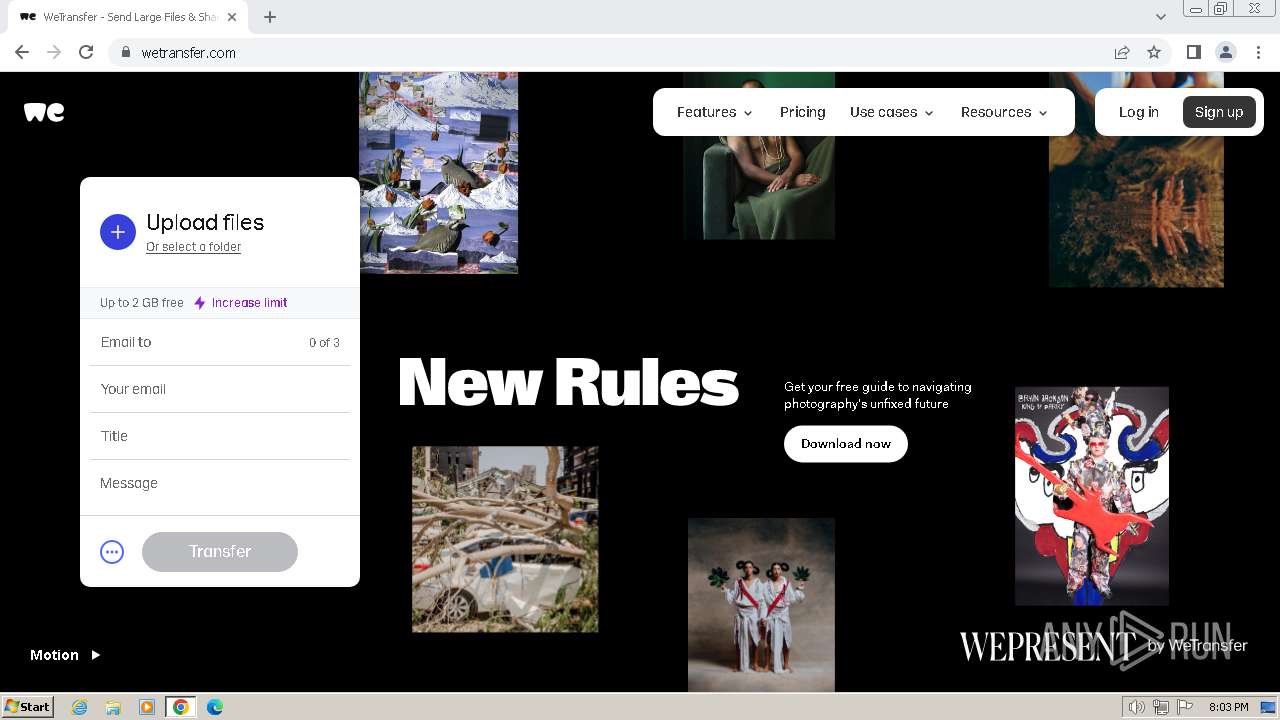
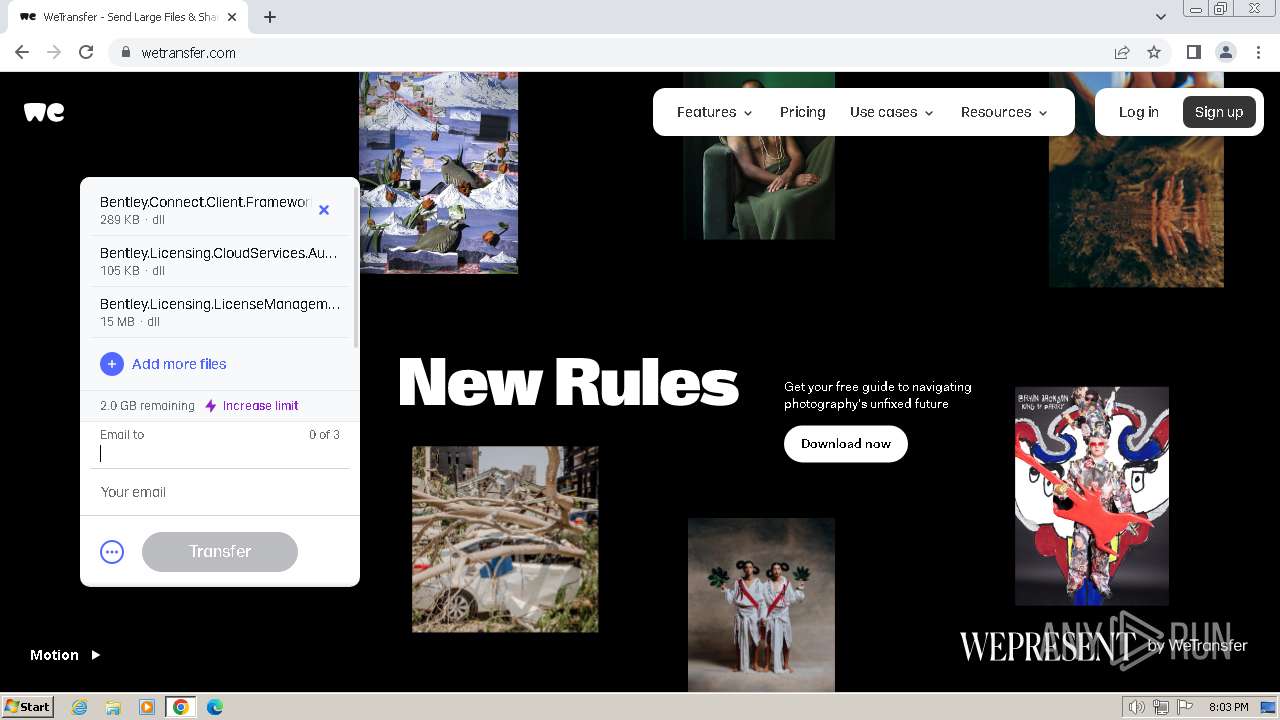
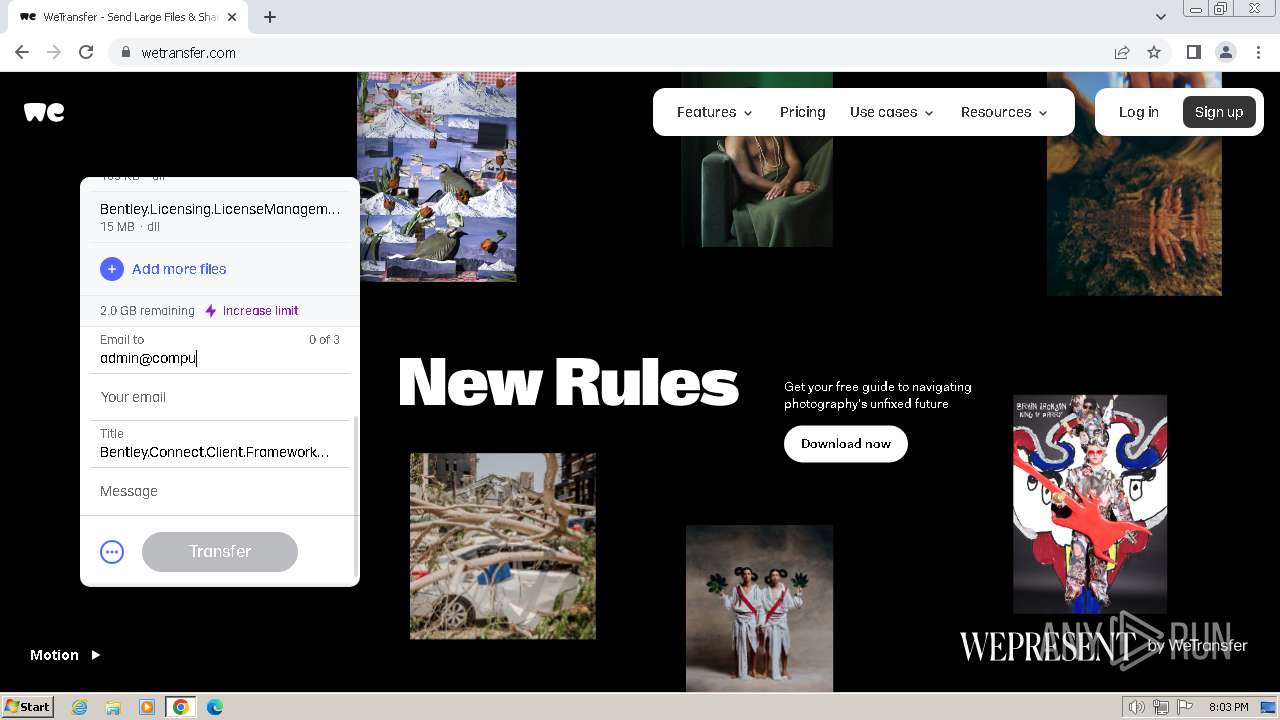
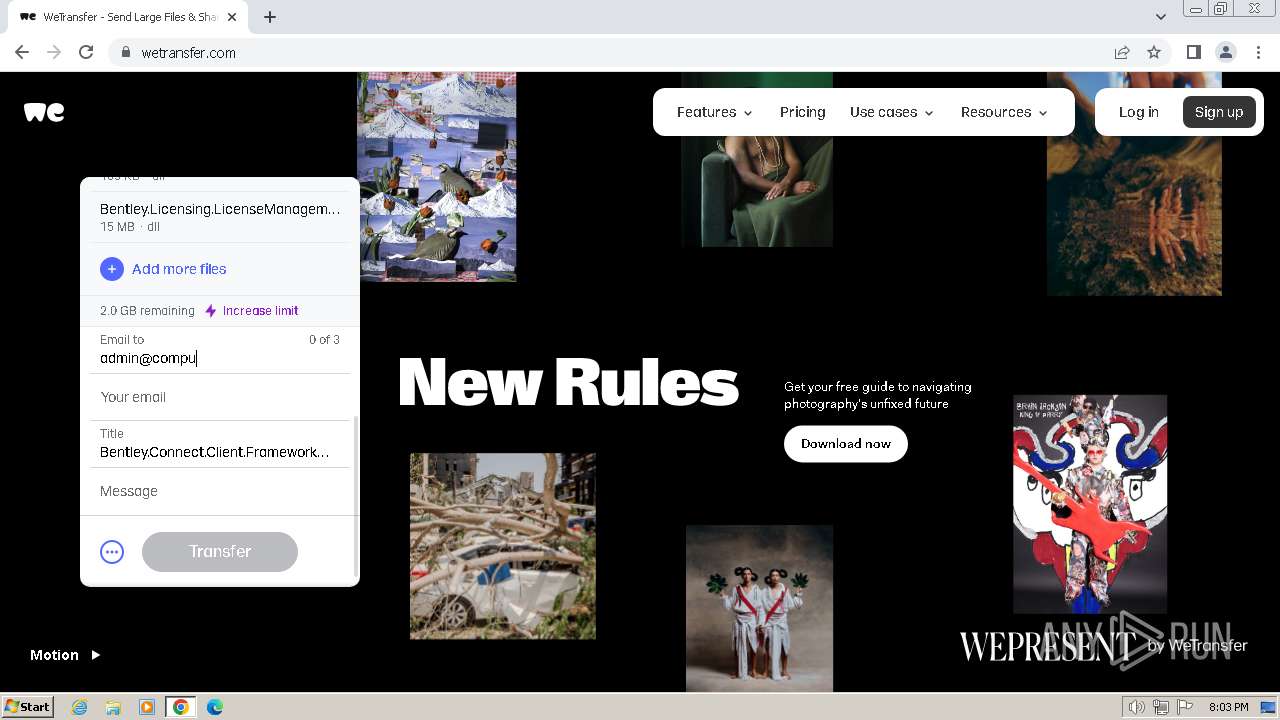
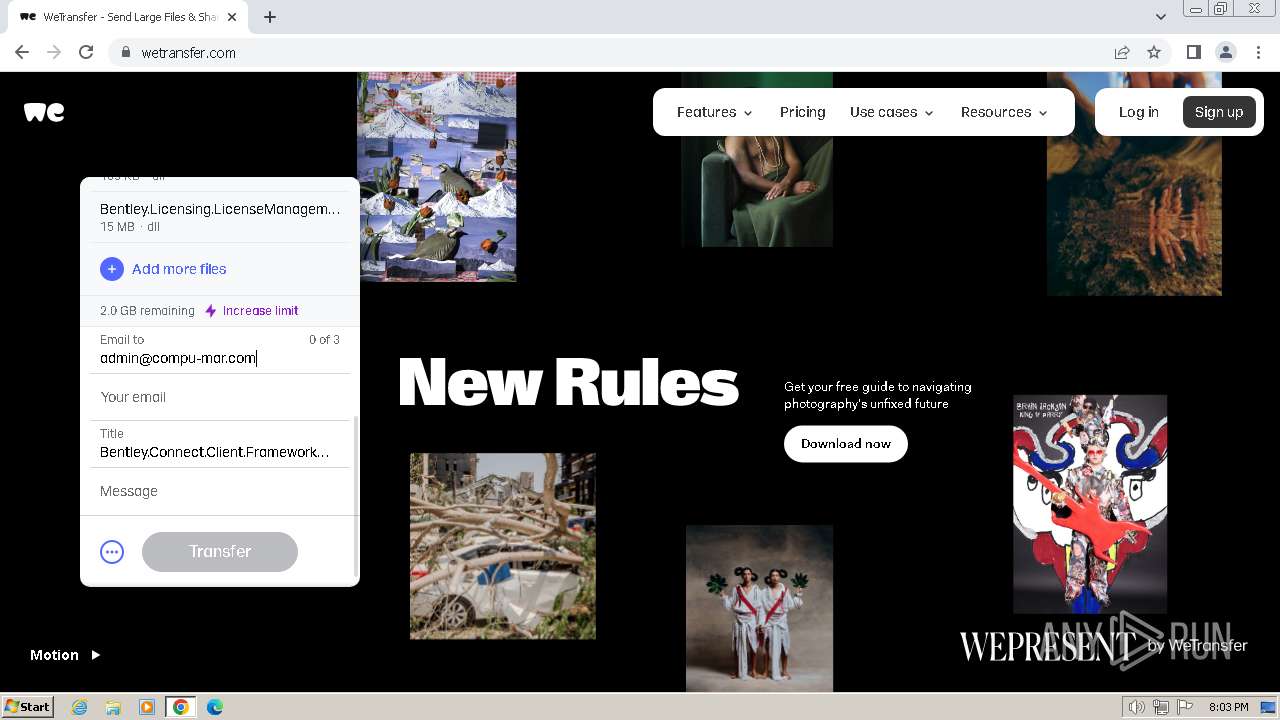
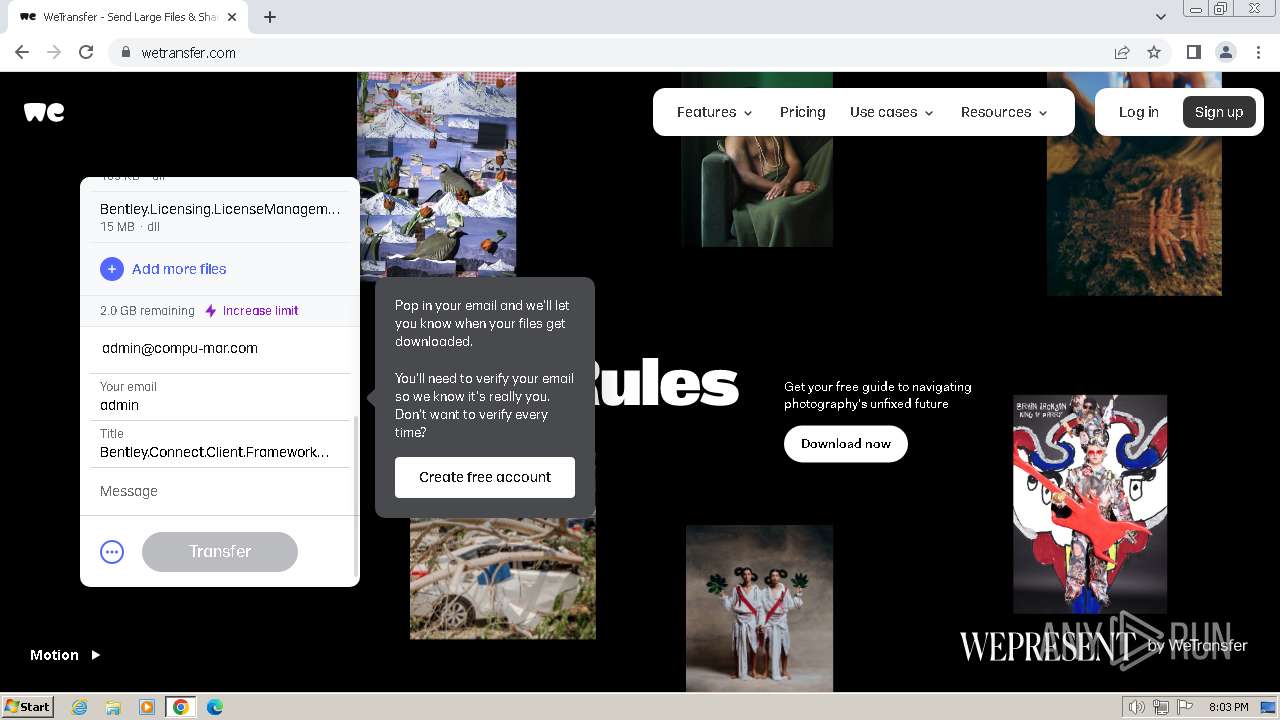
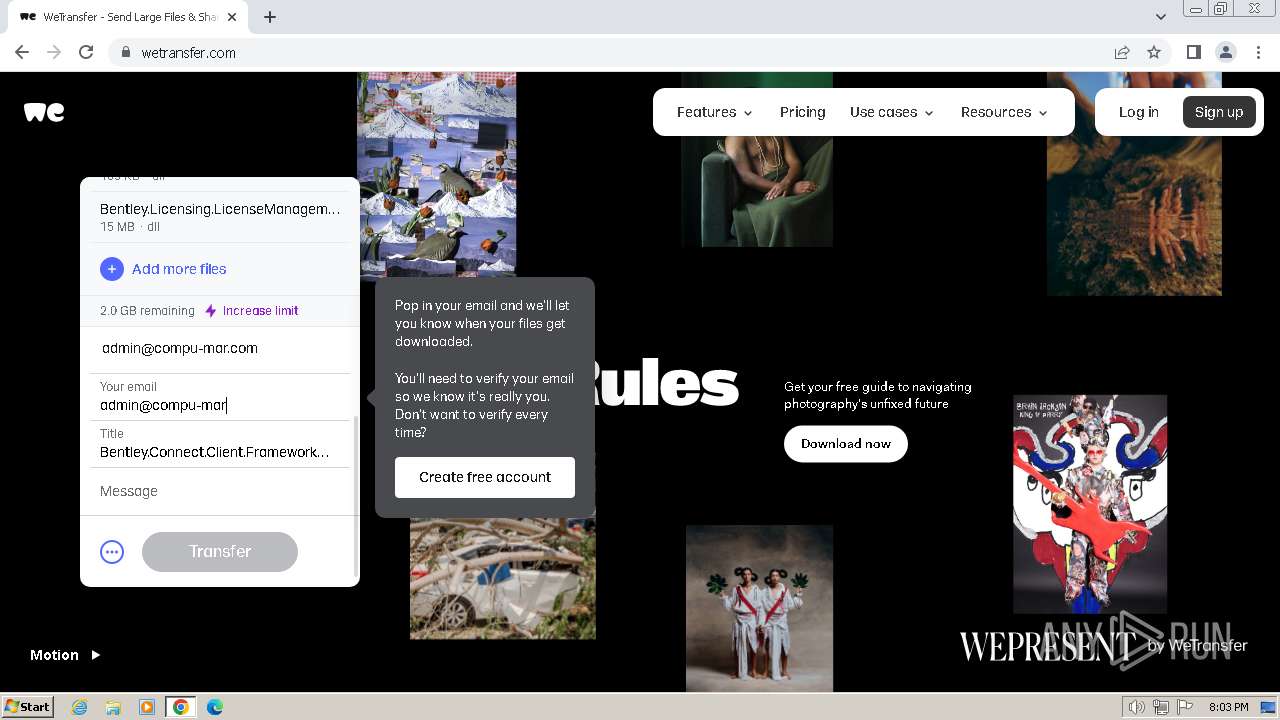
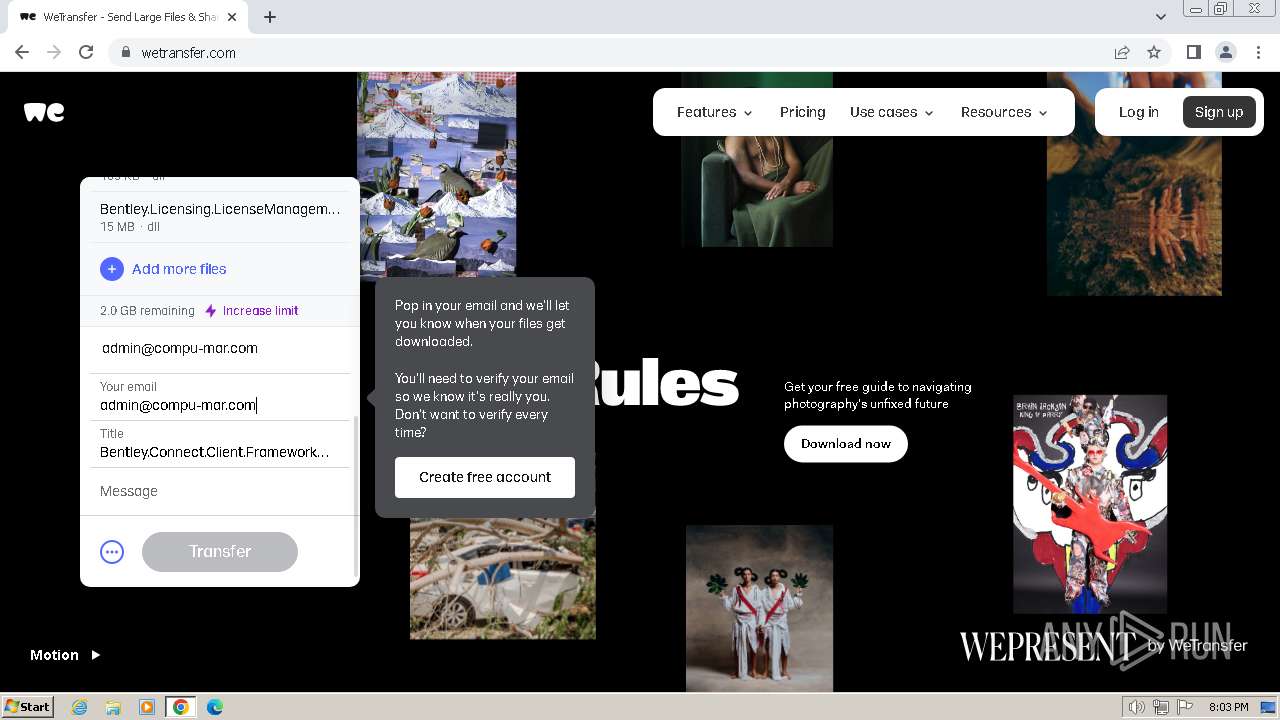
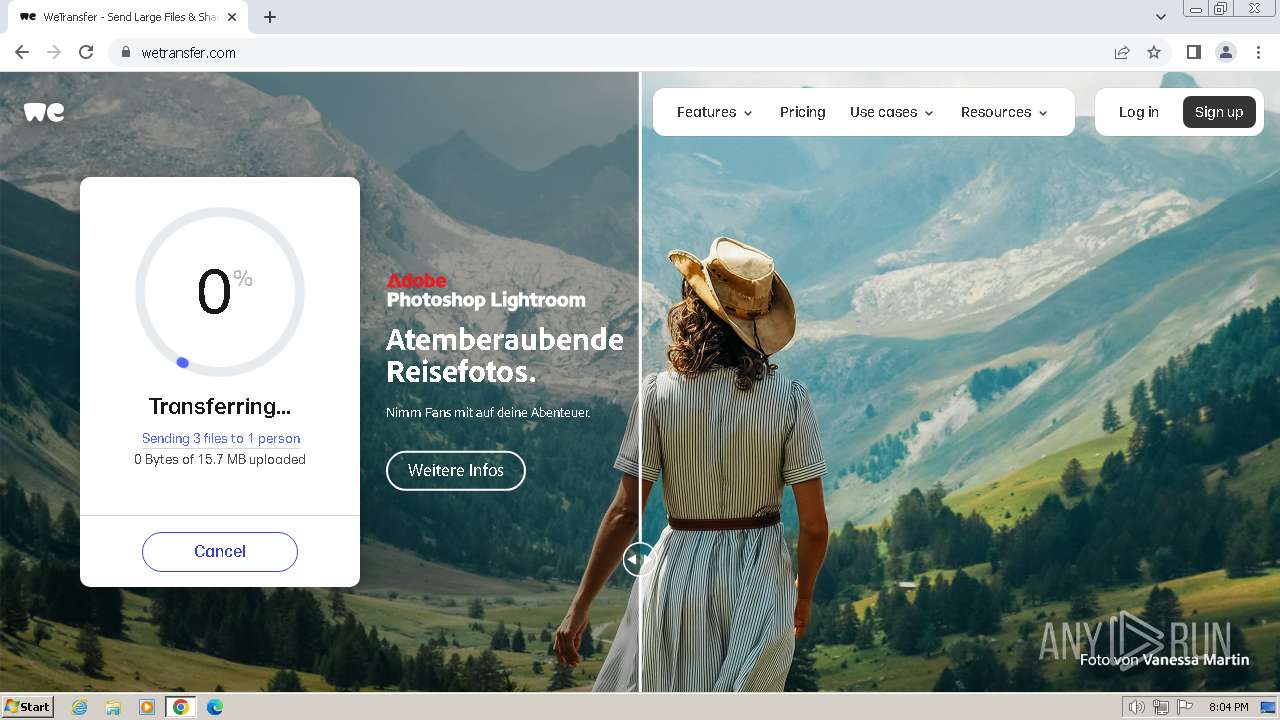
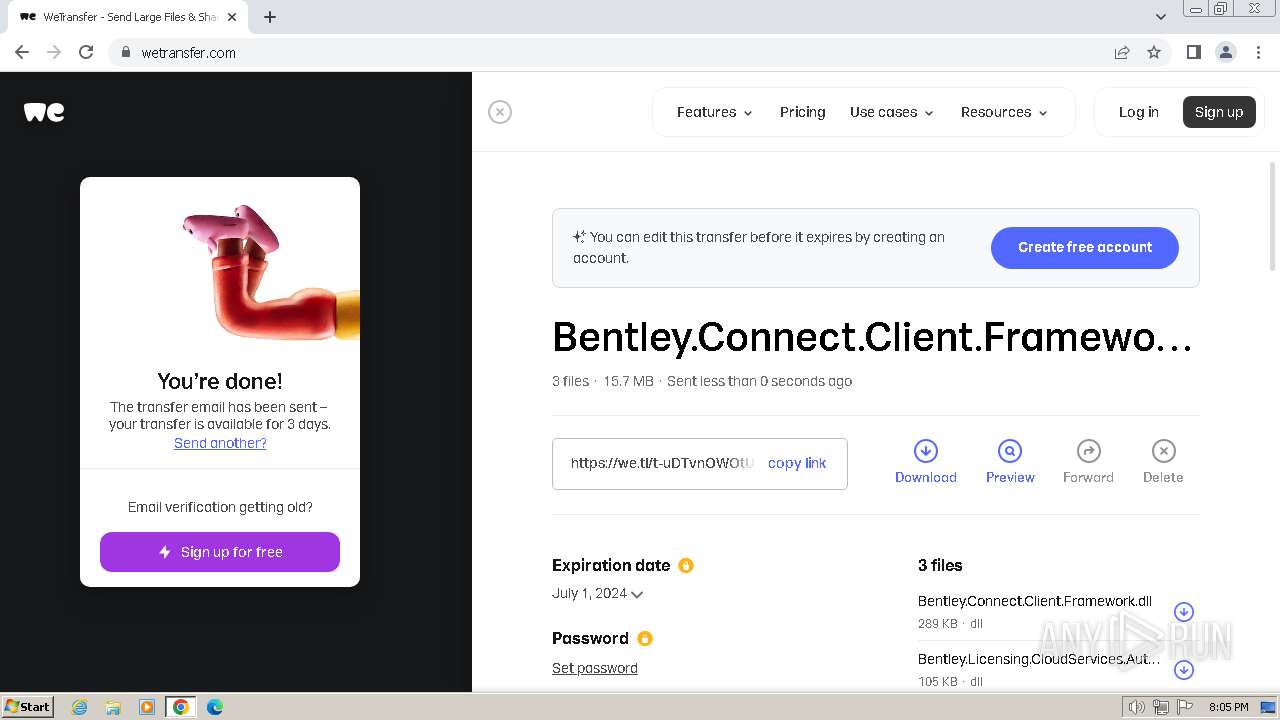
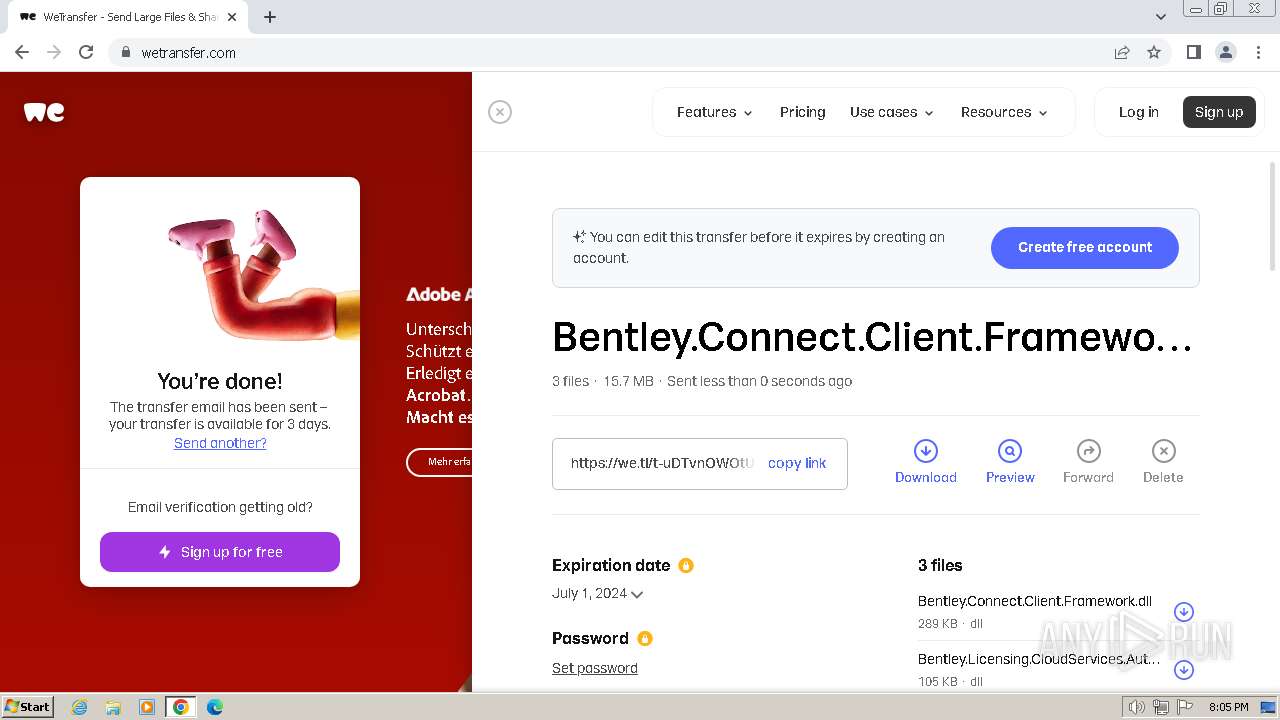
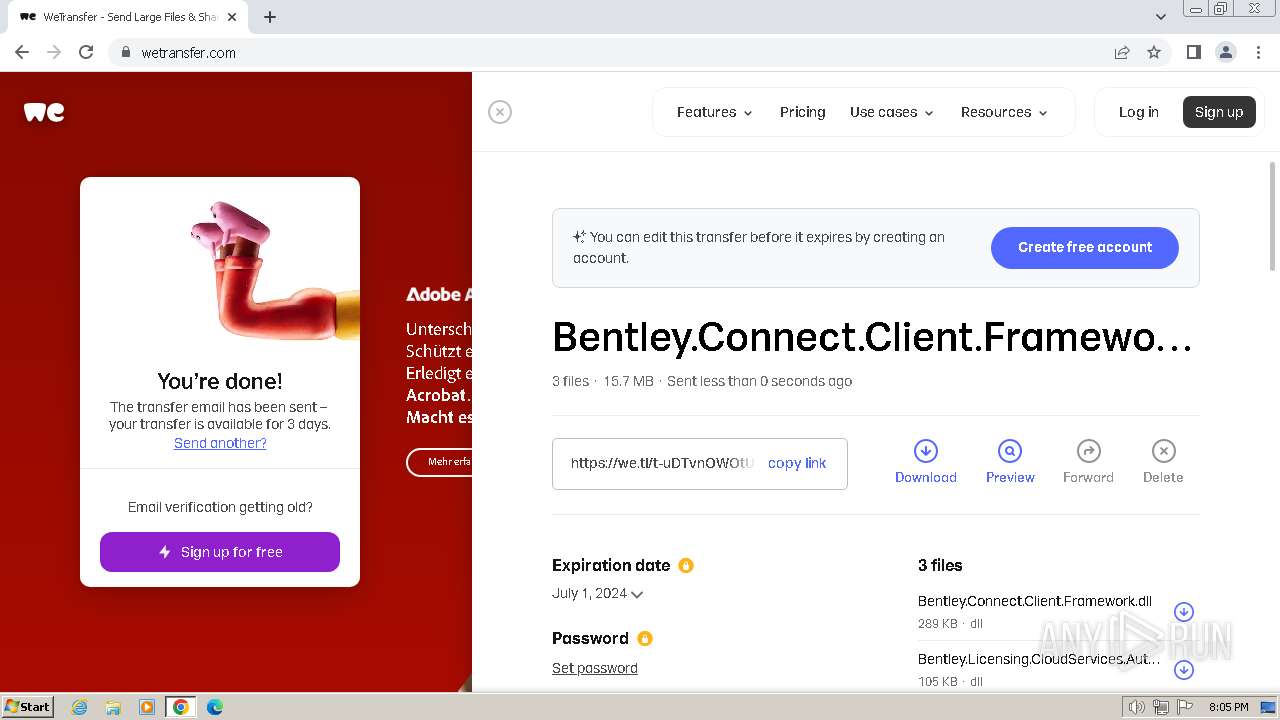
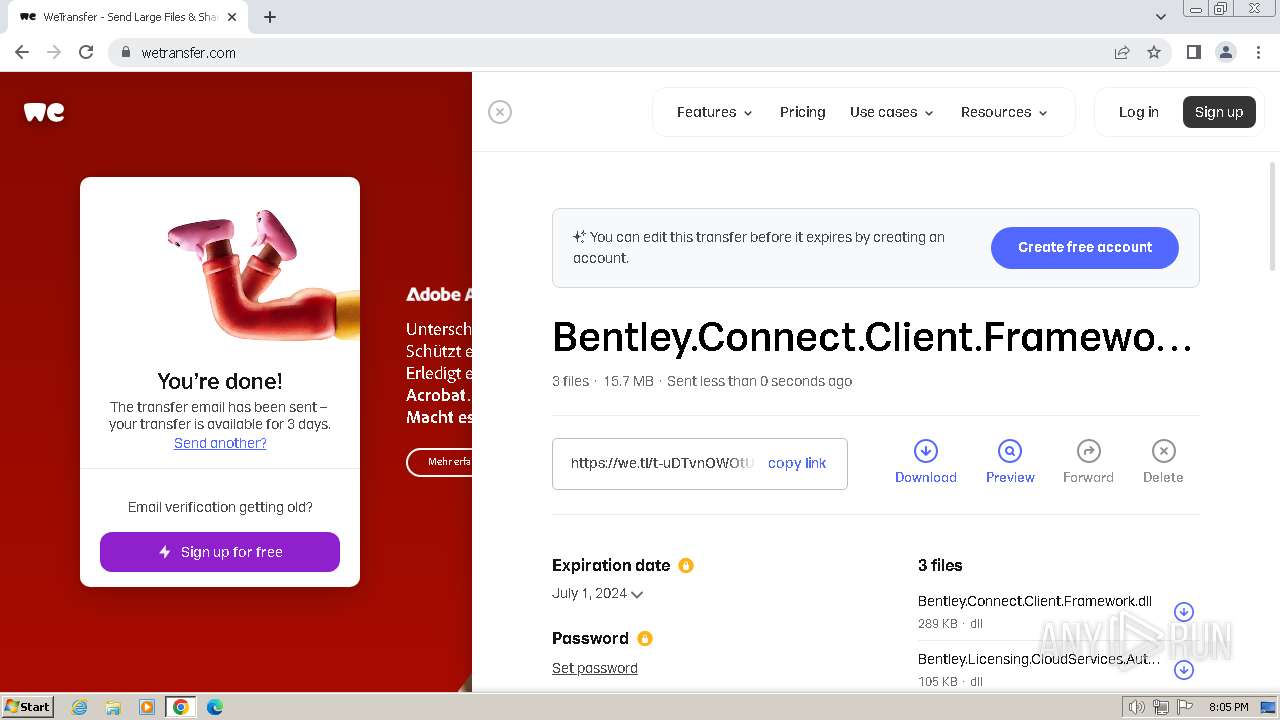
| URL: | https://we.tl/t-ulg0Q8AD5I |
| Full analysis: | https://app.any.run/tasks/71425270-f432-494f-a8c1-1528342c0057 |
| Verdict: | Malicious activity |
| Analysis date: | June 28, 2024, 19:00:50 |
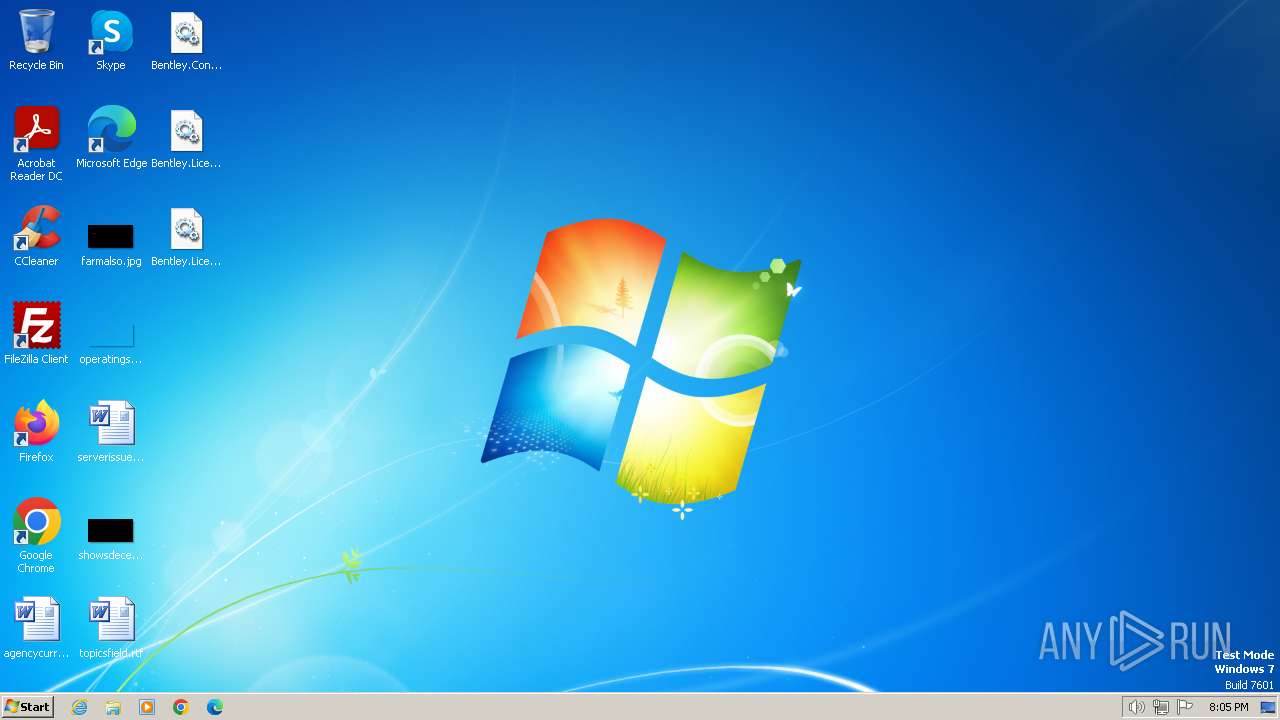
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | B0E09422BDD7C0689EC92F18B498B419 |
| SHA1: | C0C538A5DB94B99444C1A198E995C7A2409E599E |
| SHA256: | 5BEA444B0DF3998AAEA278CFD2A5C5971067881B0DC0D673597CF348C2CE7BE7 |
| SSDEEP: | 3:N8RlJKUhQs:2thQs |
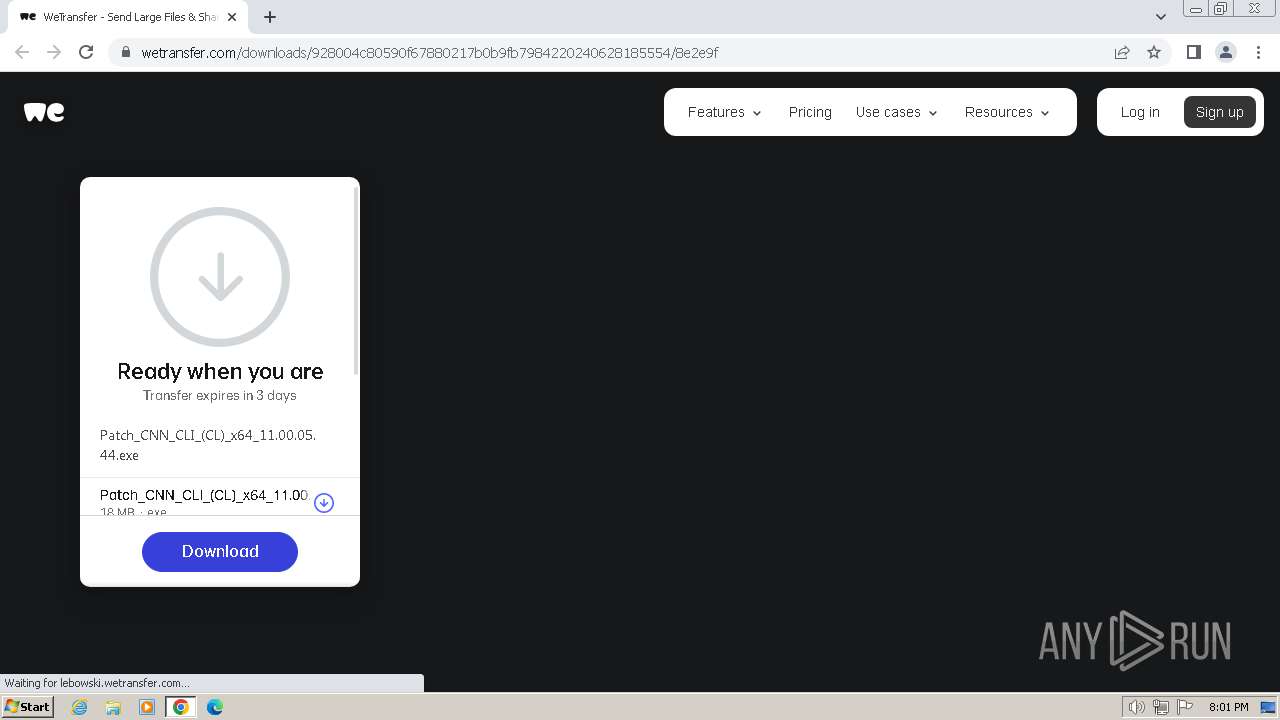
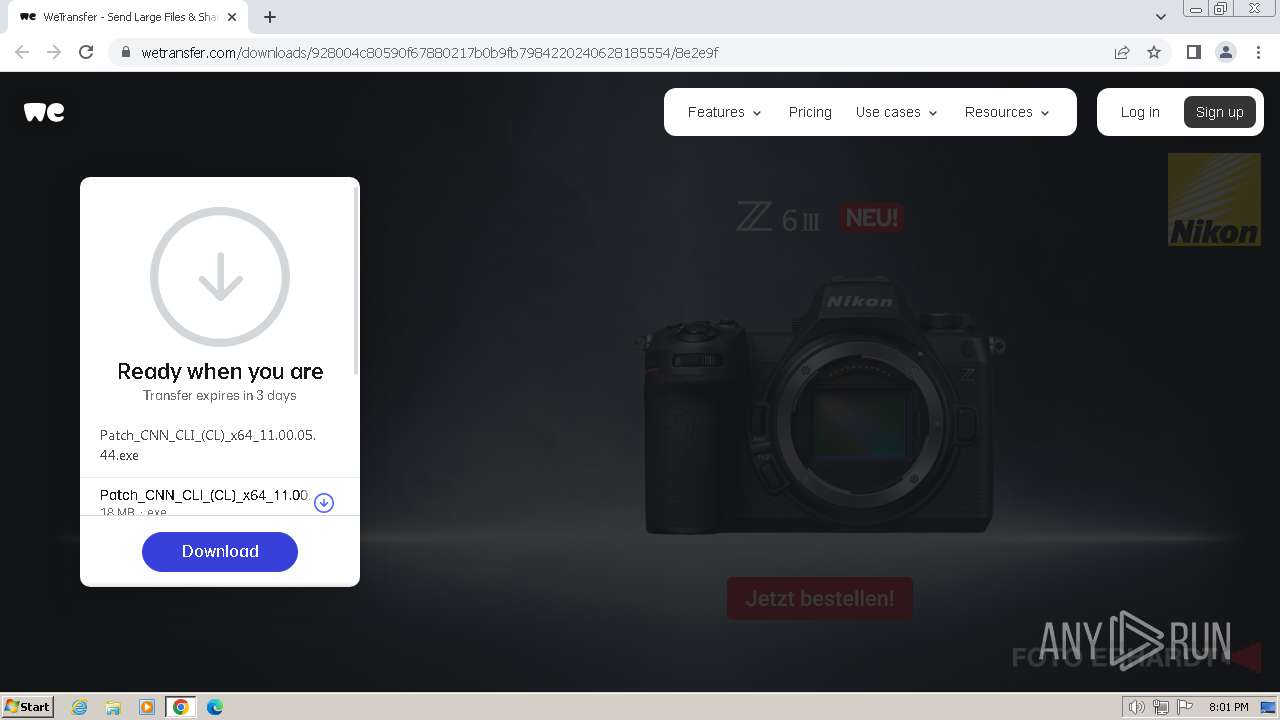
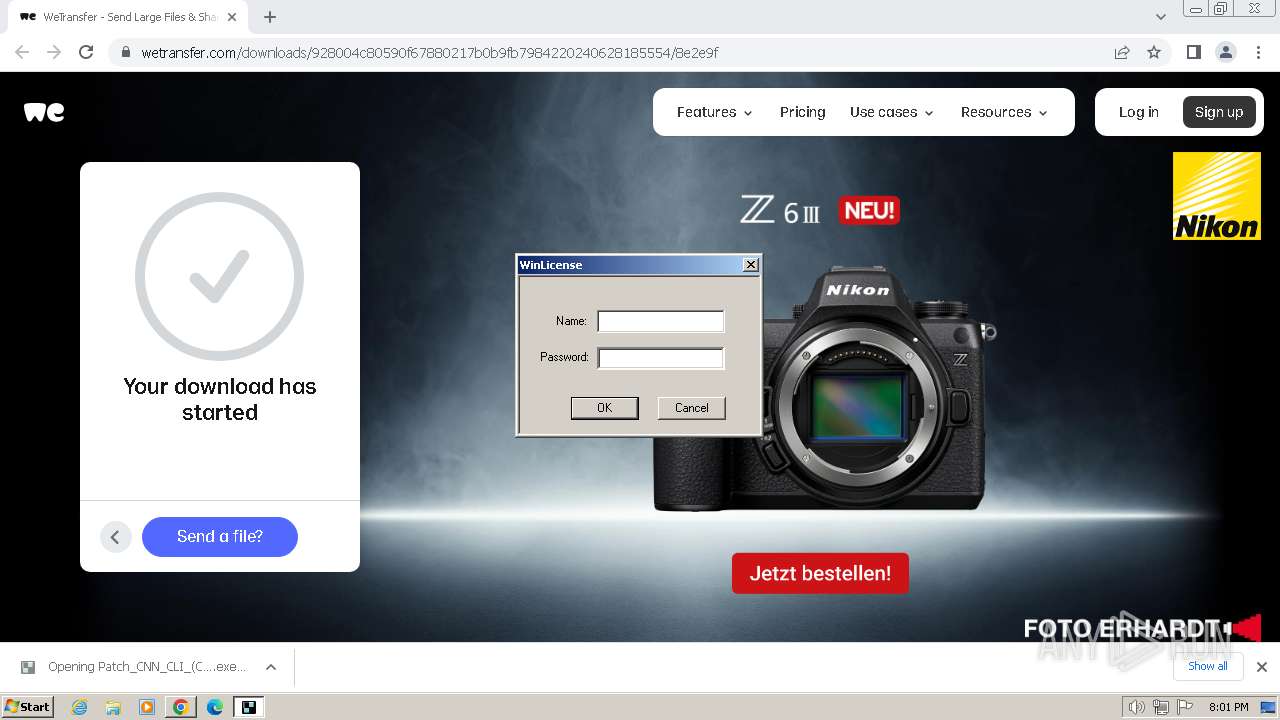
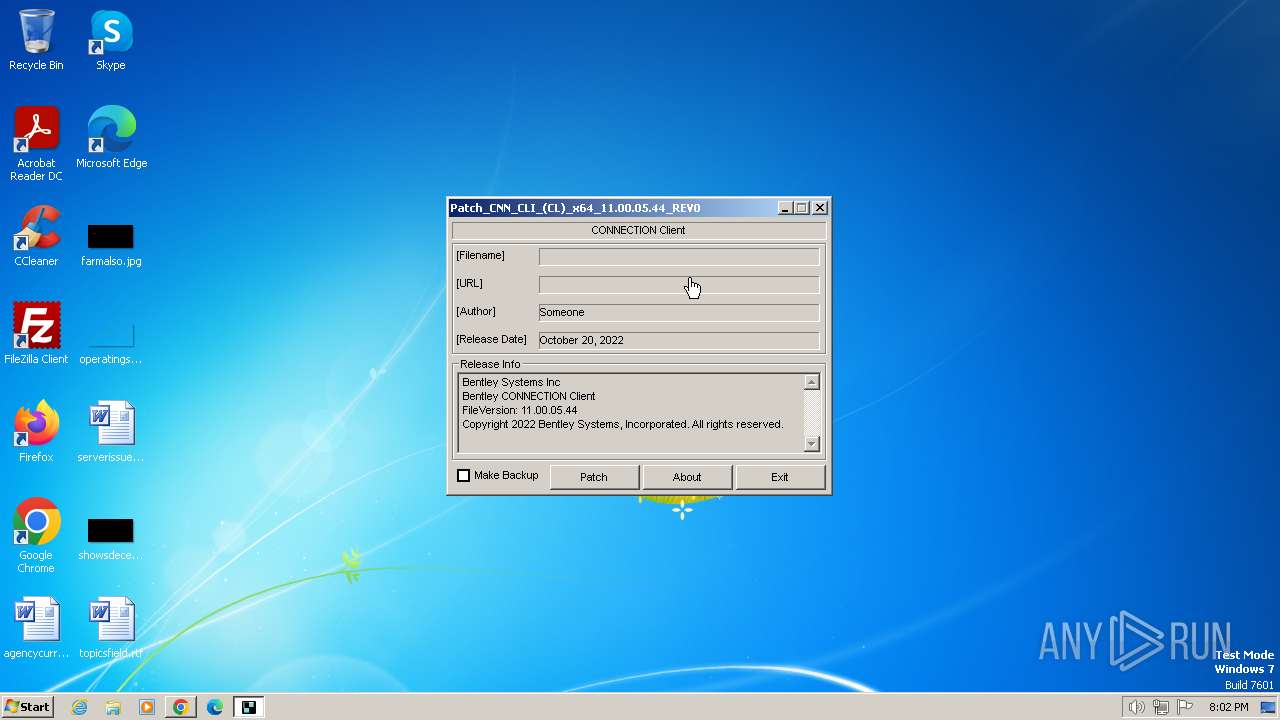
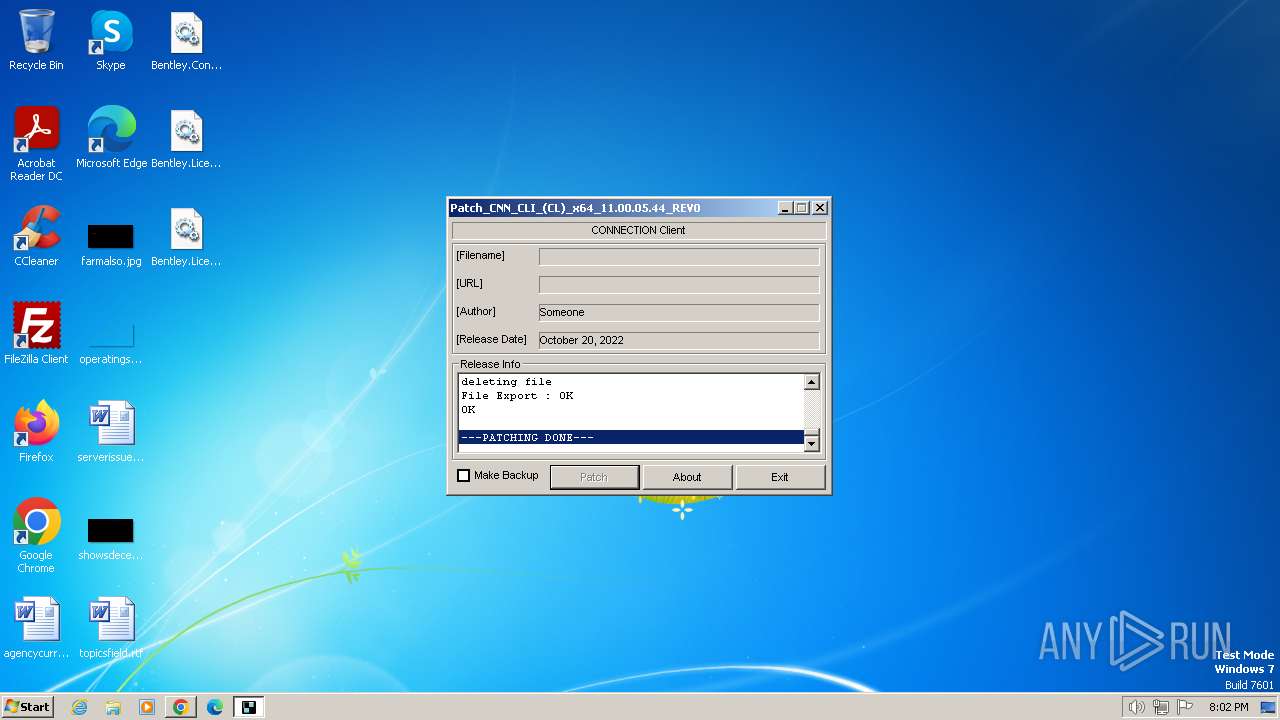
MALICIOUS
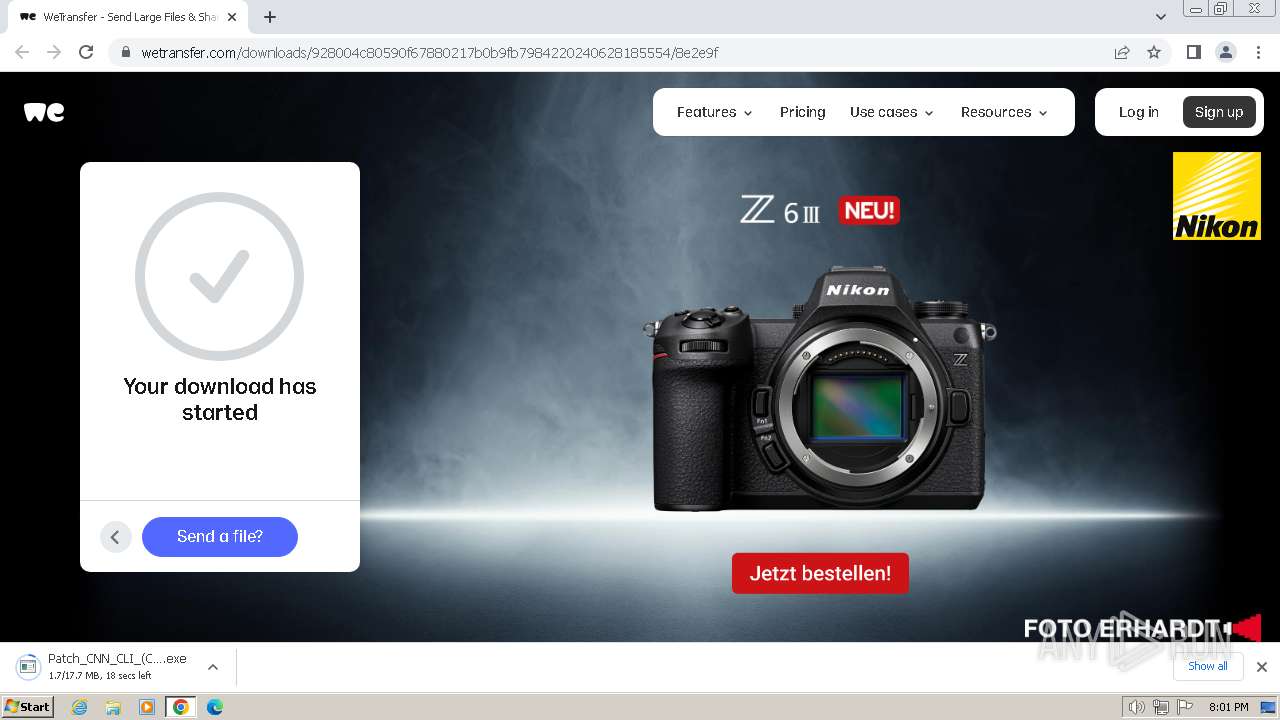
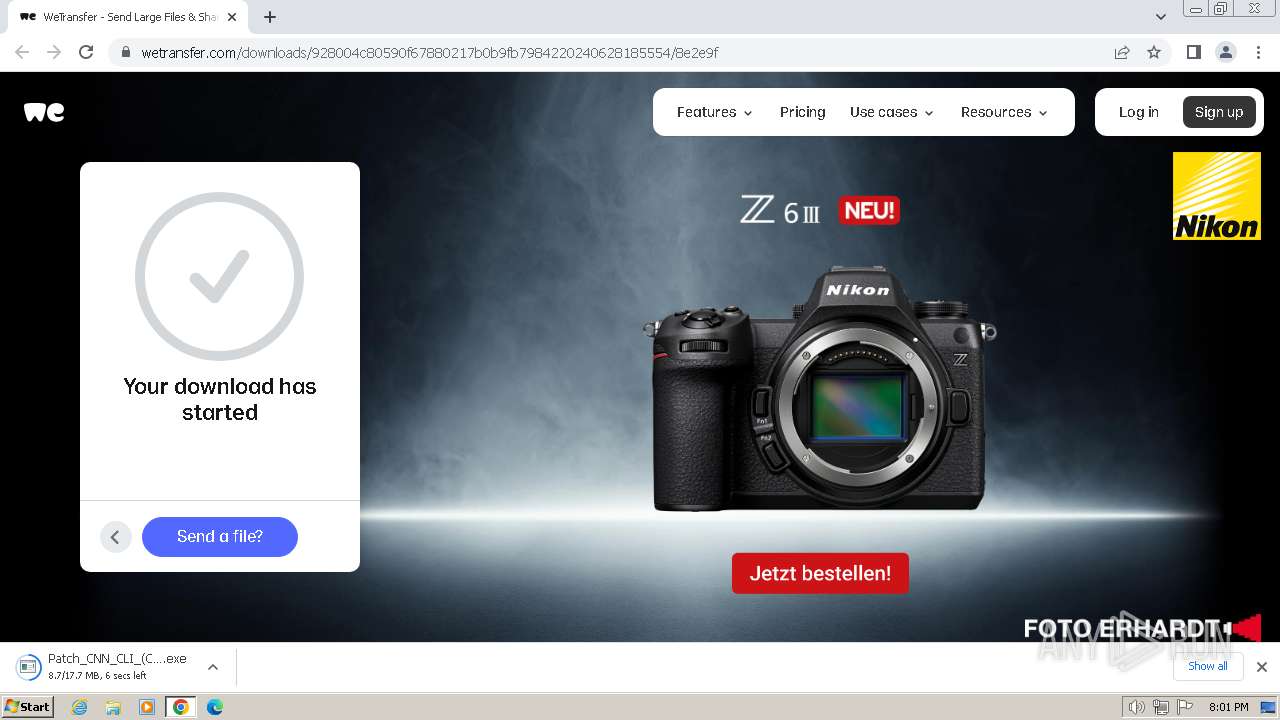
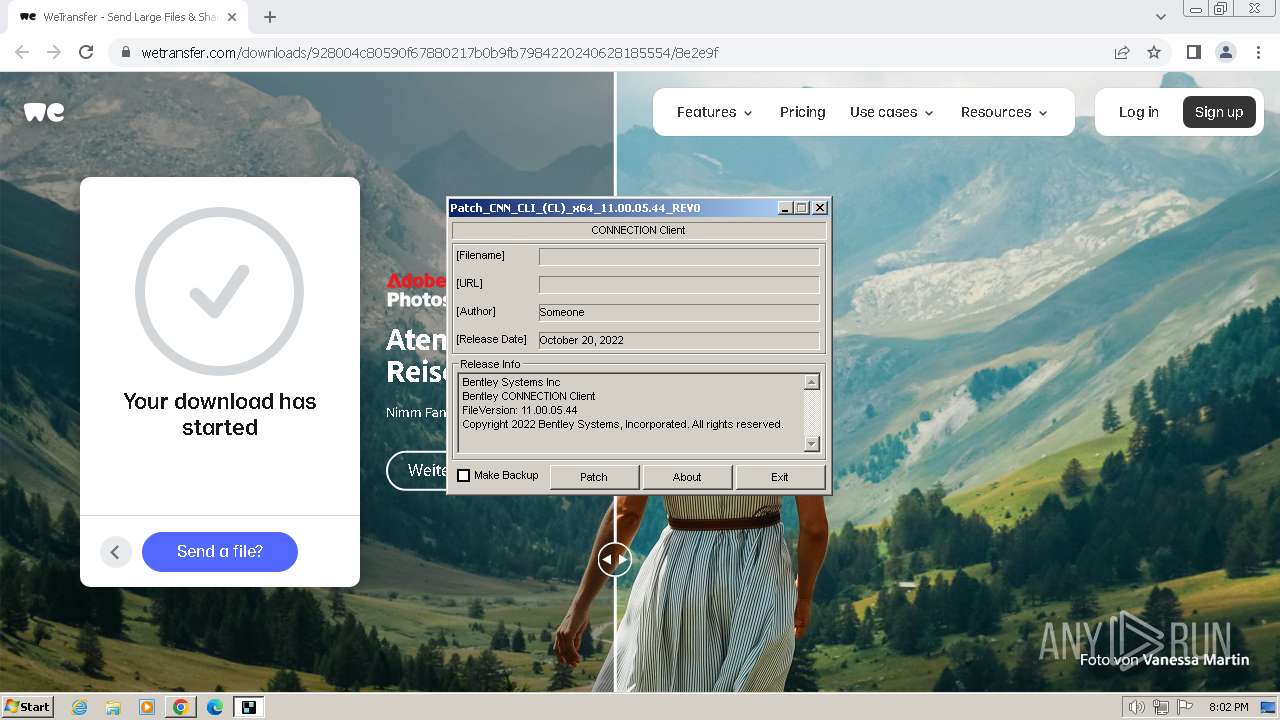
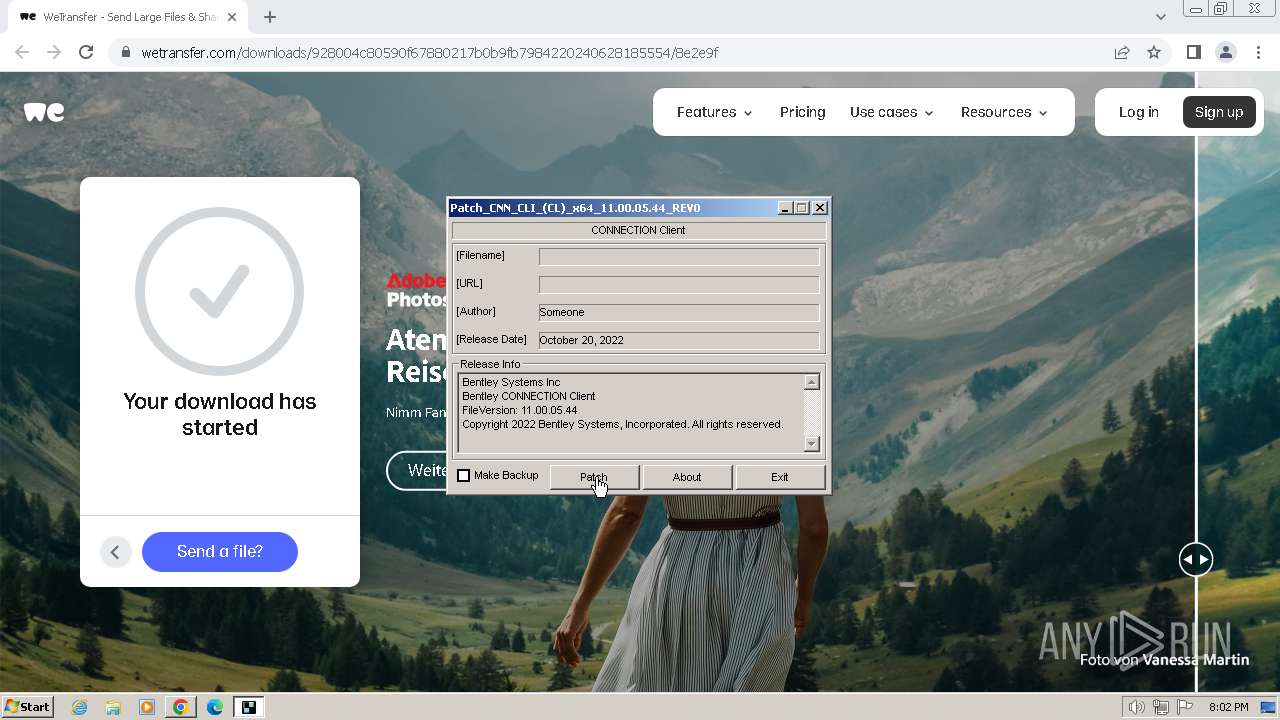
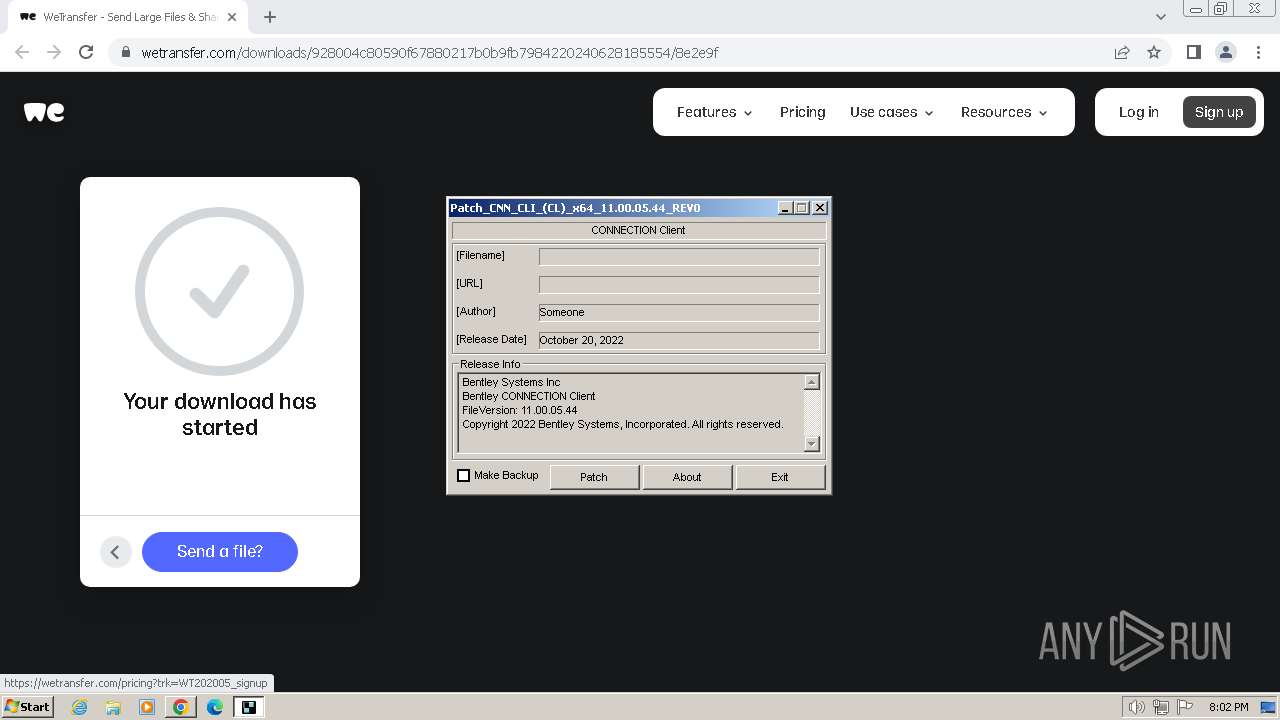
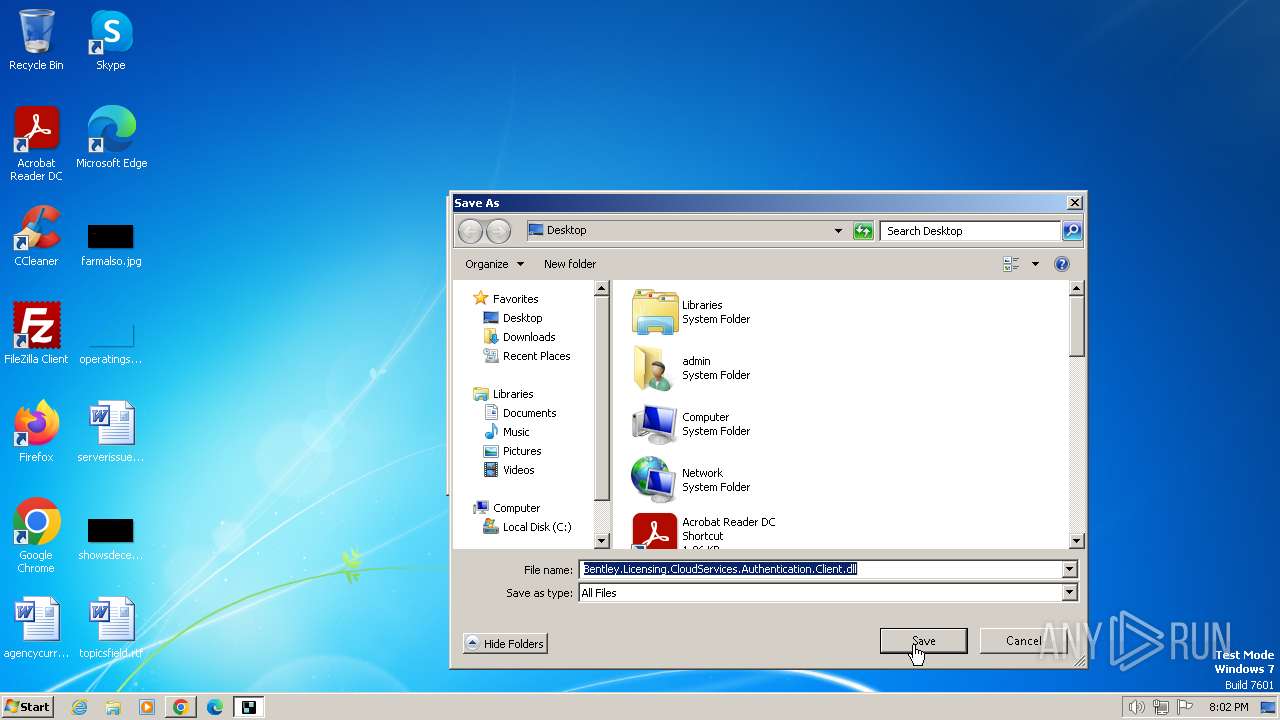
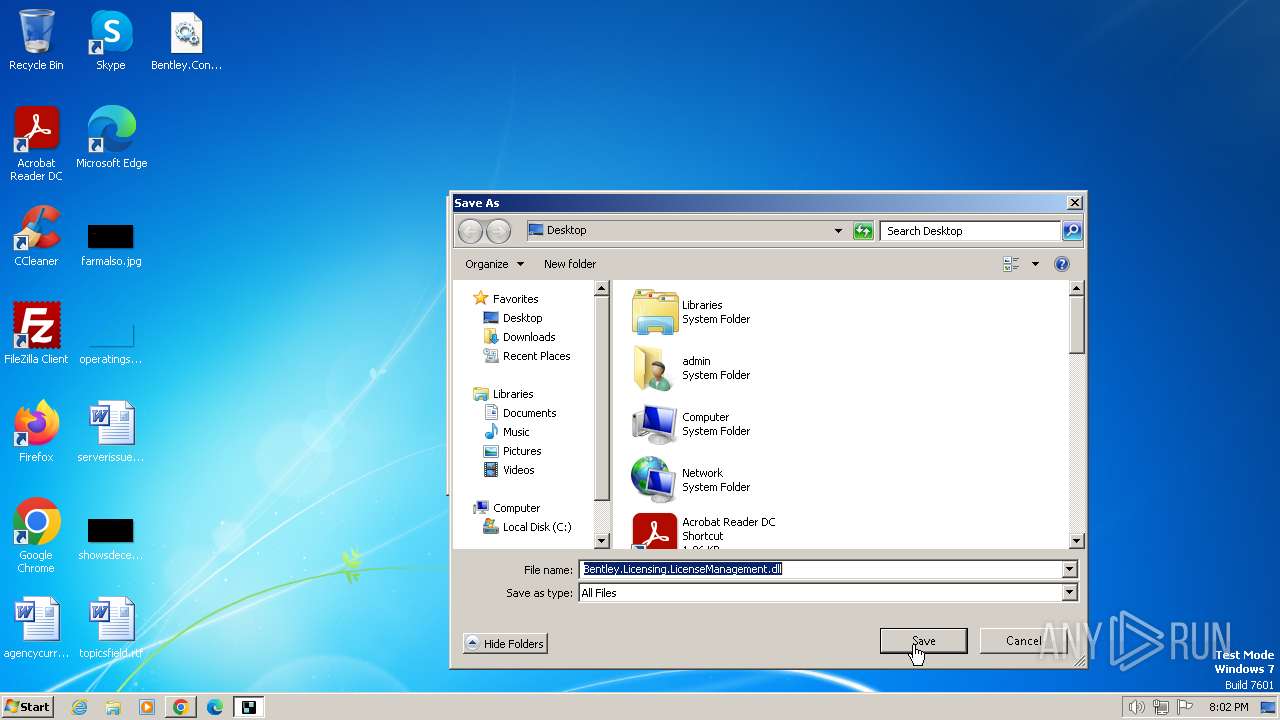
Drops the executable file immediately after the start
- Patch_CNN_CLI_(CL)_x64_11.00.05.44.exe (PID: 976)
SUSPICIOUS
Reads the BIOS version
- Patch_CNN_CLI_(CL)_x64_11.00.05.44.exe (PID: 976)
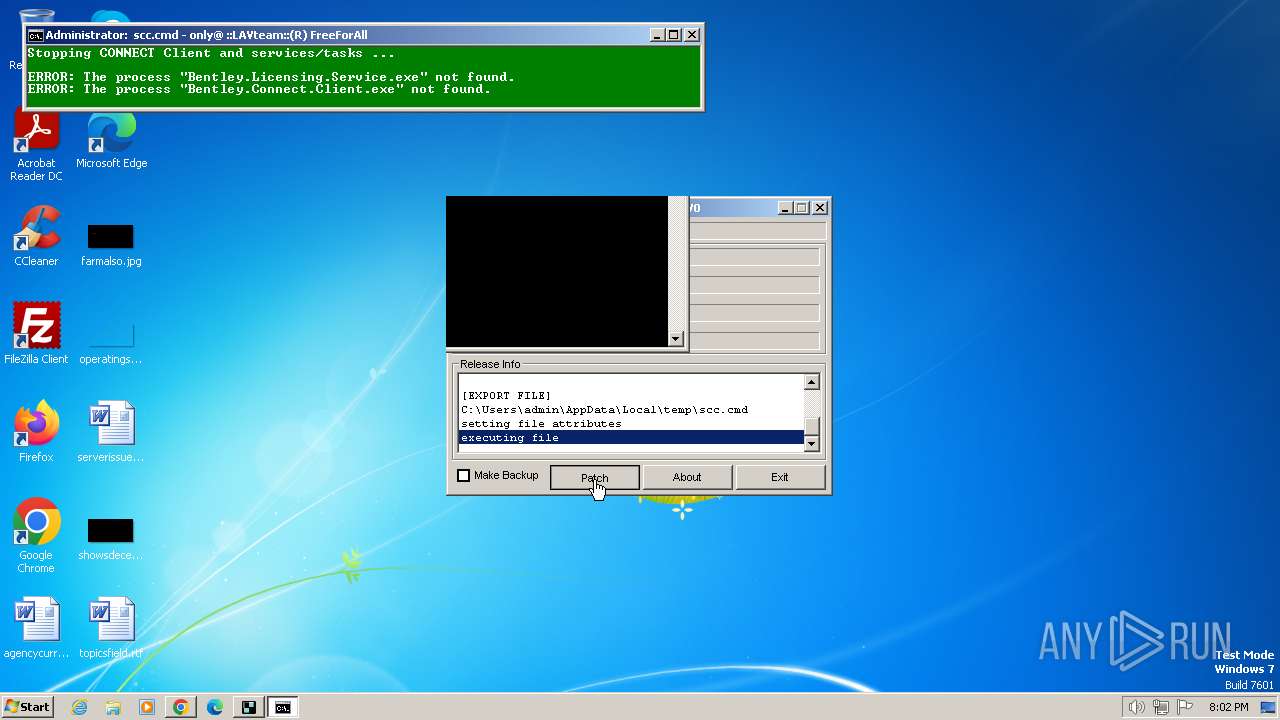
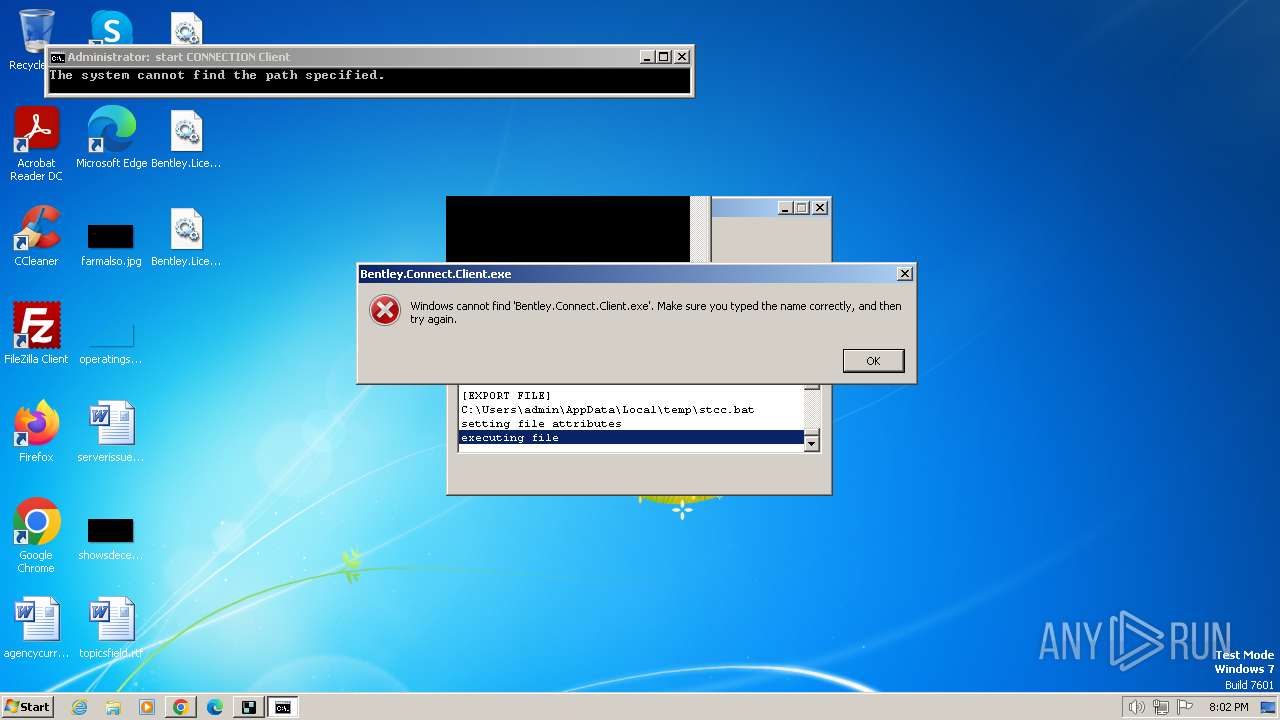
Starts CMD.EXE for commands execution
- Patch_CNN_CLI_(CL)_x64_11.00.05.44.exe (PID: 976)
Executing commands from ".cmd" file
- Patch_CNN_CLI_(CL)_x64_11.00.05.44.exe (PID: 976)
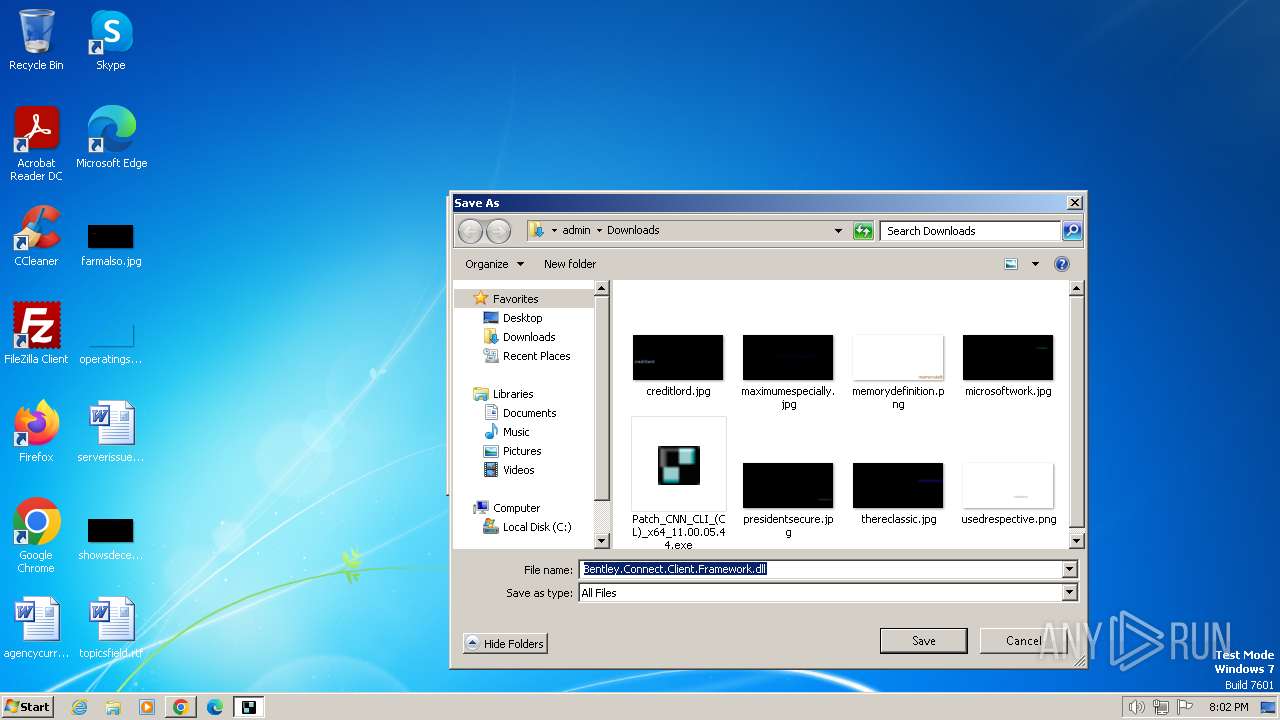
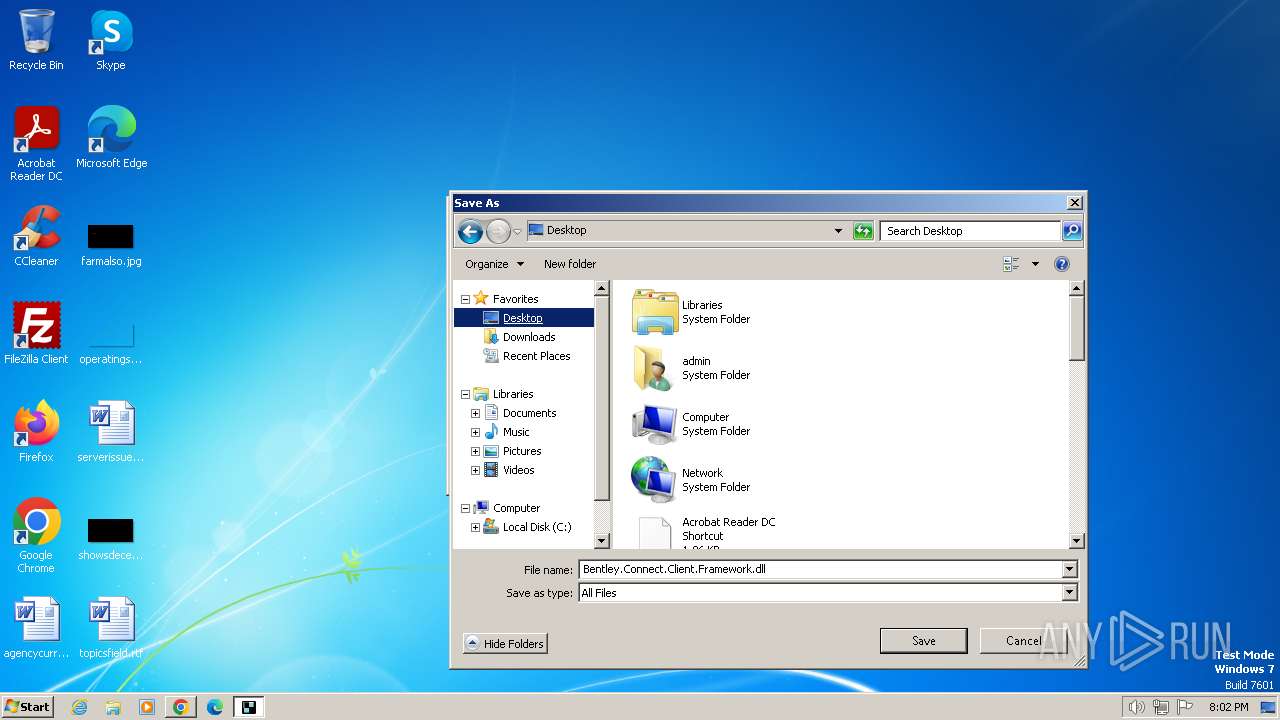
Executable content was dropped or overwritten
- Patch_CNN_CLI_(CL)_x64_11.00.05.44.exe (PID: 976)
Uses TASKKILL.EXE to kill process
- cmd.exe (PID: 2100)
Executing commands from a ".bat" file
- Patch_CNN_CLI_(CL)_x64_11.00.05.44.exe (PID: 976)
Reads the Internet Settings
- cmd.exe (PID: 1920)
- Patch_CNN_CLI_(CL)_x64_11.00.05.44.exe (PID: 976)
INFO
Checks supported languages
- wmpnscfg.exe (PID: 3308)
- Patch_CNN_CLI_(CL)_x64_11.00.05.44.exe (PID: 976)
- mode.com (PID: 2512)
- mode.com (PID: 1216)
Reads the computer name
- wmpnscfg.exe (PID: 3308)
- Patch_CNN_CLI_(CL)_x64_11.00.05.44.exe (PID: 976)
Process checks whether UAC notifications are on
- Patch_CNN_CLI_(CL)_x64_11.00.05.44.exe (PID: 976)
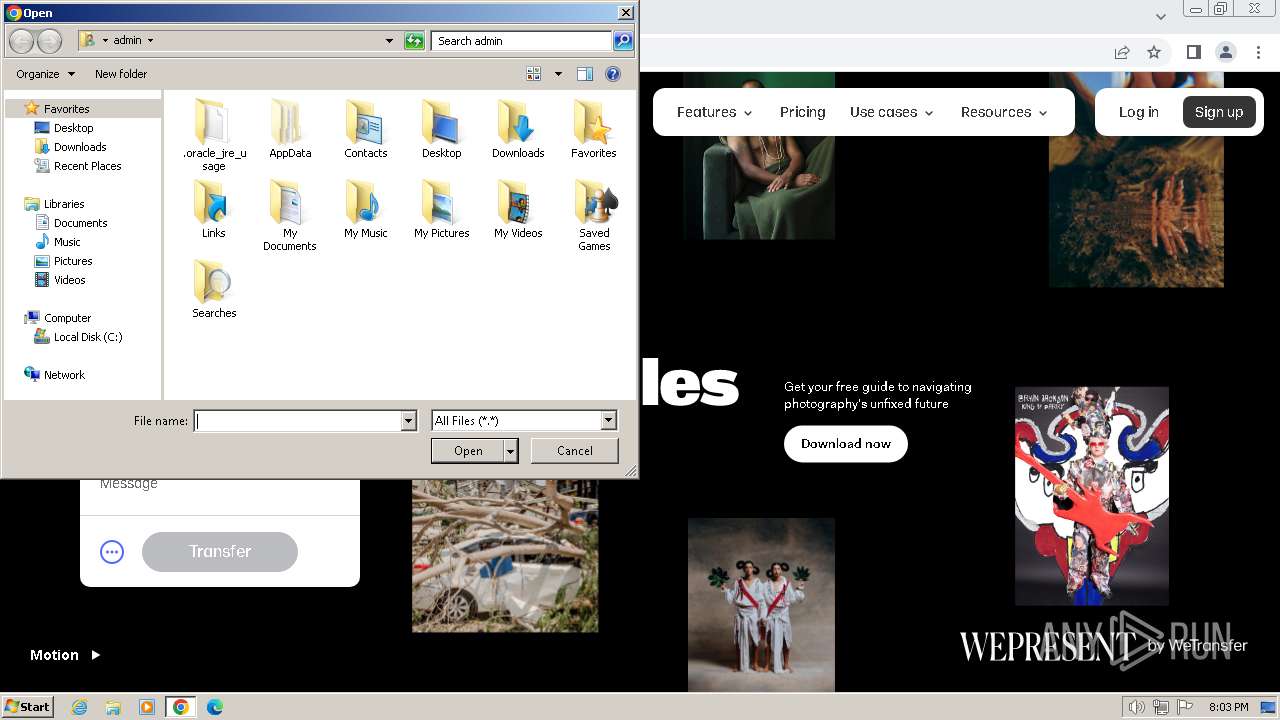
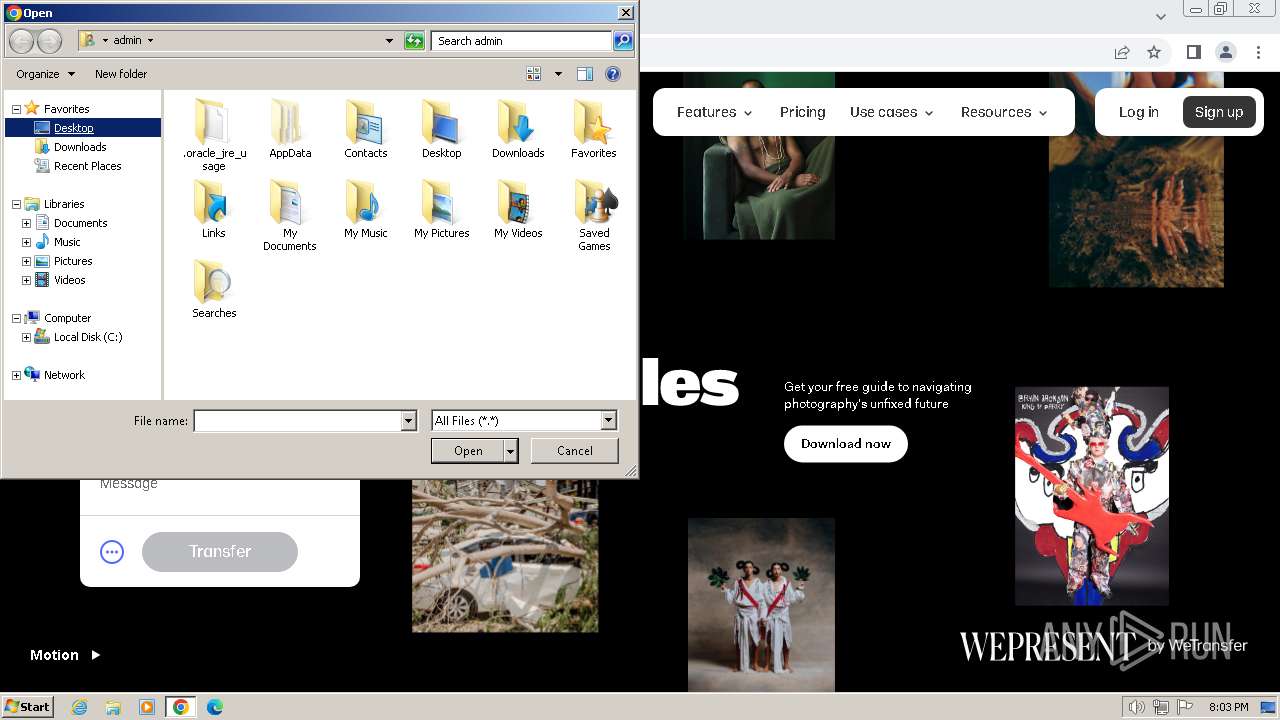
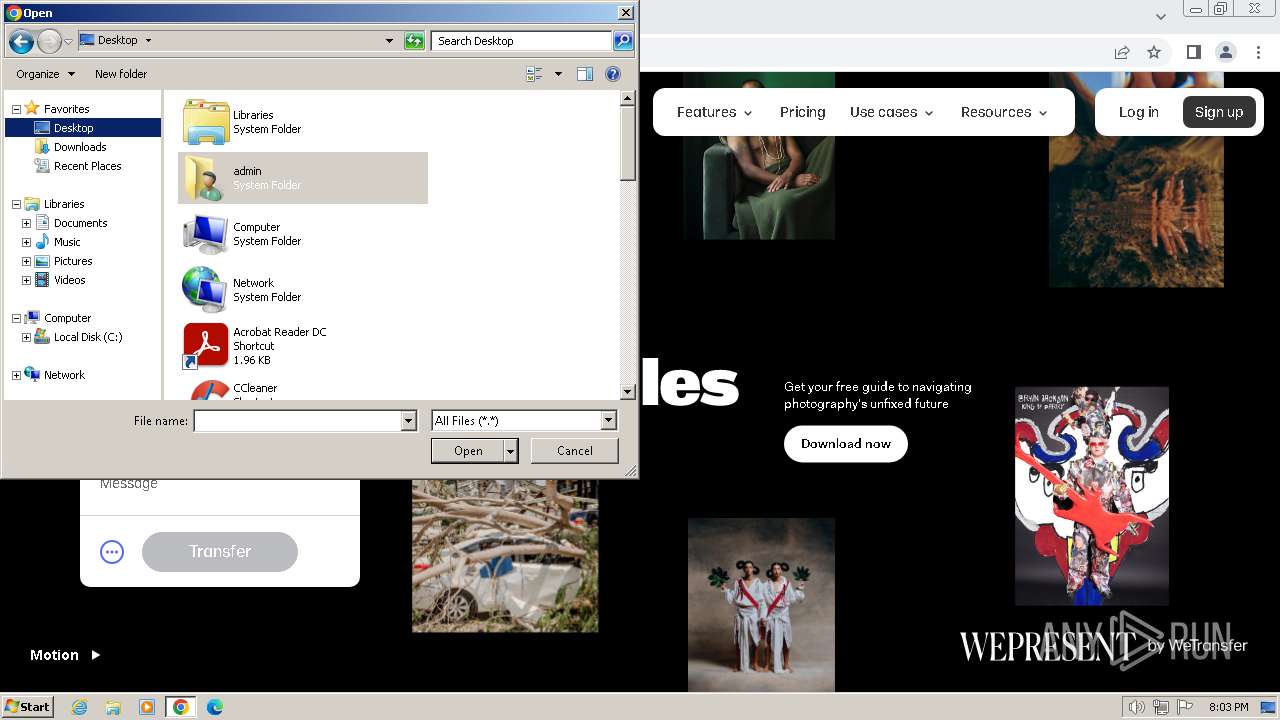
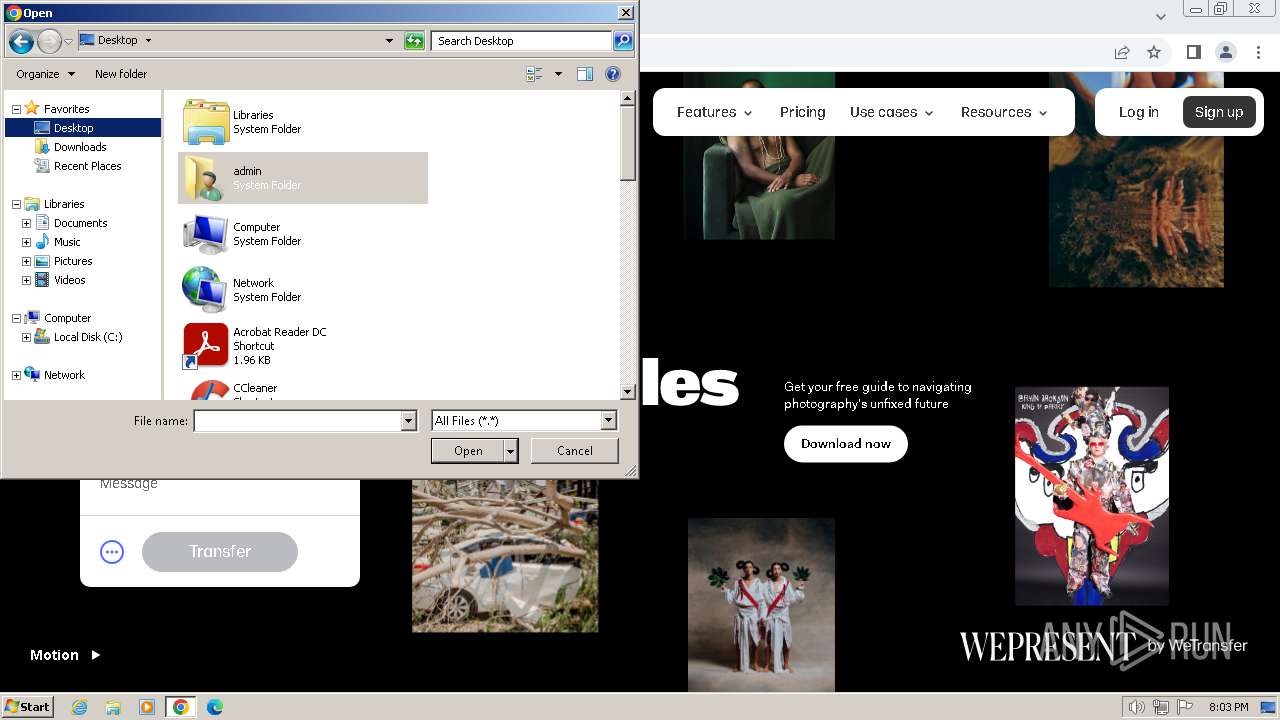
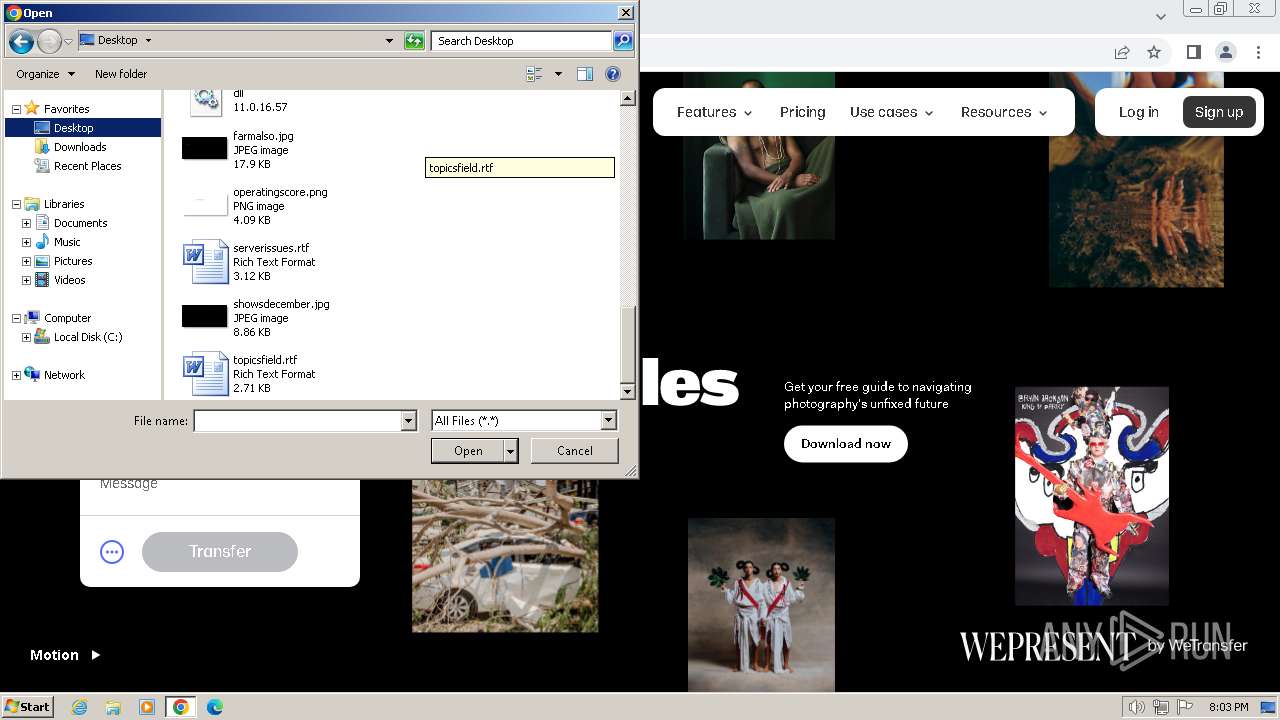
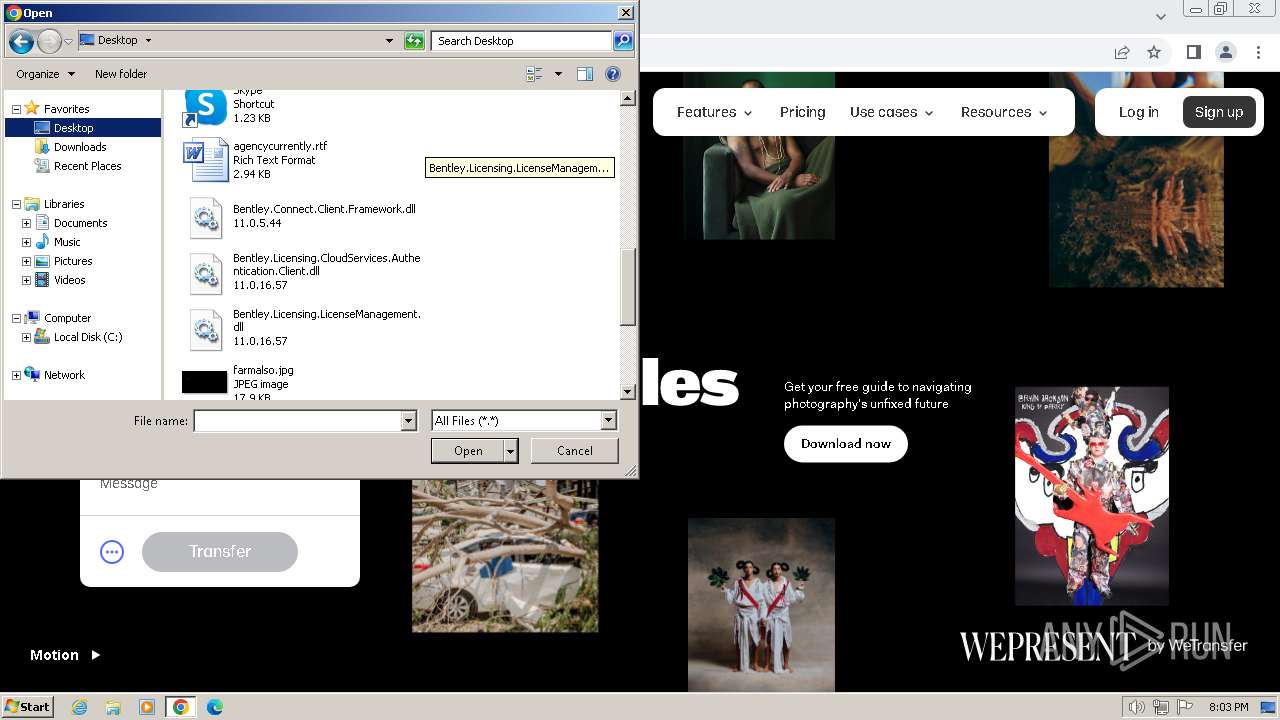
Manual execution by a user
- wmpnscfg.exe (PID: 3308)
The process uses the downloaded file
- chrome.exe (PID: 3392)
- chrome.exe (PID: 3792)
FSG packer has been detected
- Patch_CNN_CLI_(CL)_x64_11.00.05.44.exe (PID: 976)
Drops the executable file immediately after the start
- chrome.exe (PID: 3392)
- chrome.exe (PID: 3212)
- chrome.exe (PID: 2712)
Executable content was dropped or overwritten
- chrome.exe (PID: 3392)
- chrome.exe (PID: 2712)
- chrome.exe (PID: 3212)
Create files in a temporary directory
- Patch_CNN_CLI_(CL)_x64_11.00.05.44.exe (PID: 976)
Reads the machine GUID from the registry
- Patch_CNN_CLI_(CL)_x64_11.00.05.44.exe (PID: 976)
Application launched itself
- chrome.exe (PID: 3392)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
96
Monitored processes
44
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 952 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilReadIcon --lang=en-US --service-sandbox-type=icon_reader --disable-quic --mojo-platform-channel-handle=4164 --field-trial-handle=1156,i,17554600587425880886,3385982580253946947,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 976 | "C:\Users\admin\Downloads\Patch_CNN_CLI_(CL)_x64_11.00.05.44.exe" | C:\Users\admin\Downloads\Patch_CNN_CLI_(CL)_x64_11.00.05.44.exe | chrome.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 1000 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilReadIcon --lang=en-US --service-sandbox-type=icon_reader --disable-quic --mojo-platform-channel-handle=1356 --field-trial-handle=1156,i,17554600587425880886,3385982580253946947,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1044 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --mojo-platform-channel-handle=1680 --field-trial-handle=1156,i,17554600587425880886,3385982580253946947,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1072 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --mojo-platform-channel-handle=856 --field-trial-handle=1156,i,17554600587425880886,3385982580253946947,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1168 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilReadIcon --lang=en-US --service-sandbox-type=icon_reader --disable-quic --mojo-platform-channel-handle=4156 --field-trial-handle=1156,i,17554600587425880886,3385982580253946947,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1168 | ping -n 2 -w 1 127.0.0.1 | C:\Windows\System32\PING.EXE | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: TCP/IP Ping Command Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1216 | mode CON: COLS=80 LINES=2 | C:\Windows\System32\mode.com | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: DOS Device MODE Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1460 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=5 --mojo-platform-channel-handle=2044 --field-trial-handle=1156,i,17554600587425880886,3385982580253946947,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1468 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilReadIcon --lang=en-US --service-sandbox-type=icon_reader --disable-quic --mojo-platform-channel-handle=1348 --field-trial-handle=1156,i,17554600587425880886,3385982580253946947,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
Total events
27 371
Read events
27 014
Write events
332
Delete events
25
Modification events
| (PID) Process: | (3392) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3392) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3392) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (3392) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3392) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3392) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3392) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (3392) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3392) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (3392) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid |
Value: | |||
Executable files
11
Suspicious files
267
Text files
54
Unknown types
189
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3392 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RF4ec41.TMP | — | |
MD5:— | SHA256:— | |||
| 3392 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3392 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Local Storage\leveldb\LOG.old | text | |
MD5:FA25AF7098FC1571F24F200A9D105D58 | SHA256:4F40C87070B7A151FB241CCF36E7027AA703C15CA0ACB0A1759DA07B2C318574 | |||
| 3392 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:825B582C78EC88D54C215EFDF1EAD639 | SHA256:367995D01A8F13E5C30C79499F86B034775BFD009D83DC97635DE438D47DFA37 | |||
| 3392 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Session Storage\LOG.old~RF4ee83.TMP | text | |
MD5:E53573A93829681410D5E7DBB1B61C78 | SHA256:A82D28F2C1E22A2AE0ABC5F5AF0CC8EE7AD913BAB3A0BF84CE6D8D23F67E06A3 | |||
| 3392 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old~RF4eef0.TMP | text | |
MD5:4755704EAEB72509F8E78594142D80D6 | SHA256:52D45B3A4947B8B5B8C48F83F83BA6758CFB7C4434FC574124378F5B01E15999 | |||
| 3392 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old~RF4f019.TMP | — | |
MD5:— | SHA256:— | |||
| 3392 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3392 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF4ec9e.TMP | text | |
MD5:ECD3386BCC950E73B86EB128A5F57622 | SHA256:C9A068EAFBC587EDFC89392F64DDD350EEB96C5CF195CDB030BAB8F6DD33833B | |||
| 3392 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:456D3EF989973A7C218E338A6CFFAD25 | SHA256:75631D994431F254B94255C50038A3657BFC45D76FCE9D794D514E57CA678872 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
58
TCP/UDP connections
120
DNS requests
195
Threats
13
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1372 | svchost.exe | GET | 304 | 23.50.131.222:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?33775f6043c93e33 | unknown | — | — | unknown |
1060 | svchost.exe | GET | 304 | 23.50.131.202:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?a9f83325acc8ca75 | unknown | — | — | unknown |
1372 | svchost.exe | GET | 200 | 23.53.40.178:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | unknown |
1372 | svchost.exe | GET | 200 | 23.52.120.96:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | unknown |
844 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/k4ldha5kevpu7qn7k4s3mznvgu_4.10.2710.0/oimompecagnajdejgnnjijobebaeigek_4.10.2710.0_win32_ad2kbvs6jks3au5dsxn7cqflsiiq.crx3 | unknown | — | — | unknown |
844 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/k4ldha5kevpu7qn7k4s3mznvgu_4.10.2710.0/oimompecagnajdejgnnjijobebaeigek_4.10.2710.0_win32_ad2kbvs6jks3au5dsxn7cqflsiiq.crx3 | unknown | — | — | unknown |
844 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/k4ldha5kevpu7qn7k4s3mznvgu_4.10.2710.0/oimompecagnajdejgnnjijobebaeigek_4.10.2710.0_win32_ad2kbvs6jks3au5dsxn7cqflsiiq.crx3 | unknown | — | — | unknown |
844 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/k4ldha5kevpu7qn7k4s3mznvgu_4.10.2710.0/oimompecagnajdejgnnjijobebaeigek_4.10.2710.0_win32_ad2kbvs6jks3au5dsxn7cqflsiiq.crx3 | unknown | — | — | unknown |
844 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/k4ldha5kevpu7qn7k4s3mznvgu_4.10.2710.0/oimompecagnajdejgnnjijobebaeigek_4.10.2710.0_win32_ad2kbvs6jks3au5dsxn7cqflsiiq.crx3 | unknown | — | — | unknown |
844 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/k4ldha5kevpu7qn7k4s3mznvgu_4.10.2710.0/oimompecagnajdejgnnjijobebaeigek_4.10.2710.0_win32_ad2kbvs6jks3au5dsxn7cqflsiiq.crx3 | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1372 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1060 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
2564 | svchost.exe | 239.255.255.250:3702 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2076 | chrome.exe | 142.251.31.84:443 | accounts.google.com | GOOGLE | US | unknown |
3392 | chrome.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
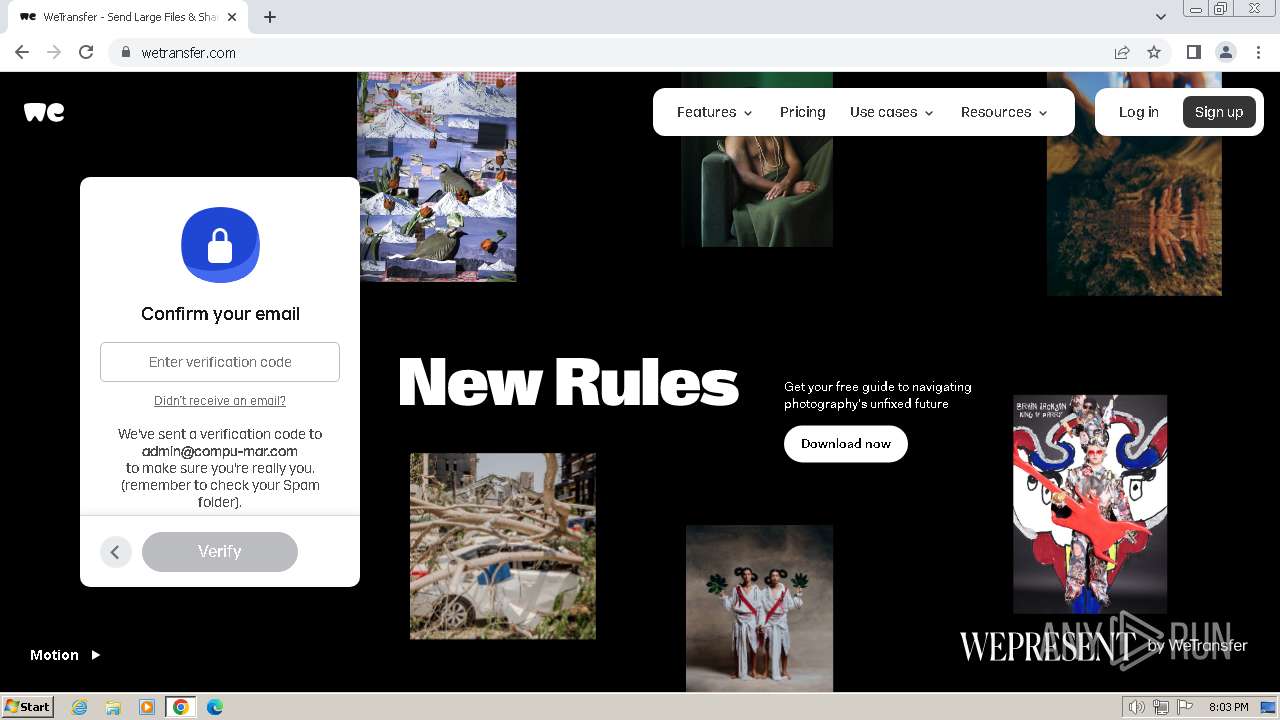
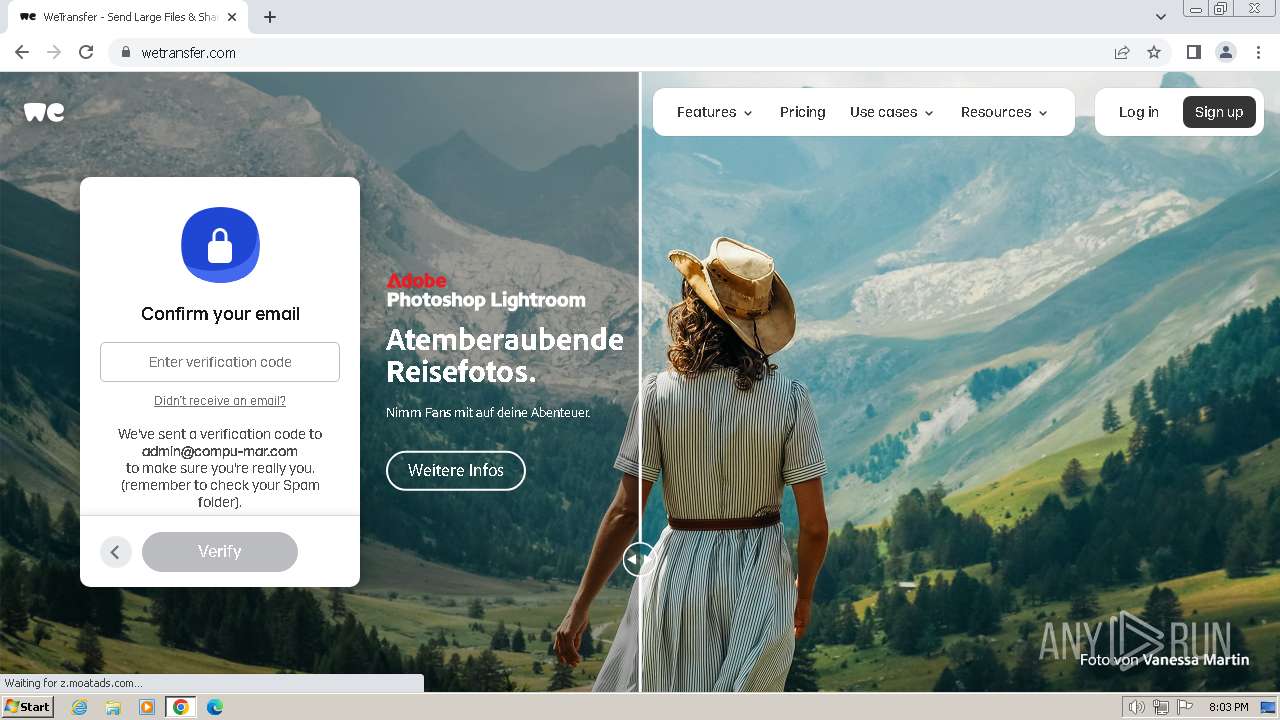
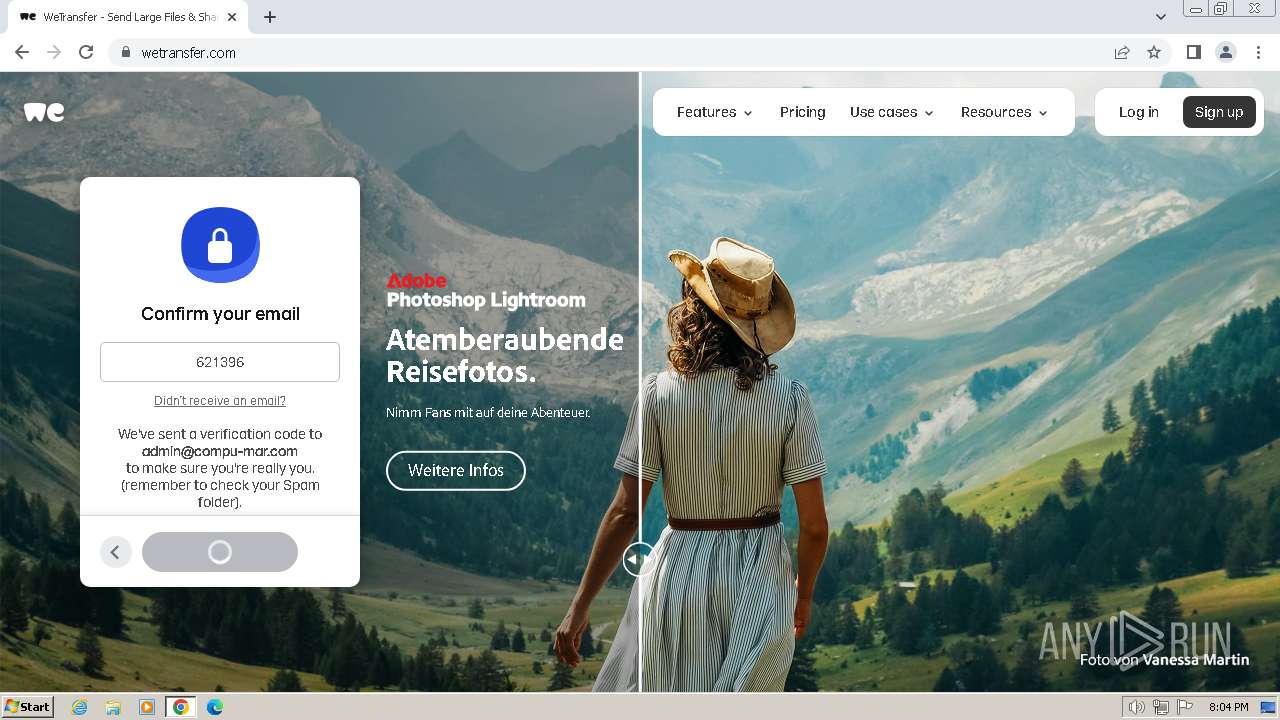
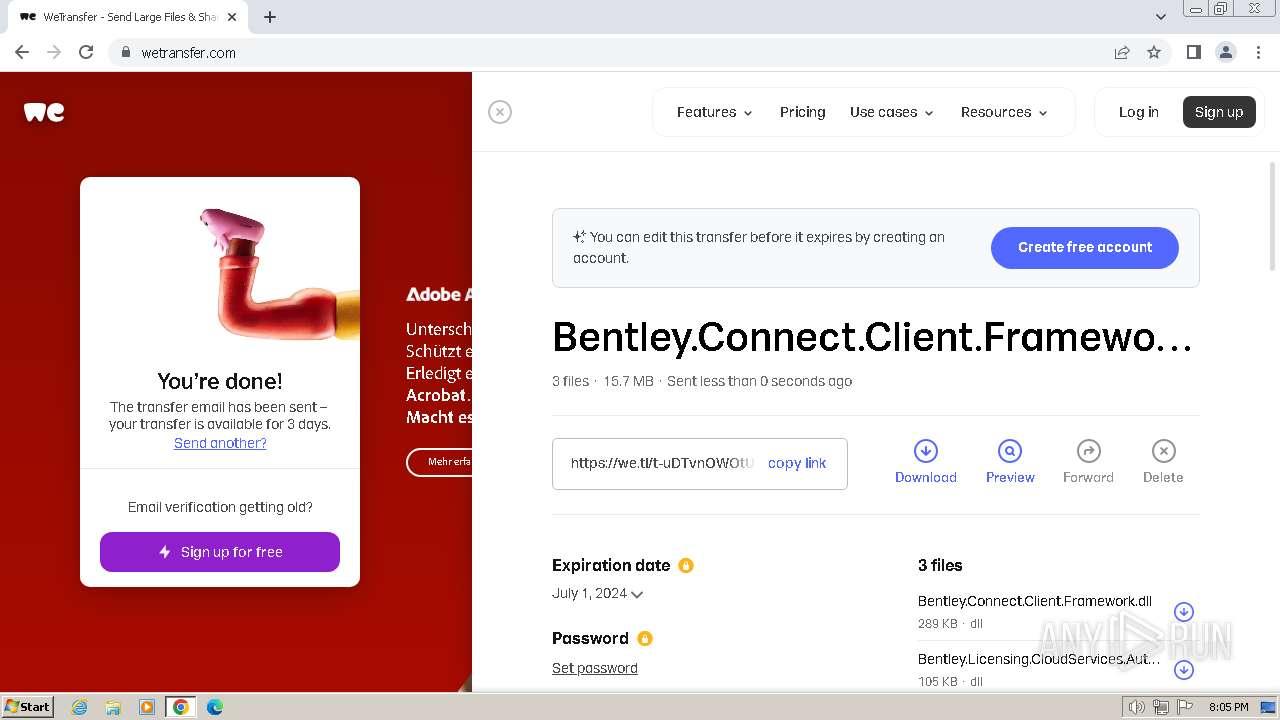
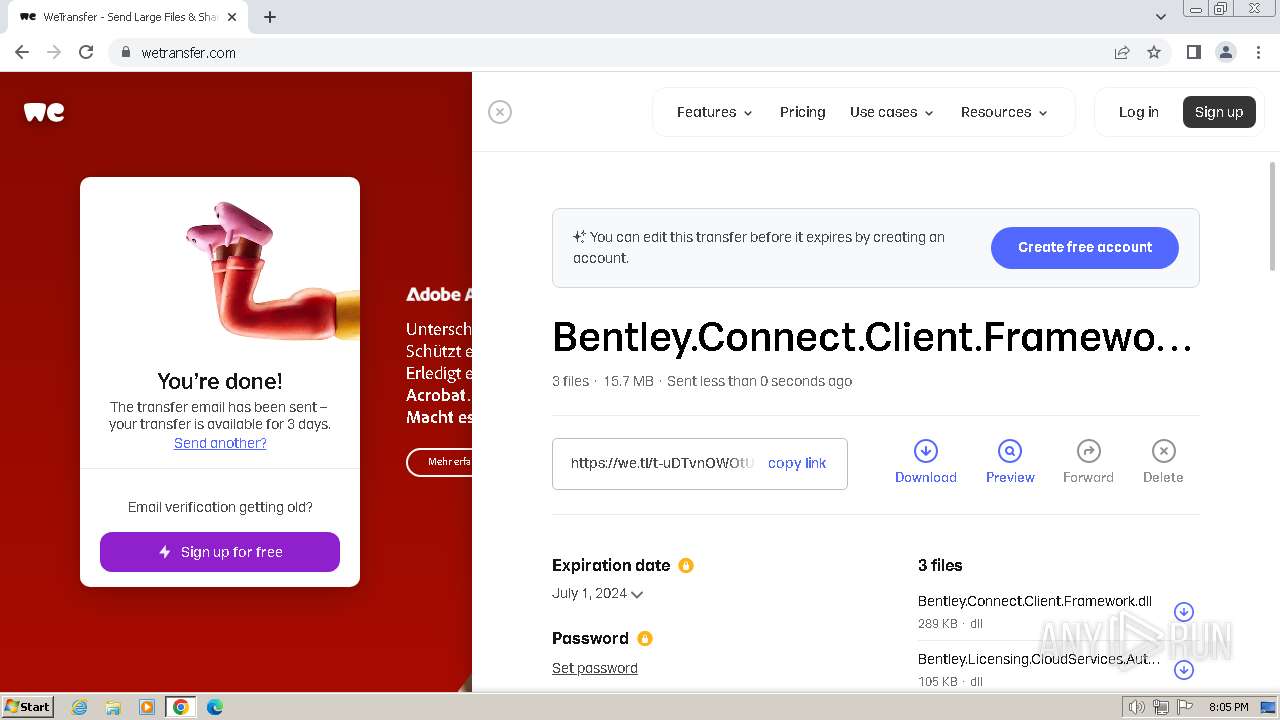
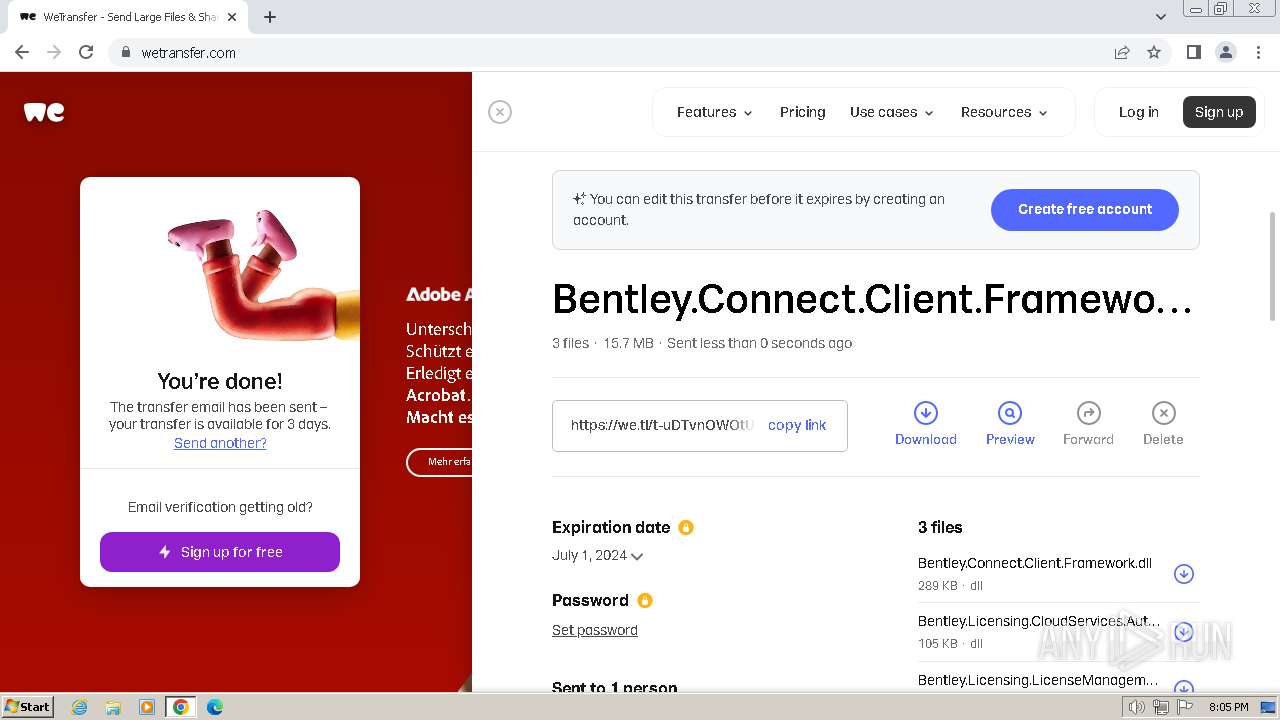
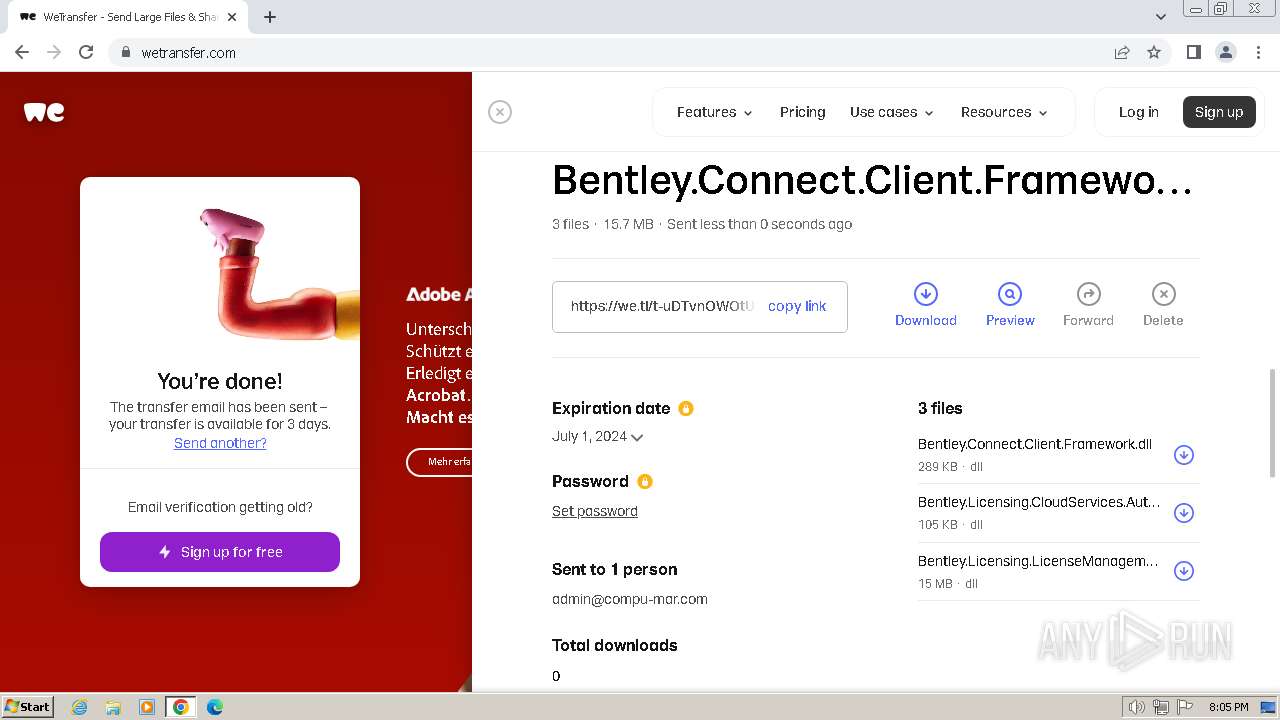
2076 | chrome.exe | 18.66.147.20:443 | we.tl | AMAZON-02 | US | unknown |
2076 | chrome.exe | 143.204.98.71:443 | wetransfer.com | AMAZON-02 | US | unknown |
2076 | chrome.exe | 151.101.193.229:443 | cdn.jsdelivr.net | FASTLY | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
accounts.google.com |
| shared |
we.tl |
| shared |
wetransfer.com |
| shared |
cdn.wetransfer.com |
| unknown |
cdn.jsdelivr.net |
| whitelisted |
tagging.wetransfer.com |
| unknown |
www.google-analytics.com |
| whitelisted |
public.profitwell.com |
| shared |
auth-session-caching.wetransfer.net |
| whitelisted |
experiments.wetransfer.com |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2076 | chrome.exe | Misc activity | ET INFO File Sharing Related Domain in DNS Lookup (wetransfer .com) |
2076 | chrome.exe | Misc activity | ET INFO File Sharing Domain Observed in TLS SNI (wetransfer .com) |
2076 | chrome.exe | Misc activity | ET INFO File Sharing Related Domain in DNS Lookup (wetransfer .com) |
2076 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Requests to a free CDN for open source projects (jsdelivr .net) |
2076 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Requests to a free CDN for open source projects (jsdelivr .net) |
2076 | chrome.exe | Misc activity | ET INFO File Sharing Related Domain in DNS Lookup (wetransfer .com) |
2076 | chrome.exe | Misc activity | ET INFO File Sharing Related Domain in DNS Lookup (wetransfer .com) |
2076 | chrome.exe | Misc activity | ET INFO File Sharing Related Domain in DNS Lookup (wetransfer .com) |
2076 | chrome.exe | Misc activity | ET INFO File Sharing Related Domain in DNS Lookup (wetransfer .com) |
2076 | chrome.exe | Misc activity | ET INFO File Sharing Related Domain in DNS Lookup (wetransfer .com) |
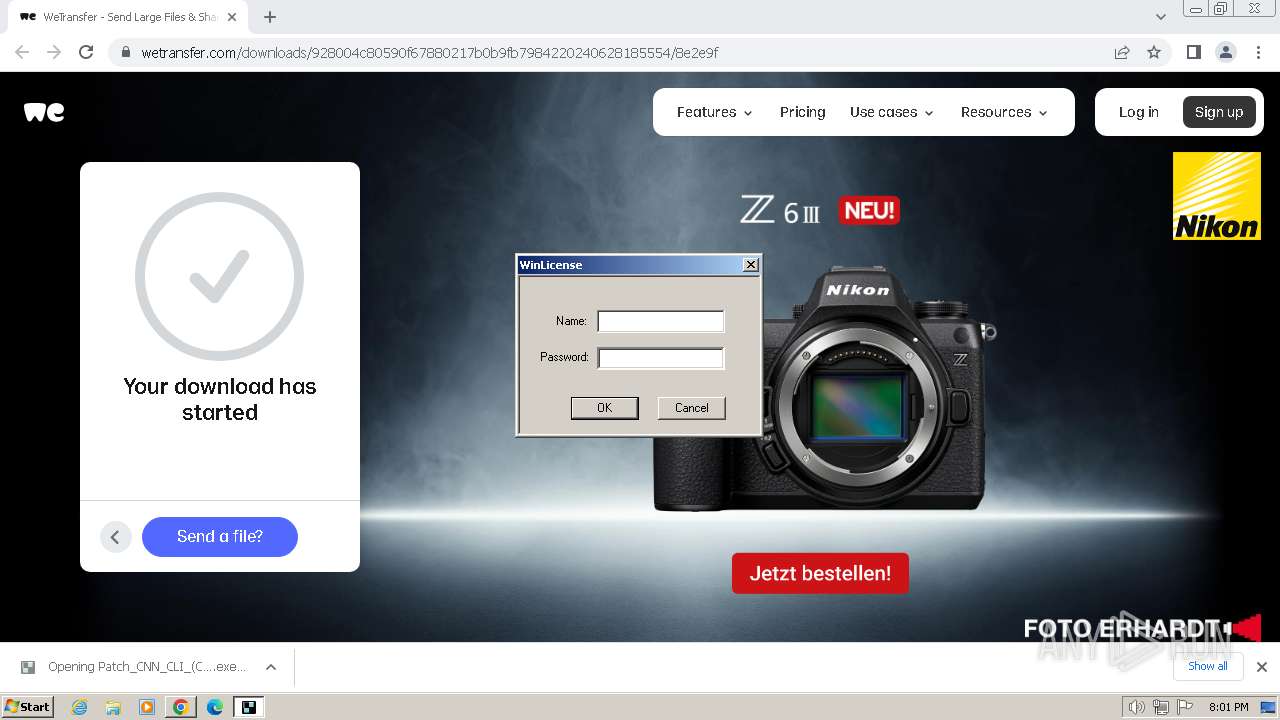
Process | Message |
|---|---|
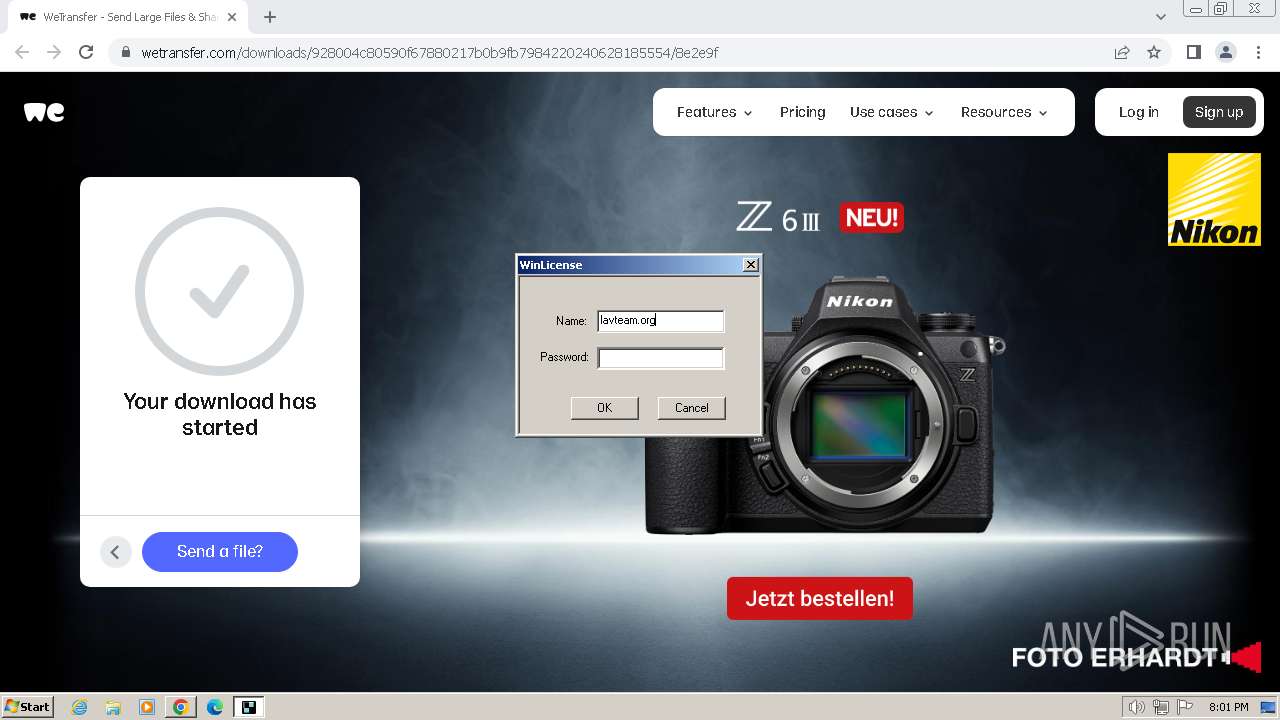
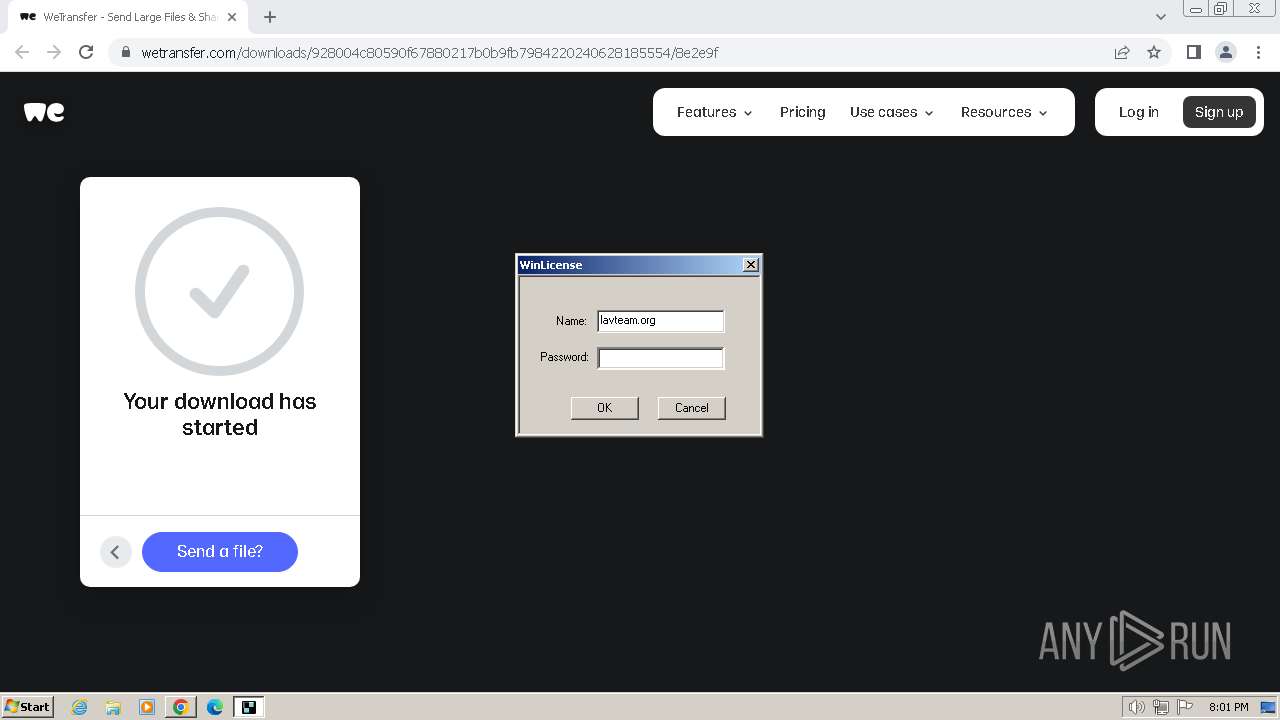
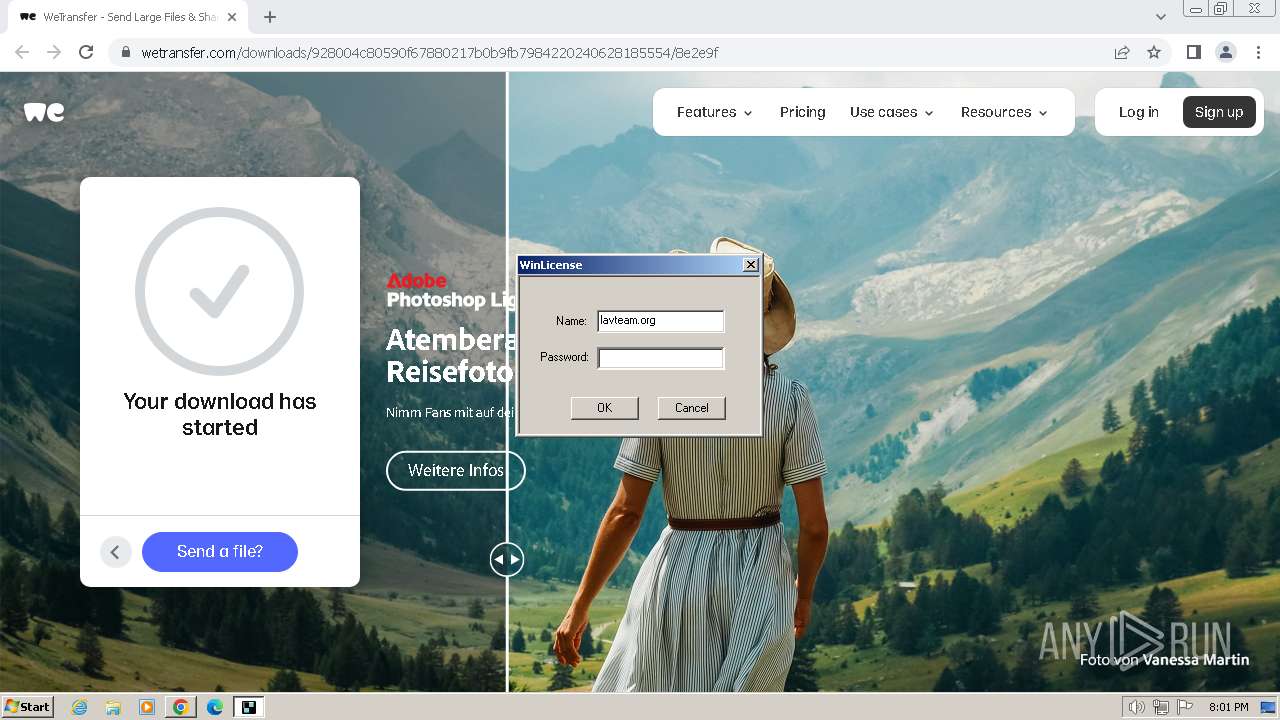
Patch_CNN_CLI_(CL)_x64_11.00.05.44.exe |
%s------------------------------------------------
--- WinLicense Professional ---
--- (c)2012 Oreans Technologies ---
------------------------------------------------
|