| File name: | inst.exe |
| Full analysis: | https://app.any.run/tasks/4aabd364-fa06-4a2c-ac48-b4f164bf3afc |
| Verdict: | Malicious activity |
| Analysis date: | December 11, 2018, 07:45:05 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | A972867B8B661D999E7D7DC20253DB95 |
| SHA1: | 93112BDEF8F443BF25FECE0D6826490B7E4F4F7C |
| SHA256: | 5BE93D7CC5A0A7D51DCAD5386B30C7133642E68EFB28D9383F7F5B29D812B6C8 |
| SSDEEP: | 49152:d5RYzxirZN3DKICwSB+NX6pKMHrawb88S1dmK2Vl:rRYtiFNTKIIDfHrawbkd2Vl |
MALICIOUS
Loads dropped or rewritten executable
- inst.exe (PID: 4012)
- setup_11.5.0.2001p.exe (PID: 2636)
Changes settings of System certificates
- inst.exe (PID: 4012)
Changes the autorun value in the registry
- setup_11.5.0.2001p.exe (PID: 2636)
SUSPICIOUS
Low-level read access rights to disk partition
- inst.exe (PID: 4012)
- setup_11.5.0.2001p.exe (PID: 2636)
Executable content was dropped or overwritten
- inst.exe (PID: 4012)
- setup_11.5.0.2001p.exe (PID: 2636)
Reads Internet Cache Settings
- inst.exe (PID: 4012)
Creates files in the user directory
- inst.exe (PID: 4012)
- setup_11.5.0.2001p.exe (PID: 2636)
Adds / modifies Windows certificates
- inst.exe (PID: 4012)
Connects to unusual port
- inst.exe (PID: 4012)
Creates a software uninstall entry
- setup_11.5.0.2001p.exe (PID: 2636)
Writes to a desktop.ini file (may be used to cloak folders)
- setup_11.5.0.2001p.exe (PID: 2636)
Creates files in the program directory
- setup_11.5.0.2001p.exe (PID: 2636)
INFO
Reads settings of System Certificates
- inst.exe (PID: 4012)
Dropped object may contain Bitcoin addresses
- setup_11.5.0.2001p.exe (PID: 2636)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (76.4) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (12.4) |
| .exe | | | Generic Win/DOS Executable (5.5) |
| .exe | | | DOS Executable Generic (5.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2018:07:20 08:58:54+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 9 |
| CodeSize: | 645632 |
| InitializedDataSize: | 1552896 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x73c1c |
| OSVersion: | 5 |
| ImageVersion: | - |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 11.0.0.1477 |
| ProductVersionNumber: | 11.0.0.1477 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Dynamic link library |
| FileSubtype: | - |
| LanguageCode: | Neutral 2 |
| CharacterSet: | Unicode |
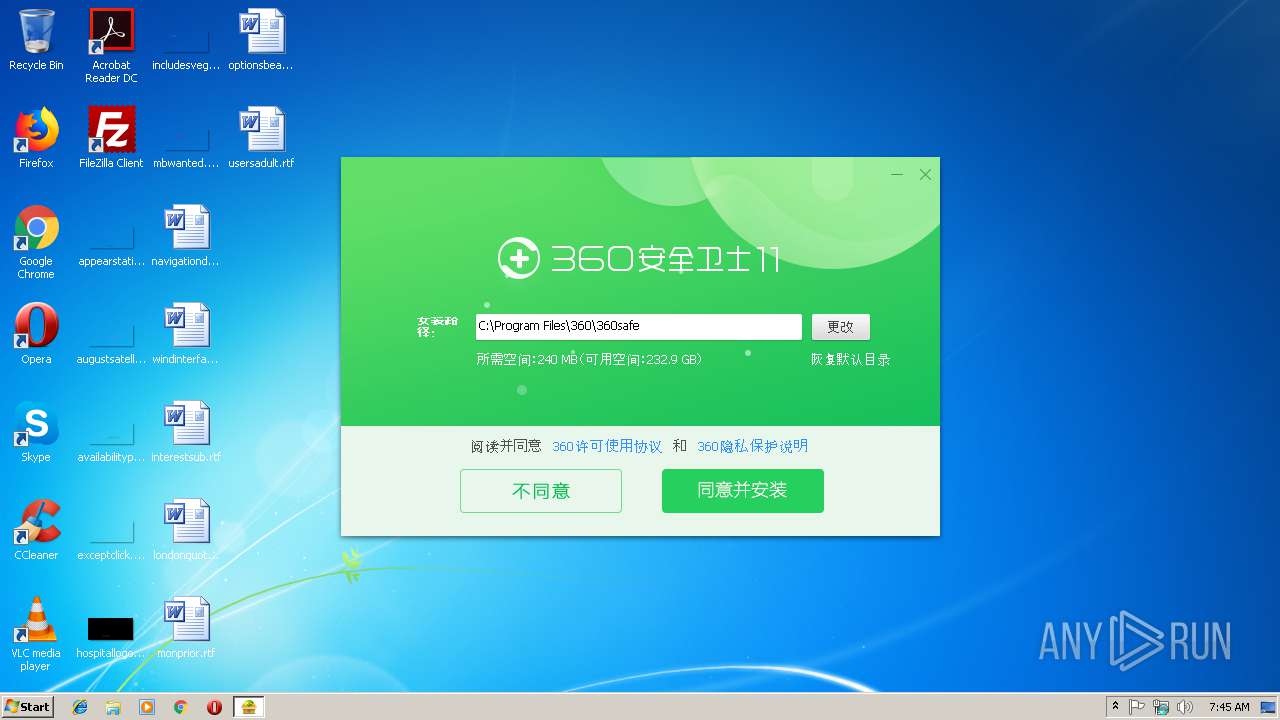
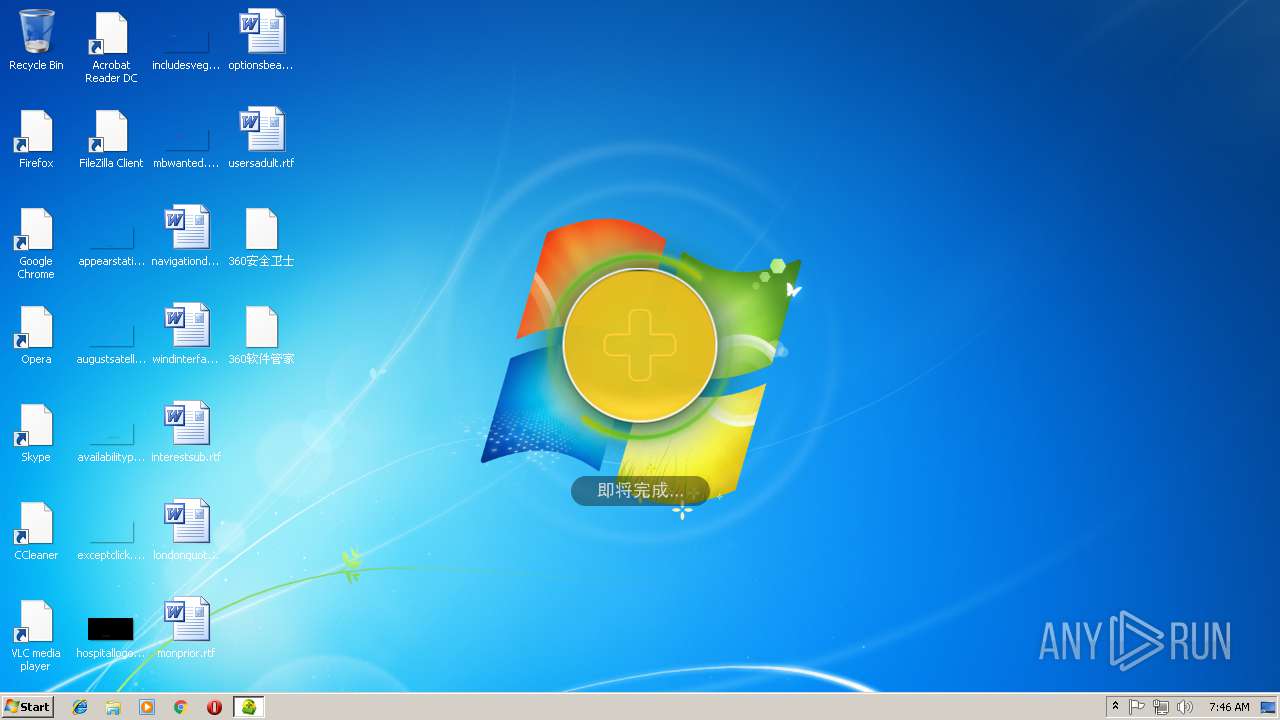
| CompanyName: | 360.cn |
| FileDescription: | 360 安全卫士在线安装程序 |
| FileVersion: | 11, 0, 0, 1477 |
| InternalName: | 360 Installer |
| LegalCopyright: | Copyright 2012 |
| OriginalFileName: | 360Installer.exe |
| ProductName: | 360 安全卫士在线安装程序 |
| ProductVersion: | 11, 0, 0, 1477 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 20-Jul-2018 06:58:54 |
| Detected languages: |
|
| Debug artifacts: |
|
| CompanyName: | 360.cn |
| FileDescription: | 360 安全卫士在线安装程序 |
| FileVersion: | 11, 0, 0, 1477 |
| InternalName: | 360 Installer |
| LegalCopyright: | Copyright 2012 |
| OriginalFilename: | 360Installer.exe |
| ProductName: | 360 安全卫士在线安装程序 |
| ProductVersion: | 11, 0, 0, 1477 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000108 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 20-Jul-2018 06:58:54 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0009D909 | 0x0009DA00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.66982 |
.rdata | 0x0009F000 | 0x0001CA2C | 0x0001CC00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.74987 |
.data | 0x000BC000 | 0x0000B70C | 0x00007E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.42897 |
.rsrc | 0x000C8000 | 0x0014D434 | 0x0014D600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.7016 |
.reloc | 0x00216000 | 0x000091B4 | 0x00009200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.34014 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.26275 | 1064 | Latin 1 / Western European | English - United States | RT_MANIFEST |
2 | 5.86453 | 4264 | Latin 1 / Western European | Chinese - PRC | RT_ICON |
3 | 5.65385 | 2440 | Latin 1 / Western European | Chinese - PRC | RT_ICON |
4 | 5.81505 | 1384 | Latin 1 / Western European | Chinese - PRC | RT_ICON |
5 | 4.16294 | 1384 | Latin 1 / Western European | Chinese - PRC | RT_ICON |
6 | 5.70608 | 1128 | Latin 1 / Western European | Chinese - PRC | RT_ICON |
9 | 5.82552 | 504 | Latin 1 / Western European | Chinese - PRC | RT_STRING |
10 | 5.76075 | 640 | Latin 1 / Western European | Chinese - PRC | RT_STRING |
11 | 5.87391 | 566 | Latin 1 / Western European | Chinese - PRC | RT_STRING |
12 | 6.37266 | 656 | Latin 1 / Western European | Chinese - PRC | RT_STRING |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
IPHLPAPI.DLL |
KERNEL32.dll |
MSIMG32.dll |
NETAPI32.dll |
OLEAUT32.dll |
PSAPI.DLL |
SETUPAPI.dll |
Total processes
35
Monitored processes
3
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
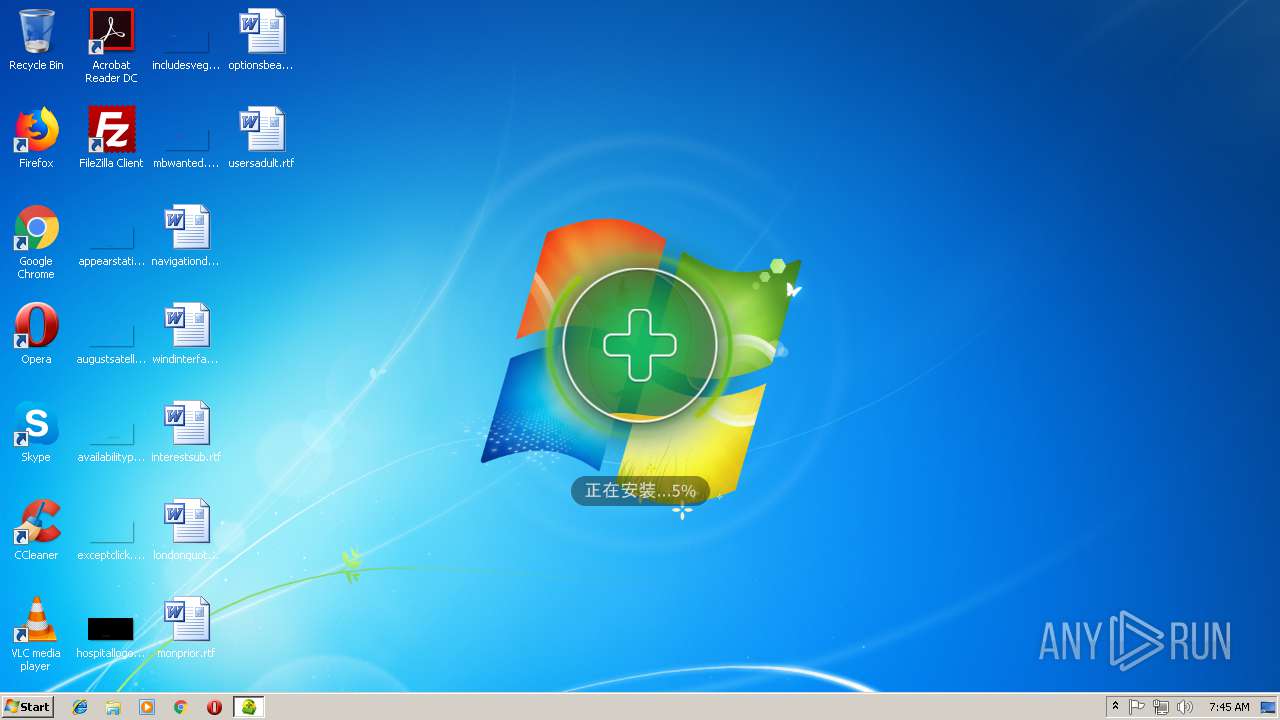
| 2636 | "C:\Users\admin\AppData\Local\Temp\setup_11.5.0.2001p.exe" /pid=h_home_inst_new /noreboot=1 /installer=1 /S /D= C:\Program Files\360\360safe /NOTIFYWND=131442 /FORCESTART /SmartSilence /instver=11.0.0.1477 /SETHOMEPAGE=FALSE /disable= | C:\Users\admin\AppData\Local\Temp\setup_11.5.0.2001p.exe | inst.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: 360 安全卫士 Exit code: 0 Version: 11.5.0.2019 Modules
| |||||||||||||||
| 3124 | "C:\Users\admin\AppData\Local\Temp\inst.exe" | C:\Users\admin\AppData\Local\Temp\inst.exe | — | explorer.exe | |||||||||||
User: admin Company: 360.cn Integrity Level: MEDIUM Description: 360 安全卫士在线安装程序 Exit code: 3221226540 Version: 11, 0, 0, 1477 Modules
| |||||||||||||||
| 4012 | "C:\Users\admin\AppData\Local\Temp\inst.exe" | C:\Users\admin\AppData\Local\Temp\inst.exe | explorer.exe | ||||||||||||
User: admin Company: 360.cn Integrity Level: HIGH Description: 360 安全卫士在线安装程序 Exit code: 1 Version: 11, 0, 0, 1477 Modules
| |||||||||||||||
Total events
3 642
Read events
602
Write events
3 035
Delete events
5
Modification events
| (PID) Process: | (4012) inst.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\inst_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (4012) inst.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\inst_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (4012) inst.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\inst_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (4012) inst.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\inst_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (4012) inst.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\inst_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (4012) inst.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\inst_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (4012) inst.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\inst_RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (4012) inst.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\inst_RASMANCS |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (4012) inst.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\inst_RASMANCS |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (4012) inst.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\inst_RASMANCS |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
Executable files
73
Suspicious files
263
Text files
686
Unknown types
24
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4012 | inst.exe | C:\Users\admin\AppData\Local\Temp\{5B15774C-0303-48a1-B55D-76AE86452496}.tmp | — | |
MD5:— | SHA256:— | |||
| 4012 | inst.exe | C:\Users\admin\AppData\Local\Temp\!@tAF8D.tmp | — | |
MD5:— | SHA256:— | |||
| 4012 | inst.exe | C:\Users\admin\AppData\Local\Temp\!@tAF8D.tmp.dir\custom_wnd.ini | — | |
MD5:— | SHA256:— | |||
| 4012 | inst.exe | C:\Users\admin\AppData\Local\Temp\!@tAF8D.tmp.dir\desktop_assistant_icon.png | — | |
MD5:— | SHA256:— | |||
| 4012 | inst.exe | C:\Users\admin\AppData\Local\Temp\!@tAF8D.tmp.dir\phone_assistant_icon.png | — | |
MD5:— | SHA256:— | |||
| 4012 | inst.exe | C:\Users\admin\AppData\Local\Temp\!@tAF8D.tmp.dir\setup.ini | — | |
MD5:— | SHA256:— | |||
| 4012 | inst.exe | C:\Users\admin\AppData\Local\Temp\setup_11.5.0.2001p.exe.P2P | — | |
MD5:— | SHA256:— | |||
| 4012 | inst.exe | C:\Users\admin\AppData\Local\Temp\setup_11.5.0.2001p.exe | — | |
MD5:— | SHA256:— | |||
| 4012 | inst.exe | C:\Users\admin\AppData\Local\Temp\setup_11.5.0.2001p.exe.mem | — | |
MD5:— | SHA256:— | |||
| 4012 | inst.exe | C:\Users\admin\AppData\Local\Temp\setup_11.5.0.2001p.exe.trt | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
100
TCP/UDP connections
124
DNS requests
8
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
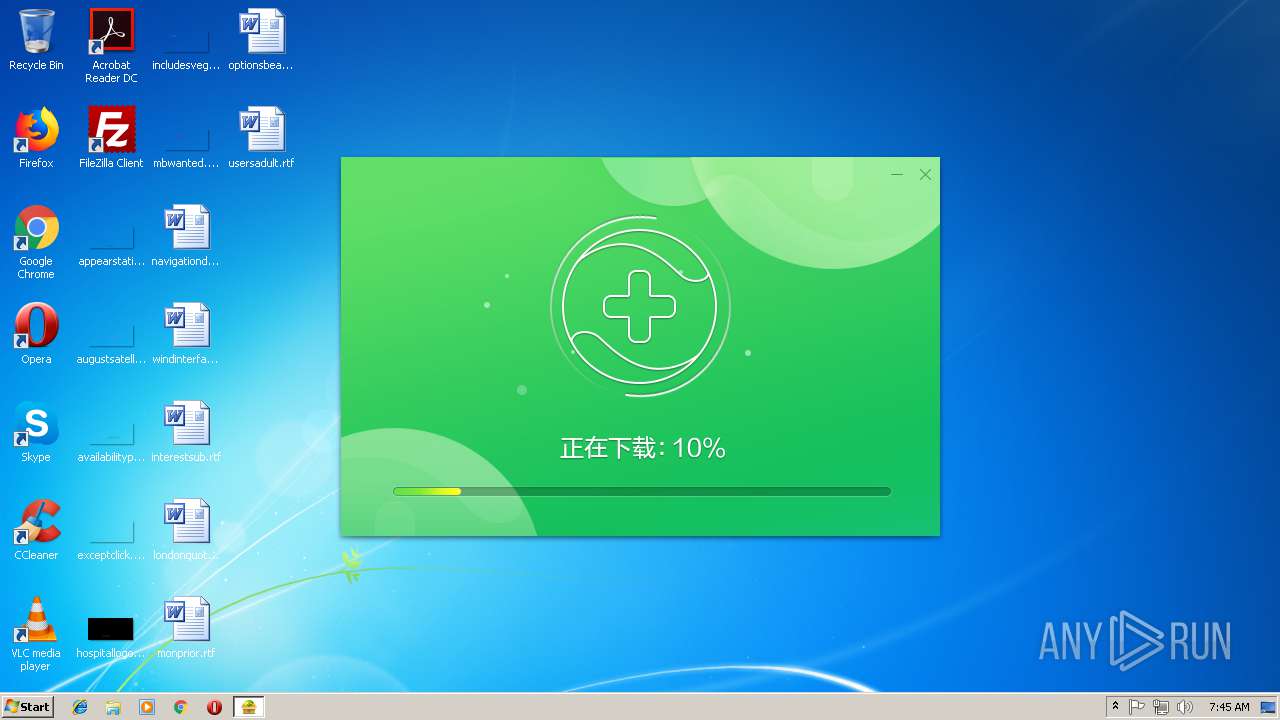
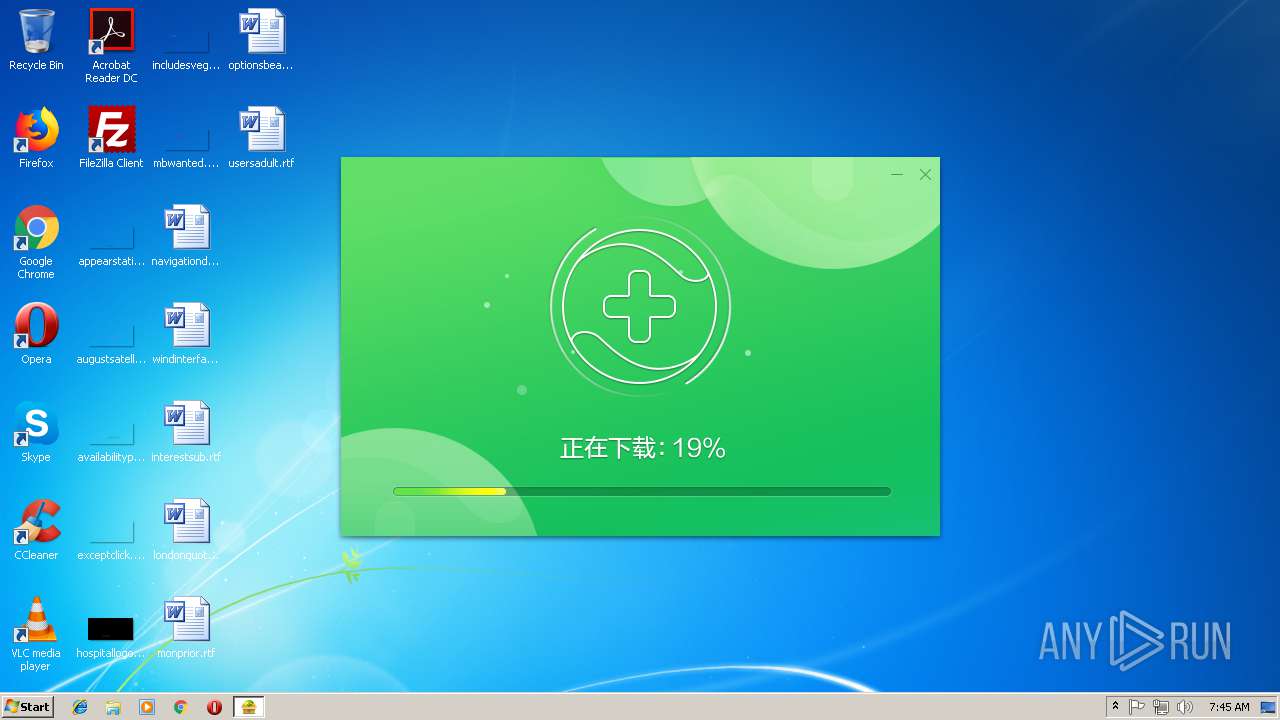
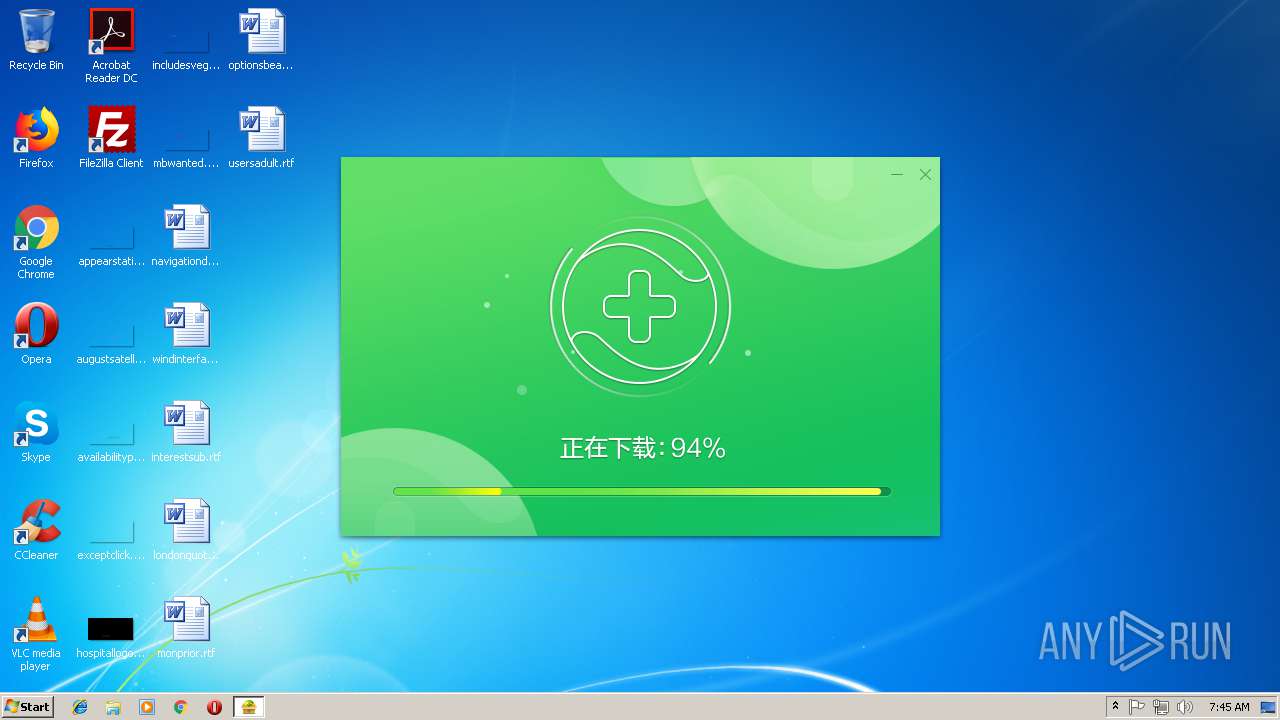
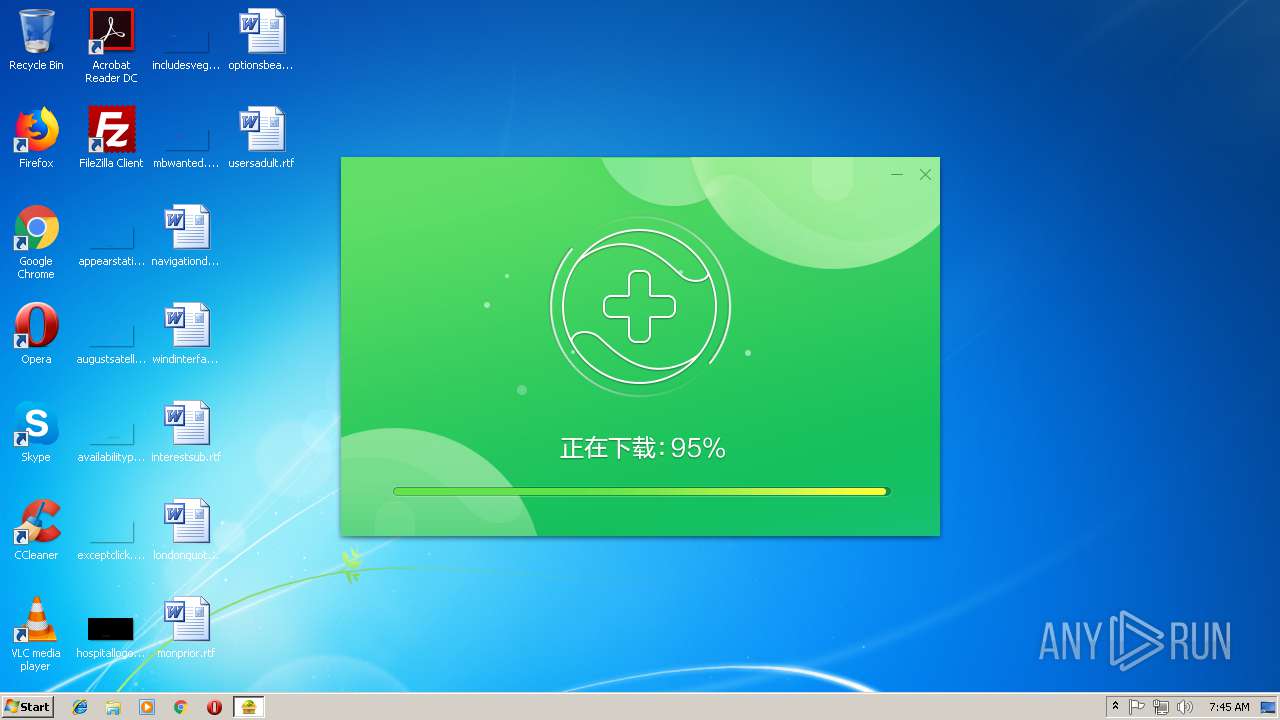
4012 | inst.exe | GET | — | 104.192.108.21:80 | http://dl.360safe.com/setup_11.5.0.2001p.exe | US | — | — | whitelisted |
4012 | inst.exe | GET | 200 | 171.8.167.89:80 | http://s.360.cn/safe/instcomp.htm?soft=1000&status=12&m=cfe1ce9b8f5123cc37f394accff90c49&from=safefinal_new&vv=10&ver=11.0.0.1477 | CN | — | — | whitelisted |
4012 | inst.exe | GET | — | 104.192.108.17:80 | http://dl.360safe.com/setup_11.5.0.2001p.exe | US | — | — | whitelisted |
4012 | inst.exe | GET | — | 104.192.108.17:80 | http://dl.360safe.com/setup_11.5.0.2001p.exe | US | — | — | whitelisted |
4012 | inst.exe | GET | — | 104.192.108.21:80 | http://dl.360safe.com/setup_11.5.0.2001p.exe | US | — | — | whitelisted |
4012 | inst.exe | GET | 200 | 171.8.167.89:80 | http://s.360.cn/safe/instcomp.htm?soft=2000&status=12&m=cfe1ce9b8f5123cc37f394accff90c49&from=safefinal_new&vv=10&ver=11.0.0.1477 | CN | — | — | whitelisted |
4012 | inst.exe | GET | — | 104.192.108.21:80 | http://dl.360safe.com/setup_11.5.0.2001p.exe | US | — | — | whitelisted |
4012 | inst.exe | GET | 200 | 171.8.167.89:80 | http://s.360.cn/safe/instcomp.htm?soft=1000&status=1&m=cfe1ce9b8f5123cc37f394accff90c49&from=safefinal_new&vv=10&ver=11.0.0.1477 | CN | — | — | whitelisted |
4012 | inst.exe | GET | 200 | 171.8.167.89:80 | http://s.360.cn/safe/instcomp.htm?soft=1000&status=8&m=cfe1ce9b8f5123cc37f394accff90c49&from=safefinal_new&vv=10&ver=11.0.0.1477 | CN | — | — | whitelisted |
4012 | inst.exe | GET | 200 | 171.8.167.89:80 | http://s.360.cn/safe/instcomp.htm?soft=425&status=1&mid=cfe1ce9b8f5123cc37f394accff90c49&from=safefinal_new&ver=11.0.0.1477&vv=10&appkey=&usetime=0&downrate=0&downlen=0 | CN | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 36.47.85.116:49549 | — | No.31,Jin-rong Street | CN | unknown |
4012 | inst.exe | 1.192.136.170:3478 | st.p.360.cn | No.31,Jin-rong Street | CN | unknown |
4012 | inst.exe | 171.8.167.89:80 | s.360.cn | No.31,Jin-rong Street | CN | suspicious |
4012 | inst.exe | 1.192.136.132:80 | tr.p.360.cn | No.31,Jin-rong Street | CN | unknown |
4012 | inst.exe | 1.192.194.210:443 | pinst.360.cn | No.31,Jin-rong Street | CN | unknown |
— | — | 222.32.81.6:41313 | — | HEXIE Information technology Co., Ltd. | CN | unknown |
— | — | 113.142.131.175:22410 | — | No.31,Jin-rong Street | CN | unknown |
4012 | inst.exe | 115.24.6.29:8090 | — | China Education and Research Network Center | CN | unknown |
— | — | 180.115.141.34:41279 | — | No.31,Jin-rong Street | CN | unknown |
— | — | 122.238.172.76:2108 | — | No.31,Jin-rong Street | CN | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
st.p.360.cn |
| whitelisted |
s.360.cn |
| whitelisted |
tr.p.360.cn |
| suspicious |
pinst.360.cn |
| whitelisted |
agt.p.360.cn |
| whitelisted |
dl.360safe.com |
| whitelisted |
agd.p.360.cn |
| whitelisted |
sd.p.360.cn |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
4012 | inst.exe | Generic Protocol Command Decode | ET INFO Session Traversal Utilities for NAT (STUN Binding Request obsolete rfc 3489 CHANGE-REQUEST attribute change IP flag false change port flag false) |
4012 | inst.exe | Generic Protocol Command Decode | ET INFO Session Traversal Utilities for NAT (STUN Binding Request obsolete rfc 3489 CHANGE-REQUEST attribute change IP flag true change port flag false) |
4012 | inst.exe | Generic Protocol Command Decode | ET INFO Session Traversal Utilities for NAT (STUN Binding Request obsolete rfc 3489 CHANGE-REQUEST attribute change IP flag false change port flag true) |
4012 | inst.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |